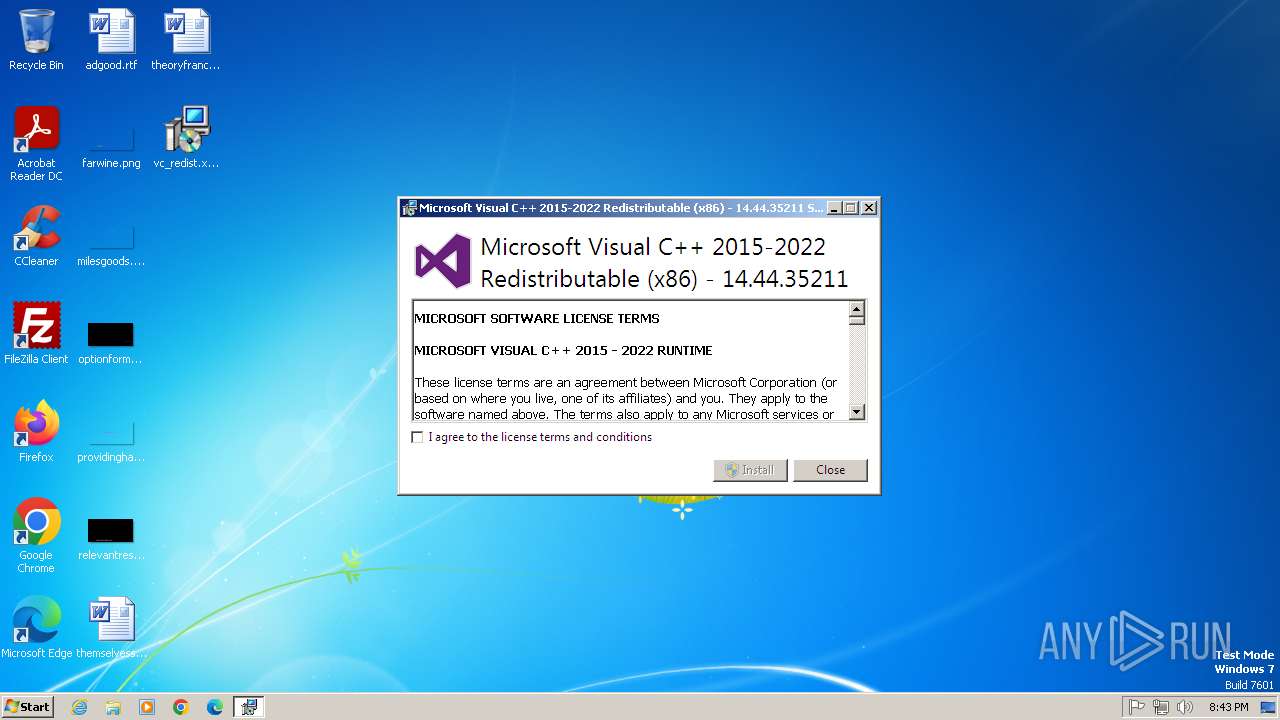
| download: | /vs/17/release/vc_redist.x86.exe |
| Full analysis: | https://app.any.run/tasks/e6af8956-8bf3-48ac-bfc4-1e7dd833bff2 |
| Verdict: | Malicious activity |
| Analysis date: | July 24, 2025, 19:43:18 |
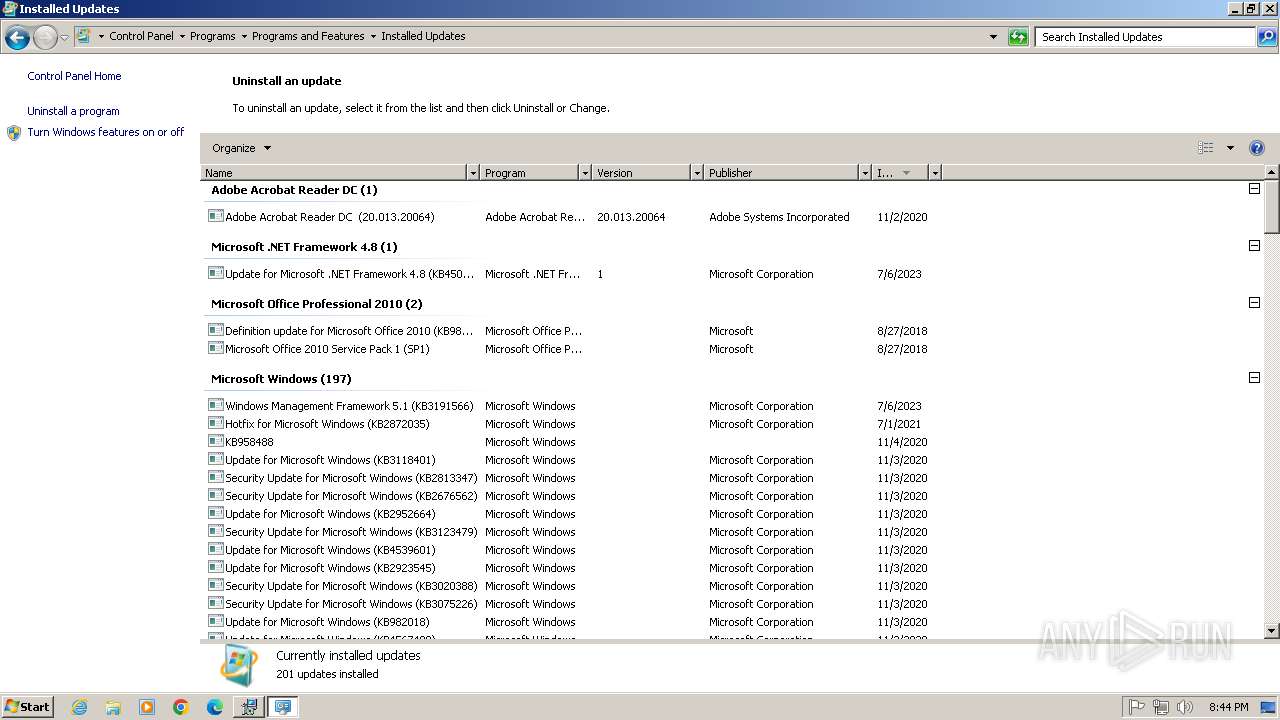
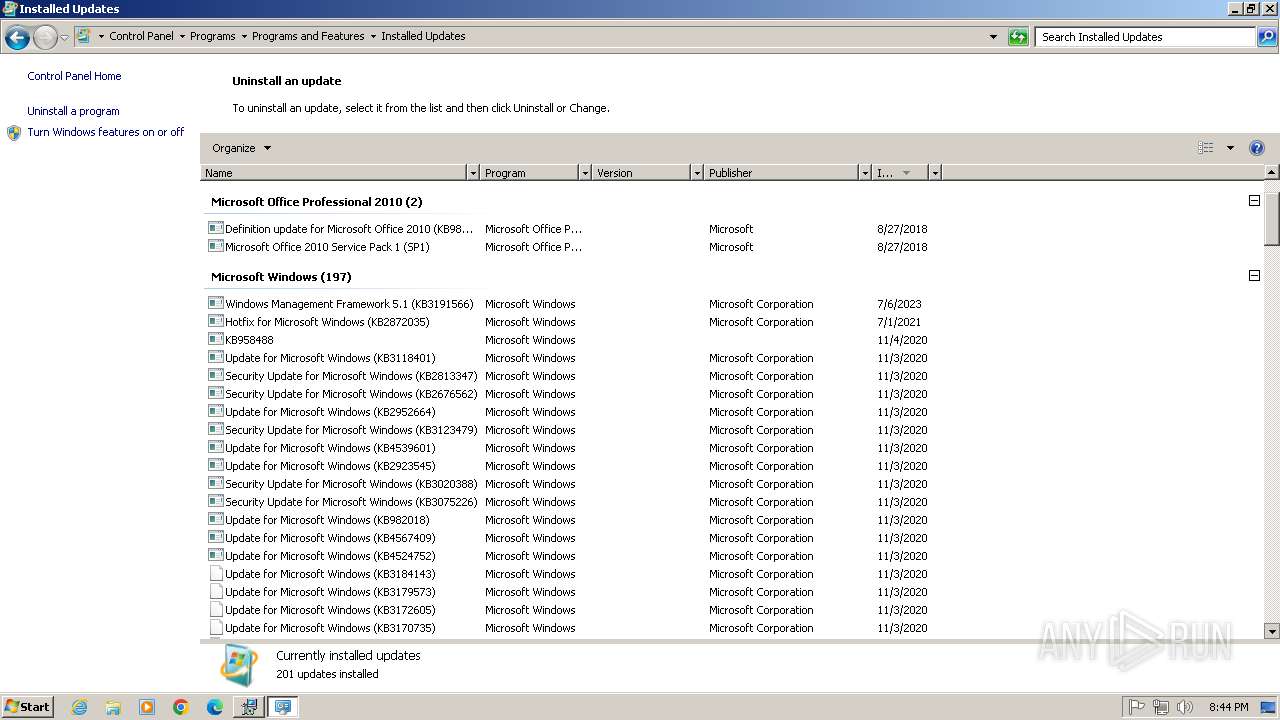
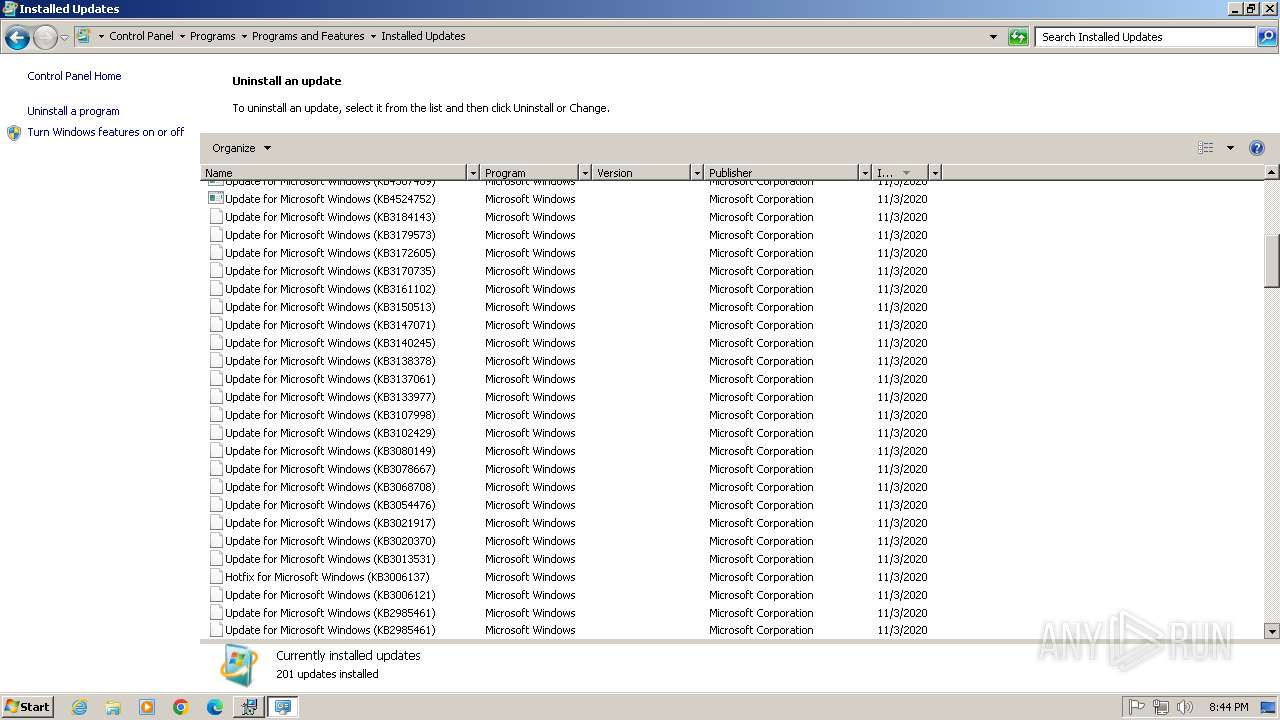
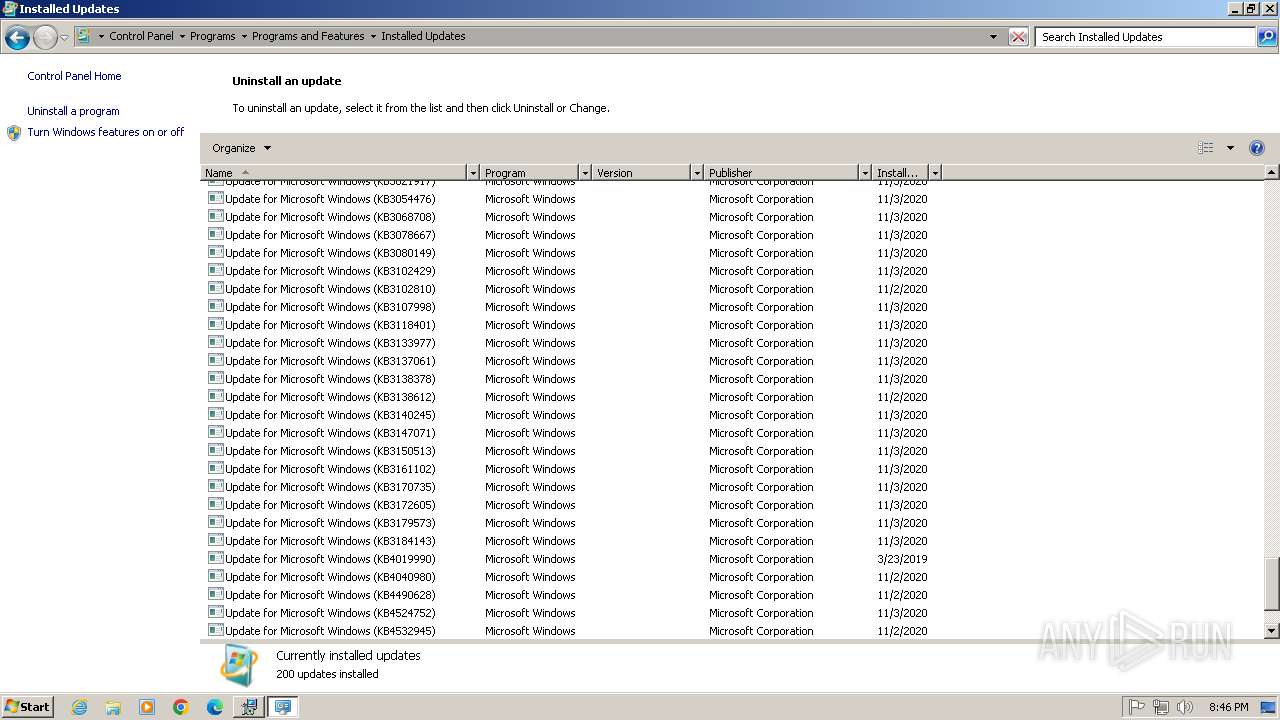
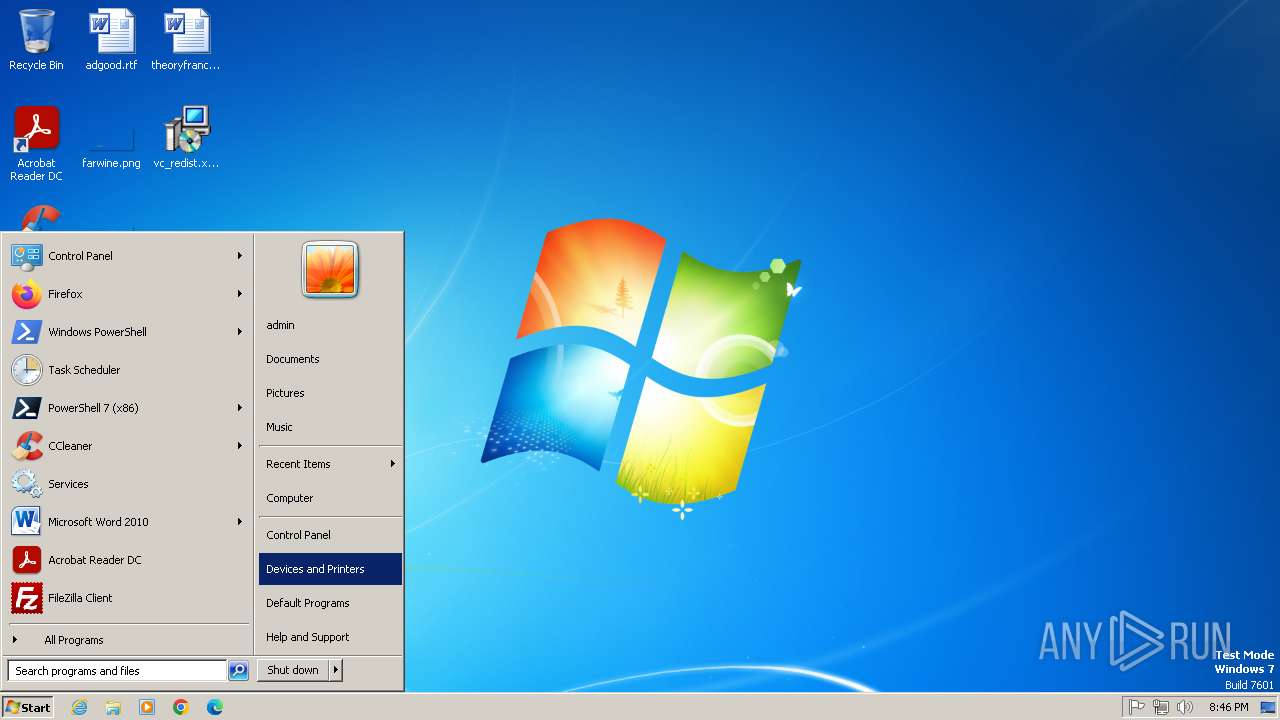
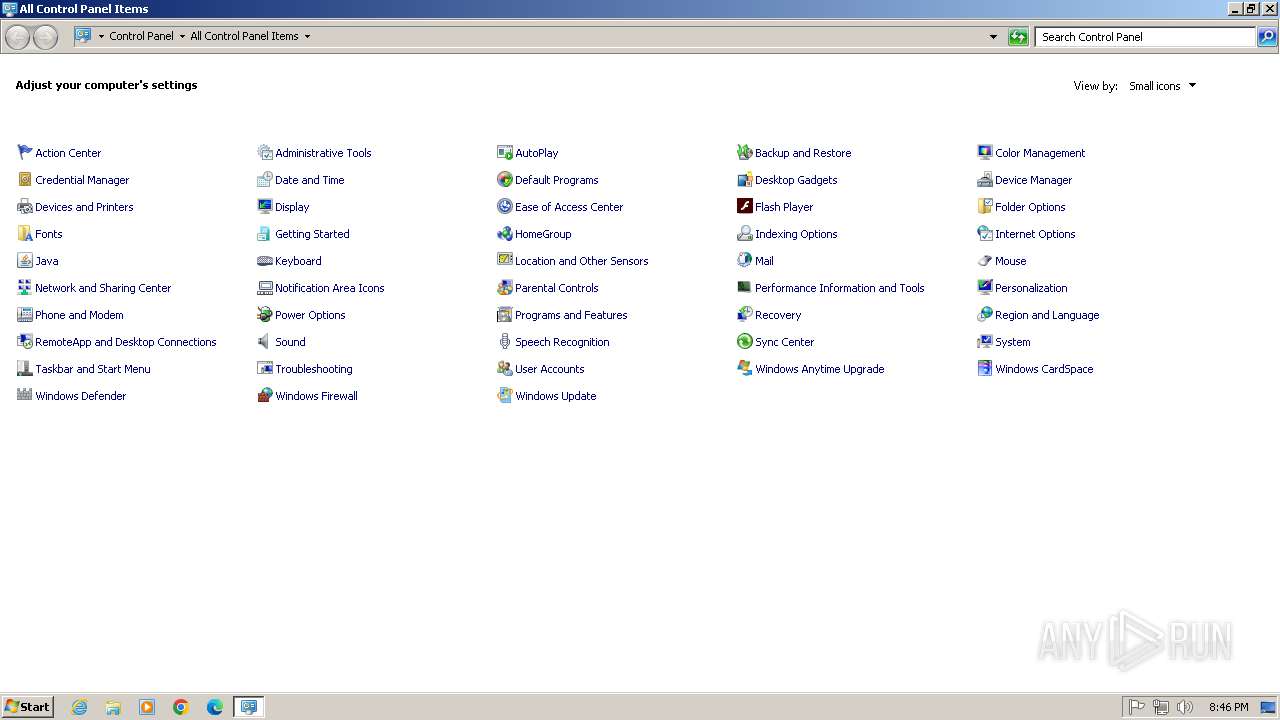
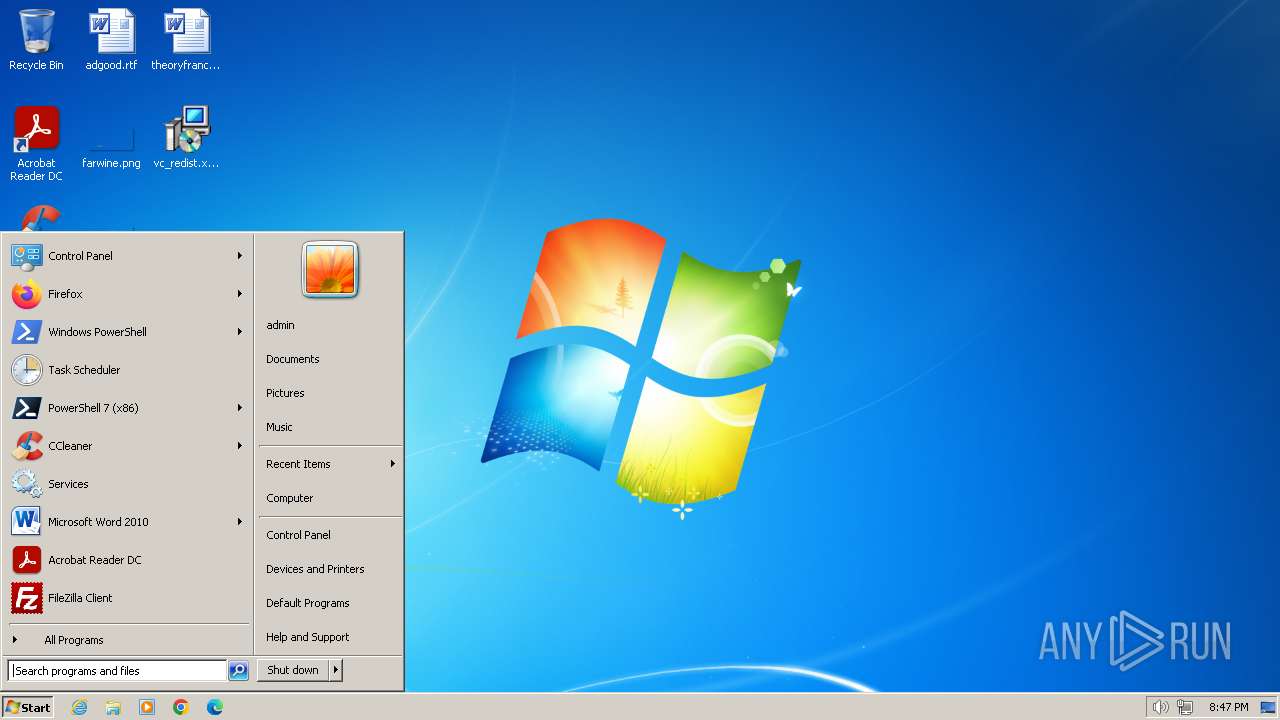
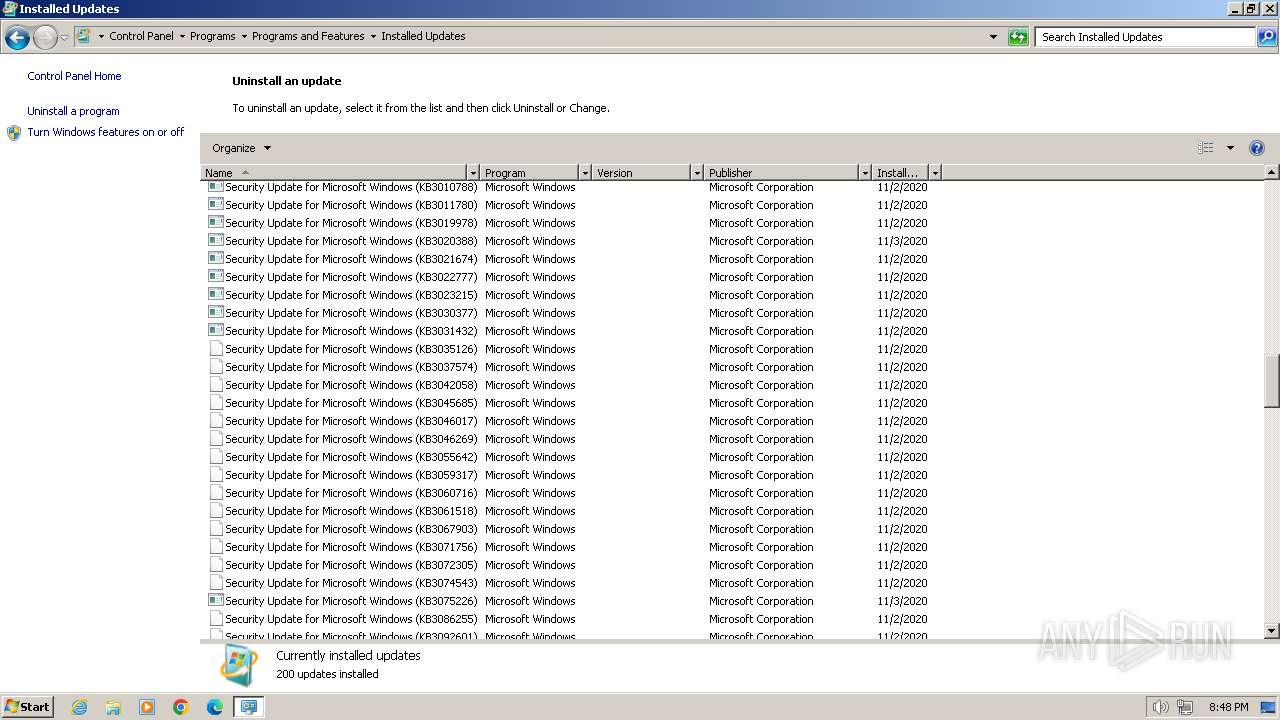
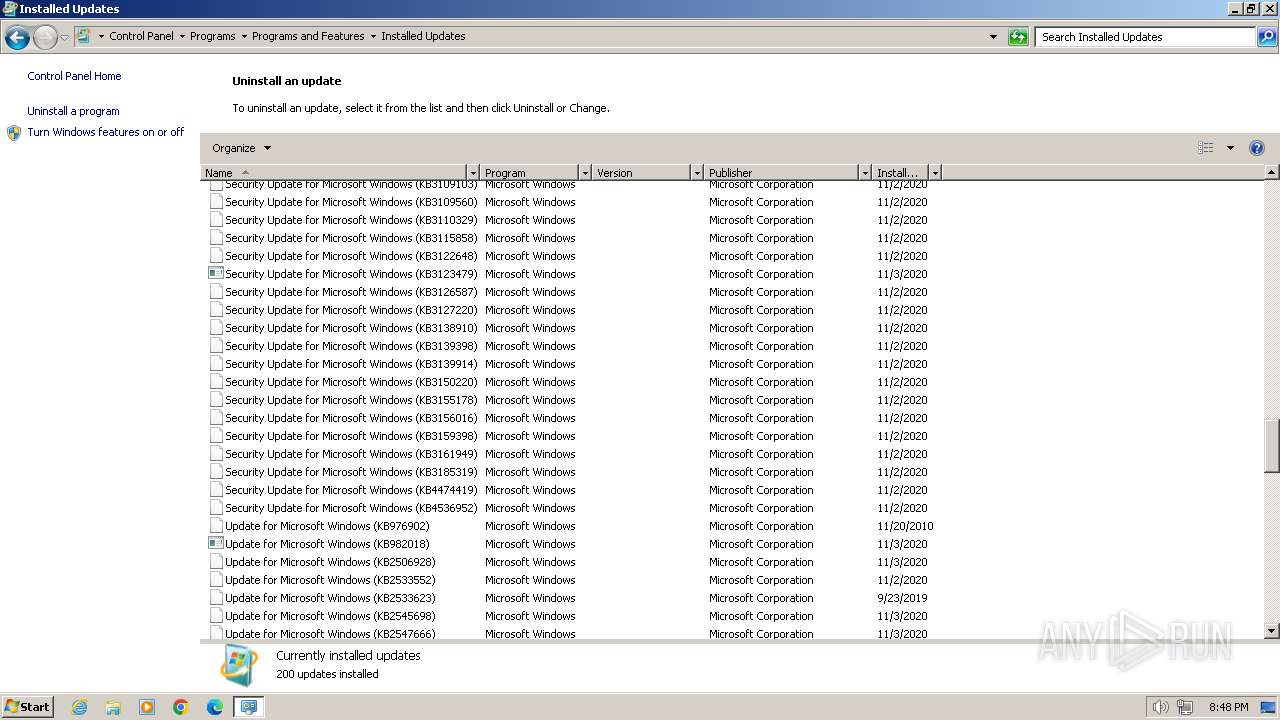
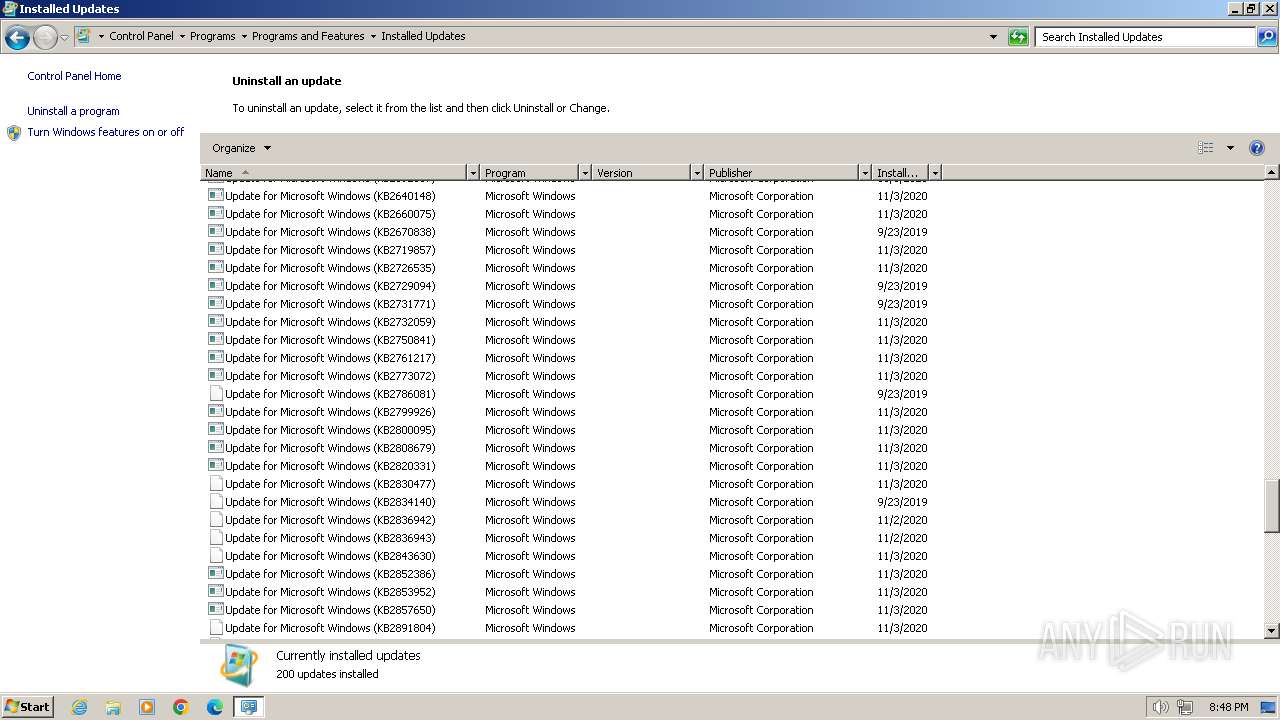
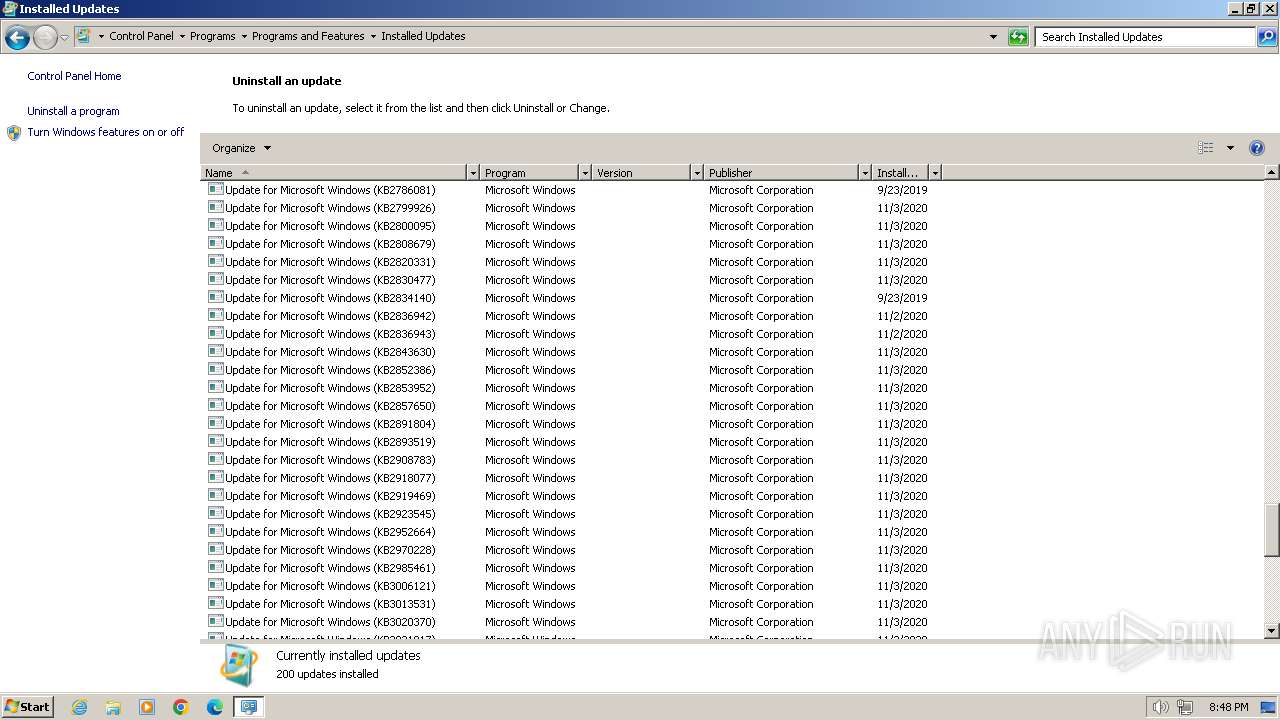
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 99F52708B06B9C695A8D64A44740BF08 |
| SHA1: | C2743FFC36D2AF40ADE0E370BE52D6B202874114 |
| SHA256: | 0C09F2611660441084CE0DF425C51C11E147E6447963C3690F97E0B25C55ED64 |
| SSDEEP: | 98304:I1svXJG6gIS6tHeVtWLPmZbbnTpwyfy8QAq38pOPdzMGqoXlF0cgl95rQXcA3RGr:j8+enNsqQ3pC/Ex9bb4 |
MALICIOUS
Changes the autorun value in the registry
- VC_redist.x86.exe (PID: 3752)
SUSPICIOUS
Starts a Microsoft application from unusual location
- vc_redist.x86.exe (PID: 848)
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 3752)
Process drops legitimate windows executable
- vc_redist.x86.exe (PID: 848)
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 3752)
- msiexec.exe (PID: 3868)
- VC_redist.x86.exe (PID: 3024)
Executable content was dropped or overwritten
- vc_redist.x86.exe (PID: 848)
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 3752)
- VC_redist.x86.exe (PID: 2208)
- VC_redist.x86.exe (PID: 3024)
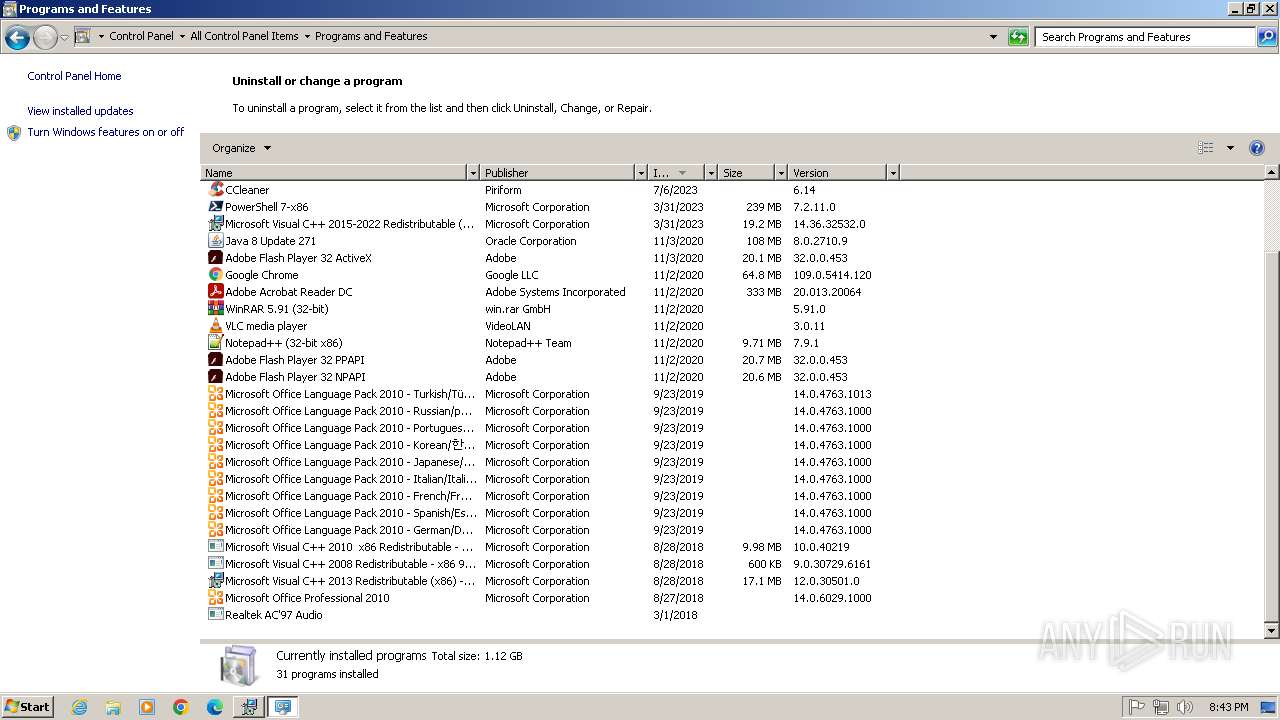
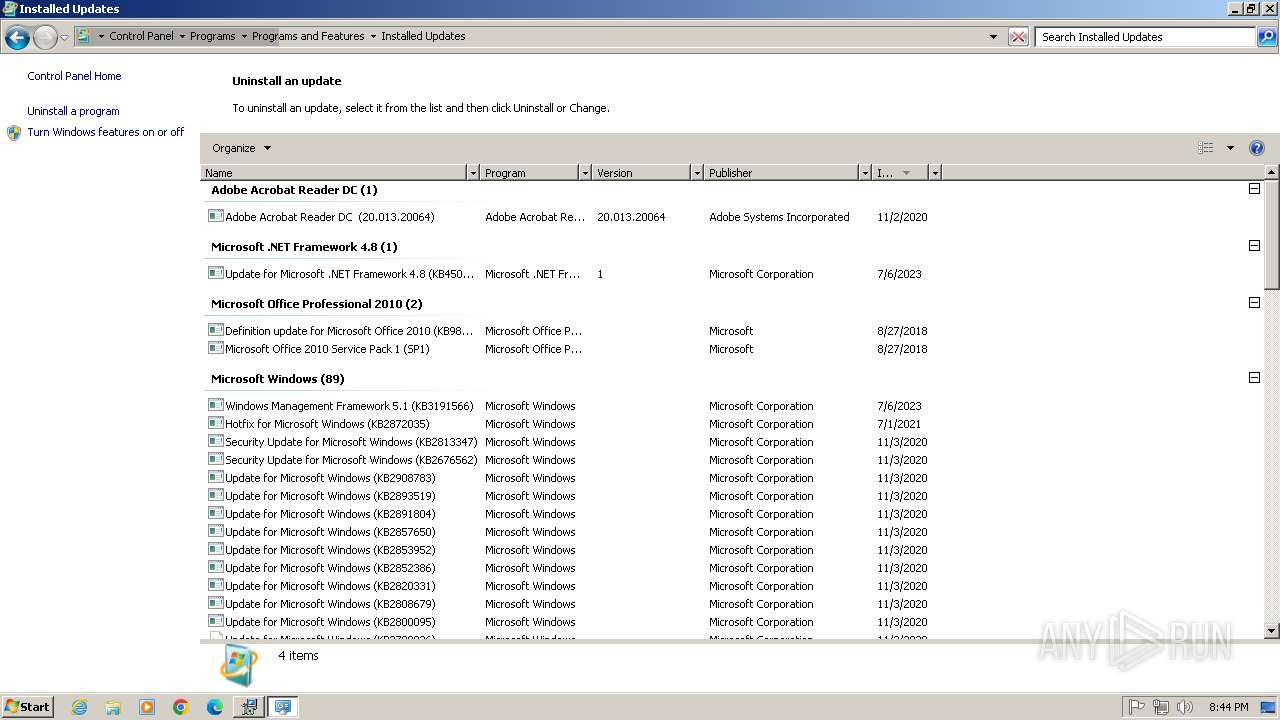
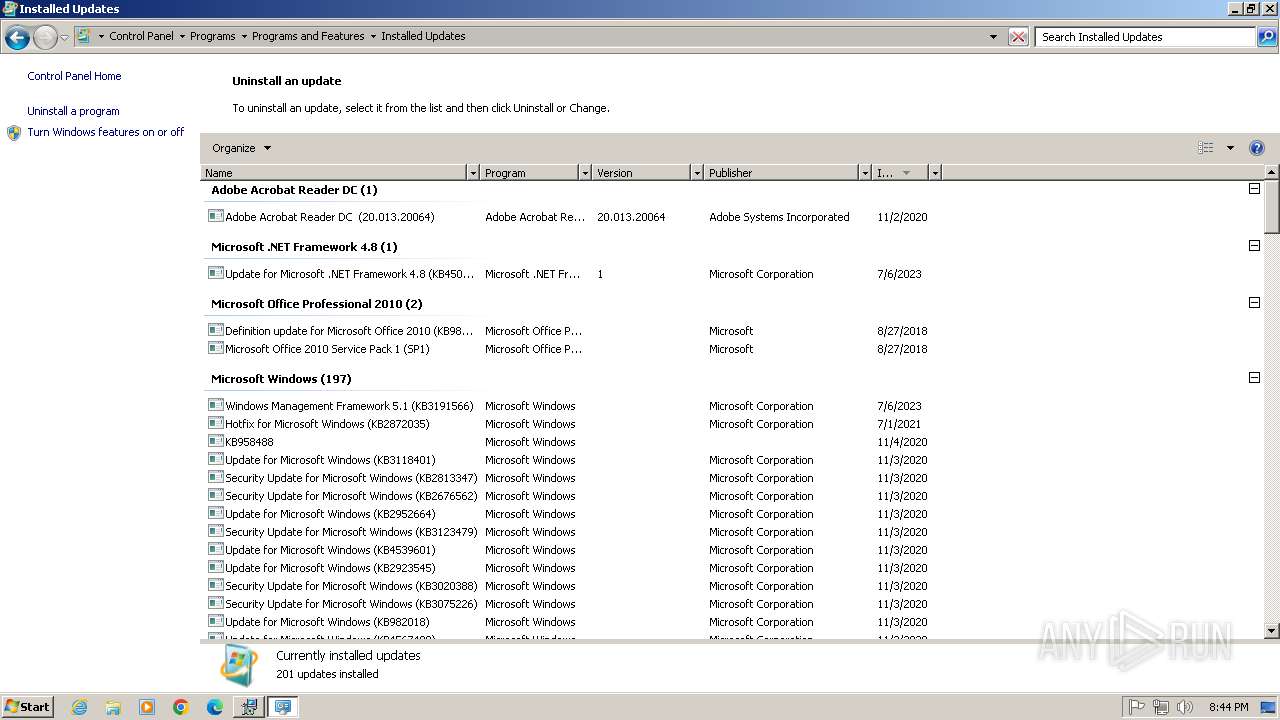
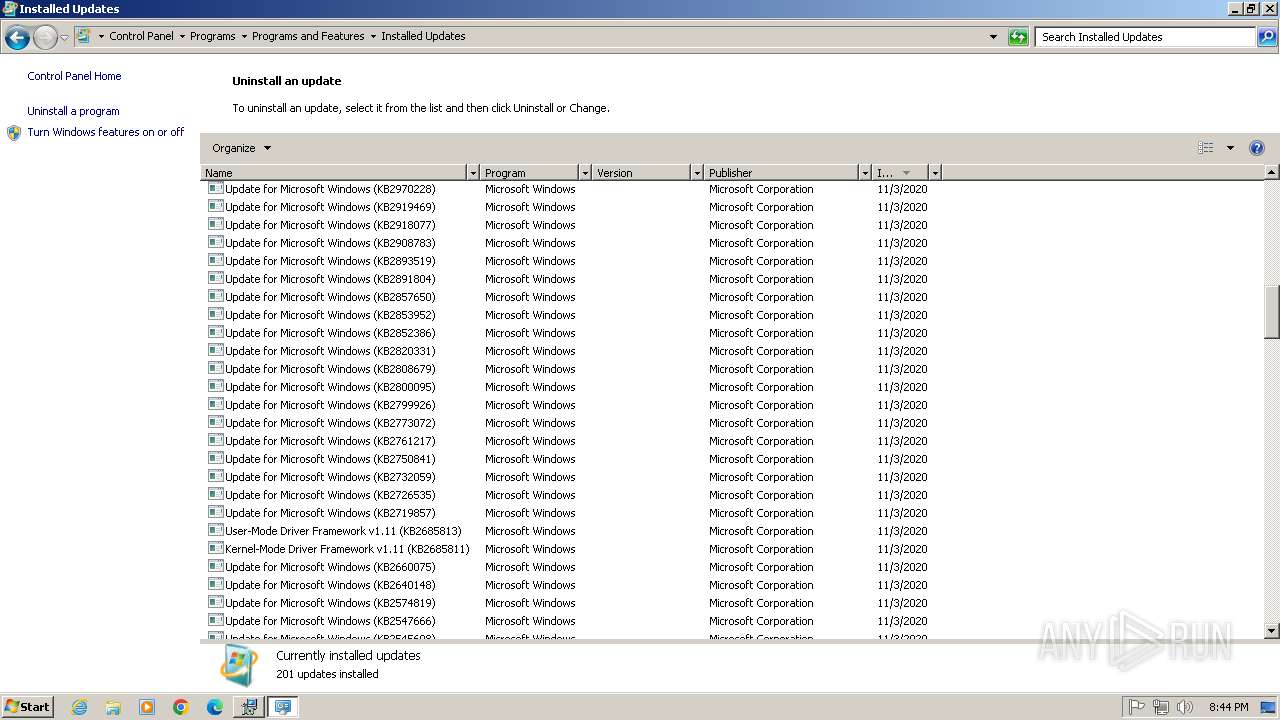
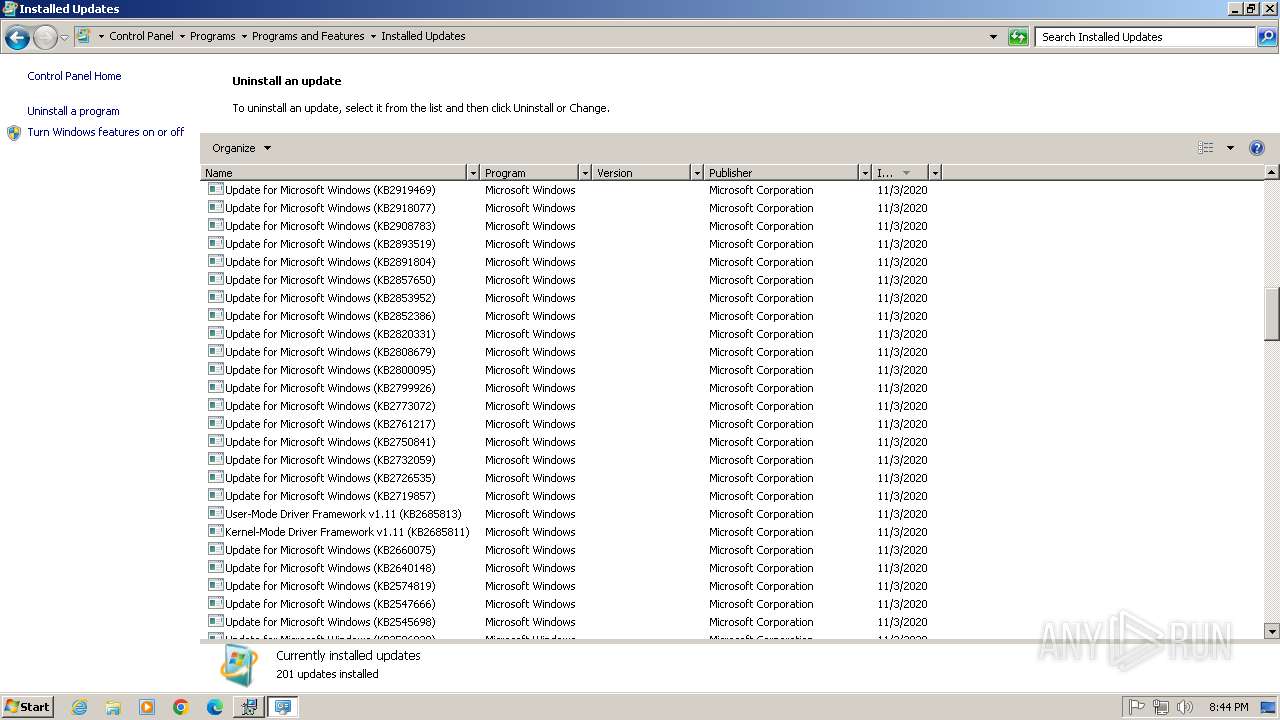
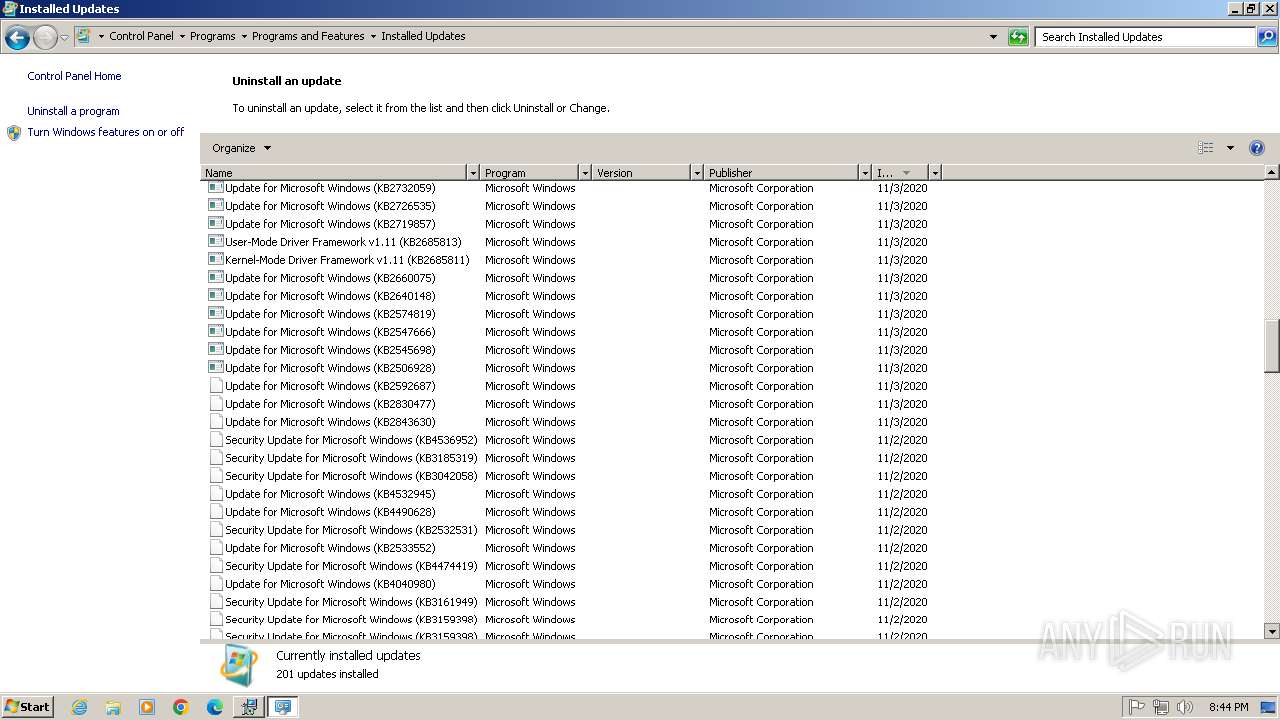
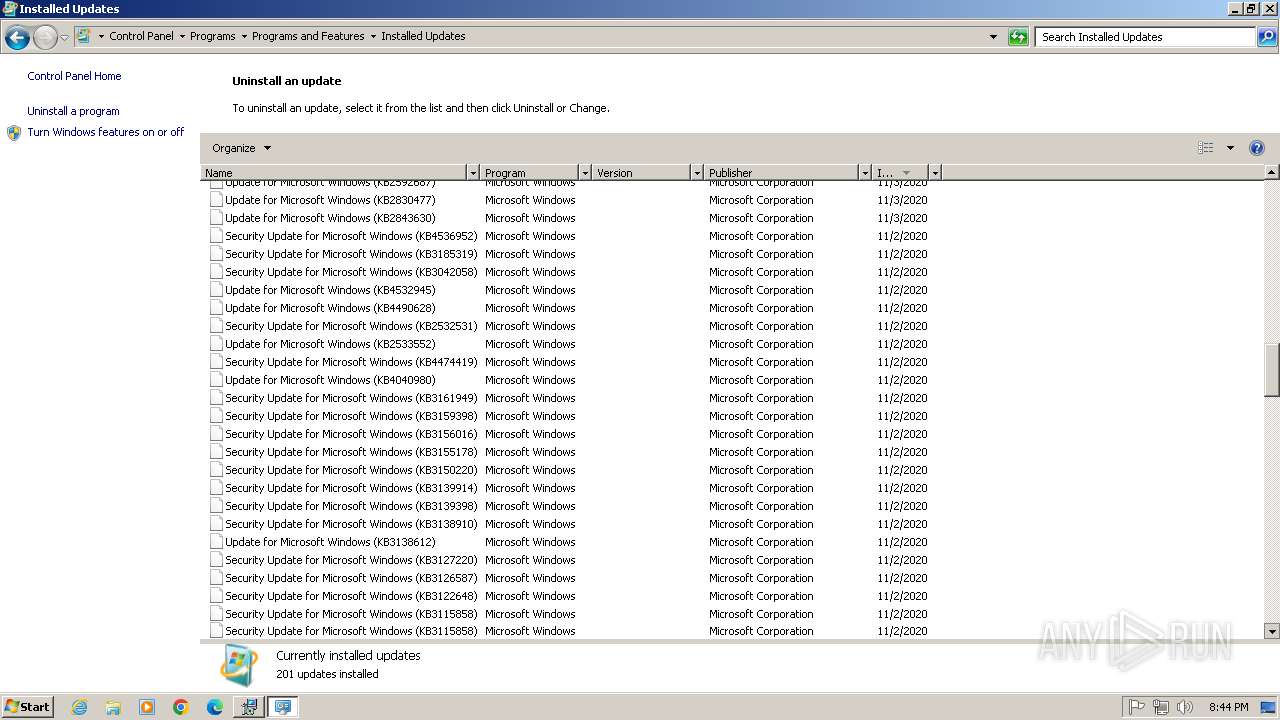
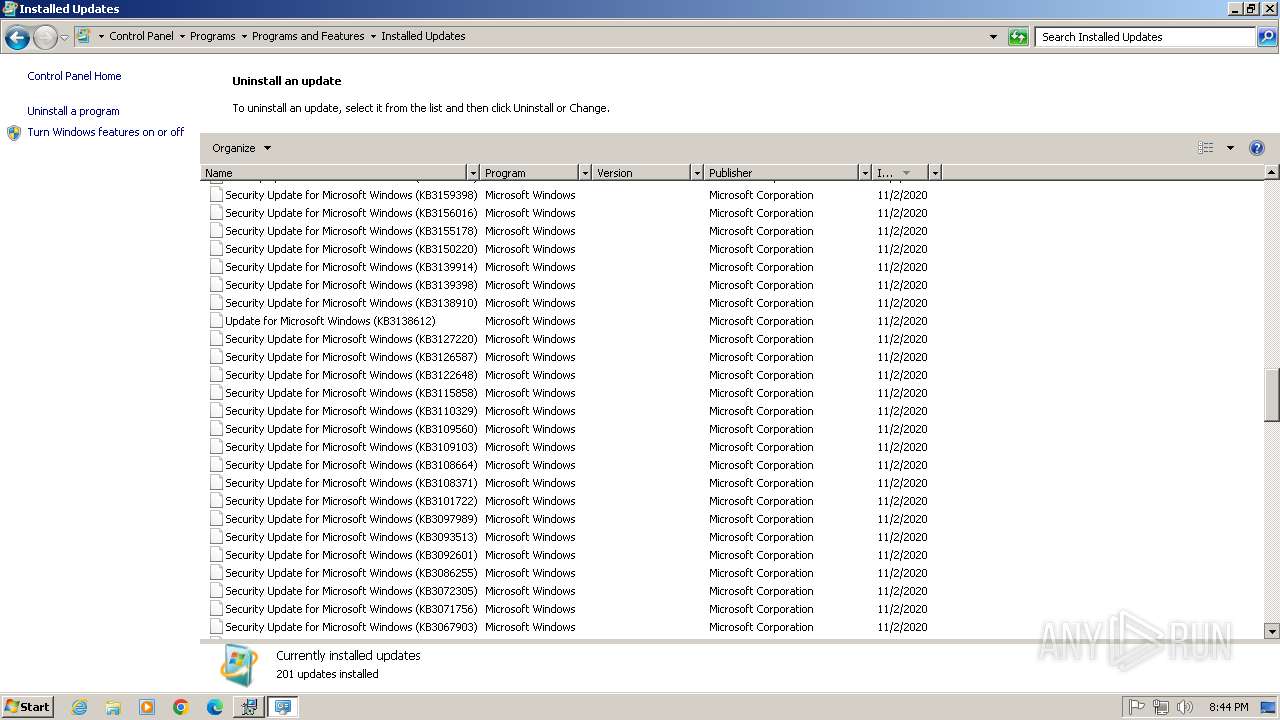
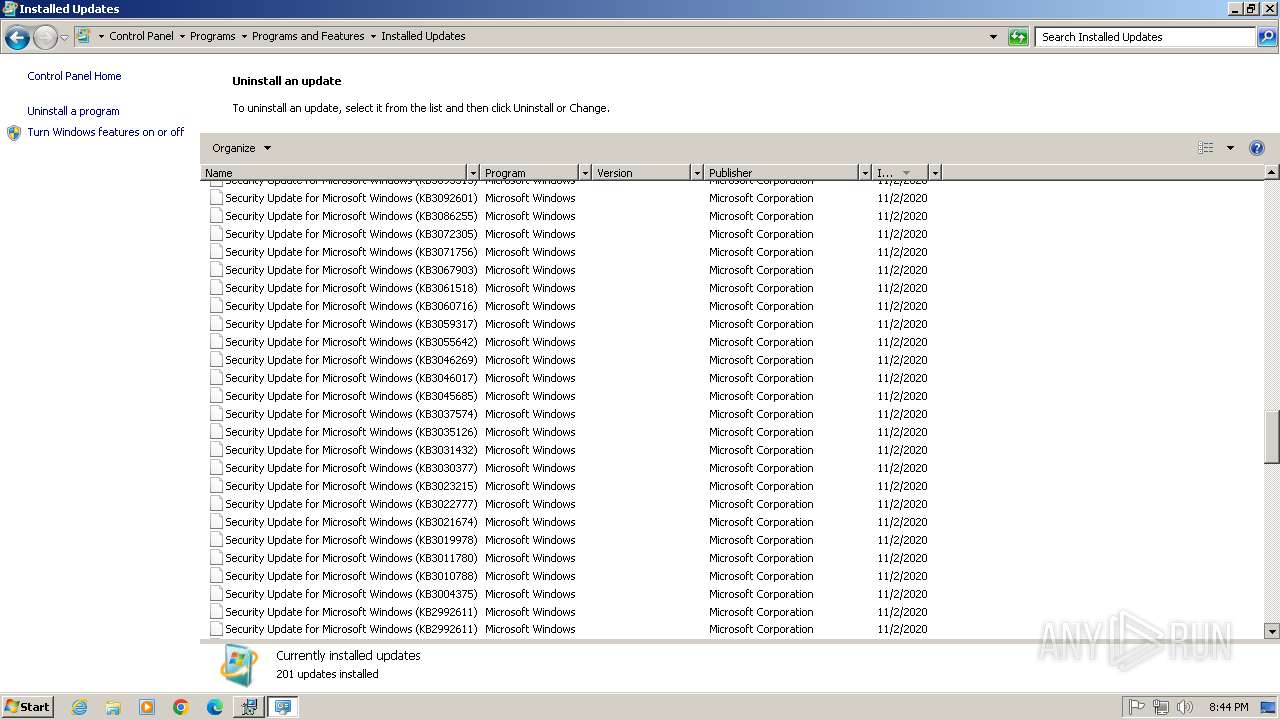
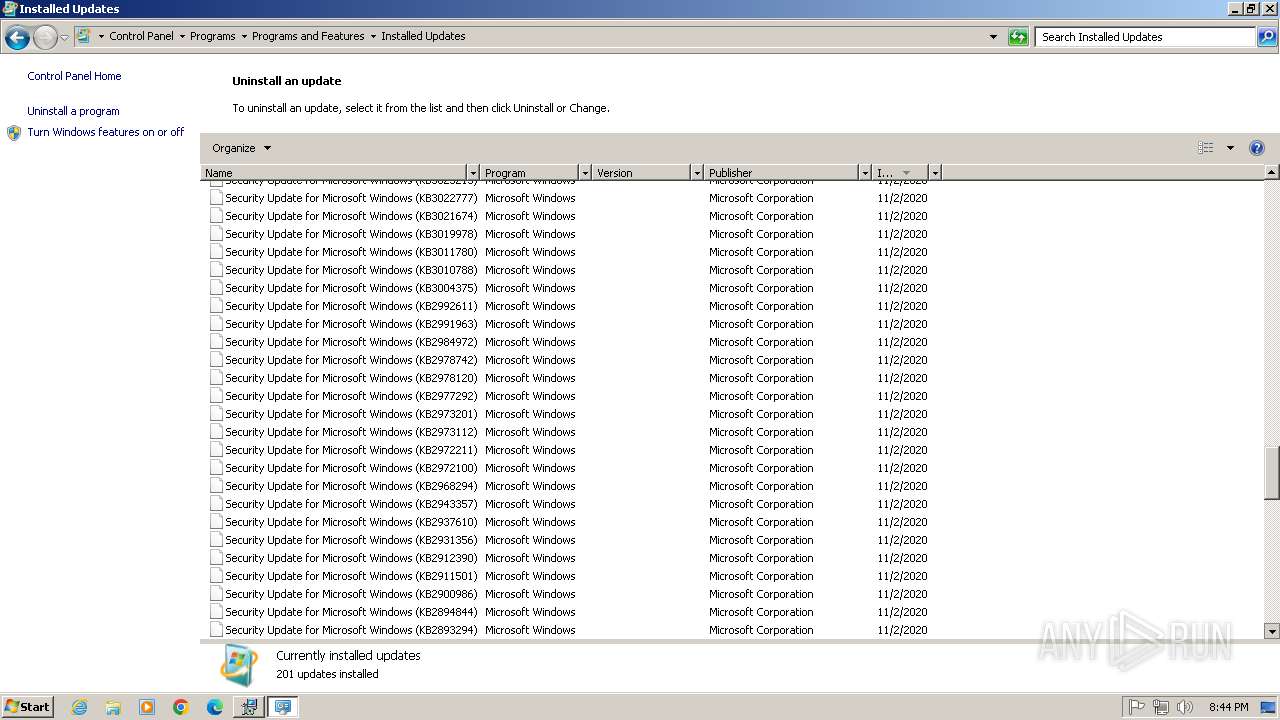
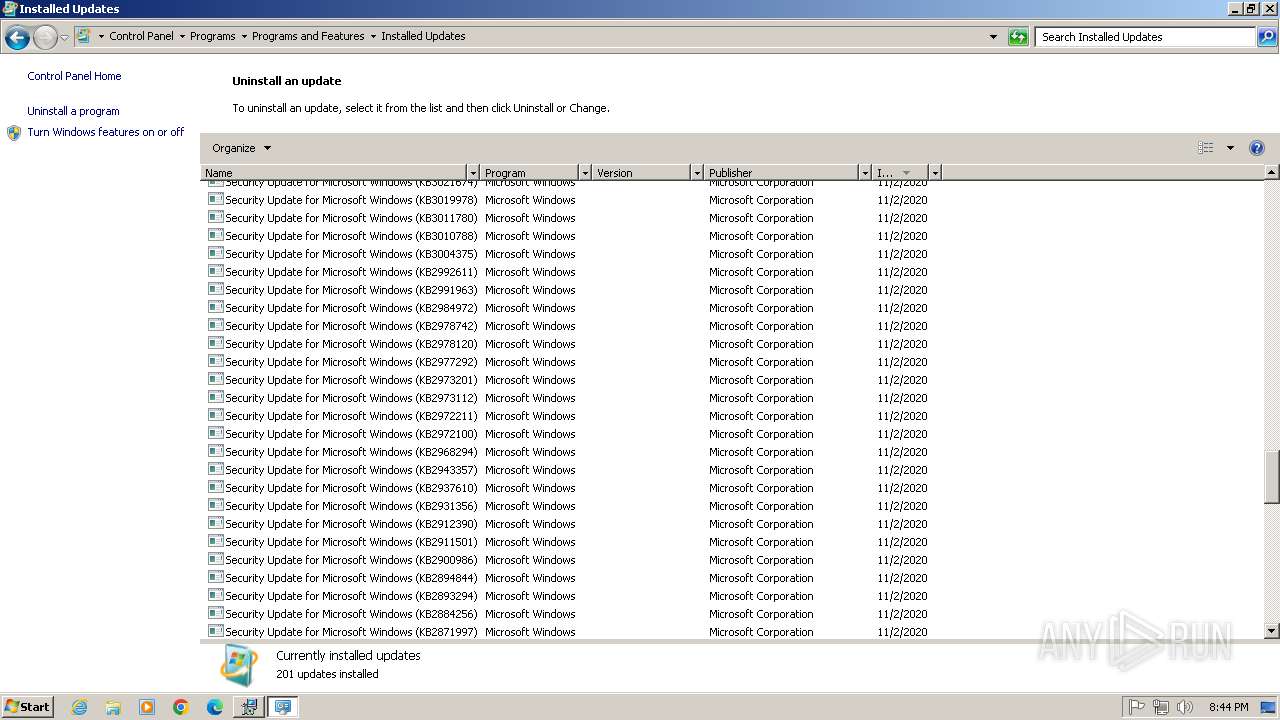
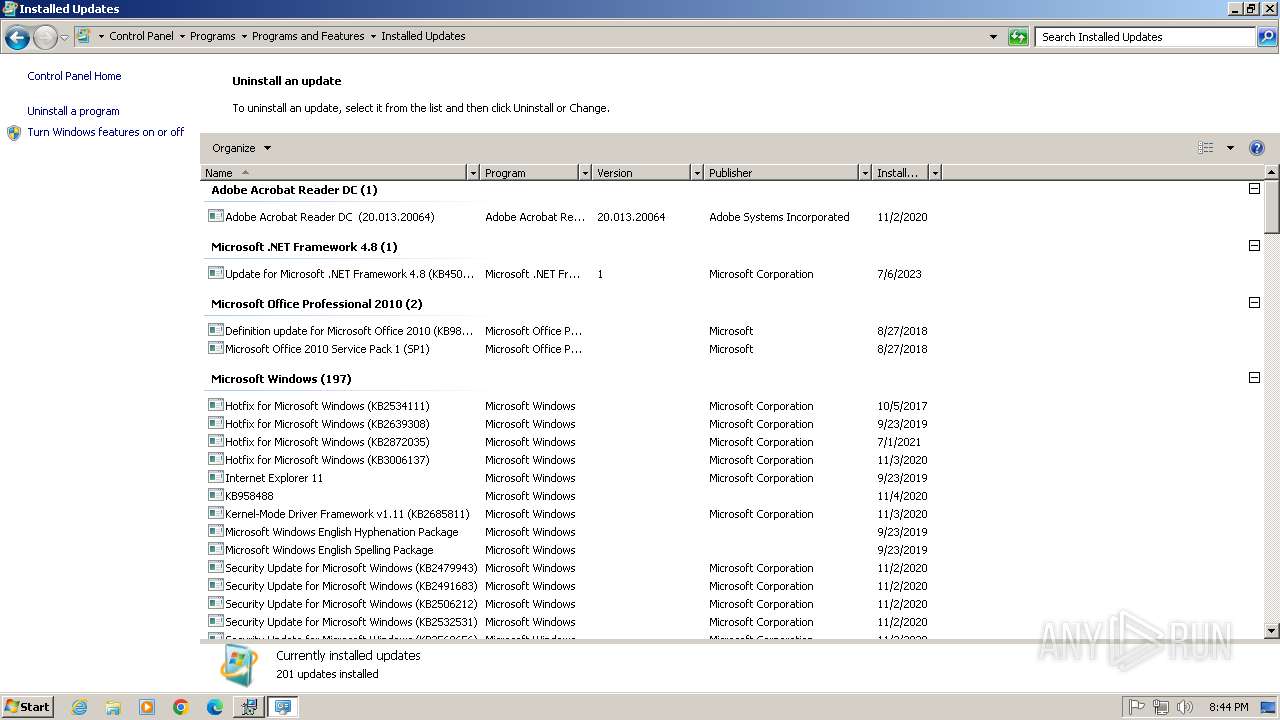
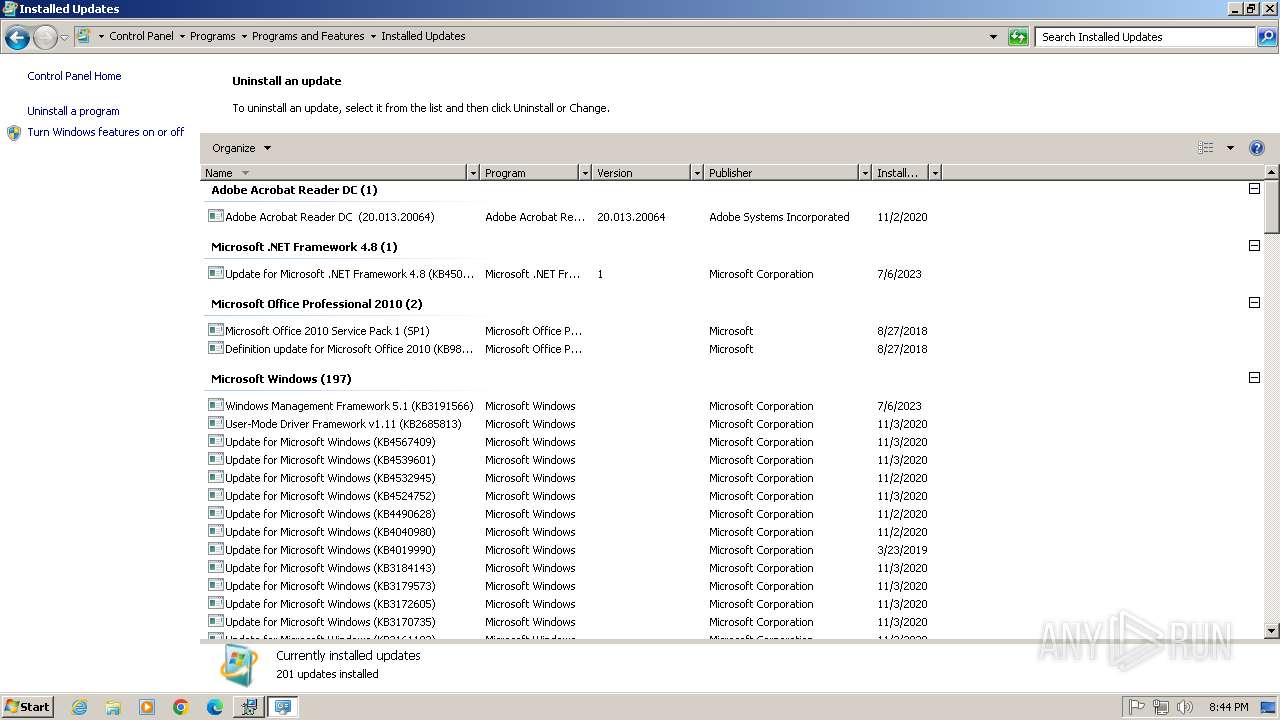
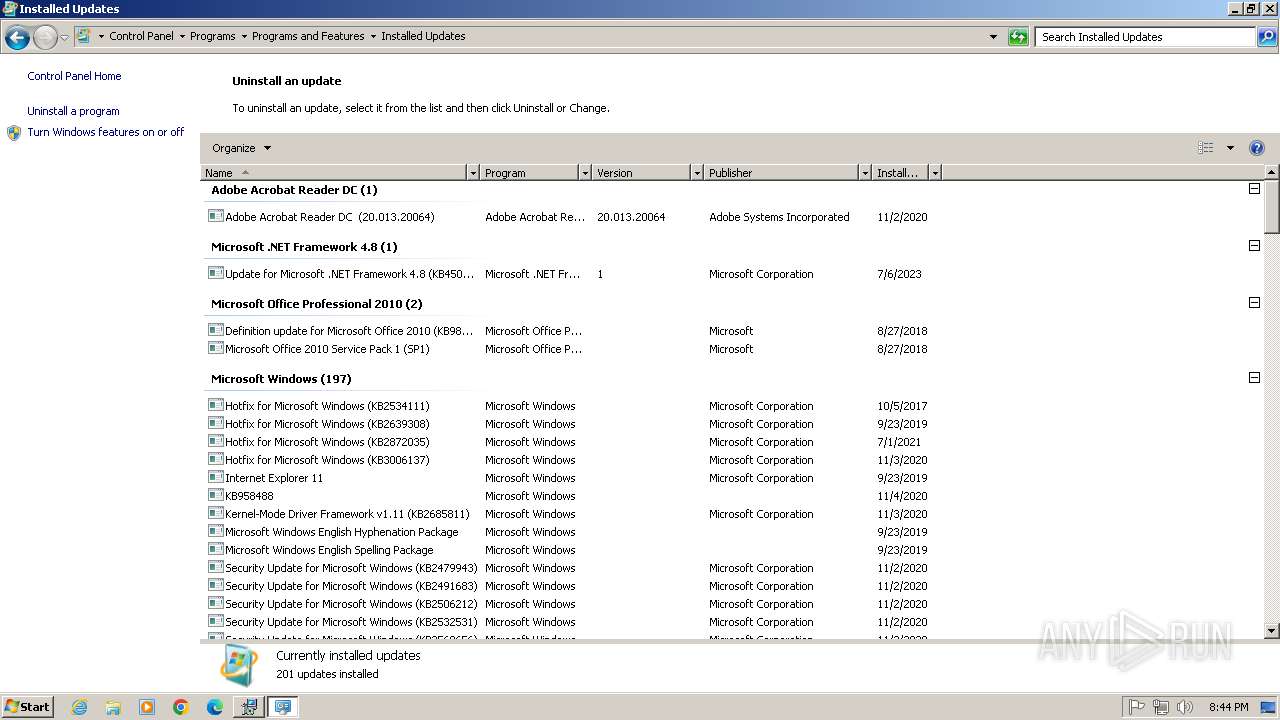
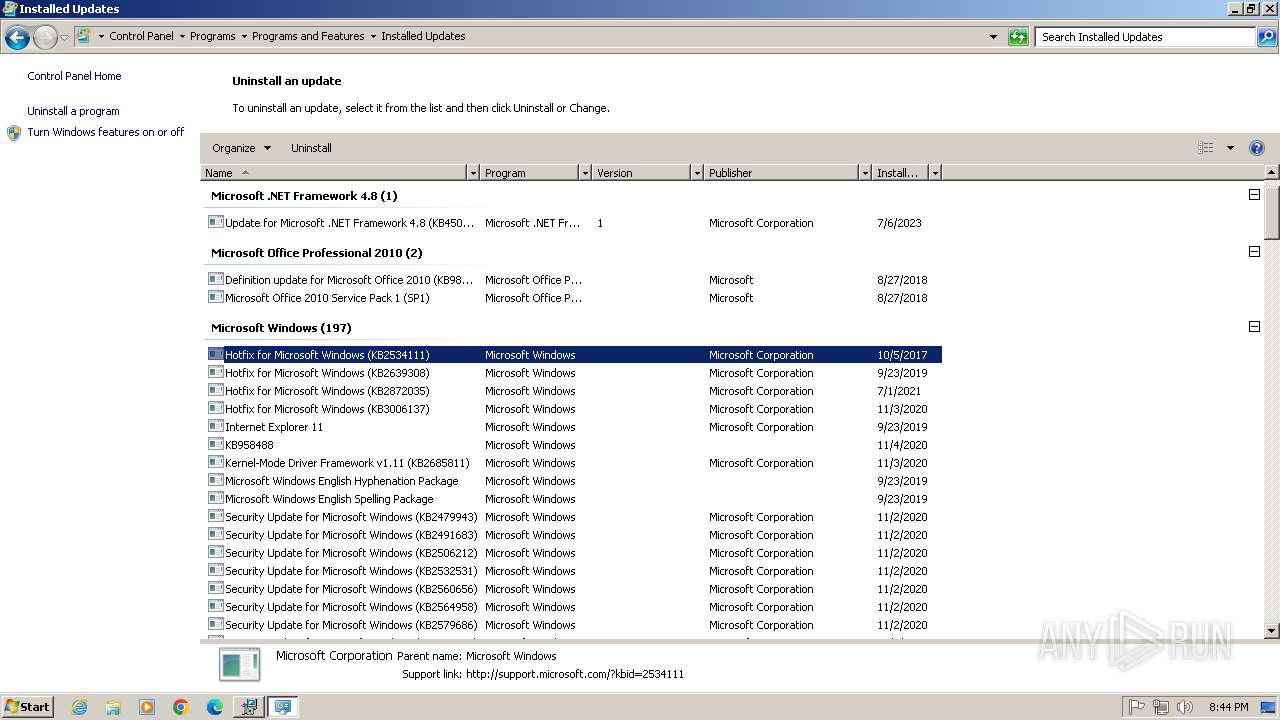
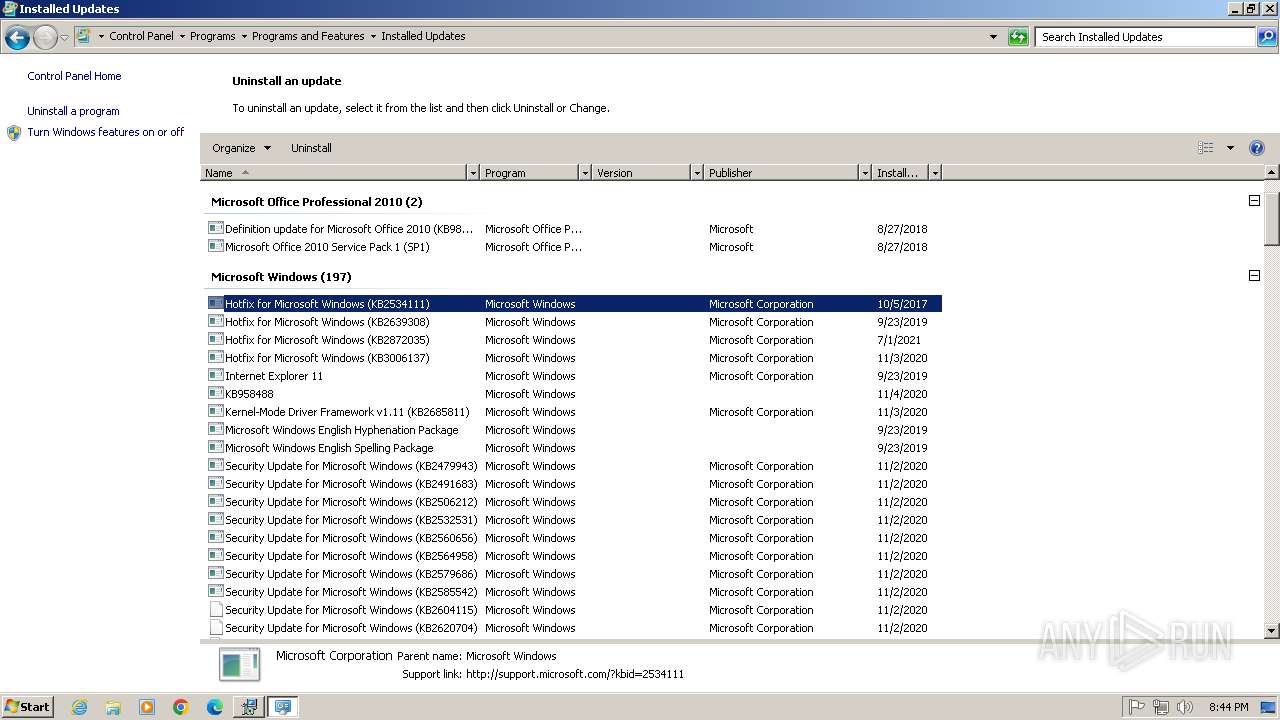
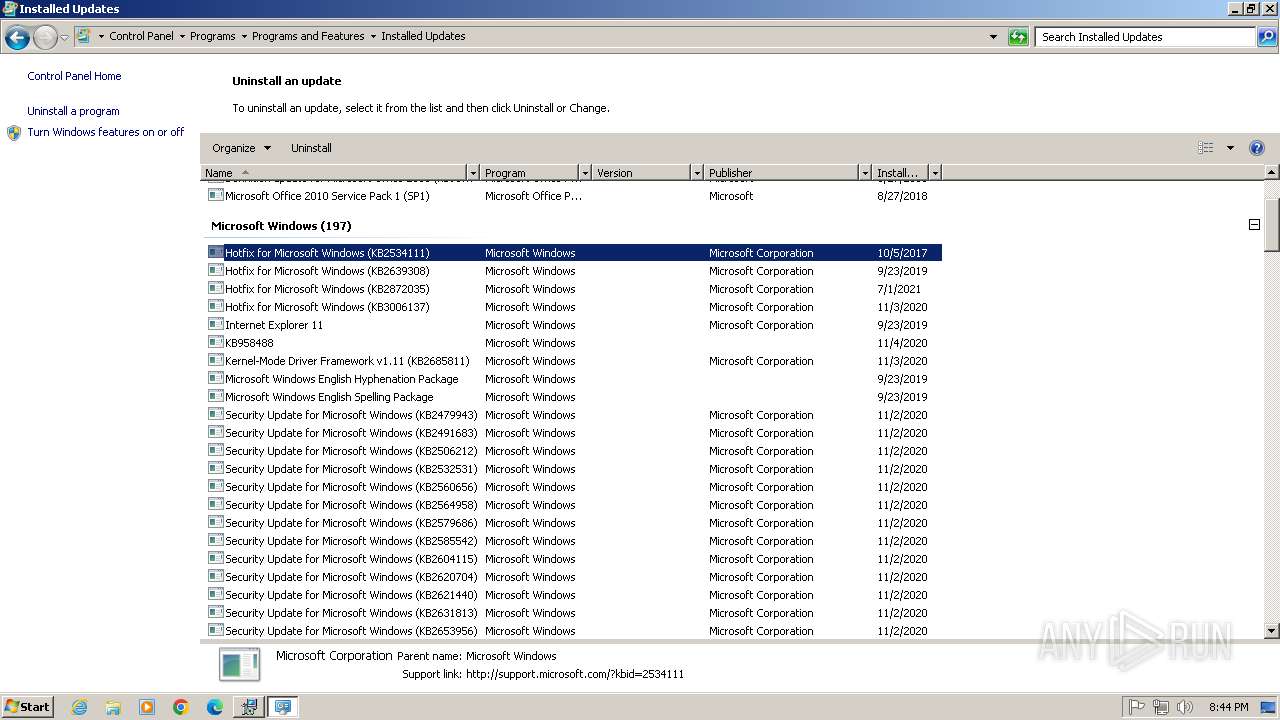
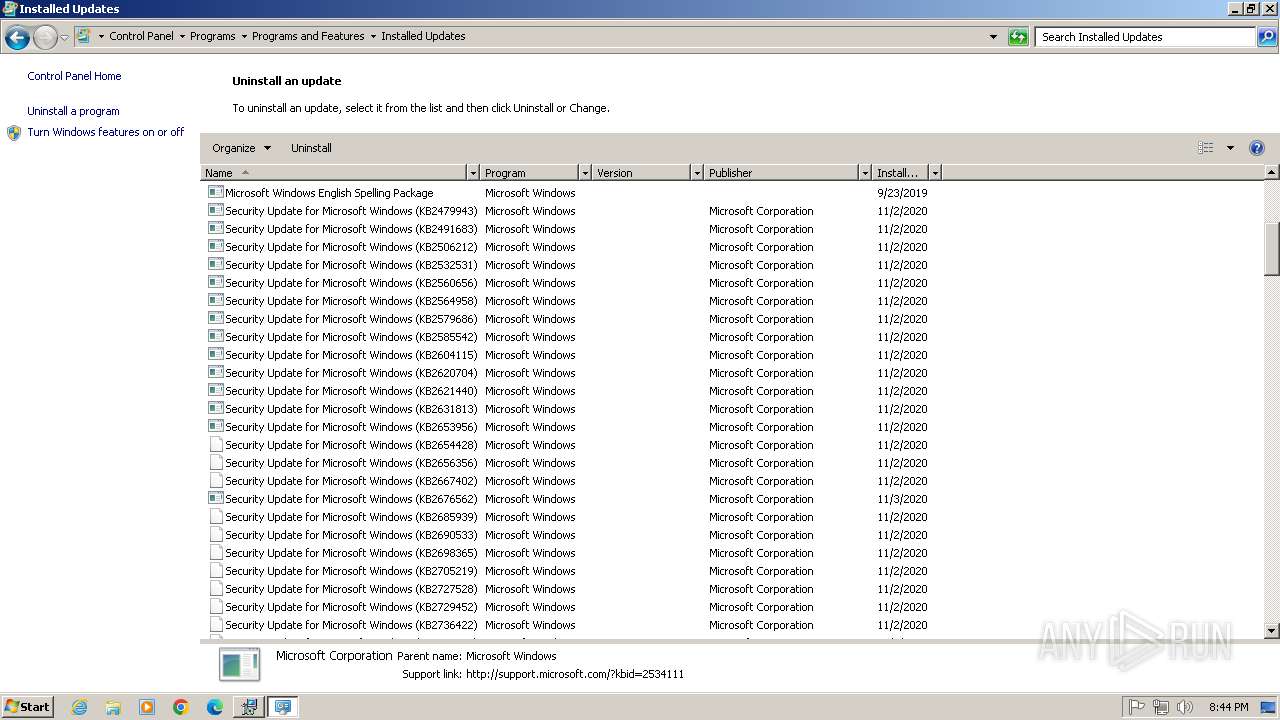
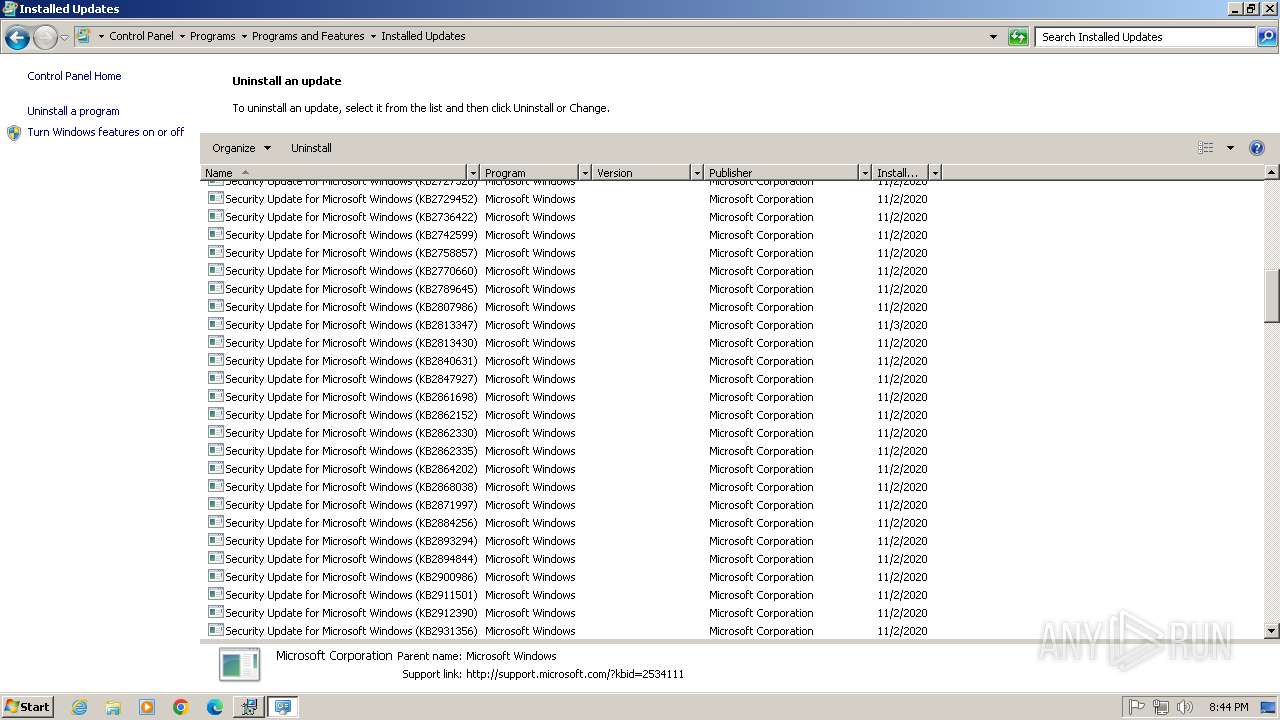
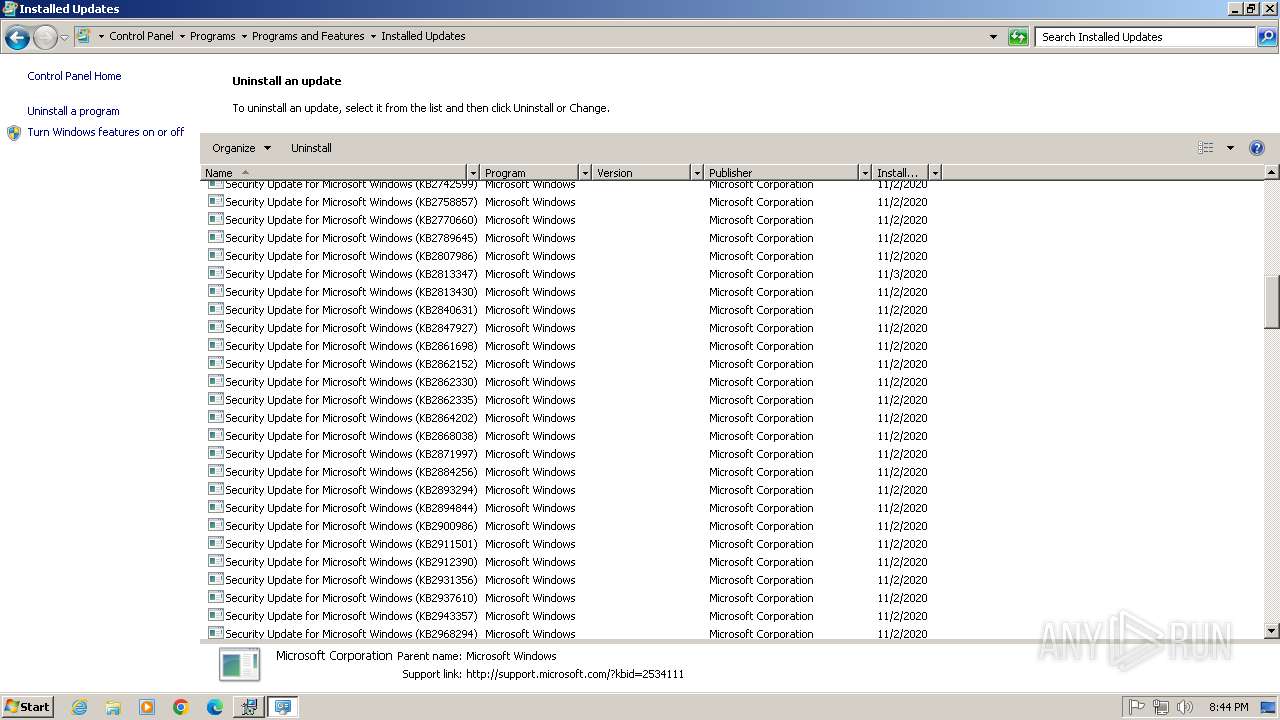
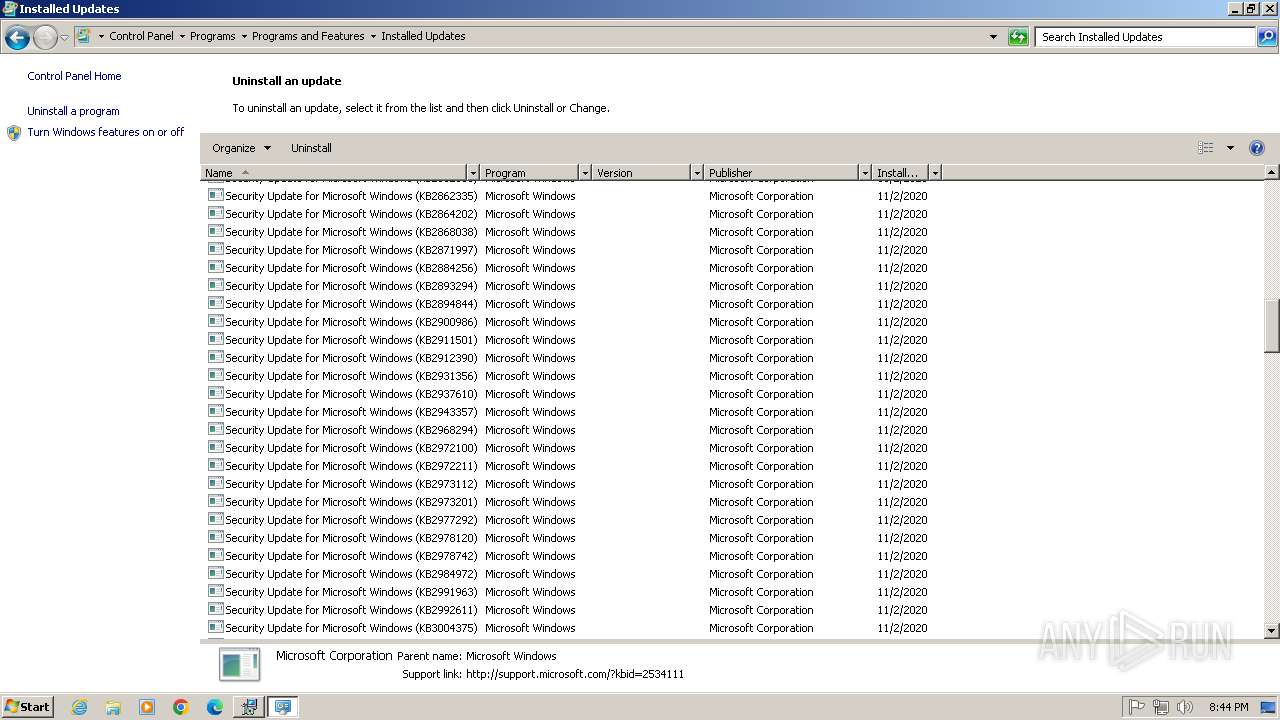
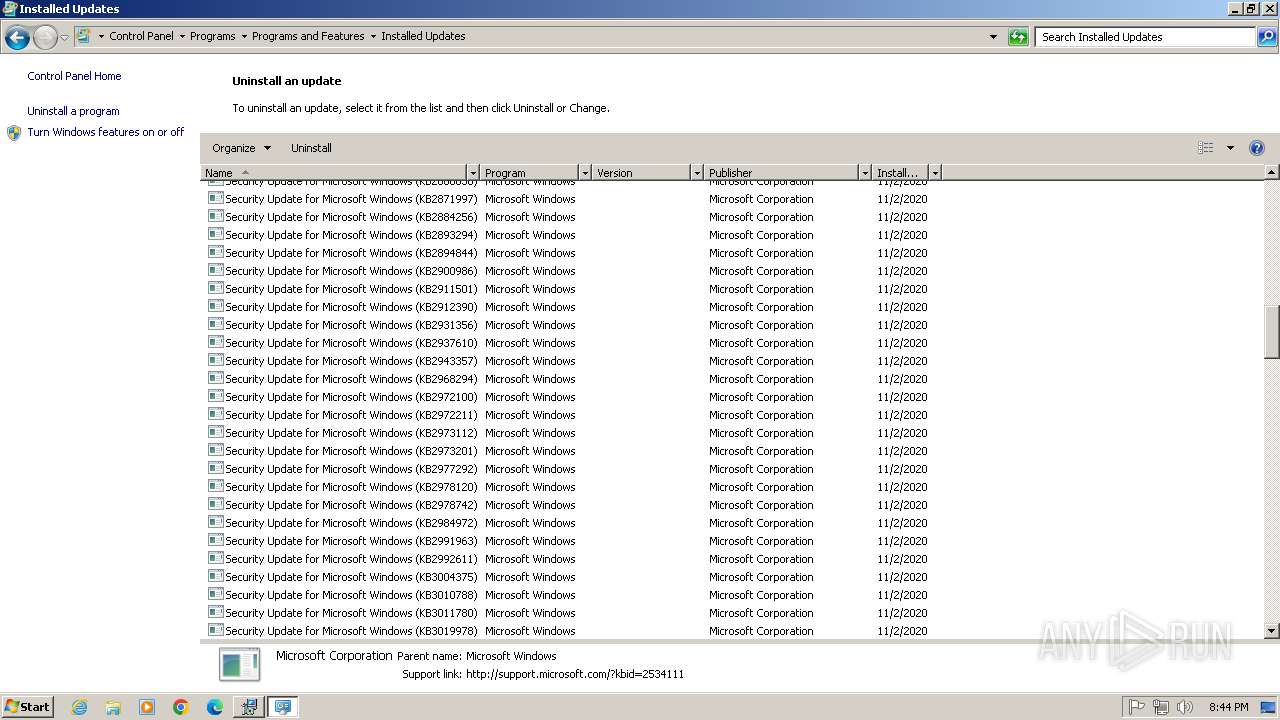
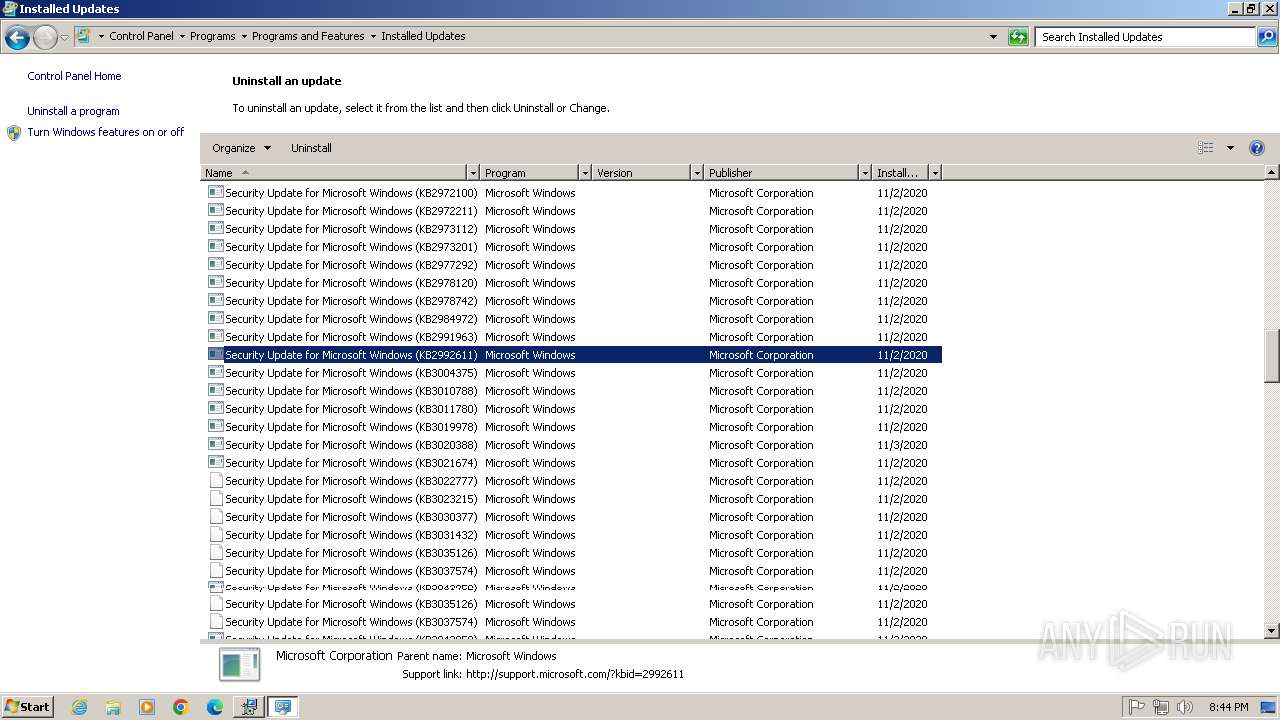
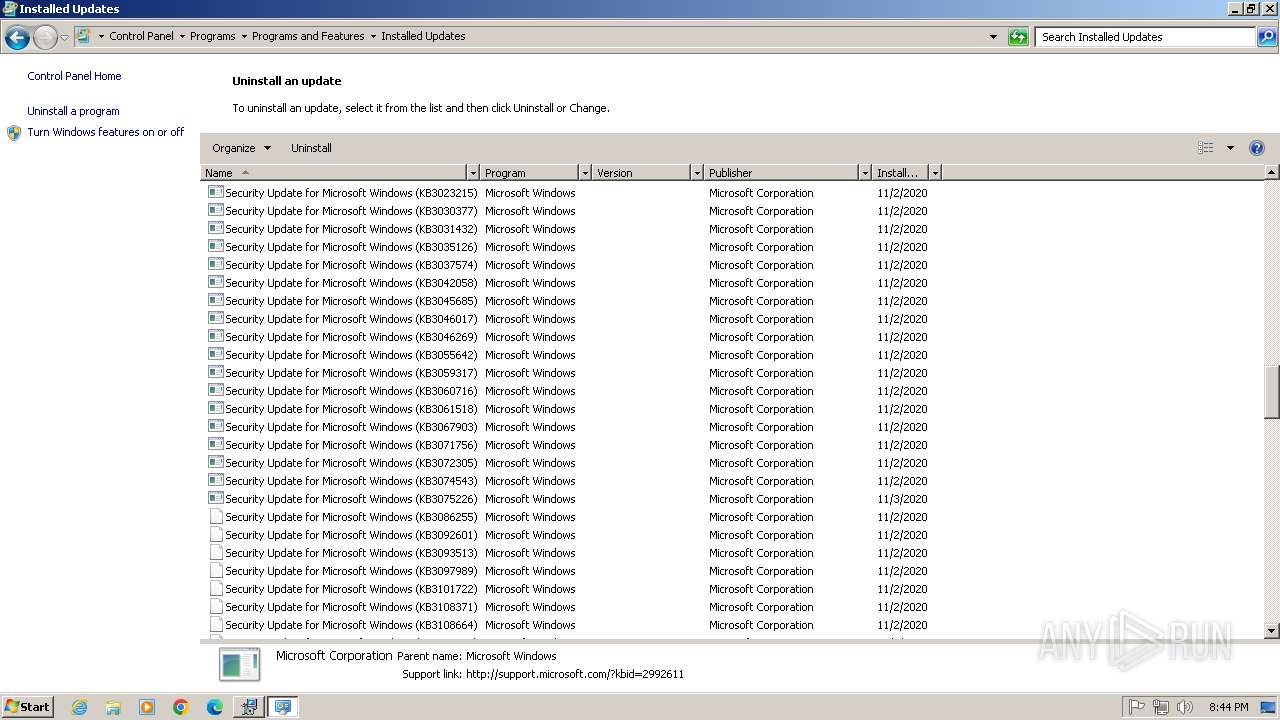
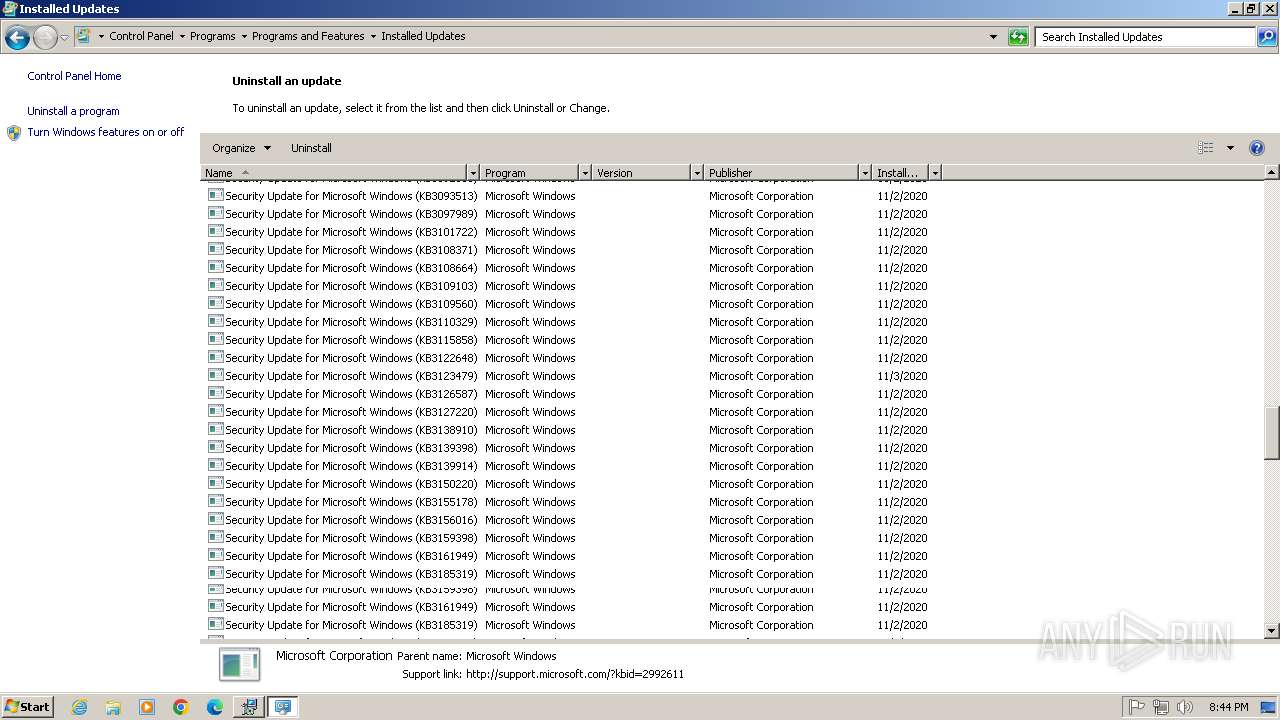
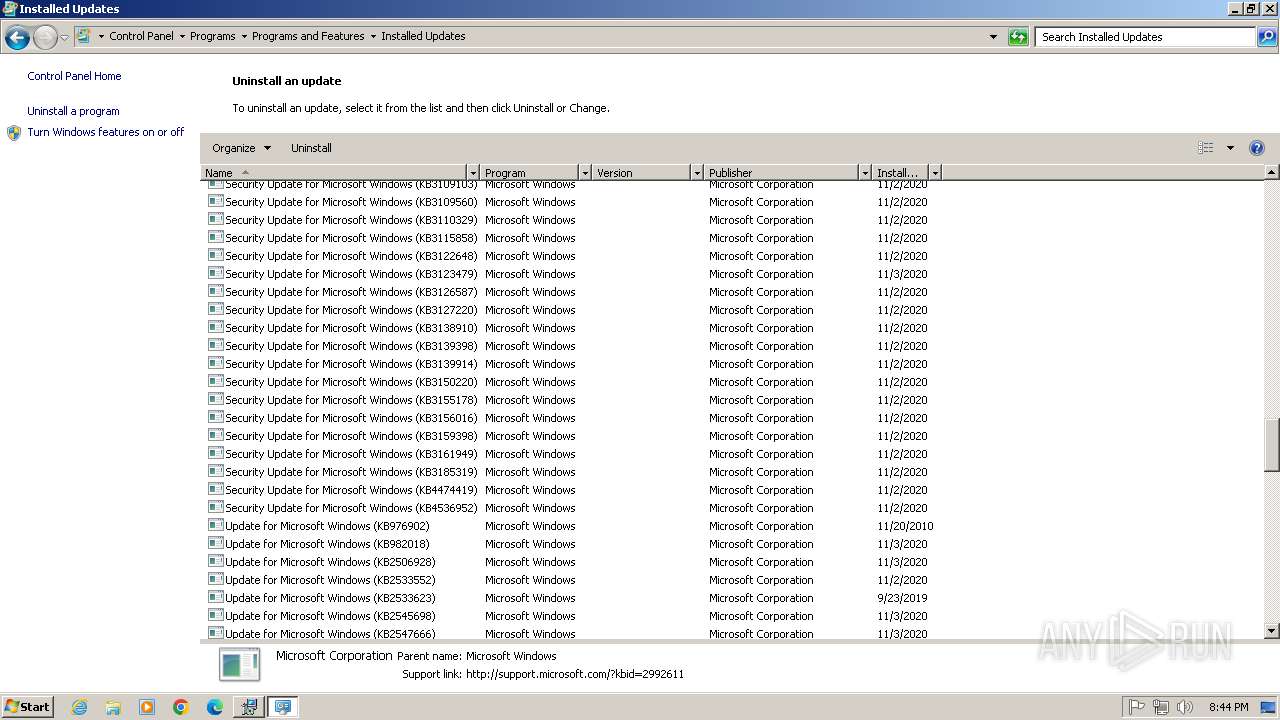
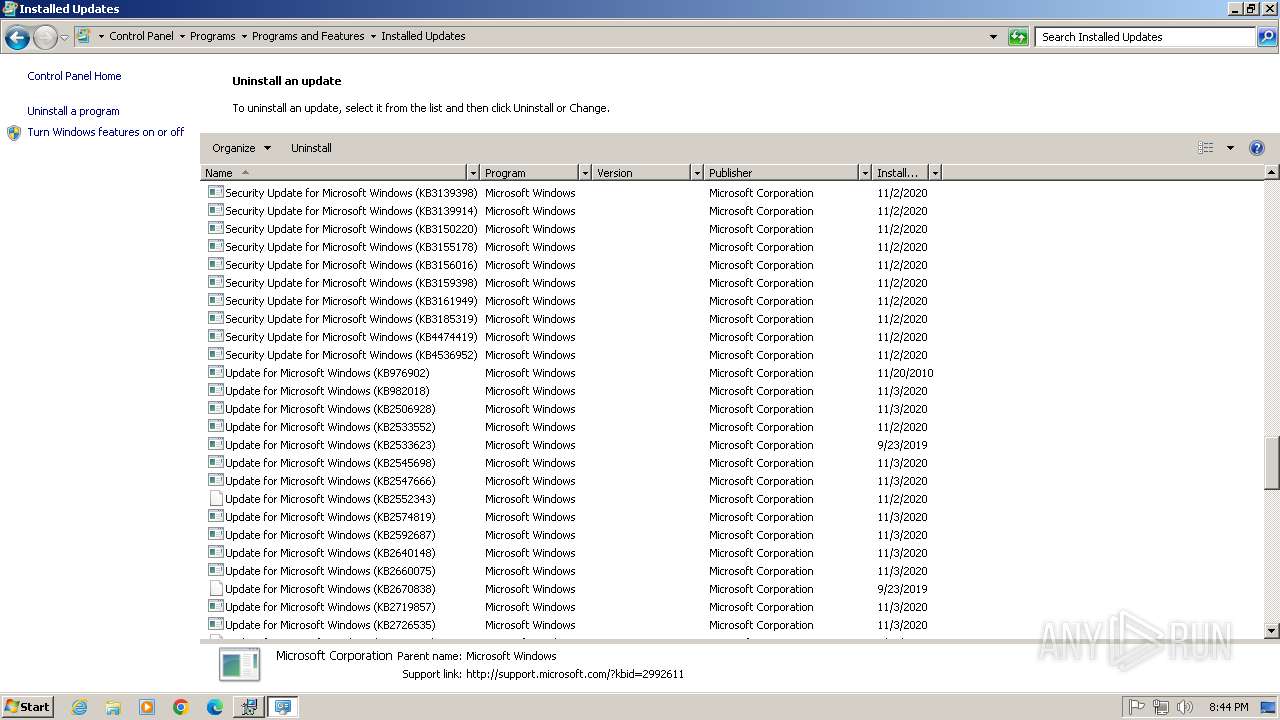
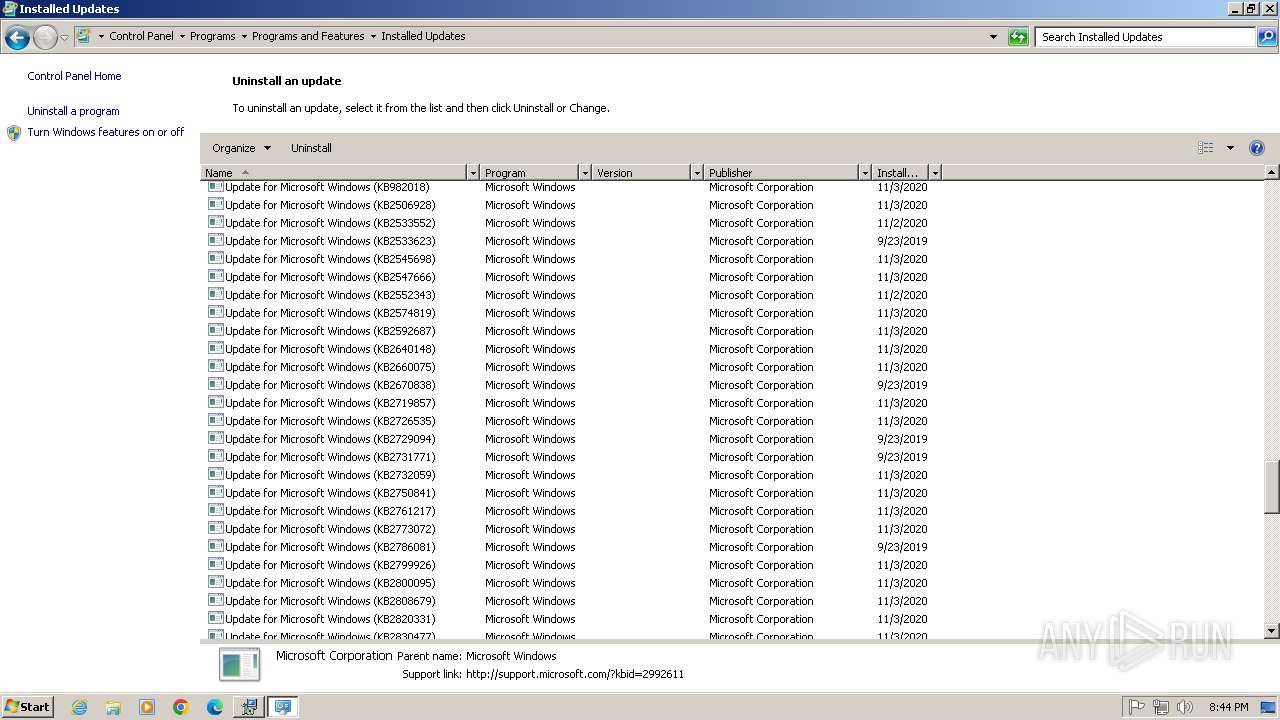
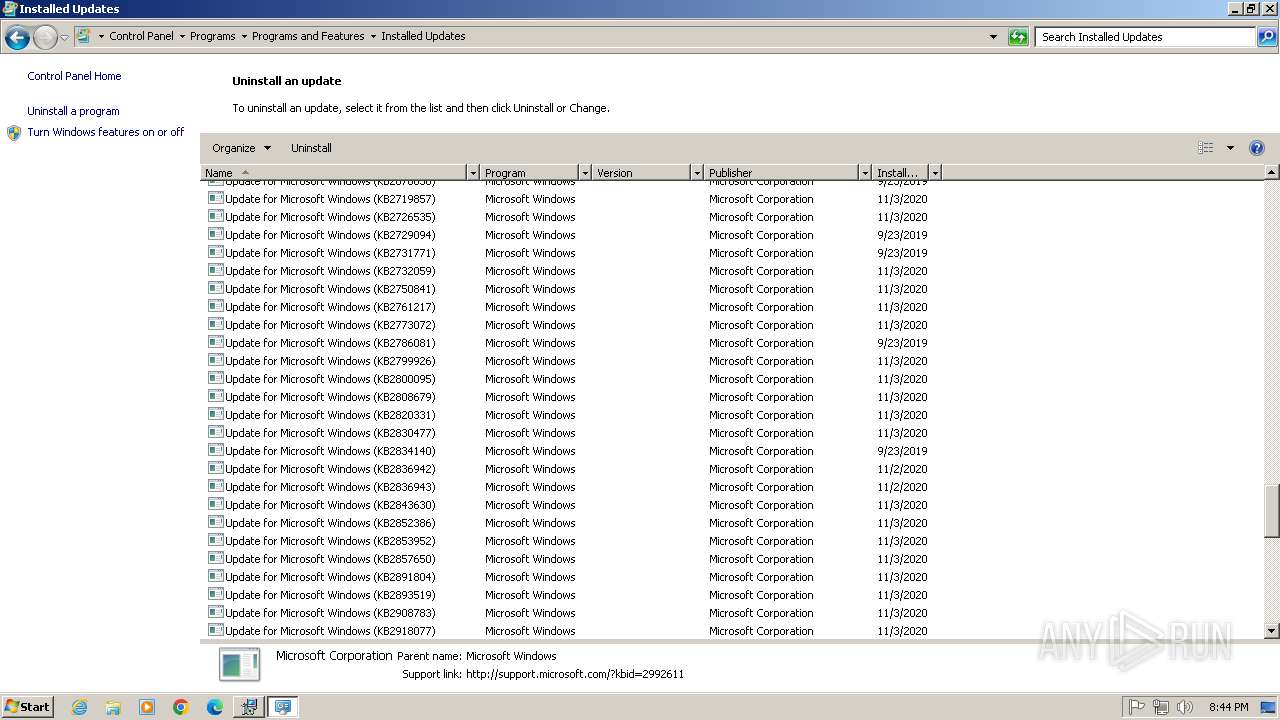
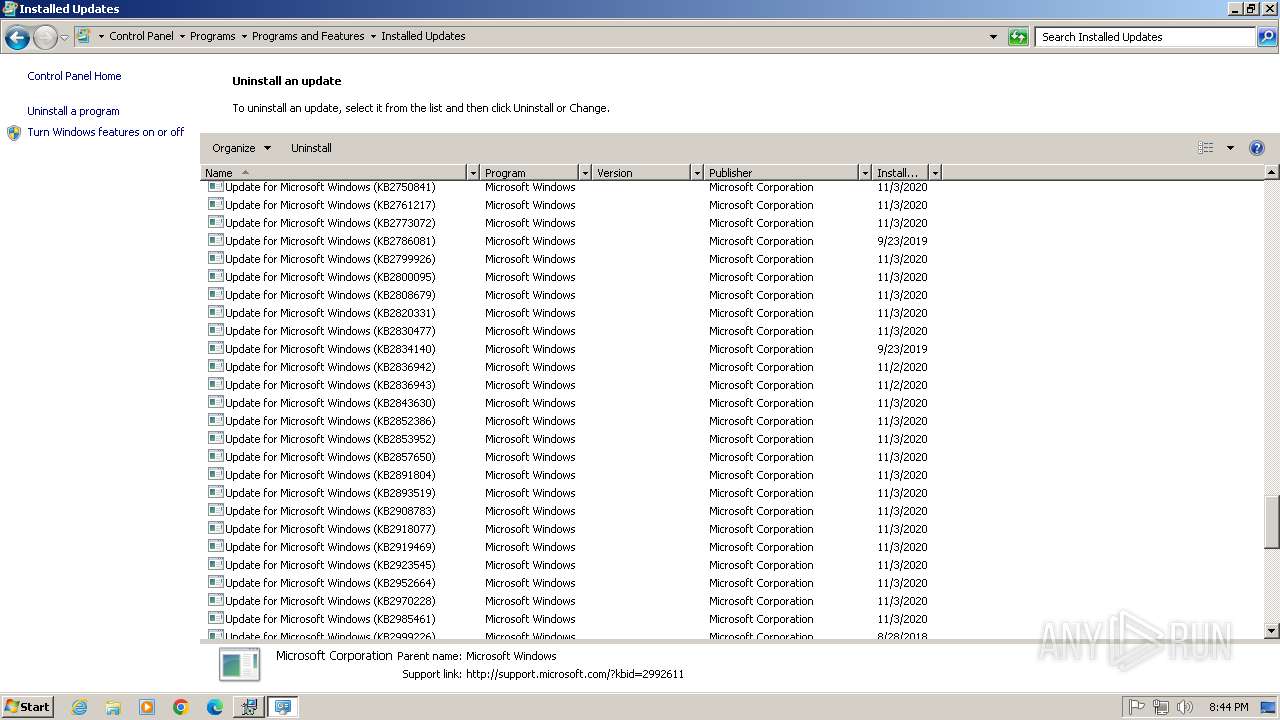
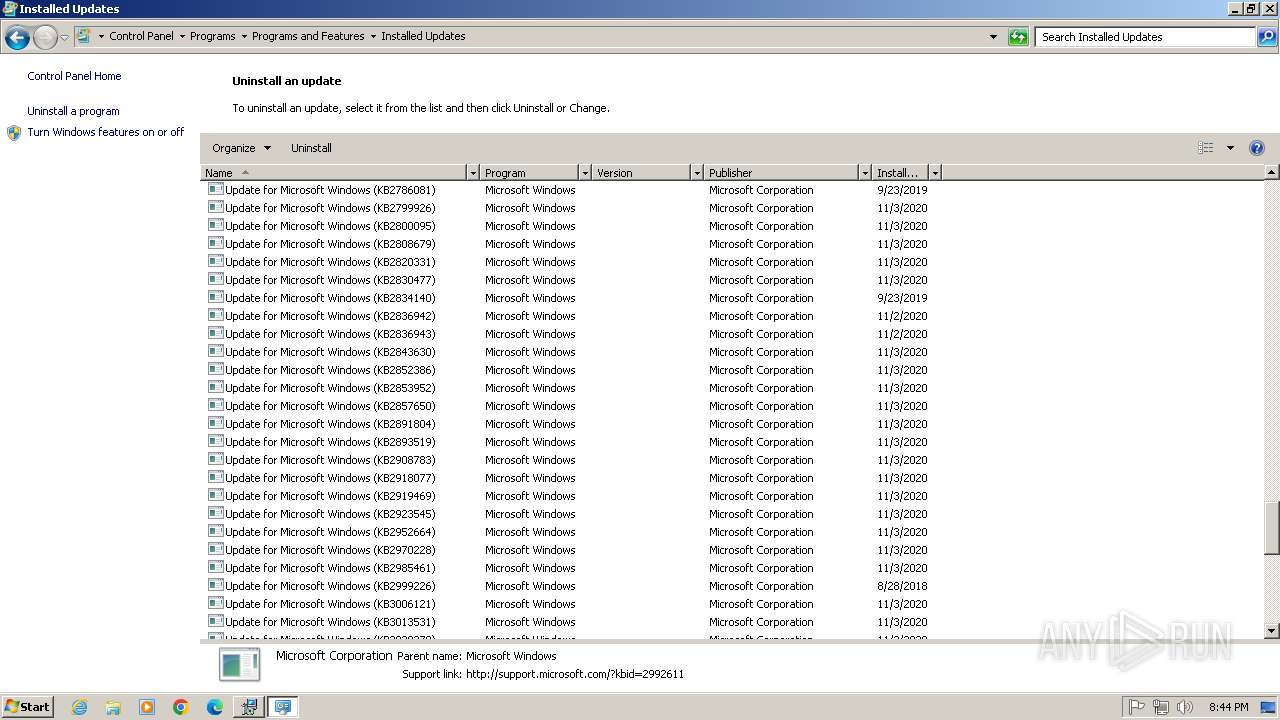
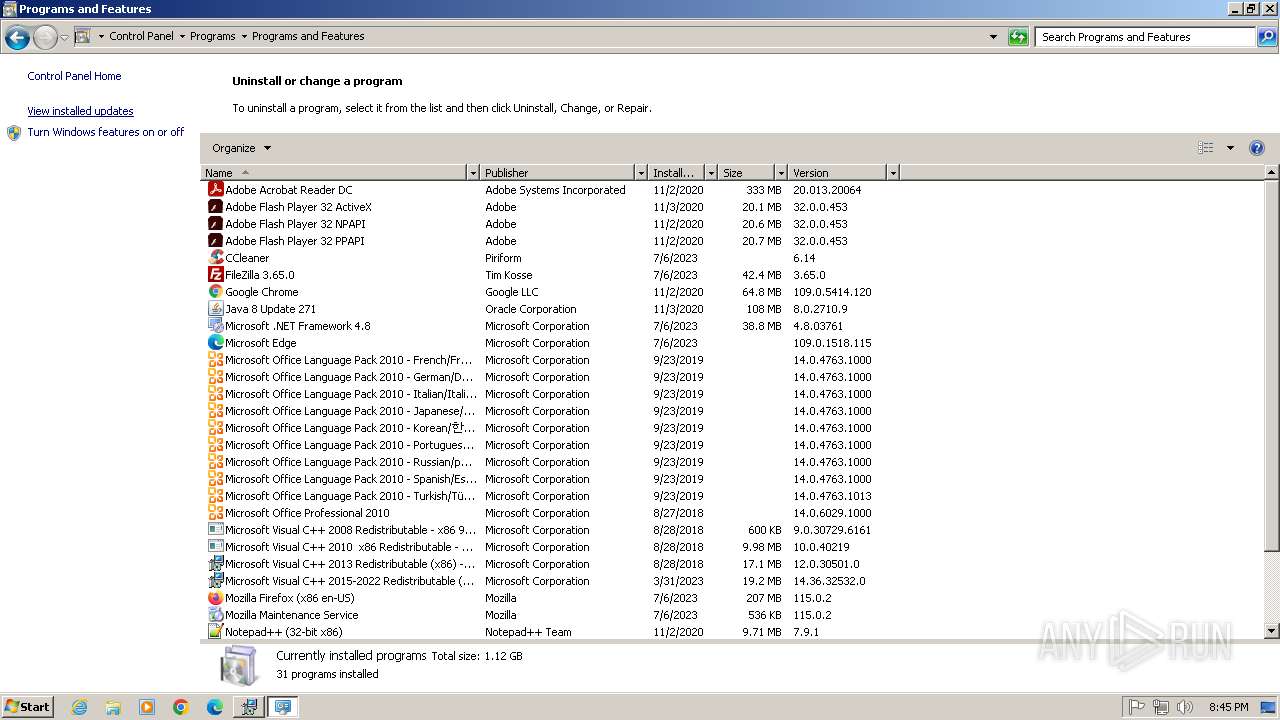
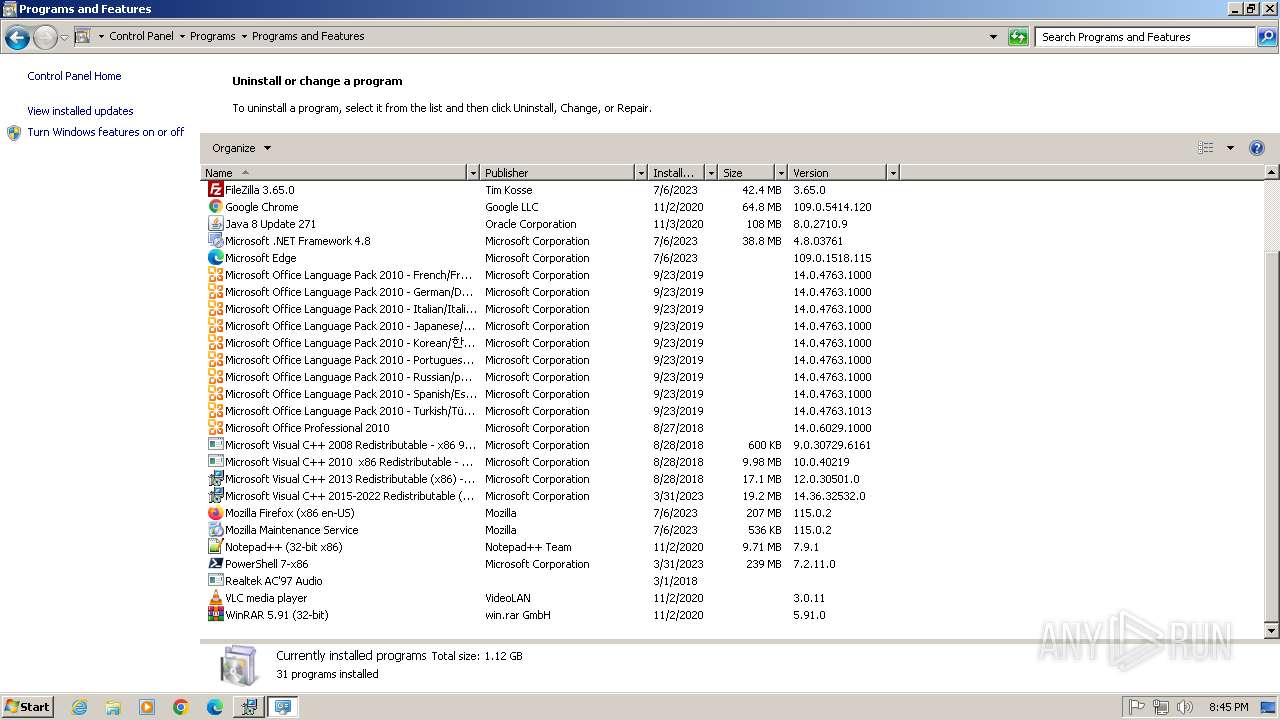
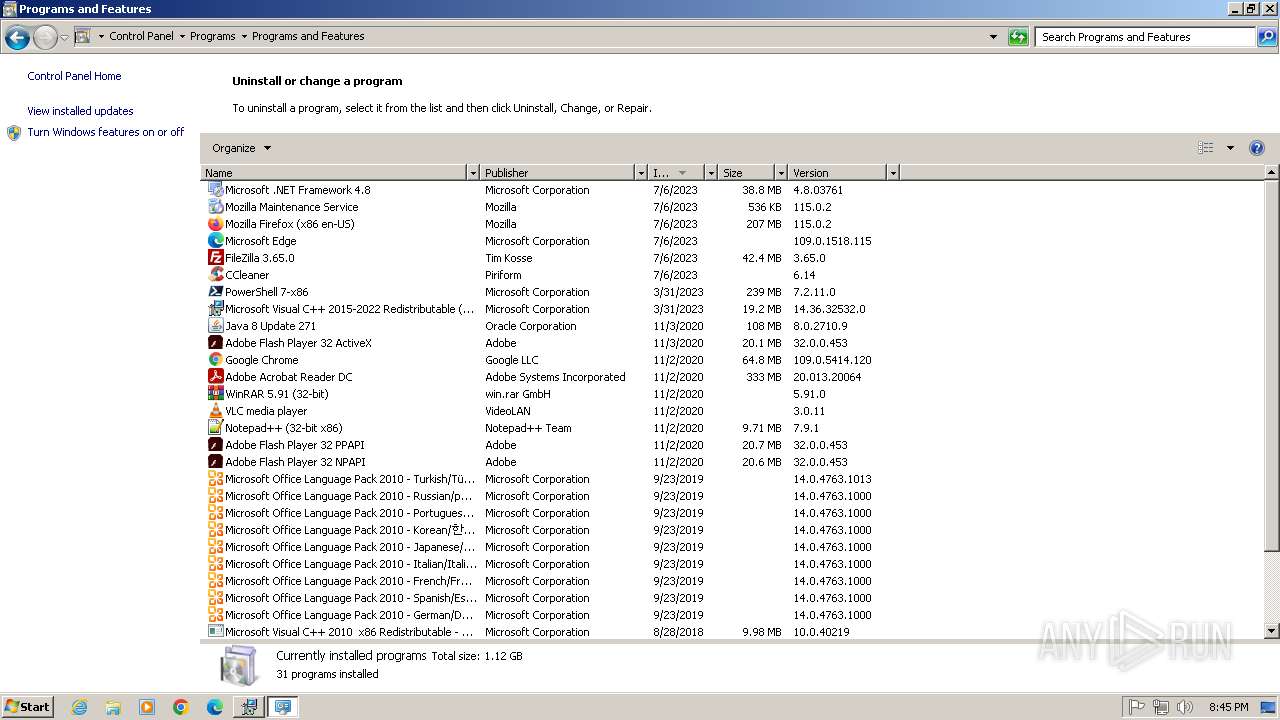
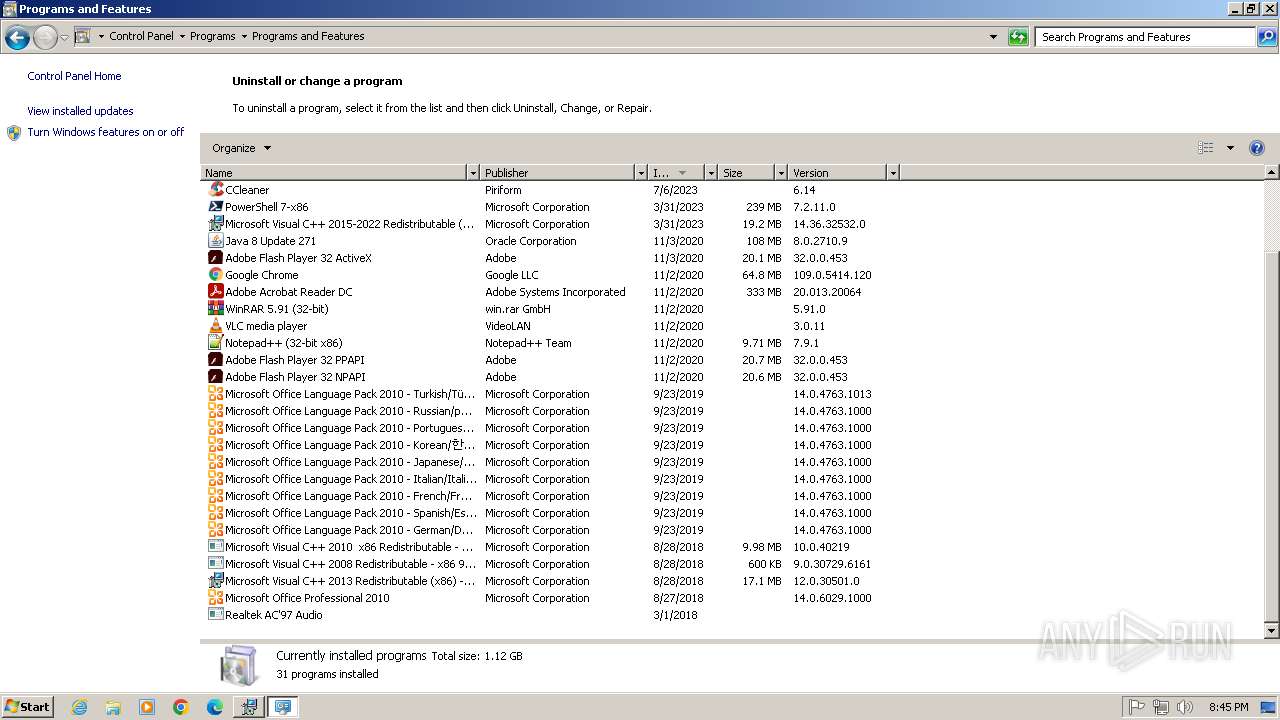
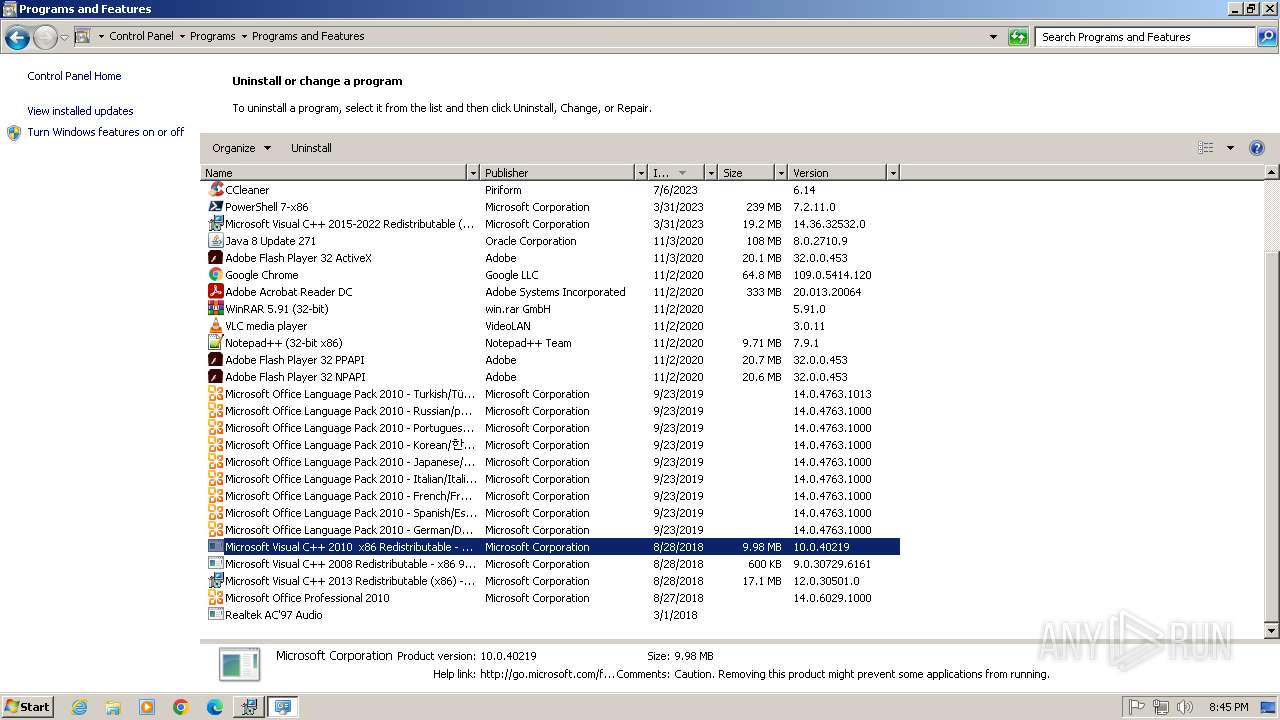
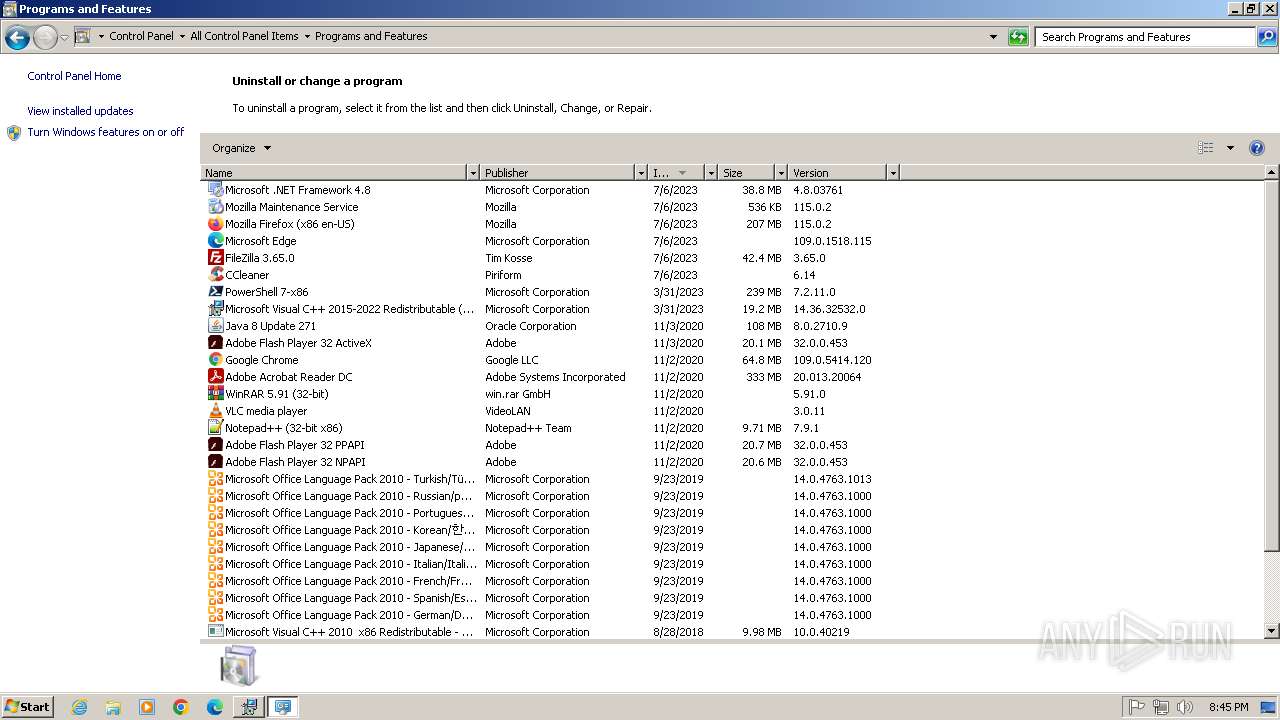
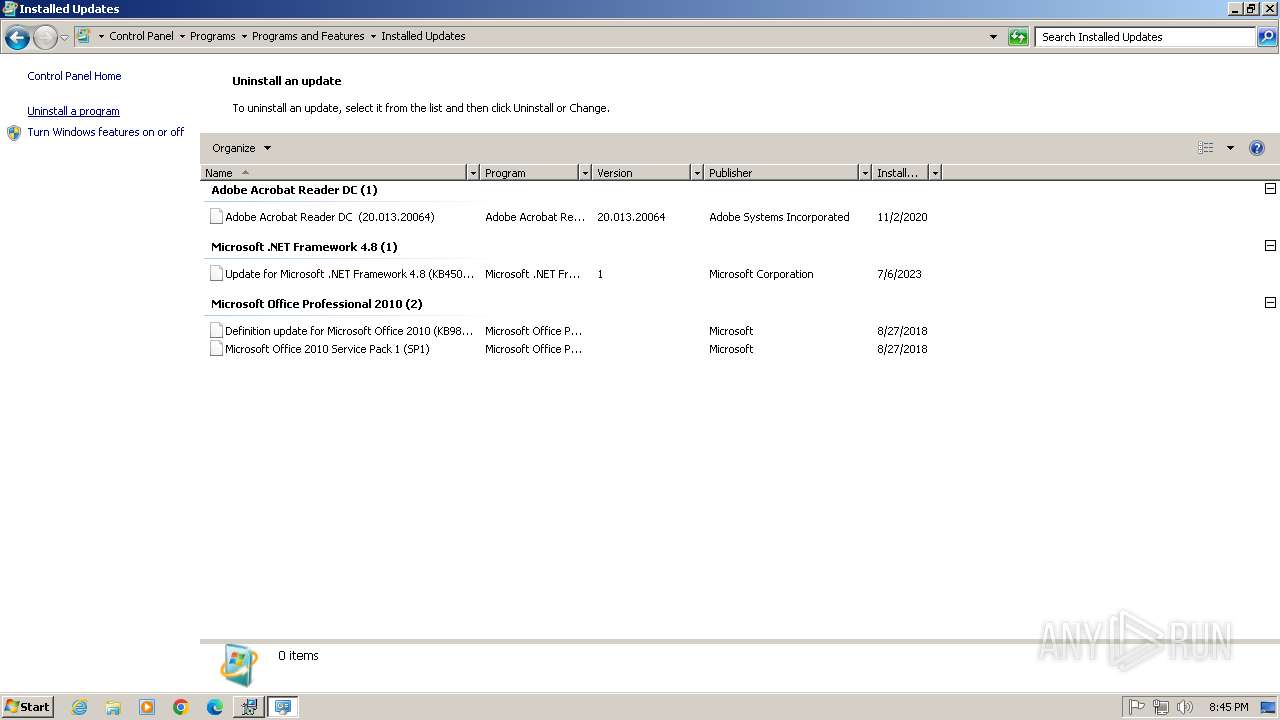
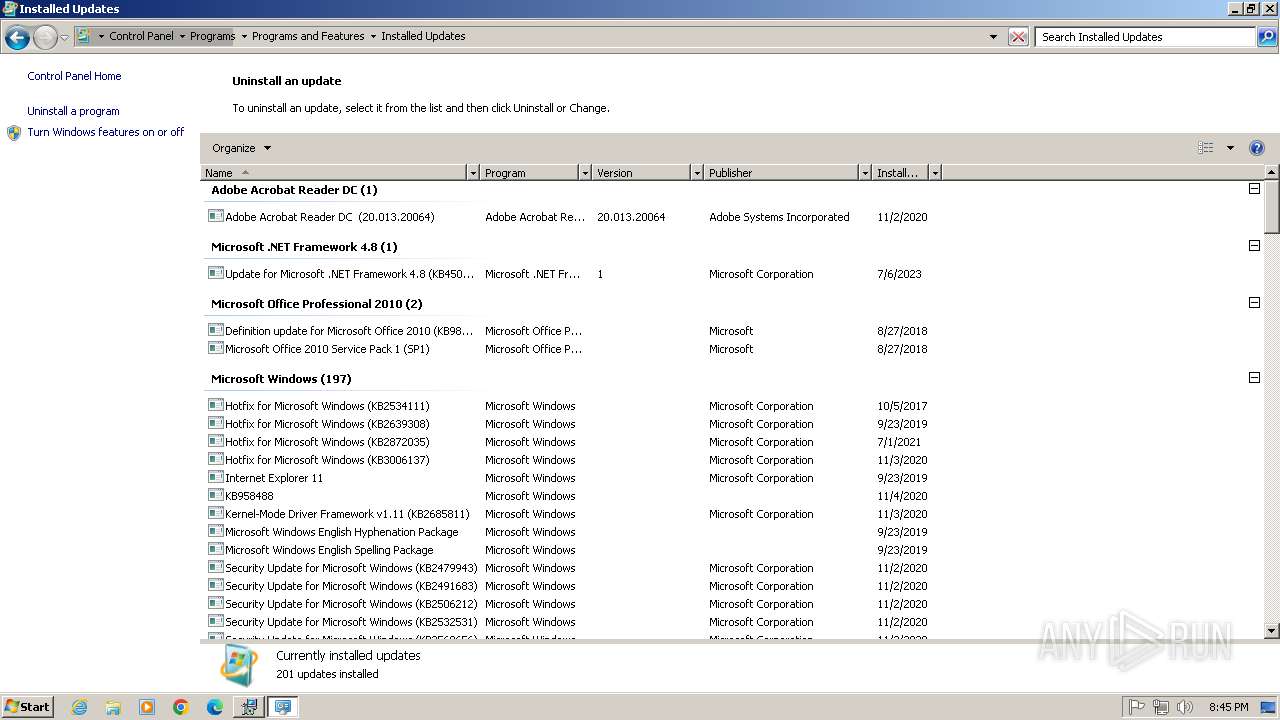
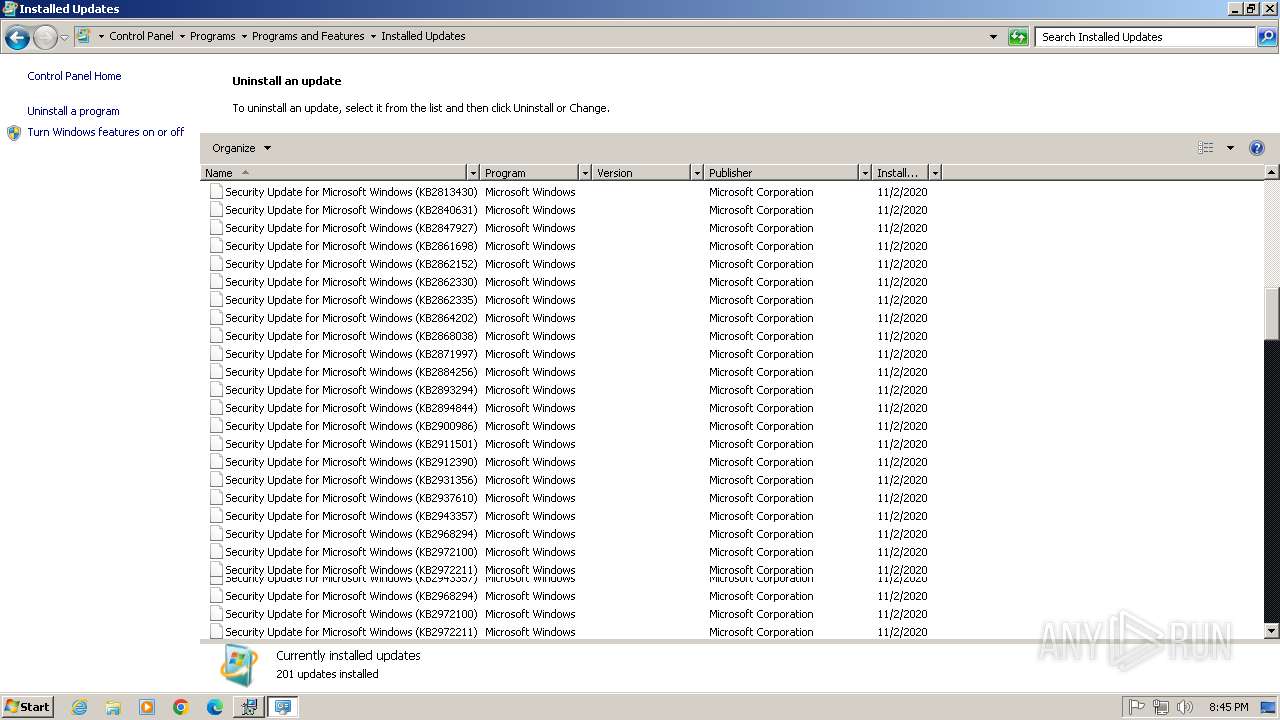
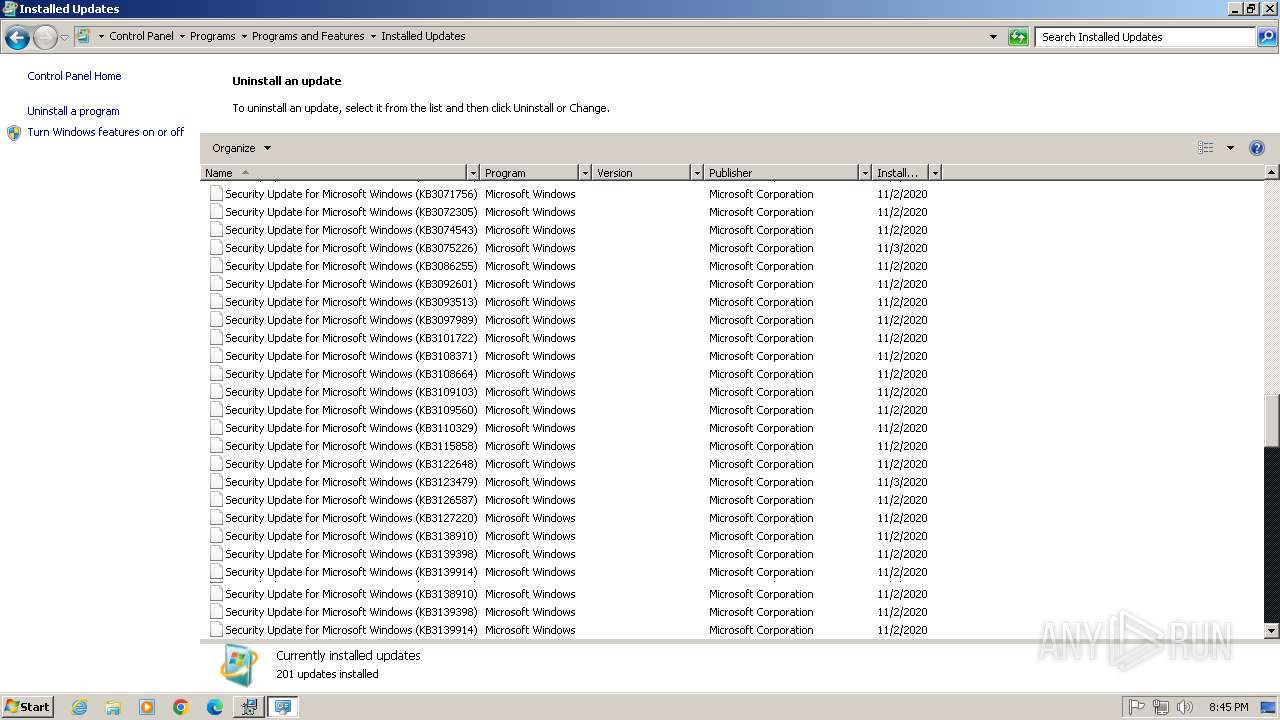
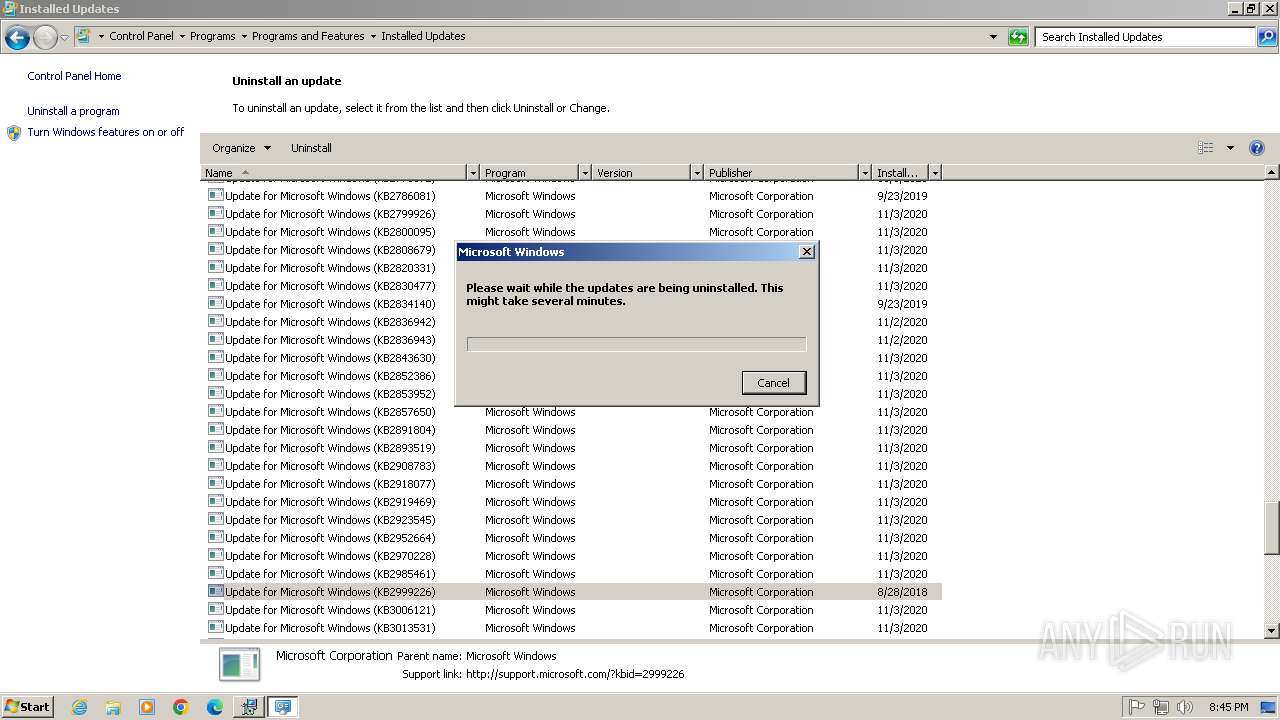
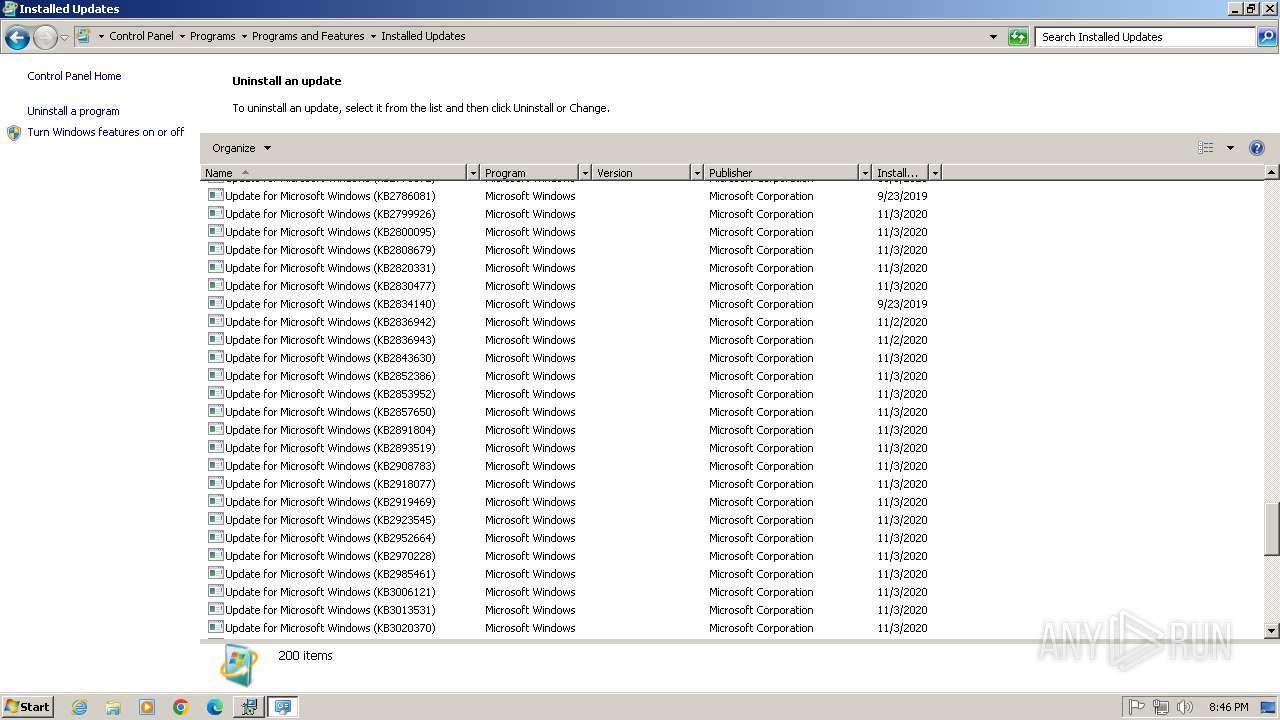
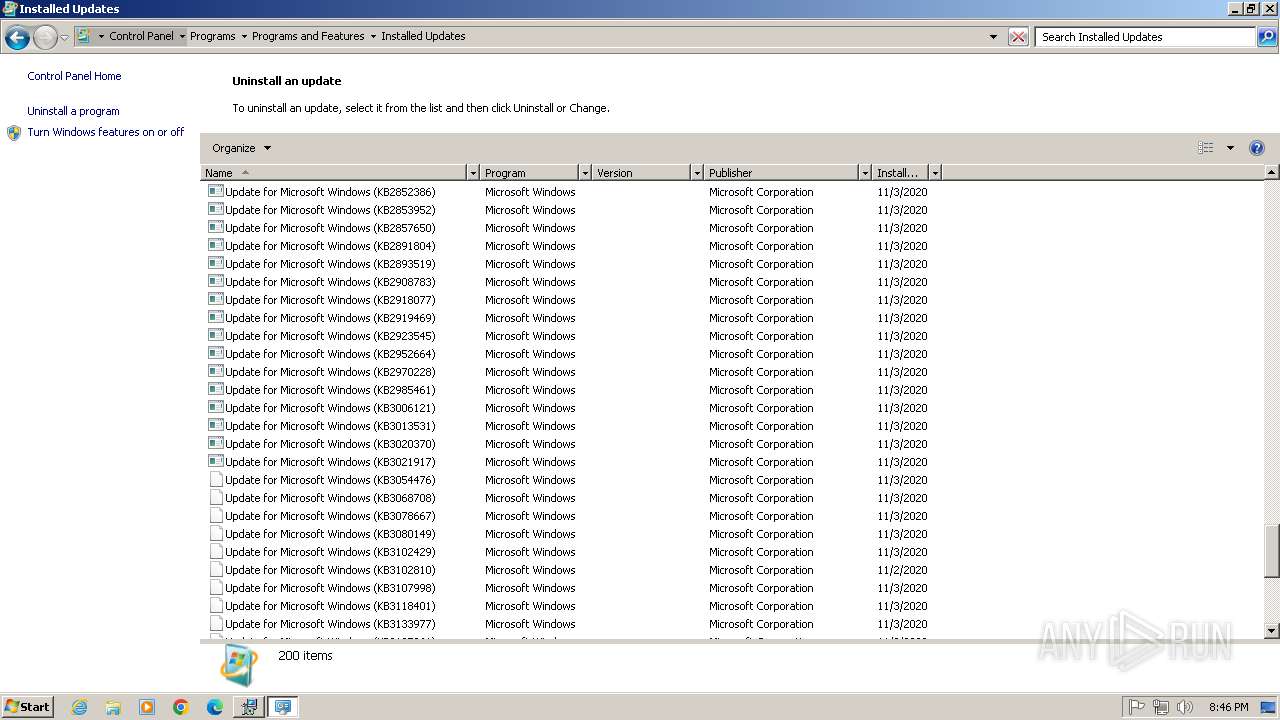
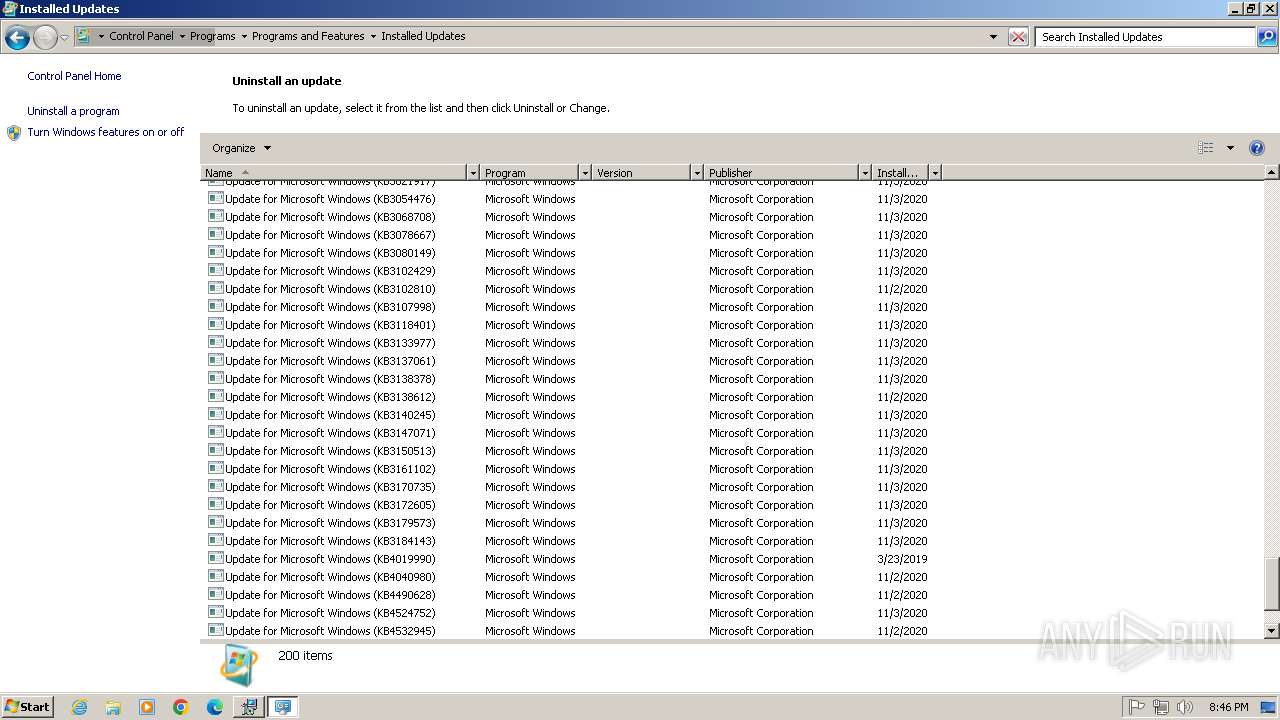
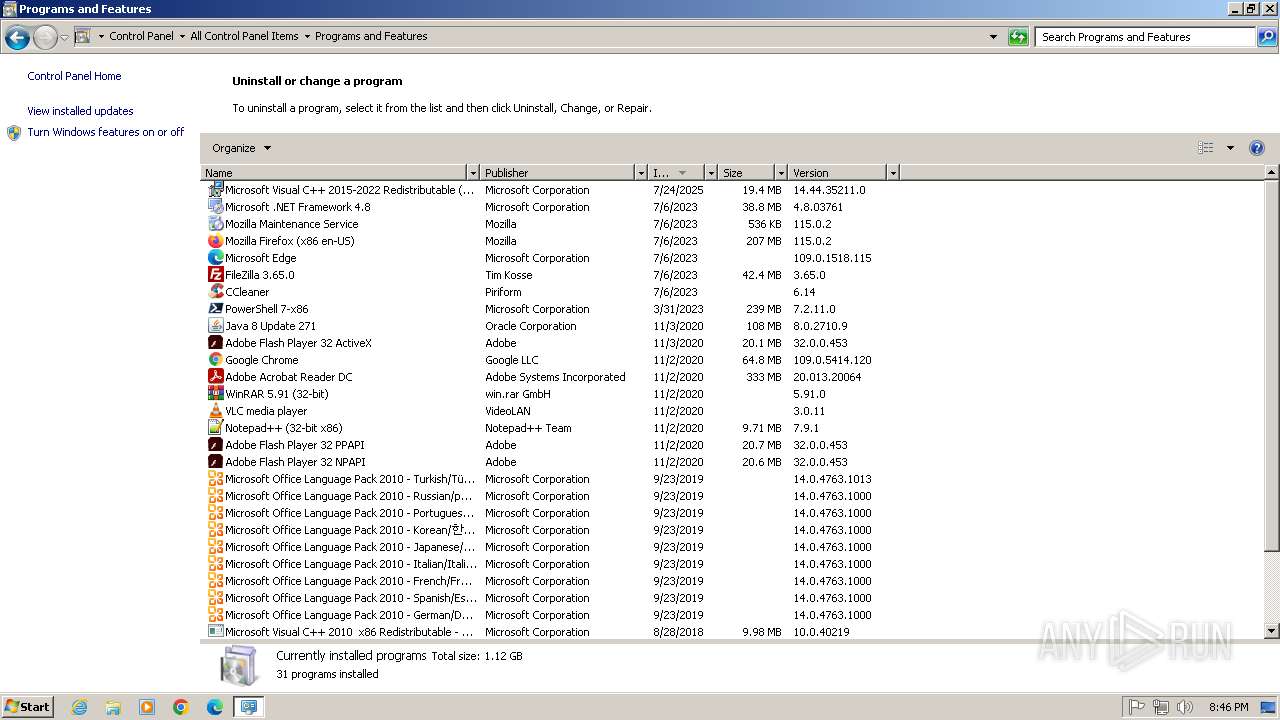
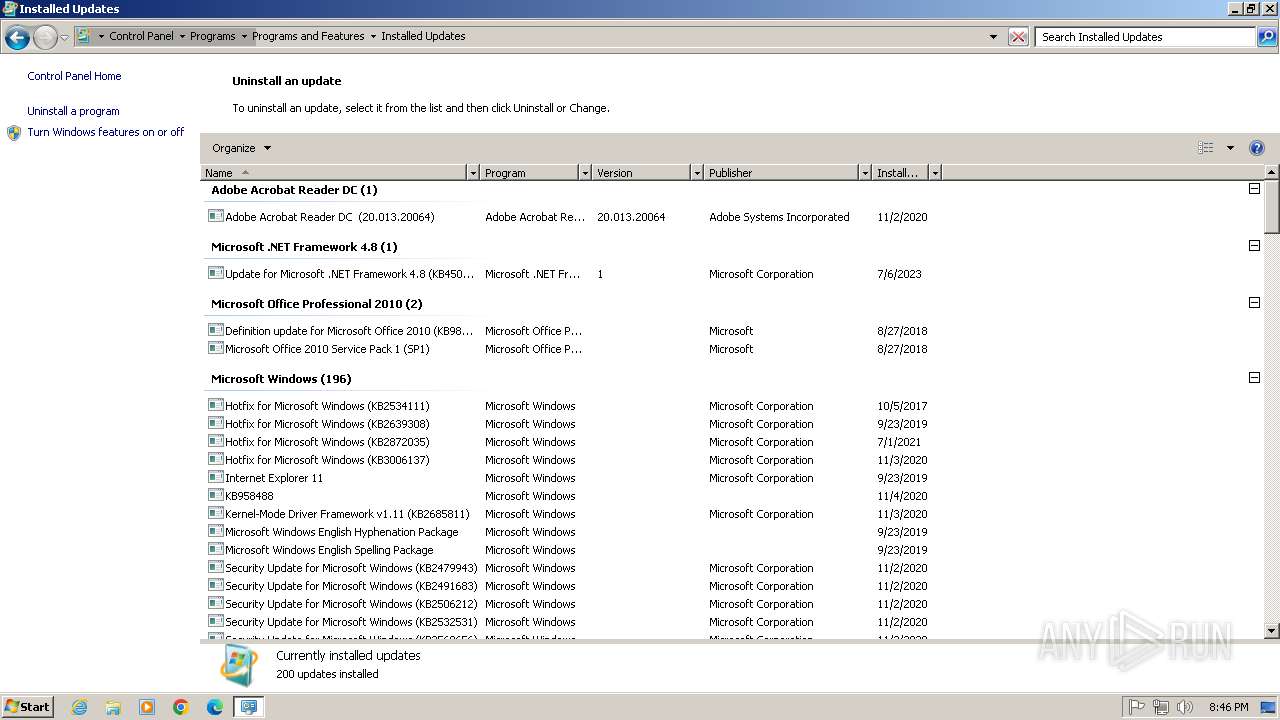
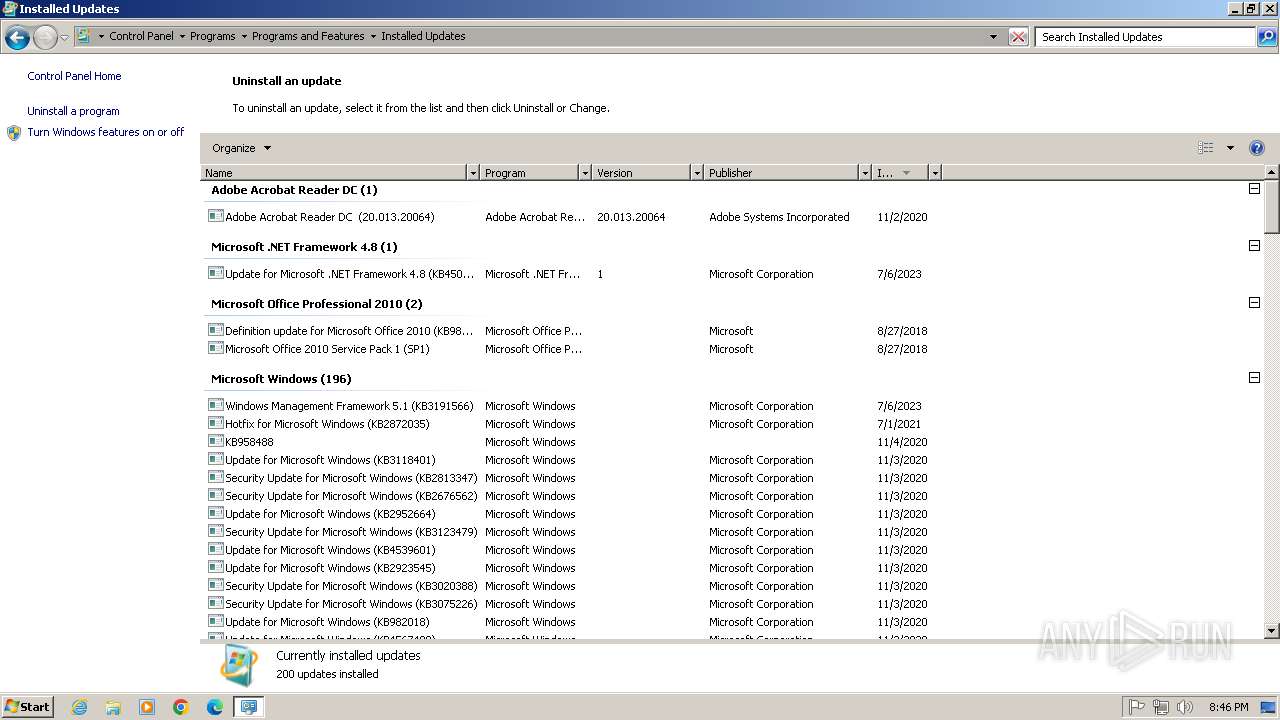
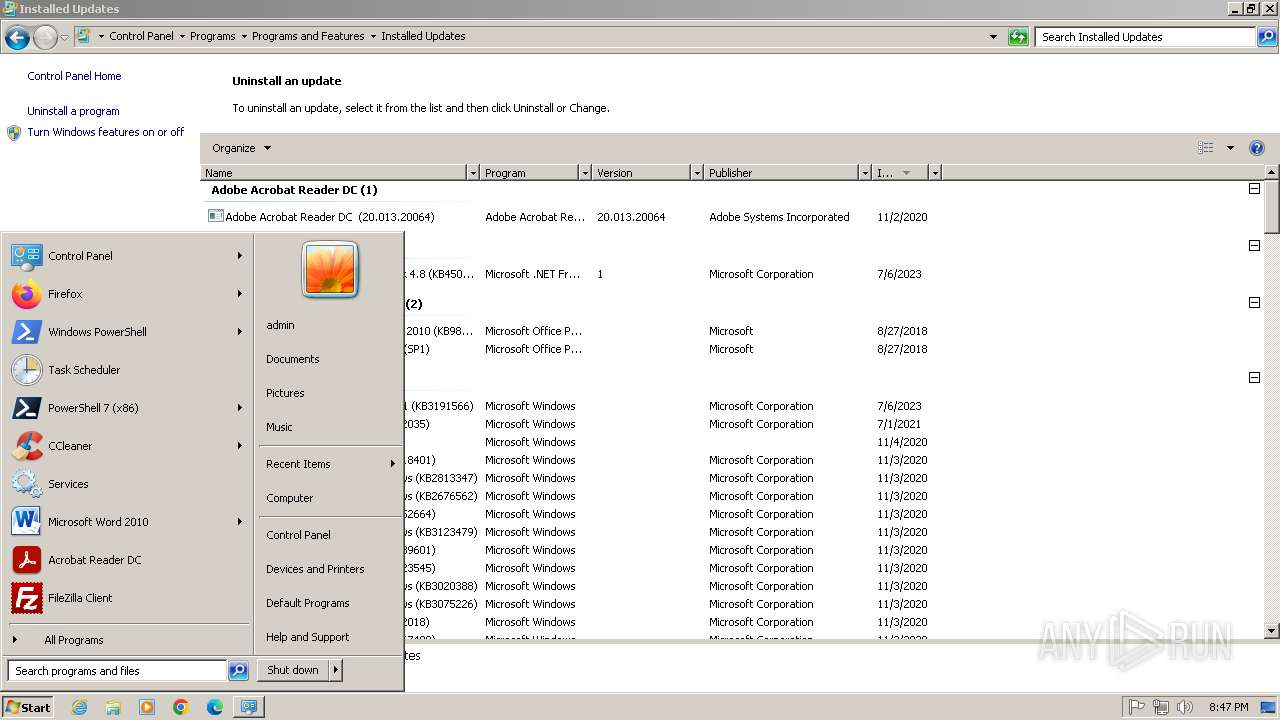
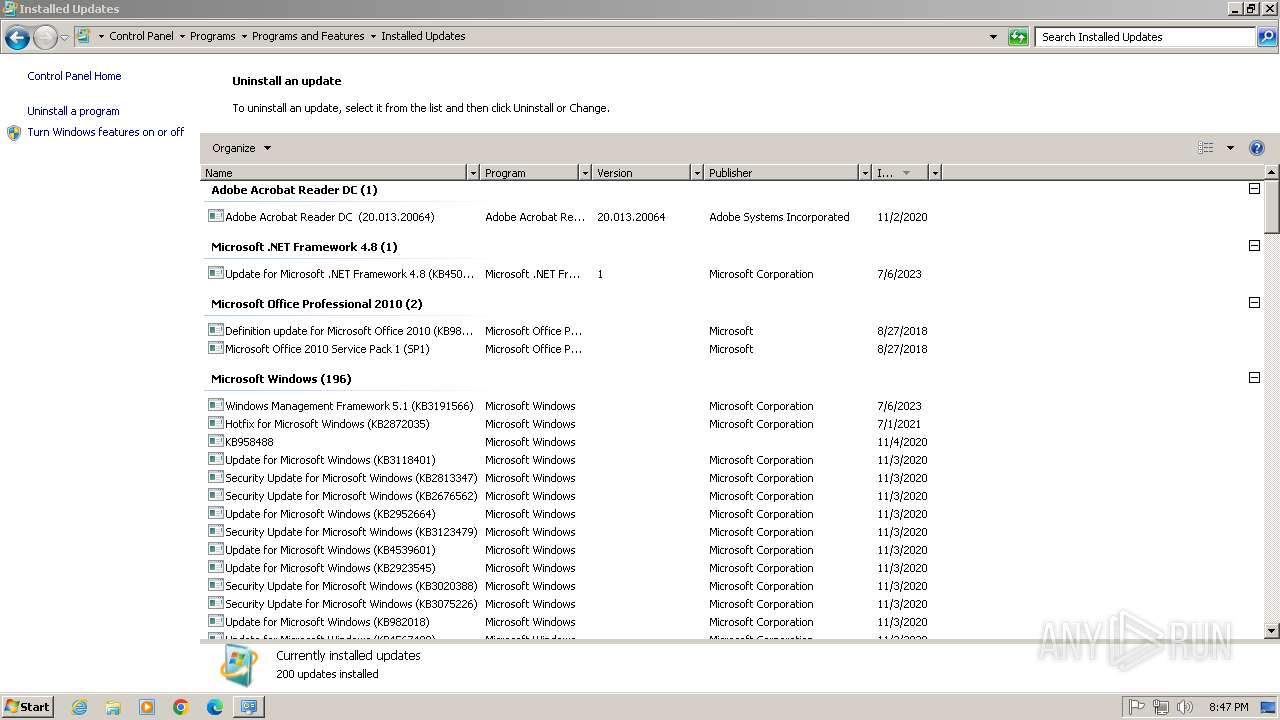
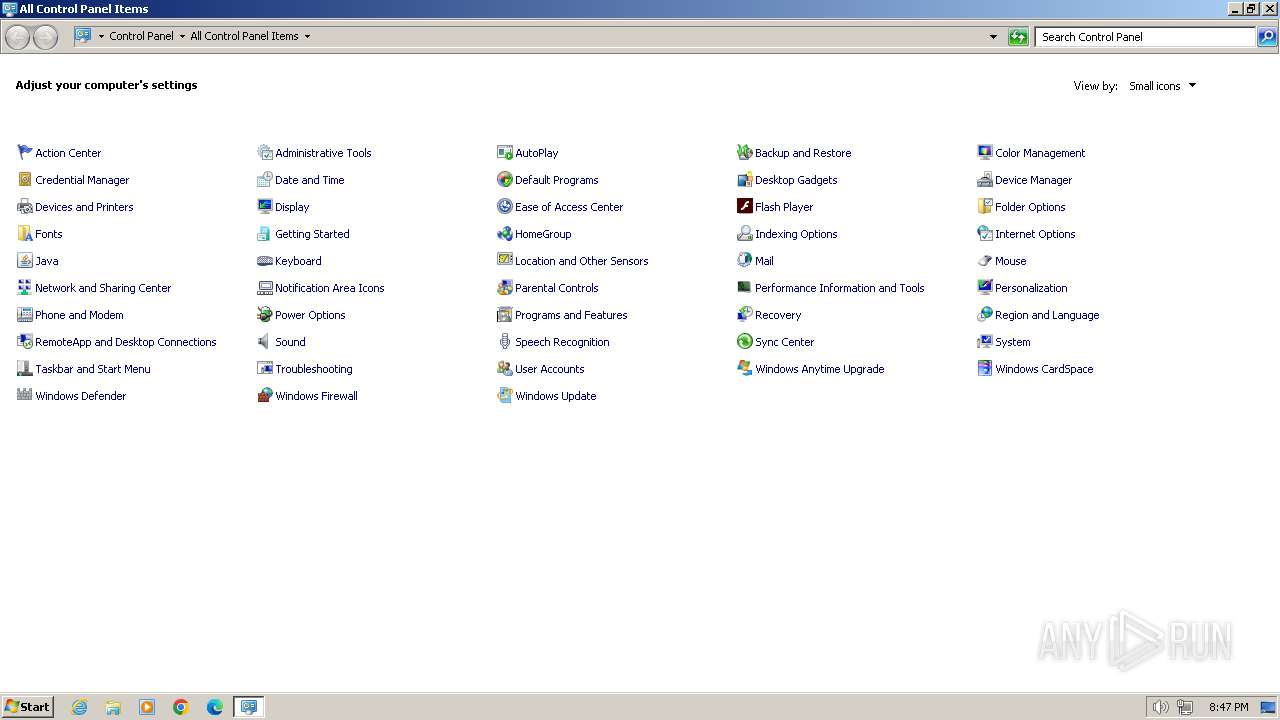
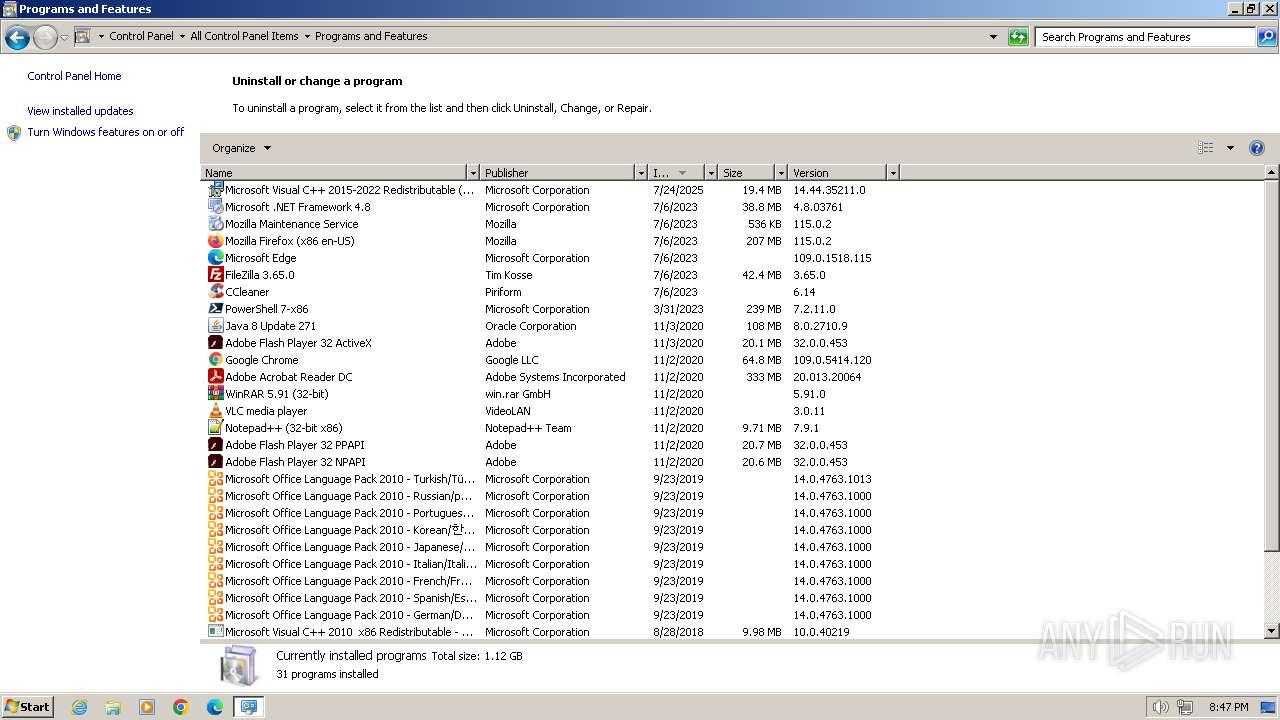
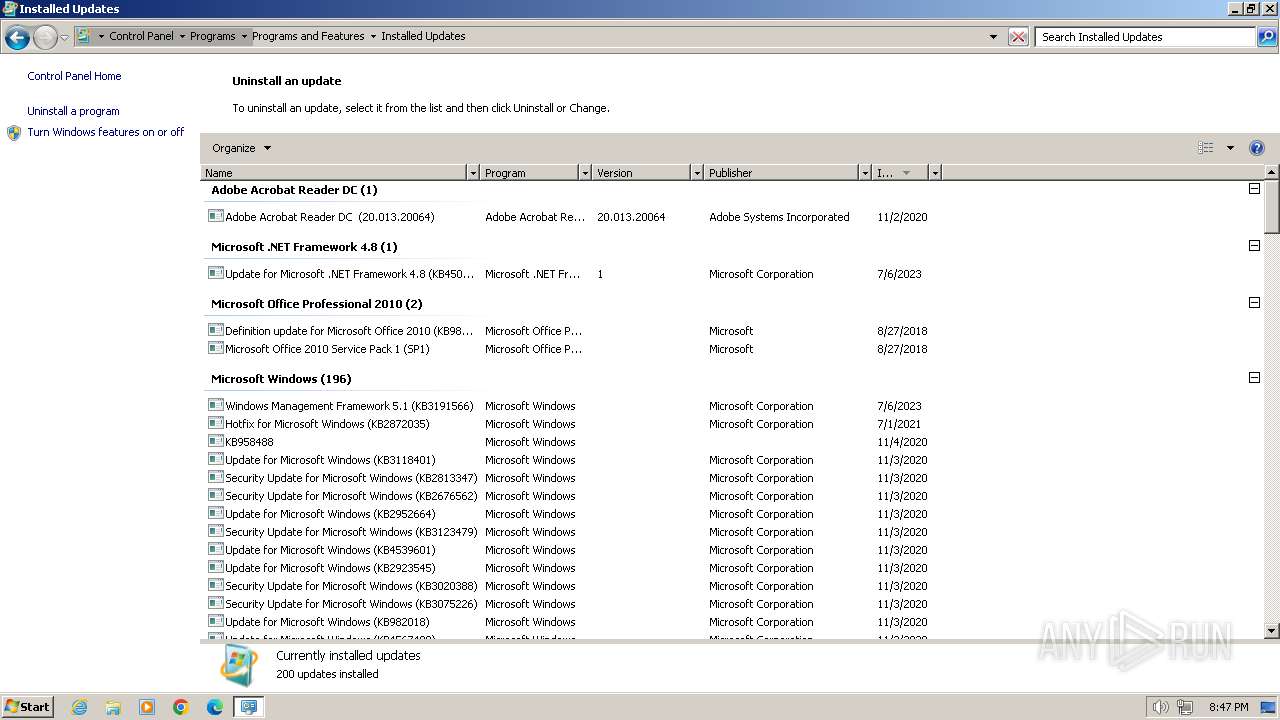
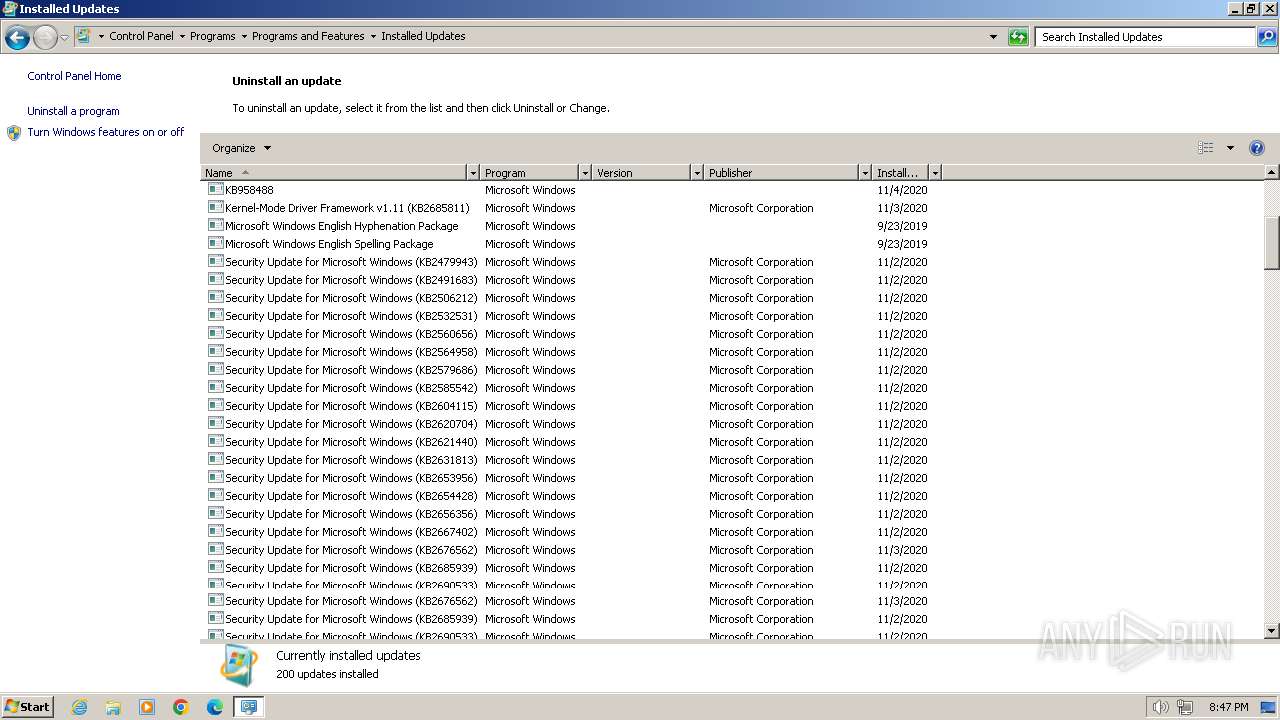
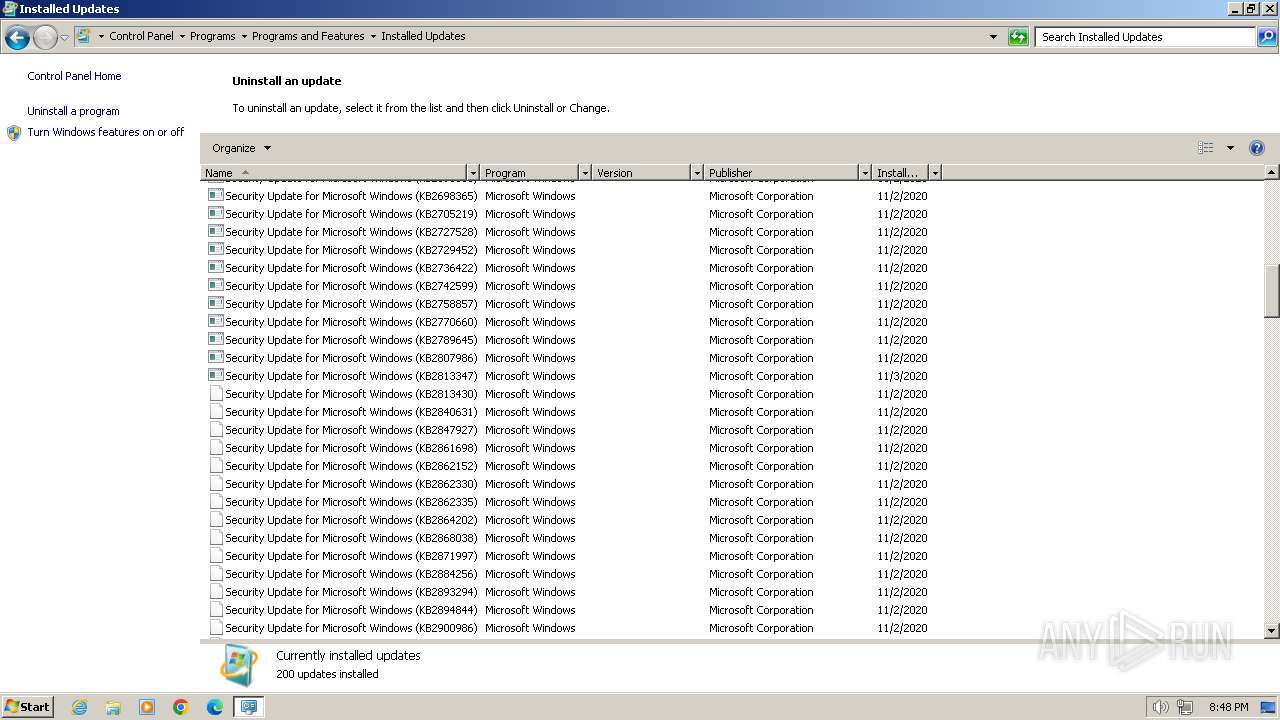
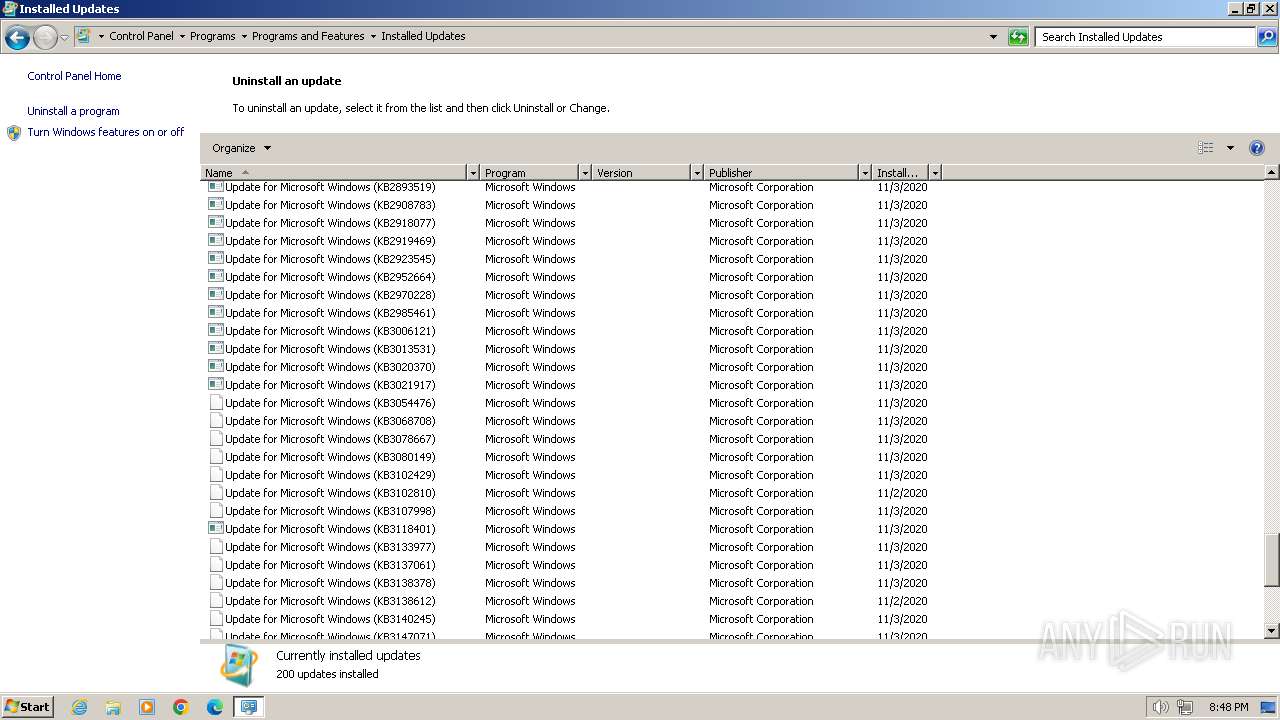
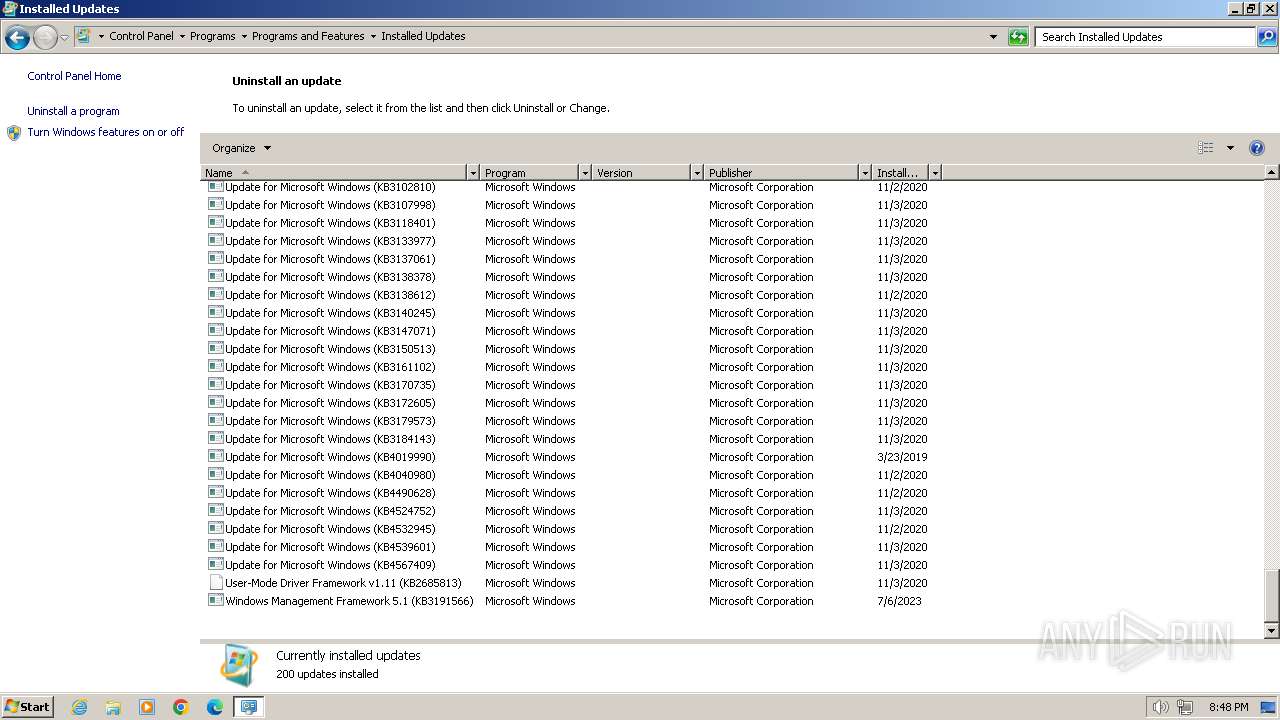
Searches for installed software
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 3752)
- VC_redist.x86.exe (PID: 2208)
- VC_redist.x86.exe (PID: 3024)
Reads security settings of Internet Explorer
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 2208)
Reads the Internet Settings
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 2208)
- sipnotify.exe (PID: 1448)
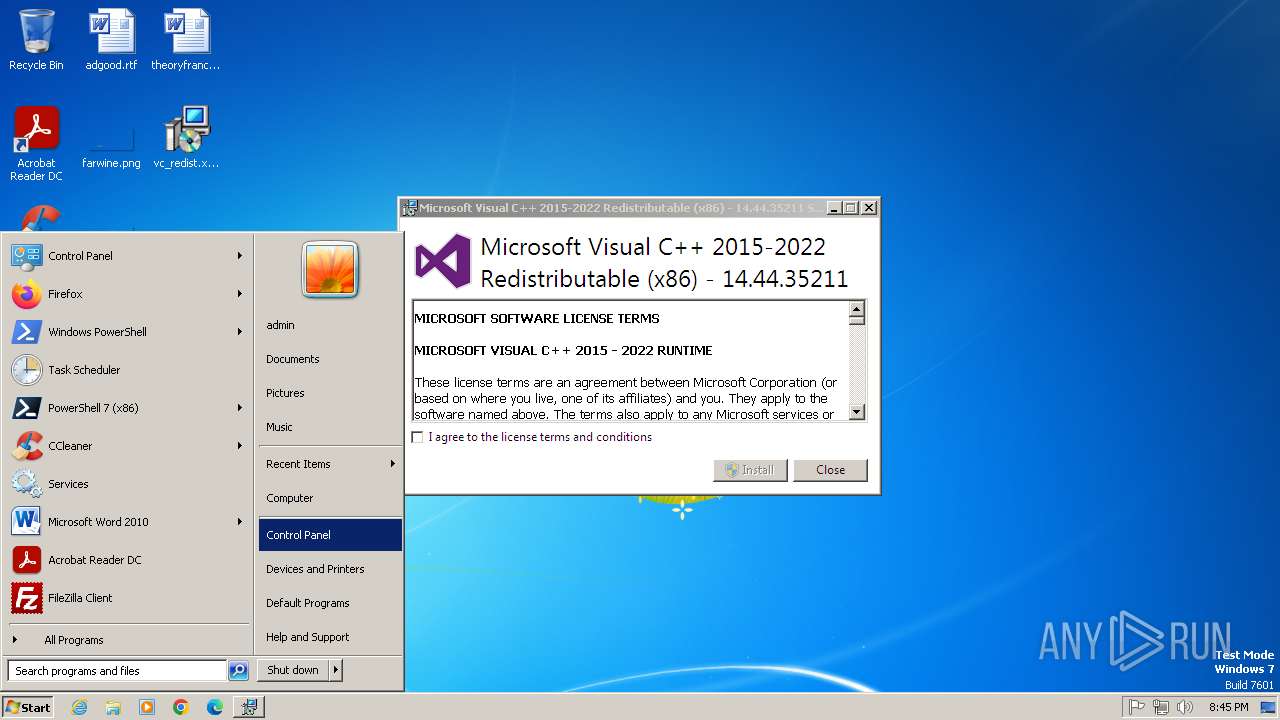
Starts itself from another location
- vc_redist.x86.exe (PID: 3300)
Executes as Windows Service
- VSSVC.exe (PID: 2820)
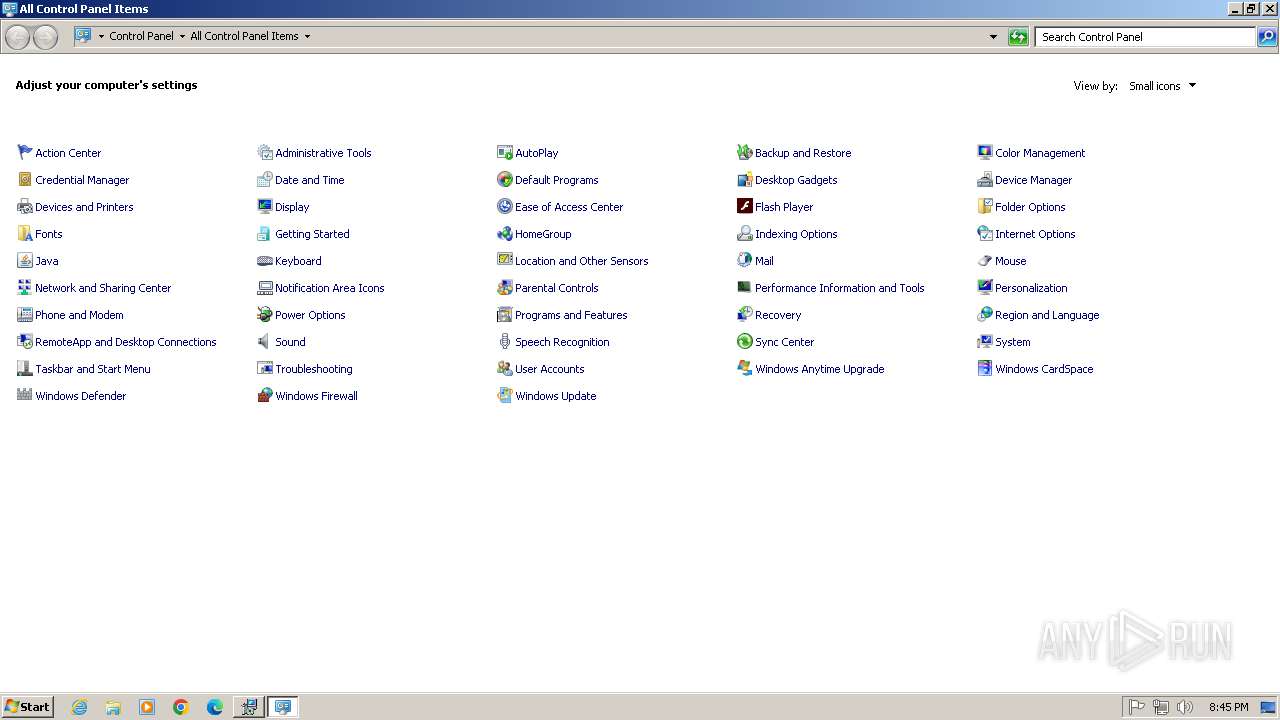
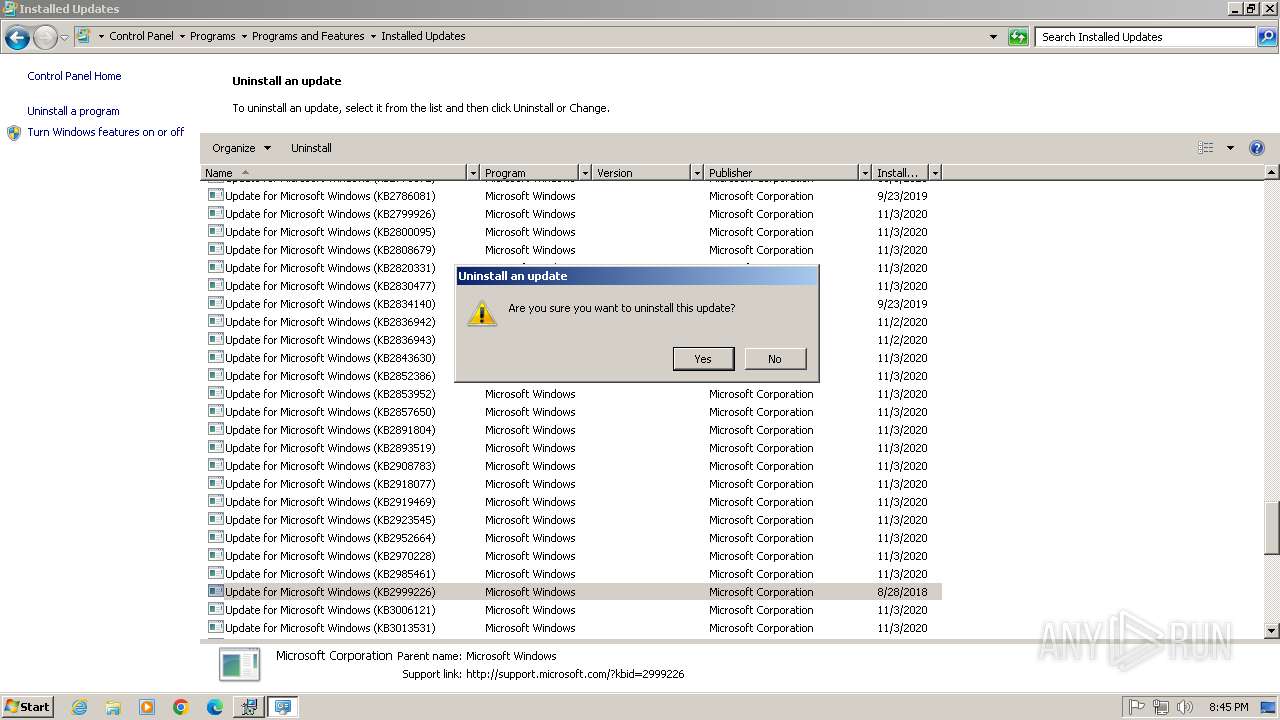
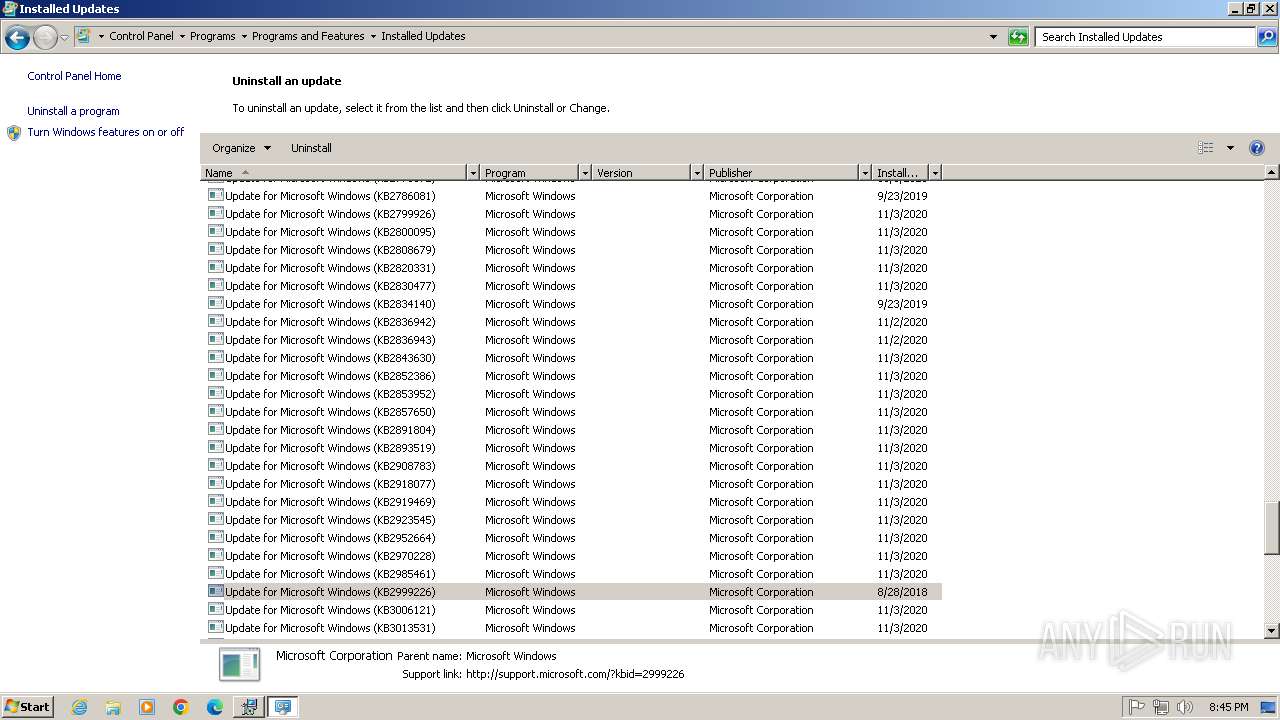
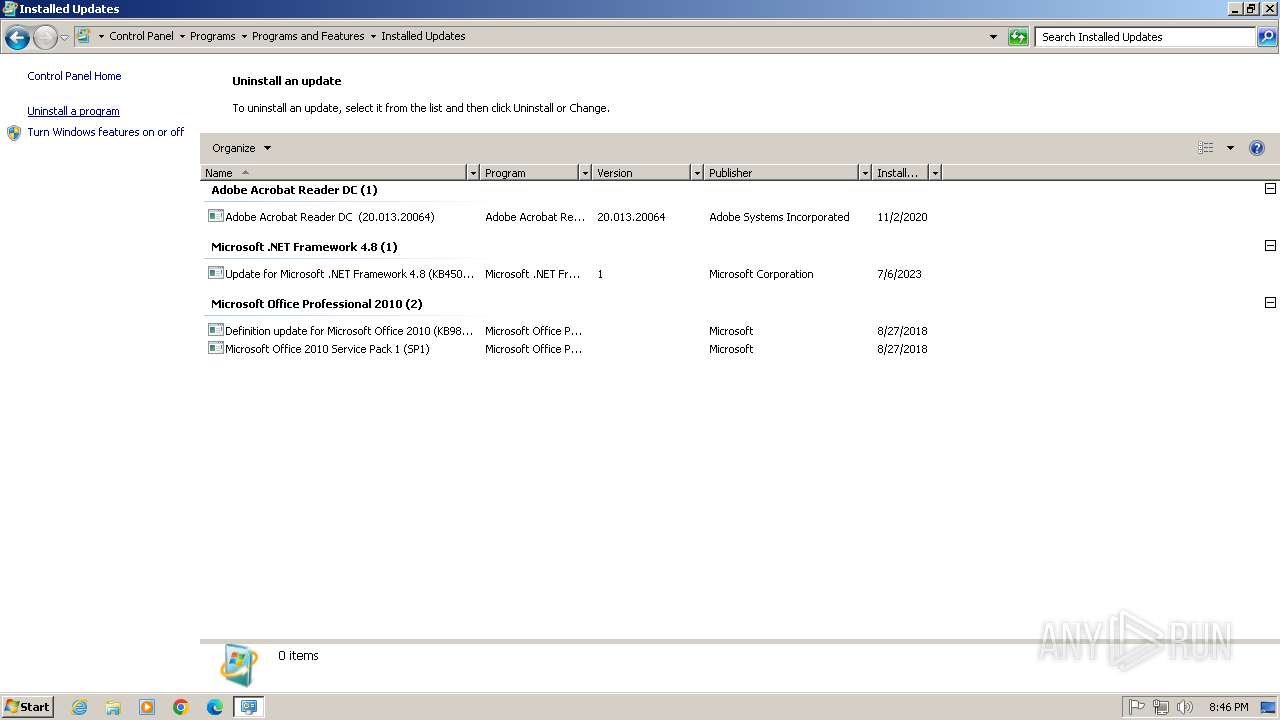
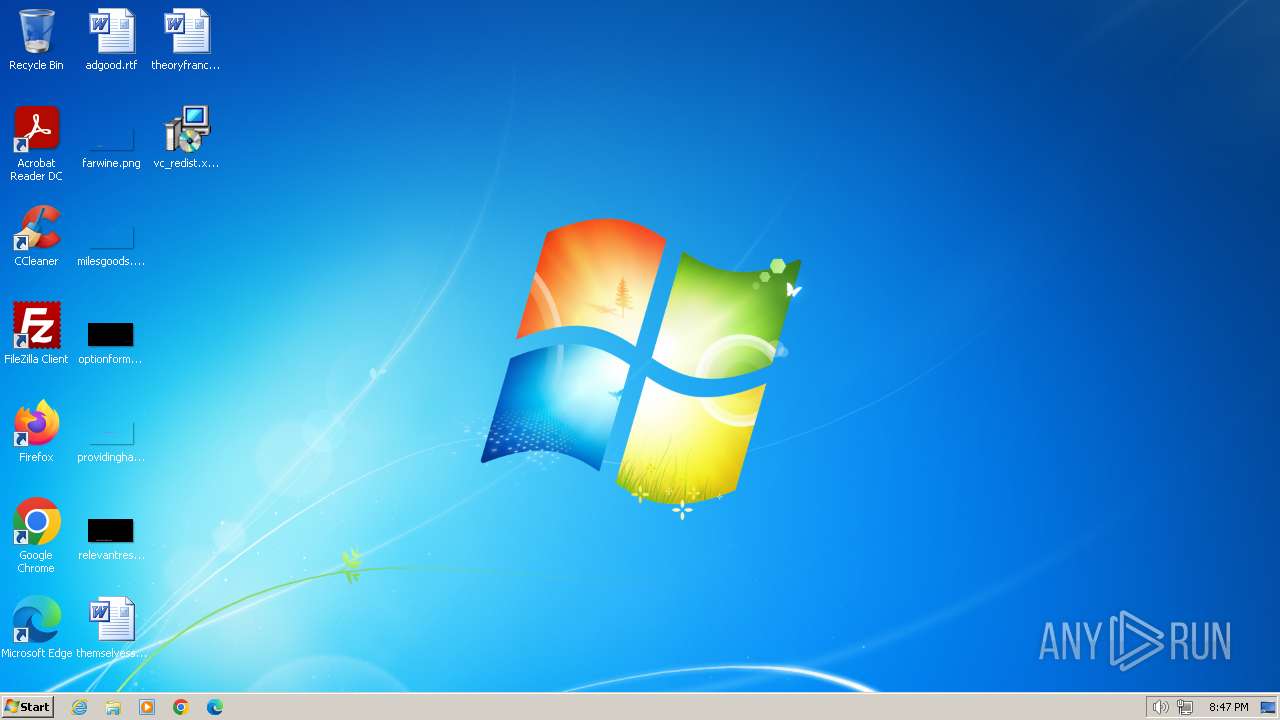
Creates a software uninstall entry
- VC_redist.x86.exe (PID: 3752)
- VC_redist.x86.exe (PID: 3024)
Application launched itself
- VC_redist.x86.exe (PID: 2356)
- VC_redist.x86.exe (PID: 2208)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3868)
The process drops C-runtime libraries
- msiexec.exe (PID: 3868)
The process executes via Task Scheduler
- ctfmon.exe (PID: 1472)
- sipnotify.exe (PID: 1448)
INFO
Create files in a temporary directory
- vc_redist.x86.exe (PID: 848)
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 3752)
- msiexec.exe (PID: 3868)
- VC_redist.x86.exe (PID: 2208)
The sample compiled with english language support
- vc_redist.x86.exe (PID: 848)
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 3752)
- VC_redist.x86.exe (PID: 2208)
- msiexec.exe (PID: 3868)
- VC_redist.x86.exe (PID: 3024)
Checks supported languages
- vc_redist.x86.exe (PID: 848)
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 3752)
- msiexec.exe (PID: 3868)
- VC_redist.x86.exe (PID: 2356)
- VC_redist.x86.exe (PID: 2208)
- VC_redist.x86.exe (PID: 3024)
- IMEKLMG.EXE (PID: 2100)
- IMEKLMG.EXE (PID: 2092)
Reads the computer name
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 3752)
- msiexec.exe (PID: 3868)
- VC_redist.x86.exe (PID: 2208)
- VC_redist.x86.exe (PID: 3024)
- IMEKLMG.EXE (PID: 2100)
- IMEKLMG.EXE (PID: 2092)
Reads the machine GUID from the registry
- vc_redist.x86.exe (PID: 3300)
- VC_redist.x86.exe (PID: 3752)
- msiexec.exe (PID: 3868)
- VC_redist.x86.exe (PID: 2208)
- VC_redist.x86.exe (PID: 3024)
Creates files in the program directory
- VC_redist.x86.exe (PID: 3752)
Launching a file from a Registry key
- VC_redist.x86.exe (PID: 3752)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3868)
Reads the software policy settings
- msiexec.exe (PID: 3868)
Creates a software uninstall entry
- msiexec.exe (PID: 3868)
Manual execution by a user
- IMEKLMG.EXE (PID: 2092)
- IMEKLMG.EXE (PID: 2100)
Process checks whether UAC notifications are on
- IMEKLMG.EXE (PID: 2100)
- IMEKLMG.EXE (PID: 2092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:03:22 22:14:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 314368 |
| InitializedDataSize: | 164352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x302e5 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 14.44.35211.0 |
| ProductVersionNumber: | 14.44.35211.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
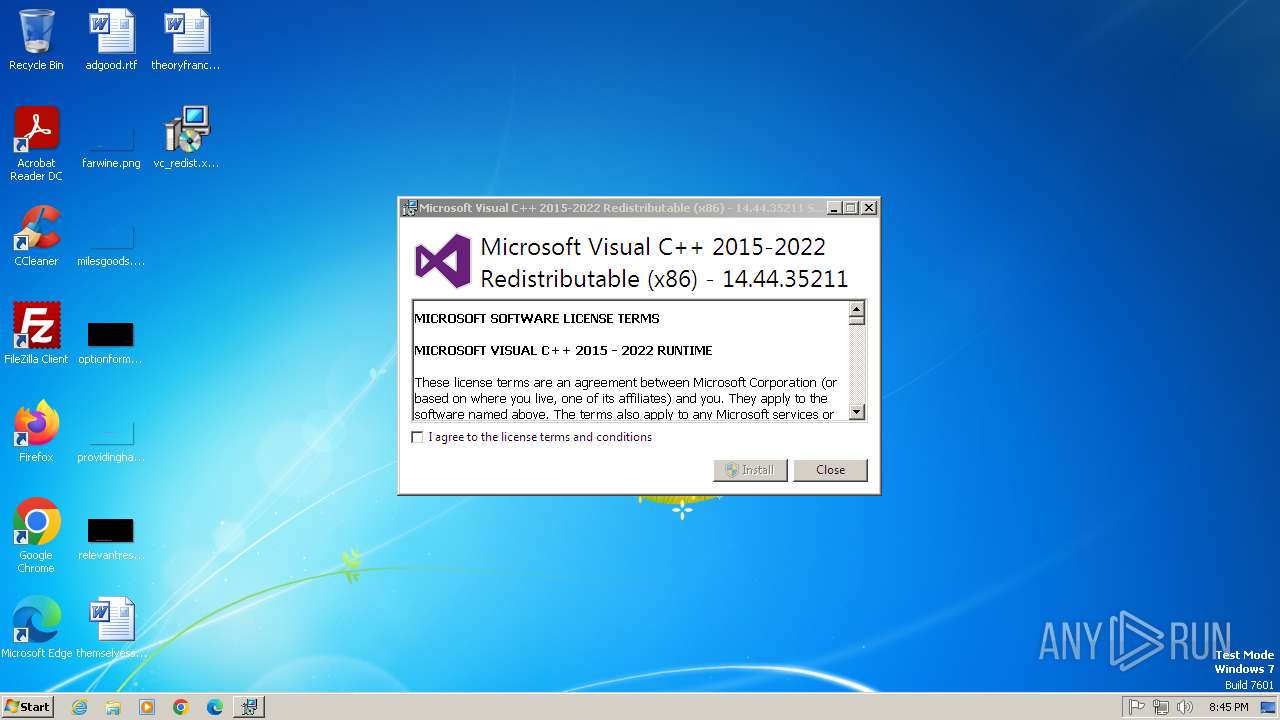
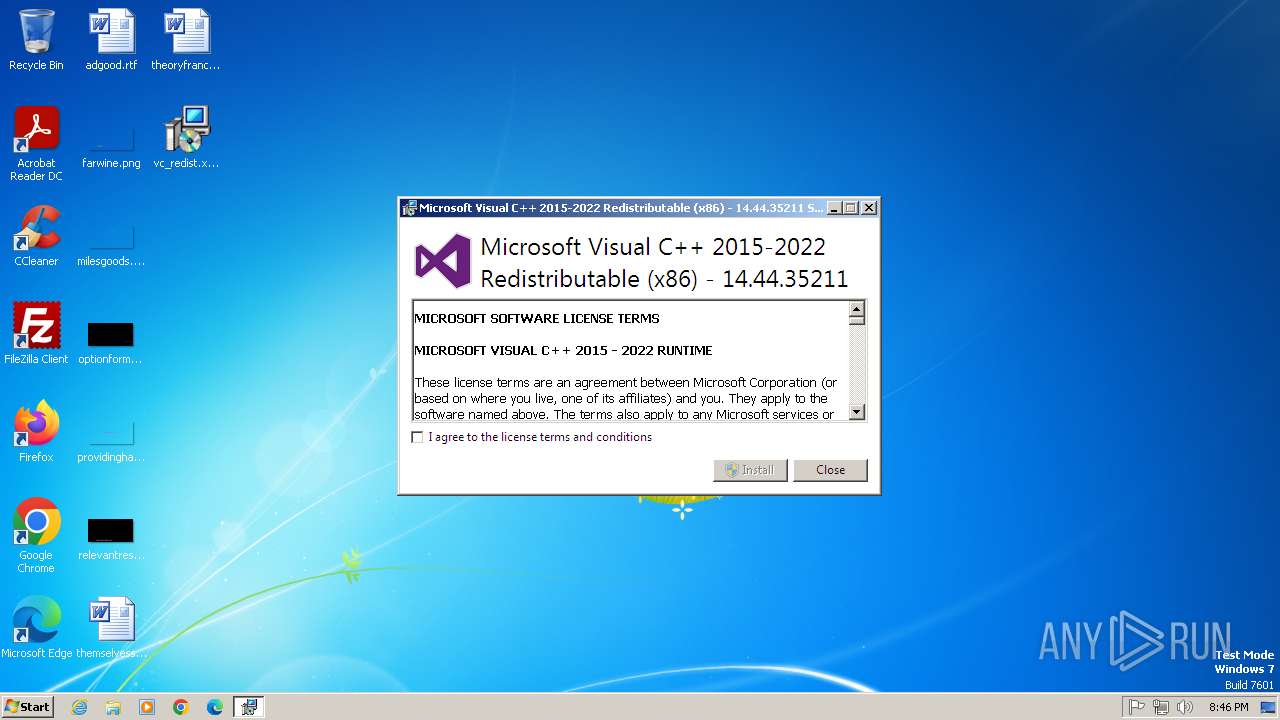
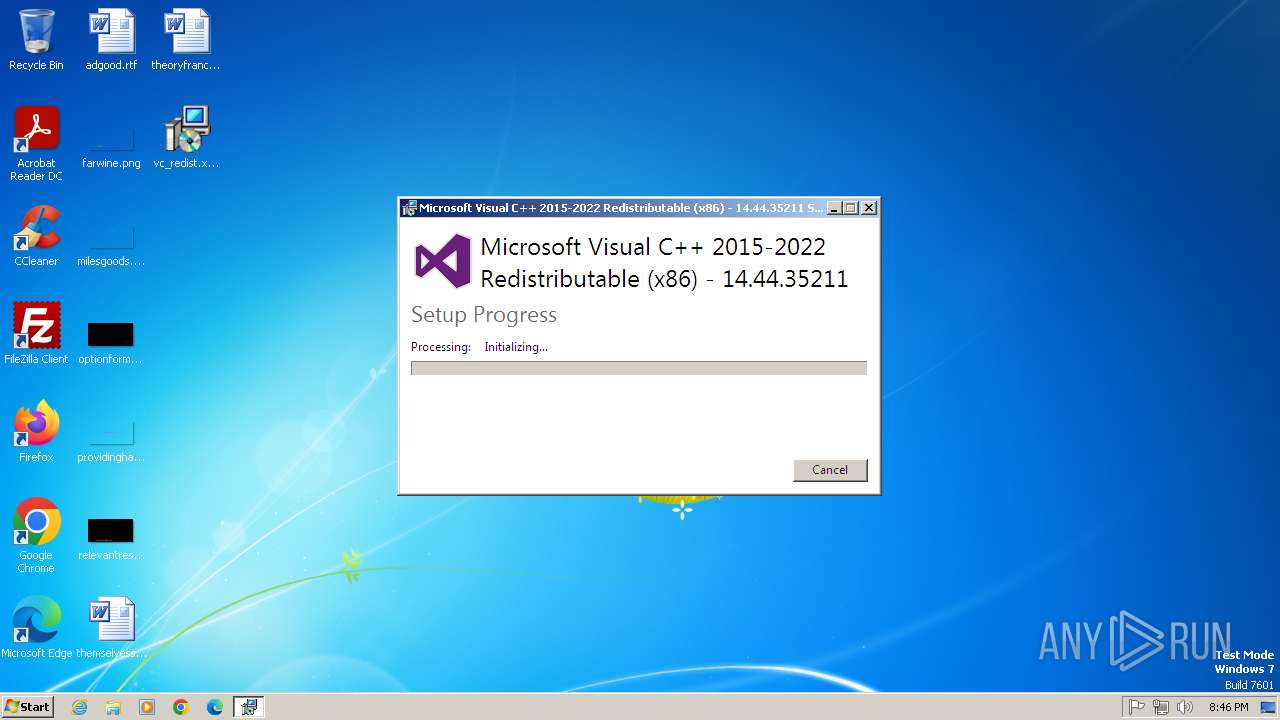
| FileDescription: | Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.44.35211 |
| FileVersion: | 14.44.35211.0 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | VC_redist.x86.exe |
| ProductName: | Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.44.35211 |
| ProductVersion: | 14.44.35211.0 |
Total processes
102
Monitored processes
13
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Users\admin\Desktop\vc_redist.x86.exe" | C:\Users\admin\Desktop\vc_redist.x86.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.44.35211 Exit code: 3010 Version: 14.44.35211.0 Modules
| |||||||||||||||
| 1448 | C:\Windows\system32\sipnotify.exe -LogonOrUnlock | C:\Windows\System32\sipnotify.exe | taskeng.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: sipnotify Exit code: 0 Version: 6.1.7602.20480 (win7sp1_ldr_escrow.191010-1716) Modules
| |||||||||||||||
| 1472 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /JPN /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2100 | "C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE" /SetPreload /KOR /Log | C:\Program Files\Common Files\microsoft shared\IME14\SHARED\IMEKLMG.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office IME 2010 Exit code: 1 Version: 14.0.4734.1000 Modules
| |||||||||||||||
| 2208 | "C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -burn.clean.room="C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -burn.filehandle.attached=152 -burn.filehandle.self=160 -uninstall -quiet -burn.related.upgrade -burn.ancestors={0b5169e3-39da-4313-808e-1f9c0407f3bf} -burn.filehandle.self=840 -burn.embedded BurnPipe.{6252A6BB-B820-4742-A426-4CB1766ACA6A} {C2C9BA95-1B62-49E4-ADA6-3A72C7C3EAE7} 3752 | C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 2356 | "C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -uninstall -quiet -burn.related.upgrade -burn.ancestors={0b5169e3-39da-4313-808e-1f9c0407f3bf} -burn.filehandle.self=840 -burn.embedded BurnPipe.{6252A6BB-B820-4742-A426-4CB1766ACA6A} {C2C9BA95-1B62-49E4-ADA6-3A72C7C3EAE7} 3752 | C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe | — | VC_redist.x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 2792 | C:\Windows\system32\DllHost.exe /Processid:{0DA7BFDF-C0A0-44EB-BE82-B7A82C4721DE} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2820 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3024 | "C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{24820034-B10A-42EE-AE58-FFA5BEE45FF1} {1001AF8B-00DE-4A81-8A1F-1A6961B84602} 2208 | C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
Total events
17 704
Read events
16 702
Write events
666
Delete events
336
Modification events
| (PID) Process: | (2820) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000D09DC78ED3FCDB01040B00009C0B0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2820) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000002A00CA8ED3FCDB01040B000040020000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2820) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000002A00CA8ED3FCDB01040B0000180F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2820) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C276C08ED3FCDB01040B000040020000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2820) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C276C08ED3FCDB01040B00009C0B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2820) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C276C08ED3FCDB01040B0000C40B0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2820) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C276C08ED3FCDB01040B0000180F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2820) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000763BC58ED3FCDB01040B0000C40B0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2820) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SwProvider_{b5946137-7b9f-4925-af80-51abd60b20d5} |
| Operation: | write | Name: | PROVIDER_BEGINPREPARE (Enter) |
Value: 4000000000000000642DA191D3FCDB01040B0000180F000001040000010000000000000000000000FEE4D7FAC354F34EA5843A0A6239B69B0000000000000000 | |||
| (PID) Process: | (2820) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SwProvider_{b5946137-7b9f-4925-af80-51abd60b20d5} |
| Operation: | write | Name: | PROVIDER_BEGINPREPARE (Leave) |
Value: 4000000000000000642DA191D3FCDB01040B0000180F000001040000000000000000000000000000FEE4D7FAC354F34EA5843A0A6239B69B0000000000000000 | |||
Executable files
65
Suspicious files
19
Text files
72
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3300 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{E39AC349-39AD-49B8-B239-73643B331B92}\.ba\wixstdba.dll | executable | |
MD5:F68F43F809840328F4E993A54B0D5E62 | SHA256:E921F69B9FB4B5AD4691809D06896C5F1D655AB75E0CE94A372319C243C56D4E | |||
| 3300 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{E39AC349-39AD-49B8-B239-73643B331B92}\.ba\thm.wxl | xml | |
MD5:FBFCBC4DACC566A3C426F43CE10907B6 | SHA256:70400F181D00E1769774FF36BCD8B1AB5FBC431418067D31B876D18CC04EF4CE | |||
| 3300 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{E39AC349-39AD-49B8-B239-73643B331B92}\.ba\1036\thm.wxl | xml | |
MD5:7B46AE8698459830A0F9116BC27DE7DF | SHA256:704DDF2E60C1F292BE95C7C79EE48FE8BA8534CEB7CCF9A9EA68B1AD788AE9D4 | |||
| 3300 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{E39AC349-39AD-49B8-B239-73643B331B92}\.ba\1036\license.rtf | text | |
MD5:A6E352E5804313CCDE3E4D5DDDDE122D | SHA256:5C13A65870D770D1642A4259EECB436257CA39016A0500F747BE9C79BE0C7009 | |||
| 3300 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{E39AC349-39AD-49B8-B239-73643B331B92}\.ba\1028\license.rtf | text | |
MD5:2B063D92663595DFE4781AE687A03D86 | SHA256:44C76290F7A2E45940E8338912FEB49BCF4E071CFA85D2D34762857743ACBC8D | |||
| 3300 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{E39AC349-39AD-49B8-B239-73643B331B92}\.ba\1029\thm.wxl | xml | |
MD5:16343005D29EC431891B02F048C7F581 | SHA256:07FB3EC174F25DFBE532D9D739234D9DFDA8E9D34F01FE660C5B4D56989FA779 | |||
| 3300 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{E39AC349-39AD-49B8-B239-73643B331B92}\.ba\1031\thm.wxl | xml | |
MD5:561F3F32DB2453647D1992D4D932E872 | SHA256:8E0DCA6E085744BFCBFF46F7DCBCFA6FBD722DFA52013EE8CEEAF682D7509581 | |||
| 3300 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{E39AC349-39AD-49B8-B239-73643B331B92}\.ba\1029\license.rtf | text | |
MD5:E7DC9CA9474A13FA4529D91BCD2AB8CC | SHA256:503C433DCDE2F3A9E7D388A5FF2B0612E7D8F90F5188D5B2B60228DB33044FDE | |||
| 3300 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{E39AC349-39AD-49B8-B239-73643B331B92}\.ba\1040\thm.wxl | xml | |
MD5:D90BC60FA15299925986A52861B8E5D5 | SHA256:0C57F40CC2091554307AA8A7C35DD38E4596E9513E9EFAE00AC30498EF4E9BC2 | |||
| 3300 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{E39AC349-39AD-49B8-B239-73643B331B92}\.ba\1040\license.rtf | text | |
MD5:BC58AD6ABB16B982AEBADC121B37E706 | SHA256:70ECF23C03B66A2B18E173332586AFA8F00F91E02A80628F4F9CB2521E27F6AC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
11
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1448 | sipnotify.exe | HEAD | 503 | 104.102.43.250:80 | http://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2JgkA?v=133978636547650000 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1104 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1448 | sipnotify.exe | 104.102.43.250:80 | query.prod.cms.rt.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
query.prod.cms.rt.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|