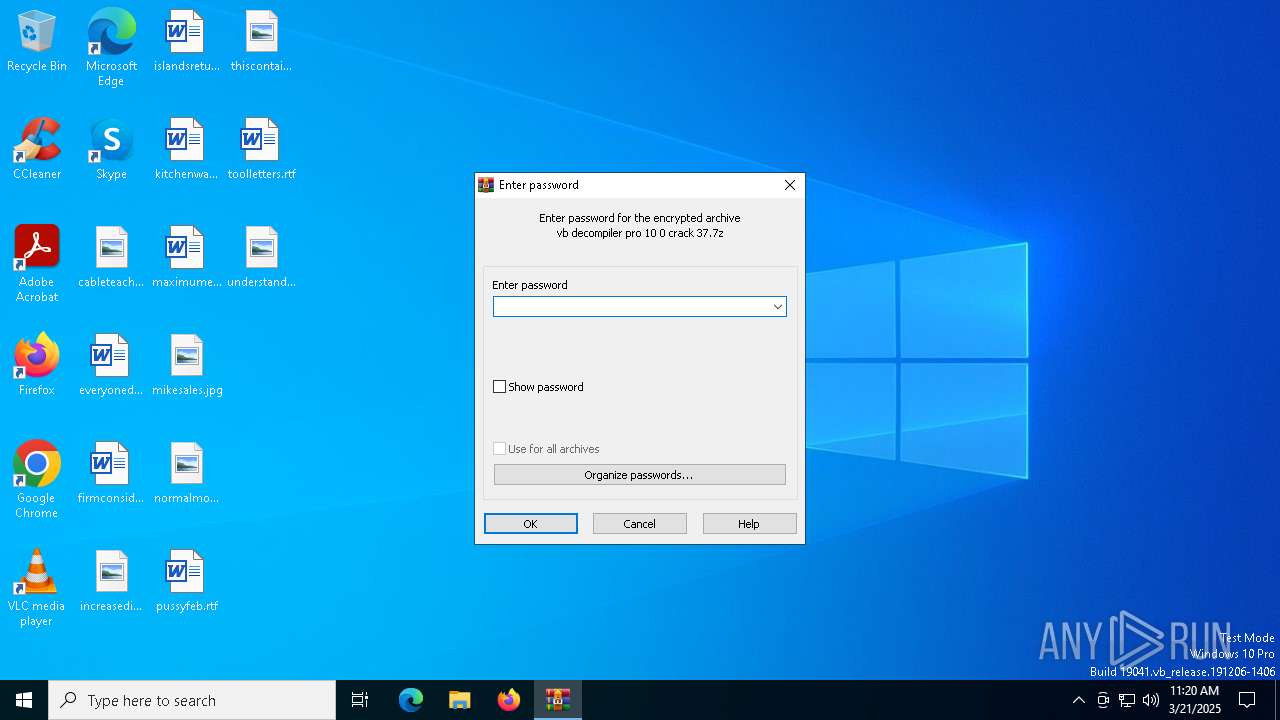
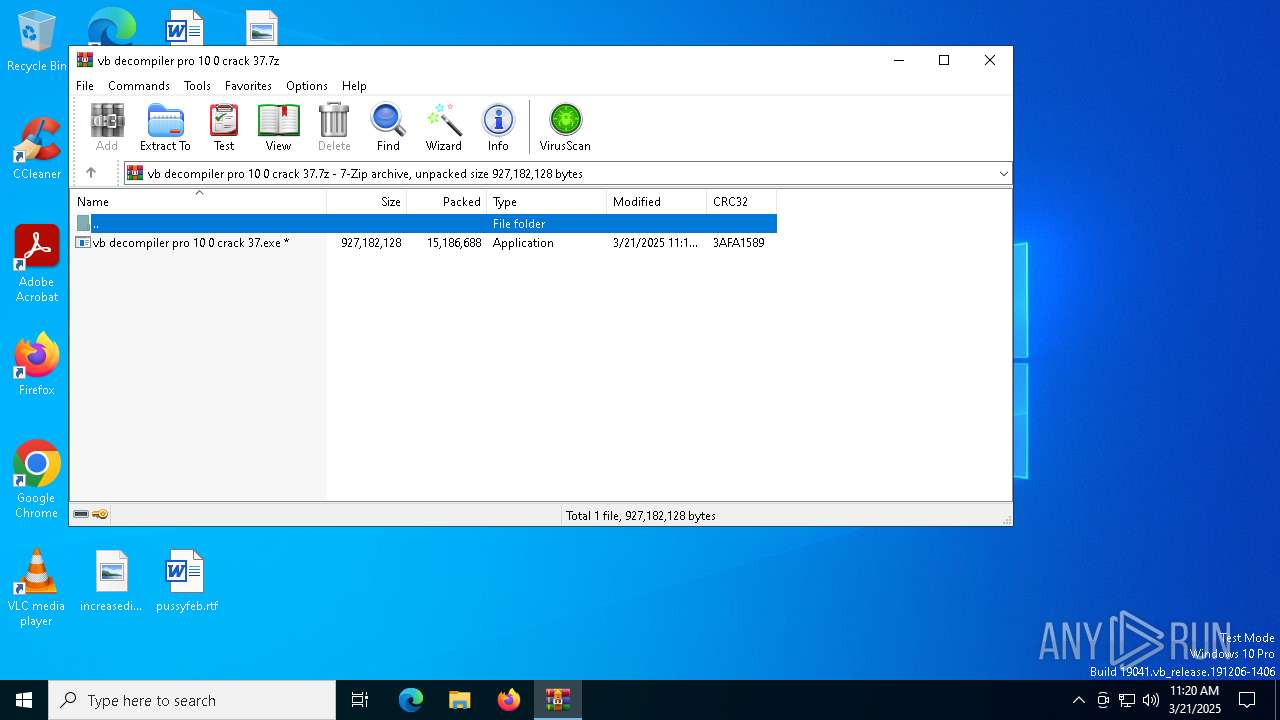
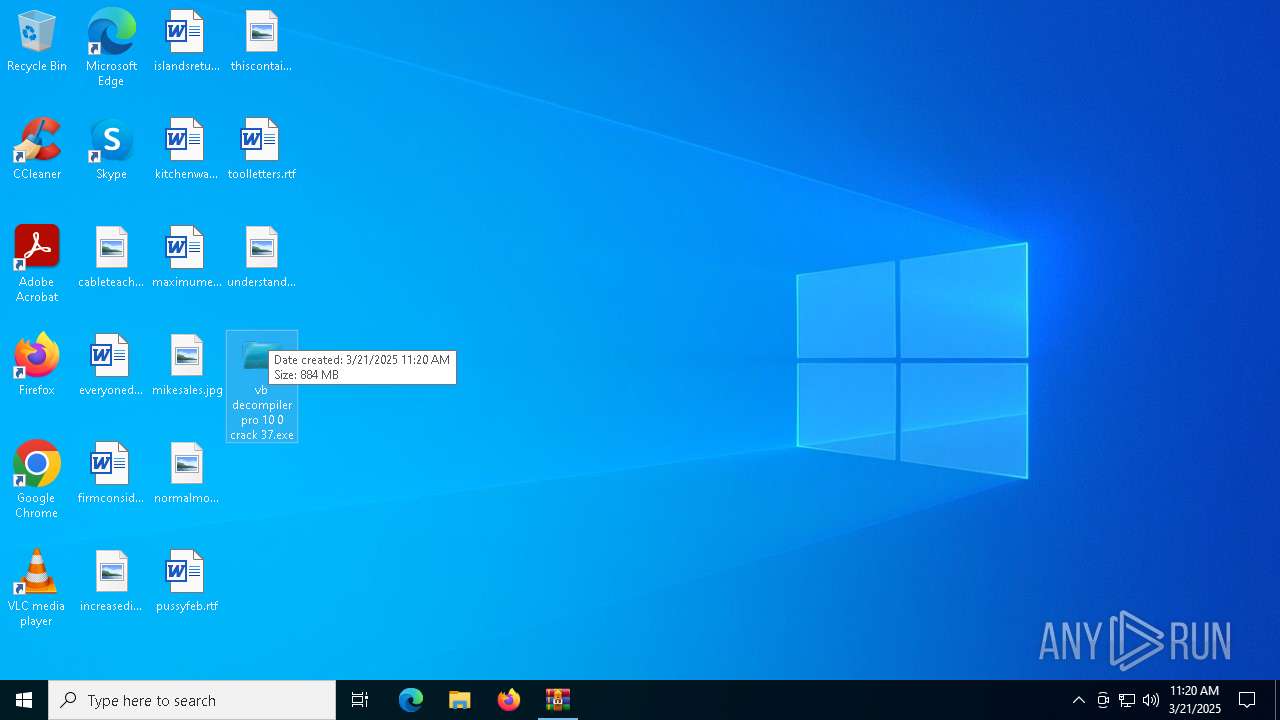
| File name: | vb decompiler pro 10 0 crack 37.7z |
| Full analysis: | https://app.any.run/tasks/f9471efd-7380-4f68-988f-2e4747bf9c30 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2025, 11:19:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 7AD148C425738CB26B4C9FC22DE597C2 |
| SHA1: | 63C372EDEDAF861867808F6364AAC3E984CAE528 |
| SHA256: | 0BEB2B50ABD4D1A951D380A085C9B46E0FD55A414A13AD3445E2F7D2285C26F8 |
| SSDEEP: | 196608:9yGf45DdT0Sd8cR5qYS2TrjSlieNCbdYOQ:9E/ASdN1zSl1NMdK |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executing commands from a ".bat" file
- vb decompiler pro 10 0 crack 37.exe (PID: 5608)
Starts CMD.EXE for commands execution
- vb decompiler pro 10 0 crack 37.exe (PID: 5608)
- cmd.exe (PID: 4696)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4696)
Get information on the list of running processes
- cmd.exe (PID: 4696)
Reads security settings of Internet Explorer
- vb decompiler pro 10 0 crack 37.exe (PID: 5608)
Application launched itself
- cmd.exe (PID: 4696)
Starts the AutoIt3 executable file
- cmd.exe (PID: 4696)
The executable file from the user directory is run by the CMD process
- Comment.com (PID: 7680)
Starts application with an unusual extension
- cmd.exe (PID: 4696)
INFO
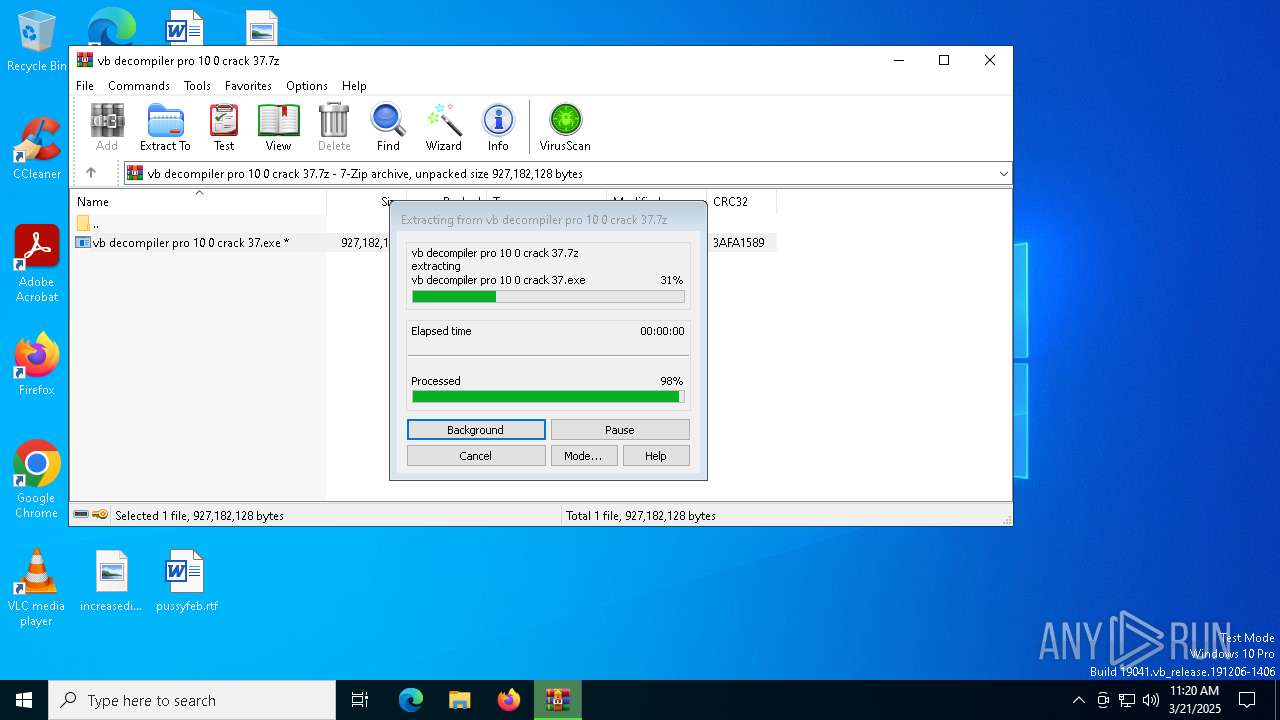
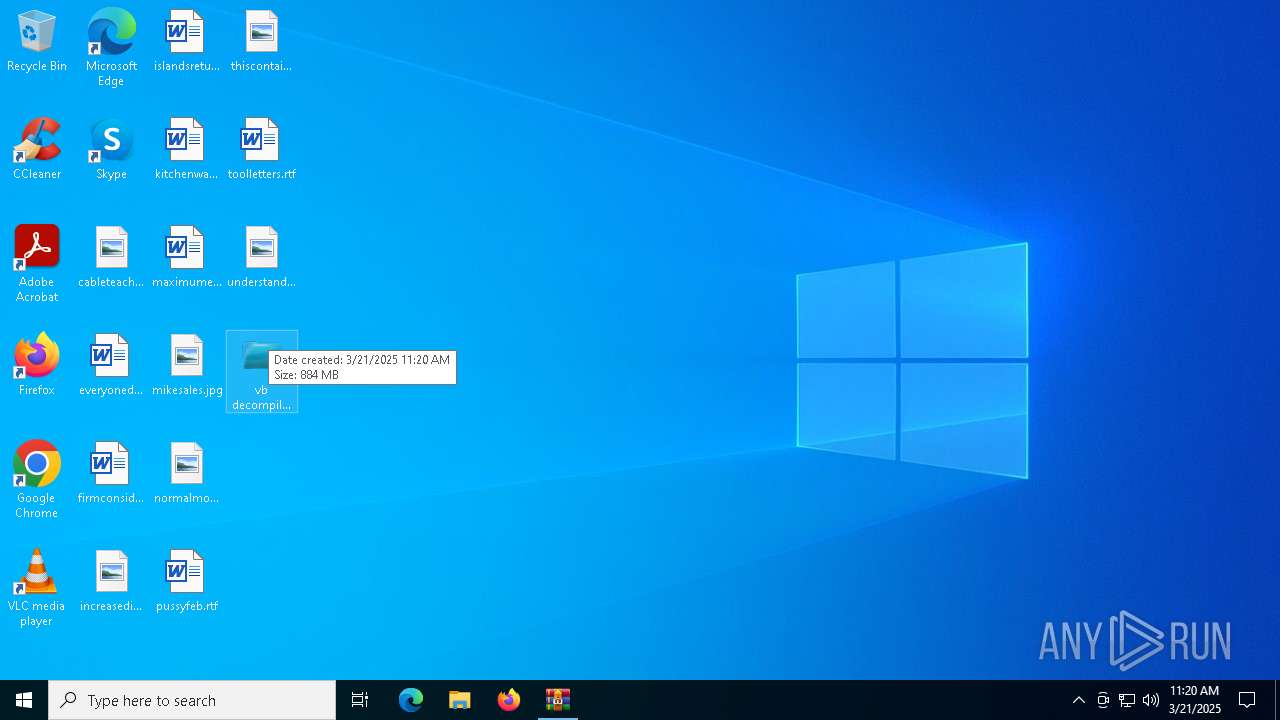
Manual execution by a user
- vb decompiler pro 10 0 crack 37.exe (PID: 5608)
Reads the computer name
- vb decompiler pro 10 0 crack 37.exe (PID: 5608)
- extrac32.exe (PID: 7280)
- Comment.com (PID: 7680)
Create files in a temporary directory
- vb decompiler pro 10 0 crack 37.exe (PID: 5608)
- extrac32.exe (PID: 7280)
Creates a new folder
- cmd.exe (PID: 7260)
Checks supported languages
- extrac32.exe (PID: 7280)
- Comment.com (PID: 7680)
Reads mouse settings
- Comment.com (PID: 7680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
146
Monitored processes
17
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | cmd /c copy /b ..\Definition.mil + ..\Along.mil + ..\Tribe.mil + ..\Attachments.mil + ..\Fascinating.mil + ..\Rebates.mil + ..\Acm.mil O | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4696 | "C:\WINDOWS\system32\CMD.exe" /c copy Mercedes.mil Mercedes.mil.bat & Mercedes.mil.bat | C:\Windows\SysWOW64\cmd.exe | — | vb decompiler pro 10 0 crack 37.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
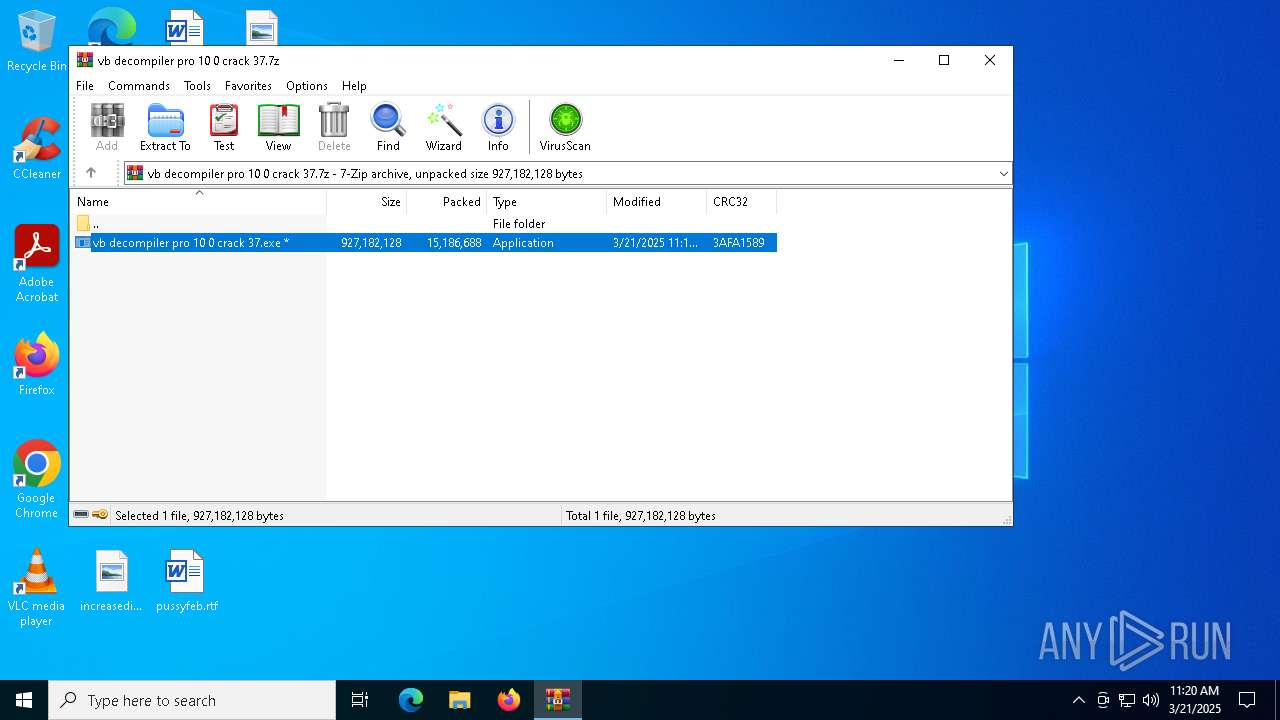
| 5608 | "C:\Users\admin\Desktop\vb decompiler pro 10 0 crack 37.exe" | C:\Users\admin\Desktop\vb decompiler pro 10 0 crack 37.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7192 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7196 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7236 | findstr "SophosHealth bdservicehost AvastUI AVGUI nsWscSvc ekrn" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7260 | cmd /c md 561377 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 994
Read events
2 969
Write events
12
Delete events
13
Modification events
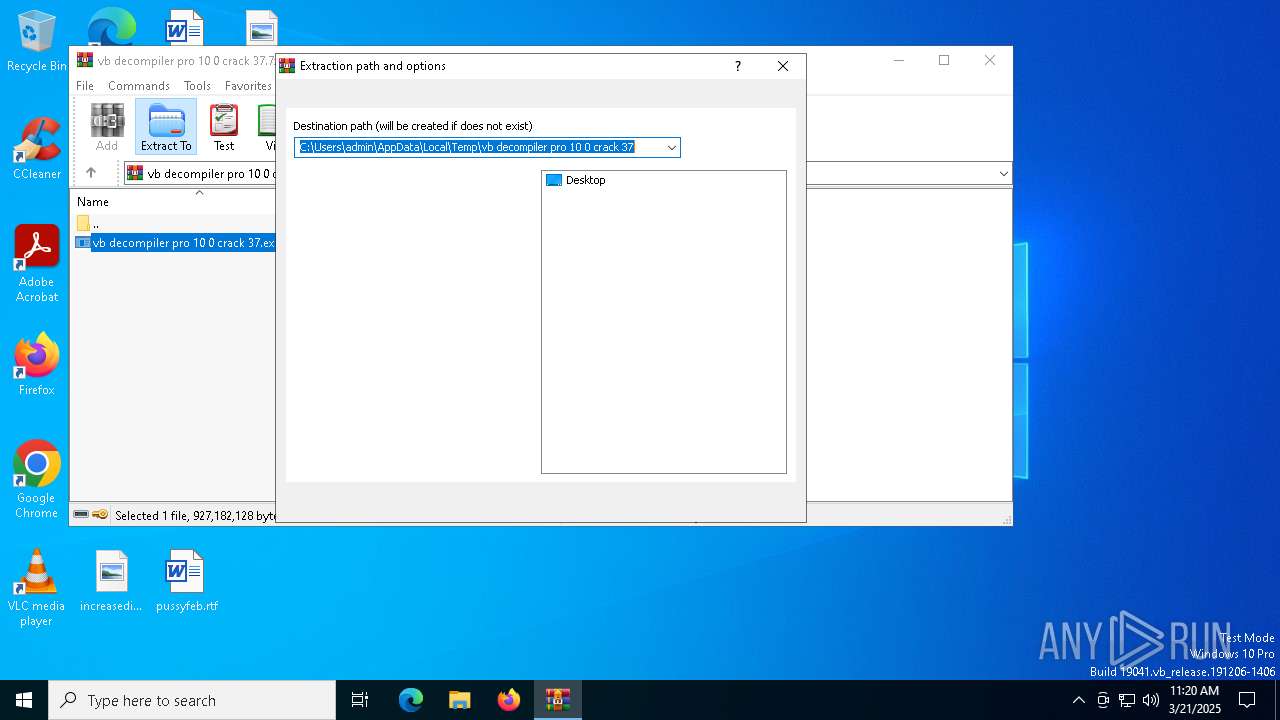
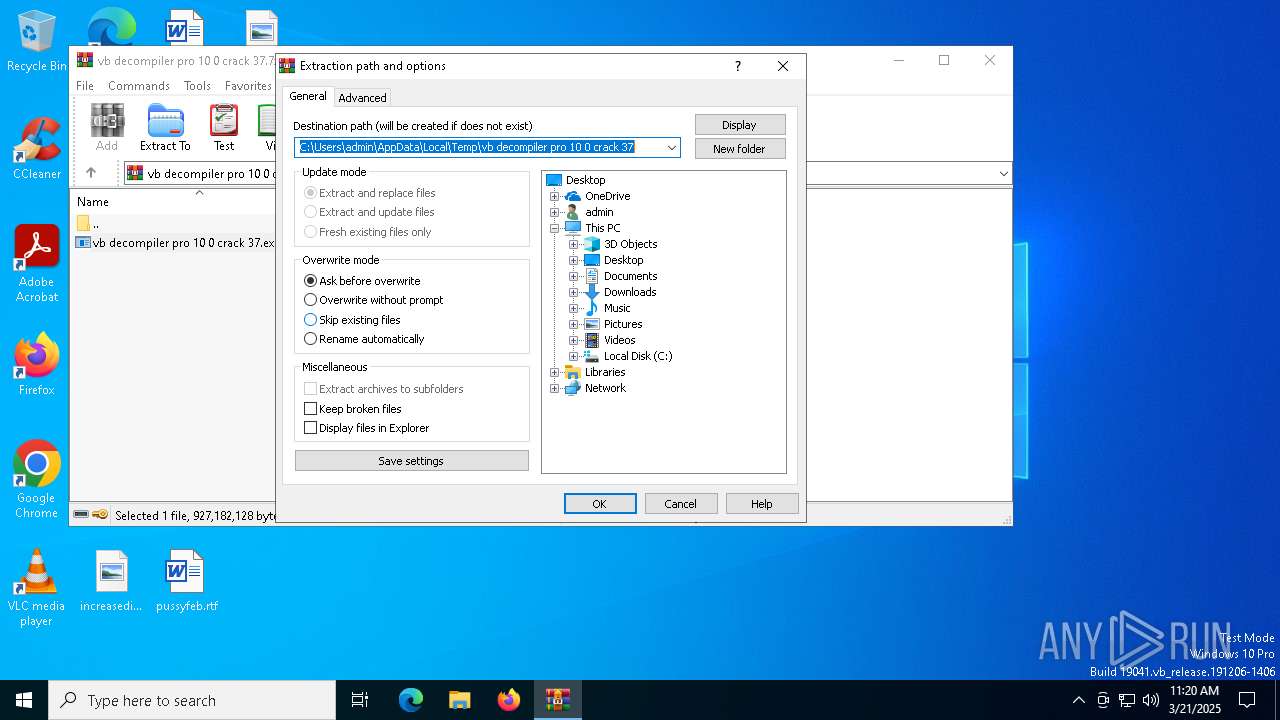
| (PID) Process: | (7572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\vb decompiler pro 10 0 crack 37.7z | |||
| (PID) Process: | (7572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
Executable files
0
Suspicious files
20
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5608 | vb decompiler pro 10 0 crack 37.exe | C:\Users\admin\AppData\Local\Temp\Acm.mil | binary | |
MD5:54299AB2DE5E9B80DE179ACB59E8A4E2 | SHA256:31520AAB3BFE96435FA344A55184C261B6253BF0F903153C08D2EB39A28735DE | |||
| 5608 | vb decompiler pro 10 0 crack 37.exe | C:\Users\admin\AppData\Local\Temp\Tribe.mil | binary | |
MD5:3734F5A1835E6E0351081A210E4A3999 | SHA256:4A27560D60288704539462FA3812FEB929C64075896AE6C27FB619C70F58D435 | |||
| 5608 | vb decompiler pro 10 0 crack 37.exe | C:\Users\admin\AppData\Local\Temp\Attachments.mil | binary | |
MD5:075F2A5D810FBB0C61D7531A9876C1B1 | SHA256:61D427C401663EF757D5F1CAF2B5CD9791500FD56F869F9BFBD2B1085BAE7BD4 | |||
| 5608 | vb decompiler pro 10 0 crack 37.exe | C:\Users\admin\AppData\Local\Temp\Definition.mil | binary | |
MD5:7B0D85A35AFBC8D240E8336144C92771 | SHA256:544217B2E247A6DD6157EC3E6735A731A1C33868E39368F65868F73B4464A109 | |||
| 7280 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Patterns | binary | |
MD5:74B43CC93DC33BA015239646E45C30AA | SHA256:56F3618E0C40AF1D9EC80ED28619B08450D8FE07D0CFCF8AD412033F00EB8B3C | |||
| 7280 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Alabama | binary | |
MD5:AFB3FA6EA26D6BAF76C6CD6930F16F6F | SHA256:66540E495C35A3E6BBE9BCAE5B679E040400588C93F78CA376B935FD0C6FD5C1 | |||
| 7280 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Flame | binary | |
MD5:3E991BD6EE2A89DEA97E030BC885425B | SHA256:57E88357BDB0B75397E8E65E7867A72D67611AA1BA452C0A2008B78518976B94 | |||
| 7280 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Cio | binary | |
MD5:2379E76B41AA0A0A66300A28D9ABA6FA | SHA256:A6CEE2ECFF989DF0309918F050D9040B3E65D99A60C65B654F9050BA5C61C72E | |||
| 4696 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Mercedes.mil.bat | text | |
MD5:171D4839FE04E509BA4599AC111E8D43 | SHA256:E02ED08BEB82C2CDF8599ECE198EF85CC2221966FEFB1982F38D9952BC951C2B | |||
| 7280 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Homework | binary | |
MD5:758A8B6B36CF08E78999422AD0C15D5B | SHA256:DCDEC828077E14EE9FD2A3250C0A5217F36E48655BFCA4B4647B1DBA27D6FB29 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
26
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5404 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5404 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
7708 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |