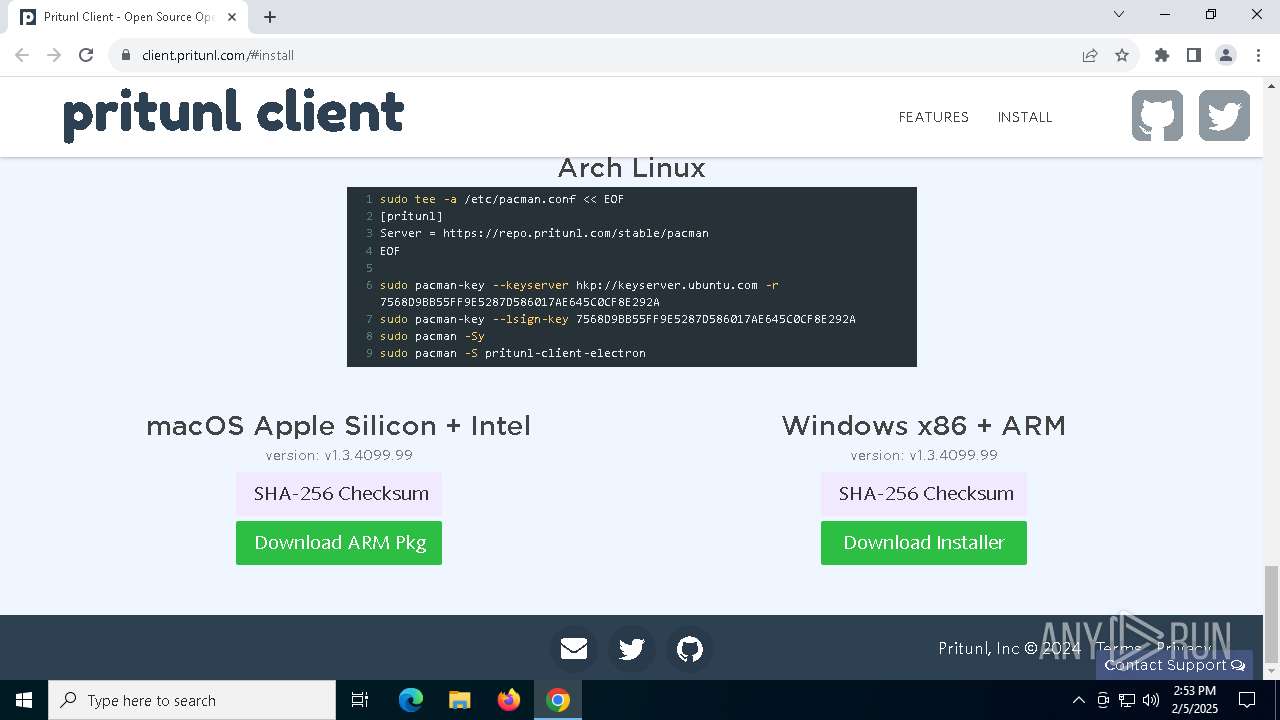
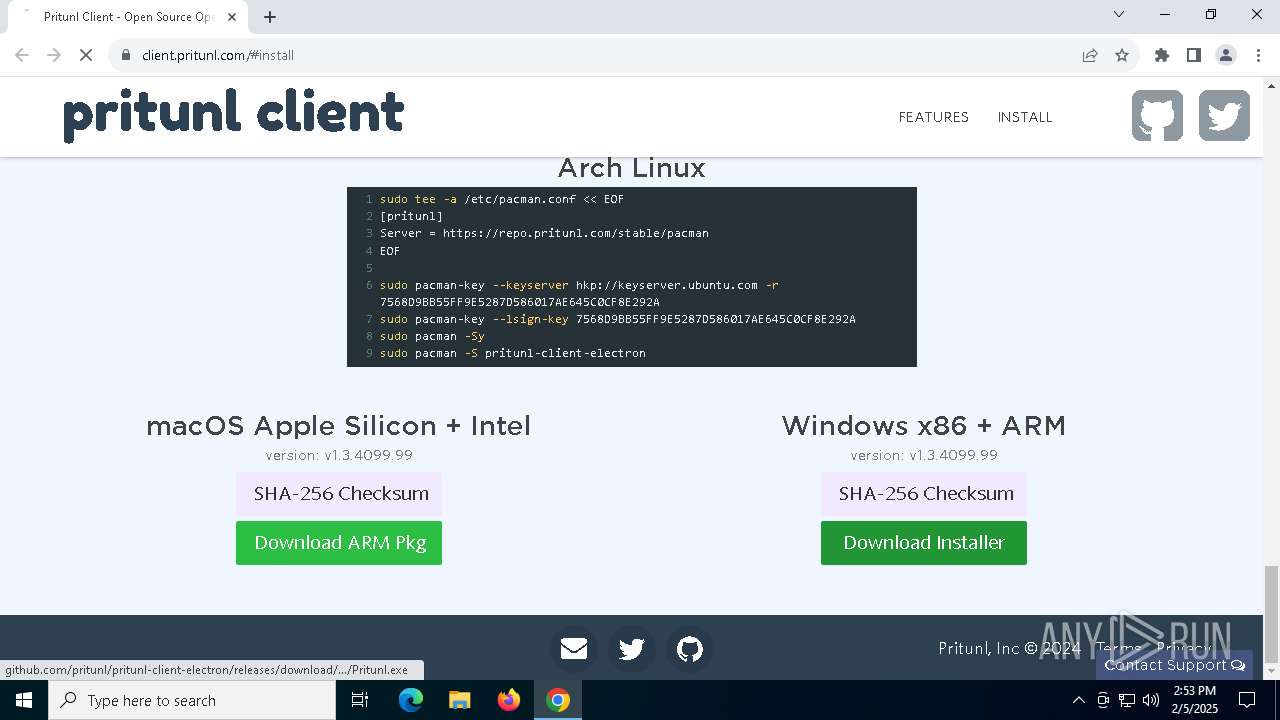
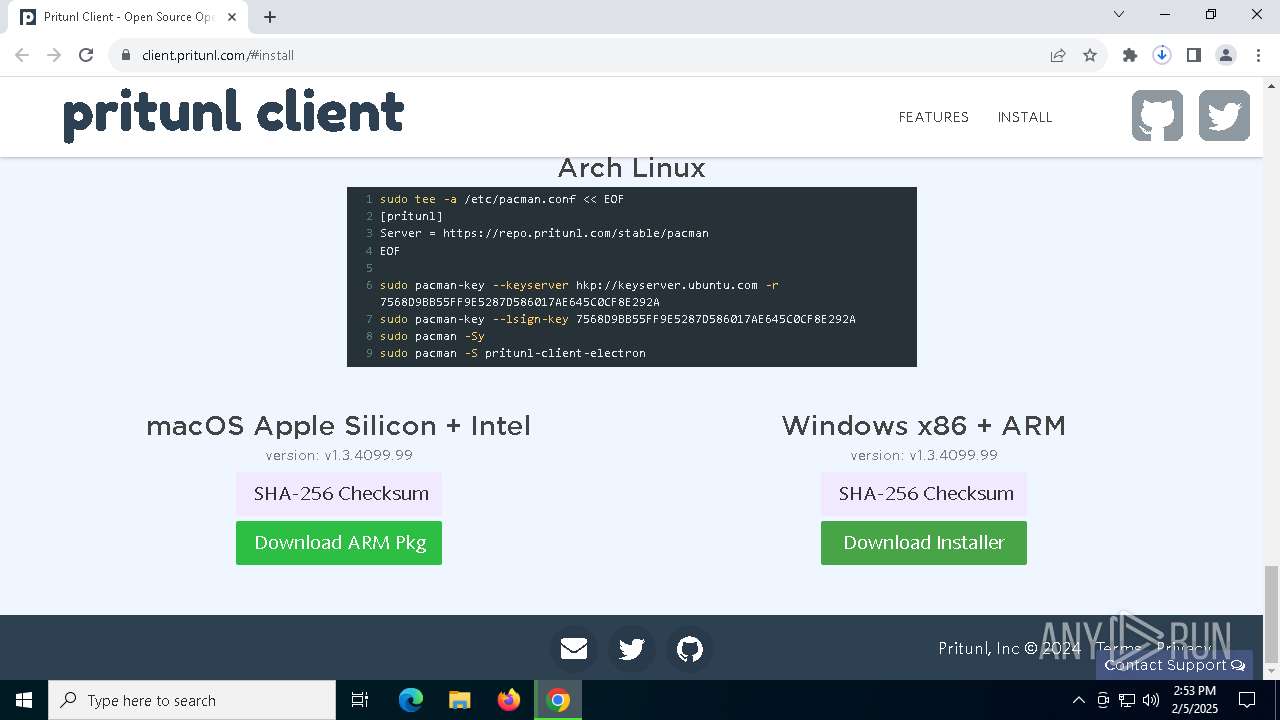
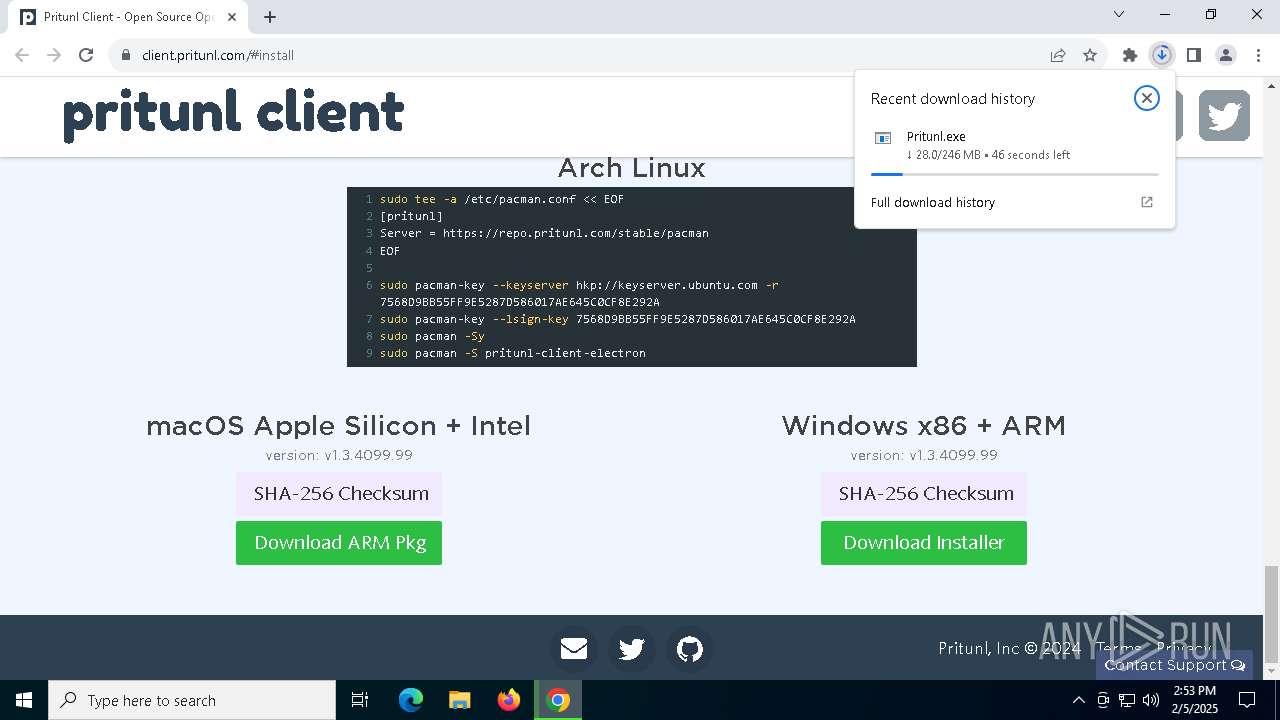
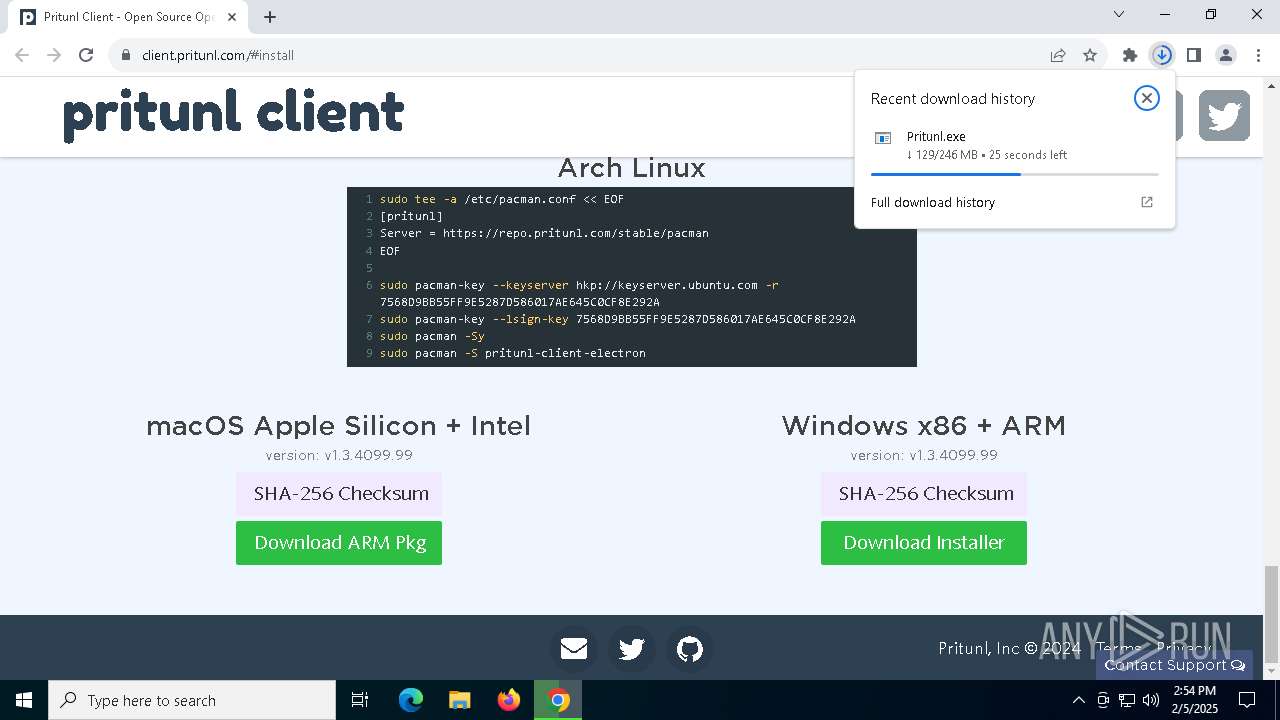
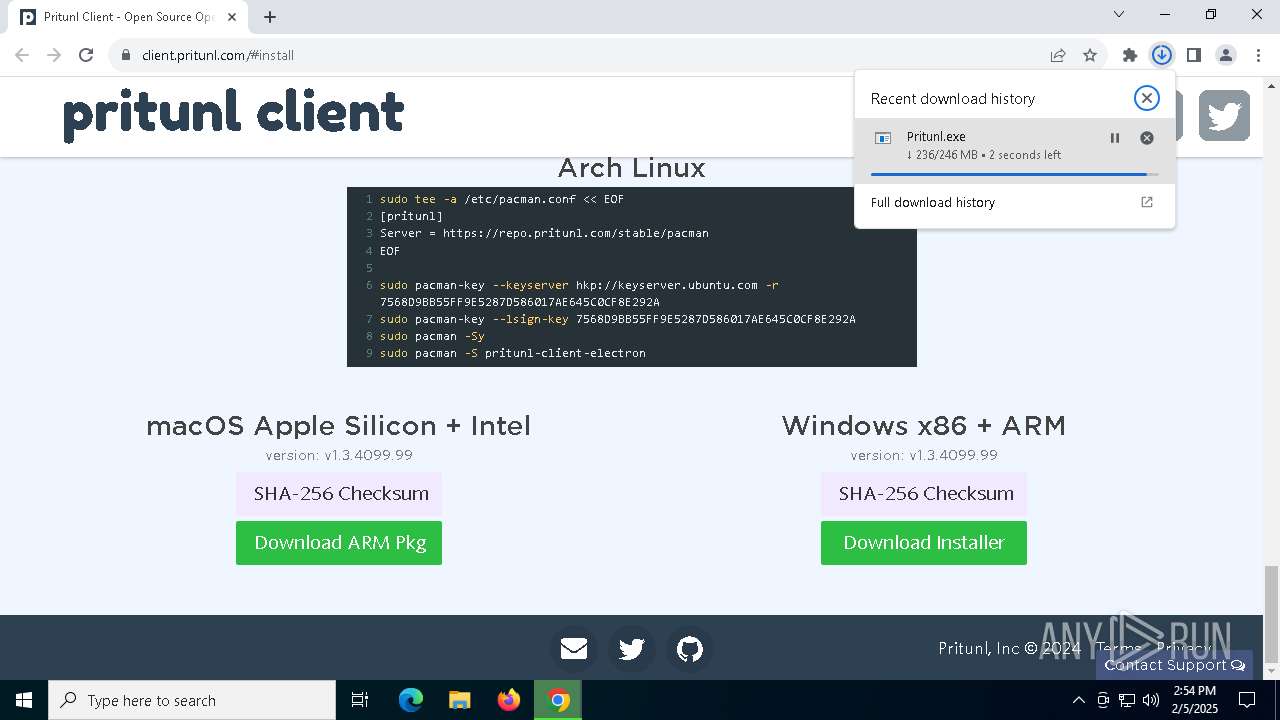
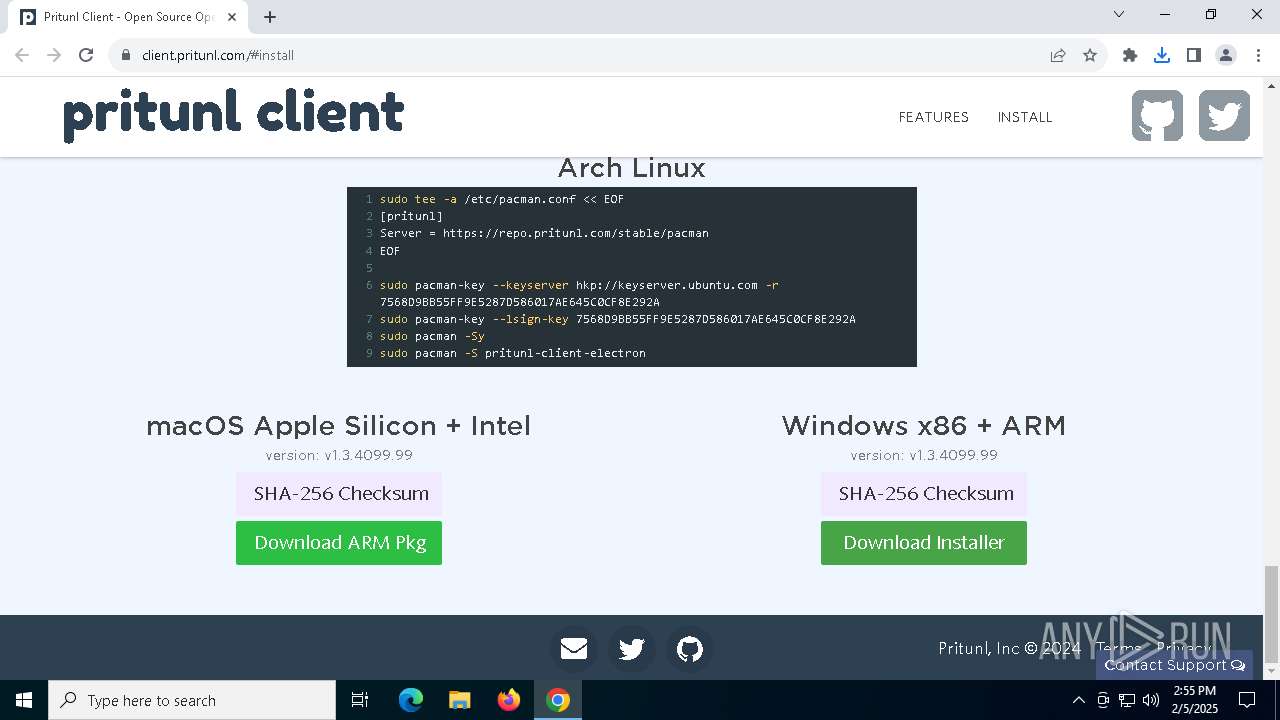
| URL: | client.pritunl.com/#install |
| Full analysis: | https://app.any.run/tasks/25d74dd1-f36e-4fd7-829a-2877403f2f8b |
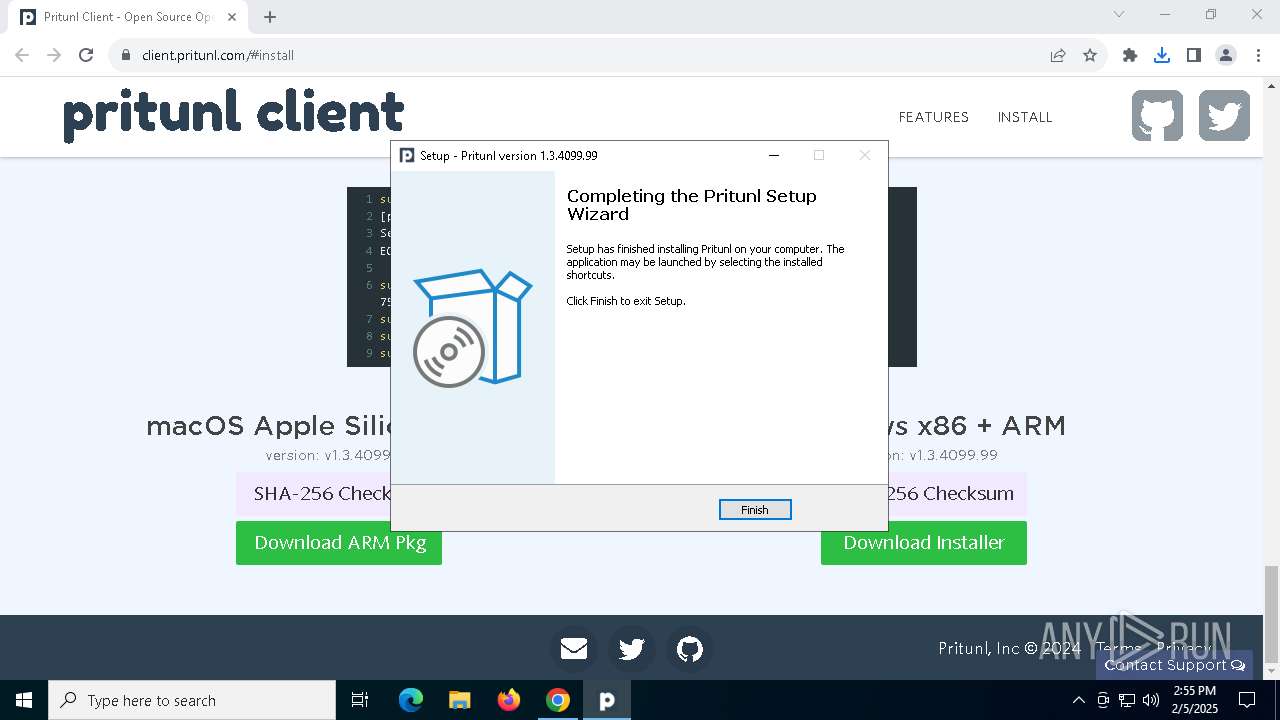
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2025, 14:53:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 65FC4DCCA11046797DC7813143C7B584 |
| SHA1: | 2F8E7913587359A9AC4238945F4A899D61E8EC95 |
| SHA256: | 0BCC0117B0F2E76167ECDFC14D02D9BE6629A58F70FA8575E583B29DD4A4313F |
| SSDEEP: | 3:Mx9yGvWEJJ:MxoGvWgJ |
MALICIOUS
Create files in the Startup directory
- Pritunl.tmp (PID: 1460)
SUSPICIOUS
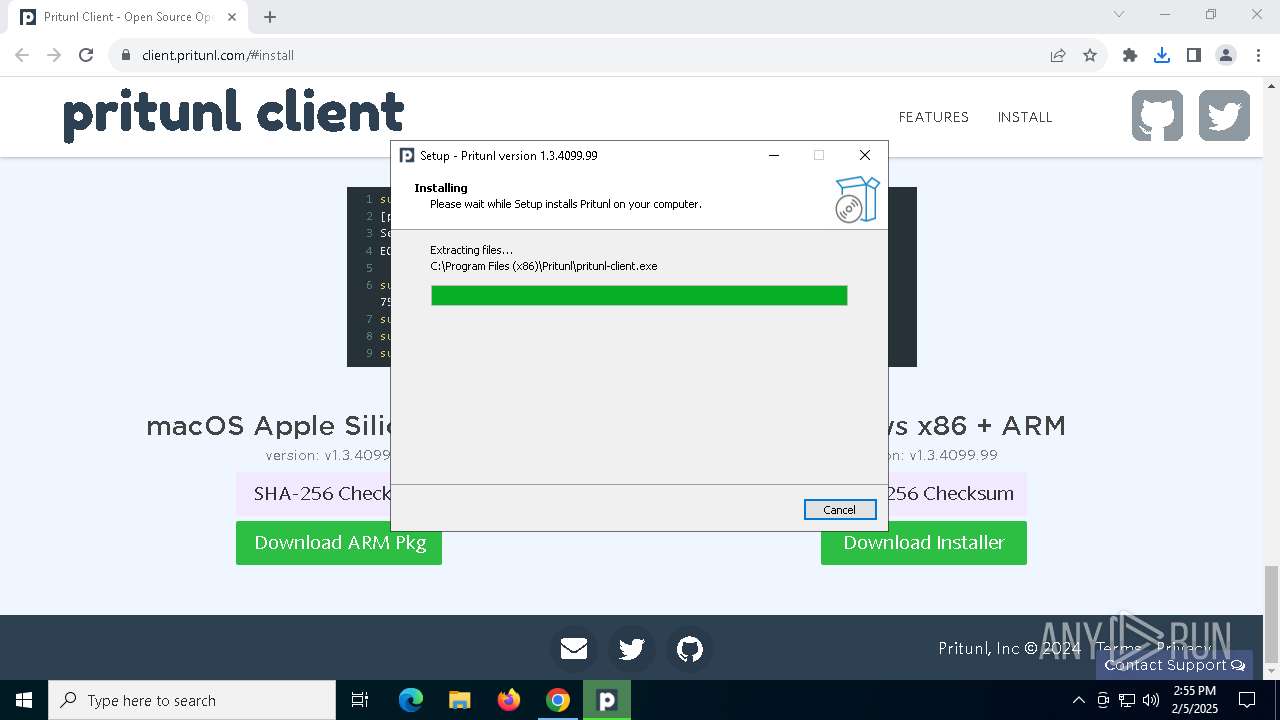
Executable content was dropped or overwritten
- Pritunl.exe (PID: 4052)
- Pritunl.exe (PID: 6888)
- Pritunl.tmp (PID: 1460)
- drvinst.exe (PID: 6684)
- pnputil.exe (PID: 5456)
Uses TASKKILL.EXE to kill process
- Pritunl.tmp (PID: 1460)
Drops a system driver (possible attempt to evade defenses)
- Pritunl.tmp (PID: 1460)
- pnputil.exe (PID: 5456)
- drvinst.exe (PID: 6684)
The process drops C-runtime libraries
- Pritunl.tmp (PID: 1460)
Starts SC.EXE for service management
- pritunl-service.exe (PID: 5208)
- pritunl-service.exe (PID: 6700)
Stops a currently running service
- sc.exe (PID: 4876)
- sc.exe (PID: 7036)
- sc.exe (PID: 1804)
- sc.exe (PID: 3172)
- sc.exe (PID: 2216)
- sc.exe (PID: 2992)
- sc.exe (PID: 5460)
- sc.exe (PID: 6728)
- sc.exe (PID: 644)
- sc.exe (PID: 6692)
- sc.exe (PID: 6912)
- sc.exe (PID: 6608)
Process drops legitimate windows executable
- Pritunl.tmp (PID: 1460)
Checks Windows Trust Settings
- drvinst.exe (PID: 6684)
Creates files in the driver directory
- drvinst.exe (PID: 6684)
Sets the service to start on system boot
- sc.exe (PID: 1200)
Windows service management via SC.EXE
- sc.exe (PID: 4444)
- sc.exe (PID: 5636)
- sc.exe (PID: 6456)
- sc.exe (PID: 3736)
- sc.exe (PID: 7052)
- sc.exe (PID: 6684)
- sc.exe (PID: 5652)
- sc.exe (PID: 6640)
- sc.exe (PID: 1868)
- sc.exe (PID: 6772)
- sc.exe (PID: 5096)
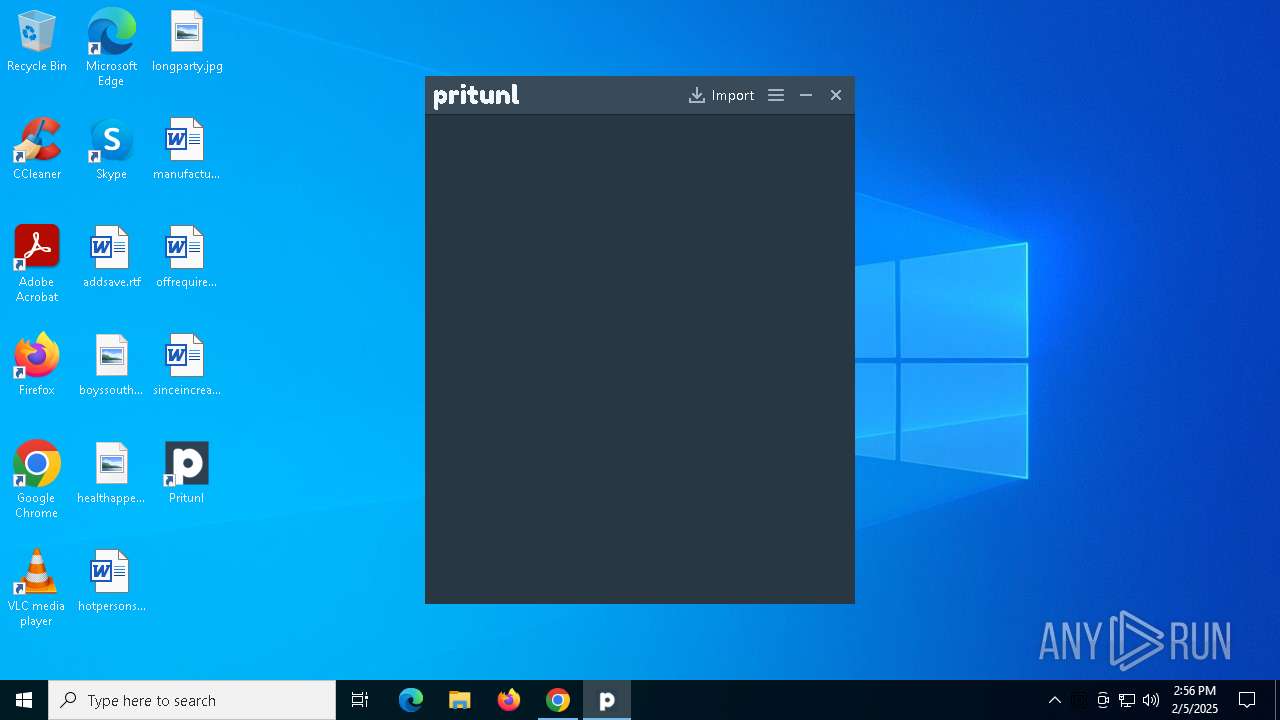
Executes as Windows Service
- pritunl-service.exe (PID: 6700)
Creates a new Windows service
- sc.exe (PID: 7004)
Adds/modifies Windows certificates
- pritunl-service.exe (PID: 6700)
Application launched itself
- pritunl.exe (PID: 3888)
INFO
Create files in a temporary directory
- Pritunl.exe (PID: 4052)
- Pritunl.exe (PID: 6888)
- Pritunl.tmp (PID: 1460)
- pnputil.exe (PID: 5456)
- pritunl.exe (PID: 3888)
Reads the computer name
- Pritunl.tmp (PID: 6700)
- Pritunl.tmp (PID: 1460)
- Pritunl.exe (PID: 6888)
- pritunl-service.exe (PID: 6700)
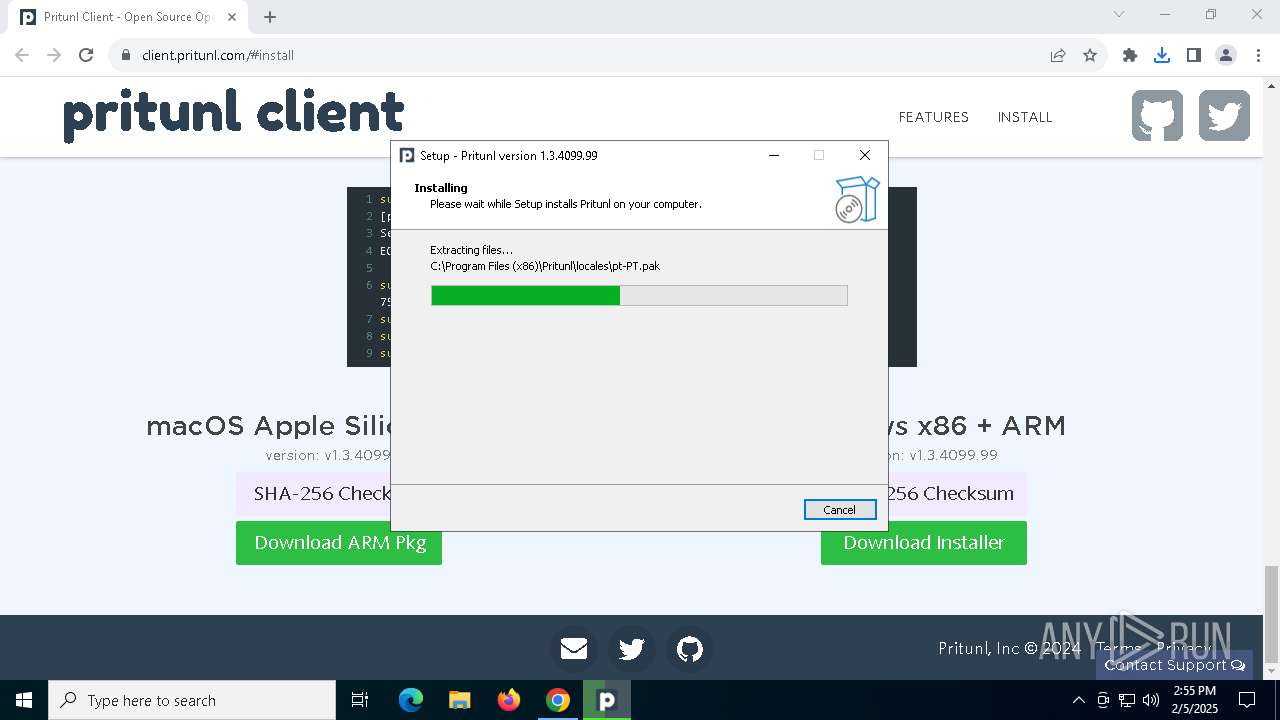
Checks supported languages
- Pritunl.tmp (PID: 6700)
- Pritunl.exe (PID: 6888)
- Pritunl.tmp (PID: 1460)
- pritunl-service.exe (PID: 5208)
- Pritunl.exe (PID: 4052)
- drvinst.exe (PID: 6684)
- tapctl.exe (PID: 7112)
- pritunl-service.exe (PID: 6700)
- tapctl.exe (PID: 1328)
- pritunl.exe (PID: 6520)
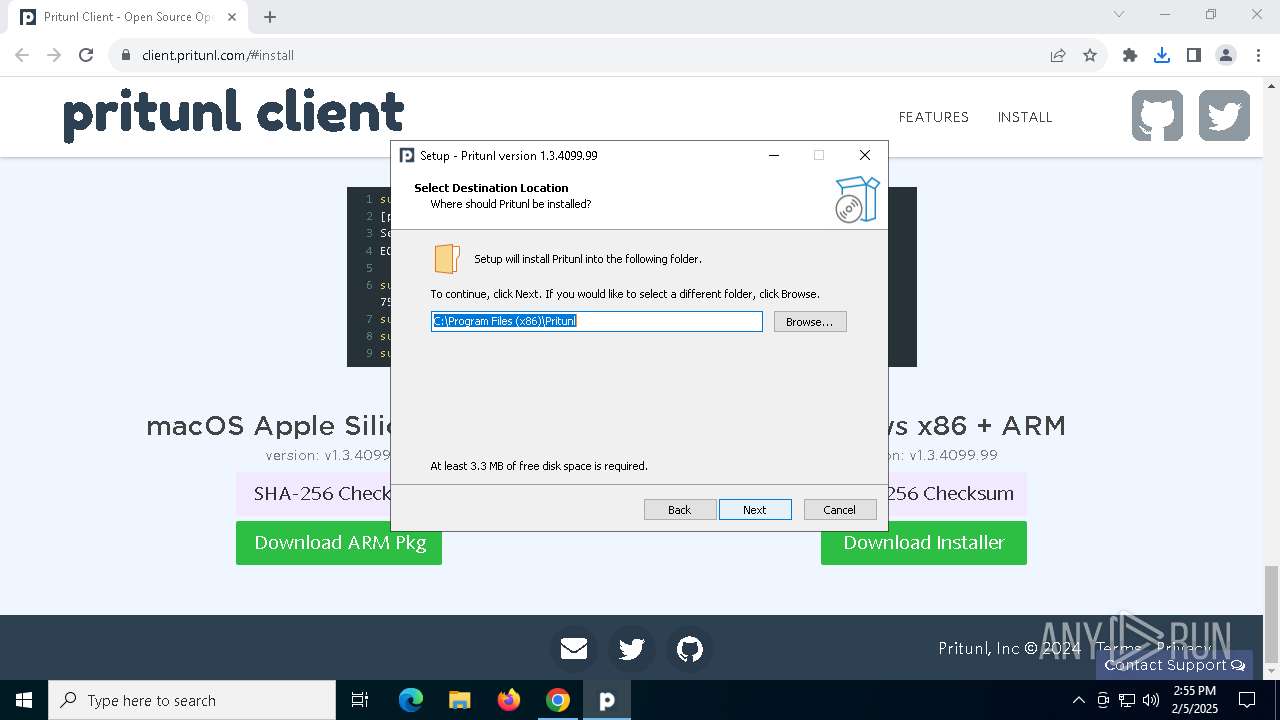
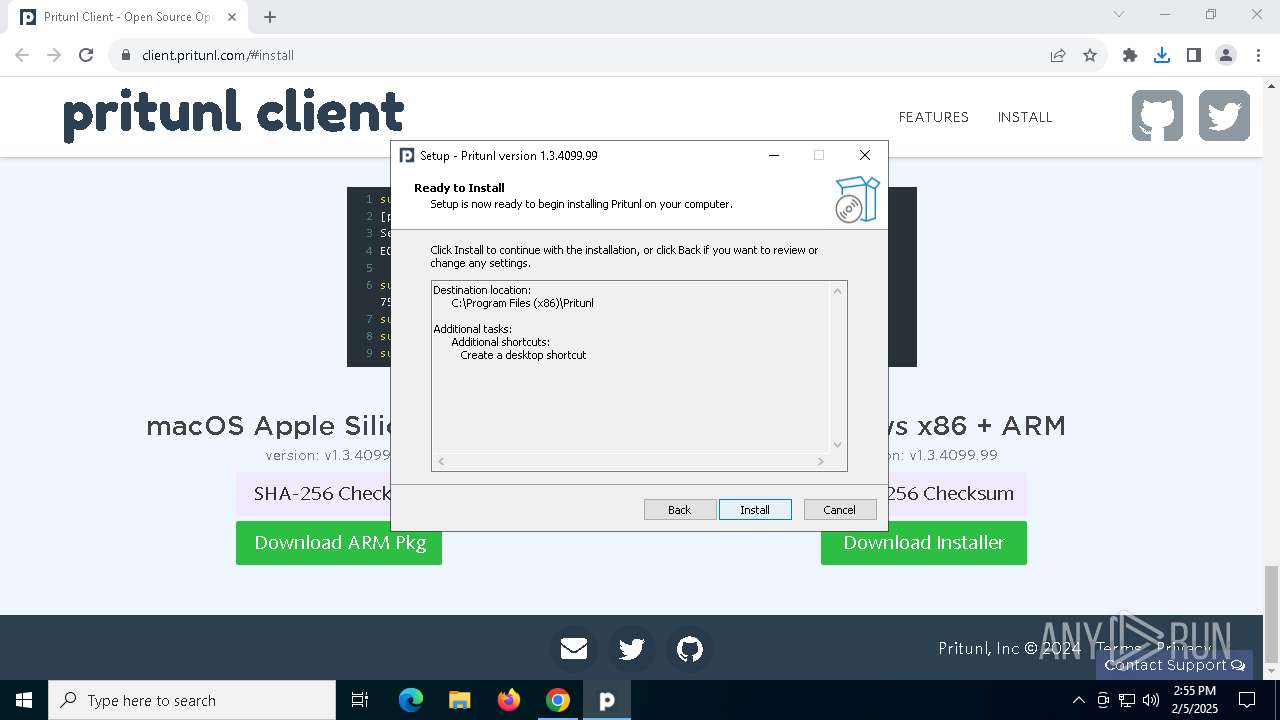
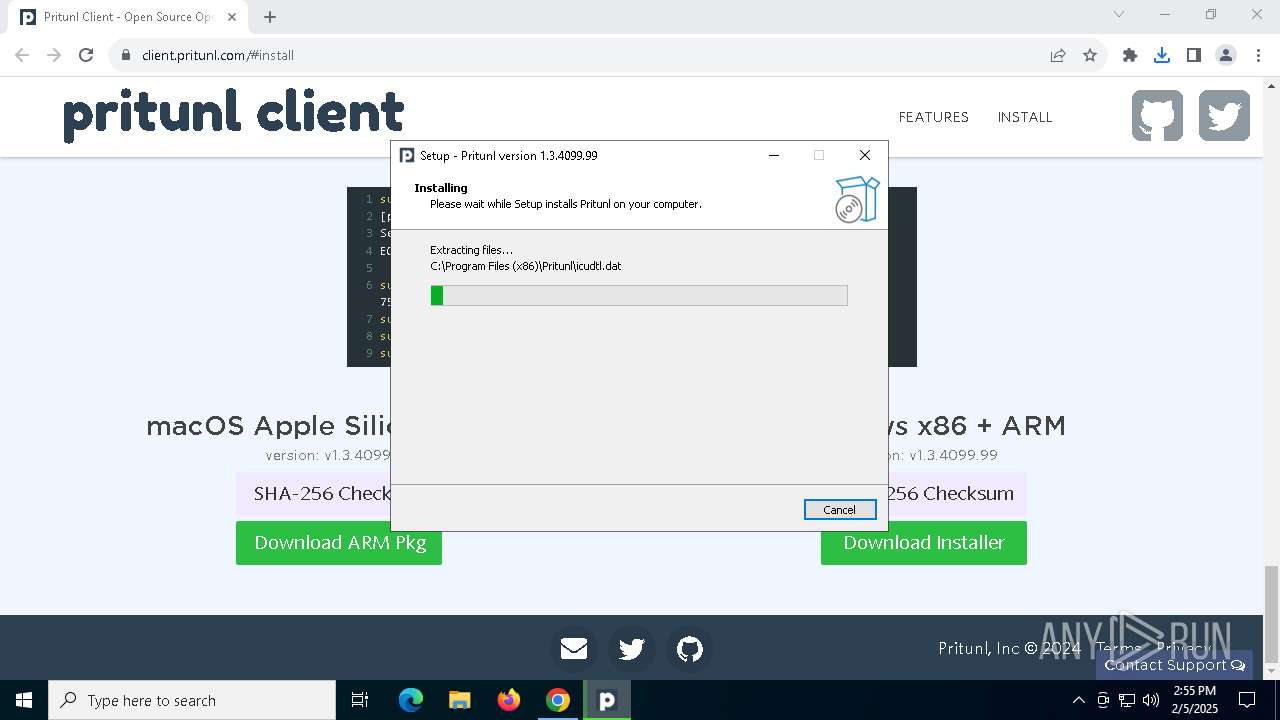
Creates files in the program directory
- Pritunl.tmp (PID: 1460)
- pritunl-service.exe (PID: 6700)
The sample compiled with english language support
- Pritunl.tmp (PID: 1460)
- pnputil.exe (PID: 5456)
- drvinst.exe (PID: 6684)
- chrome.exe (PID: 1796)
Compiled with Borland Delphi (YARA)
- Pritunl.tmp (PID: 1460)
Process checks computer location settings
- Pritunl.tmp (PID: 6700)
Detects InnoSetup installer (YARA)
- Pritunl.tmp (PID: 1460)
Executable content was dropped or overwritten
- chrome.exe (PID: 5752)
- chrome.exe (PID: 1796)
Creates a software uninstall entry
- Pritunl.tmp (PID: 1460)
Application launched itself
- chrome.exe (PID: 5752)
Reads the machine GUID from the registry
- drvinst.exe (PID: 6684)
- pritunl.exe (PID: 3888)
- pritunl-service.exe (PID: 6700)
Drops encrypted JS script (Microsoft Script Encoder)
- pritunl-service.exe (PID: 5208)
- pritunl-service.exe (PID: 6700)
Reads the software policy settings
- pritunl-service.exe (PID: 6700)
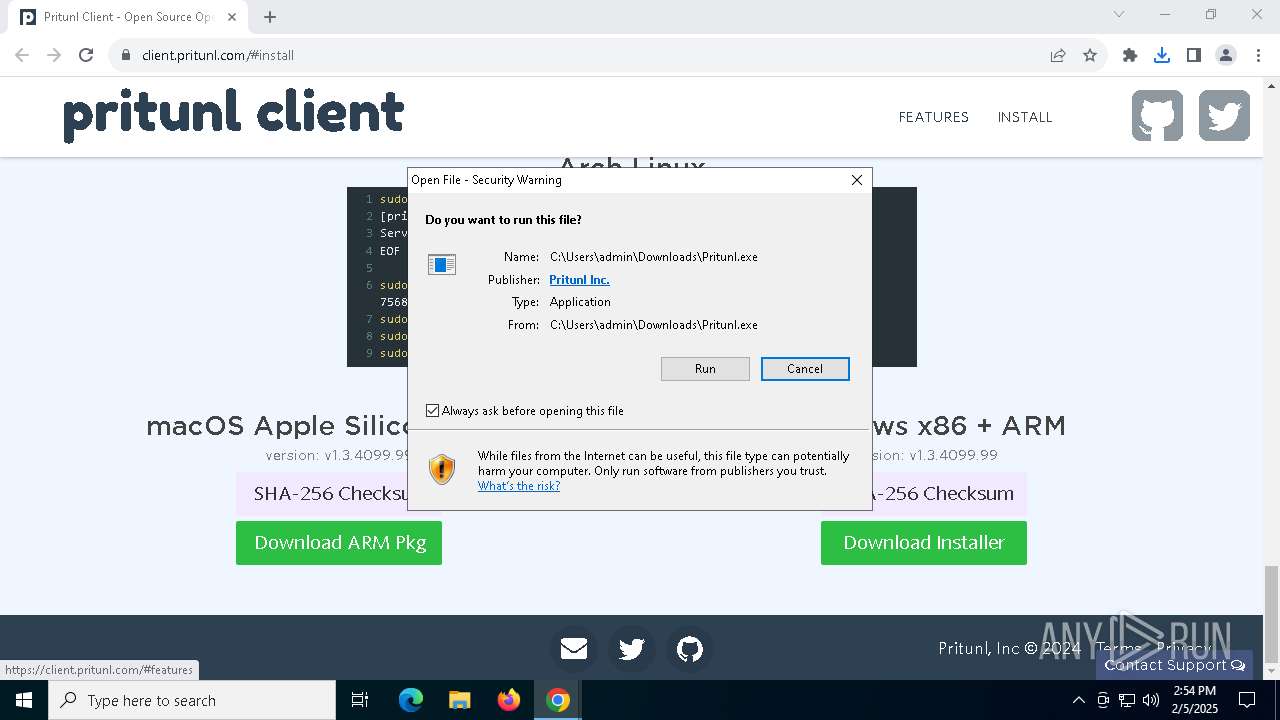
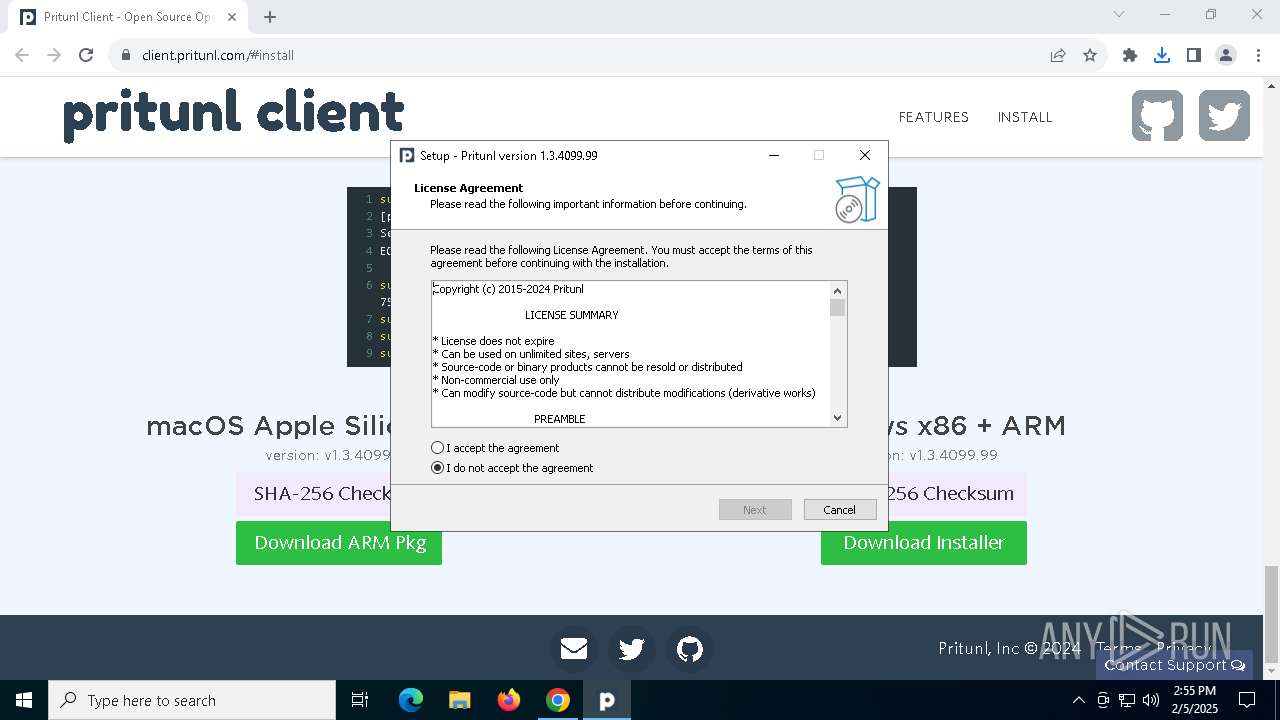
Manual execution by a user
- pritunl.exe (PID: 3888)
Checks proxy server information
- pritunl.exe (PID: 3888)
Creates files or folders in the user directory
- pritunl.exe (PID: 3888)
- pritunl.exe (PID: 5828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
228
Monitored processes
90
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | sc.exe stop WireGuardTunnel$pritunl3 | C:\Windows\System32\sc.exe | — | pritunl-service.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | sc.exe config pritunl start=auto "displayname=Pritunl Client Helper Service" "binpath=\"C:\Program Files (x86)\Pritunl\pritunl-service.exe\"" | C:\Windows\System32\sc.exe | — | pritunl-service.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1304 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Pritunl\openvpn\tapctl.exe" list | C:\Program Files (x86)\Pritunl\openvpn\tapctl.exe | — | pritunl-service.exe | |||||||||||
User: SYSTEM Company: The OpenVPN Project Integrity Level: SYSTEM Description: Utility to manipulate TUN/TAP adapters on Windows Exit code: 0 Version: 2.6.12.0 Modules
| |||||||||||||||
| 1328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5456 --field-trial-handle=1940,i,17049331827235107557,12174176349149151584,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1460 | "C:\Users\admin\AppData\Local\Temp\is-959N8.tmp\Pritunl.tmp" /SL5="$802DE,256551874,863744,C:\Users\admin\Downloads\Pritunl.exe" /SPAWNWND=$802A8 /NOTIFYWND=$70304 | C:\Users\admin\AppData\Local\Temp\is-959N8.tmp\Pritunl.tmp | Pritunl.exe | ||||||||||||
User: admin Company: Pritunl Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3536 --field-trial-handle=1940,i,17049331827235107557,12174176349149151584,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
20 799
Read events
20 715
Write events
55
Delete events
29
Modification events
| (PID) Process: | (5752) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5752) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5752) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5752) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5752) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3692) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000040F14CEADD77DB01 | |||
| (PID) Process: | (5752) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (5752) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (5752) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (5752) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
Executable files
49
Suspicious files
521
Text files
51
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF13cd07.TMP | — | |
MD5:— | SHA256:— | |||
| 5752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF13cd07.TMP | — | |
MD5:— | SHA256:— | |||
| 5752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF13cd07.TMP | — | |
MD5:— | SHA256:— | |||
| 5752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF13cd07.TMP | — | |
MD5:— | SHA256:— | |||
| 5752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF13cd36.TMP | — | |
MD5:— | SHA256:— | |||
| 5752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
77
DNS requests
81
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6732 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6732 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6968 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
6968 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
6968 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
5752 | chrome.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
6968 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | unknown | — | — | whitelisted |
6968 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6968 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.136:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5752 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1852 | chrome.exe | 104.26.14.194:443 | client.pritunl.com | CLOUDFLARENET | US | unknown |
1852 | chrome.exe | 108.177.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.pritunl.com |
| unknown |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cloud.typography.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
1852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
1852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
1852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
1852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
1852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
1852 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |