| File name: | answers |
| Full analysis: | https://app.any.run/tasks/00cc8c09-804f-4555-8b7a-9253b0cb30fe |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 00:54:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 5BA1D905D8F8DEC624A643B0D883F17F |
| SHA1: | FB6D67D374090627B23F35CCB86D55424E45BB2B |
| SHA256: | 0BD113F9C86C51B223FFDE70AB1FD983E621F591772A9F65C263540D877F0773 |
| SSDEEP: | 384:Gw51UFSxqdVvWCDvLUKELu4VYyDpzOe/8P49ovyR8uwFYCDCkCpCnTUIwu:GwFxqL4K/M/ptuvy2PX |
MALICIOUS
Application was dropped or rewritten from another process
- Update.exe (PID: 3924)
- Squirrel.exe (PID: 1780)
- Update.exe (PID: 256)
- Update.exe (PID: 2432)
- Update.exe (PID: 3680)
- Update.exe (PID: 1116)
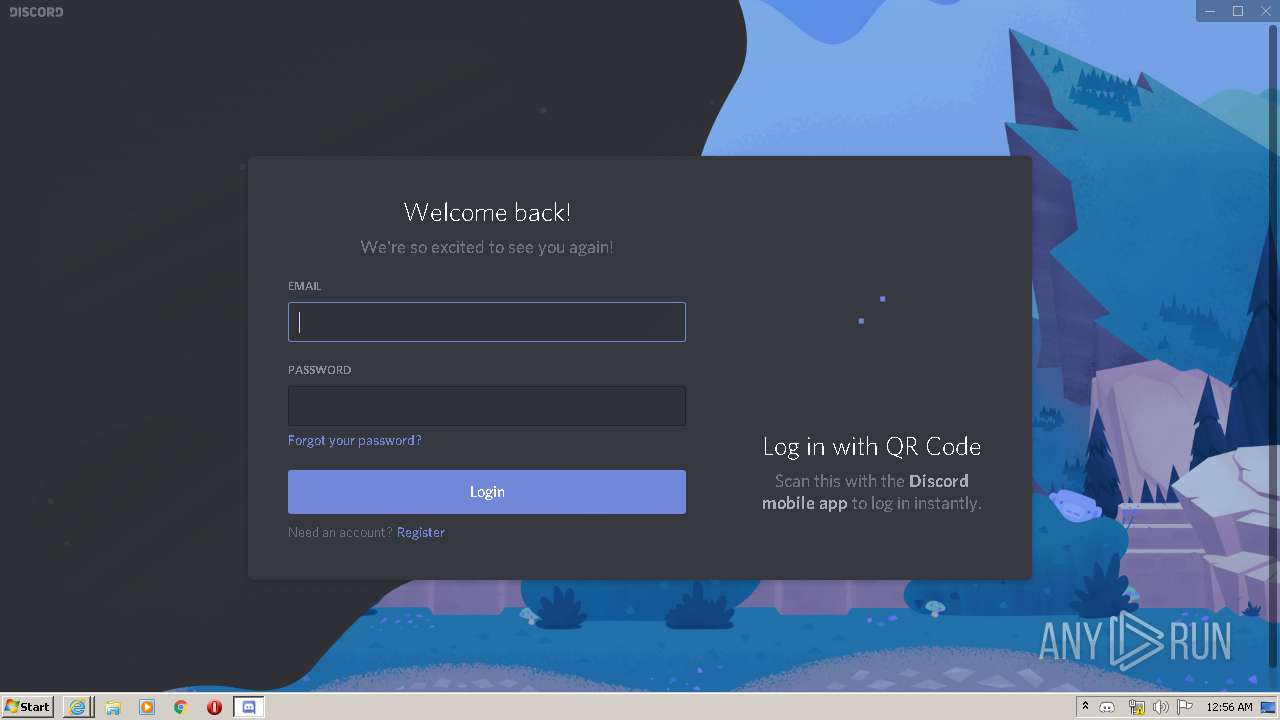
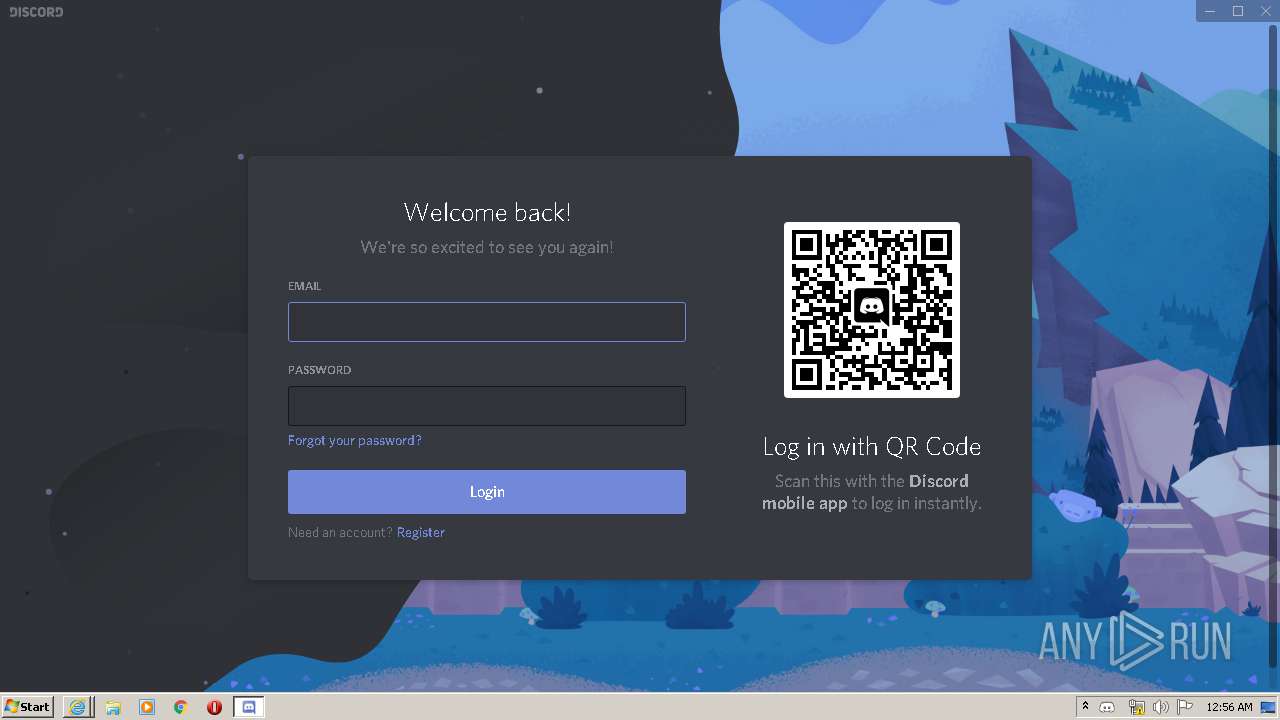
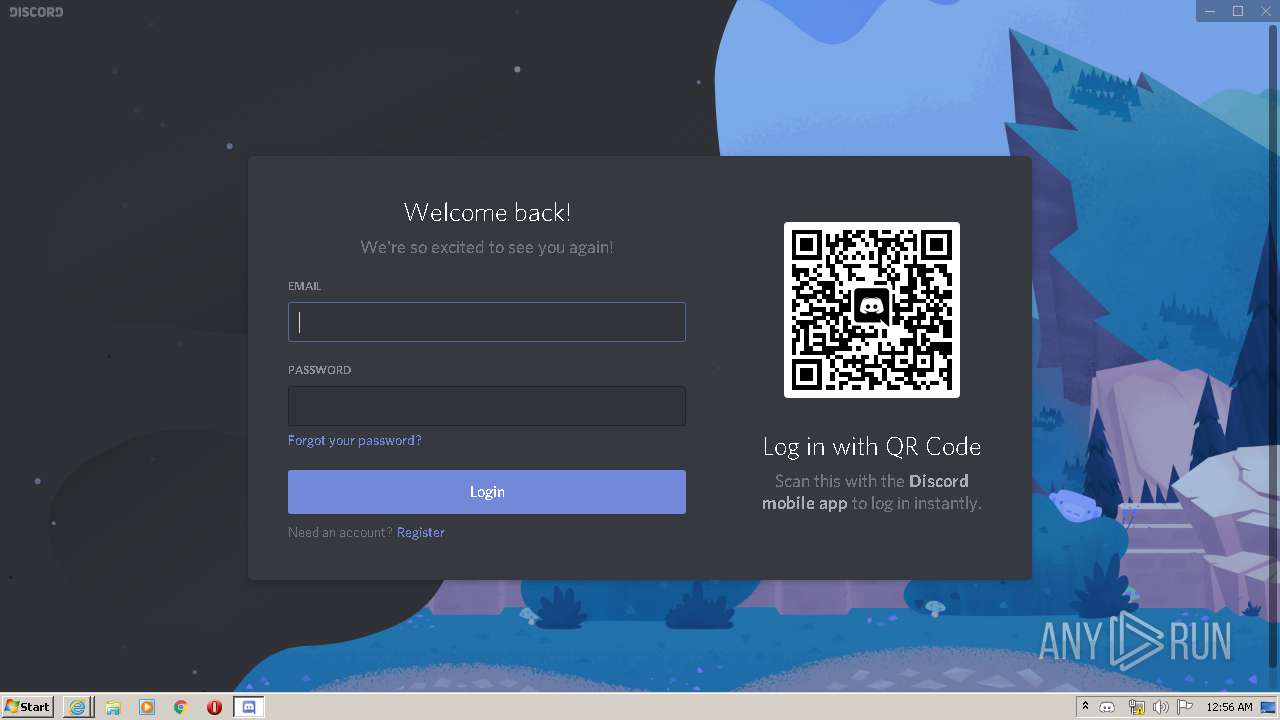
Loads dropped or rewritten executable
- Discord.exe (PID: 2544)
- Discord.exe (PID: 3452)
- Discord.exe (PID: 2960)
- Discord.exe (PID: 3420)
- Discord.exe (PID: 872)
- Discord.exe (PID: 3156)
- Discord.exe (PID: 1412)
- Discord.exe (PID: 2780)
- Discord.exe (PID: 2052)
- Discord.exe (PID: 3584)
- Discord.exe (PID: 3720)
- Discord.exe (PID: 3036)
- Discord.exe (PID: 3488)
- Discord.exe (PID: 3880)
- Discord.exe (PID: 2740)
- Discord.exe (PID: 3192)
Changes the autorun value in the registry
- reg.exe (PID: 2600)
SUSPICIOUS
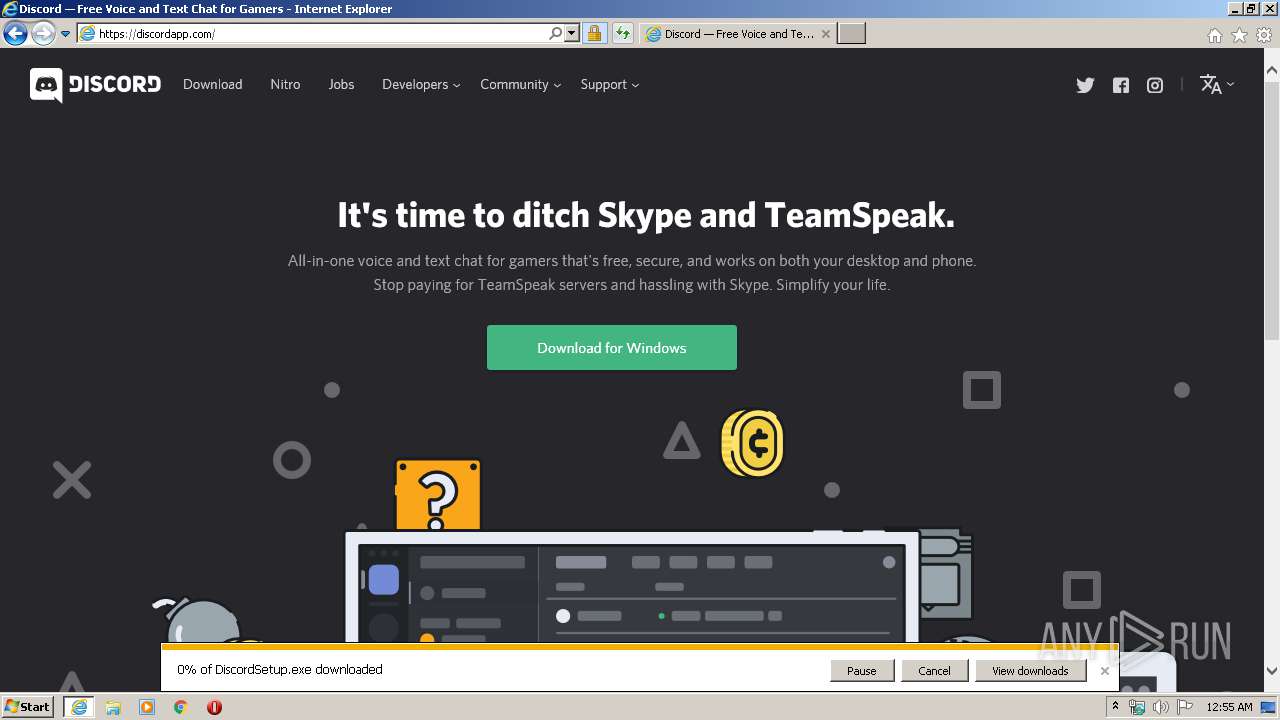
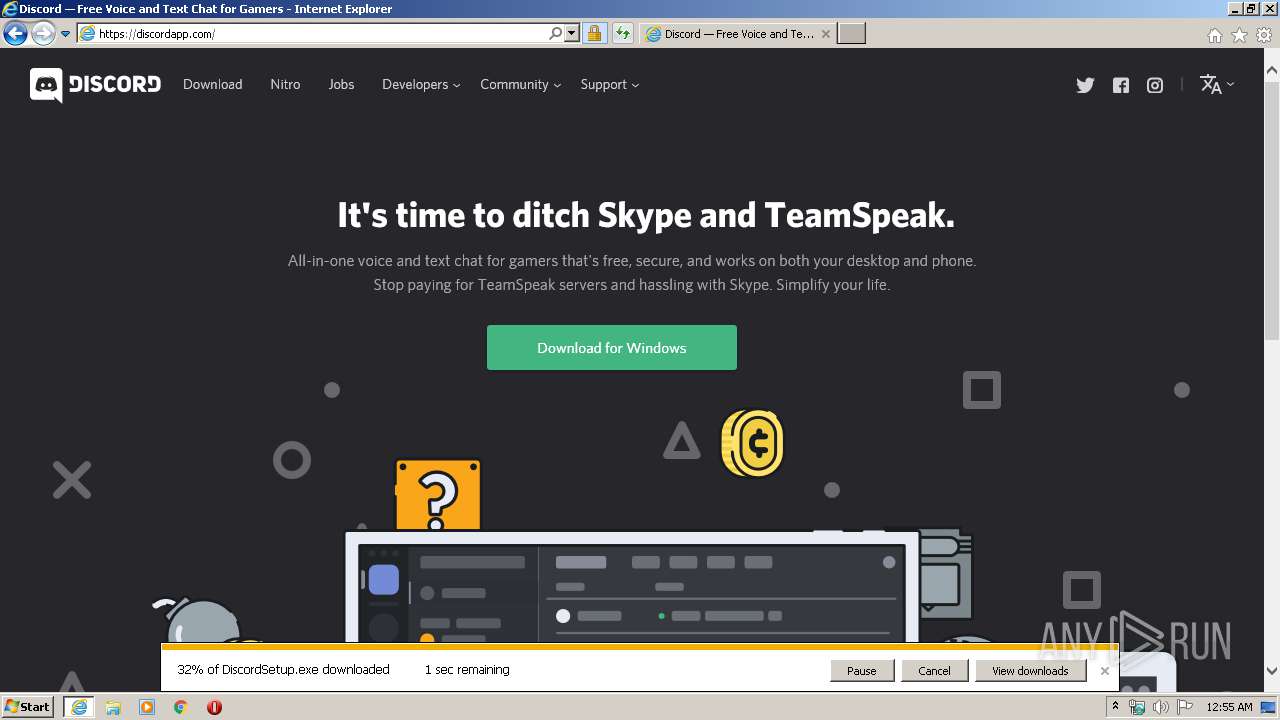
Executable content was dropped or overwritten
- DiscordSetup.exe (PID: 3692)
- Update.exe (PID: 3924)
- Discord.exe (PID: 1412)
Starts itself from another location
- Update.exe (PID: 3924)
Creates files in the user directory
- Update.exe (PID: 256)
- Discord.exe (PID: 3452)
- Discord.exe (PID: 1412)
Modifies the open verb of a shell class
- reg.exe (PID: 2576)
Application launched itself
- Discord.exe (PID: 2544)
- Discord.exe (PID: 3452)
- Discord.exe (PID: 3156)
- Discord.exe (PID: 1412)
- Discord.exe (PID: 2740)
Uses REG.EXE to modify Windows registry
- Discord.exe (PID: 2544)
Creates a software uninstall entry
- Update.exe (PID: 3924)
Reads Environment values
- Update.exe (PID: 2432)
- Update.exe (PID: 3680)
- Update.exe (PID: 1116)
Starts CMD.EXE for commands execution
- Discord.exe (PID: 3720)
INFO
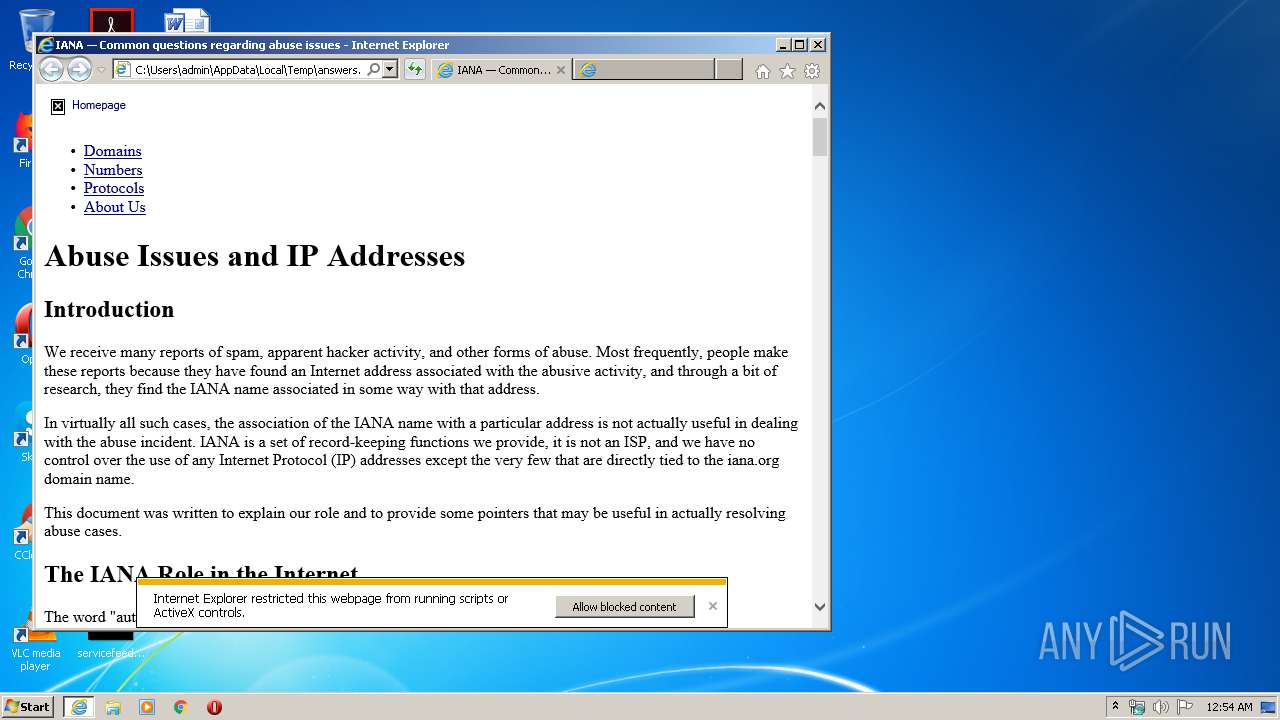
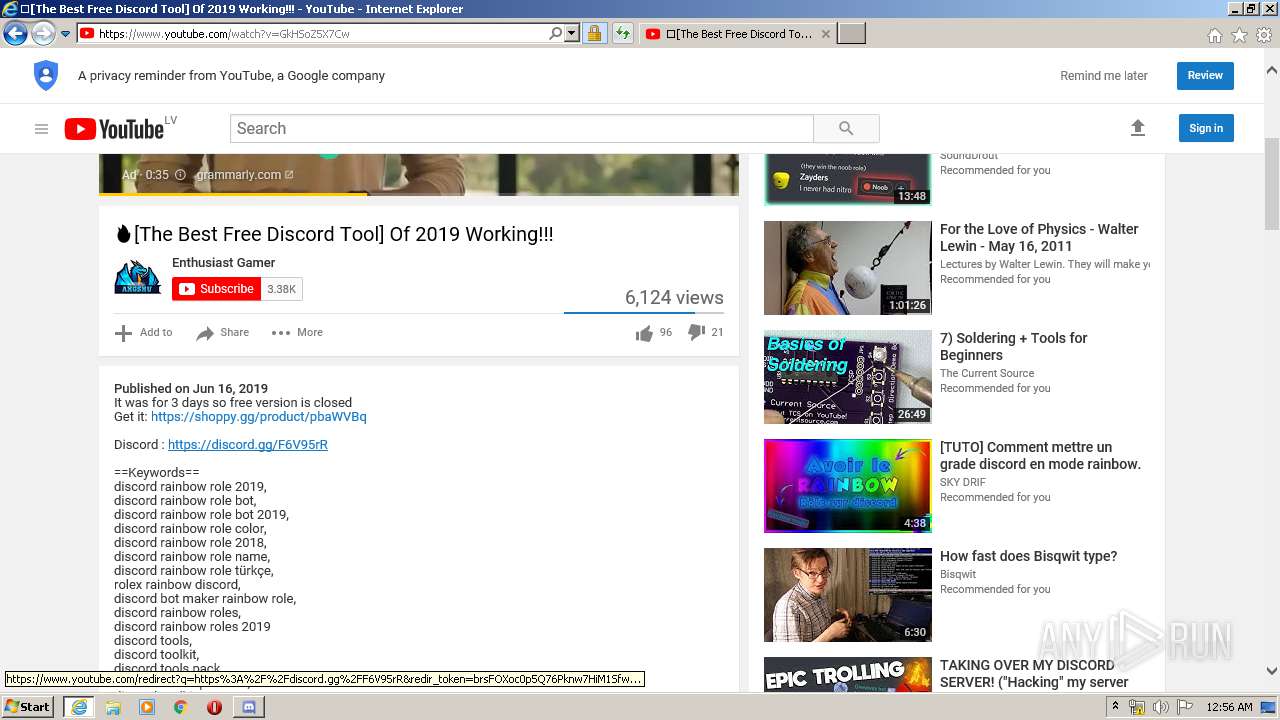
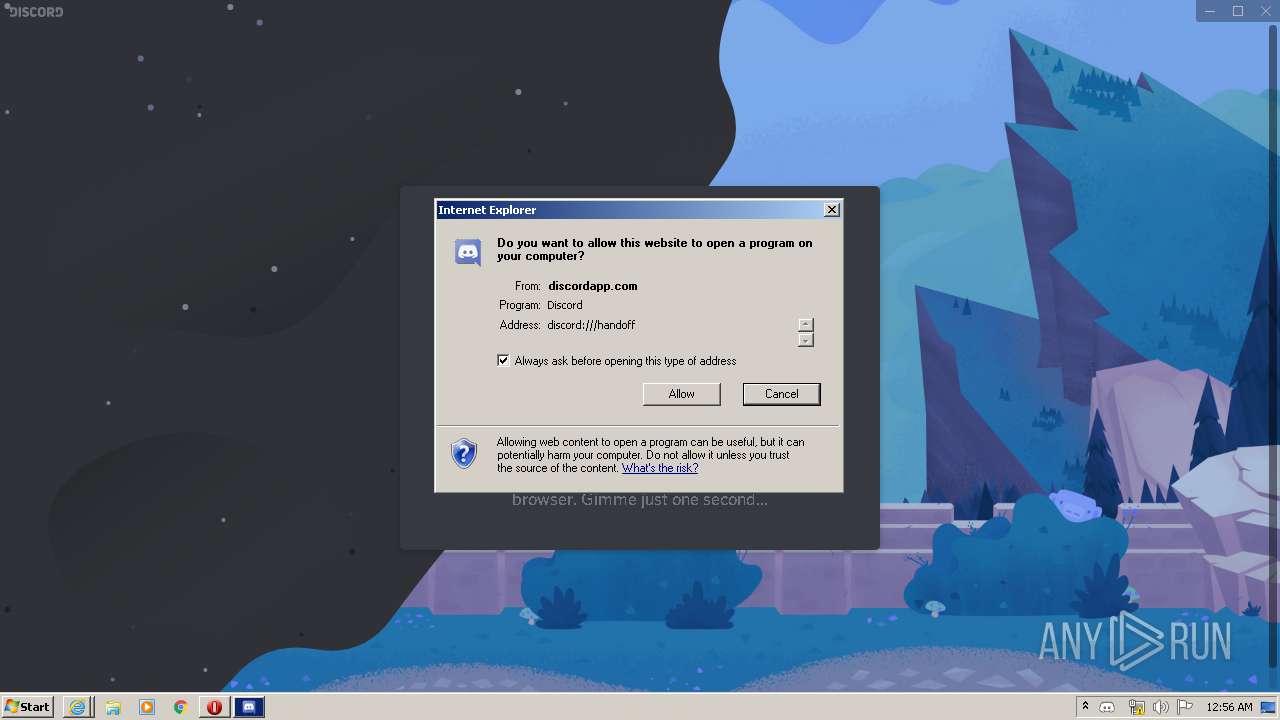
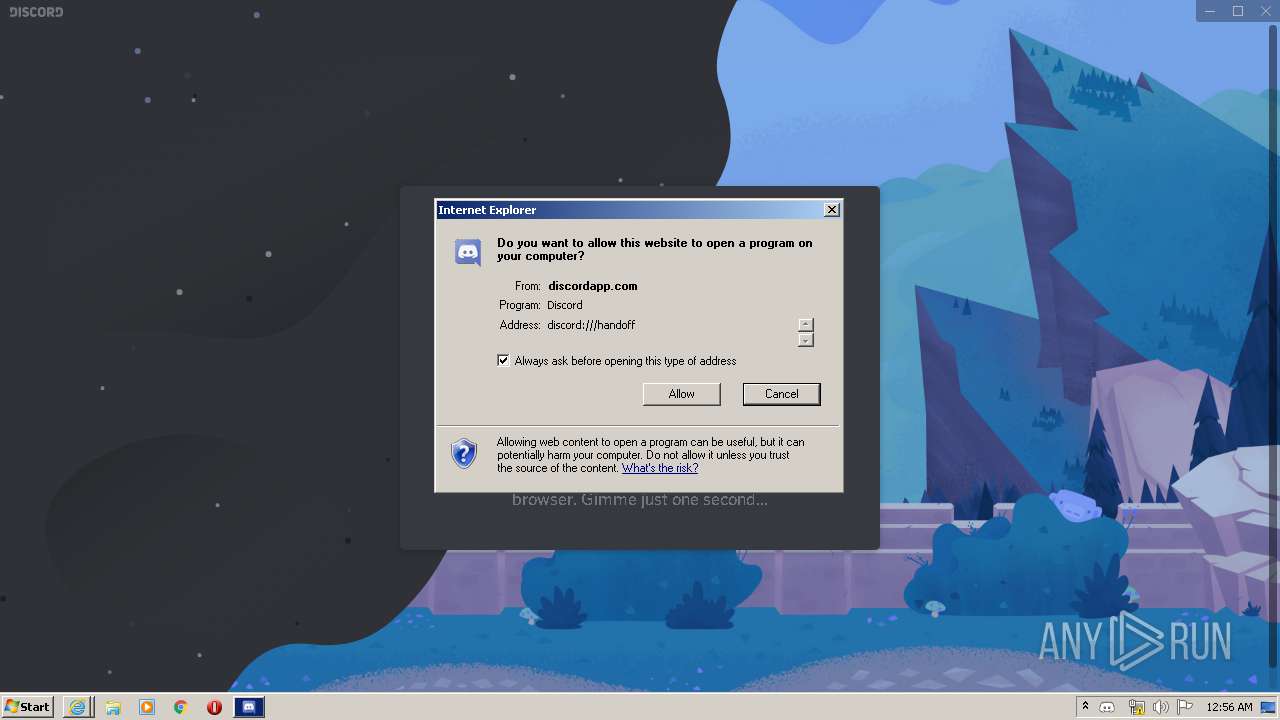
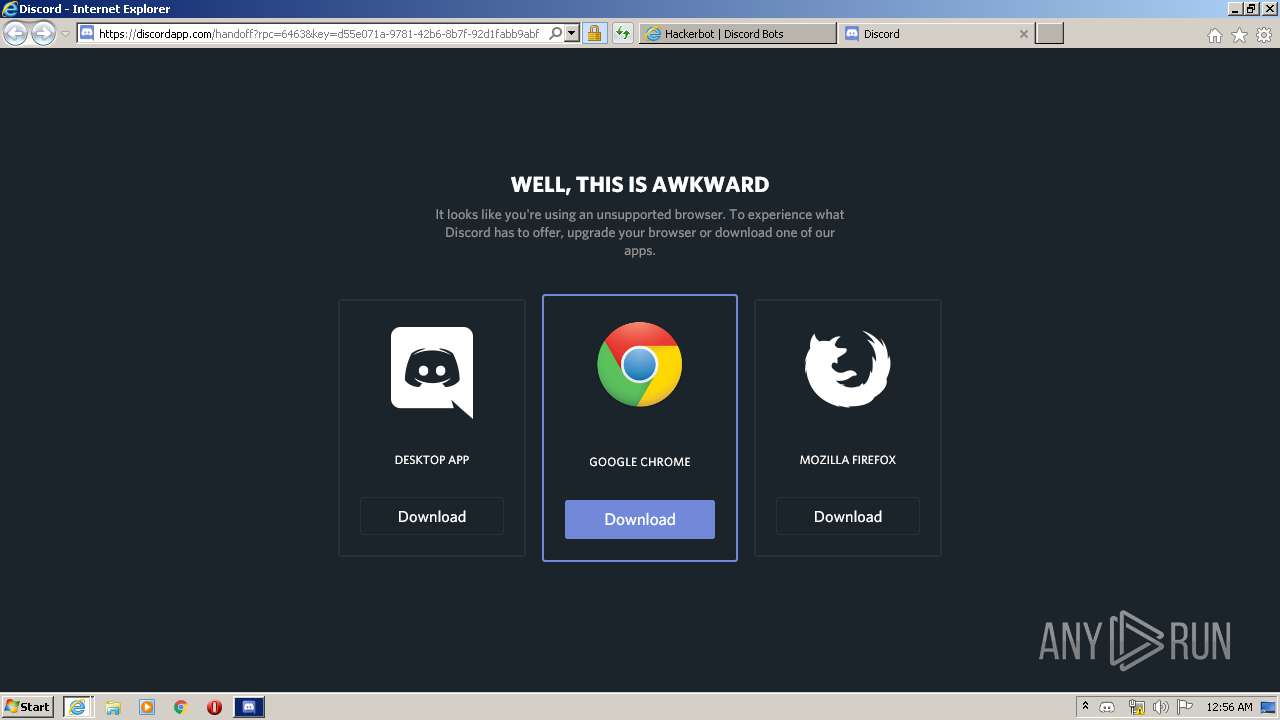
Reads internet explorer settings
- iexplore.exe (PID: 1712)
- iexplore.exe (PID: 2536)
- iexplore.exe (PID: 3868)
- iexplore.exe (PID: 1852)
Application launched itself
- iexplore.exe (PID: 3868)
- iexplore.exe (PID: 2676)
Reads settings of System Certificates
- iexplore.exe (PID: 1712)
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 2536)
- iexplore.exe (PID: 3868)
- iexplore.exe (PID: 1852)
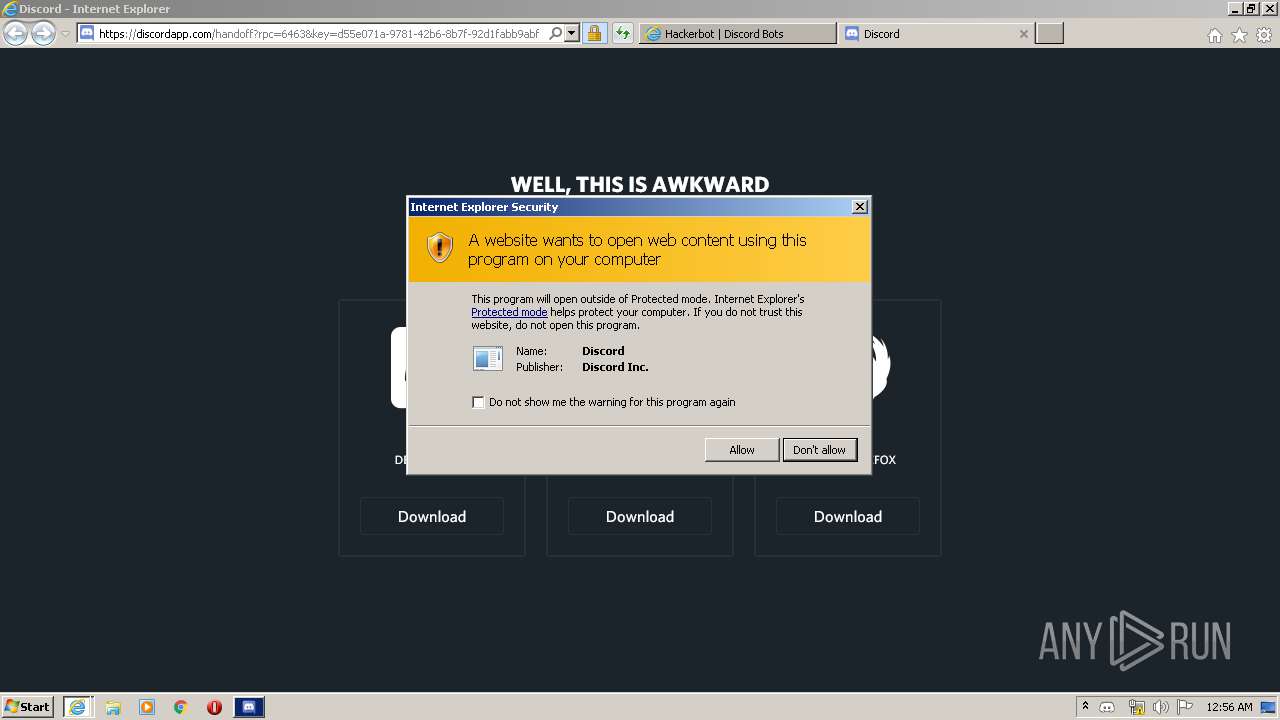
Modifies the phishing filter of IE
- iexplore.exe (PID: 2676)
Reads Internet Cache Settings
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 1712)
- iexplore.exe (PID: 1852)
Changes internet zones settings
- iexplore.exe (PID: 2676)
Creates files in the user directory
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 1712)
- iexplore.exe (PID: 1852)
Reads the hosts file
- Discord.exe (PID: 2544)
- Discord.exe (PID: 3452)
- Discord.exe (PID: 1412)
- Discord.exe (PID: 2740)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1852)
- iexplore.exe (PID: 1712)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 2536)
- iexplore.exe (PID: 3868)
Changes settings of System certificates
- iexplore.exe (PID: 2536)
- iexplore.exe (PID: 2676)
- iexplore.exe (PID: 3868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| Title: | IANA — Common questions regarding abuse issues |
|---|---|
| ContentType: | text/html; charset=utf-8 |
| viewport: | width=device-width, initial-scale=1 |
Total processes
79
Monitored processes
35
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | C:\Users\admin\AppData\Local\Discord\Update.exe --createShortcut Discord.exe --setupIcon C:\Users\admin\AppData\Local\Discord\app.ico | C:\Users\admin\AppData\Local\Discord\Update.exe | — | Discord.exe | |||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 1.1.1.0 Modules
| |||||||||||||||
| 872 | "C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe" --type=gpu-process --enable-features=SharedArrayBuffer --no-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4259354444907474087 --mojo-platform-channel-handle=1088 /prefetch:2 | C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe | — | Discord.exe | |||||||||||
User: admin Company: Discord Inc. Integrity Level: MEDIUM Description: Discord Exit code: 0 Version: 0.0.305 Modules
| |||||||||||||||
| 1116 | C:\Users\admin\AppData\Local\Discord\Update.exe --check https://discordapp.com/api/updates/stable | C:\Users\admin\AppData\Local\Discord\Update.exe | Discord.exe | ||||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 1.1.1.0 Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe" --squirrel-firstrun | C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe | Discord.exe | ||||||||||||
User: admin Company: Discord Inc. Integrity Level: MEDIUM Description: Discord Exit code: 0 Version: 0.0.305 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2676 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1780 | "C:\Users\admin\AppData\Local\Discord\app-0.0.305\Squirrel.exe" --updateSelf=C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | C:\Users\admin\AppData\Local\Discord\app-0.0.305\Squirrel.exe | — | Update.exe | |||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 4294967295 Version: 1.1.1.0 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2676 CREDAT:2692394 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2052 | "C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe" --type=gpu-process --enable-features=SharedArrayBuffer --disable-gpu-sandbox --no-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=14516772295025036138 --mojo-platform-channel-handle=1580 /prefetch:2 | C:\Users\admin\AppData\Local\Discord\app-0.0.305\Discord.exe | — | Discord.exe | |||||||||||
User: admin Company: Discord Inc. Integrity Level: MEDIUM Description: Discord Exit code: 0 Version: 0.0.305 Modules
| |||||||||||||||
| 2432 | C:\Users\admin\AppData\Local\Discord\Update.exe --check https://discordapp.com/api/updates/stable | C:\Users\admin\AppData\Local\Discord\Update.exe | Discord.exe | ||||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 0 Version: 1.1.1.0 Modules
| |||||||||||||||
| 2536 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2676 CREDAT:144390 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 942
Read events
3 737
Write events
9 110
Delete events
4 095
Modification events
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3261429582 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30796058 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2676) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
36
Suspicious files
485
Text files
1 499
Unknown types
243
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2676 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7B6CAAE403F9130B.TMP | — | |
MD5:— | SHA256:— | |||
| 2676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1712 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\6ZEQR2R1.txt | — | |
MD5:— | SHA256:— | |||
| 1712 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\4JAHJFGH.txt | — | |
MD5:— | SHA256:— | |||
| 1712 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\WQ45PFBG.txt | — | |
MD5:— | SHA256:— | |||
| 1712 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\D6T40UBX.txt | — | |
MD5:— | SHA256:— | |||
| 1712 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\NNWGU9U4.txt | — | |
MD5:— | SHA256:— | |||
| 1712 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\FUARK0PK.txt | — | |
MD5:— | SHA256:— | |||
| 1712 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 1712 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\e70a8ff8[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
323
TCP/UDP connections
473
DNS requests
170
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
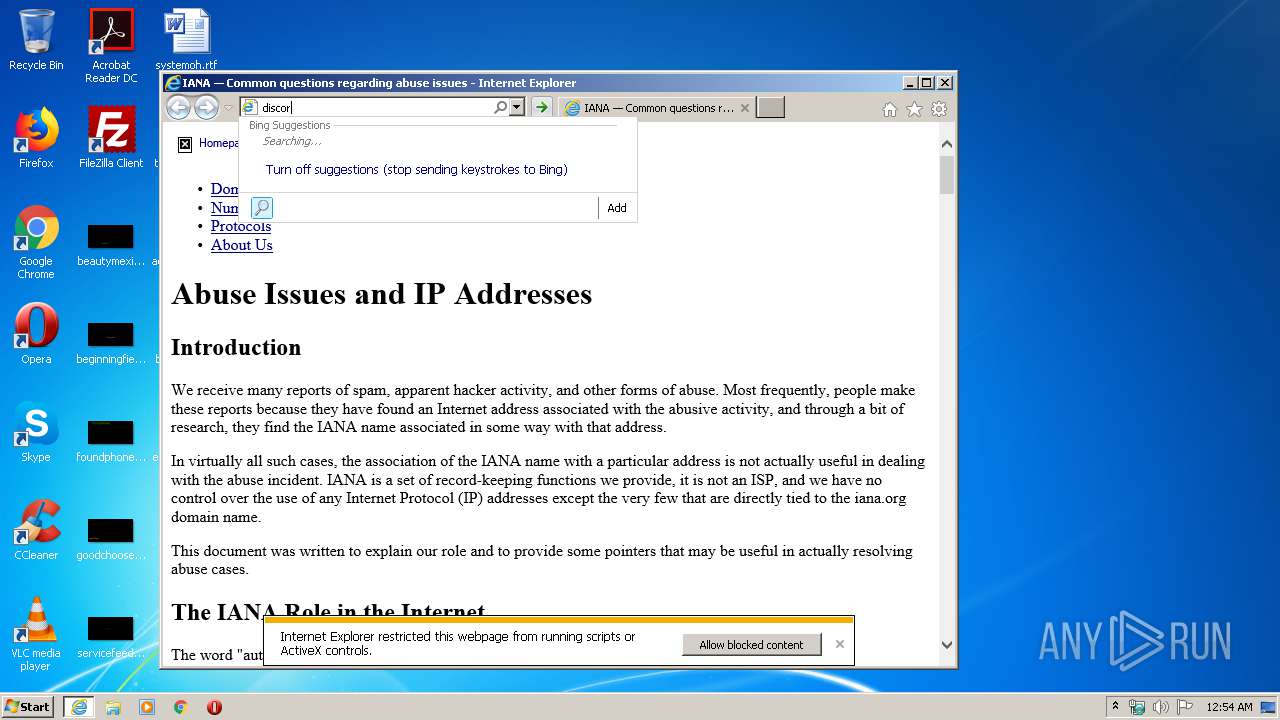
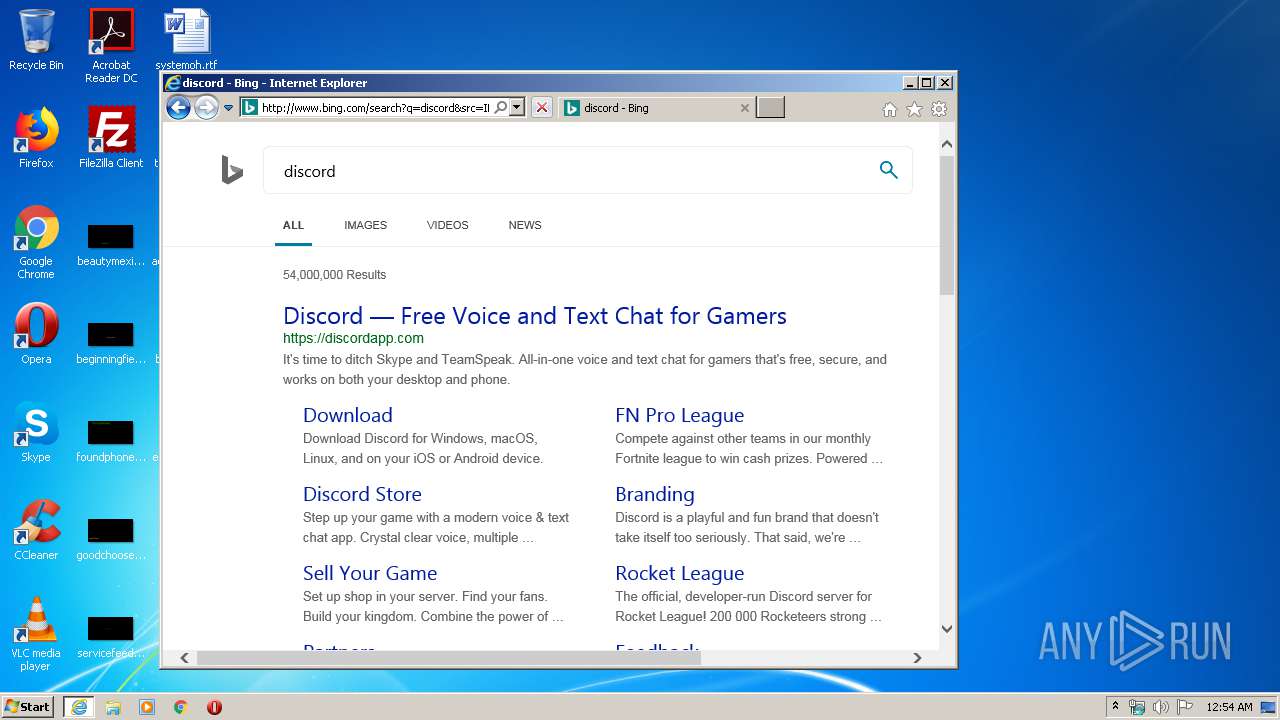
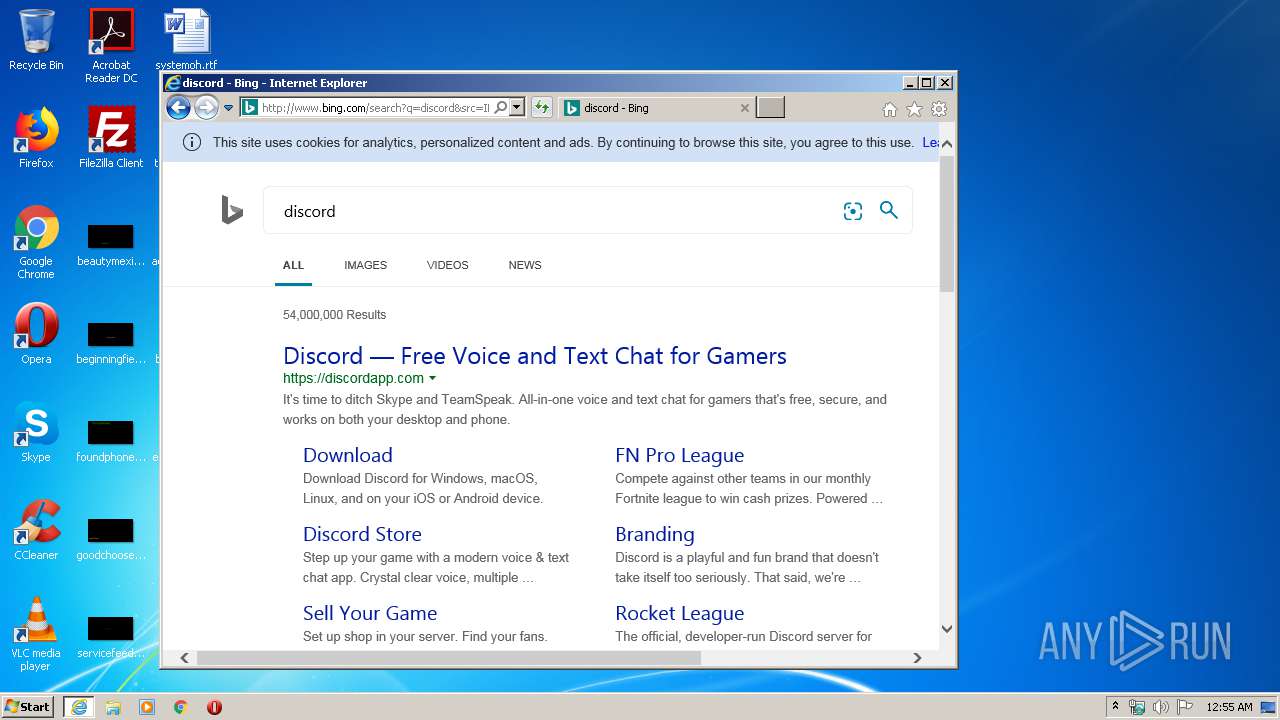
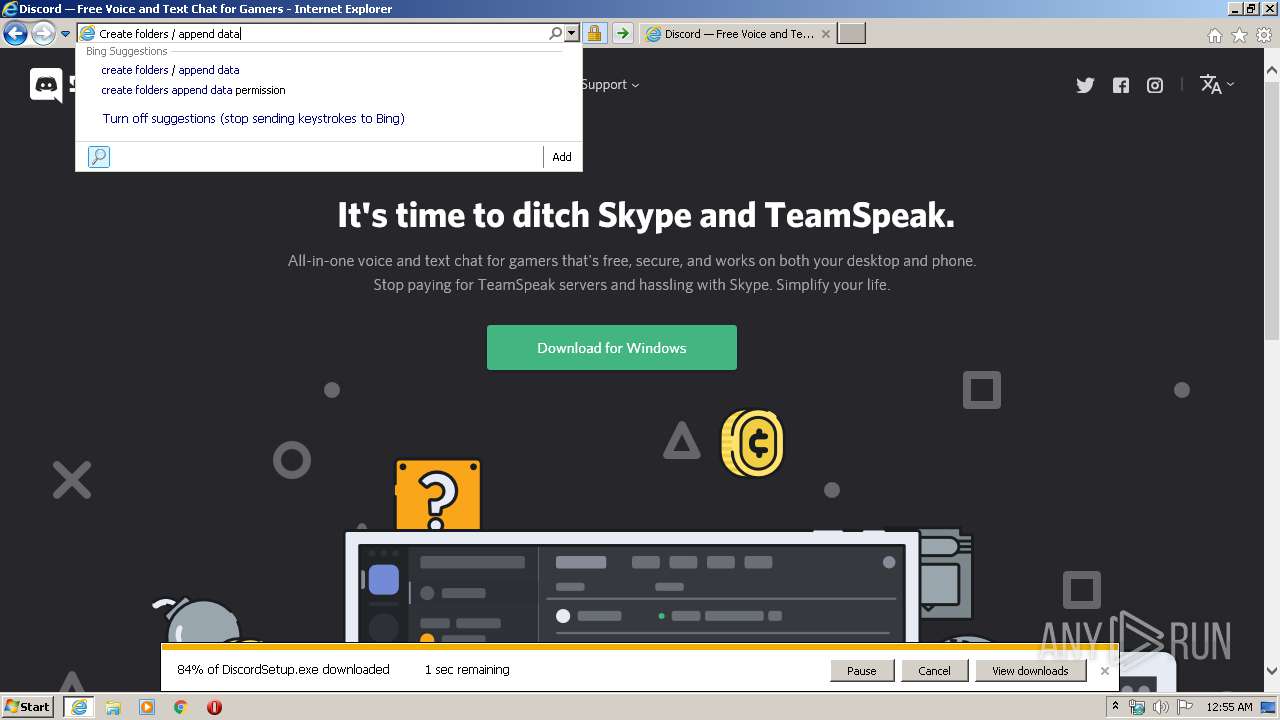
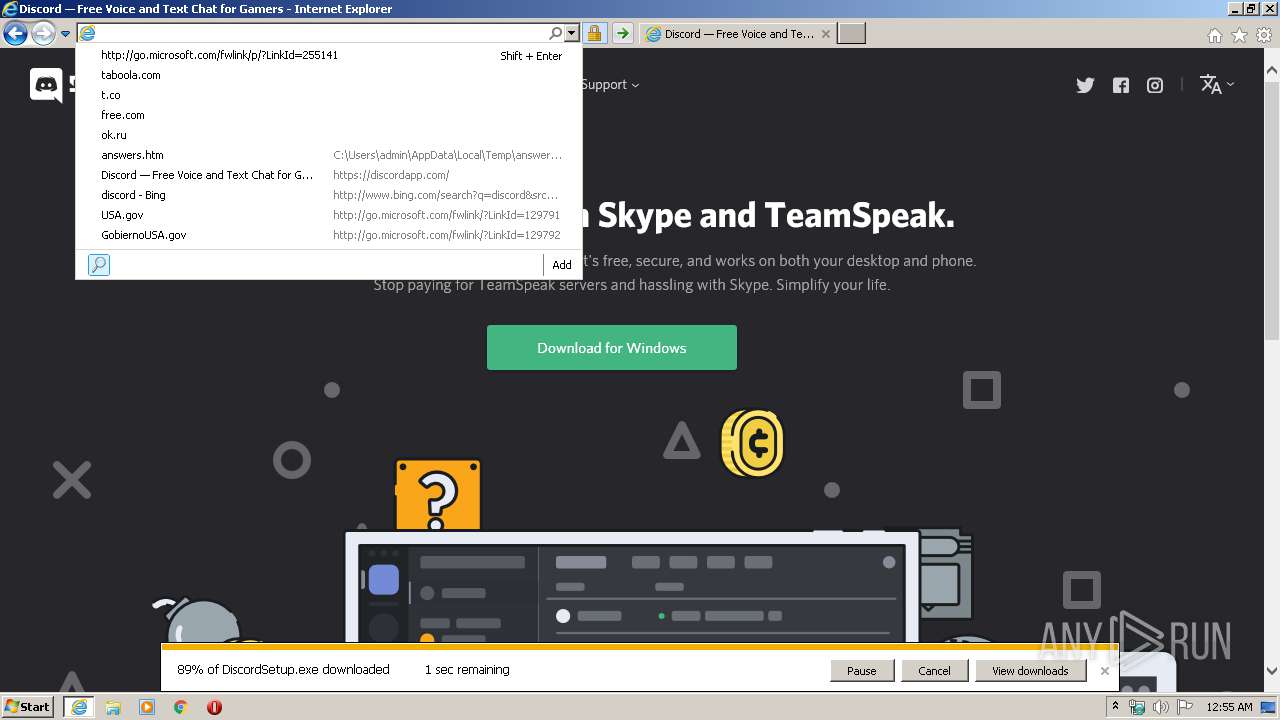
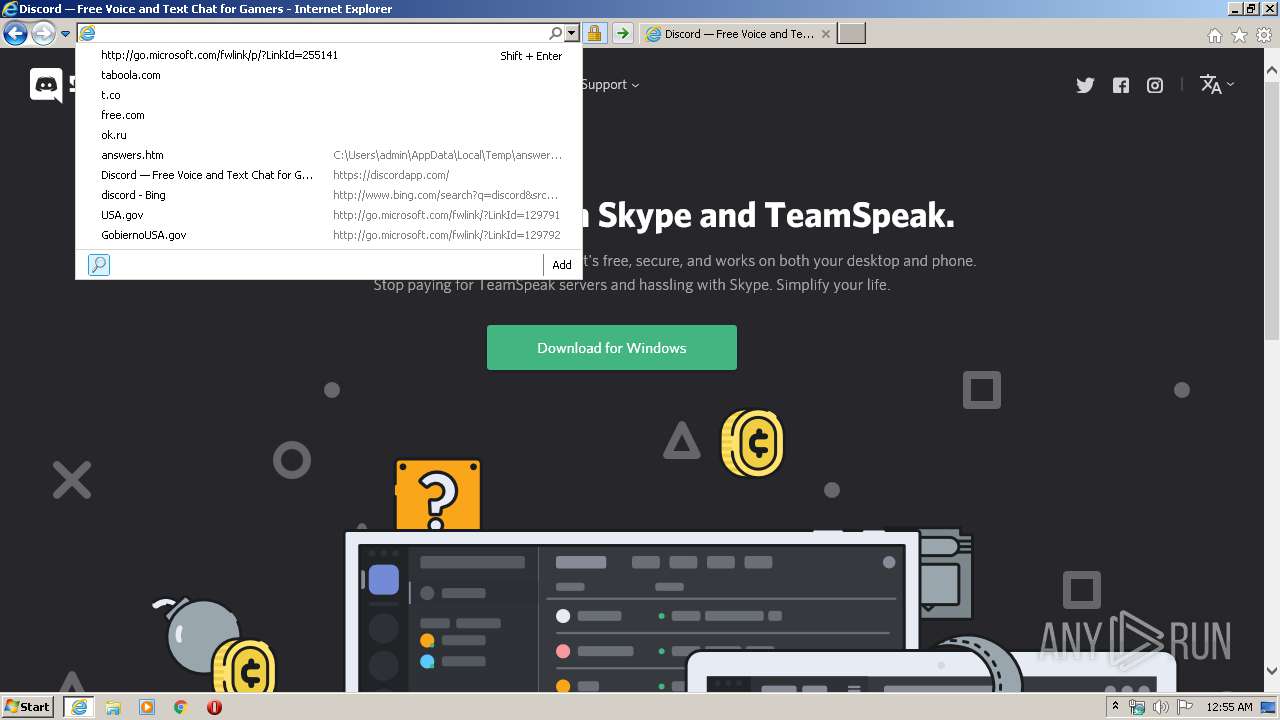
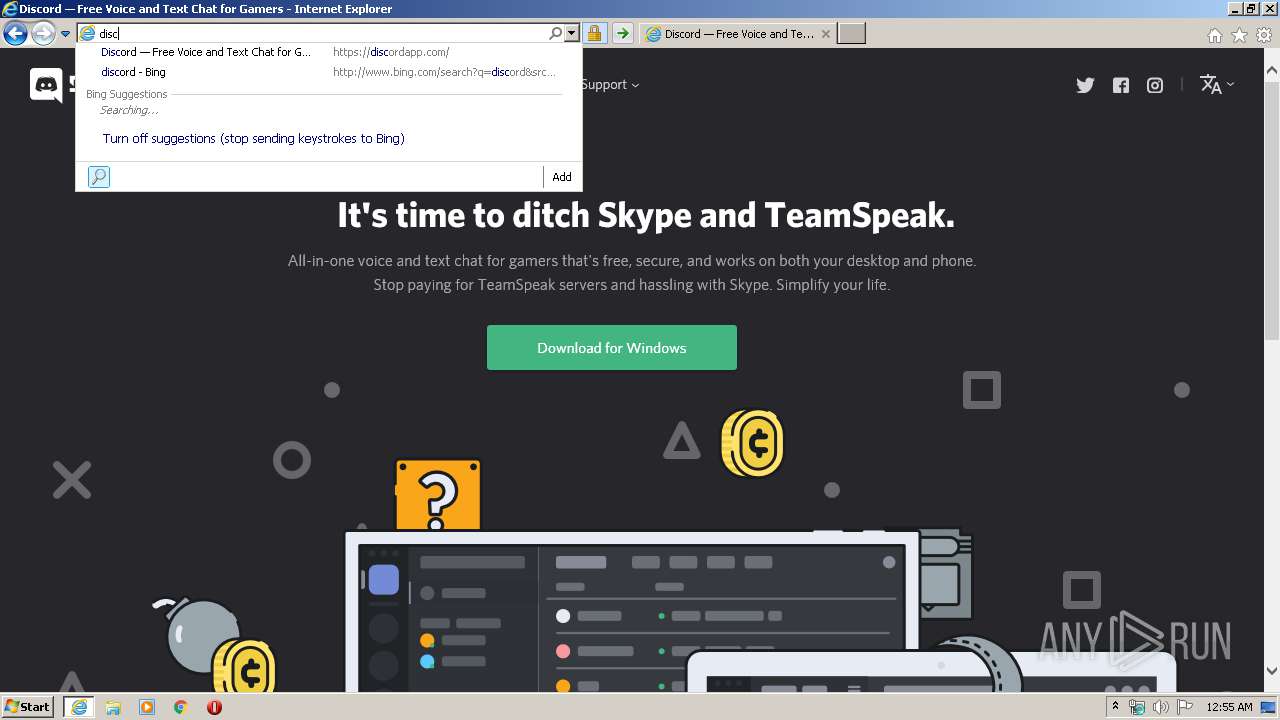
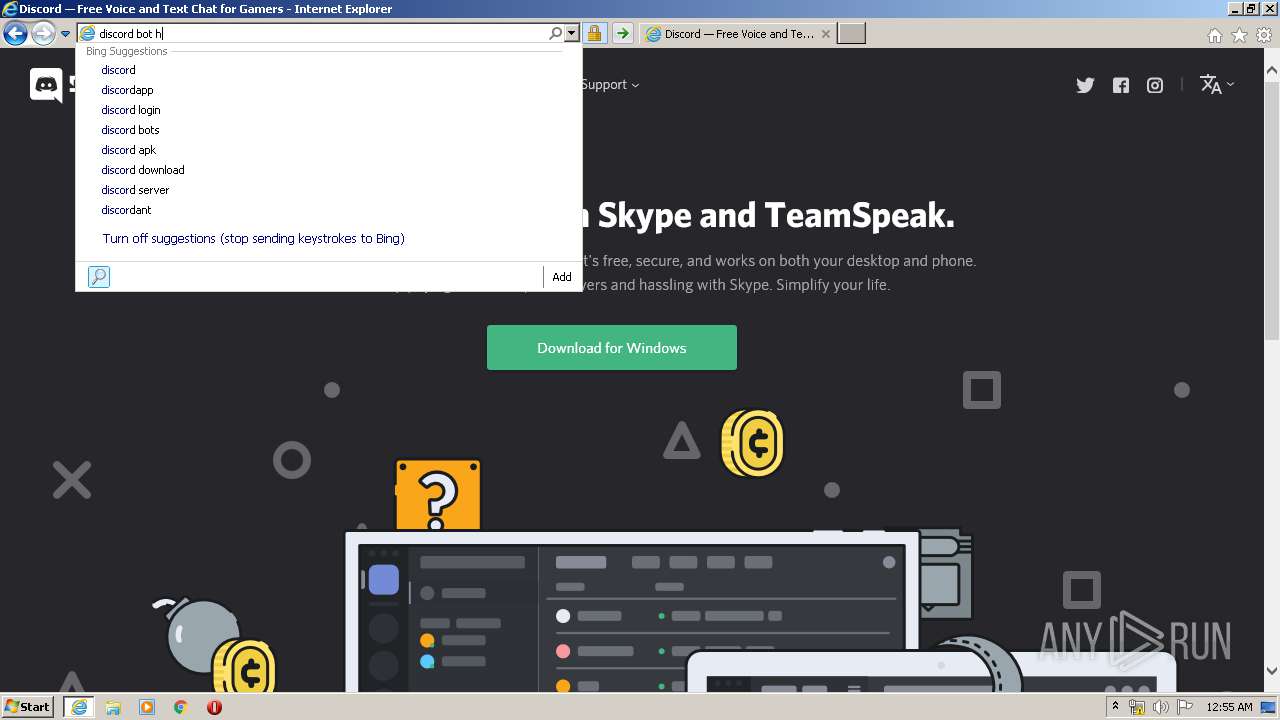
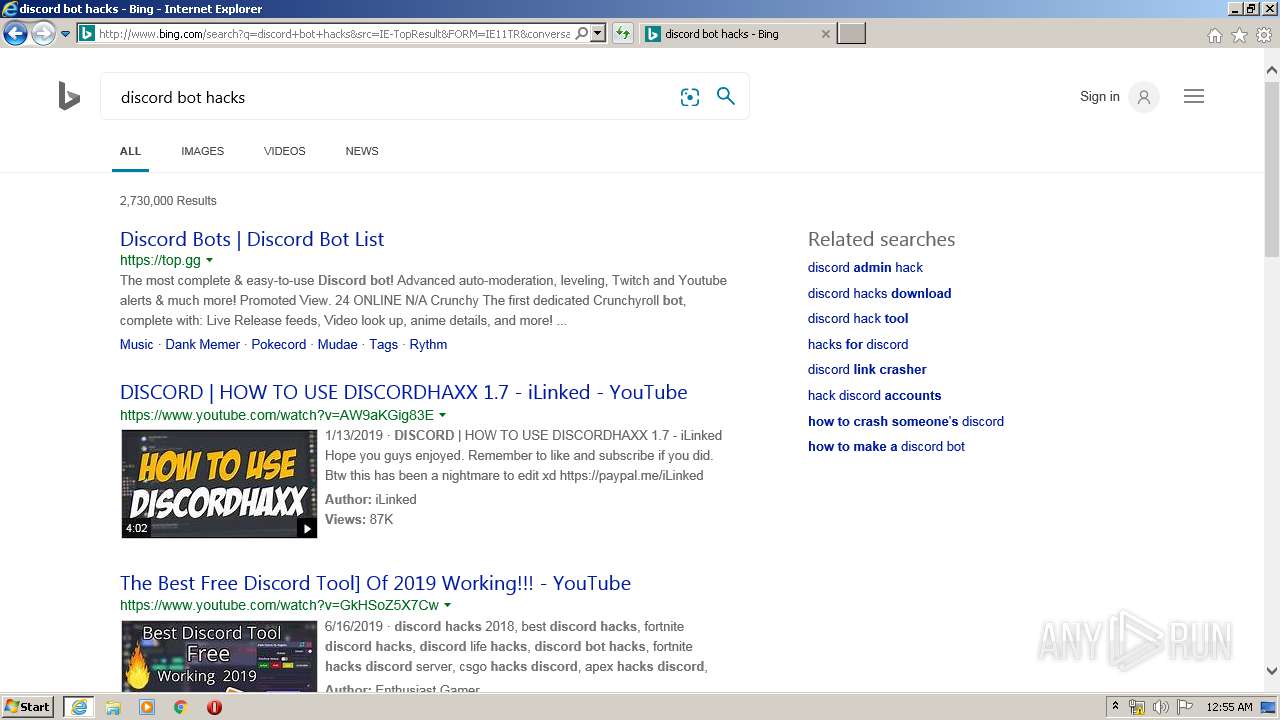
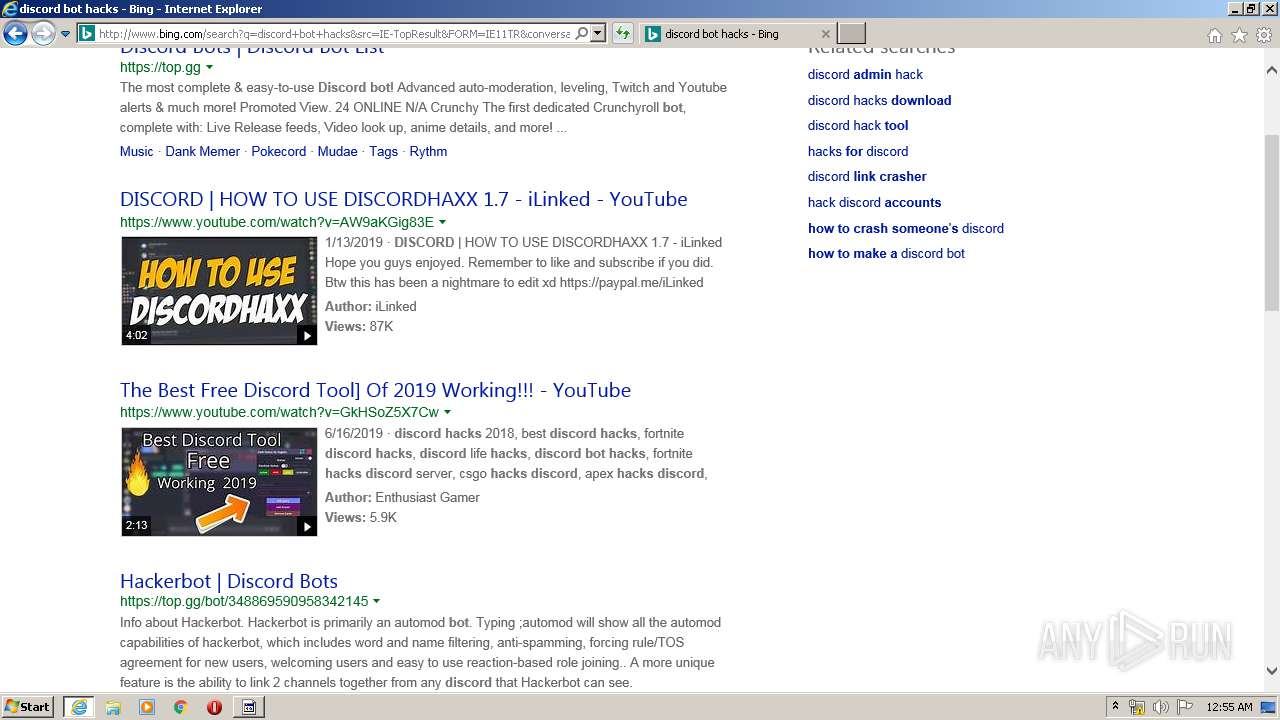
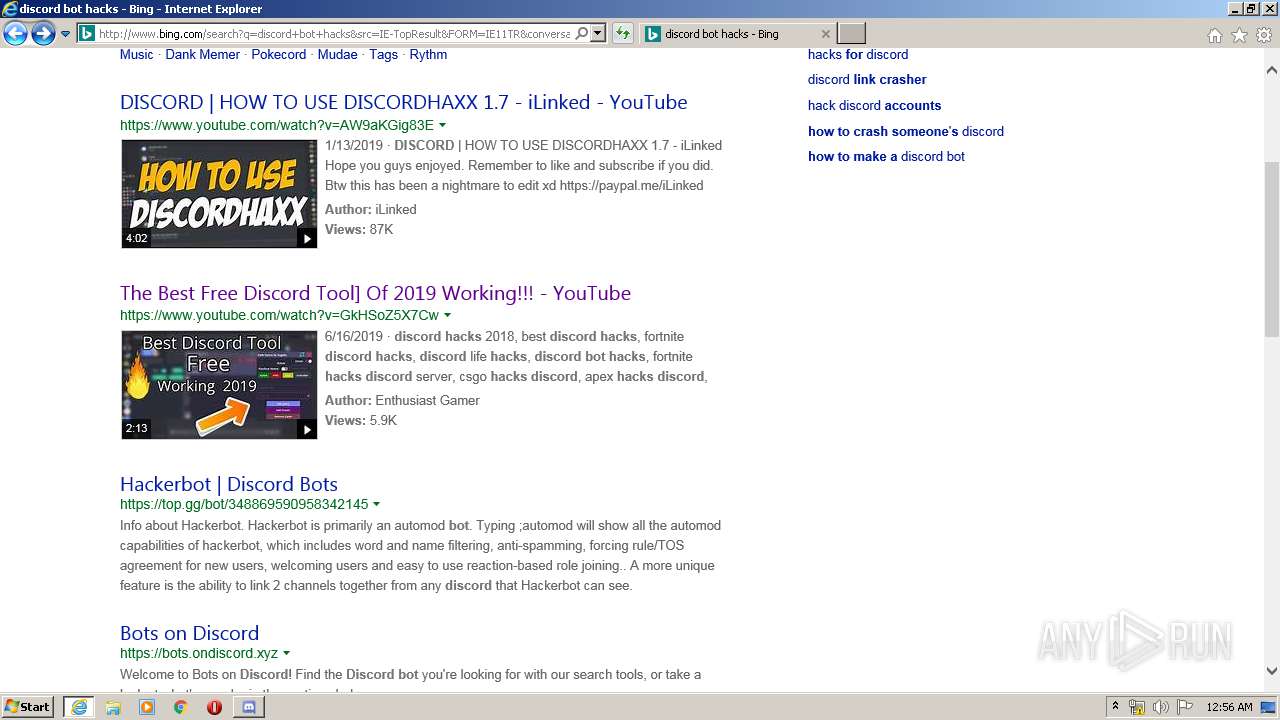
1712 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=discor&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
1712 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=discord&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
1712 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Z/28/cj,nj/3f1e2270/f8c6dd44.js | US | text | 773 b | whitelisted |
1712 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=discord&src=IE-TopResult&FORM=IE11TR&conversationid= | US | html | 38.2 Kb | whitelisted |
1712 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=disco&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
1712 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Z/2g/cj,nj/4c7364c5/40e1b425.js | US | text | 816 b | whitelisted |
1712 | iexplore.exe | POST | 204 | 204.79.197.200:80 | http://www.bing.com/fd/ls/lsp.aspx? | US | image | 11.2 Kb | whitelisted |
1712 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2Z/2M/cj,nj/93002ee5/ce33b6aa.js | US | text | 177 b | whitelisted |
1712 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/47/A/cj,nj/64cc4a49/e70a8ff8.js | US | text | 354 b | whitelisted |
1712 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5g/cj,nj/e3ca6b81/a77c5ed0.js?bu=Erkg2CCEIIcgnQWeIKAg6SCiIMsgpSDVIJUh3SC-H88ezR7BHw | US | text | 5.42 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1712 | iexplore.exe | 40.126.1.136:443 | login.microsoftonline.com | Microsoft Corporation | US | unknown |
1712 | iexplore.exe | 40.90.137.127:443 | login.live.com | Microsoft Corporation | US | unknown |
1712 | iexplore.exe | 2.16.106.113:80 | a4.bing.com | Akamai International B.V. | — | whitelisted |
1712 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1712 | iexplore.exe | 13.107.3.254:80 | 8aecaa58dd00fa0bf761e82f4d2c62b9.clo.footprintdns.com | Microsoft Corporation | US | whitelisted |
1712 | iexplore.exe | 104.18.24.243:80 | ocsp.msocsp.com | Cloudflare Inc | US | shared |
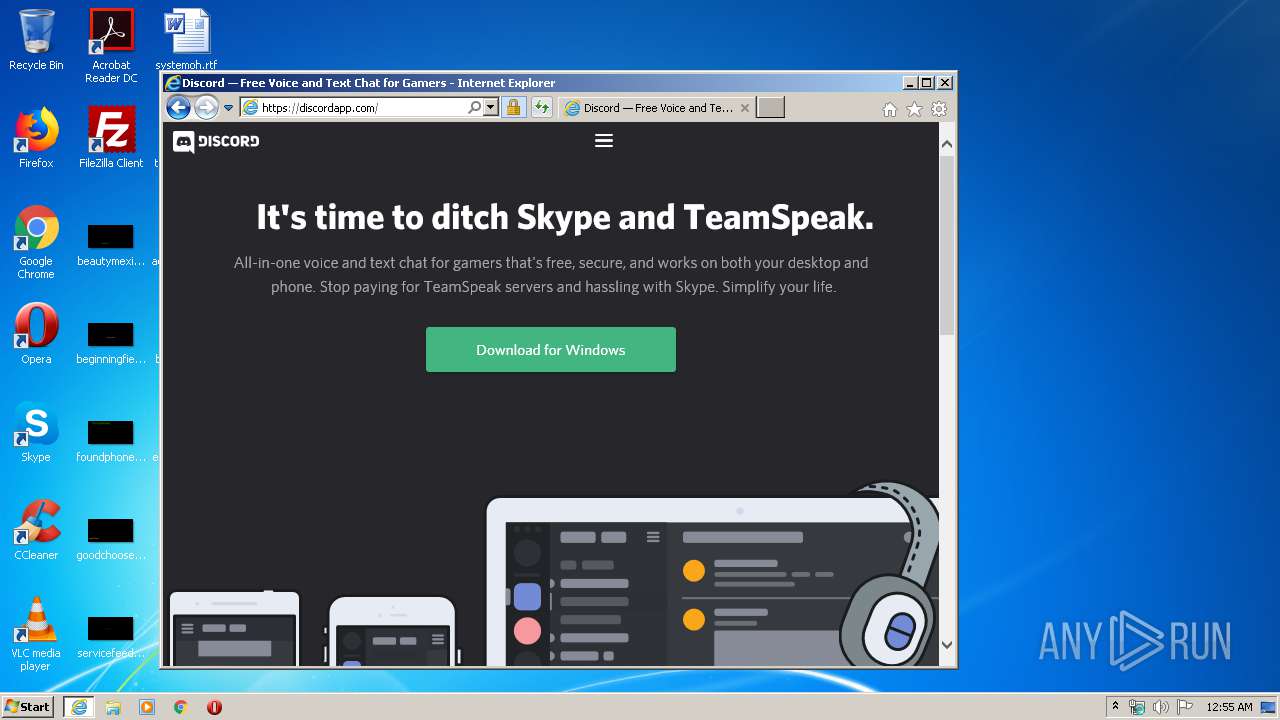
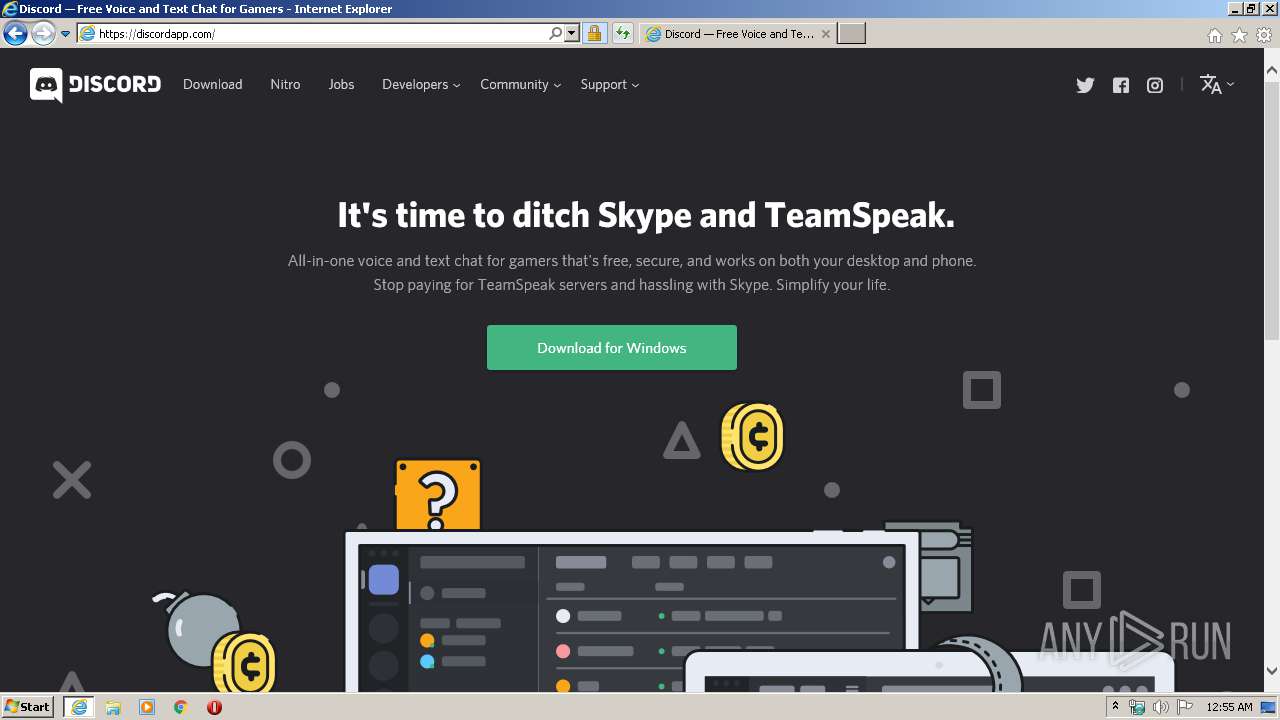
1712 | iexplore.exe | 162.159.134.233:443 | discordapp.com | Cloudflare Inc | — | shared |
1712 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1712 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
1712 | iexplore.exe | 216.58.207.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
a4.bing.com |
| whitelisted |
d2de9f6f639263daf26ec8cf66682f85.clo.footprintdns.com |
| unknown |
www2.bing.com |
| whitelisted |
8aecaa58dd00fa0bf761e82f4d2c62b9.clo.footprintdns.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1712 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
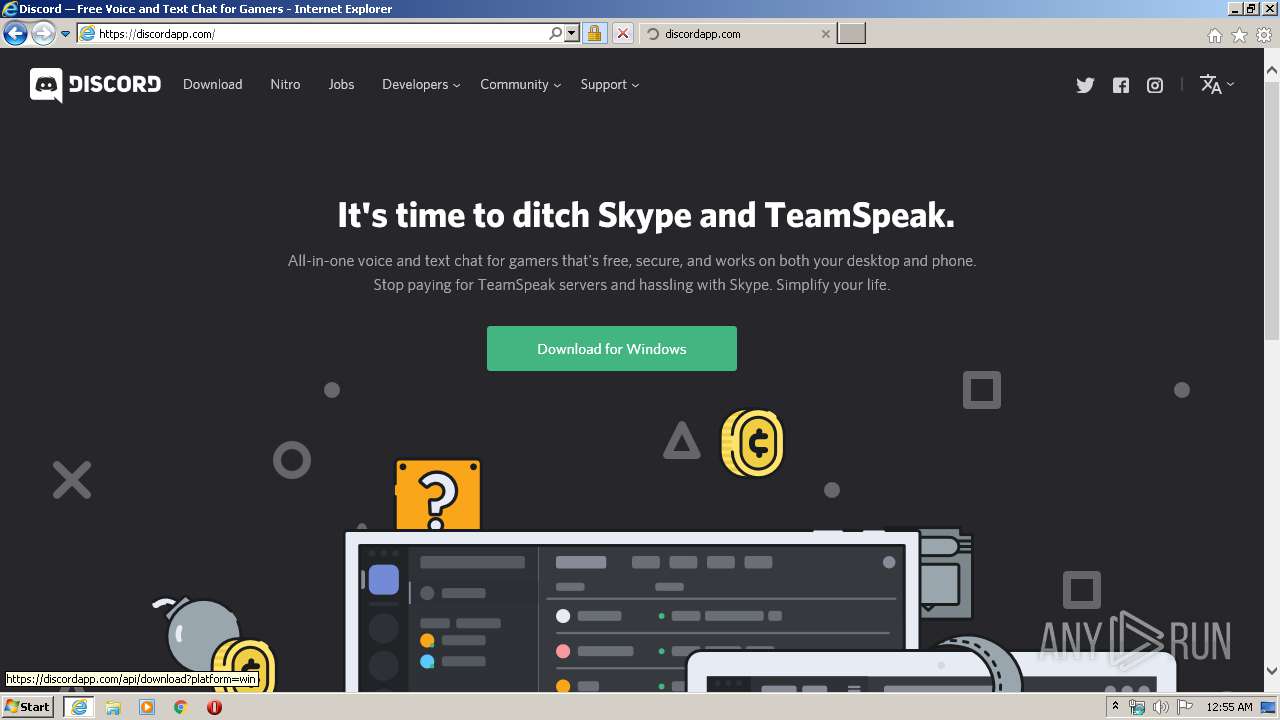
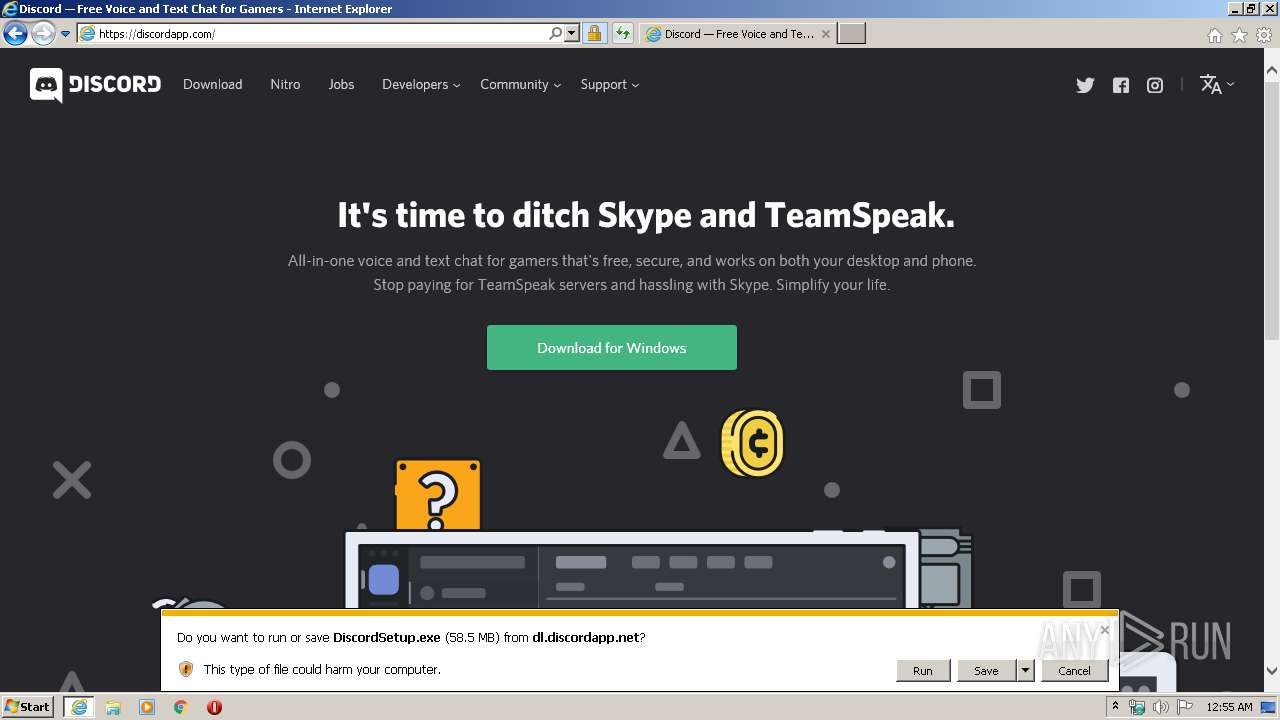
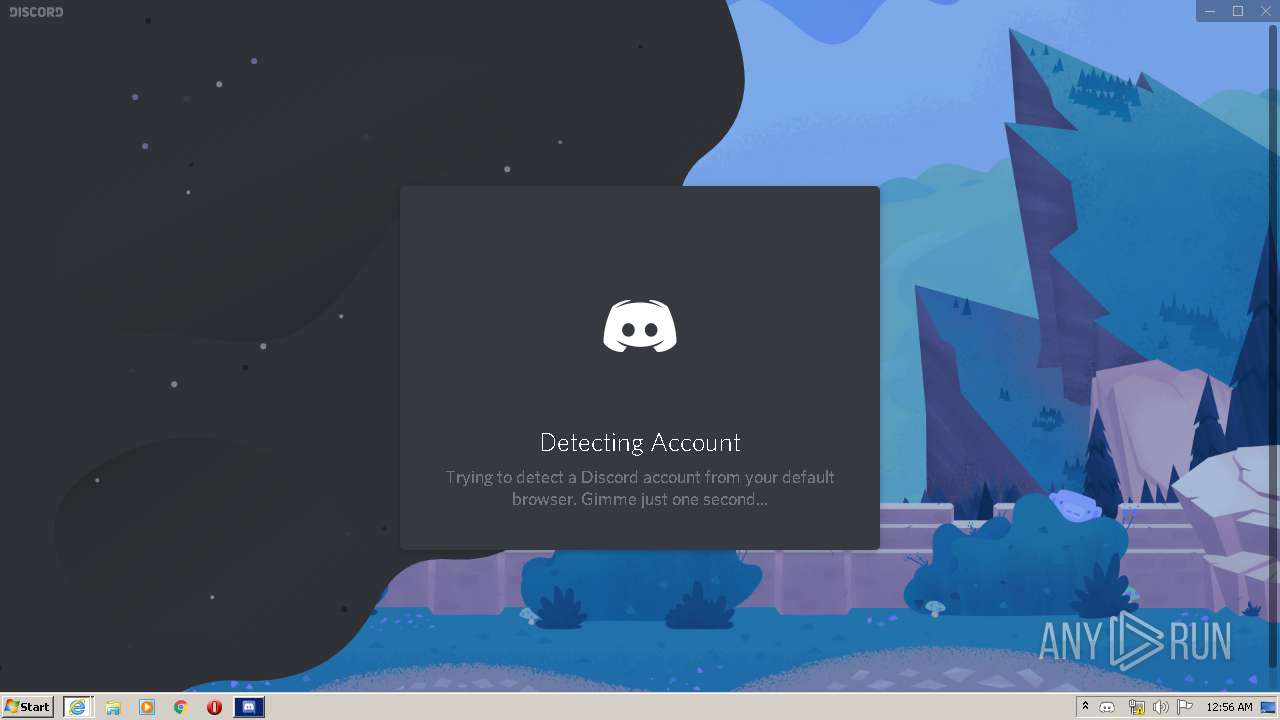
DiscordSetup.exe | Start up installer: |
DiscordSetup.exe | Want standard install |
DiscordSetup.exe | Elevated process: ?
|
Discord.exe | [3488:3540:0222/005638.602:VERBOSE1:crash_service_main.cc(81)] Session start. cmdline is [--reporter-url=https://sentry.io/api/146342/minidump/?sentry_key=384ce4413de74fe0be270abe03b2b35a --application-name=Discord "--crashes-directory=C:\Users\admin\AppData\Local\Temp\Discord Crashes" --v=1]
|
Discord.exe | [3488:3540:0222/005638.603:VERBOSE1:crash_service.cc(279)] checkpoint is C:\Users\admin\AppData\Local\Temp\Discord Crashes\crash_checkpoint.txt
server is https://sentry.io/api/146342/minidump/?sentry_key=384ce4413de74fe0be270abe03b2b35a
maximum 128 reports/day
reporter is electron-crash-service
|
Discord.exe | [3488:3540:0222/005638.603:VERBOSE1:crash_service.cc(275)] pipe name is \\.\pipe\Discord Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\Discord Crashes
|
Discord.exe | [3488:3540:0222/005638.603:VERBOSE1:crash_service_main.cc(95)] Ready to process crash requests
|
Discord.exe | [3488:3540:0222/005638.603:VERBOSE1:crash_service.cc(147)] window handle is 00140224
|
Discord.exe | [3488:2872:0222/005638.604:VERBOSE1:crash_service.cc(309)] client start. pid = 1412
|