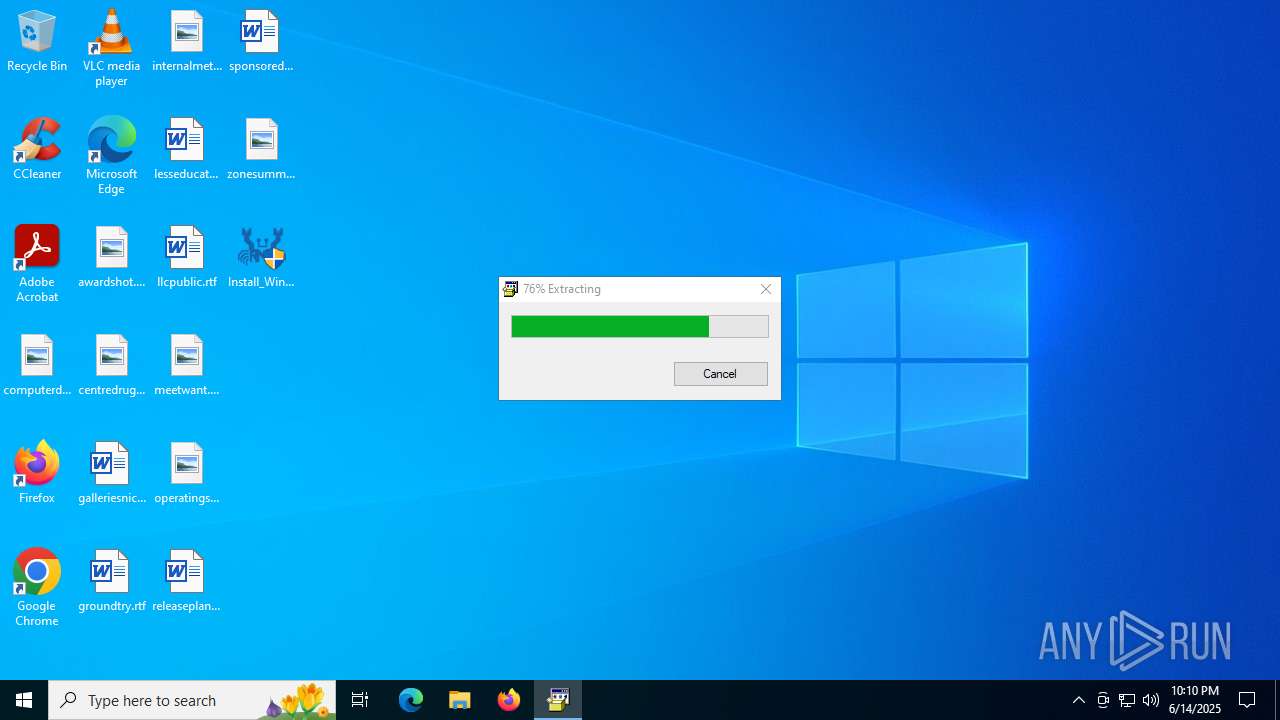
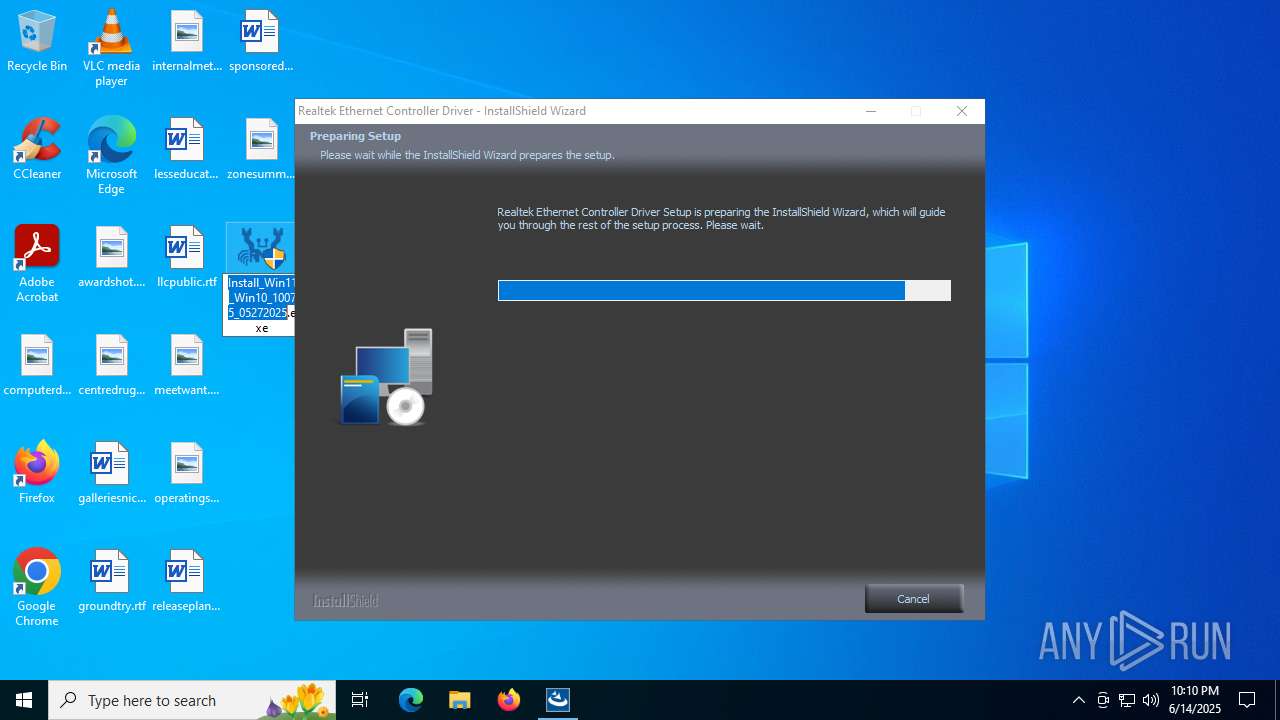
| File name: | Install_Win11_Win10_10075_05272025.exe |
| Full analysis: | https://app.any.run/tasks/0aea80f9-f2c2-414a-bf3e-3be093e350f0 |
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2025, 22:10:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 55153247B5B032ED9B46A2AEB0A591F8 |
| SHA1: | 912481D478A354072D53FD708CB54EE4E37D9B20 |
| SHA256: | 0BC6FE69018FBE94623B134461A2CB586D2DA6ED642B5E297170629AC4EC4AA6 |
| SSDEEP: | 98304:2rM94ikkrFFNhC2WsKDH/ZXm1TofSBVdlTD7UnhnD7YGkWnbwcKhcb6uwDhQF9TH:jVi81E |
MALICIOUS
No malicious indicators.SUSPICIOUS
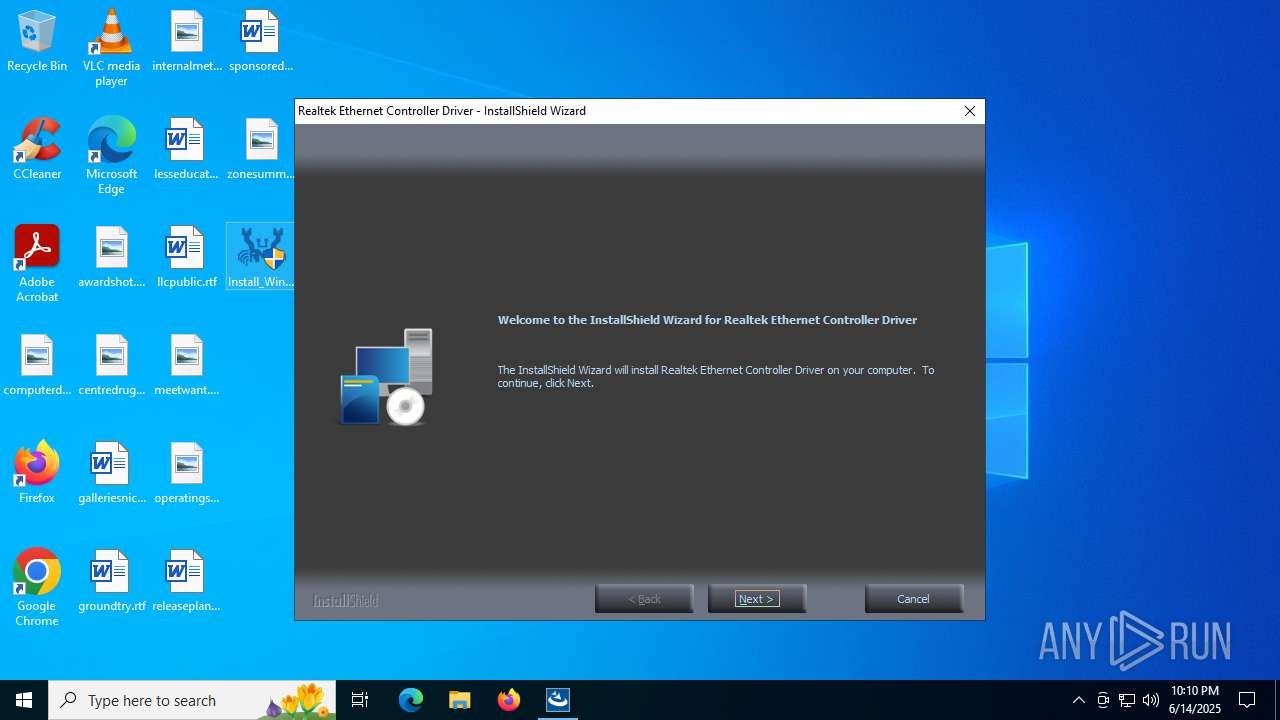
Executable content was dropped or overwritten
- Install_Win11_Win10_10075_05272025.exe (PID: 5168)
- setup.exe (PID: 2980)
- setup.exe (PID: 4580)
- RTINSTALLER64.EXE (PID: 2632)
- drvinst.exe (PID: 4684)
Drops a system driver (possible attempt to evade defenses)
- Install_Win11_Win10_10075_05272025.exe (PID: 5168)
- setup.exe (PID: 4580)
- RTINSTALLER64.EXE (PID: 2632)
- drvinst.exe (PID: 4684)
Starts itself from another location
- setup.exe (PID: 2980)
Searches for installed software
- setup.exe (PID: 4580)
- dllhost.exe (PID: 3936)
There is functionality for taking screenshot (YARA)
- setup.exe (PID: 4580)
- setup.exe (PID: 2980)
Executes as Windows Service
- VSSVC.exe (PID: 3980)
INFO
Reads the computer name
- Install_Win11_Win10_10075_05272025.exe (PID: 5168)
- setup.exe (PID: 2980)
- setup.exe (PID: 4580)
- ISBEW64.exe (PID: 1728)
- ISBEW64.exe (PID: 6676)
- ISBEW64.exe (PID: 4768)
- ISBEW64.exe (PID: 2612)
- ISBEW64.exe (PID: 1472)
- ISBEW64.exe (PID: 4080)
Checks supported languages
- setup.exe (PID: 2980)
- Install_Win11_Win10_10075_05272025.exe (PID: 5168)
- setup.exe (PID: 4580)
- ISBEW64.exe (PID: 1728)
- ISBEW64.exe (PID: 2612)
- ISBEW64.exe (PID: 4080)
- ISBEW64.exe (PID: 6676)
- ISBEW64.exe (PID: 4768)
- ISBEW64.exe (PID: 1472)
Create files in a temporary directory
- setup.exe (PID: 2980)
- Install_Win11_Win10_10075_05272025.exe (PID: 5168)
- setup.exe (PID: 4580)
The sample compiled with english language support
- Install_Win11_Win10_10075_05272025.exe (PID: 5168)
- setup.exe (PID: 2980)
- setup.exe (PID: 4580)
Reads Environment values
- setup.exe (PID: 4580)
Manages system restore points
- SrTasks.exe (PID: 6688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (46.7) |
|---|---|---|
| .exe | | | Winzip Win32 self-extracting archive (generic) (38.8) |
| .exe | | | Win32 Executable (generic) (7.6) |
| .exe | | | Generic Win/DOS Executable (3.3) |
| .exe | | | DOS Executable Generic (3.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:11:29 18:00:00+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 107520 |
| InitializedDataSize: | 183808 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x19e1c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
155
Monitored processes
19
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Program Files (x86)\Realtek\NICDRV_8169\RTINSTALLER64.EXE" /CHKNICEXIST /VISTA8169 /chkvid 10ec /chkpid 8168 /chksvid 0000 /chkssid 0000 | C:\Program Files (x86)\Realtek\NICDRV_8169\RTINSTALLER64.EXE | — | setup.exe | |||||||||||
User: admin Company: Realtek Semiconductor Corp. Integrity Level: HIGH Description: RTInstaller Exit code: 0 Version: 1.0.0.95 Modules
| |||||||||||||||
| 1472 | C:\Users\admin\AppData\Local\Temp\{FE068DA1-6F72-463E-A2BD-F4B0ACF900CD}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{EC5D84BD-0445-4537-8BC9-54084A771609} | C:\Users\admin\AppData\Local\Temp\{FE068DA1-6F72-463E-A2BD-F4B0ACF900CD}\ISBEW64.exe | — | setup.exe | |||||||||||
User: admin Company: Flexera Integrity Level: HIGH Description: InstallShield (R) 64-bit Setup Engine Version: 29.0.111 Modules
| |||||||||||||||
| 1728 | C:\Users\admin\AppData\Local\Temp\{FE068DA1-6F72-463E-A2BD-F4B0ACF900CD}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{298BCA1D-4114-48C7-B63D-6669F1080195} | C:\Users\admin\AppData\Local\Temp\{FE068DA1-6F72-463E-A2BD-F4B0ACF900CD}\ISBEW64.exe | — | setup.exe | |||||||||||
User: admin Company: Flexera Integrity Level: HIGH Description: InstallShield (R) 64-bit Setup Engine Version: 29.0.111 Modules
| |||||||||||||||
| 2612 | C:\Users\admin\AppData\Local\Temp\{FE068DA1-6F72-463E-A2BD-F4B0ACF900CD}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{B115A3BA-491C-4D59-B472-D9BE8041CD03} | C:\Users\admin\AppData\Local\Temp\{FE068DA1-6F72-463E-A2BD-F4B0ACF900CD}\ISBEW64.exe | — | setup.exe | |||||||||||
User: admin Company: Flexera Integrity Level: HIGH Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 29.0.111 Modules
| |||||||||||||||
| 2612 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | "C:\Program Files (x86)\Realtek\NICDRV_8169\RTINSTALLER64.EXE" /I /NCFI /VISTA8169 /X64 /f WIN10\rt640x64.inf | C:\Program Files (x86)\Realtek\NICDRV_8169\RTINSTALLER64.EXE | setup.exe | ||||||||||||
User: admin Company: Realtek Semiconductor Corp. Integrity Level: HIGH Description: RTInstaller Exit code: 0 Version: 1.0.0.95 Modules
| |||||||||||||||
| 2732 | "C:\Users\admin\Desktop\Install_Win11_Win10_10075_05272025.exe" | C:\Users\admin\Desktop\Install_Win11_Win10_10075_05272025.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2808 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2980 | .\setup.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\setup.exe | Install_Win11_Win10_10075_05272025.exe | ||||||||||||
User: admin Company: Realtek Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Version: 1.0.0.38 Modules
| |||||||||||||||
| 3936 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 491
Read events
8 287
Write events
183
Delete events
21
Modification events
| (PID) Process: | (4580) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | delete value | Name: | %IS_PREREQ%-Realtek Ethernet Controller Driver |
Value: | |||
| (PID) Process: | (4580) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion |
| Operation: | delete value | Name: | %IS_PREREQF%-Realtek Ethernet Controller Driver |
Value: | |||
| (PID) Process: | (4580) setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | ISSetupPrerequisistes |
Value: | |||
| (PID) Process: | (4580) setup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000007A7B5D3379DDDB01E4110000F40F0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3936) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000009250B33379DDDB01600F00005C0E0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3936) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000045B4B53379DDDB01600F0000000E0000E8030000010000000000000000000000707499010CE25945815C0862984B117100000000000000000000000000000000 | |||
| (PID) Process: | (3936) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000007A7B5D3379DDDB01600F00005C0E0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3936) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000E4187A3379DDDB01600F00005C0E0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3936) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000E4187A3379DDDB01600F00005C0E0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3936) dllhost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000001F7C7C3379DDDB01600F00005C0E0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
34
Suspicious files
68
Text files
672
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5168 | Install_Win11_Win10_10075_05272025.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\0x0405.ini | text | |
MD5:AEE41AC183A4D1BEC95A511BC7F959FC | SHA256:E3A0AAF26E309FABCD308473387855F2E4B673358588439C4503B2965E5A8A0E | |||
| 5168 | Install_Win11_Win10_10075_05272025.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\0x0413.ini | text | |
MD5:715BA0228A81E4B327E0E21574F22B68 | SHA256:E2FA233AE46457D27061F7F2C6B06A7972B65070035FCBFF783B77F815F32A21 | |||
| 5168 | Install_Win11_Win10_10075_05272025.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\0x0403.ini | text | |
MD5:B306203AA1539AE5A541D42116066101 | SHA256:B456FC5A73D06BA3B76BF803A875A4CA742BE1C7AC7E1A88A35CB62CE3346E3B | |||
| 5168 | Install_Win11_Win10_10075_05272025.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\0x0412.ini | text | |
MD5:59B2E4A2D3898F3E4F49186FF150E26C | SHA256:9416C7B55D1FD9DC06F20E1E3EBBAC1357217113833553D49586E339360529C7 | |||
| 5168 | Install_Win11_Win10_10075_05272025.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\0x0415.ini | text | |
MD5:081B0A4DBEFF974A5F43B98233717ED9 | SHA256:86A5EBFA31CC4904EF85060F92A8FFBED7305E00ECBB3C5EBCCDA630A7EC58E9 | |||
| 5168 | Install_Win11_Win10_10075_05272025.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\0x0402.ini | text | |
MD5:A65C6EA55E2CF446FF4DE8DE928B9518 | SHA256:B3D3321A0B5BB440D6439F3AF39B3BBAD11F4C1426004C706F1BE117410EF9E0 | |||
| 5168 | Install_Win11_Win10_10075_05272025.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\0x0406.ini | text | |
MD5:75BFC6FA26A38A09F22331B425F99179 | SHA256:8CD689EA619D6C331304E26098D4CF6C20FF4CC28FD9CAD1548BFE5ABC545350 | |||
| 5168 | Install_Win11_Win10_10075_05272025.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\0x0418.ini | text | |
MD5:739987392765A57C69219D090C3C9F4D | SHA256:F5D32C808C85B3A7C3229527903F0876D82C8FB7750F35E198A6E5D94242CBCF | |||
| 5168 | Install_Win11_Win10_10075_05272025.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\0x040c.ini | text | |
MD5:9A10EDDF9169F9508688EACE7B9E7797 | SHA256:D31B120F79C2FB8CD6F3FD7EDE220A30CA3BB84E4D3C8B05C1BCC833734D13CF | |||
| 5168 | Install_Win11_Win10_10075_05272025.exe | C:\Users\admin\AppData\Local\Temp\7zS03486957\0x0404.ini | text | |
MD5:CD658D92DF1AD180483136CD6960E7F6 | SHA256:5D31E009A36325032AB1521D2B1CA1A5BE89BB969D1948D4FE99C387B1055DB1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
51
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6216 | RUXIMICS.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.32.76:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
6216 | RUXIMICS.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.2:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.76:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
5628 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6216 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6216 | RUXIMICS.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |