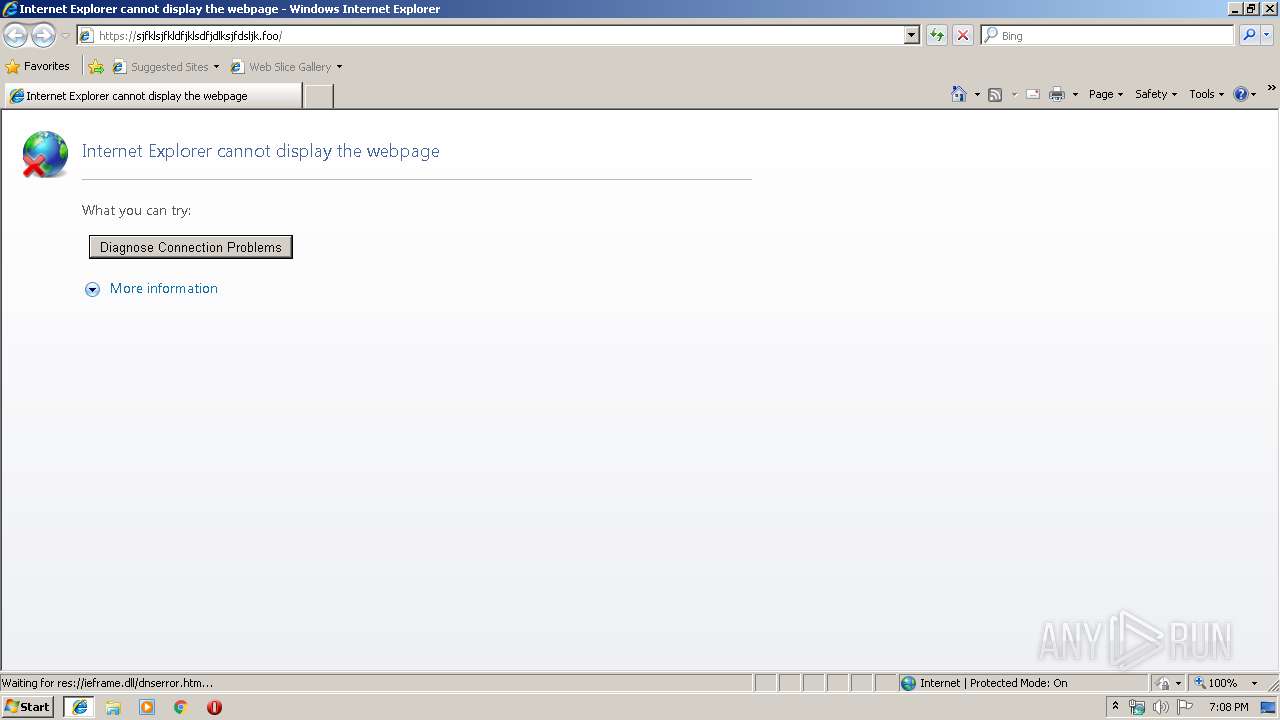
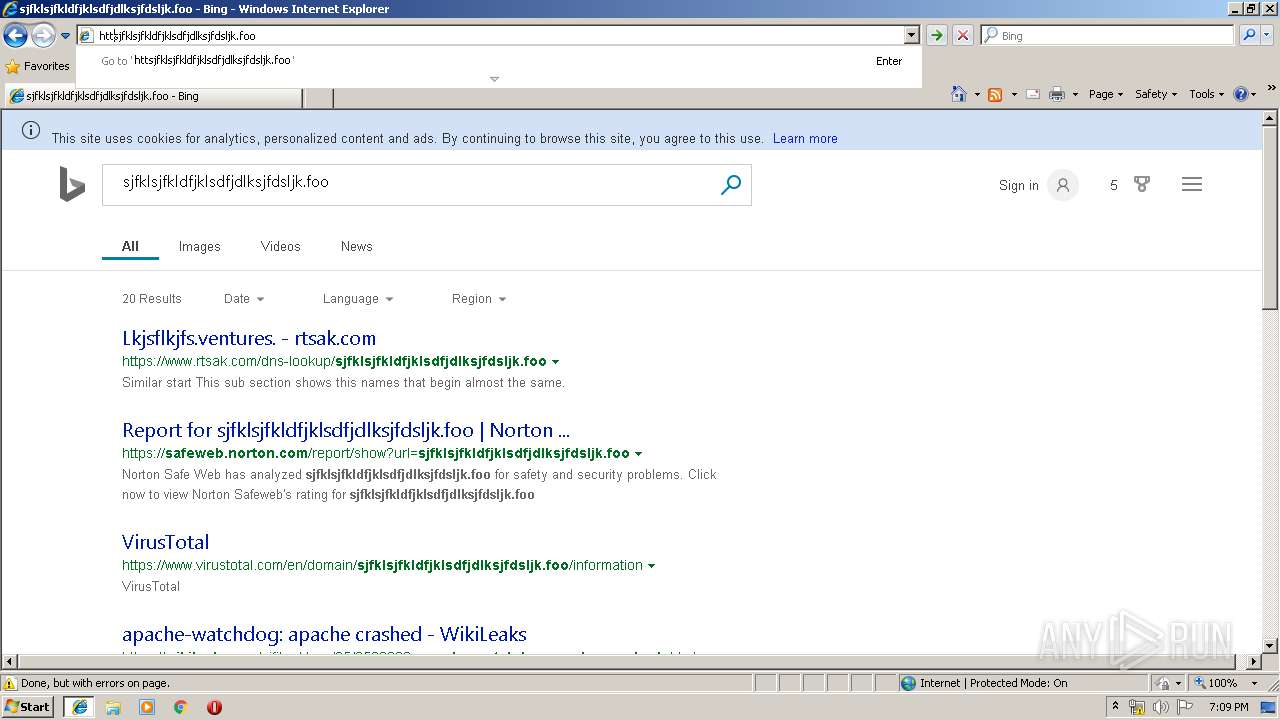
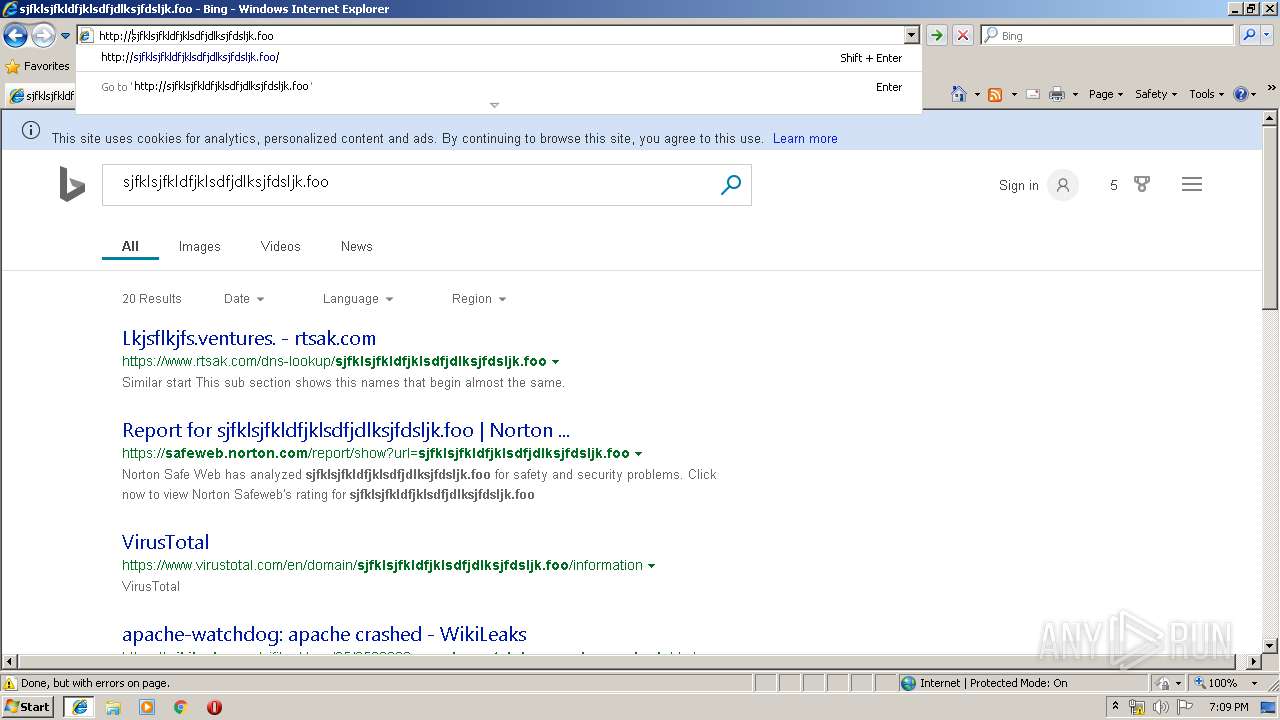
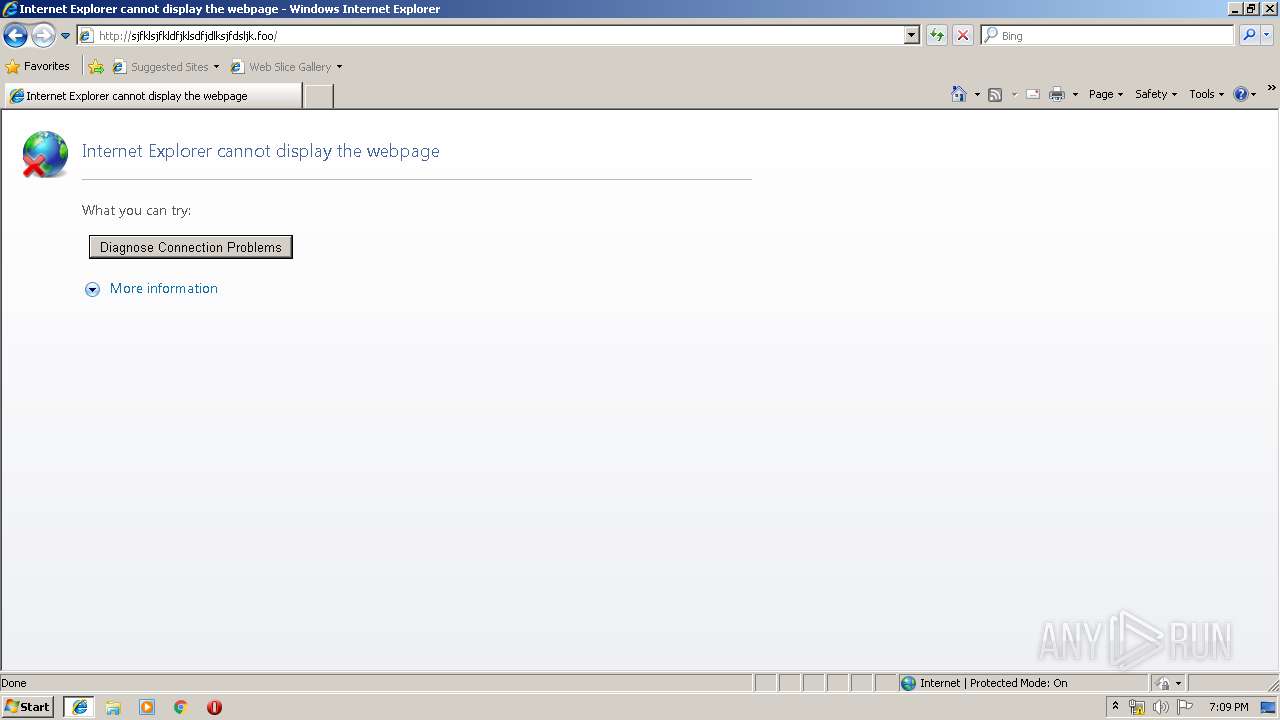
| URL: | https://sjfklsjfkldfjklsdfjdlksjfdsljk.foo |
| Full analysis: | https://app.any.run/tasks/f46d5241-74d4-4afc-a675-2d818db47b6c |
| Verdict: | No threats detected |
| Analysis date: | August 27, 2019, 18:08:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 23CF753705D094BB779344BBAAA3E73F |
| SHA1: | 74485DA315E93EAA34ED77FC49CDDC5D34CFBBFB |
| SHA256: | 0C12096CF631791EB506826F45658F1FCF729336ABCD517495A09A6BC299298C |
| SSDEEP: | 3:N8CDgN5PdL6K:2CDgNRd1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3556)
- iexplore.exe (PID: 3892)
Application launched itself
- iexplore.exe (PID: 3556)
Changes internet zones settings
- iexplore.exe (PID: 3556)
Reads internet explorer settings
- iexplore.exe (PID: 3892)
Reads settings of System Certificates
- iexplore.exe (PID: 3892)
Creates files in the user directory
- iexplore.exe (PID: 3892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3556 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3892 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3556 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
488
Read events
369
Write events
117
Delete events
2
Modification events
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {B39DFBB1-C8F5-11E9-B86F-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3556) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307080002001B00120008002B001C01 | |||
Executable files
0
Suspicious files
0
Text files
70
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:0D1372C6EC8E3EC6375552E822F02C78 | SHA256:2197D003E0D315AC1AADBC0CA82D9A4390720D4ABA9A114D182B47A6EDD2C4F5 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5213UZDR\dnserror[1] | html | |
MD5:68E03ED57EC741A4AFBBCD11FAB1BDBE | SHA256:1FF3334C3EB27033F8F37029FD72F648EDD4551FCE85FC1F5159FEAEA1439630 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7KHOTT9L\ErrorPageTemplate[1] | text | |
MD5:F4FE1CB77E758E1BA56B8A8EC20417C5 | SHA256:8D018639281B33DA8EB3CE0B21D11E1D414E59024C3689F92BE8904EB5779B5F | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5213UZDR\noConnect[1] | image | |
MD5:3CB8FACCD5DE434D415AB75C17E8FD86 | SHA256:6976C426E3AC66D66303C114B22B2B41109A7DE648BA55FFC3E5A53BD0DB09E7 | |||
| 3556 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\X061CYTG\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ROXI36JF\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3892 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\X061CYTG\httpErrorPagesScripts[1] | text | |
MD5:E7CA76A3C9EE0564471671D500E3F0F3 | SHA256:58268CA71A28973B756A48BBD7C9DC2F6B87B62AE343E582CE067C725275B63C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
15
DNS requests
9
Threats
0
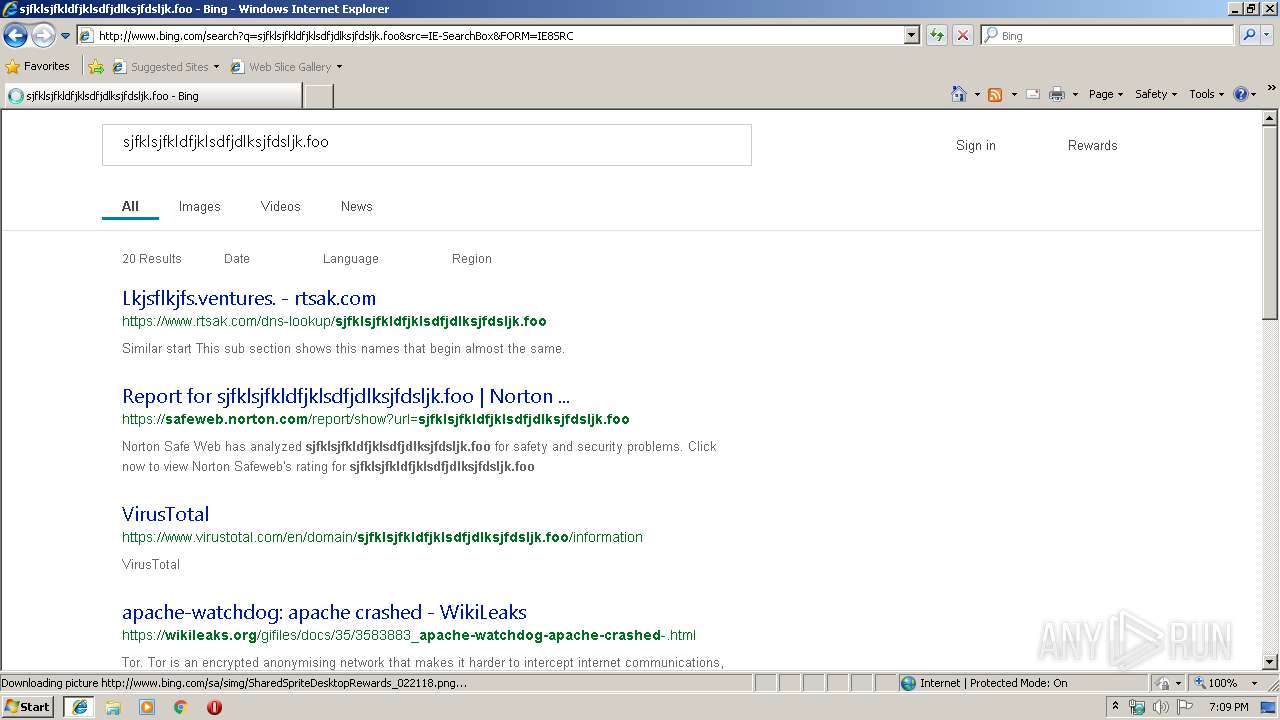
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3892 | iexplore.exe | POST | 200 | 204.79.197.200:80 | http://www.bing.com/rewardsapp/ncheader?ver=8_1_2_6229154&IID=SERP.5027&IG=8E9D882B9FA2451CA5618F9ADED5758A | US | html | 97 b | whitelisted |
3556 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=8E9D882B9FA2451CA5618F9ADED5758A&CID=1250681A4BB46FEB2E4F65DF4A586EB3&Type=Event.CPT&DATA={"pp":{"S":"L","FC":16,"BC":250,"SE":-1,"TC":-1,"H":266,"BP":3532,"CT":3547,"IL":3},"ad":[-1,-1,1260,560,1260,498,0]}&P=SERP&DA=DUB02 | US | compressed | 32.5 Kb | whitelisted |
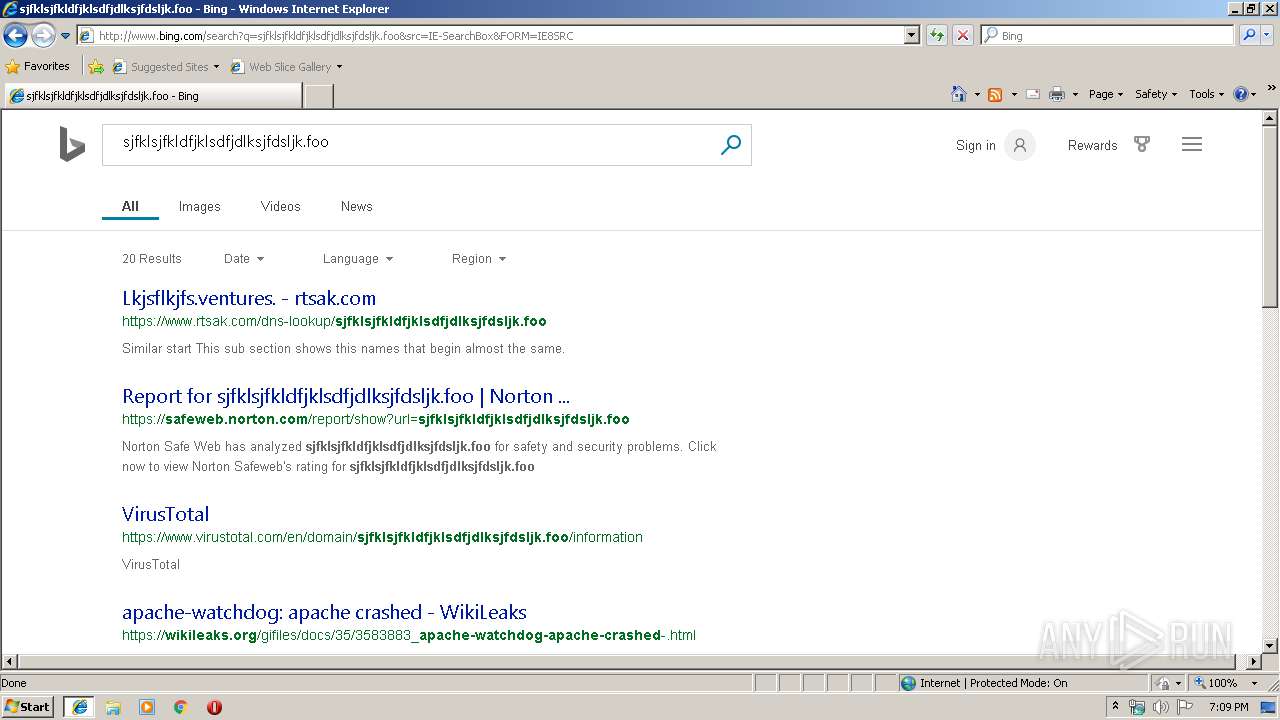
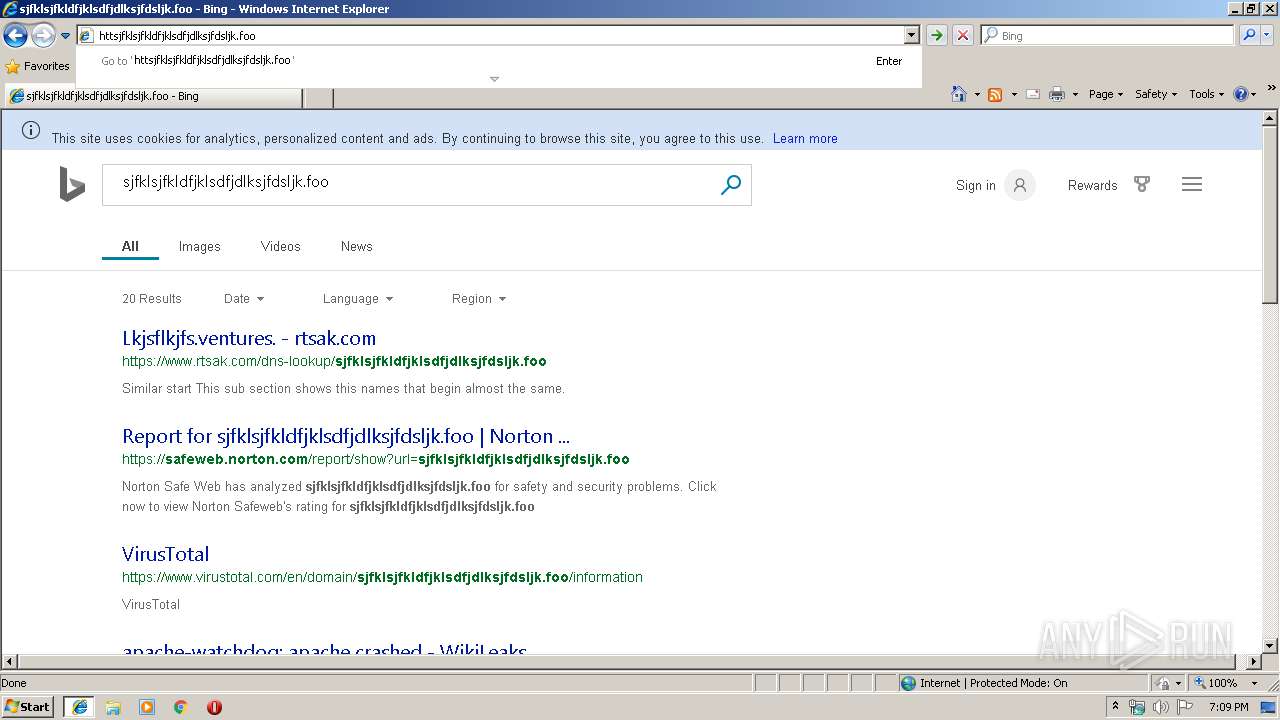
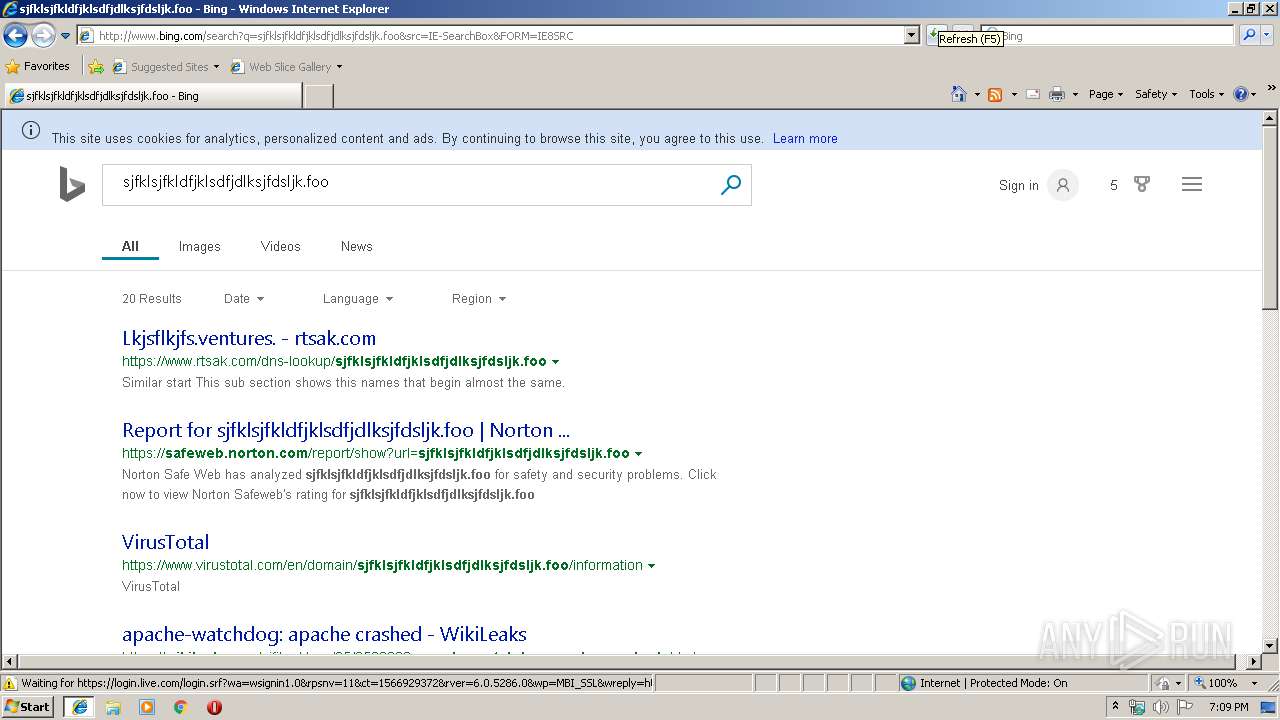
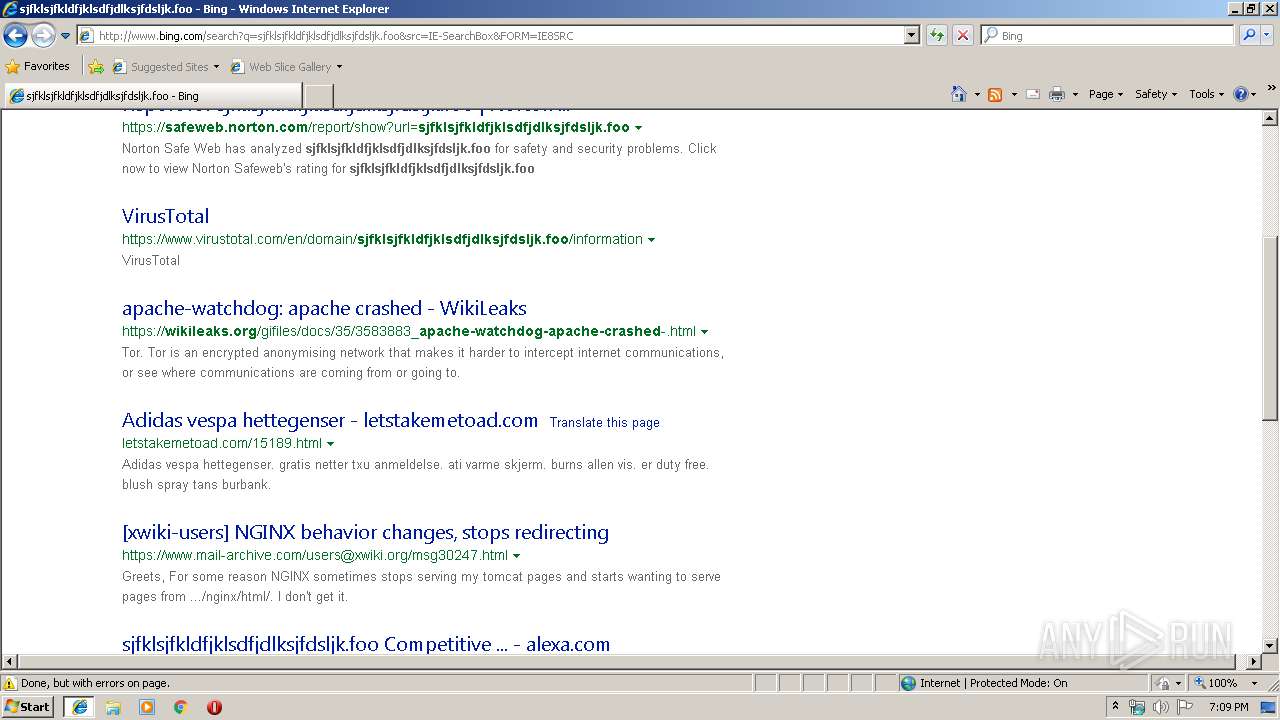
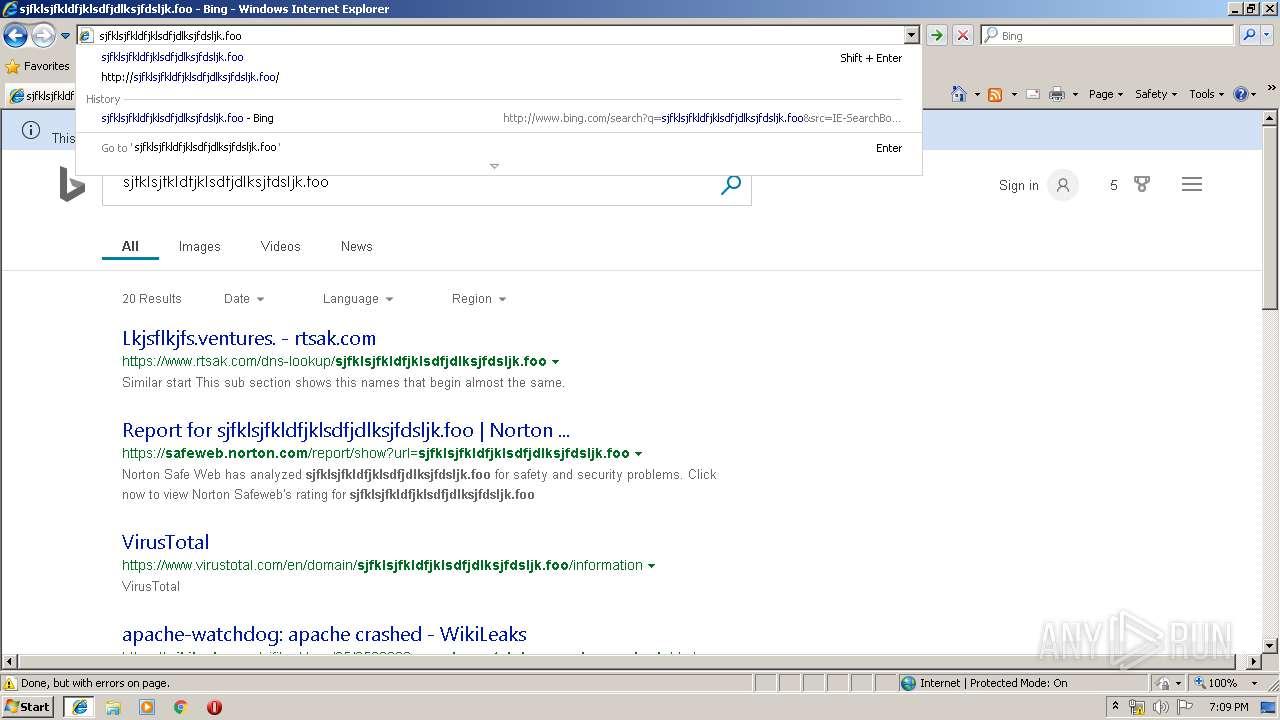
3892 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=sjfklsjfkldfjklsdfjdlksjfdsljk.foo&src=IE-SearchBox&FORM=IE8SRC | US | html | 32.5 Kb | whitelisted |
3892 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/30/1b/cj,nj/3f1e2270/f8c6dd44.js | US | text | 773 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/4X/2Z/cj,nj/8e81c8c7/37f3511b.js | US | text | 529 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/30/1H/cj,nj/bf587ad6/f1d86b5a.js | US | text | 181 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/5b/24/cj,nj/08abbb2f/e177b199.js | US | text | 2.86 Kb | whitelisted |
3892 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=8E9D882B9FA2451CA5618F9ADED5758A&CID=1250681A4BB46FEB2E4F65DF4A586EB3&Type=Event.ClientInst&DATA=[{"T":"CI.ClientSideLoggingAudit","FID":"CI","Name":"gif_request_sent","Text":"true"}] | US | compressed | 529 b | whitelisted |
3892 | iexplore.exe | GET | 200 | 40.86.215.224:80 | http://85e5363e73628ef2cd3b2f106fb1b3b4.clo.footprintdns.com/apc/trans.gif | CA | image | 43 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3556 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3892 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3892 | iexplore.exe | 40.90.137.124:443 | login.live.com | Microsoft Corporation | US | unknown |
3892 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3892 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3892 | iexplore.exe | 40.86.215.224:80 | 85e5363e73628ef2cd3b2f106fb1b3b4.clo.footprintdns.com | Microsoft Corporation | CA | whitelisted |
3892 | iexplore.exe | 168.62.19.224:80 | 806bda6b479486244a98565dbe7021cd.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
3892 | iexplore.exe | 204.79.197.222:80 | fp.msedge.net | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
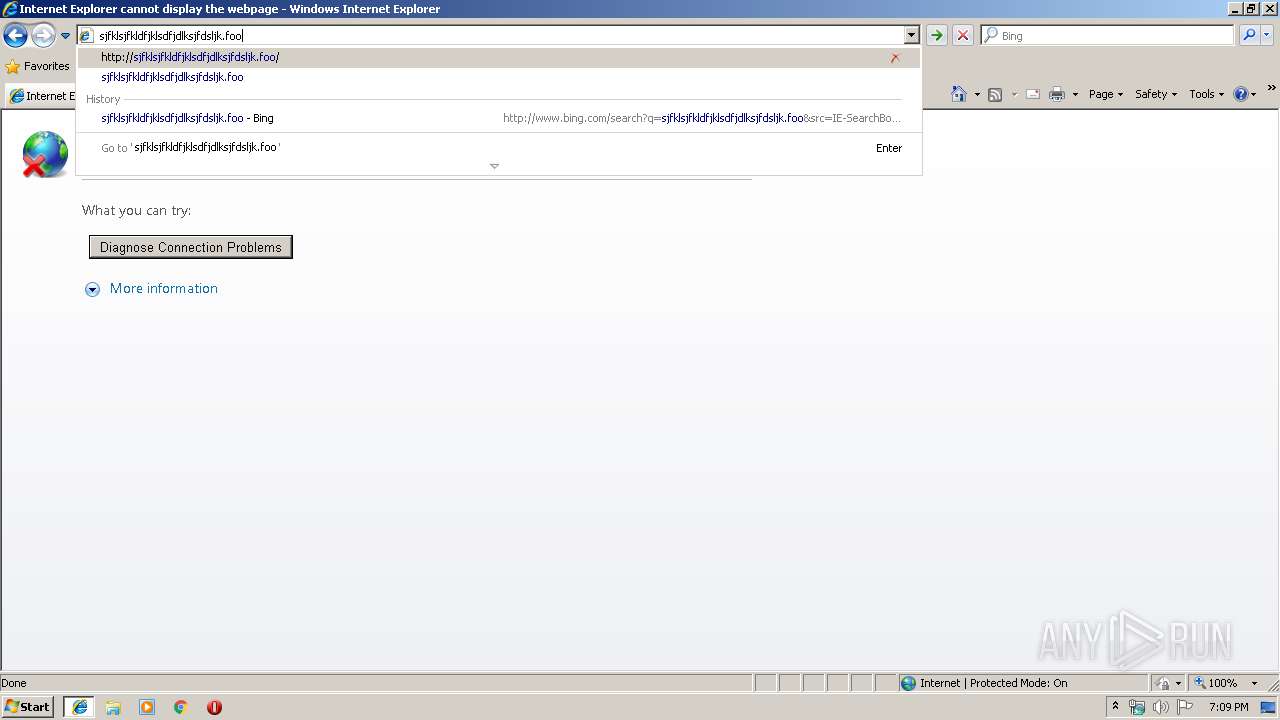
sjfklsjfkldfjklsdfjdlksjfdsljk.foo |
| malicious |
dns.msftncsi.com |
| shared |
login.live.com |
| whitelisted |
85e5363e73628ef2cd3b2f106fb1b3b4.clo.footprintdns.com |
| unknown |
cb43275e0ea29c039f402161e7b55024.clo.footprintdns.com |
| unknown |
806bda6b479486244a98565dbe7021cd.clo.footprintdns.com |
| unknown |
fp.msedge.net |
| whitelisted |