| File name: | lordgarson@aol.com(勒索).exe |
| Full analysis: | https://app.any.run/tasks/bdf609a2-5a98-43fc-ba73-2a3fe19d112c |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2021, 01:14:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | ED887CC2269C6412DE672153452CD780 |
| SHA1: | 801D14F79ABC0E103992613AE4E816FF58BE018F |
| SHA256: | 0BE6C958225E804FD64A921F196CD9868540748DFEBE37D3FC5468786A0B9F5A |
| SSDEEP: | 24576:+l6x6UpvNWbJdlJI/Gx305UELNv9tJ+4BQE+OdrOAIxvTwOYZlGfd7xYy:jxRUJwGm5UKQVU1cflOy |
MALICIOUS
Deletes shadow copies
- cmd.exe (PID: 1212)
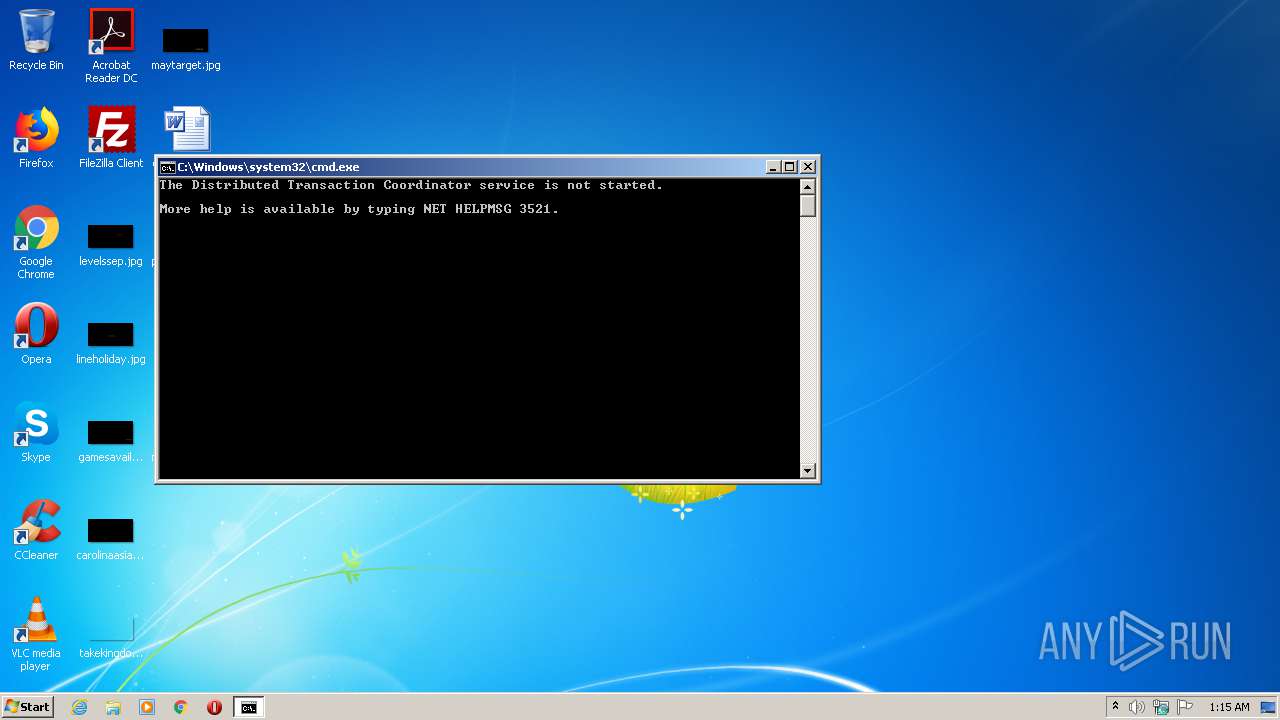
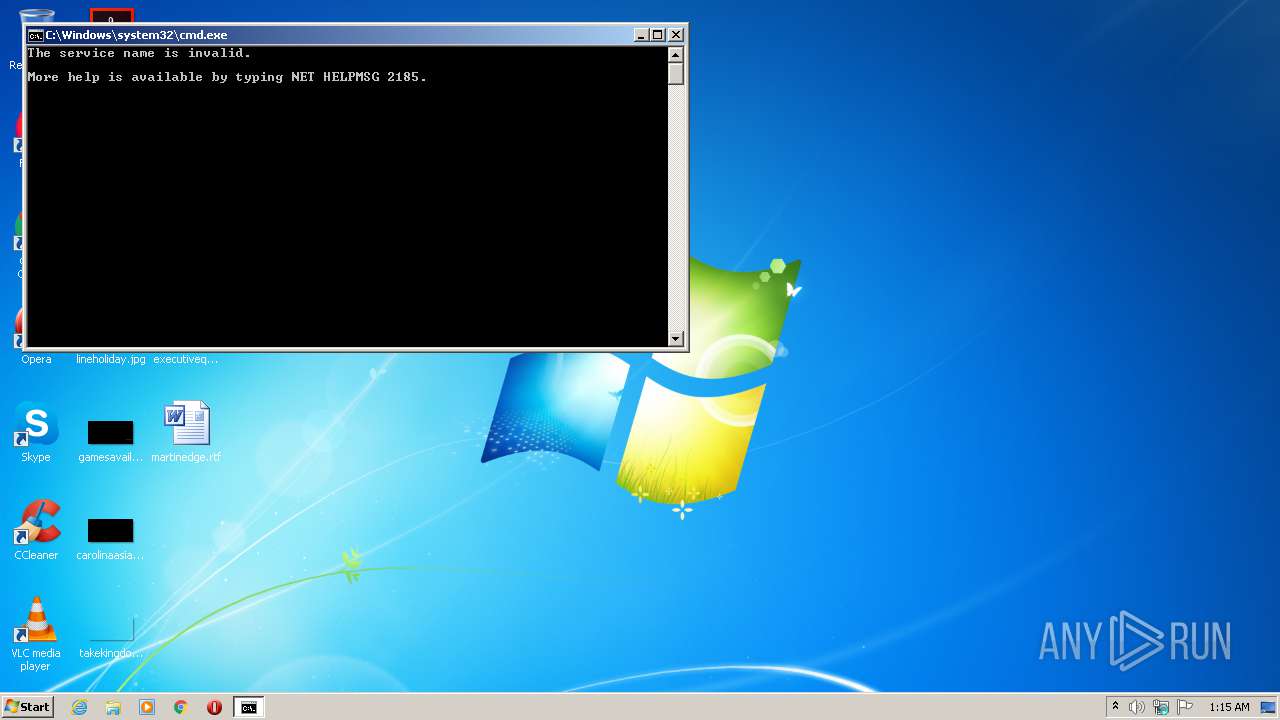
Starts NET.EXE for service management
- cmd.exe (PID: 1756)
- cmd.exe (PID: 2080)
- cmd.exe (PID: 312)
- cmd.exe (PID: 1956)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 4084)
- cmd.exe (PID: 1836)
- cmd.exe (PID: 2292)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 3736)
Turns off the firewall via NETSH.EXE
- cmd.exe (PID: 1592)
SUSPICIOUS
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2448)
- cmd.exe (PID: 1592)
Starts CMD.EXE for commands execution
- lordgarson@aol.com(勒索).exe (PID: 3040)
Creates files in the program directory
- lordgarson@aol.com(勒索).exe (PID: 3040)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:12:23 13:49:47+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 1027072 |
| InitializedDataSize: | 325120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xafa75 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 23-Dec-2020 12:49:47 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 23-Dec-2020 12:49:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000FAA48 | 0x000FAC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64065 |
.rdata | 0x000FC000 | 0x00037A60 | 0x00037C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.30695 |
.data | 0x00134000 | 0x000097EC | 0x00006E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93559 |
.rsrc | 0x0013E000 | 0x000001E0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.71768 |
.reloc | 0x0013F000 | 0x0000DF24 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.59373 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
KERNEL32.dll |
Normaliz.dll |
WLDAP32.dll |
WS2_32.dll |
Total processes
85
Monitored processes
35
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | C:\Windows\system32\cmd.exe /c net stop MSSQLSERVER | C:\Windows\system32\cmd.exe | — | lordgarson@aol.com(勒索).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 956 | net stop MSSQL$CONTOSO1 | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | net stop MSSQLSERVER | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1212 | C:\Windows\system32\cmd.exe /c wbadmin delete catalog -quiet | C:\Windows\system32\cmd.exe | — | lordgarson@aol.com(勒索).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294967294 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1496 | bcdedit /set {default} recoveryenabled no | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1592 | C:\Windows\system32\cmd.exe /c netsh advfirewall set currentprofile state off | C:\Windows\system32\cmd.exe | — | lordgarson@aol.com(勒索).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1616 | C:\Windows\system32\cmd.exe /c net stop SQLBrowser | C:\Windows\system32\cmd.exe | — | lordgarson@aol.com(勒索).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1756 | C:\Windows\system32\cmd.exe /c net stop SQLWriter | C:\Windows\system32\cmd.exe | — | lordgarson@aol.com(勒索).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1836 | C:\Windows\system32\cmd.exe /c net stop SQLSERVERAGENT | C:\Windows\system32\cmd.exe | — | lordgarson@aol.com(勒索).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1956 | C:\Windows\system32\cmd.exe /c net stop MSDTC | C:\Windows\system32\cmd.exe | — | lordgarson@aol.com(勒索).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
205
Read events
100
Write events
105
Delete events
0
Modification events
| (PID) Process: | (2700) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2700) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (2700) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (2700) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (2700) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (2700) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (2700) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (2700) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (2700) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (2700) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3040 | lordgarson@aol.com(勒索).exe | C:\ProgramData\IDk.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3040 | lordgarson@aol.com(勒索).exe | POST | — | 94.130.46.250:8080 | http://94.130.46.250:8080/1614CEEEC50A9336EBF690886CAA747D6811C45D37086A3FA7B11C9E83926C6C | DE | — | — | malicious |
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3040 | lordgarson@aol.com(勒索).exe | 104.23.98.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
3040 | lordgarson@aol.com(勒索).exe | 78.47.82.133:80 | www.sfml-dev.org | Hetzner Online GmbH | DE | suspicious |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3040 | lordgarson@aol.com(勒索).exe | 94.130.46.250:8080 | — | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sfml-dev.org |
| suspicious |
dns.msftncsi.com |
| shared |
pastebin.com |
| malicious |
ocsp.digicert.com |
| whitelisted |