| File name: | worker 2.exe |
| Full analysis: | https://app.any.run/tasks/2a501973-9b3d-444d-8316-fa95e801b8a0 |
| Verdict: | Malicious activity |
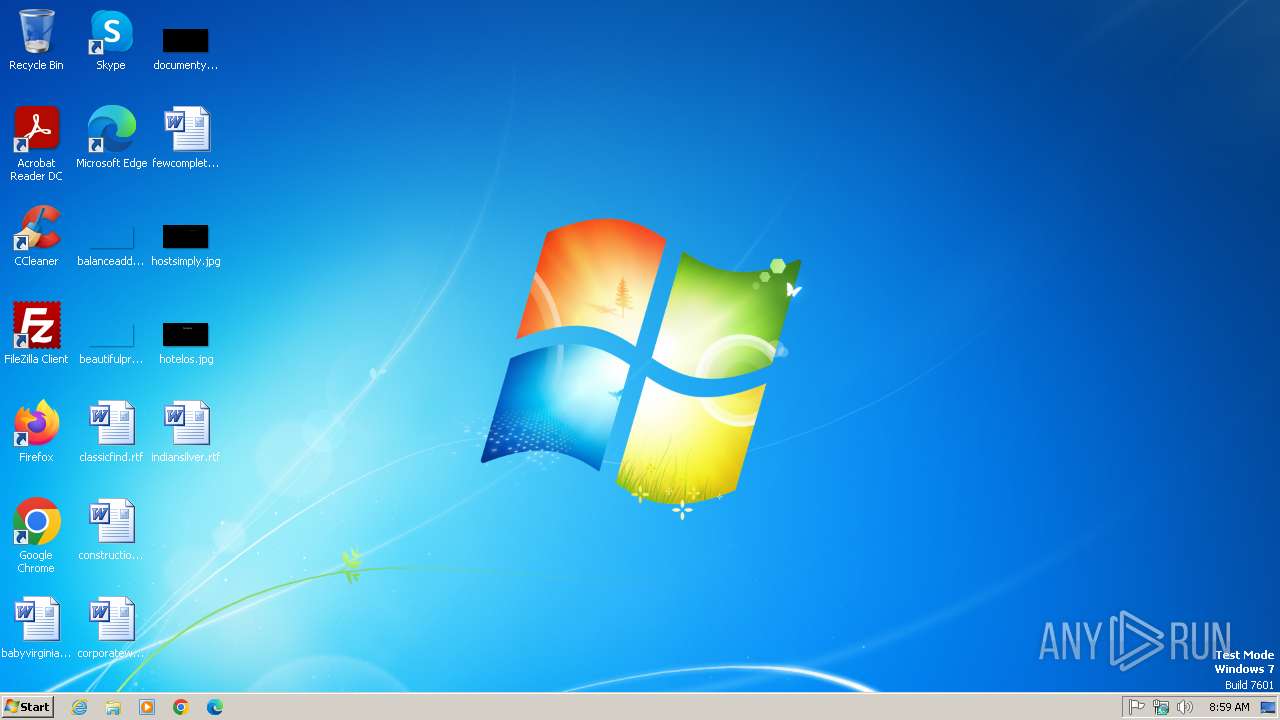
| Analysis date: | March 24, 2025, 08:59:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | C66EF3007A36023CBEE0CF24AD95246C |
| SHA1: | BD028575A6313524B16FF54204BBE4A60708159F |
| SHA256: | 0BB8E0A1827E48B851B152F46B68D0B8C0F8D7FB315BCA2C204C42F153D13AC6 |
| SSDEEP: | 24576:BJZEZJPVUVTmTj0CfOZuzhg1HREnUjwSGvQ+giNxMOacZR+:BJZEPPMT2j0CGZuimnUVGvQ+giNOOPR+ |
MALICIOUS
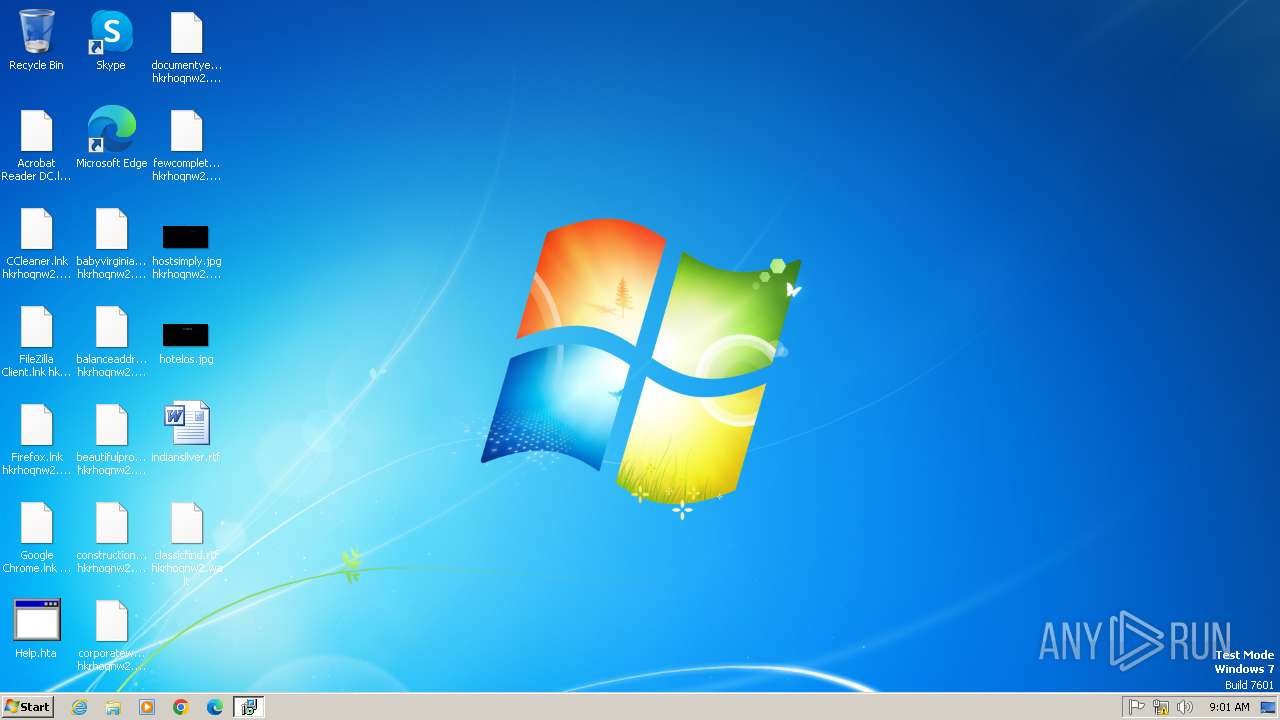
Application was injected by another process
- svchost.exe (PID: 596)
Runs injected code in another process
- worker 2.exe (PID: 1880)
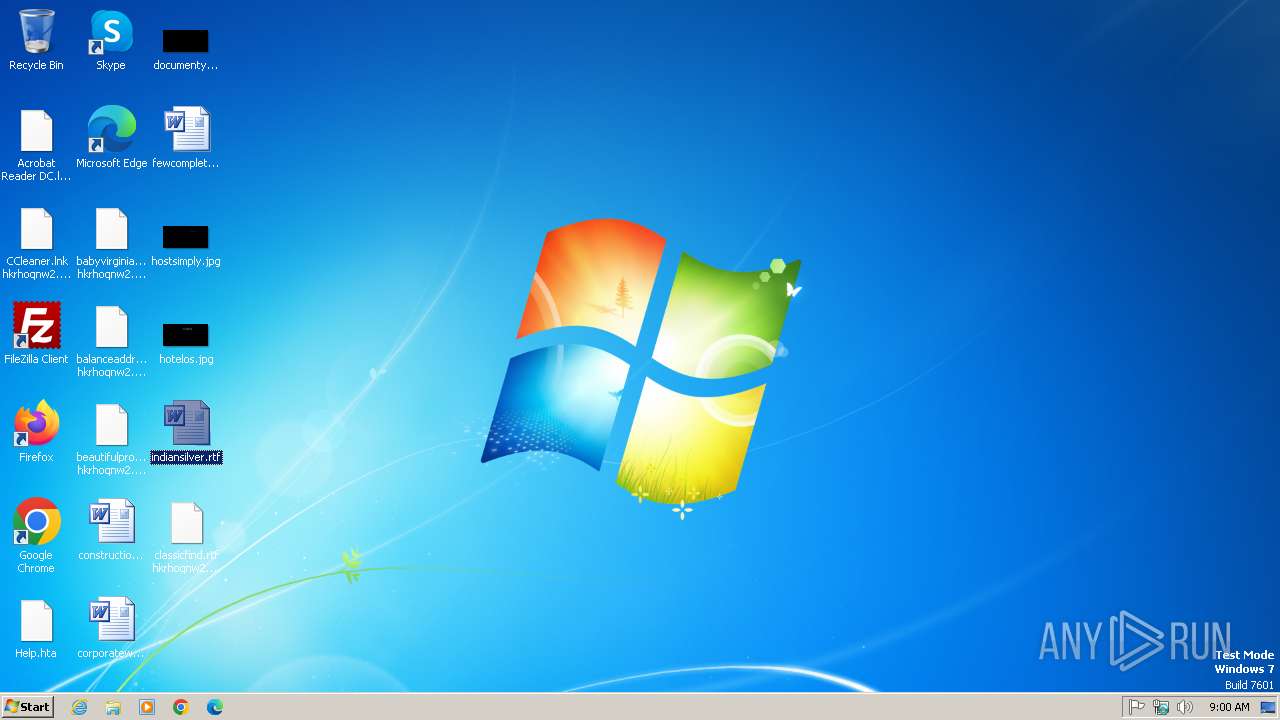
Changes the autorun value in the registry
- svchost.exe (PID: 596)
SUSPICIOUS
Executes as Windows Service
- worker 2.exe (PID: 1880)
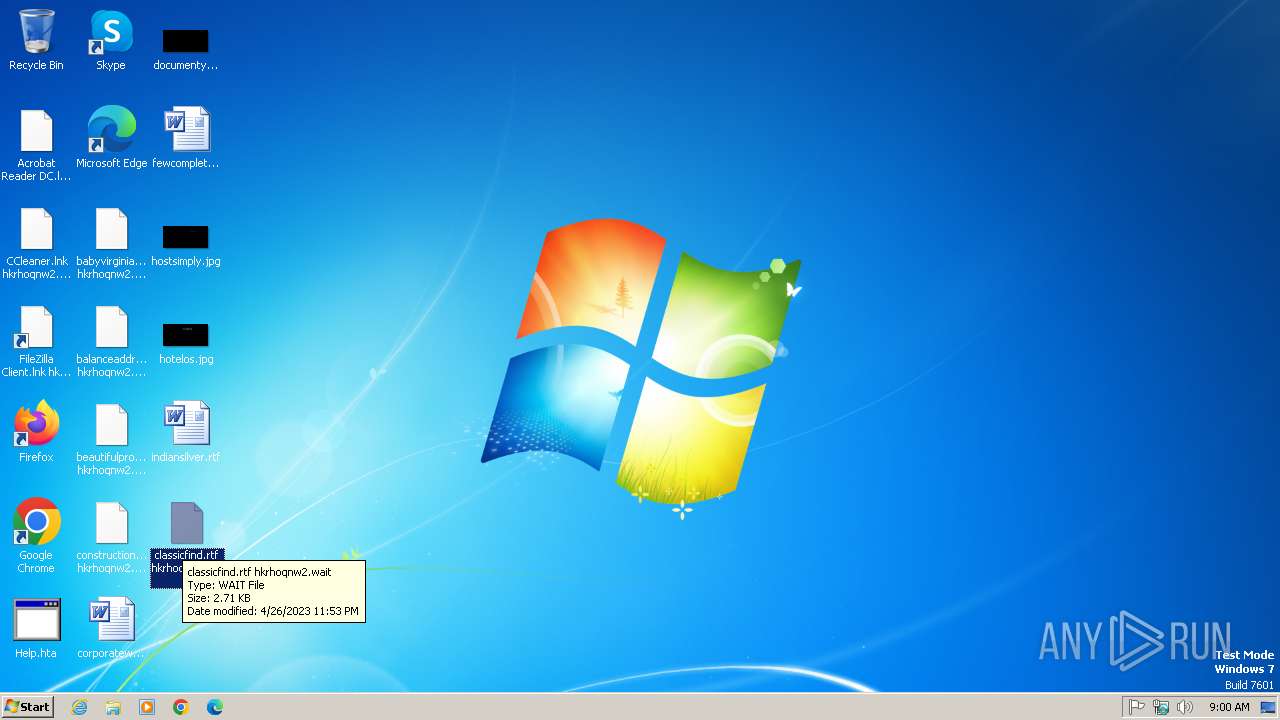
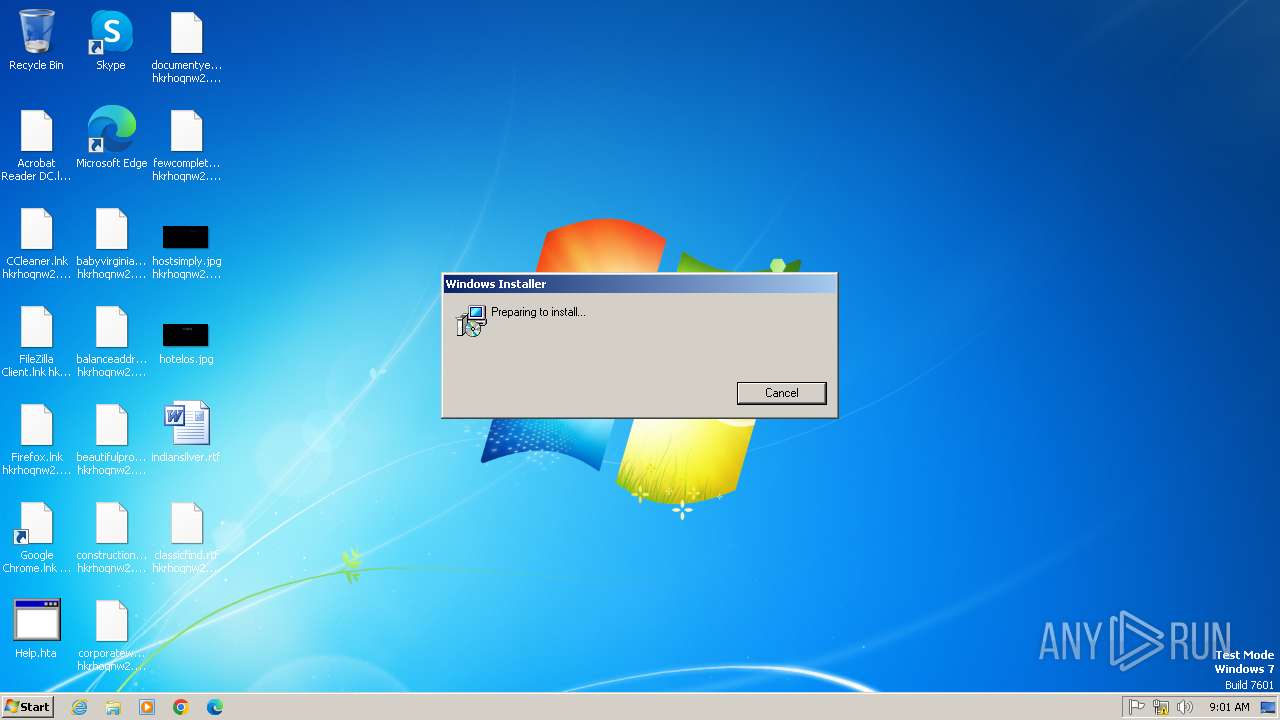
Executable content was dropped or overwritten
- worker 2.exe (PID: 1880)
Starts CMD.EXE for commands execution
- worker 2.exe (PID: 1880)
- worker 2.exe (PID: 1596)
Hides command output
- cmd.exe (PID: 1336)
- cmd.exe (PID: 1824)
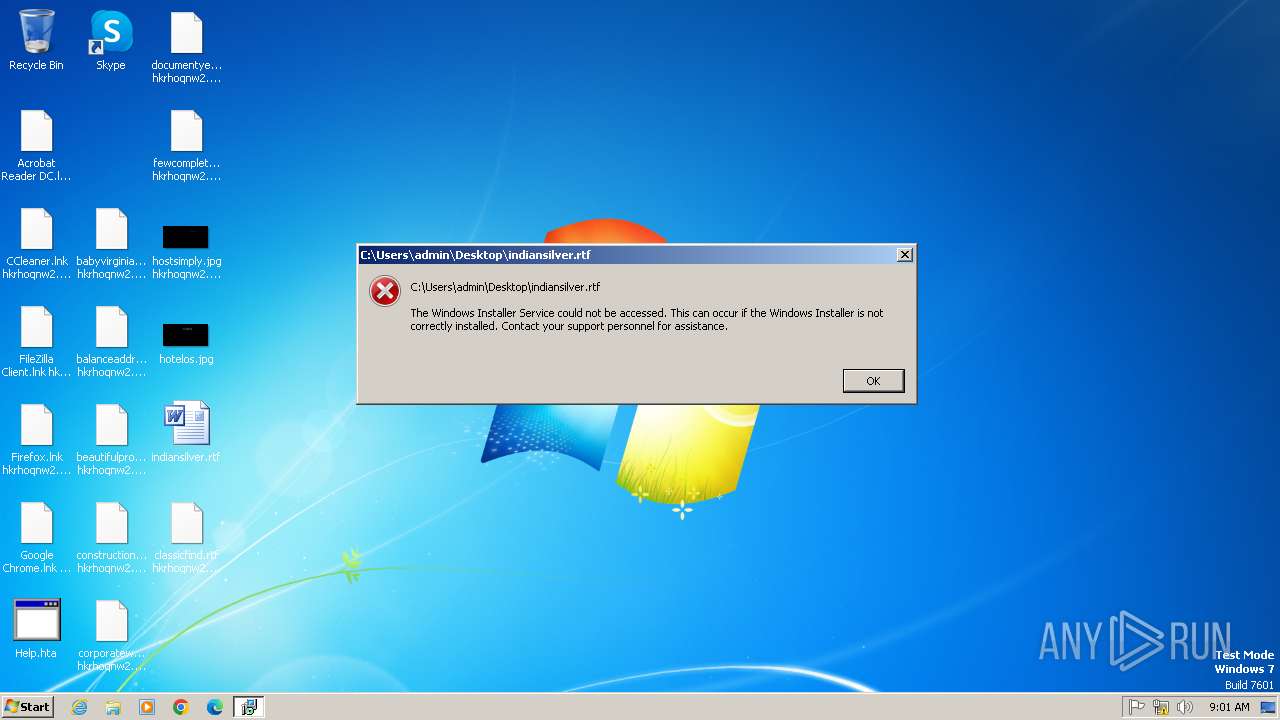
Changes default file association
- svchost.exe (PID: 596)
INFO
Reads the computer name
- worker 2.exe (PID: 1880)
- worker 2.exe (PID: 1596)
Checks supported languages
- worker 2.exe (PID: 1880)
- worker 2.exe (PID: 1596)
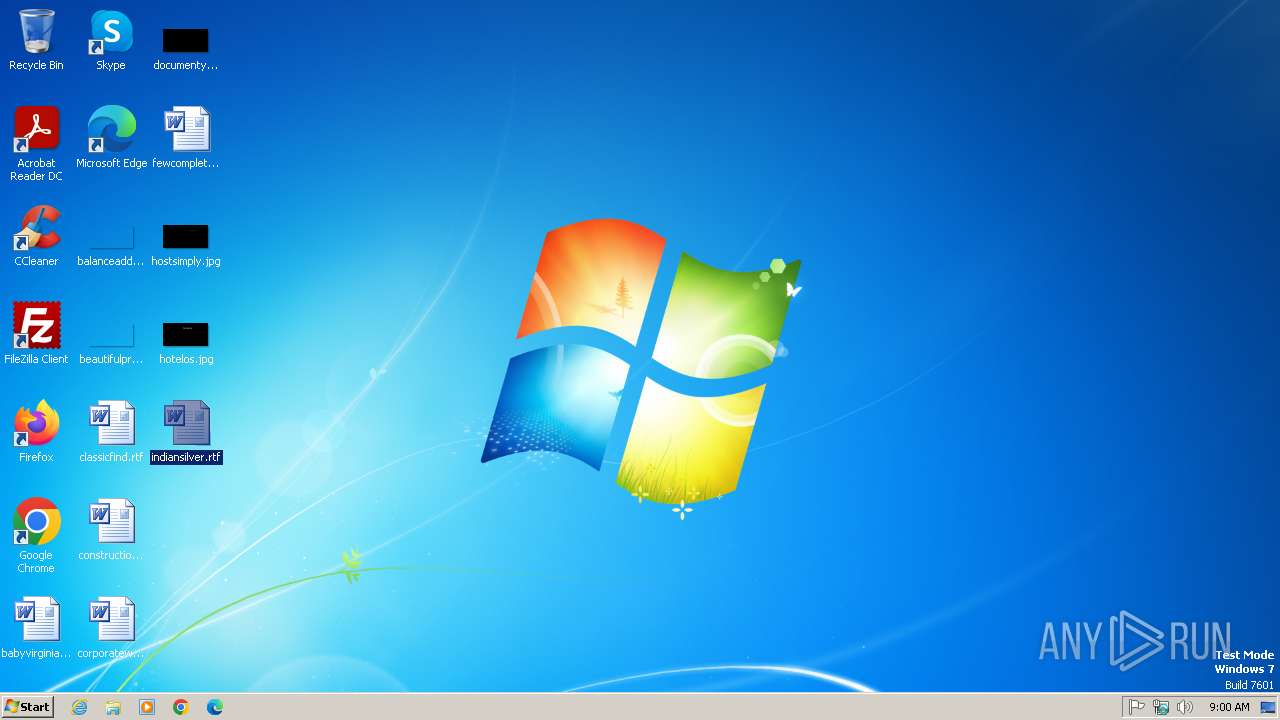
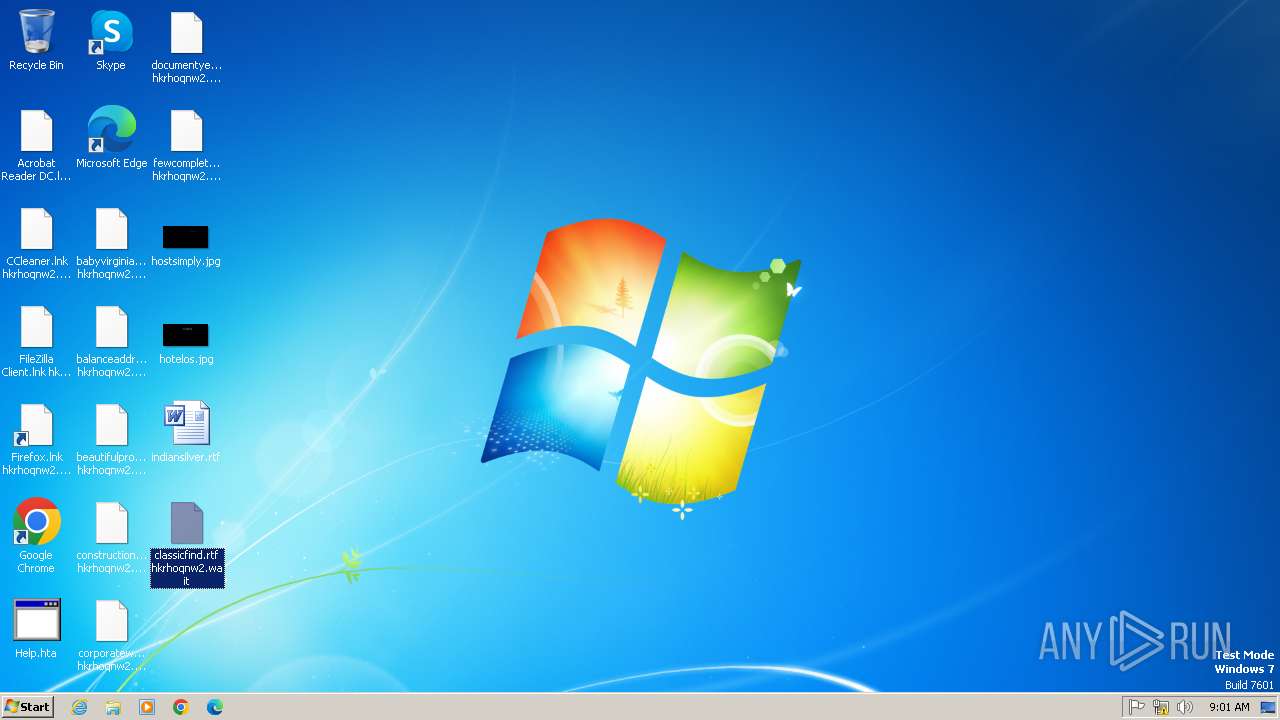
Manual execution by a user
- WINWORD.EXE (PID: 2392)
- WINWORD.EXE (PID: 2352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:07:27 02:07:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.34 |
| CodeSize: | 1167872 |
| InitializedDataSize: | 2560 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5545 |
| OSVersion: | 4 |
| ImageVersion: | 4 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
70
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | C:\Windows\system32\svchost.exe -k DcomLaunch | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1336 | /c del "C:\Users\admin\AppData\Local\Temp\worker 2.exe" >> NUL | C:\Windows\System32\cmd.exe | — | worker 2.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1596 | "C:\Users\admin\AppData\Local\Temp\worker 2.exe" | C:\Users\admin\AppData\Local\Temp\worker 2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1824 | /c del "C:\Users\admin\AppData\Local\Temp\worker 2.exe" >> NUL | C:\Windows\System32\cmd.exe | — | worker 2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1880 | "C:\Users\admin\AppData\Local\Temp\worker 2.exe" | C:\Users\admin\AppData\Local\Temp\worker 2.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\indiansilver.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 1 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\indiansilver.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 1 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2840 | "C:\Users\admin\AppData\Local\Temp\worker 2.exe" | C:\Users\admin\AppData\Local\Temp\worker 2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
239
Read events
236
Write events
3
Delete events
0
Modification events
| (PID) Process: | (596) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.wait\shell\open\command |
| Operation: | write | Name: | en |
Value: 0602000000A40000525341310008000001000100AD7B2EB37D74C81FEA9081D7D675C554201806AF7A7066E555149EFEBFBBD3BA3797B6EF545A37A77AE50D5A0A8655D5A38FC7279D70B09809ED1FA644913C3DCC133CCAE8F9CF064CCD22D9BB038343591D61FB8BD3F983250C02D93125BD215F5BD1FAF0CF5F426C10CCAD64FC887073E277C9CFBF107094120F0CC9D5A3F087564671E10D043FA0EF7C93ACAE334A531DA910DA927496D94D87A5E4A91ED2057D9DEB9116484ACE753B4D077F06FA9AD0170C229BF7A1627C01E5AF5E2C0C5856F511553CAEA2A0024C67265365865588B8C6746905A1D634C0D154BD822A28E6EF35683ECD955711310E9213890C5A93C693C08C1798A3639096A9B28A93 | |||
| (PID) Process: | (596) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.wait\shell\open\command |
| Operation: | write | Name: | n |
Value: F096073A41951D29EBC79123848F762DF9A267DE0C49906AA8A4C24A8BCC45891CB77901B6BB4F450484C5076157AEFB045DEFE09A1396E45AB7DCF788726B869E2BA7074AB2F56D2134AF16B9499412C1F193552B19DFE7D1F2297F4B09CBEA892CD254F796852DFDDA9CD28CF55C9EE6E7DAE9474E4C30C0FE2C38A55F9C246D692BD348745413A377C3F4FB26CD830EBB5C5AE1421E07EF5B2E2B64228939718EDCD8FDA7D891AE75A20A9AA7B88B8C2EE0D06757CC591B200A8CB87BC5C129AAE6C3AE9071CB88D84C2246788B7DCA0177241D9810078C773B18393C47F0934E4E95AEA13B75E17FFEC0454F6294207283DB7C01A32255E74347A5F67383458ECF387E5E103808488016A993CEFA94245DCD37DDBF19188860DDB6C096A46CFC4C893C0407374F66EE4F8537E4735C07BA495FB1EC9935B2477767FDDE9EAB3D2E632BCC18E8674C11B0E5BE79E1185E724FDFC2F6510CE5AB5F1DA078402816F35D36A516180A5E2277809F26021F42E4E1B3291C57758EF77E52C2F632531D1B9CCFC2F6931F96909BECAA60095CD1E53B1FEFEB9AD3C36F422CE5F3B712E2549DA5D9AFC3C764280840591A12FD7F86B94D3D76EBADDC4AEDB2D792FB8E750490FDD8E213194A1D0228C3885540A324CCDC0056254EE8B57CE7DC614D6777620AB43977E1F423A549D30E55FB0A61E5F101971D55A1F679AADE95DEAF1E1DF4750125CEF2233C868240D5E6C9FB79FDF283A55DC870474290FA0102F85BAA758CF5AAC79C88ACBA34478C7C6D9DE9B39130221FA17C438EAAF7BC15AB694C2E3CA95EDBEC72231836CC9F340B075F0302D071F4DB10657B59CC48D9CC42F16A326F3E03A9671BCB1383B1636A950753E39037F7E760A4850D953F05663E13B756D4B68A9AAB9E5FD7BAFE52EF4AD5ED4A2A7D94ECA55857B6D233540750FA6E96B474469C4ABA28E26DC0A7E7AE74482B52349E79FCE672C52C99E4E87DAECF936B68FE365A952D0A802E92B50205B47D2A7E88E01F85B94E92D872ECCB4B02C57C9D813D81A000390C9852B5B9D9DE0A014B253AC115DC6B615F20309F168E1D35B0087970FC66C7D1361D05C5C3EE85EB8CD2D42C5091A146E61CC7E10E8EFC9FAAFC87469B076D85071CC6D6D5432E32F958E8E20F7A5834904BF0138B326305BD01A9C37DDAC58C9BB6651AD9CE50F0472D6999B9DF9DCE63CF675B999C72B5C4A7E956EF0C27450FD96BAC4A71F19C8369384EEF5C14C6D6283B5D25E533295B2F1DE65BA1A8E63EEE84C5FA94FE543FFE69FB0D97895B67DB83FEC959FD9603D4BA3CD7187413C5A643E37471DF2297FC5698BED2B8D0DF34C7F18E857DC4D74CC86DB535BEB1A673406899DB218E2AFAD0187315C833DD23F79034A67F5F199EF135D91417AF144CA736D0AD0C7AF9C33C6FB0153B312298B2EF3B5D99D0193C0EDE0170A896D6AB986584EA87D75D2061A7EA2969D39173728AEC5822E7581BBE72184D53281581E5BF4080AAE236645E8DE18D66234F711F9EB96D95CA62F1E7561A3F3F5E2837A87BDA0C4AE8C028CF51AFAB82688D686DD7C260E643127580C4D6C1BFA3CD16AEAD18E3CA4E0A475CEBF9368480D498E0F5E07A0D50234C720959D185773C95DBCE2281481ACF60C4BDD7C048F4B088B17030DA1AF51158C0CC081A85870619B64ABCAEDB2F8A46F06CAB2C71DB0AD7F9AD333A5E2A62496121591B0C0B748DCE5AE69D0580AAA30EA8035920AC4CF36AA2D5E2FDCE1271F76A4D5C1D8FD521A0E8771D14C6D270BCD11C52CDD296600F | |||
| (PID) Process: | (596) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | open |
Value: "c:\help.hta" | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1880 | worker 2.exe | C:\Windows\utox.exe | executable | |
MD5:431D094D2B0A95AB73A1253DA8D87083 | SHA256:C418B88BC52442B3469EB882C277AA6FFBF87350887FAADAA937BAF75DF5D5AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |