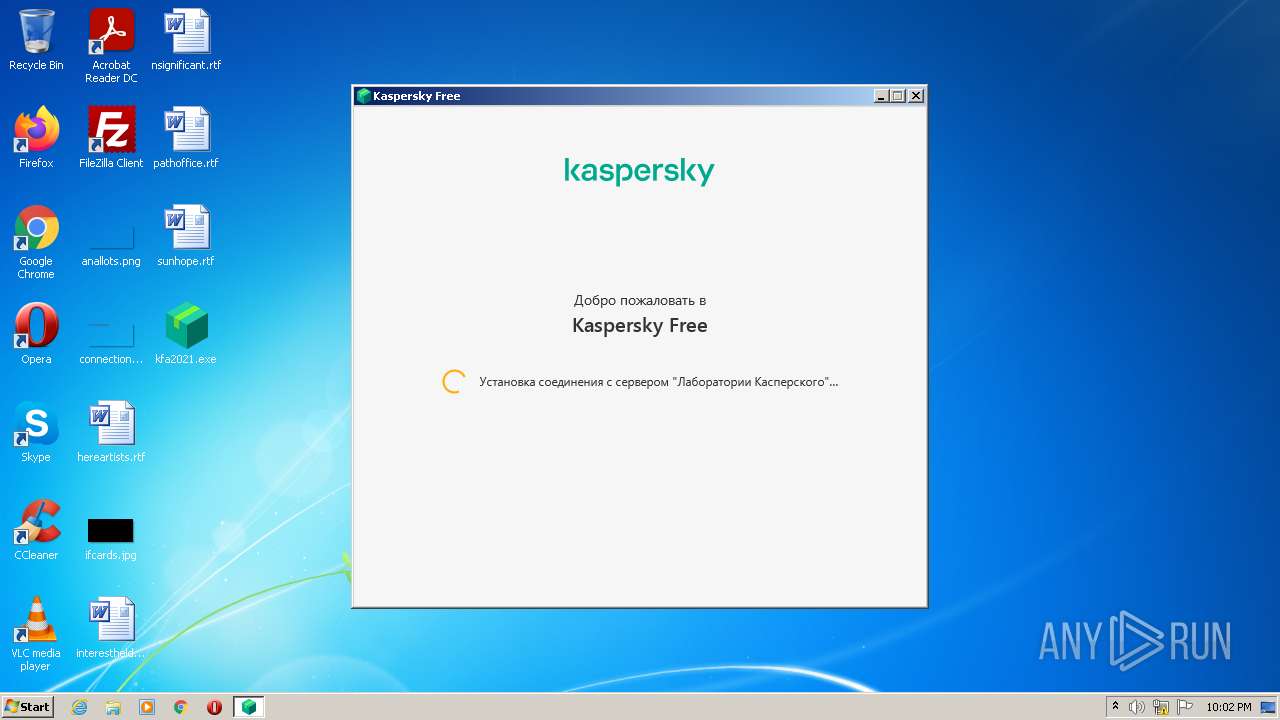
| File name: | kfa2021.exe |
| Full analysis: | https://app.any.run/tasks/95f7d3f0-5bb1-48a7-85b9-809d1bda5361 |
| Verdict: | Malicious activity |
| Analysis date: | February 24, 2022, 22:02:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C7C566334C90DFA3BD6F4284C149185D |
| SHA1: | 25630307A52E3DC28DA2573953780A7A5238E73A |
| SHA256: | 0C0962D03EBCC2BBC32EFAACEB38A7242BD6374E5FC3F21C550D09011CA4E8B2 |
| SSDEEP: | 49152:FlINc3mvkxq9HnIQVeYCpwrHdLYp7U3oxc2pqxWwEb9ojnr4LEe8xBj9M4O1wl0R:LINc3vIHnIwCMH2pI4C2pijnr4LEVnB+ |
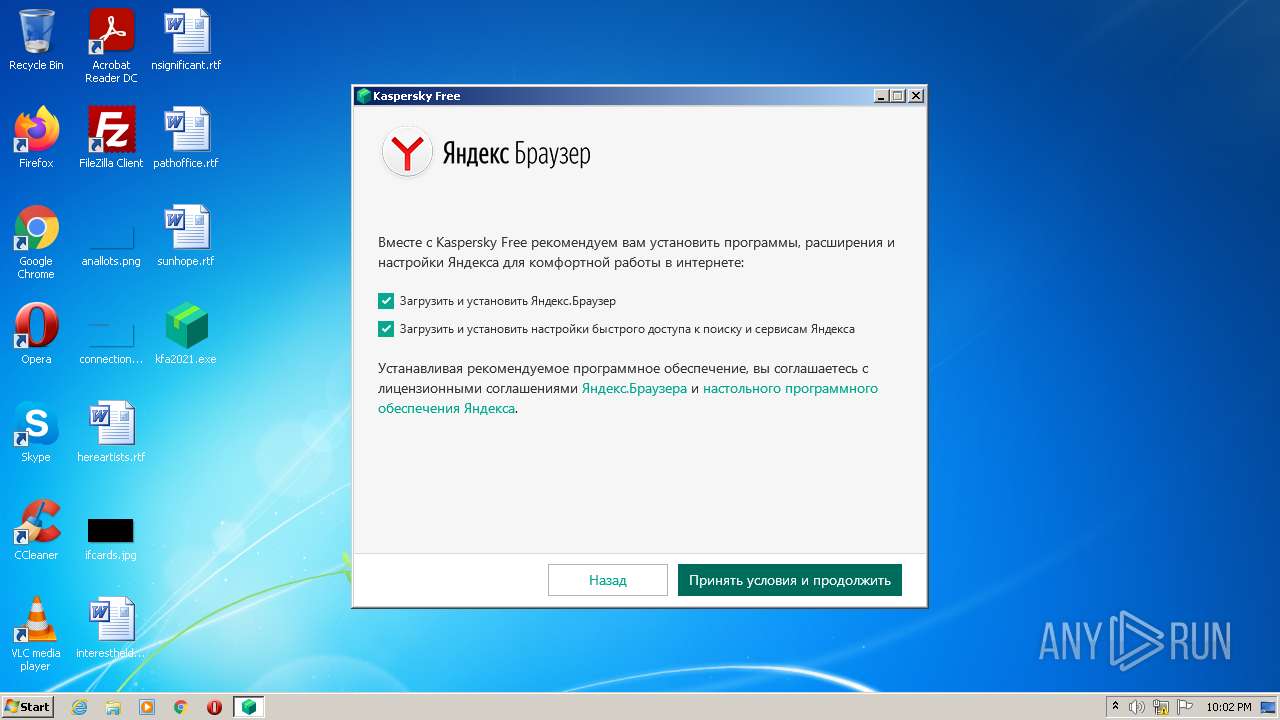
MALICIOUS
Drops executable file immediately after starts
- kfa2021.exe (PID: 3228)
- kfa2021.exe (PID: 1424)
Loads dropped or rewritten executable
- kfa2021.exe (PID: 3228)
- kfa2021.exe (PID: 1424)
- TEST_WPF.EXE (PID: 2096)
Application was dropped or rewritten from another process
- TEST_WPF.EXE (PID: 2096)
SUSPICIOUS
Drops a file with too old compile date
- kfa2021.exe (PID: 3228)
- kfa2021.exe (PID: 1424)
Reads the computer name
- kfa2021.exe (PID: 3228)
- kfa2021.exe (PID: 1424)
- TEST_WPF.EXE (PID: 2096)
Executable content was dropped or overwritten
- kfa2021.exe (PID: 3228)
- kfa2021.exe (PID: 1424)
Checks supported languages
- kfa2021.exe (PID: 3228)
- kfa2021.exe (PID: 1424)
- TEST_WPF.EXE (PID: 2096)
Reads Microsoft Outlook installation path
- kfa2021.exe (PID: 3228)
- kfa2021.exe (PID: 1424)
Drops a file that was compiled in debug mode
- kfa2021.exe (PID: 3228)
- kfa2021.exe (PID: 1424)
Application launched itself
- kfa2021.exe (PID: 3228)
Creates files in the user directory
- kfa2021.exe (PID: 3228)
Creates files in the program directory
- kfa2021.exe (PID: 1424)
INFO
Reads settings of System Certificates
- kfa2021.exe (PID: 3228)
- kfa2021.exe (PID: 1424)
Checks Windows Trust Settings
- kfa2021.exe (PID: 3228)
- kfa2021.exe (PID: 1424)
Reads the computer name
- WISPTIS.EXE (PID: 1284)
Checks supported languages
- WISPTIS.EXE (PID: 1284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| OriginalFileName: | Setup.exe |
|---|---|
| InternalName: | Setup |
| ProductVersion: | 21.2.16.590 |
| ProductName: | Kaspersky Free |
| LegalTrademarks: | Зарегистрированные товарные знаки и знаки обслуживания являются собственностью их правообладателей |
| LegalCopyright: | © 2020 АО "Лаборатория Касперского" |
| FileVersion: | 21.2.16.590 |
| FileDescription: | Kaspersky Free [21.2.16.590.0.2.0] |
| CompanyName: | Лаборатория Касперского |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 21.2.16.590 |
| FileVersionNumber: | 21.2.16.590 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x23ca |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2512896 |
| CodeSize: | 297984 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2021:09:01 10:23:07+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Sep-2021 08:23:07 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Лаборатория Касперского |
| FileDescription: | Kaspersky Free [21.2.16.590.0.2.0] |
| FileVersion: | 21.2.16.590 |
| LegalCopyright: | © 2020 АО "Лаборатория Касперского" |
| LegalTrademarks: | Зарегистрированные товарные знаки и знаки обслуживания являются собственностью их правообладателей |
| ProductName: | Kaspersky Free |
| ProductVersion: | 21.2.16.590 |
| InternalName: | Setup |
| OriginalFilename: | Setup.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Sep-2021 08:23:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00048AFE | 0x00048C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6739 |
.rdata | 0x0004A000 | 0x000166D8 | 0x00016800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22777 |
.data | 0x00061000 | 0x00005C38 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.40147 |
.rsrc | 0x00067000 | 0x0024840C | 0x00248600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.68329 |
.reloc | 0x002B0000 | 0x00004454 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.54909 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.27937 | 1606 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.03205 | 67624 | Latin 1 / Western European | Process Default Language | RT_ICON |
3 | 3.34315 | 16936 | Latin 1 / Western European | Process Default Language | RT_ICON |
4 | 3.49595 | 9640 | Latin 1 / Western European | Process Default Language | RT_ICON |
5 | 2.89003 | 104 | Latin 1 / Western European | Process Default Language | RT_GROUP_ICON |
6 | 3.94447 | 2440 | Latin 1 / Western European | Process Default Language | RT_ICON |
7 | 4.26631 | 1128 | Latin 1 / Western European | Process Default Language | RT_ICON |
GETSI.Z | 7.99838 | 110893 | Latin 1 / Western European | UNKNOWN | SZIP |
SETUP.DLL.Z | 7.99986 | 1896451 | Latin 1 / Western European | UNKNOWN | SZIP |
SUSPENDEDBYPASS.MSI.Z | 7.96893 | 8957 | Latin 1 / Western European | UNKNOWN | SZIP |
Imports
KERNEL32.dll |
RPCRT4.dll (delay-loaded) |
Total processes
46
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1284 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | TEST_WPF.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 24 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1424 | "C:\Users\admin\Desktop\kfa2021.exe" /-elevated= | C:\Users\admin\Desktop\kfa2021.exe | kfa2021.exe | ||||||||||||
User: admin Company: ??????????? ??????????? Integrity Level: HIGH Description: Kaspersky Free [21.2.16.590.0.2.0] Exit code: 0 Version: 21.2.16.590 Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Temp\725A3C14-95BD-11EC-BE1B-12A9866C77DE\TEST_WPF.EXE" "C:\Users\admin\AppData\Local\Temp\21C3A527DB59CE11EBB1219A68C677ED\setup.dll" | C:\Users\admin\AppData\Local\Temp\725A3C14-95BD-11EC-BE1B-12A9866C77DE\TEST_WPF.EXE | — | kfa2021.exe | |||||||||||
User: admin Integrity Level: HIGH Description: test_wpf Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3040 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | TEST_WPF.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3228 | "C:\Users\admin\Desktop\kfa2021.exe" | C:\Users\admin\Desktop\kfa2021.exe | Explorer.EXE | ||||||||||||
User: admin Company: ??????????? ??????????? Integrity Level: MEDIUM Description: Kaspersky Free [21.2.16.590.0.2.0] Exit code: 0 Version: 21.2.16.590 Modules
| |||||||||||||||
Total events
11 674
Read events
11 397
Write events
272
Delete events
5
Modification events
| (PID) Process: | (3228) kfa2021.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLab\IEOverride\Main |
| Operation: | write | Name: | Enable Browser Extensions |
Value: no | |||
| (PID) Process: | (3228) kfa2021.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLab\IEOverride\Main |
| Operation: | write | Name: | UseSWRender |
Value: 1 | |||
| (PID) Process: | (3228) kfa2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3228) kfa2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3228) kfa2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3228) kfa2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3228) kfa2021.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLabSetup\Setup21.2.16.590.0.2.0 |
| Operation: | write | Name: | TrashFiles |
Value: C:\ProgramData\Kaspersky Lab Setup Files\KFA21.2.16.590.0.2.0
| |||
| (PID) Process: | (3228) kfa2021.exe | Key: | HKEY_CURRENT_USER\Software\KasperskyLabSetup\Setup21.2.16.590.0.2.0 |
| Operation: | write | Name: | TrashFiles |
Value: C:\ProgramData\Kaspersky Lab Setup Files\KFA21.2.16.590.0.2.0
C:\ProgramData\Kaspersky Lab Setup Files
| |||
| (PID) Process: | (3228) kfa2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3228) kfa2021.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
3
Suspicious files
3
Text files
37
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3228 | kfa2021.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_B514E3306E9B5CC22C1D3DB90570477A | binary | |
MD5:— | SHA256:— | |||
| 3228 | kfa2021.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3228 | kfa2021.exe | C:\Users\admin\AppData\Local\Temp\67E72D9F-95BD-11EC-BE1B-12A9866C77DE\check_new_version.html | html | |
MD5:— | SHA256:— | |||
| 3228 | kfa2021.exe | C:\Users\admin\AppData\Local\Temp\67E72D9F-95BD-11EC-BE1B-12A9866C77DE\kis-style.css | text | |
MD5:98D7269182AE679FC12FE0964741EE74 | SHA256:52787DA054F3DAF09EC9494565735EA3A14428556AE6129110CAA0D8975F38EB | |||
| 3228 | kfa2021.exe | C:\Users\admin\AppData\Local\Temp\67E72D9F-95BD-11EC-BE1B-12A9866C77DE\ksn_page.html | html | |
MD5:— | SHA256:— | |||
| 3228 | kfa2021.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_B514E3306E9B5CC22C1D3DB90570477A | der | |
MD5:— | SHA256:— | |||
| 3228 | kfa2021.exe | C:\Users\admin\AppData\Local\Temp\E9D27E76DB59CE11EBB1219A68C677ED\setup.dll | executable | |
MD5:— | SHA256:— | |||
| 3228 | kfa2021.exe | C:\Users\admin\AppData\Local\Temp\67E72D9F-95BD-11EC-BE1B-12A9866C77DE\print.png | image | |
MD5:20A2383C3AC20C88FD1A923DD9083FD6 | SHA256:364542744A99FA8BD55D53372A0E96CE7F7C4D0EF7A0D32699BFE9D0BC25BF76 | |||
| 3228 | kfa2021.exe | C:\Users\admin\AppData\Local\Temp\67E72D9F-95BD-11EC-BE1B-12A9866C77DE\kis-script.js | text | |
MD5:026425CCBF4417EEFA444285707132EF | SHA256:97E5F342227EA23C27C1B660F111847FCDD9D7B23C1D248C733A36F983FD7F04 | |||
| 3228 | kfa2021.exe | C:\Users\admin\AppData\Local\Temp\67E72D9F-95BD-11EC-BE1B-12A9866C77DE\jquery.custom_select.min.js | text | |
MD5:D2C620C462B75696EEA1FB22FB23602A | SHA256:DD678D32073078552E0E2C35EED78F16CC8D6E8662D4734518561A1B183F775C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3228 | kfa2021.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6f6f6d234061d742 | US | compressed | 4.70 Kb | whitelisted |
3228 | kfa2021.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3228 | kfa2021.exe | 195.122.169.10:443 | dm.s.kaspersky-labs.com | Level 3 Communications, Inc. | GB | suspicious |
3228 | kfa2021.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
3228 | kfa2021.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1424 | kfa2021.exe | 195.122.169.10:443 | dm.s.kaspersky-labs.com | Level 3 Communications, Inc. | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dm.s.kaspersky-labs.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |