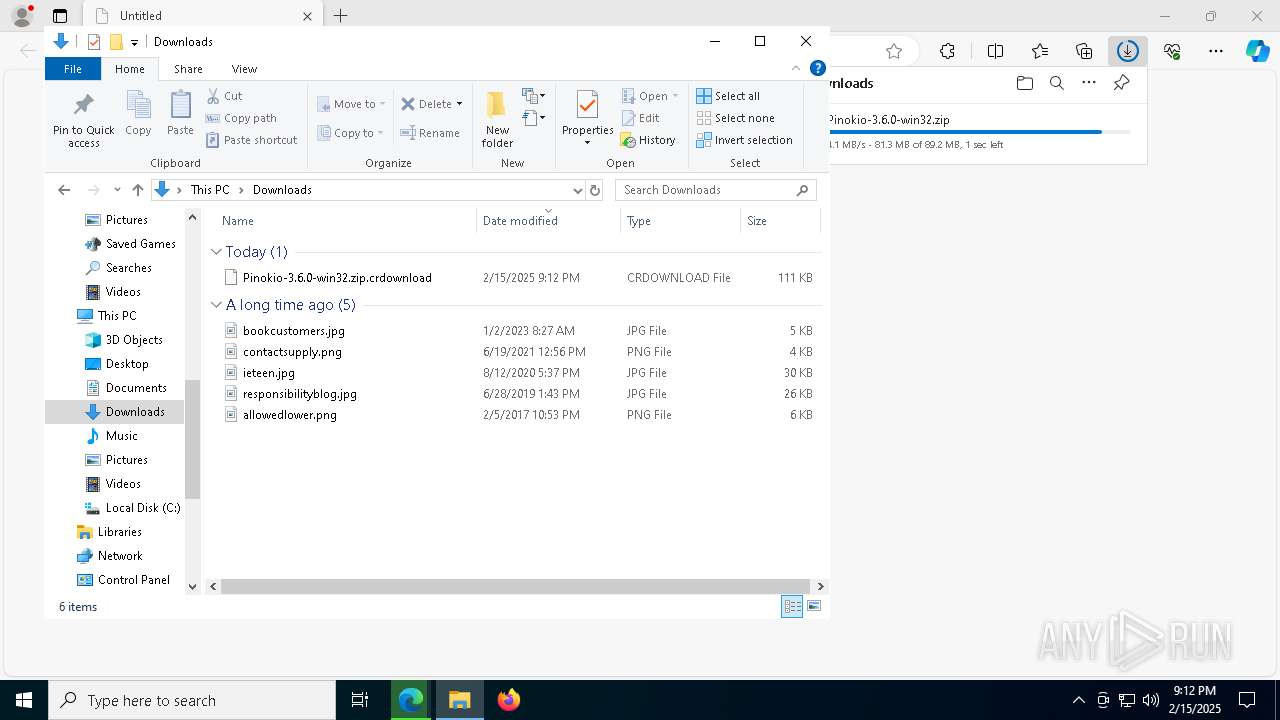
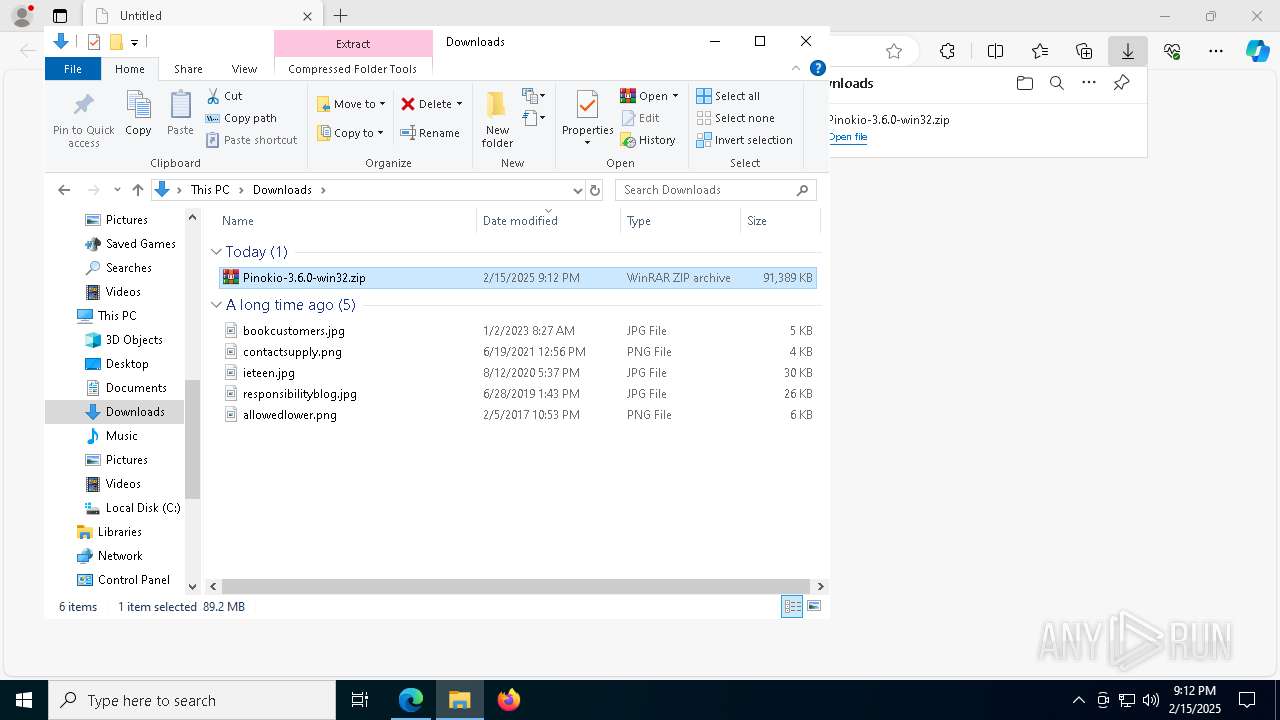
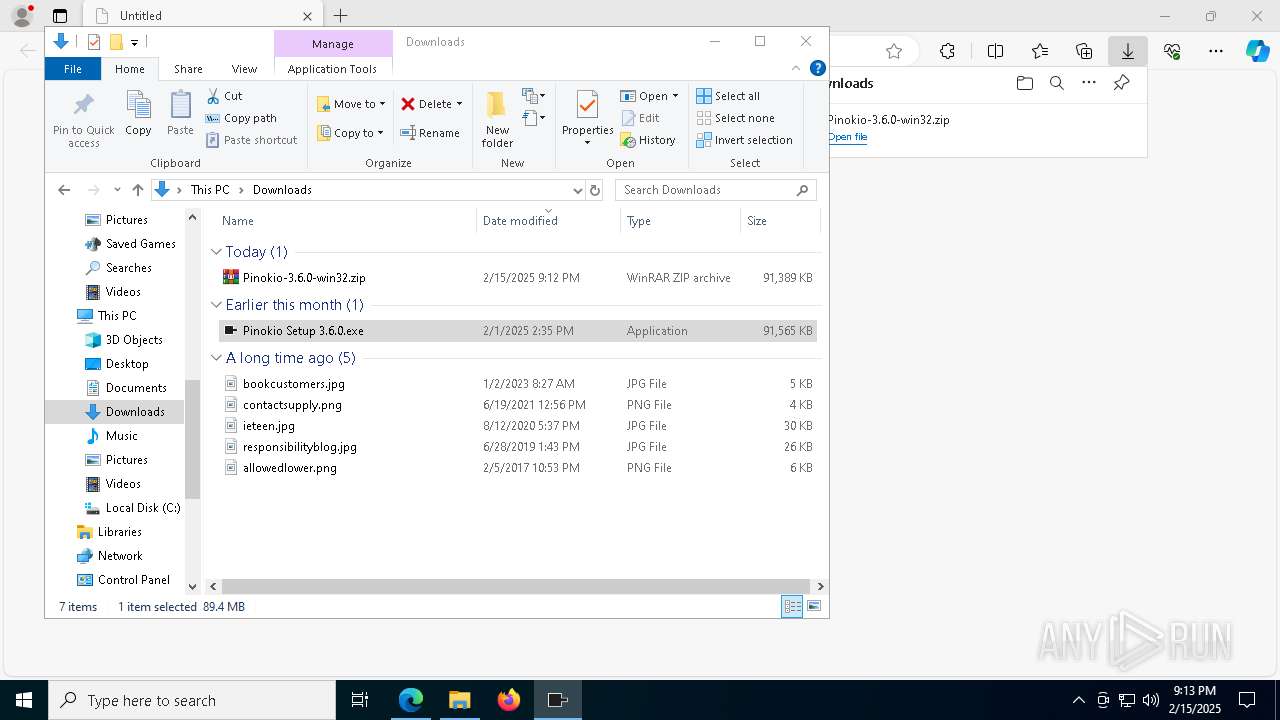
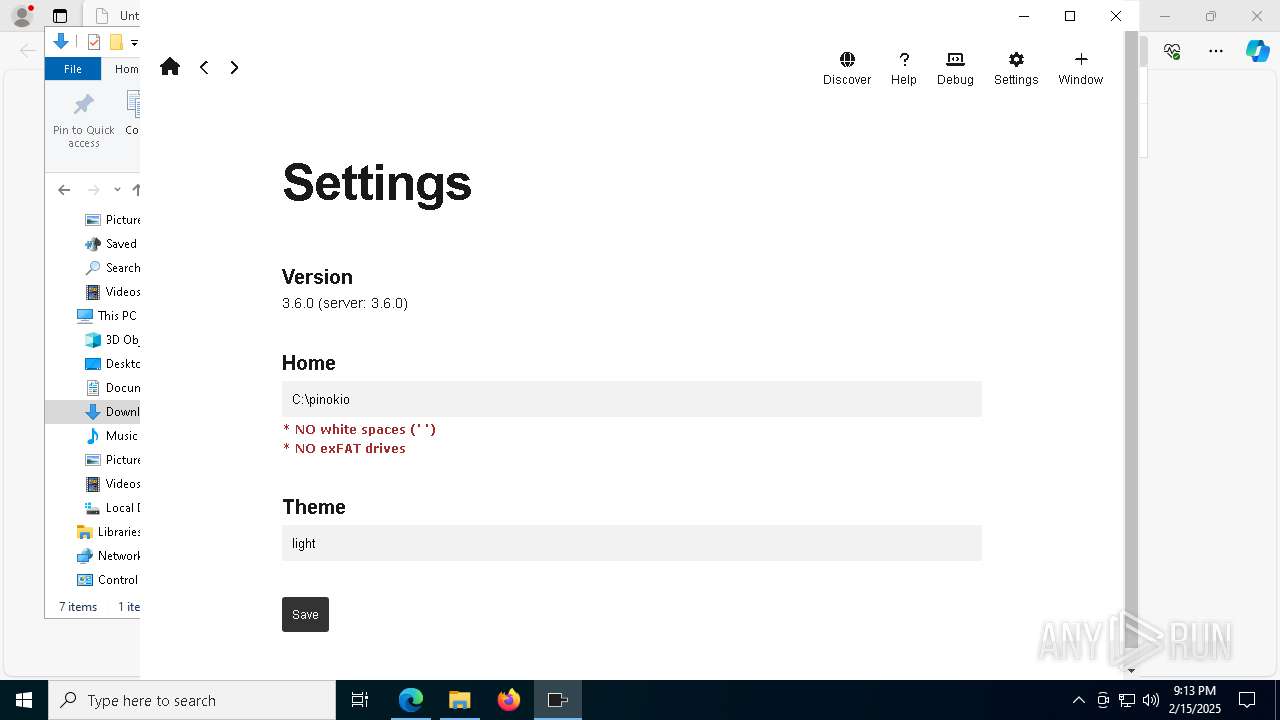
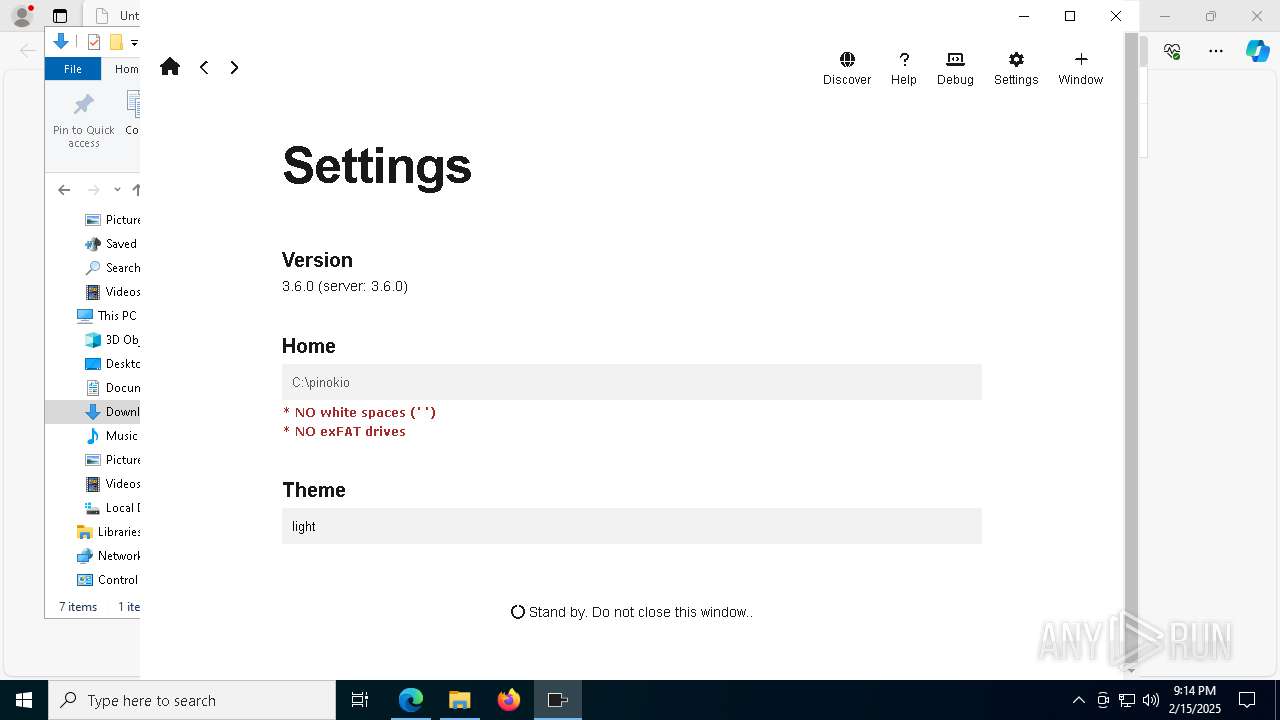
| URL: | https://github.com/pinokiocomputer/pinokio/releases/download/3.6.0/Pinokio-3.6.0-win32.zip |
| Full analysis: | https://app.any.run/tasks/f6999a1c-345b-419d-a77b-2ba3c92b2de9 |
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2025, 21:12:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 67A50B651D852E1A393CDCC5BEC37E96 |
| SHA1: | BE920198E41F692F7D0963388860B08FDBEB37E8 |
| SHA256: | 0BAA2CC51F5D82CDA7699C6F4404E7352A7837F5369DB2217F5854F6CD655933 |
| SSDEEP: | 3:N8tEdlMLK2dIVp1L0kCWnLwKKjaLVlon:2ugLMY4LwRwe |
MALICIOUS
Changes powershell execution policy (Unrestricted)
- Pinokio.exe (PID: 644)
Run PowerShell with an invisible window
- powershell.exe (PID: 2224)
SUSPICIOUS
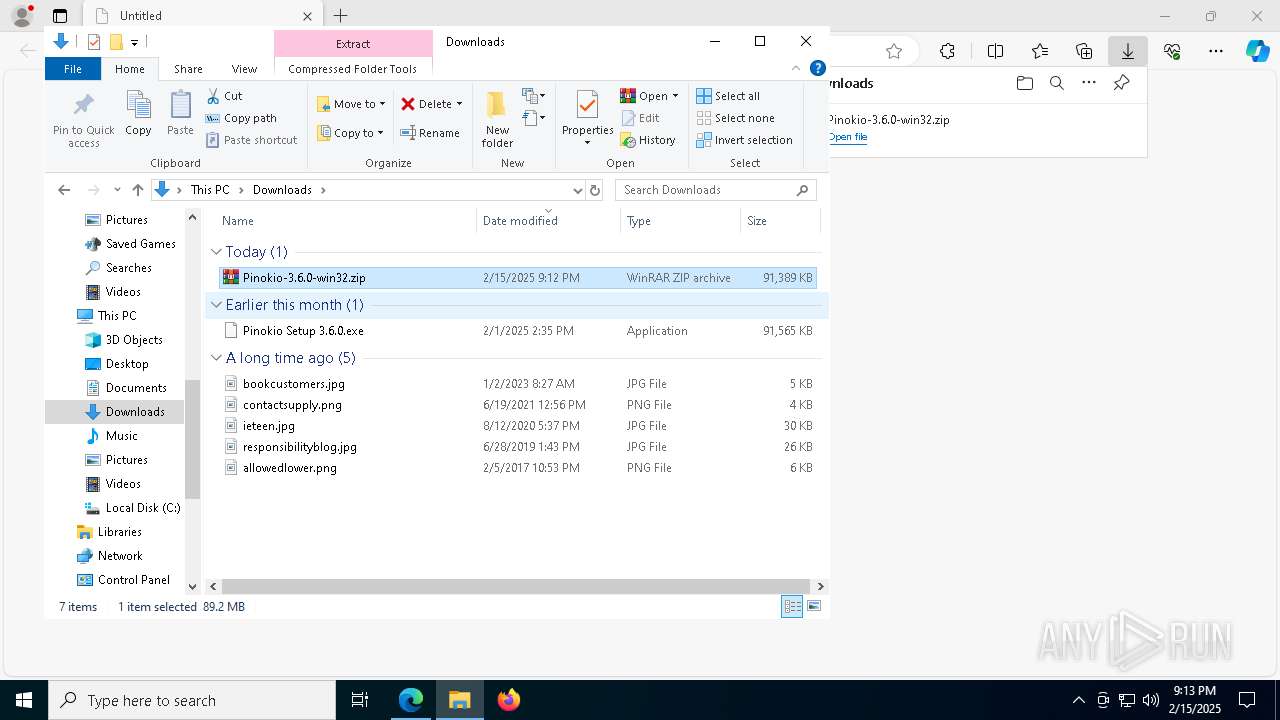
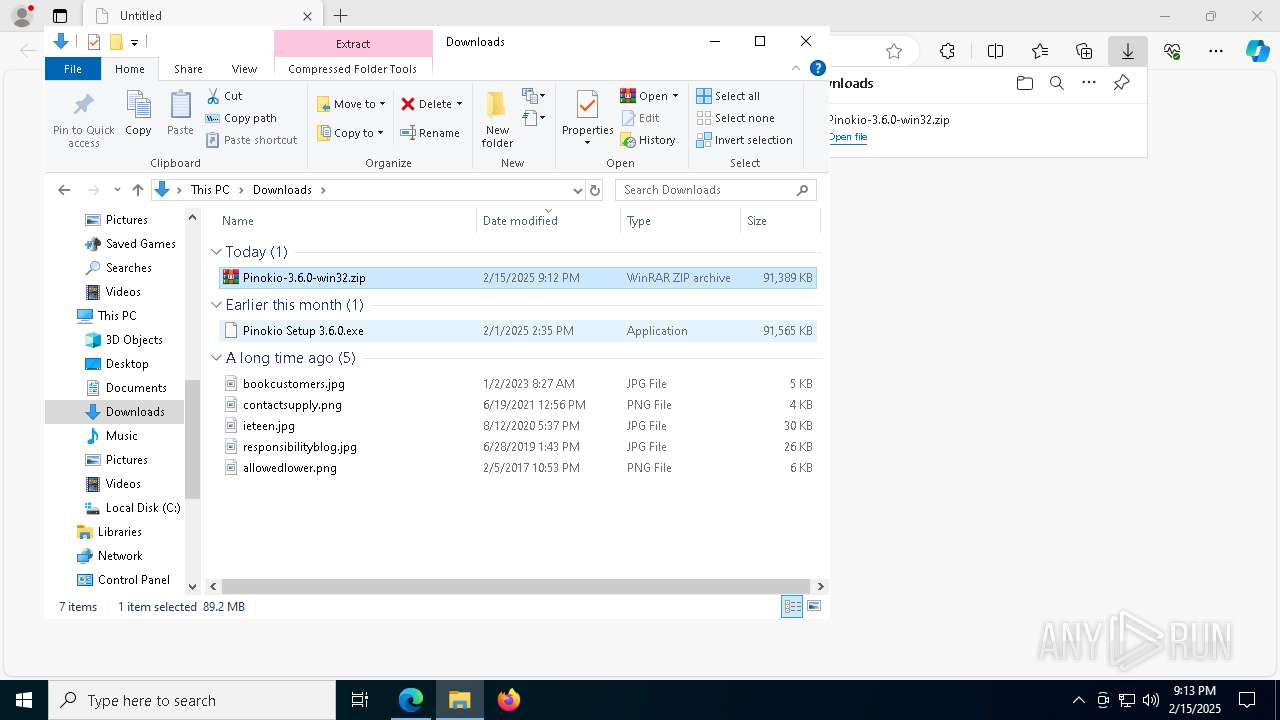
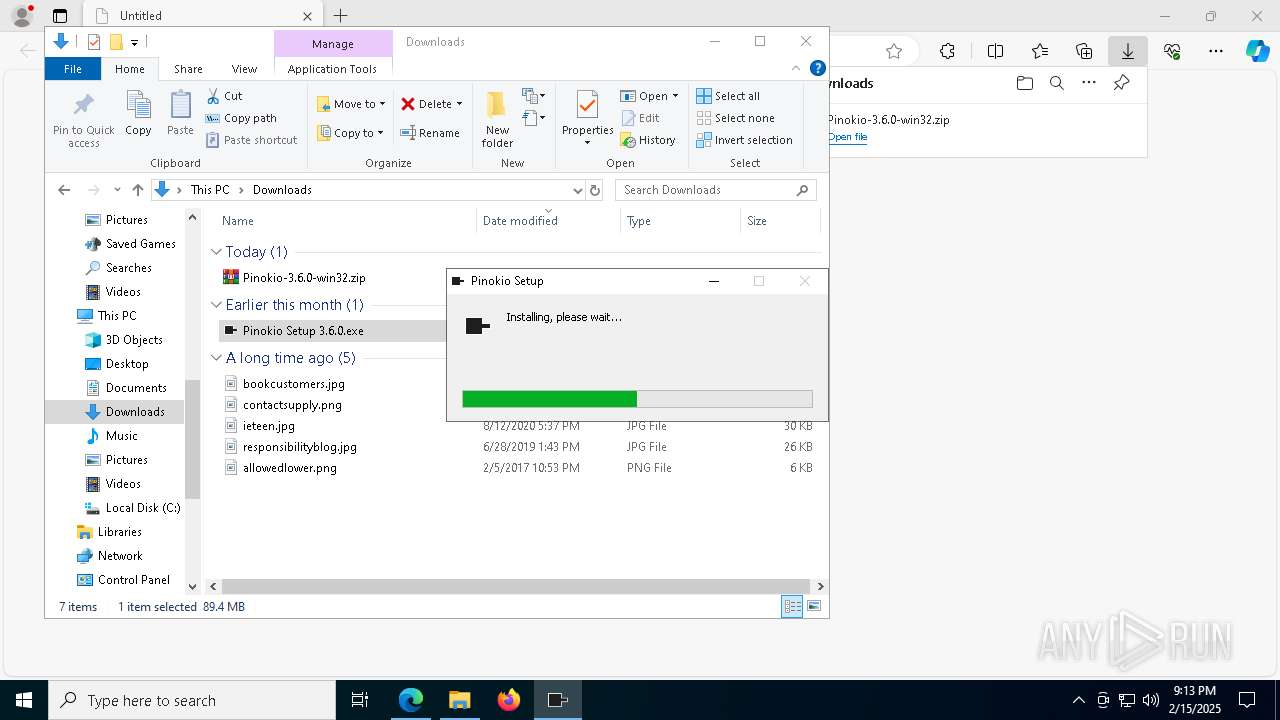
The process creates files with name similar to system file names
- Pinokio Setup 3.6.0.exe (PID: 7500)
Malware-specific behavior (creating "System.dll" in Temp)
- Pinokio Setup 3.6.0.exe (PID: 7500)
Executable content was dropped or overwritten
- Pinokio Setup 3.6.0.exe (PID: 7500)
Drops 7-zip archiver for unpacking
- Pinokio Setup 3.6.0.exe (PID: 7500)
Process drops legitimate windows executable
- Pinokio Setup 3.6.0.exe (PID: 7500)
Reads security settings of Internet Explorer
- Pinokio Setup 3.6.0.exe (PID: 7500)
There is functionality for taking screenshot (YARA)
- Pinokio Setup 3.6.0.exe (PID: 7500)
Creates a software uninstall entry
- Pinokio Setup 3.6.0.exe (PID: 7500)
Starts CMD.EXE for commands execution
- Pinokio.exe (PID: 644)
- powershell.exe (PID: 2224)
Starts application with an unusual extension
- cmd.exe (PID: 4244)
- cmd.exe (PID: 5652)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 6228)
The process bypasses the loading of PowerShell profile settings
- Pinokio.exe (PID: 644)
The process hides Powershell's copyright startup banner
- Pinokio.exe (PID: 644)
Application launched itself
- Pinokio.exe (PID: 644)
Starts POWERSHELL.EXE for commands execution
- Pinokio.exe (PID: 644)
- cmd.exe (PID: 7512)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5588)
Executing commands from a ".bat" file
- Pinokio.exe (PID: 644)
- powershell.exe (PID: 2224)
Starts process via Powershell
- powershell.exe (PID: 2224)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 6228)
The process deletes folder without confirmation
- Pinokio.exe (PID: 644)
INFO
Application launched itself
- msedge.exe (PID: 6232)
- msedge.exe (PID: 7232)
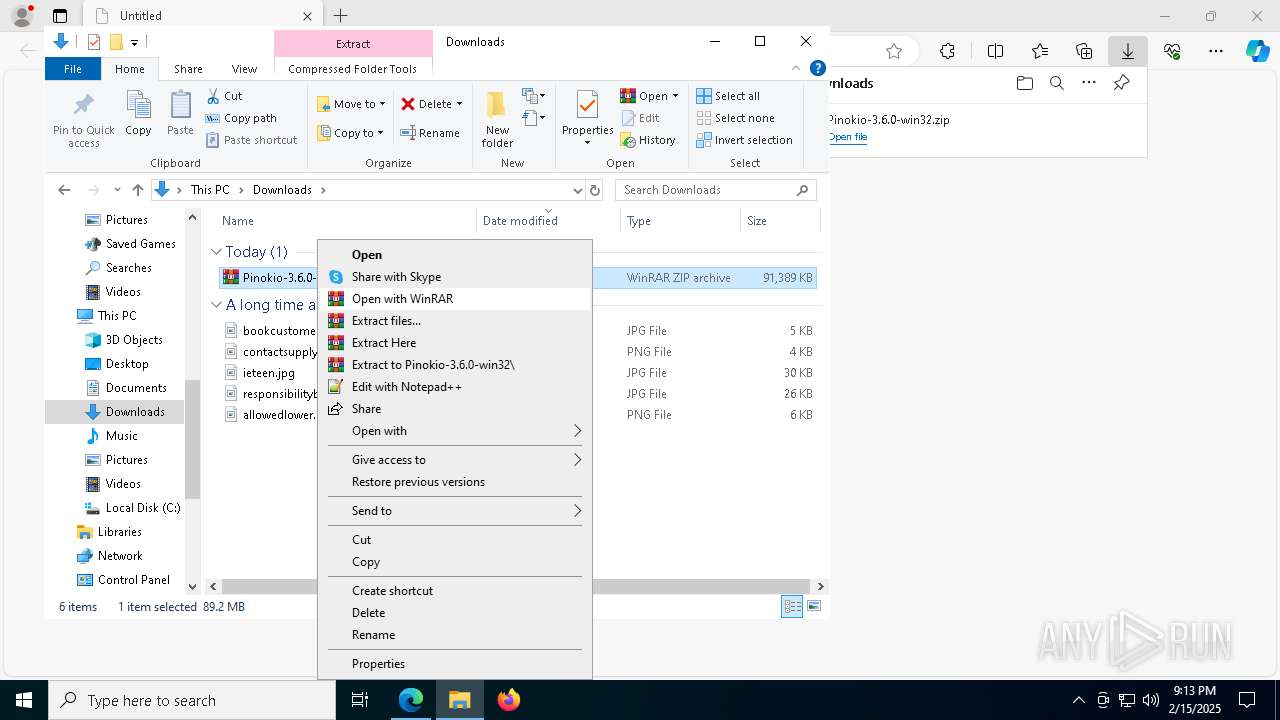
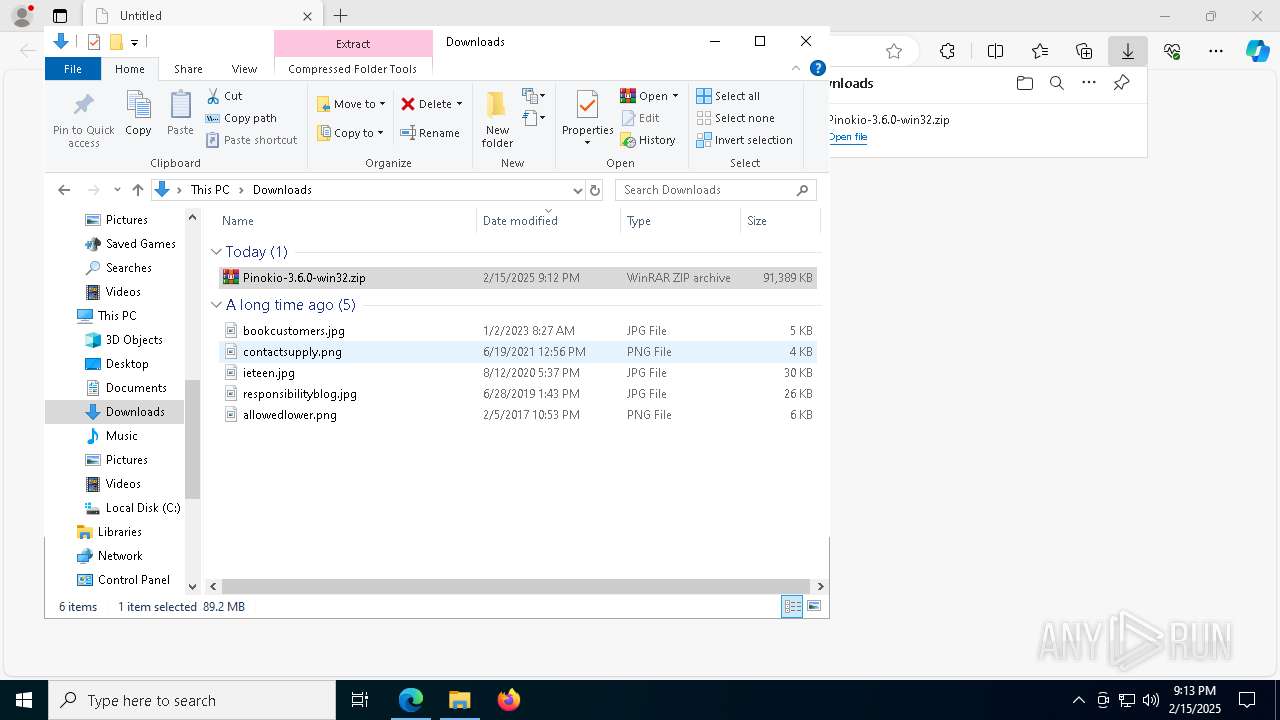
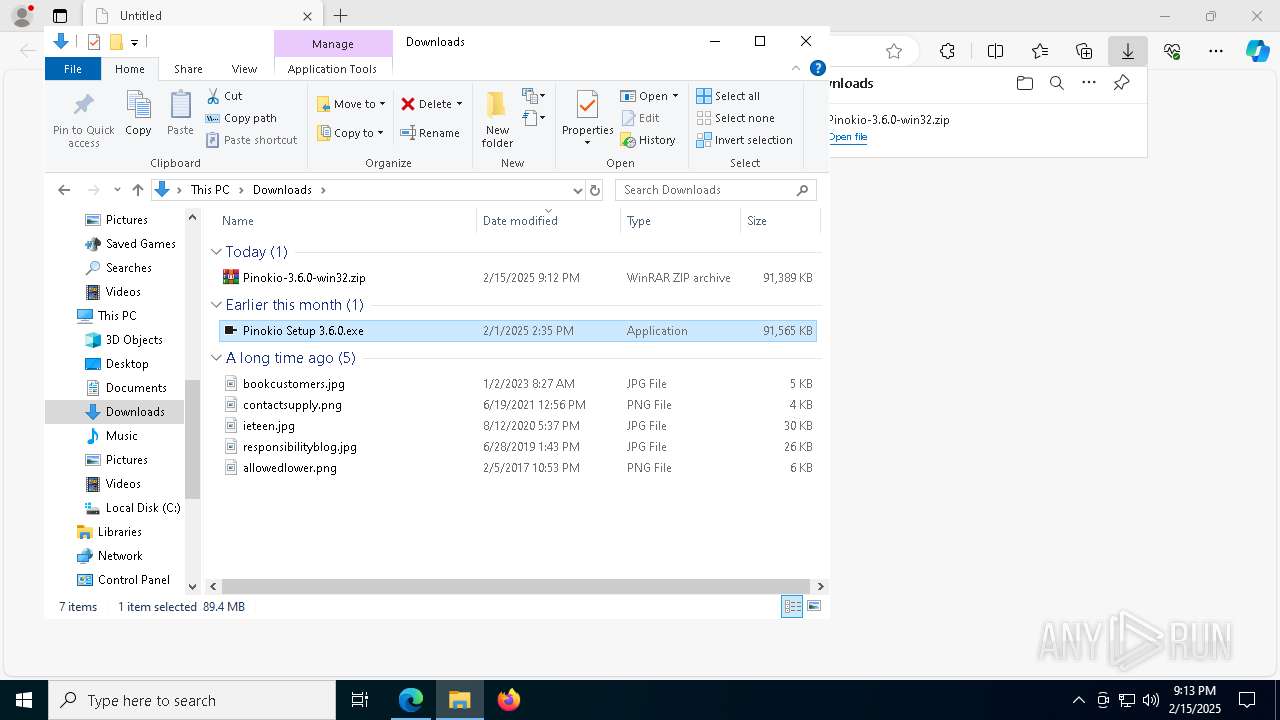
Manual execution by a user
- WinRAR.exe (PID: 5576)
- Pinokio Setup 3.6.0.exe (PID: 7500)
- Pinokio.exe (PID: 644)
Checks supported languages
- Pinokio Setup 3.6.0.exe (PID: 7500)
- Pinokio.exe (PID: 644)
- Pinokio.exe (PID: 6444)
- Pinokio.exe (PID: 5888)
- chcp.com (PID: 7192)
- Pinokio.exe (PID: 7348)
- Pinokio.exe (PID: 7940)
- chcp.com (PID: 4996)
- Pinokio.exe (PID: 8148)
- Pinokio.exe (PID: 2992)
- chcp.com (PID: 4708)
- Pinokio.exe (PID: 6172)
- Pinokio.exe (PID: 2632)
- Pinokio.exe (PID: 7884)
- Pinokio.exe (PID: 5544)
- Pinokio.exe (PID: 2956)
- Pinokio.exe (PID: 6200)
- identity_helper.exe (PID: 7856)
- Pinokio.exe (PID: 7636)
- identity_helper.exe (PID: 7276)
- chcp.com (PID: 5192)
Reads the computer name
- Pinokio Setup 3.6.0.exe (PID: 7500)
- Pinokio.exe (PID: 644)
- Pinokio.exe (PID: 6444)
- Pinokio.exe (PID: 5888)
- Pinokio.exe (PID: 7940)
- identity_helper.exe (PID: 7856)
- identity_helper.exe (PID: 7276)
- Pinokio.exe (PID: 7636)
The sample compiled with english language support
- Pinokio Setup 3.6.0.exe (PID: 7500)
Create files in a temporary directory
- Pinokio Setup 3.6.0.exe (PID: 7500)
- Pinokio.exe (PID: 644)
Creates files or folders in the user directory
- Pinokio Setup 3.6.0.exe (PID: 7500)
- Pinokio.exe (PID: 644)
- Pinokio.exe (PID: 5888)
- Pinokio.exe (PID: 7636)
Reads Environment values
- Pinokio.exe (PID: 644)
- Pinokio.exe (PID: 2992)
- identity_helper.exe (PID: 7856)
- identity_helper.exe (PID: 7276)
Reads product name
- Pinokio.exe (PID: 644)
- Pinokio.exe (PID: 2992)
Changes the display of characters in the console
- cmd.exe (PID: 4244)
- cmd.exe (PID: 5652)
- cmd.exe (PID: 2976)
- cmd.exe (PID: 6228)
Checks proxy server information
- Pinokio.exe (PID: 644)
Reads the machine GUID from the registry
- Pinokio.exe (PID: 644)
- Pinokio.exe (PID: 7636)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2928)
- powershell.exe (PID: 6860)
- powershell.exe (PID: 7364)
- powershell.exe (PID: 7356)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 3076)
- powershell.exe (PID: 7388)
- powershell.exe (PID: 6768)
- powershell.exe (PID: 3900)
- powershell.exe (PID: 4160)
Process checks computer location settings
- Pinokio.exe (PID: 644)
- Pinokio.exe (PID: 7348)
- Pinokio.exe (PID: 5544)
Node.js compiler has been detected
- Pinokio.exe (PID: 644)
Reads CPU info
- Pinokio.exe (PID: 644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
334
Monitored processes
194
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Pinokio.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ff821745fd8,0x7ff821745fe4,0x7ff821745ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 420 | powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Pinokio.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6732 --field-trial-handle=2300,i,14628655738861493315,4306279532505398752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | "C:\Users\admin\AppData\Local\Programs\Pinokio\Pinokio.exe" | C:\Users\admin\AppData\Local\Programs\Pinokio\Pinokio.exe | — | explorer.exe | |||||||||||
User: admin Company: https://twitter.com/cocktailpeanut Integrity Level: MEDIUM Description: Pinokio Version: 3.6.0 Modules
| |||||||||||||||
| 768 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | powershell.exe -NoProfile -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Pinokio.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2516 --field-trial-handle=2404,i,15848449830192152995,12371532475723895352,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
225 159
Read events
225 098
Write events
43
Delete events
18
Modification events
| (PID) Process: | (6232) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6232) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6232) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6232) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6232) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B9A79008CB8C2F00 | |||
| (PID) Process: | (6232) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 0F639608CB8C2F00 | |||
| (PID) Process: | (6232) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328416 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9889DFA7-B58D-49CD-A8DF-549BC920DAEC} | |||
| (PID) Process: | (6232) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328416 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {582676FC-80D6-4A2B-9B55-A68FED42AB58} | |||
| (PID) Process: | (6232) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FB88B008CB8C2F00 | |||
| (PID) Process: | (6232) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
68
Suspicious files
888
Text files
431
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF134ebf.TMP | — | |
MD5:— | SHA256:— | |||
| 6232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF134ebf.TMP | — | |
MD5:— | SHA256:— | |||
| 6232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF134edf.TMP | — | |
MD5:— | SHA256:— | |||
| 6232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF134eee.TMP | — | |
MD5:— | SHA256:— | |||
| 6232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF134f1d.TMP | — | |
MD5:— | SHA256:— | |||
| 6232 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
66
DNS requests
68
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7980 | svchost.exe | HEAD | 200 | 217.20.57.34:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739985685&P2=404&P3=2&P4=J9EZNAy9SGSx2%2b9Lu%2bFaRTkahIGMObFn%2fdf7H5G%2fK69mmZXgm4QDu%2fj9PJzty8DCxxYbBed5aGLwsGJUYopLZA%3d%3d | unknown | — | — | whitelisted |
624 | SIHClient.exe | GET | 200 | 23.209.214.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7152 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7980 | svchost.exe | GET | 206 | 217.20.57.34:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739985685&P2=404&P3=2&P4=J9EZNAy9SGSx2%2b9Lu%2bFaRTkahIGMObFn%2fdf7H5G%2fK69mmZXgm4QDu%2fj9PJzty8DCxxYbBed5aGLwsGJUYopLZA%3d%3d | unknown | — | — | whitelisted |
7980 | svchost.exe | GET | 206 | 217.20.57.34:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739985685&P2=404&P3=2&P4=J9EZNAy9SGSx2%2b9Lu%2bFaRTkahIGMObFn%2fdf7H5G%2fK69mmZXgm4QDu%2fj9PJzty8DCxxYbBed5aGLwsGJUYopLZA%3d%3d | unknown | — | — | whitelisted |
7980 | svchost.exe | GET | 206 | 217.20.57.34:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739985685&P2=404&P3=2&P4=J9EZNAy9SGSx2%2b9Lu%2bFaRTkahIGMObFn%2fdf7H5G%2fK69mmZXgm4QDu%2fj9PJzty8DCxxYbBed5aGLwsGJUYopLZA%3d%3d | unknown | — | — | whitelisted |
7980 | svchost.exe | GET | 206 | 217.20.57.34:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739985685&P2=404&P3=2&P4=J9EZNAy9SGSx2%2b9Lu%2bFaRTkahIGMObFn%2fdf7H5G%2fK69mmZXgm4QDu%2fj9PJzty8DCxxYbBed5aGLwsGJUYopLZA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1864 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2324 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6536 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6232 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6536 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
6536 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6536 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |