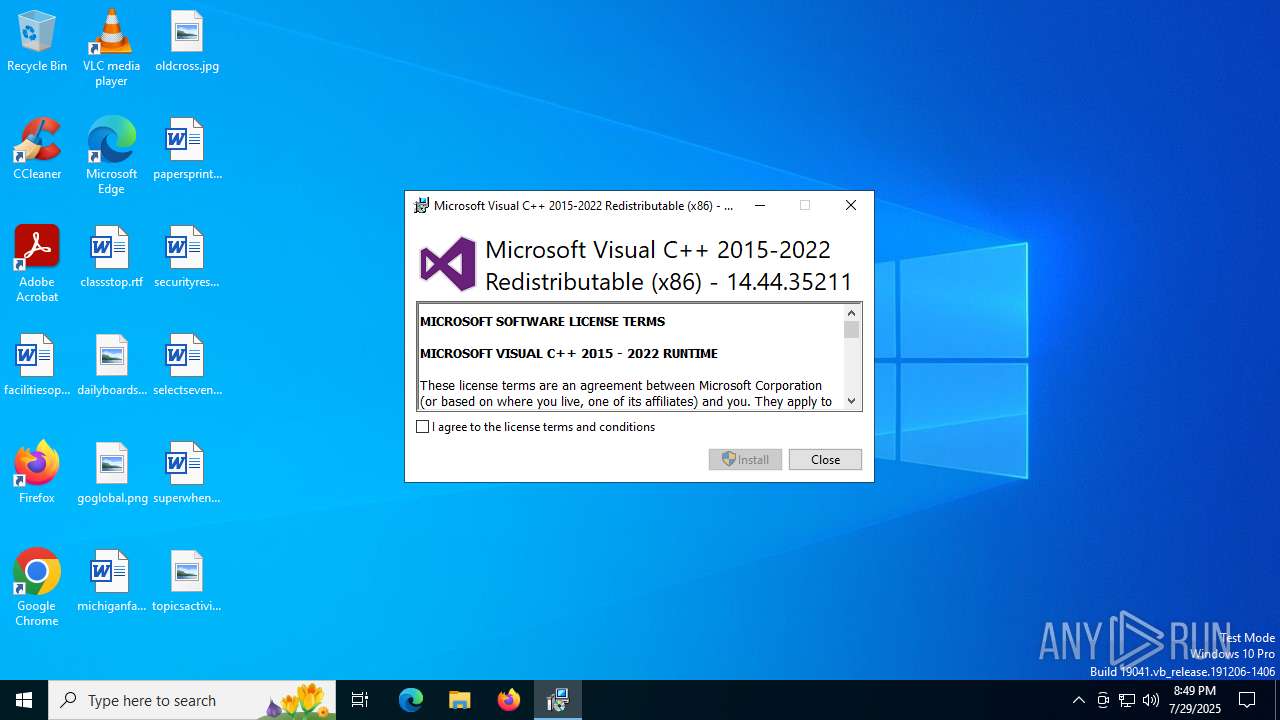
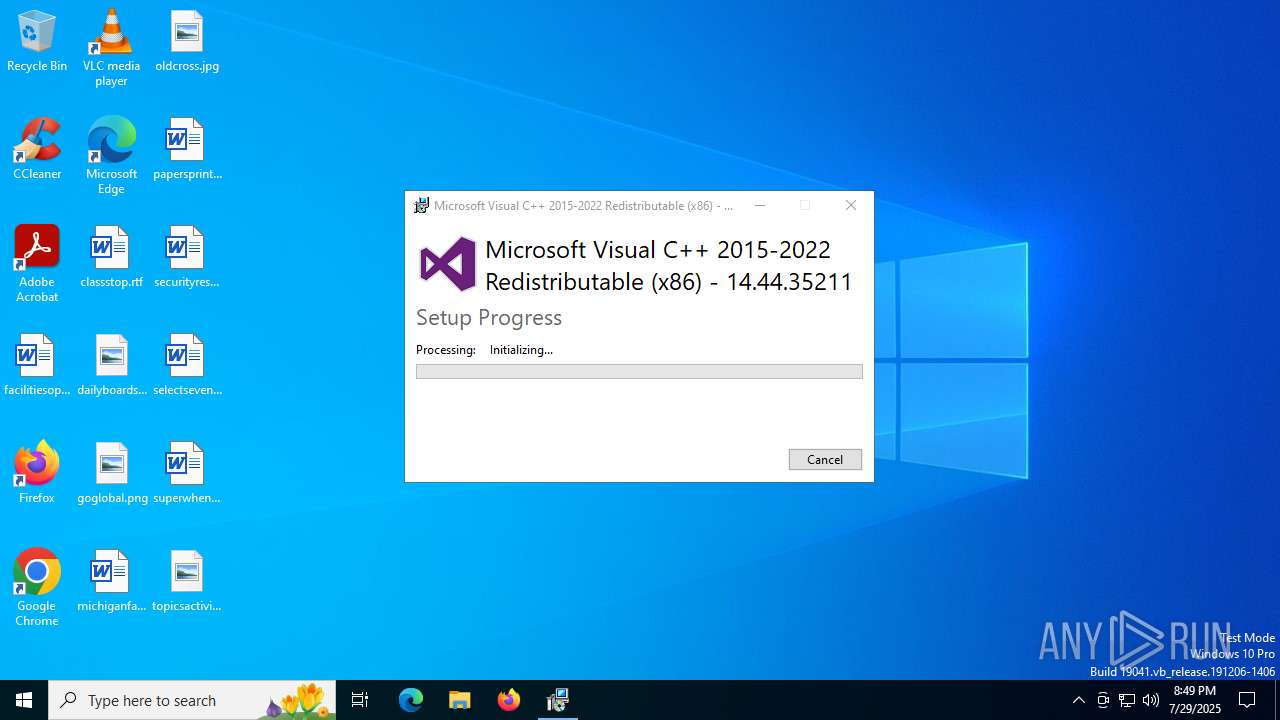
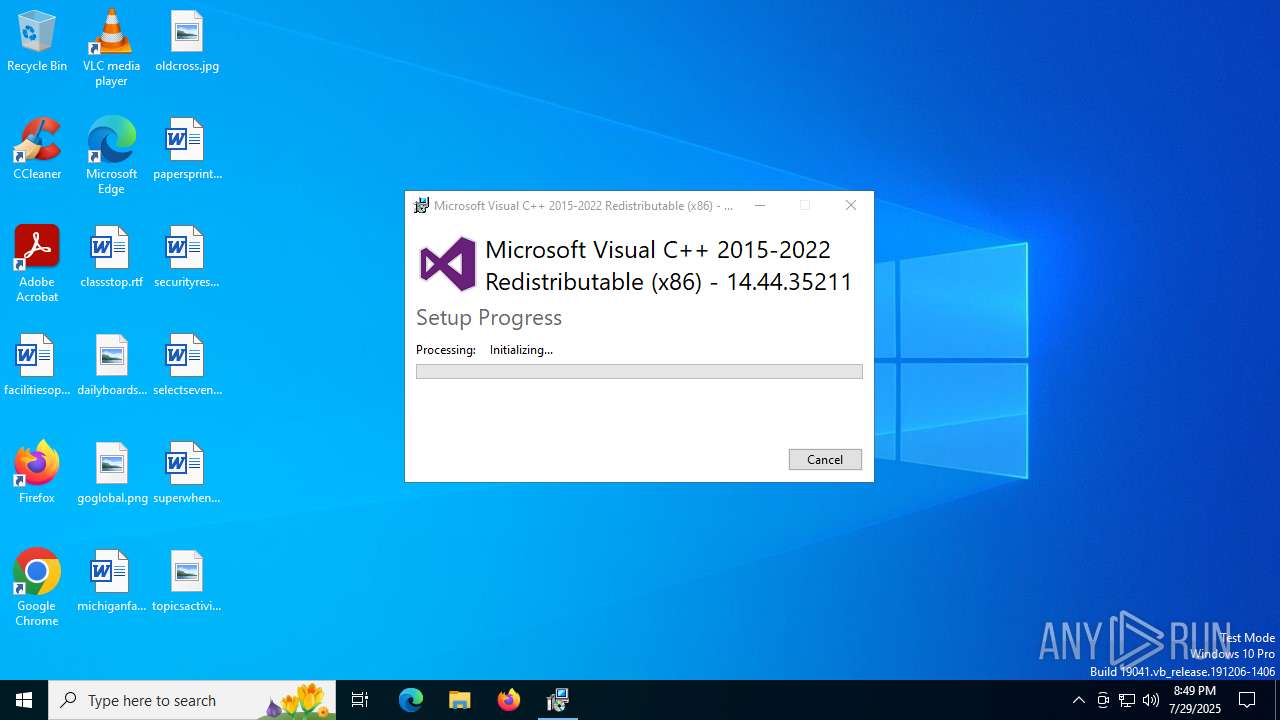
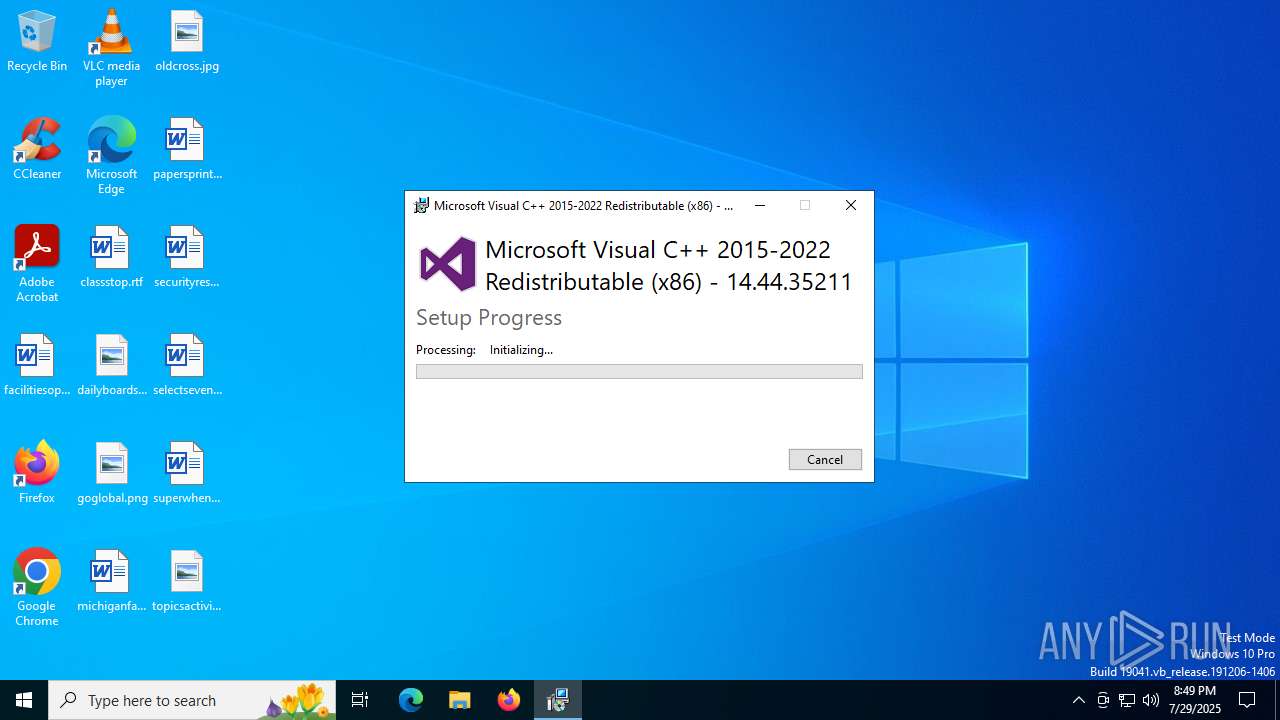
| File name: | VC_redist_14.44.35211.0_32bit.exe |
| Full analysis: | https://app.any.run/tasks/eedddc30-2c6c-4ed1-95ad-f4ef5baad875 |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2025, 20:49:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 99F52708B06B9C695A8D64A44740BF08 |
| SHA1: | C2743FFC36D2AF40ADE0E370BE52D6B202874114 |
| SHA256: | 0C09F2611660441084CE0DF425C51C11E147E6447963C3690F97E0B25C55ED64 |
| SSDEEP: | 98304:I1svXJG6gIS6tHeVtWLPmZbbnTpwyfy8QAq38pOPdzMGqoXlF0cgl95rQXcA3RGr:j8+enNsqQ3pC/Ex9bb4 |
MALICIOUS
Changes the autorun value in the registry
- VC_redist.x86.exe (PID: 4372)
SUSPICIOUS
Process drops legitimate windows executable
- VC_redist_14.44.35211.0_32bit.exe (PID: 1728)
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
- VC_redist.x86.exe (PID: 4372)
- msiexec.exe (PID: 4080)
- VC_redist.x86.exe (PID: 2620)
Starts a Microsoft application from unusual location
- VC_redist_14.44.35211.0_32bit.exe (PID: 1728)
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
- VC_redist.x86.exe (PID: 4372)
Executable content was dropped or overwritten
- VC_redist_14.44.35211.0_32bit.exe (PID: 1728)
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
- VC_redist.x86.exe (PID: 4372)
- VC_redist.x86.exe (PID: 4188)
- VC_redist.x86.exe (PID: 2620)
Searches for installed software
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
- dllhost.exe (PID: 6312)
- VC_redist.x86.exe (PID: 2620)
- VC_redist.x86.exe (PID: 4188)
Reads security settings of Internet Explorer
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
- VC_redist.x86.exe (PID: 4188)
Starts itself from another location
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
Executes as Windows Service
- VSSVC.exe (PID: 4456)
Creates a software uninstall entry
- VC_redist.x86.exe (PID: 4372)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4080)
Application launched itself
- VC_redist.x86.exe (PID: 4460)
- VC_redist.x86.exe (PID: 4188)
The process drops C-runtime libraries
- msiexec.exe (PID: 4080)
INFO
The sample compiled with english language support
- VC_redist_14.44.35211.0_32bit.exe (PID: 1728)
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
- VC_redist.x86.exe (PID: 4372)
- msiexec.exe (PID: 4080)
- VC_redist.x86.exe (PID: 4188)
- VC_redist.x86.exe (PID: 2620)
Checks supported languages
- VC_redist_14.44.35211.0_32bit.exe (PID: 1728)
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
- VC_redist.x86.exe (PID: 4372)
- msiexec.exe (PID: 4080)
- VC_redist.x86.exe (PID: 4460)
- VC_redist.x86.exe (PID: 4188)
- VC_redist.x86.exe (PID: 2620)
Create files in a temporary directory
- VC_redist_14.44.35211.0_32bit.exe (PID: 1728)
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
- VC_redist.x86.exe (PID: 4372)
- VC_redist.x86.exe (PID: 4188)
Reads the computer name
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
- VC_redist.x86.exe (PID: 4372)
- msiexec.exe (PID: 4080)
- VC_redist.x86.exe (PID: 4188)
- VC_redist.x86.exe (PID: 2620)
Process checks computer location settings
- VC_redist_14.44.35211.0_32bit.exe (PID: 6680)
- VC_redist.x86.exe (PID: 4188)
Manages system restore points
- SrTasks.exe (PID: 6004)
Launching a file from a Registry key
- VC_redist.x86.exe (PID: 4372)
Creates files in the program directory
- VC_redist.x86.exe (PID: 4372)
Reads the machine GUID from the registry
- VC_redist.x86.exe (PID: 4372)
- msiexec.exe (PID: 4080)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4080)
Reads the software policy settings
- msiexec.exe (PID: 4080)
Creates a software uninstall entry
- msiexec.exe (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:22 22:14:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 314368 |
| InitializedDataSize: | 164352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x302e5 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 14.44.35211.0 |
| ProductVersionNumber: | 14.44.35211.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.44.35211 |
| FileVersion: | 14.44.35211.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | VC_redist.x86.exe |
| ProductName: | Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.44.35211 |
| ProductVersion: | 14.44.35211.0 |
Total processes
150
Monitored processes
12
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1728 | "C:\Users\admin\AppData\Local\Temp\VC_redist_14.44.35211.0_32bit.exe" | C:\Users\admin\AppData\Local\Temp\VC_redist_14.44.35211.0_32bit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.44.35211 Exit code: 0 Version: 14.44.35211.0 Modules
| |||||||||||||||
| 2620 | "C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{3D0EB09A-911F-47F5-B430-549D3A134B9F} {DBB90E5B-E3F4-4EE7-BE55-3CC33543B81B} 4188 | C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 4080 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4188 | "C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -burn.clean.room="C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -burn.filehandle.attached=536 -burn.filehandle.self=556 -uninstall -quiet -burn.related.upgrade -burn.ancestors={0b5169e3-39da-4313-808e-1f9c0407f3bf} -burn.filehandle.self=1128 -burn.embedded BurnPipe.{44D78198-69AA-4363-AEF9-AFB10DF3E108} {659AA81B-E75D-432C-9564-D24CE0026C8E} 4372 | C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 4372 | "C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.be\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{E53758BC-8A0C-456D-BAE6-9D07CD51D7CB} {F8D87826-E5CD-42BC-8EB9-E5138C99C0A5} 6680 | C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.be\VC_redist.x86.exe | VC_redist_14.44.35211.0_32bit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.44.35211 Exit code: 0 Version: 14.44.35211.0 Modules
| |||||||||||||||
| 4456 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4460 | "C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -uninstall -quiet -burn.related.upgrade -burn.ancestors={0b5169e3-39da-4313-808e-1f9c0407f3bf} -burn.filehandle.self=1128 -burn.embedded BurnPipe.{44D78198-69AA-4363-AEF9-AFB10DF3E108} {659AA81B-E75D-432C-9564-D24CE0026C8E} 4372 | C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe | — | VC_redist.x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 6004 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6312 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6360 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 385
Read events
10 516
Write events
606
Delete events
263
Modification events
| (PID) Process: | (4372) VC_redist.x86.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000D260714BCA00DC01141100004C090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6312) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000A8D3734BCA00DC01A818000068190000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6312) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000006A62904BCA00DC01A818000068190000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6312) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000006A62904BCA00DC01A818000068190000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6312) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000002DB2924BCA00DC01A818000068190000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6312) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000005215954BCA00DC01A818000068190000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6312) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6312) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000B1C7C44BCA00DC01A818000068190000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6312) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009C2BC74BCA00DC01A8180000801B0000E80300000100000000000000000000003F819CC02769434EA28C1BA11AED46F900000000000000000000000000000000 | |||
| (PID) Process: | (4456) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 480000000000000029D9D74BCA00DC016811000014050000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
65
Suspicious files
35
Text files
67
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6680 | VC_redist_14.44.35211.0_32bit.exe | C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.ba\logo.png | image | |
MD5:D6BD210F227442B3362493D046CEA233 | SHA256:335A256D4779EC5DCF283D007FB56FD8211BBCAF47DCD70FE60DED6A112744EF | |||
| 1728 | VC_redist_14.44.35211.0_32bit.exe | C:\Users\admin\AppData\Local\Temp\{FCB10958-18C0-4BCD-87EA-722D05D1DF88}\.cr\VC_redist_14.44.35211.0_32bit.exe | executable | |
MD5:F216F5EE89B18A28A3936FAB57C16179 | SHA256:4A6E1044FF0F49D2E3B12F7C40352C7E573E0C58F3B3CC0B55B63C95EDE87828 | |||
| 6680 | VC_redist_14.44.35211.0_32bit.exe | C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.ba\1031\thm.wxl | xml | |
MD5:561F3F32DB2453647D1992D4D932E872 | SHA256:8E0DCA6E085744BFCBFF46F7DCBCFA6FBD722DFA52013EE8CEEAF682D7509581 | |||
| 6680 | VC_redist_14.44.35211.0_32bit.exe | C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.ba\1029\thm.wxl | xml | |
MD5:16343005D29EC431891B02F048C7F581 | SHA256:07FB3EC174F25DFBE532D9D739234D9DFDA8E9D34F01FE660C5B4D56989FA779 | |||
| 6680 | VC_redist_14.44.35211.0_32bit.exe | C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.ba\wixstdba.dll | executable | |
MD5:F68F43F809840328F4E993A54B0D5E62 | SHA256:E921F69B9FB4B5AD4691809D06896C5F1D655AB75E0CE94A372319C243C56D4E | |||
| 6680 | VC_redist_14.44.35211.0_32bit.exe | C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.ba\1029\license.rtf | text | |
MD5:E7DC9CA9474A13FA4529D91BCD2AB8CC | SHA256:503C433DCDE2F3A9E7D388A5FF2B0612E7D8F90F5188D5B2B60228DB33044FDE | |||
| 6680 | VC_redist_14.44.35211.0_32bit.exe | C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.ba\license.rtf | text | |
MD5:04B33F0A9081C10E85D0E495A1294F83 | SHA256:8099DC3CF9502C335DA829E5C755948A12E3E6DE490EB492A99DEB673D883D8B | |||
| 6680 | VC_redist_14.44.35211.0_32bit.exe | C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.ba\1028\license.rtf | text | |
MD5:2B063D92663595DFE4781AE687A03D86 | SHA256:44C76290F7A2E45940E8338912FEB49BCF4E071CFA85D2D34762857743ACBC8D | |||
| 6680 | VC_redist_14.44.35211.0_32bit.exe | C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.ba\thm.wxl | xml | |
MD5:FBFCBC4DACC566A3C426F43CE10907B6 | SHA256:70400F181D00E1769774FF36BCD8B1AB5FBC431418067D31B876D18CC04EF4CE | |||
| 6680 | VC_redist_14.44.35211.0_32bit.exe | C:\Users\admin\AppData\Local\Temp\{D31E023B-5222-4933-949D-AA970B322F8C}\.ba\thm.xml | xml | |
MD5:F62729C6D2540015E072514226C121C7 | SHA256:F13BAE0EC08C91B4A315BB2D86EE48FADE597E7A5440DCE6F751F98A3A4D6916 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
36
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.48.23.162:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
3644 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4080 | msiexec.exe | GET | 200 | 23.48.23.162:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4080 | msiexec.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6668 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5968 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.48.23.162:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5328 | SearchApp.exe | 92.123.104.31:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5328 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
fp-afd-nocache.azureedge.net |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |