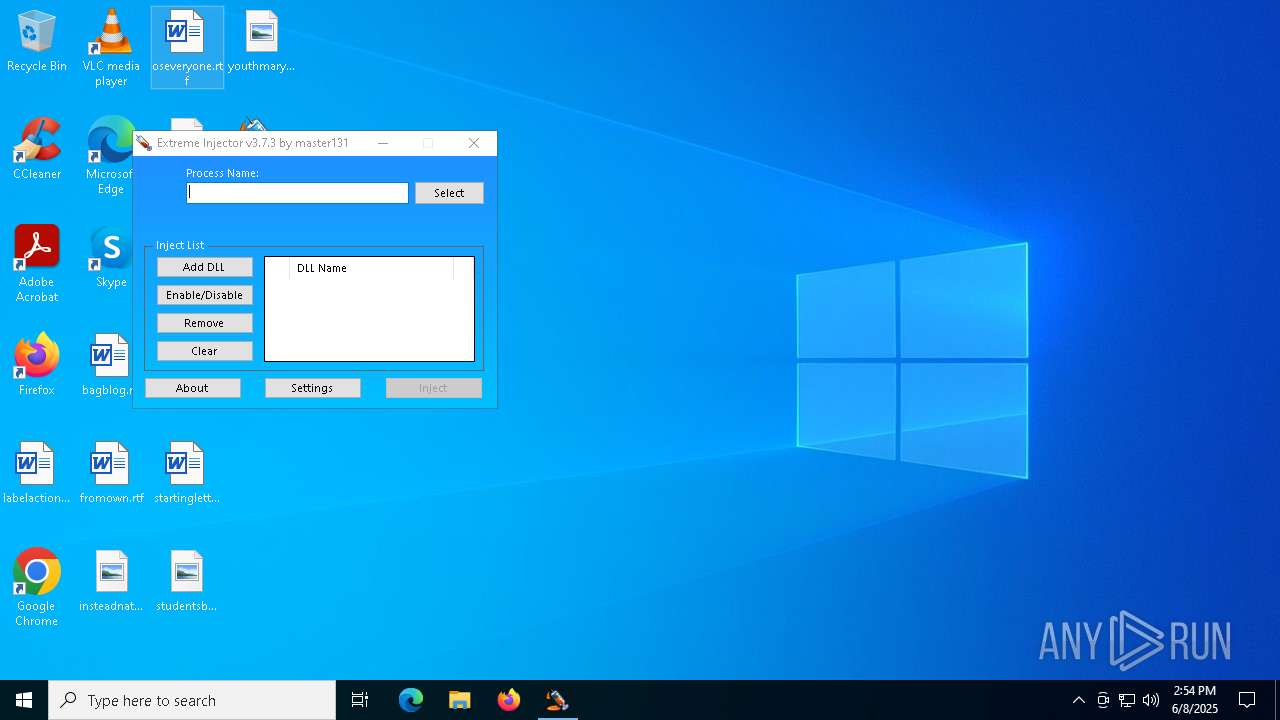
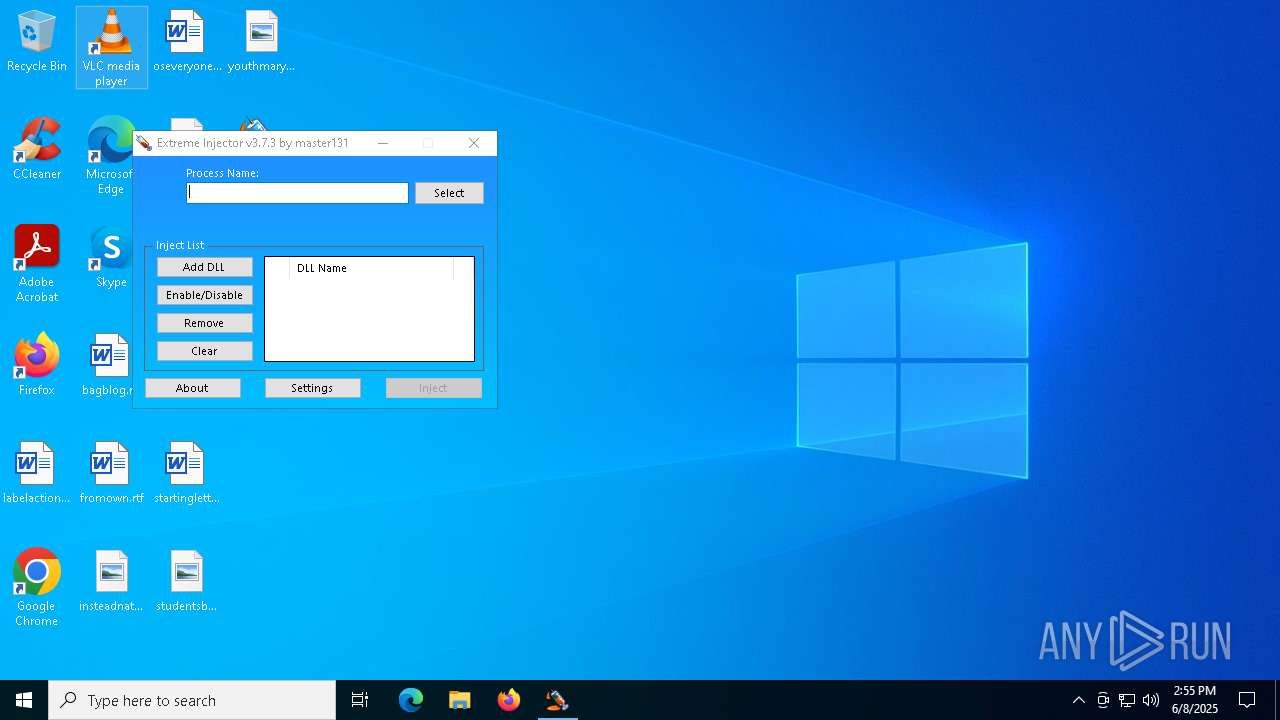
| File name: | Extremeinjectorv3.exe |
| Full analysis: | https://app.any.run/tasks/8ac020d3-c8f9-4147-9274-15f7d8a9446f |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | June 08, 2025, 14:52:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 3F078774D8057214C187DC258CA3B97E |
| SHA1: | 47DFD36ABC09640F8C54C59DA5951E8C8228D4EE |
| SHA256: | 0BAFC201B29468E6BB2FE33543924FE55969539942A292E090515DF90275A03E |
| SSDEEP: | 98304:HOWyGRrccpJkmHdc8KXxvh9WJldpdMwjWOzq62Llf0Mje27uj2Gd3+fa8BnLneRy:x7WDIZCLkWl |
MALICIOUS
DCRAT mutex has been found
- refRuntime.exe (PID: 5116)
- RuntimeBroker.exe (PID: 4980)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 1324)
DARKCRYSTAL has been detected (SURICATA)
- RuntimeBroker.exe (PID: 4980)
Connects to the CnC server
- RuntimeBroker.exe (PID: 4980)
DCRAT has been detected (YARA)
- RuntimeBroker.exe (PID: 4980)
SUSPICIOUS
Executable content was dropped or overwritten
- Extremeinjectorv3.exe (PID: 1348)
- Plague V2.exe (PID: 2104)
- refRuntime.exe (PID: 5116)
- RuntimeBroker.exe (PID: 4980)
Reads security settings of Internet Explorer
- Extremeinjectorv3.exe (PID: 1348)
- Plague V2.exe (PID: 2104)
- Extreme Injector v3.exe (PID: 6028)
- refRuntime.exe (PID: 5116)
Reads the date of Windows installation
- Extreme Injector v3.exe (PID: 6028)
- refRuntime.exe (PID: 5116)
Application launched itself
- Extreme Injector v3.exe (PID: 6028)
Executing commands from a ".bat" file
- wscript.exe (PID: 1324)
- refRuntime.exe (PID: 5116)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 1324)
- refRuntime.exe (PID: 5116)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1324)
The process creates files with name similar to system file names
- refRuntime.exe (PID: 5116)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 8180)
Starts application with an unusual extension
- cmd.exe (PID: 8180)
There is functionality for taking screenshot (YARA)
- RuntimeBroker.exe (PID: 4980)
INFO
Reads the computer name
- Extremeinjectorv3.exe (PID: 1348)
- Plague V2.exe (PID: 2104)
- Extreme Injector v3.exe (PID: 6028)
- Extreme Injector v3.exe (PID: 716)
- refRuntime.exe (PID: 5116)
- RuntimeBroker.exe (PID: 4980)
Checks supported languages
- Extremeinjectorv3.exe (PID: 1348)
- Plague V2.exe (PID: 2104)
- Extreme Injector v3.exe (PID: 6028)
- Extreme Injector v3.exe (PID: 716)
- refRuntime.exe (PID: 5116)
- chcp.com (PID: 4452)
- RuntimeBroker.exe (PID: 4980)
Process checks computer location settings
- Extremeinjectorv3.exe (PID: 1348)
- Plague V2.exe (PID: 2104)
- Extreme Injector v3.exe (PID: 6028)
- refRuntime.exe (PID: 5116)
Create files in a temporary directory
- Extremeinjectorv3.exe (PID: 1348)
- Extreme Injector v3.exe (PID: 716)
- refRuntime.exe (PID: 5116)
Drops encrypted VBS script (Microsoft Script Encoder)
- Plague V2.exe (PID: 2104)
Reads the machine GUID from the registry
- Extreme Injector v3.exe (PID: 6028)
- Extreme Injector v3.exe (PID: 716)
- refRuntime.exe (PID: 5116)
- RuntimeBroker.exe (PID: 4980)
Disables trace logs
- Extreme Injector v3.exe (PID: 716)
- RuntimeBroker.exe (PID: 4980)
Checks proxy server information
- Extreme Injector v3.exe (PID: 716)
- slui.exe (PID: 7556)
- RuntimeBroker.exe (PID: 4980)
Reads Environment values
- Extreme Injector v3.exe (PID: 716)
- refRuntime.exe (PID: 5116)
- RuntimeBroker.exe (PID: 4980)
Reads the software policy settings
- Extreme Injector v3.exe (PID: 716)
- slui.exe (PID: 7556)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- Extreme Injector v3.exe (PID: 716)
Potential library load (Base64 Encoded 'LoadLibrary')
- Extreme Injector v3.exe (PID: 716)
Failed to create an executable file in Windows directory
- refRuntime.exe (PID: 5116)
Creates files in the program directory
- refRuntime.exe (PID: 5116)
Changes the display of characters in the console
- cmd.exe (PID: 8180)
.NET Reactor protector has been detected
- RuntimeBroker.exe (PID: 4980)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- RuntimeBroker.exe (PID: 4980)
Found Base64 encoded reference to WMI classes (YARA)
- RuntimeBroker.exe (PID: 4980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (75) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (15.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.6) |
| .exe | | | Win32 Executable (generic) (2.5) |
| .exe | | | Win16/32 Executable Delphi generic (1.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:06:15 16:44:28+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | 3584 |
| InitializedDataSize: | 3284480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ae1 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
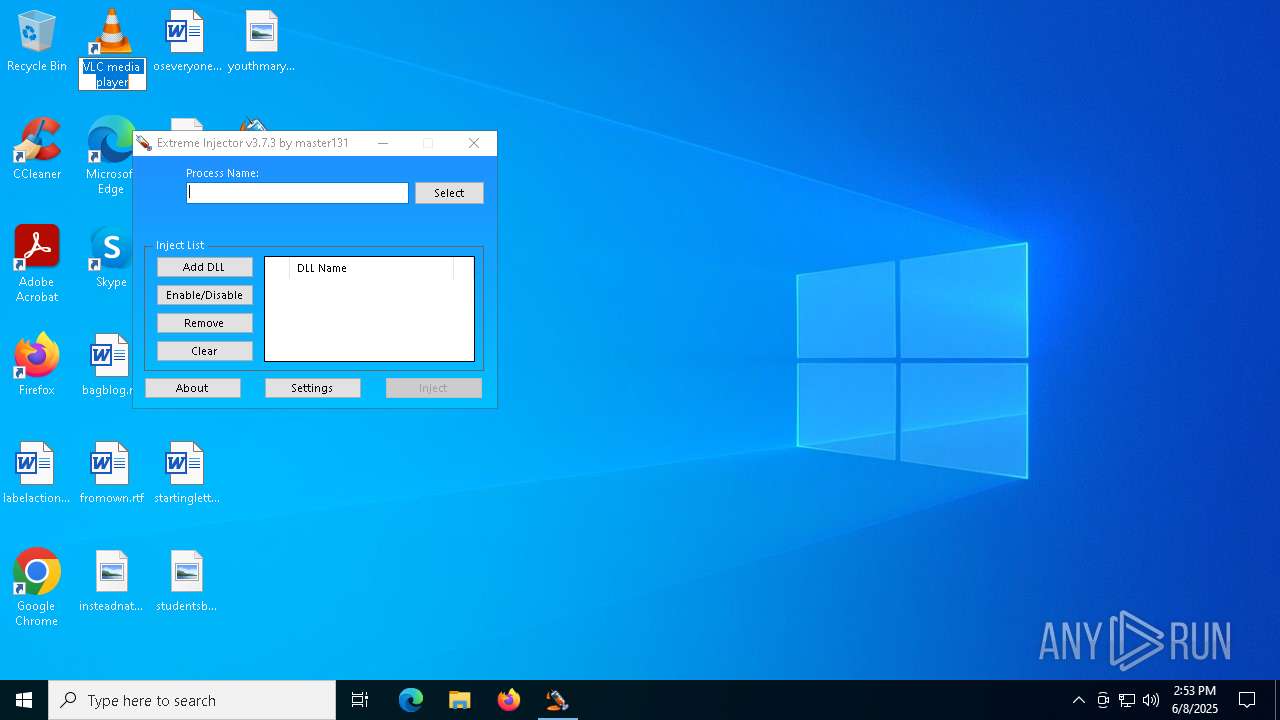
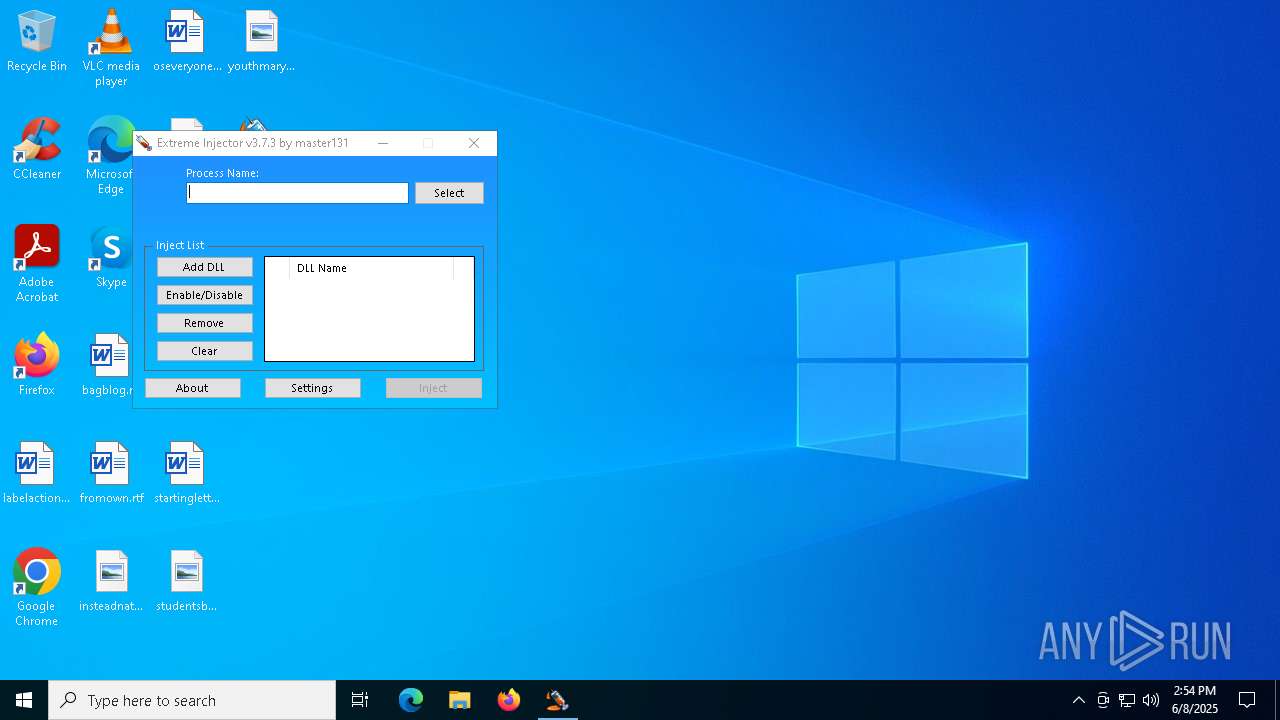
| FileVersionNumber: | 3.7.3.0 |
| ProductVersionNumber: | 3.7.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | master131 |
| FileDescription: | Extreme Injector |
| FileVersion: | 3.7.3.0 |
| InternalName: | Extreme Injector.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | master131 |
| OriginalFileName: | Extreme Injector.exe |
| ProductName: | Extreme Injector |
| ProductVersion: | 3.7.3.0 |
| AssemblyVersion: | 3.7.3.0 |
Total processes
140
Monitored processes
15
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 716 | "C:\Users\admin\AppData\Local\Temp\Extreme Injector v3.exe" | C:\Users\admin\AppData\Local\Temp\Extreme Injector v3.exe | Extreme Injector v3.exe | ||||||||||||
User: admin Company: master131 Integrity Level: HIGH Description: Extreme Injector Version: 3.7.3.0 Modules
| |||||||||||||||
| 1324 | "C:\WINDOWS\System32\WScript.exe" "C:\chainAgent\gRnrZbmR3Q0seZ97dFG6ysapNW1b.vbe" | C:\Windows\SysWOW64\wscript.exe | — | Plague V2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\Desktop\Extremeinjectorv3.exe" | C:\Users\admin\Desktop\Extremeinjectorv3.exe | explorer.exe | ||||||||||||
User: admin Company: master131 Integrity Level: MEDIUM Description: Extreme Injector Exit code: 0 Version: 3.7.3.0 Modules
| |||||||||||||||
| 2104 | "C:\Users\admin\AppData\Local\Temp\Plague V2.exe" | C:\Users\admin\AppData\Local\Temp\Plague V2.exe | Extremeinjectorv3.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4452 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4980 | "C:\Users\Default\Favorites\RuntimeBroker.exe" | C:\Users\Default\Favorites\RuntimeBroker.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 1.2.7.1277 Modules
| |||||||||||||||
| 5116 | "C:\chainAgent/refRuntime.exe" | C:\chainAgent\refRuntime.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 6028 | "C:\Users\admin\AppData\Local\Temp\Extreme Injector v3.exe" | C:\Users\admin\AppData\Local\Temp\Extreme Injector v3.exe | — | Extremeinjectorv3.exe | |||||||||||
User: admin Company: master131 Integrity Level: MEDIUM Description: Extreme Injector Exit code: 0 Version: 3.7.3.0 Modules
| |||||||||||||||
| 6060 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 017
Read events
13 000
Write events
17
Delete events
0
Modification events
| (PID) Process: | (2104) Plague V2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbe\OpenWithProgids |
| Operation: | write | Name: | VBEFile |
Value: | |||
| (PID) Process: | (716) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (716) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (716) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (716) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (716) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (716) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (716) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (716) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (716) Extreme Injector v3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Extreme Injector v3_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
12
Suspicious files
1
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1348 | Extremeinjectorv3.exe | C:\Users\admin\AppData\Local\Temp\Plague V2.exe | executable | |
MD5:2101E74C3A0F6D22A4D3229A96525614 | SHA256:63EBB84A84E3F5207FFC807A0864DD3432B19E9C4B738B251ECFE19C8C6C8D1E | |||
| 5116 | refRuntime.exe | C:\chainAgent\298dbb8ceba5a2 | text | |
MD5:375B87771C3B831D0BDFA179EAA1205F | SHA256:9FCF5E85BBC70706AA90C0343BE54443BE42926A6E60A3C69ECD3974151FB4D0 | |||
| 5116 | refRuntime.exe | C:\chainAgent\6203df4a6bafc7 | text | |
MD5:F710C06250E269DCFAB8CE54F9A32D8D | SHA256:364EE81D5FCC02E5B09B6D5350E869A86600642621B5C5B21E9E2C25F611B83F | |||
| 5116 | refRuntime.exe | C:\Users\admin\Desktop\GwaGuwKd.log | executable | |
MD5:0B2AFABFAF0DD55AD21AC76FBF03B8A0 | SHA256:DD4560987BD87EF3E6E8FAE220BA22AA08812E9743352523C846553BD99E4254 | |||
| 5116 | refRuntime.exe | C:\chainAgent\ctfmon.exe | executable | |
MD5:40B5F27EBE55D4D3E9F45911111EFD03 | SHA256:4C5967FACC2CAADAD86421A0FF784831C9FC2FABB1399E6449BFC0F318F66571 | |||
| 5116 | refRuntime.exe | C:\chainAgent\26c12092da979c | text | |
MD5:BE44AA0FF3FB54E3938B75866337A360 | SHA256:F9EEE6DDB7B3B7B953EEE7DDFF2435FFBD244776D8EA0E0DE053CAF334E6BB47 | |||
| 5116 | refRuntime.exe | C:\ProgramData\USOShared\Logs\System.exe | executable | |
MD5:40B5F27EBE55D4D3E9F45911111EFD03 | SHA256:4C5967FACC2CAADAD86421A0FF784831C9FC2FABB1399E6449BFC0F318F66571 | |||
| 5116 | refRuntime.exe | C:\ProgramData\USOShared\Logs\27d1bcfc3c54e0 | text | |
MD5:3AB60F7A80961A0FBCE04C1E7A05EC0E | SHA256:D4BB3DC7004D36132D62A5EF8043A25AB8C7F98D0781CB93A0D48B5FBE816962 | |||
| 716 | Extreme Injector v3.exe | C:\Users\admin\AppData\Local\Temp\settings.xml | xml | |
MD5:637E6E76264DC228F7636707D1ABDA8B | SHA256:8C3CAD04D8152F658717AD7CE6E0671CBC71E3E2CF4EF30550860C96DDA54FFD | |||
| 5116 | refRuntime.exe | C:\Users\admin\Desktop\mnXtFaaT.log | executable | |
MD5:D8BF2A0481C0A17A634D066A711C12E9 | SHA256:2B93377EA087225820A9F8E4F331005A0C600D557242366F06E0C1EAE003D669 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
115
TCP/UDP connections
51
DNS requests
18
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 40.126.32.133:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.4:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | POST | 200 | 20.190.160.4:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | POST | 200 | 20.190.160.14:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | POST | 200 | 20.190.160.20:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | GET | 200 | 140.82.121.4:443 | https://raw.githubusercontent.com/master131/ExtremeInjector/master/version | unknown | text | 5 b | whitelisted |
— | — | GET | 304 | 172.202.163.200:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 172.202.163.200:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
5624 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5408 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7864 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
716 | Extreme Injector v3.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
4980 | RuntimeBroker.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
4980 | RuntimeBroker.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |