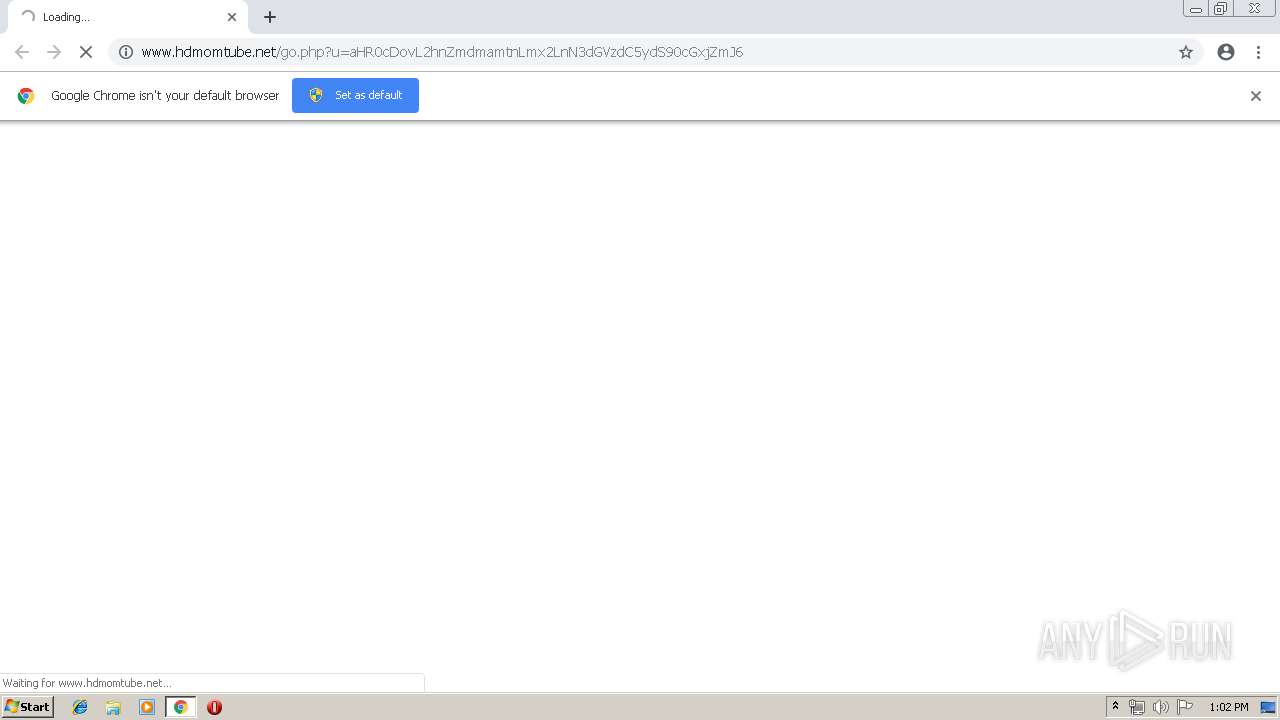
| URL: | http://www.hdmomtube.net/go.php?u=aHR0cDovL2hnZmdmamtnLmx2LnN3dGVzdC5ydS90cGxjZmJ6 |
| Full analysis: | https://app.any.run/tasks/24dbfc76-d2e3-43d5-a7a4-c80f32455b60 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 12:02:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 45632DDC6F9FDBA2D68DBB4C6A6FCCAE |
| SHA1: | 58F87F3C77B19E0E2C6CFC2AD7A056EA8F4F38C9 |
| SHA256: | 0BDFAC0EFDA496913E76E98B5C3D06CF64468504CE6C5B62CC74AC5983C06872 |
| SSDEEP: | 3:N1KJS4EdQgIR0LV6W+I5B6IRLmVlrB27sidA:Cc4/RyV1UsLMji6 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
19
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9339774103985802545 --mojo-platform-channel-handle=4648 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11076113240247848259 --mojo-platform-channel-handle=4432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5128431287912637146 --mojo-platform-channel-handle=5032 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=14846457759106036303 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14846457759106036303 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=66203899630775436 --mojo-platform-channel-handle=988 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1923491324929673401 --mojo-platform-channel-handle=4916 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12117607906725720461 --mojo-platform-channel-handle=4572 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --service-pipe-token=15540309883557182829 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15540309883557182829 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12874967464117114997 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12874967464117114997 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3392 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,15379422907693368005,9165559896744267503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10508026501533320008 --mojo-platform-channel-handle=4660 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
149
Read events
90
Write events
55
Delete events
4
Modification events
| (PID) Process: | (3624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4024) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3624-13205419357572750 |
Value: 259 | |||
| (PID) Process: | (3624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3624) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3624) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
51
Text files
138
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f83d95c4-d131-4416-aa73-a5e425c33f4d.tmp | — | |
MD5:— | SHA256:— | |||
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
40
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
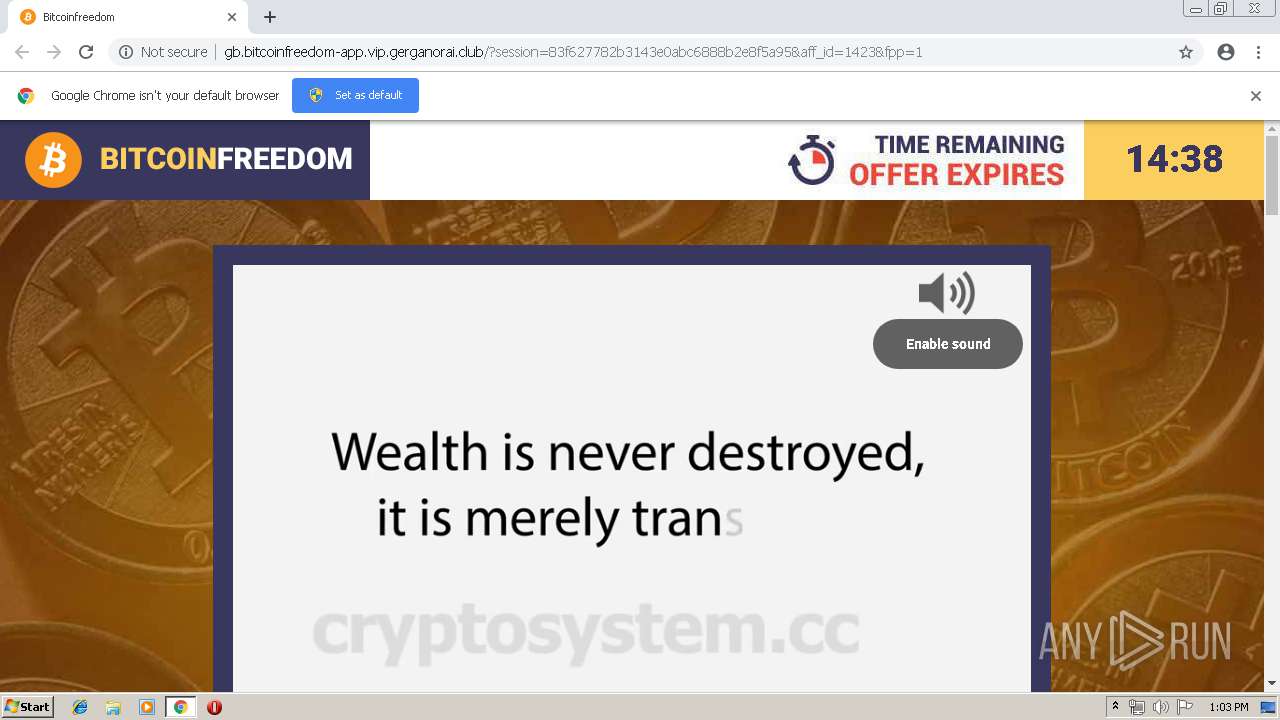
3624 | chrome.exe | GET | 302 | 92.53.96.217:80 | http://cl40002.tmweb.ru/new_pp | RU | — | — | suspicious |
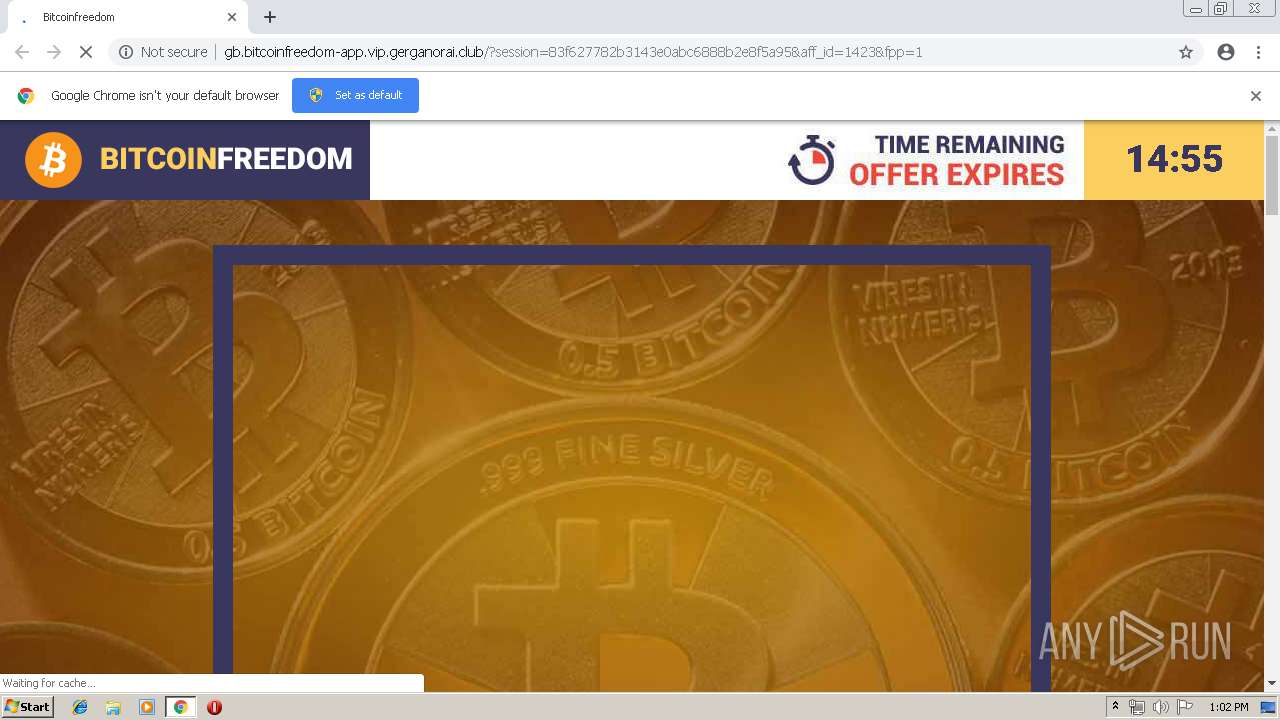
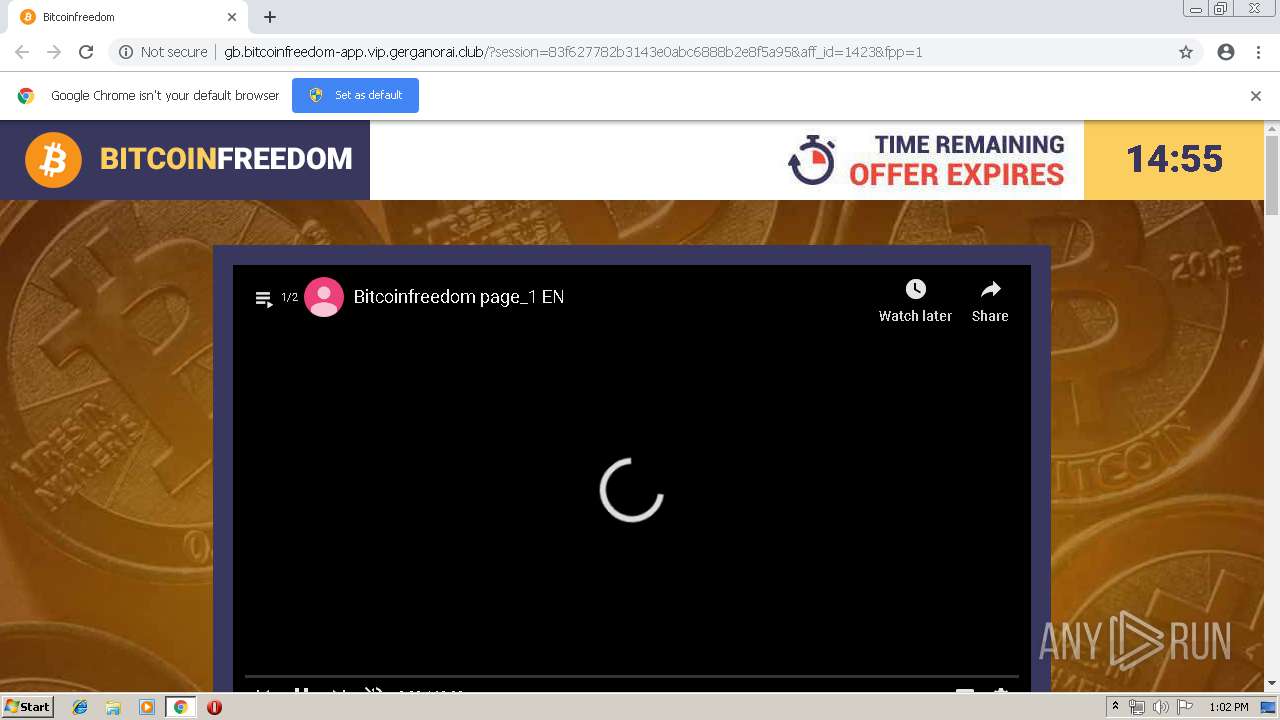
3624 | chrome.exe | GET | 302 | 104.18.48.221:80 | http://vip.gerganorai.club/tracker?offer_id=3441&aff_id=1423&u=0:50,1140:50&gl=off | US | — | — | suspicious |
3624 | chrome.exe | GET | 301 | 104.27.168.12:80 | http://www.hdmomtube.net/go.php?u=aHR0cDovL2hnZmdmamtnLmx2LnN3dGVzdC5ydS90cGxjZmJ6 | US | — | — | shared |
3624 | chrome.exe | GET | 301 | 77.222.56.187:80 | http://hgfgfjkg.lv.swtest.ru/tplcfbz | RU | html | 350 b | malicious |
3624 | chrome.exe | GET | 200 | 104.18.49.221:80 | http://gb.bitcoinfreedom-app.vip.gerganorai.club/img/logoText.png | US | image | 2.32 Kb | suspicious |
3624 | chrome.exe | GET | 200 | 104.18.49.221:80 | http://gb.bitcoinfreedom-app.vip.gerganorai.club/css/bootstrap.min.css | US | text | 19.2 Kb | suspicious |
3624 | chrome.exe | GET | 200 | 104.18.49.221:80 | http://gb.bitcoinfreedom-app.vip.gerganorai.club/css/include_fonts.css | US | text | 120 b | suspicious |
3624 | chrome.exe | GET | 200 | 104.18.49.221:80 | http://gb.bitcoinfreedom-app.vip.gerganorai.club/?session=83f627782b3143e0abc6888b2e8f5a95&aff_id=1423&fpp=1 | US | html | 5.80 Kb | suspicious |
3624 | chrome.exe | GET | 200 | 104.18.49.221:80 | http://gb.bitcoinfreedom-app.vip.gerganorai.club/css/css1.css | US | text | 5.42 Kb | suspicious |
3624 | chrome.exe | GET | 200 | 104.18.49.221:80 | http://gb.bitcoinfreedom-app.vip.gerganorai.club/css/style_pop_up.css | US | text | 1001 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3624 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 104.18.48.221:80 | vip.gerganorai.club | Cloudflare Inc | US | shared |
3624 | chrome.exe | 104.18.49.221:80 | vip.gerganorai.club | Cloudflare Inc | US | shared |
3624 | chrome.exe | 109.206.172.153:443 | geo1.investmen.pw | Serverel Inc. | NL | suspicious |
3624 | chrome.exe | 216.58.207.72:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 172.217.22.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 216.58.210.14:443 | s.ytimg.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 74.125.71.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3624 | chrome.exe | 35.186.228.179:443 | google-analytics.bi.owox.com | Google Inc. | US | whitelisted |
3624 | chrome.exe | 216.58.207.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hdmomtube.net |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
hgfgfjkg.lv.swtest.ru |
| malicious |
cl40002.tmweb.ru |
| suspicious |
vip.gerganorai.club |
| suspicious |
gb.bitcoinfreedom-app.vip.gerganorai.club |
| suspicious |
geo1.investmen.pw |
| suspicious |
www.googletagmanager.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |