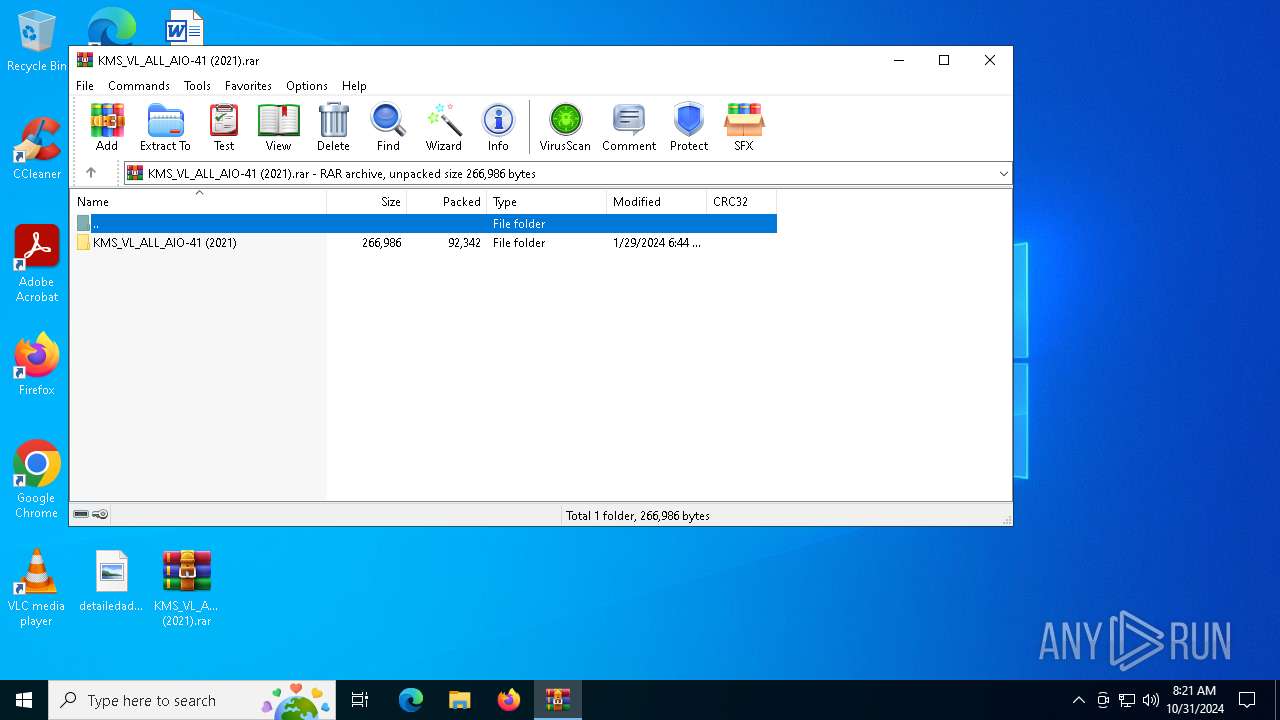
| File name: | KMS_VL_ALL_AIO-41 (2021).rar |
| Full analysis: | https://app.any.run/tasks/8350f143-3cb9-454f-b692-511e8ae825c5 |
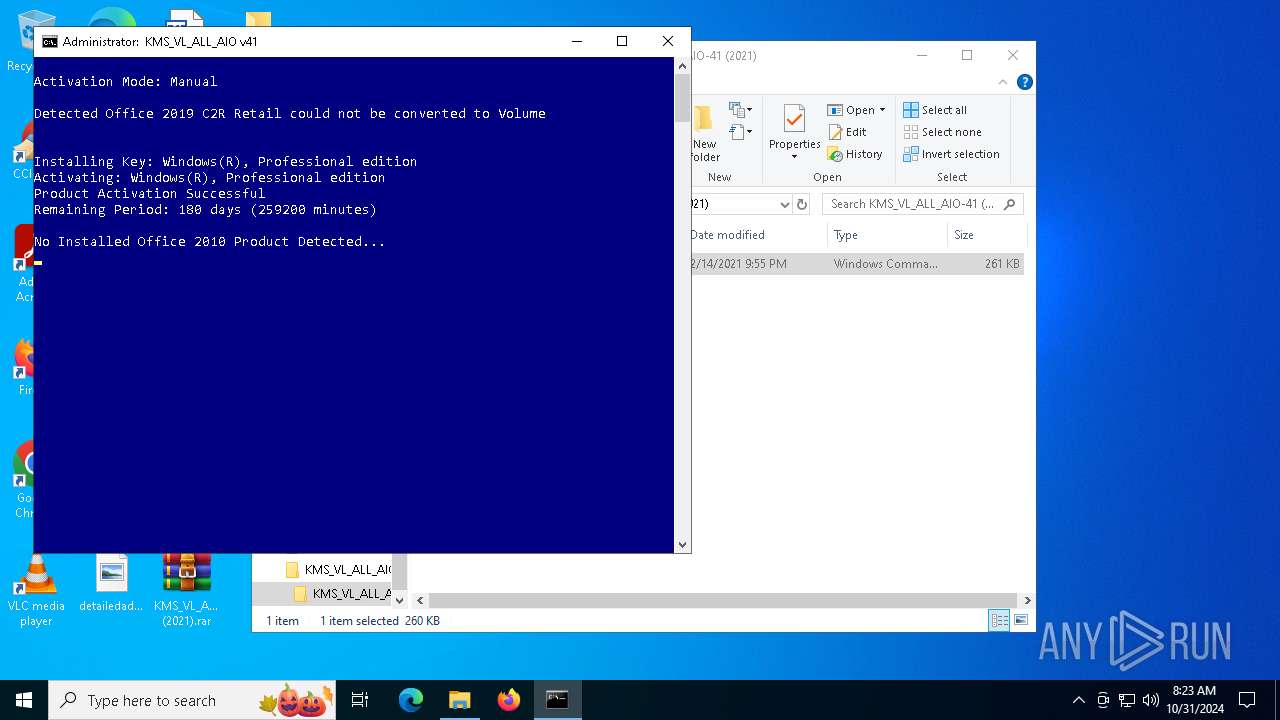
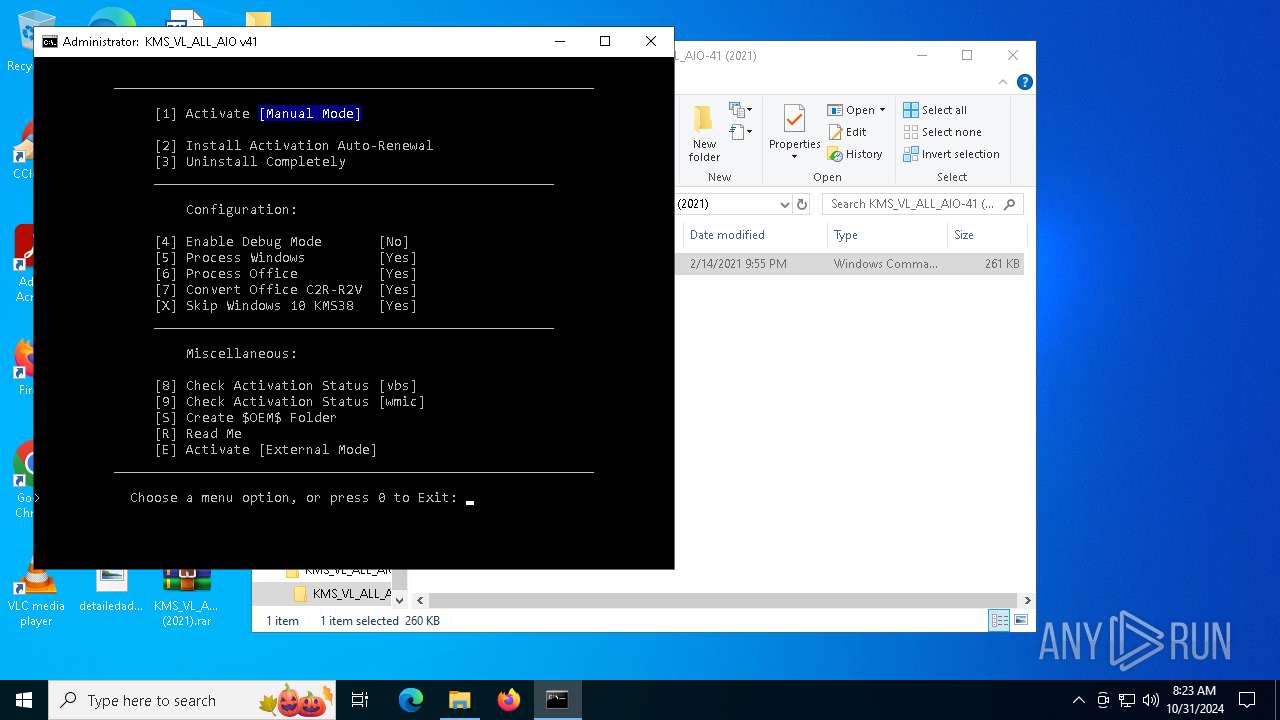
| Verdict: | Malicious activity |
| Analysis date: | October 31, 2024, 08:21:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 53CE8DDCE4450134F5B64535ADF183D5 |
| SHA1: | A8611913871AC825BA1D9F05FB135BCC15DD47D2 |
| SHA256: | 0BDA17749DA9011CD7BF14C019C085F408F3FF1B3C200ECBCEFFD6B7C467A556 |
| SSDEEP: | 3072:yZTVlu7zqQM0pSZOZGI4L3Ng8OD49iSP/GcF+aKGuYUF8d9:yZTVlunqQM0EZt9LiIiSP/Gc1KGuYFr |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6568)
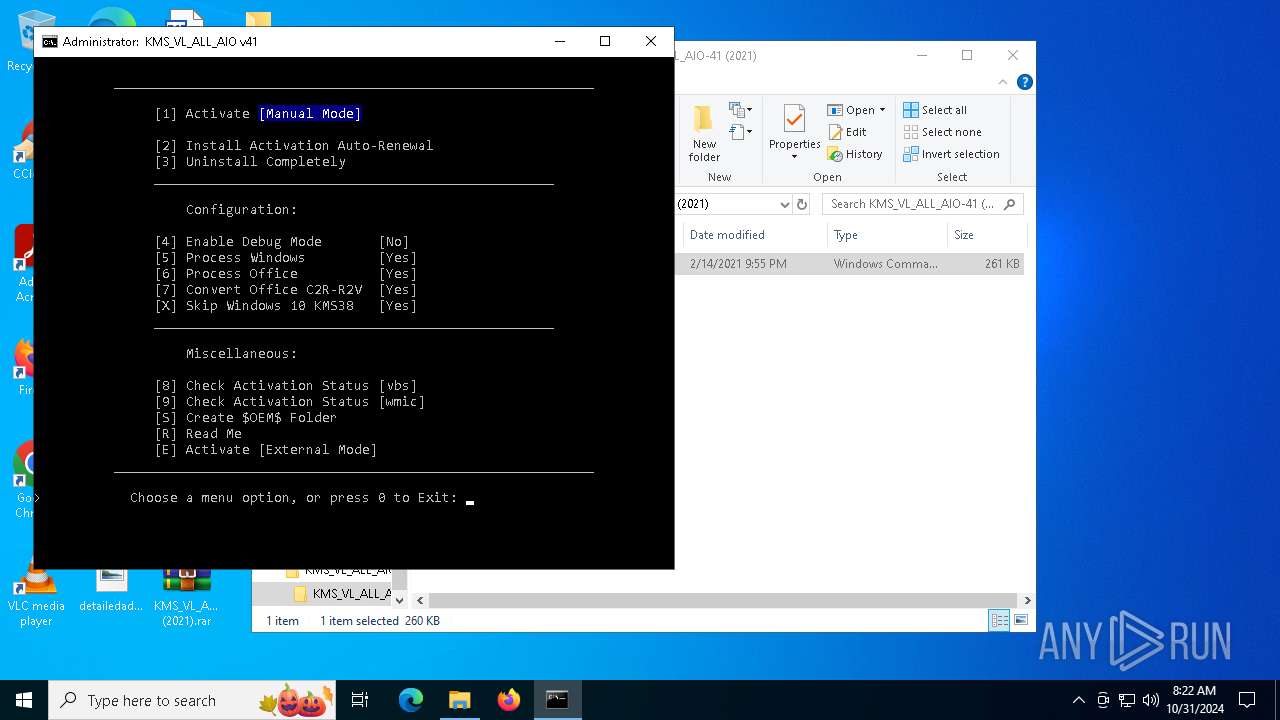
Starts NET.EXE for service management
- cmd.exe (PID: 1788)
- net.exe (PID: 1588)
- net.exe (PID: 6628)
- net.exe (PID: 6204)
Uses WMIC.EXE to add exclusions to the Windows Defender
- cmd.exe (PID: 1788)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 1788)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1788)
Starts SC.EXE for service management
- cmd.exe (PID: 1788)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1788)
Executes script without checking the security policy
- powershell.exe (PID: 5596)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1788)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1788)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 1788)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 1788)
CSC.EXE is used to compile C# code
- csc.exe (PID: 1180)
Executable content was dropped or overwritten
- csc.exe (PID: 1180)
- powershell.exe (PID: 5596)
Hides command output
- cmd.exe (PID: 5512)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 1332)
- cmd.exe (PID: 5048)
- cmd.exe (PID: 1028)
- cmd.exe (PID: 5328)
- cmd.exe (PID: 2648)
- cmd.exe (PID: 6904)
- cmd.exe (PID: 6416)
- cmd.exe (PID: 4060)
- cmd.exe (PID: 7056)
- cmd.exe (PID: 2724)
- cmd.exe (PID: 6892)
- cmd.exe (PID: 3532)
- cmd.exe (PID: 5356)
- cmd.exe (PID: 2648)
- cmd.exe (PID: 6800)
- cmd.exe (PID: 2776)
- cmd.exe (PID: 6900)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5512)
- cmd.exe (PID: 1788)
- cmd.exe (PID: 2000)
- cmd.exe (PID: 1068)
- cmd.exe (PID: 5172)
- cmd.exe (PID: 5516)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 5356)
- cmd.exe (PID: 944)
- cmd.exe (PID: 1788)
The process executes VB scripts
- cmd.exe (PID: 1788)
Lists all scheduled tasks
- schtasks.exe (PID: 3832)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1788)
INFO
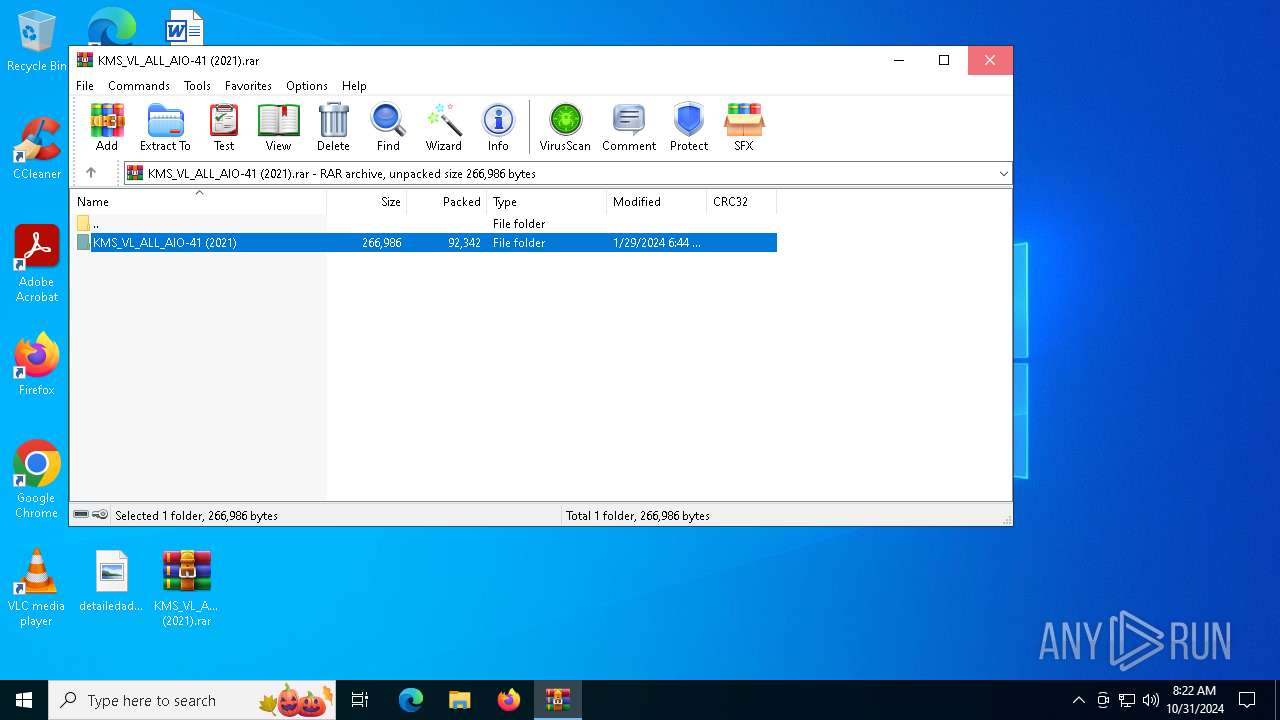
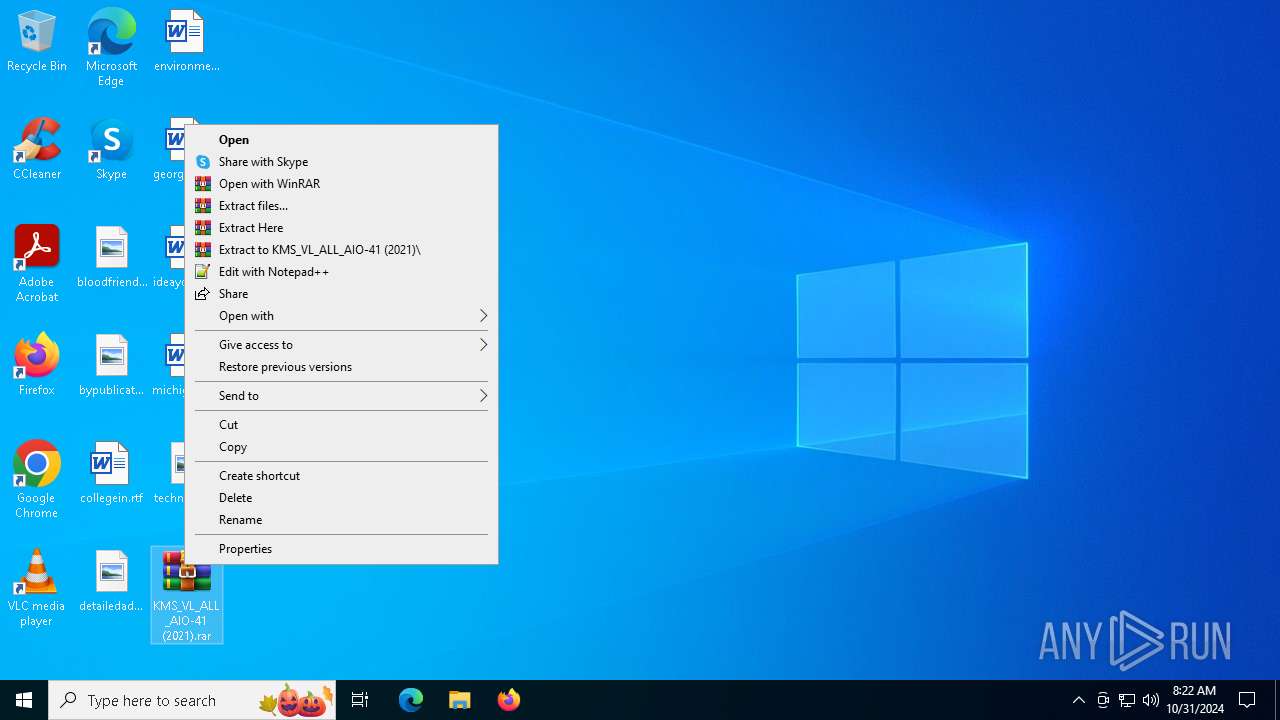
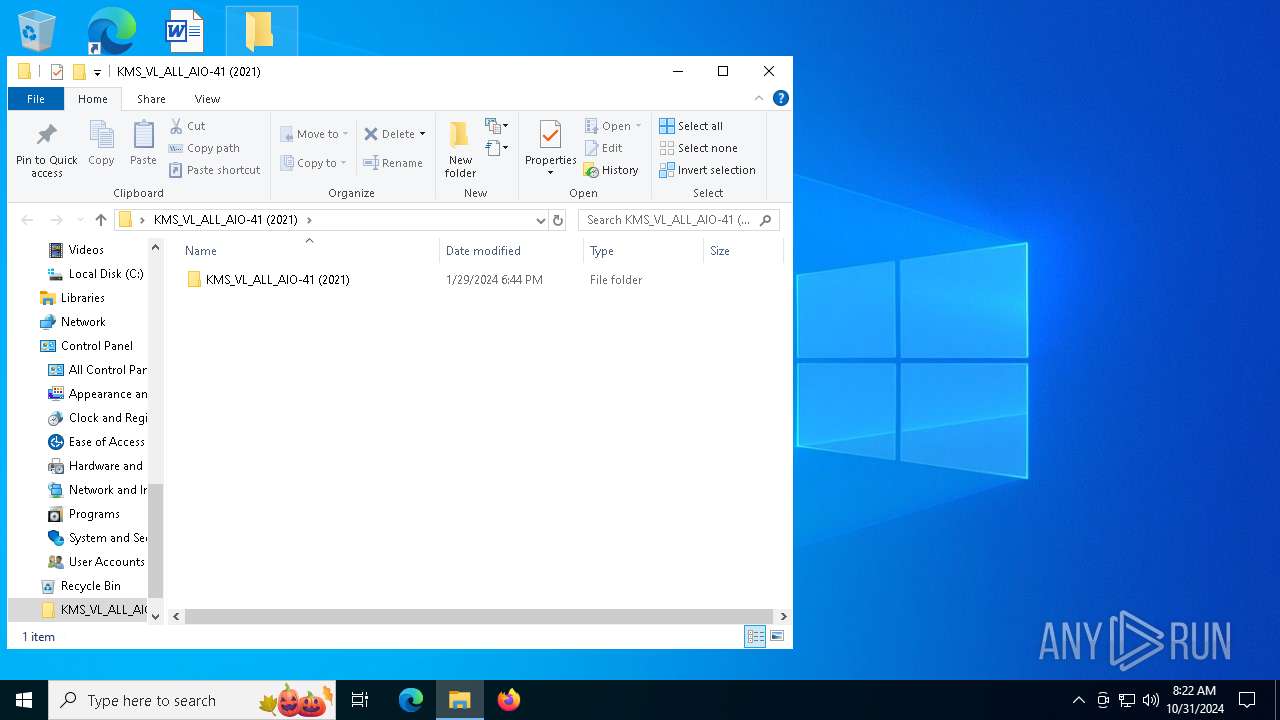
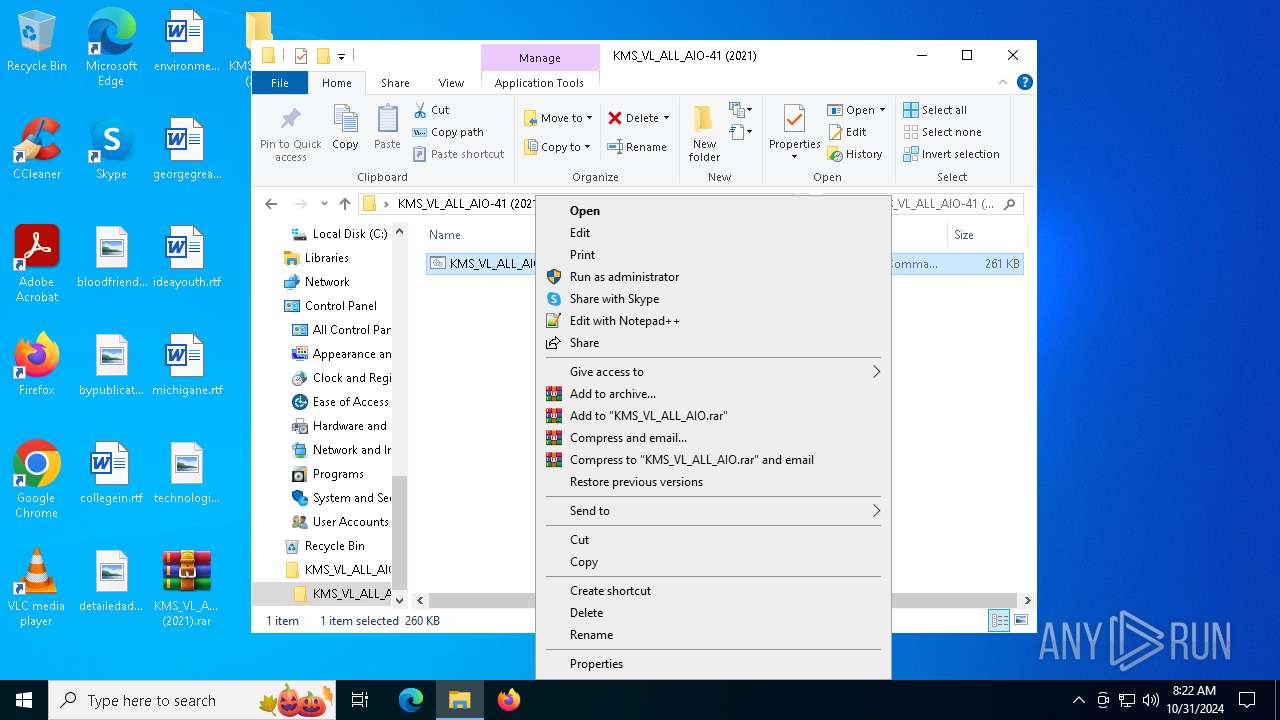
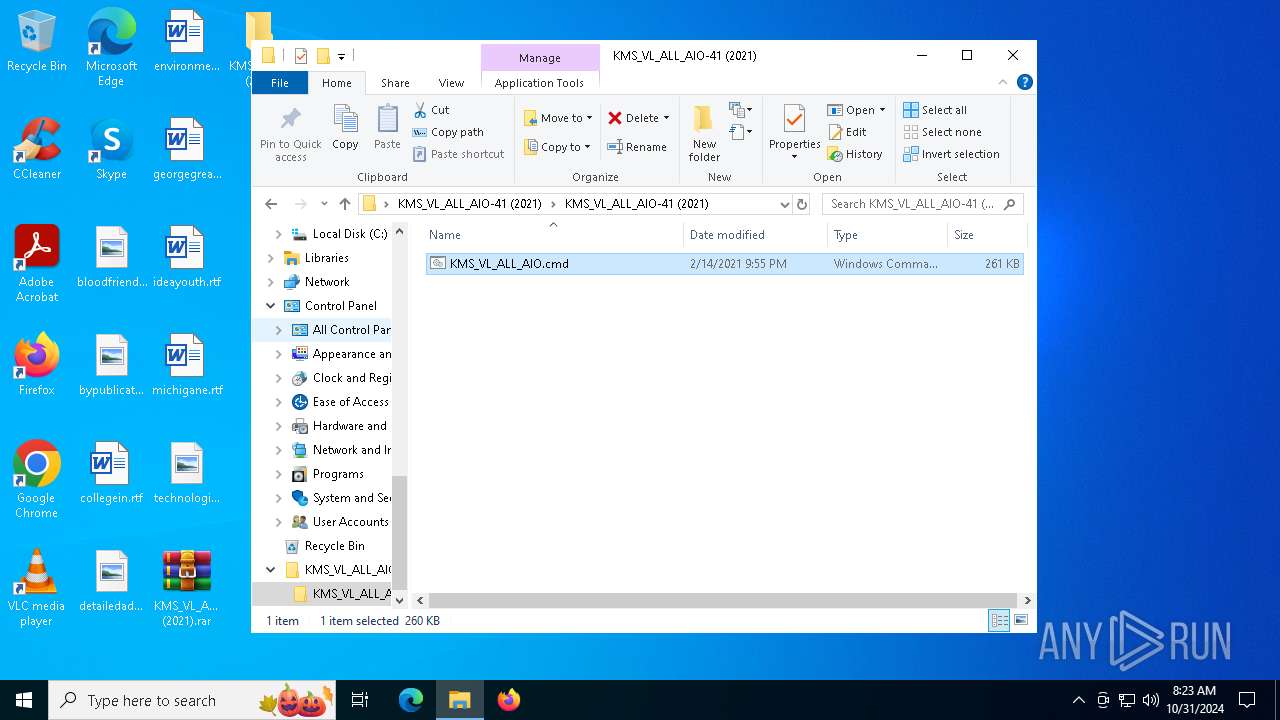
Manual execution by a user
- WinRAR.exe (PID: 4076)
- cmd.exe (PID: 1788)
Checks operating system version
- cmd.exe (PID: 1788)
Starts MODE.COM to configure console settings
- mode.com (PID: 7120)
- mode.com (PID: 6900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 92342 |
| UncompressedSize: | 266986 |
| OperatingSystem: | Win32 |
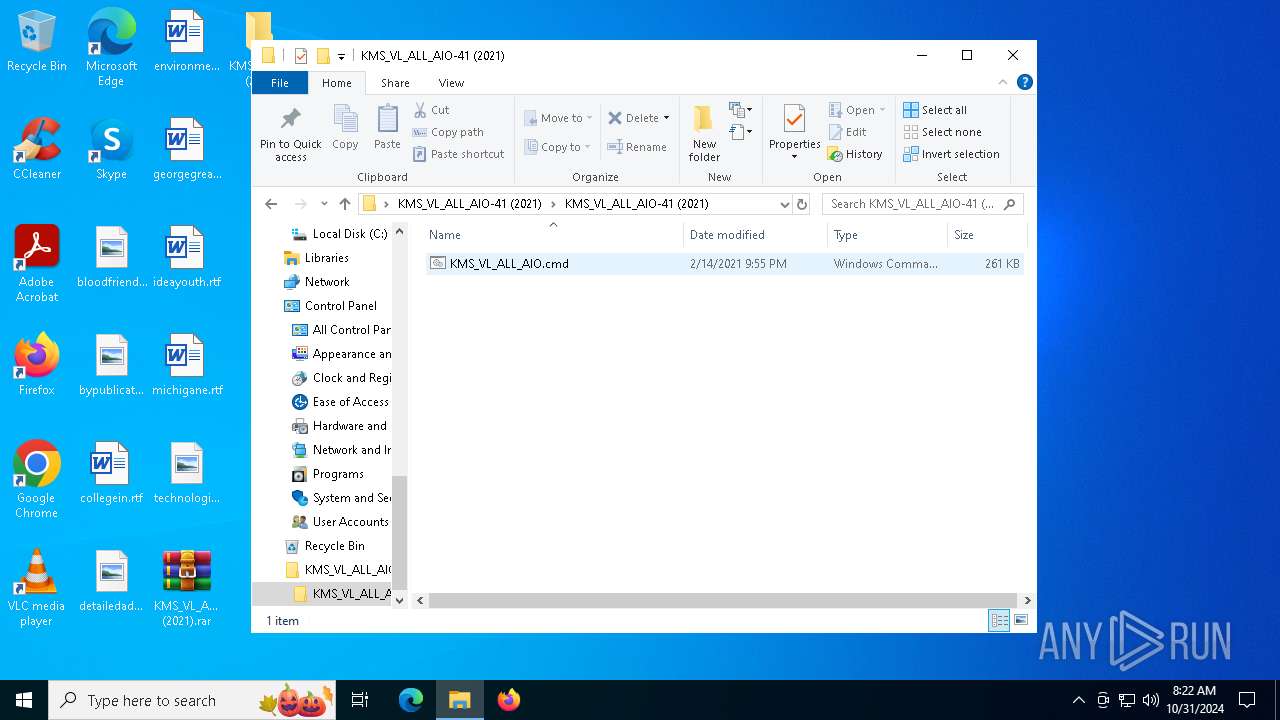
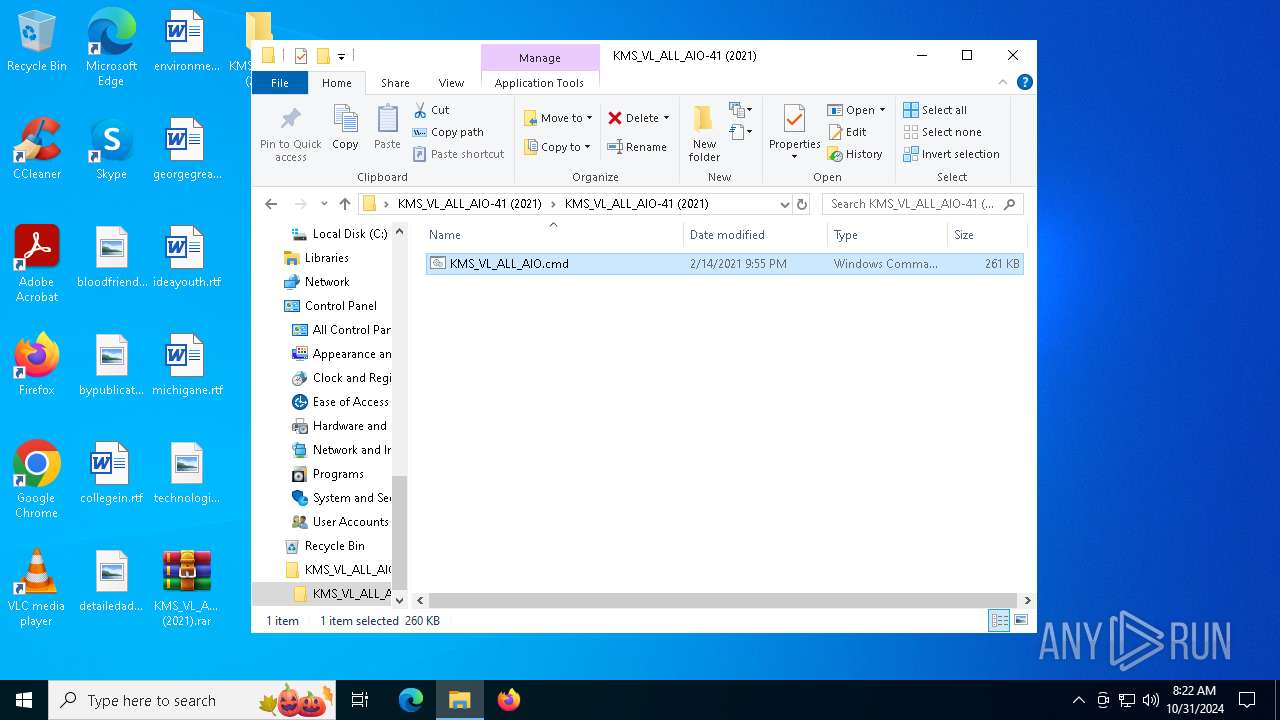
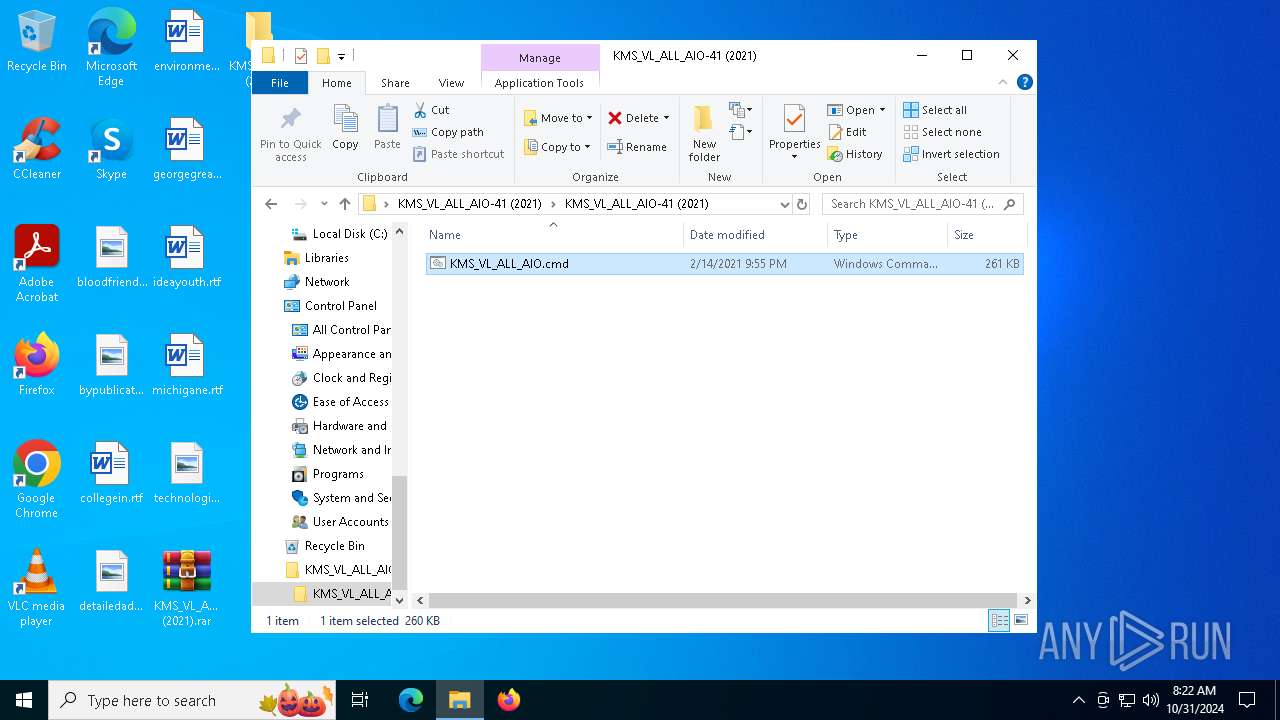
| ArchivedFileName: | KMS_VL_ALL_AIO-41 (2021)/KMS_VL_ALL_AIO.cmd |
Total processes
533
Monitored processes
397
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | findstr /I /C:"PowerPoint2019Volume" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 204 | find /i "Office16Professional2019MSDNR_" "C:\WINDOWS\Temp\crvRetail.txt" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | findstr /I /C:"PublisherVolume" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | findstr /I /C:"WordRetail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | "C:\WINDOWS\System32\SLUI.exe" RuleId=eeba1977-569e-4571-b639-7623d8bfecc0;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=2de67392-b7a7-462a-b1ca-108dd189f588;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 512 | reg delete "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform\59a52881-a989-479d-af46-f275c6370663" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | reg query HKLM\SOFTWARE\Microsoft\Office\ClickToRun\Configuration /v ProductReleaseIds | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | findstr /I /C:"MondoRetail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /c "prompt #$H#$E# & echo on & for %B in (1) do rem" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 692 | C:\WINDOWS\system32\cmd.exe /c dir /b /ad C:\WINDOWS\System32\spp\tokens\skus | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 958
Read events
21 922
Write events
31
Delete events
5
Modification events
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\KMS_VL_ALL_AIO-41 (2021).rar | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | psize |
Value: 80 | |||
Executable files
2
Suspicious files
3
Text files
14
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5596 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xegfgvkv.nha.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3008 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:75CAA1D6A7BD559C47C625DF76C6214F | SHA256:0605D595C5F483DB87EC2561ECD580B6AB064DA8A69CD613E2F06B21E4A04638 | |||
| 4076 | WinRAR.exe | C:\Users\admin\Desktop\KMS_VL_ALL_AIO-41 (2021)\KMS_VL_ALL_AIO-41 (2021)\KMS_VL_ALL_AIO.cmd | text | |
MD5:D8773D33FB91612DAA29B03DE2DDFE8F | SHA256:DA611F3C11A01D7AA27C76A2975136D074F10D6A43B716997CB1C59D5C02F9B1 | |||
| 1788 | cmd.exe | C:\Windows\Temp\crvProductIds.txt | text | |
MD5:D57FBDD4D9B2D0BBACC4088E18EAF010 | SHA256:D4F290F488267D8076273CD57451947C2EAF895E6DDB28BD41F252955C236E8F | |||
| 1788 | cmd.exe | C:\Windows\Temp\slmgr.vbs | text | |
MD5:3903BCAB32A4A853DFA54962112D4D02 | SHA256:95FC646D222D324DB46F603A7F675C329FE59A567ED27FDAED2A572A19206816 | |||
| 3828 | findstr.exe | C:\Windows\Temp\crvRetail.txt | text | |
MD5:41C898D0D6922B8993F75E70631D1213 | SHA256:5ECBCEE677C451CAAD7FDD94A879292DA699CE10A6B82016F3C762F6925CCD04 | |||
| 1788 | cmd.exe | C:\Windows\Temp\sppchk.txt | text | |
MD5:1F3EA1427D787A6420BFF6B8E1FD1EA4 | SHA256:BE033784A227FFA2F367E6B23893D45654FC5FFF24A95CDDA0DD03821BDE109F | |||
| 4692 | findstr.exe | C:\Windows\Temp\crvVolume.txt | text | |
MD5:52CC3301F59D01DB50AE1DDC3A5FA471 | SHA256:E3C6585D4E23EAFA59DA1331D360D9DAFE429A3BA6257AD1378721CA20E125F0 | |||
| 5596 | powershell.exe | C:\Windows\System32\SppExtComObjHook.dll | executable | |
MD5:C1B097EDE269EF5941C27B66621105EB | SHA256:A1FE9948E692B1FA2EBBA3C3D6FB2B88F7D97B418398369AD3865418C4E3CB88 | |||
| 1788 | cmd.exe | C:\Windows\Temp\c2rchk.txt | text | |
MD5:D57FBDD4D9B2D0BBACC4088E18EAF010 | SHA256:D4F290F488267D8076273CD57451947C2EAF895E6DDB28BD41F252955C236E8F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
48
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
624 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6384 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6404 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6404 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
624 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 2.23.209.131:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |