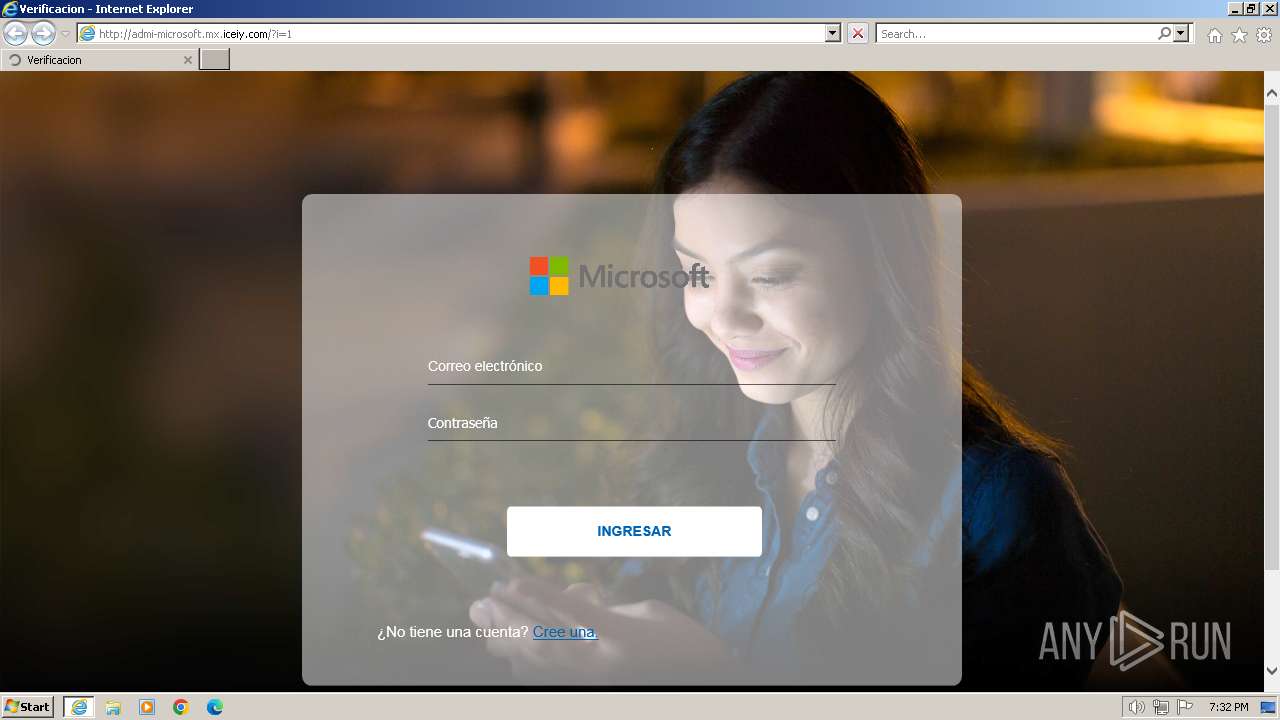
| URL: | admi-microsoft.mx.iceiy.com |
| Full analysis: | https://app.any.run/tasks/e871d80c-e49a-4d2b-b137-6418114bc0a1 |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2023, 19:31:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5940AEE13971D388576B8BAA837410E5 |
| SHA1: | 9059CC4701F4FDC9035F4E918CAE4279F1844DC1 |
| SHA256: | 0C1A278E4C79675D38CDBCEC3ACC10A0DD47F2E9DA44C9F65E272330C584C1D3 |
| SSDEEP: | 3:oIJxAutgz:oIbAuu |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- wmpnscfg.exe (PID: 120)
Application launched itself
- iexplore.exe (PID: 1072)
Reads the computer name
- wmpnscfg.exe (PID: 120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Internet Explorer\iexplore.exe" "admi-microsoft.mx.iceiy.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1072 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
21 112
Read events
21 044
Write events
66
Delete events
2
Modification events
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1072) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
26
Text files
37
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\3XG1DOXF.htm | html | |
MD5:A5993FAF102A1604FC96E3DF0B4AC2AA | SHA256:54326592ED5899E30F7FB4BF2F6B839C1C2D543350CAFBDEFDCBD27FA4164408 | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\L29VSDD5.txt | text | |
MD5:8A074F0AD0AA1A3905B6140D717402D6 | SHA256:D55BB2FE312AC071E7D41D365826973D254E267F7937DA11928A269B58F110E7 | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\CO2ZQRAV.htm | html | |
MD5:13F8D641C9495A4937A51A684A91AE58 | SHA256:7E0D14D4AEE129D0A6D75E274608297DCDC2F6CC787926EB84858EF7A2C1A499 | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\recibir[1].js | text | |
MD5:F75A6F1E4FDB9C1DEF264E6F8D87B6DE | SHA256:FBD80BCE4212A79AD73E8E5494144EC5F6703A6230D76A37EB54E546BF16A12E | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:42D7B505DCFA2990A28209234E0BE513 | SHA256:E10633B7B38B717BD5A8C53BAACCDF61BD4714906D387150E998518FB5D5015C | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E87CE99F124623F95572A696C80EFCAF_F134D707C209C83E02D4485138FE5D48 | binary | |
MD5:BFF1B13E838EFA1607A24232DA9B75BA | SHA256:4A2FC8B714CA5E9A734A34E8E7D383D6ECCEF9E8E9A4942F432B0AE7770F5358 | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E87CE99F124623F95572A696C80EFCAF_F134D707C209C83E02D4485138FE5D48 | binary | |
MD5:CA53CAB2900193D0AA126102C46AA38A | SHA256:31BD6038A82A73EEF708CD9E4D6BFF0A49D40609619185AFD55FF0C8A070E0E0 | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Montserrat-Regular[1].htm | html | |
MD5:56403A22E907C6B48209AD85146010E7 | SHA256:091E2594F8A0005298D07B48B82EB1A7D5FBF21BF14967A386B066CFB2E24210 | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Montserrat-Italic[1].htm | html | |
MD5:56403A22E907C6B48209AD85146010E7 | SHA256:091E2594F8A0005298D07B48B82EB1A7D5FBF21BF14967A386B066CFB2E24210 | |||
| 2068 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:8AEA421CE0EFF50A110201B7F5DE8174 | SHA256:48704288B1093D4323D6013EDA344E3816566C59C60B35DDB5B9EF0988986FD6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
45
DNS requests
18
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2068 | iexplore.exe | GET | 200 | 185.27.134.60:80 | http://admi-microsoft.mx.iceiy.com/ | GB | html | 838 b | unknown |
2068 | iexplore.exe | GET | 200 | 185.27.134.60:80 | http://admi-microsoft.mx.iceiy.com/?i=1 | GB | html | 12.7 Kb | unknown |
2068 | iexplore.exe | GET | 200 | 185.27.134.60:80 | http://admi-microsoft.mx.iceiy.com/Logo-PNG.png | GB | image | 23.8 Kb | unknown |
2068 | iexplore.exe | GET | 200 | 185.27.134.60:80 | http://admi-microsoft.mx.iceiy.com/recibir.js | GB | text | 697 b | unknown |
2068 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2fa7828491fdb1d6 | GB | compressed | 4.66 Kb | unknown |
2068 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
2068 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?608cb4ab6d3f68d3 | GB | compressed | 4.66 Kb | unknown |
2068 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
2068 | iexplore.exe | GET | 302 | 185.27.134.60:80 | http://admi-microsoft.mx.iceiy.com/fonts/montserrat/Montserrat-Light.ttf | GB | html | 215 b | unknown |
2068 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEA1uFYrLabZxEtE2U5X5DGM%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2068 | iexplore.exe | 185.27.134.60:80 | admi-microsoft.mx.iceiy.com | Wildcard UK Limited | GB | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2068 | iexplore.exe | 142.250.186.42:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
2068 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2068 | iexplore.exe | 172.217.23.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2068 | iexplore.exe | 173.231.16.77:443 | api.ipify.org | WEBNX | US | unknown |
2068 | iexplore.exe | 34.117.186.192:443 | ipinfo.io | GOOGLE-CLOUD-PLATFORM | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
admi-microsoft.mx.iceiy.com |
| unknown |
ajax.googleapis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
api.ipify.org |
| shared |
ipinfo.io |
| shared |
aeonfree.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
2068 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2068 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2068 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
2068 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
2068 | iexplore.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2068 | iexplore.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2068 | iexplore.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2068 | iexplore.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |