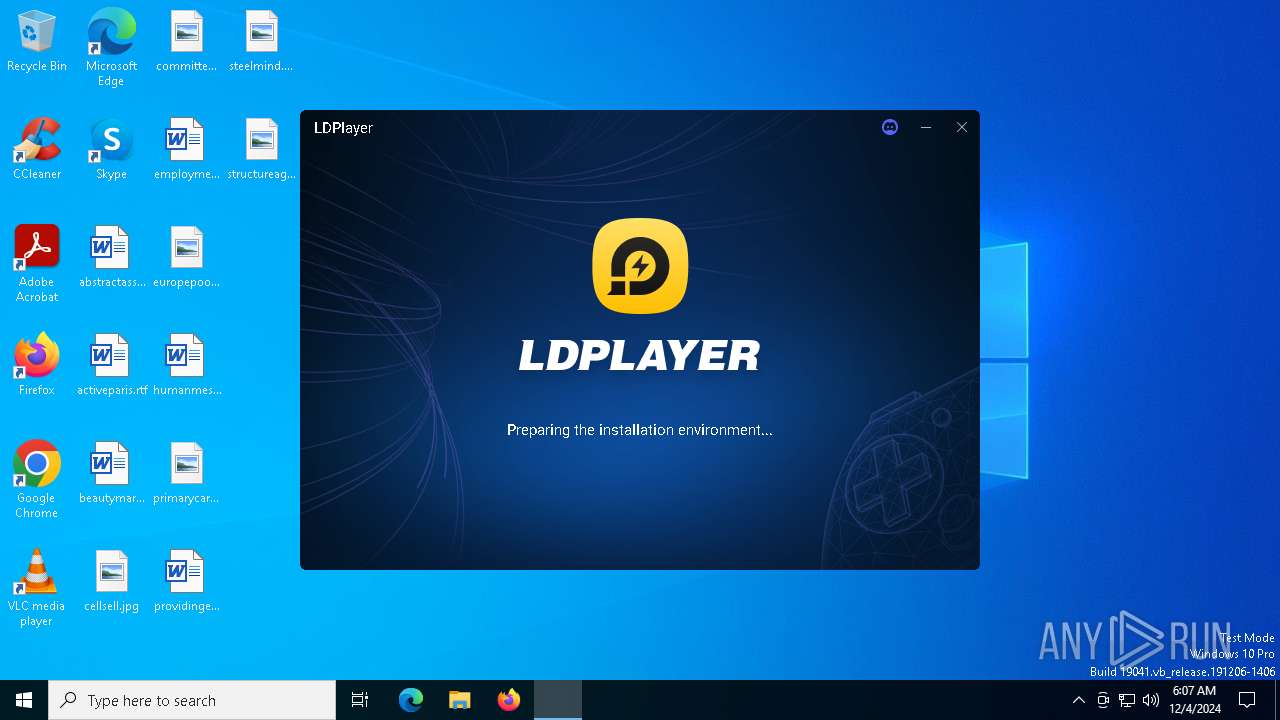
| File name: | LDPlayer9_ens_1001_ld.exe |
| Full analysis: | https://app.any.run/tasks/f10fd775-1217-4a9d-b4e5-d4f96bd5d060 |
| Verdict: | Malicious activity |
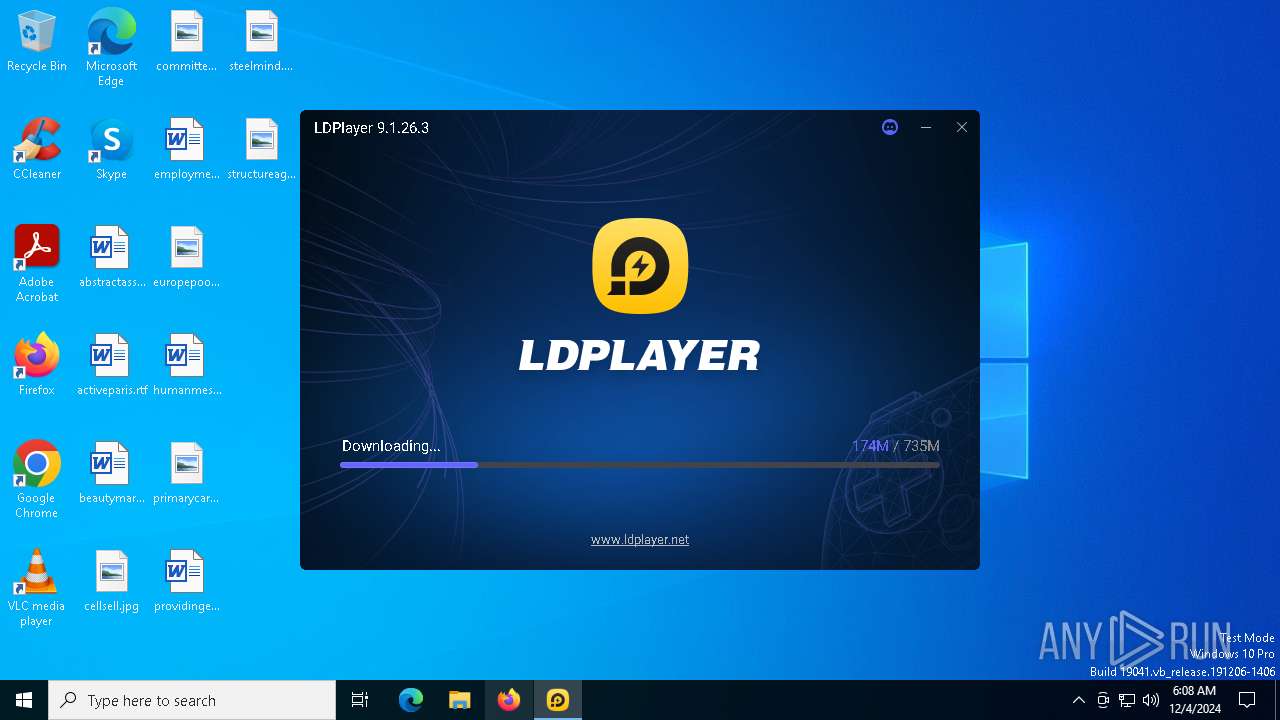
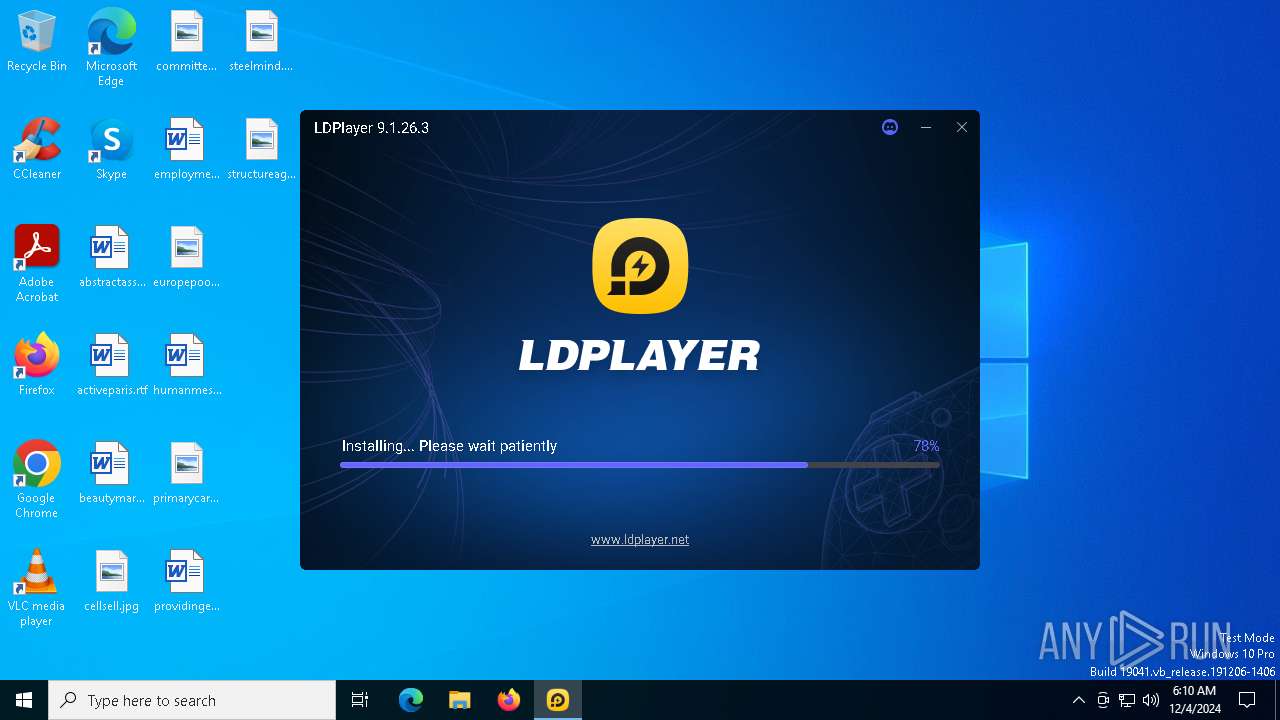
| Analysis date: | December 04, 2024, 06:07:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 881C61873A75748F9374C63A035AFECC |
| SHA1: | 6E410FB4733044FB131946184FE1FEC1BCD68336 |
| SHA256: | 0BA02EB39F93E0B5B408D77EE9937847F4DE2244120B3AF3F41F8E3425C9281C |
| SSDEEP: | 98304:V1EQlUiLeiYxQKN5DooPUEUMoj4Flc891YtoAlVXm1M3cJRRL+rssQarhYfLrt2G:U |
MALICIOUS
Starts NET.EXE for service management
- dnrepairer.exe (PID: 4648)
- net.exe (PID: 5540)
Registers / Runs the DLL via REGSVR32.EXE
- dnrepairer.exe (PID: 4648)
SUSPICIOUS
Reads security settings of Internet Explorer
- LDPlayer.exe (PID: 4320)
- LDPlayer9_ens_1001_ld.exe (PID: 6156)
- dnplayer.exe (PID: 6756)
Executable content was dropped or overwritten
- LDPlayer.exe (PID: 4320)
- Dism.exe (PID: 7032)
- dnrepairer.exe (PID: 4648)
- dnplayer.exe (PID: 6756)
Process drops legitimate windows executable
- LDPlayer.exe (PID: 4320)
- dnrepairer.exe (PID: 4648)
- dnplayer.exe (PID: 6756)
Checks Windows Trust Settings
- LDPlayer.exe (PID: 4320)
- LDPlayer9_ens_1001_ld.exe (PID: 6156)
- dnplayer.exe (PID: 6756)
Drops 7-zip archiver for unpacking
- LDPlayer.exe (PID: 4320)
The process drops C-runtime libraries
- LDPlayer.exe (PID: 4320)
- dnrepairer.exe (PID: 4648)
- dnplayer.exe (PID: 6756)
The process creates files with name similar to system file names
- Dism.exe (PID: 7032)
Uses ICACLS.EXE to modify access control lists
- dnrepairer.exe (PID: 4648)
- LDPlayer.exe (PID: 4320)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 5556)
Takes ownership (TAKEOWN.EXE)
- dnrepairer.exe (PID: 4648)
- LDPlayer.exe (PID: 4320)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1216)
- regsvr32.exe (PID: 5980)
Starts POWERSHELL.EXE for commands execution
- dnrepairer.exe (PID: 4648)
Drops a system driver (possible attempt to evade defenses)
- dnrepairer.exe (PID: 4648)
Creates a software uninstall entry
- LDPlayer.exe (PID: 4320)
The process checks if it is being run in the virtual environment
- conhost.exe (PID: 4596)
INFO
Creates files or folders in the user directory
- LDPlayer9_ens_1001_ld.exe (PID: 6156)
- LDPlayer.exe (PID: 4320)
- dnrepairer.exe (PID: 4648)
- dnplayer.exe (PID: 6756)
Reads the software policy settings
- LDPlayer.exe (PID: 4320)
- LDPlayer9_ens_1001_ld.exe (PID: 6156)
- dnplayer.exe (PID: 6756)
Reads the computer name
- LDPlayer.exe (PID: 4320)
- LDPlayer9_ens_1001_ld.exe (PID: 6156)
- DismHost.exe (PID: 5556)
- Ld9BoxSVC.exe (PID: 5968)
- dnplayer.exe (PID: 6756)
- Ld9BoxSVC.exe (PID: 7048)
- Ld9BoxHeadless.exe (PID: 6272)
- Ld9BoxHeadless.exe (PID: 5212)
- identity_helper.exe (PID: 3772)
- Ld9BoxHeadless.exe (PID: 7028)
- Ld9BoxHeadless.exe (PID: 6488)
- Ld9BoxHeadless.exe (PID: 6924)
Checks proxy server information
- LDPlayer.exe (PID: 4320)
- LDPlayer9_ens_1001_ld.exe (PID: 6156)
- dnplayer.exe (PID: 6756)
Checks supported languages
- LDPlayer.exe (PID: 4320)
- LDPlayer9_ens_1001_ld.exe (PID: 6156)
- dnrepairer.exe (PID: 4648)
- DismHost.exe (PID: 5556)
- Ld9BoxSVC.exe (PID: 5968)
- dnplayer.exe (PID: 6756)
- driverconfig.exe (PID: 3080)
- vbox-img.exe (PID: 6840)
- Ld9BoxHeadless.exe (PID: 6272)
- vbox-img.exe (PID: 5864)
- vbox-img.exe (PID: 6076)
- Ld9BoxHeadless.exe (PID: 7028)
- Ld9BoxSVC.exe (PID: 7048)
- Ld9BoxHeadless.exe (PID: 6488)
- Ld9BoxHeadless.exe (PID: 6924)
- identity_helper.exe (PID: 3772)
- Ld9BoxHeadless.exe (PID: 5212)
Reads the machine GUID from the registry
- LDPlayer.exe (PID: 4320)
- LDPlayer9_ens_1001_ld.exe (PID: 6156)
- dnrepairer.exe (PID: 4648)
- dnplayer.exe (PID: 6756)
Sends debugging messages
- Dism.exe (PID: 7032)
- DismHost.exe (PID: 5556)
- Ld9BoxHeadless.exe (PID: 6272)
- Ld9BoxHeadless.exe (PID: 7028)
- dnplayer.exe (PID: 6756)
Create files in a temporary directory
- Dism.exe (PID: 7032)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4596)
- powershell.exe (PID: 6252)
- powershell.exe (PID: 6780)
The process uses the downloaded file
- powershell.exe (PID: 4596)
- powershell.exe (PID: 6252)
- powershell.exe (PID: 6780)
Reads Environment values
- DismHost.exe (PID: 5556)
- identity_helper.exe (PID: 3772)
Creates files in the program directory
- dnrepairer.exe (PID: 4648)
Application launched itself
- msedge.exe (PID: 6600)
- msedge.exe (PID: 6092)
- msedge.exe (PID: 7684)
Manual execution by a user
- msedge.exe (PID: 6092)
Reads CPU info
- dnplayer.exe (PID: 6756)
Attempting to use instant messaging service
- msedge.exe (PID: 1328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:11:06 02:04:33+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 1216000 |
| InitializedDataSize: | 1440768 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xec908 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
268
Monitored processes
131
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5396 --field-trial-handle=1568,i,15557206030707830002,8901318633945224920,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 628 | sc query vmms | C:\Windows\SysWOW64\sc.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1564 --field-trial-handle=1568,i,15557206030707830002,8901318633945224920,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1216 | "regsvr32" "C:\Program Files\ldplayer9box\x86\VBoxProxyStub-x86.dll" /s | C:\Windows\SysWOW64\regsvr32.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1220 | "regsvr32" "C:\Program Files\ldplayer9box\VBoxC.dll" /s | C:\Windows\System32\regsvr32.exe | — | dnrepairer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2316 --field-trial-handle=1568,i,15557206030707830002,8901318633945224920,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
| 1356 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Ld9BoxHeadless.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1460 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3528 --field-trial-handle=1568,i,15557206030707830002,8901318633945224920,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | |||||||||||||||
Total events
70 854
Read events
70 330
Write events
495
Delete events
29
Modification events
| (PID) Process: | (6156) LDPlayer9_ens_1001_ld.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\lden |
| Operation: | write | Name: | pcmac |
Value: 5f76b7939c1d0c92e8f8d4c0bf100f64 | |||
| (PID) Process: | (4320) LDPlayer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\ld\dnplayer_en |
| Operation: | write | Name: | pcid |
Value: 5f76b7939c1d0c92e8f8d4c0bf100f64 | |||
| (PID) Process: | (3172) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Usages\1.3.6.1.5.5.7.3.3 |
| Operation: | write | Name: | DefaultId |
Value: {00AAC56B-CD44-11D0-8CC2-00C04FC295EE} | |||
| (PID) Process: | (3172) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\FinalPolicy\{00AAC56B-CD44-11D0-8CC2-00C04FC295EE} |
| Operation: | write | Name: | $DLL |
Value: WINTRUST.DLL | |||
| (PID) Process: | (3172) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\FinalPolicy\{00AAC56B-CD44-11D0-8CC2-00C04FC295EE} |
| Operation: | write | Name: | $Function |
Value: SoftpubAuthenticode | |||
| (PID) Process: | (3172) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Initialization\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $DLL |
Value: WINTRUST.DLL | |||
| (PID) Process: | (3172) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Initialization\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $Function |
Value: SoftpubInitialize | |||
| (PID) Process: | (3172) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Message\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $DLL |
Value: WINTRUST.DLL | |||
| (PID) Process: | (3172) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Message\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $Function |
Value: SoftpubLoadMessage | |||
| (PID) Process: | (3172) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Cryptography\Providers\Trust\Signature\{64B9D180-8DA2-11CF-8736-00AA00A485EB} |
| Operation: | write | Name: | $DLL |
Value: WINTRUST.DLL | |||
Executable files
478
Suspicious files
554
Text files
203
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6156 | LDPlayer9_ens_1001_ld.exe | C:\LDPlayer\LDPlayer9\LDPlayer.exe.tmp | — | |
MD5:— | SHA256:— | |||
| 6156 | LDPlayer9_ens_1001_ld.exe | C:\LDPlayer\LDPlayer9\LDPlayer.exe | — | |
MD5:— | SHA256:— | |||
| 4320 | LDPlayer.exe | C:\Users\admin\AppData\Roaming\XuanZhi\fonts\NotoSans-Regular.otf | — | |
MD5:— | SHA256:— | |||
| 4320 | LDPlayer.exe | C:\LDPlayer\LDPlayer9\data-3G.vmdk | — | |
MD5:— | SHA256:— | |||
| 4320 | LDPlayer.exe | C:\LDPlayer\LDPlayer9\data.vmdk | — | |
MD5:— | SHA256:— | |||
| 4320 | LDPlayer.exe | C:\LDPlayer\LDPlayer9\dnresource.rcc | — | |
MD5:— | SHA256:— | |||
| 6156 | LDPlayer9_ens_1001_ld.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B039FEA45CB4CC4BBACFC013C7C55604_32532FE6EE279C8A04951B3E75CC9341 | binary | |
MD5:FC35BBBB7B10D3301A37121FEEE269B3 | SHA256:EA953B75E416EA9E21296B9771AD97002733888109B0A924AAA2C8FF339A5520 | |||
| 4320 | LDPlayer.exe | C:\LDPlayer\LDPlayer9\backup_icon.ico | image | |
MD5:0549142952918BE8CB7E6AF8C8A5C9F7 | SHA256:8A06CE27B58CEBBF42D53923A5060EFD20F32F6576F37D6196B72902555BD522 | |||
| 6156 | LDPlayer9_ens_1001_ld.exe | C:\Users\admin\AppData\Roaming\lddownloader_en\fonts\Roboto-Regular.otf | ttf | |
MD5:4ACD5F0E312730F1D8B8805F3699C184 | SHA256:72336333D602F1C3506E642E0D0393926C0EC91225BF2E4D216FCEBD82BB6CB5 | |||
| 6156 | LDPlayer9_ens_1001_ld.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B039FEA45CB4CC4BBACFC013C7C55604_32532FE6EE279C8A04951B3E75CC9341 | der | |
MD5:3593C317B9D0CAC065066ACEF58F2243 | SHA256:128C5E71B2FBDEF45050061871822CF0C8DCA8EEDAB443B5E924E369A49C8CDD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
297
DNS requests
267
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6156 | LDPlayer9_ens_1001_ld.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ5rEWLwbJFq%2FmAU80sm7E%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6156 | LDPlayer9_ens_1001_ld.exe | GET | 200 | 104.18.20.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEH6Hwxq9kZ5xalNEESzfRqk%3D | unknown | — | — | whitelisted |
6280 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7144 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7144 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4320 | LDPlayer.exe | GET | 301 | 163.181.131.177:80 | http://apien.ldmnq.com/statisticsMnqEvent?sv=0900012603&openid=1001&m=5f76b7939c1d0c92e8f8d4c0bf100f64&event_key=install&event_value=&event_type=player&z=1733292673 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3508 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 104.126.37.184:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6156 | LDPlayer9_ens_1001_ld.exe | 163.181.92.232:443 | res.ldrescdn.com | Zhejiang Taobao Network Co.,Ltd | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
res.ldrescdn.com |
| unknown |
www.google-analytics.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
apien.ldmnq.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1328 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1328 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1328 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1328 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1328 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1328 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
1328 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1328 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1328 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
1328 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |