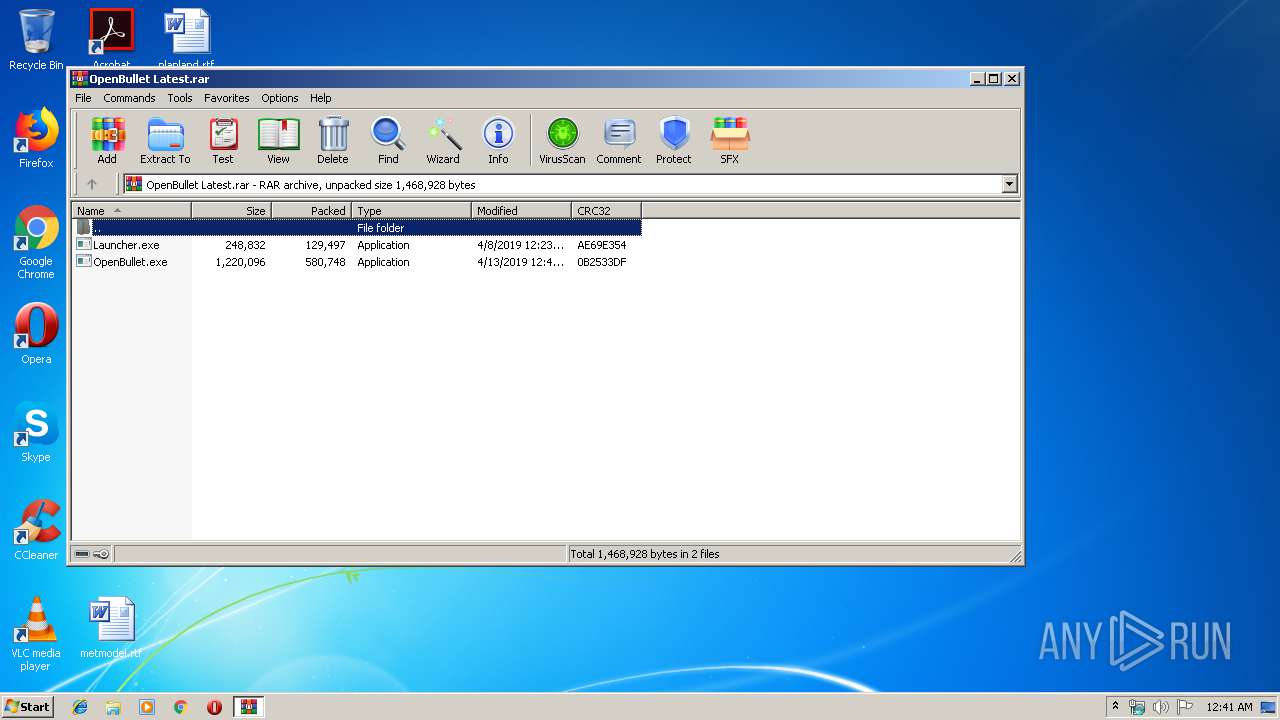
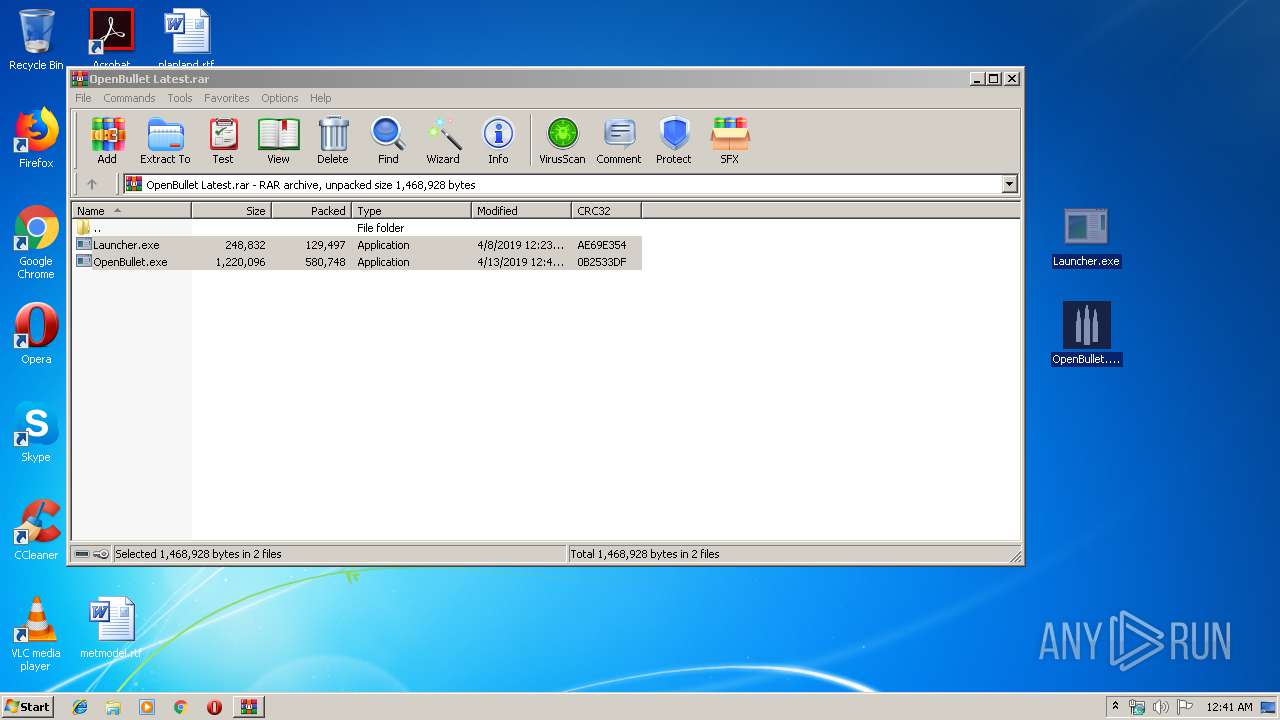
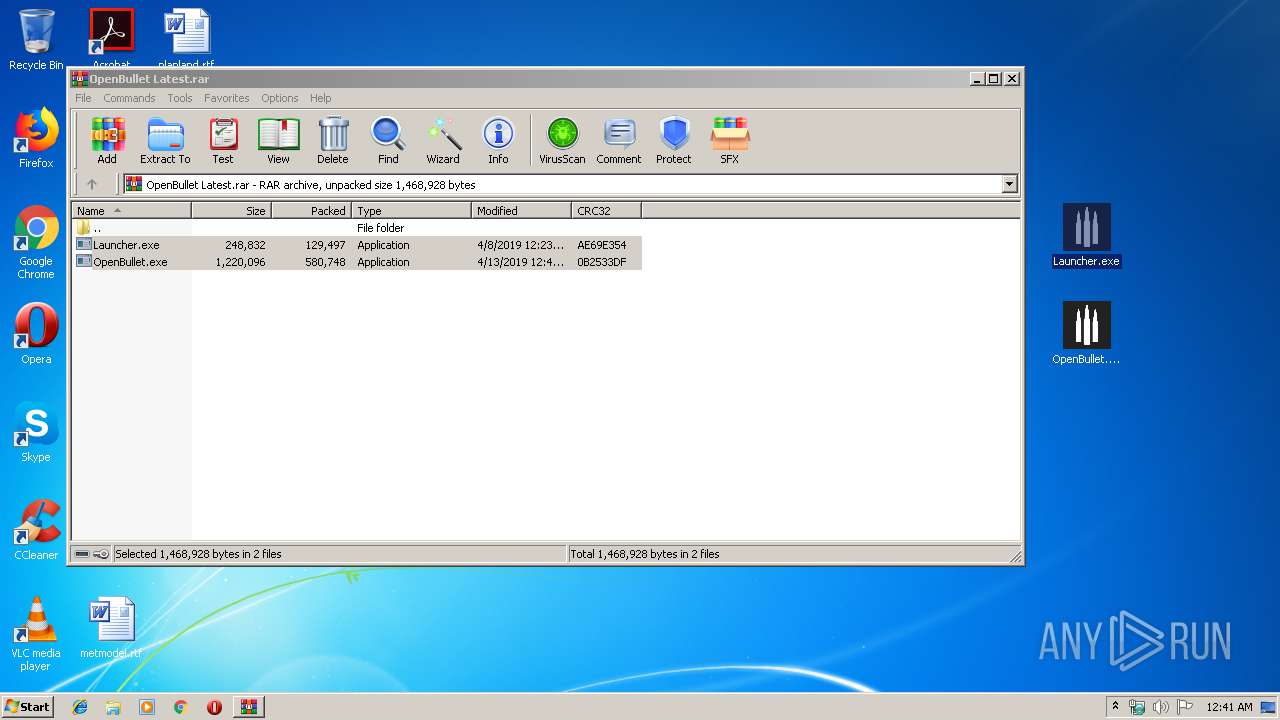
| File name: | OpenBullet Latest.rar |
| Full analysis: | https://app.any.run/tasks/4b888502-29fa-4e1f-9117-8d01ebfc1bb7 |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2019, 23:41:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 099DB5D09B48B3DD30B306066C31D149 |
| SHA1: | 47F635DA9D7C77D9EDF7076DBEBD944361E1FB51 |
| SHA256: | 0B9E6BFF272B85C7B272548E1729185B0FA11F8892093D72A70613CF446D2001 |
| SSDEEP: | 12288:OROk+WuBjvARx3LYuq/G2lDtoTNNYN6PyrT6z4gYwpD8dBFFlOQVAxFPEp8U77Qs:O4k+n03MsVUdHwizEwIEp8qQ0L |
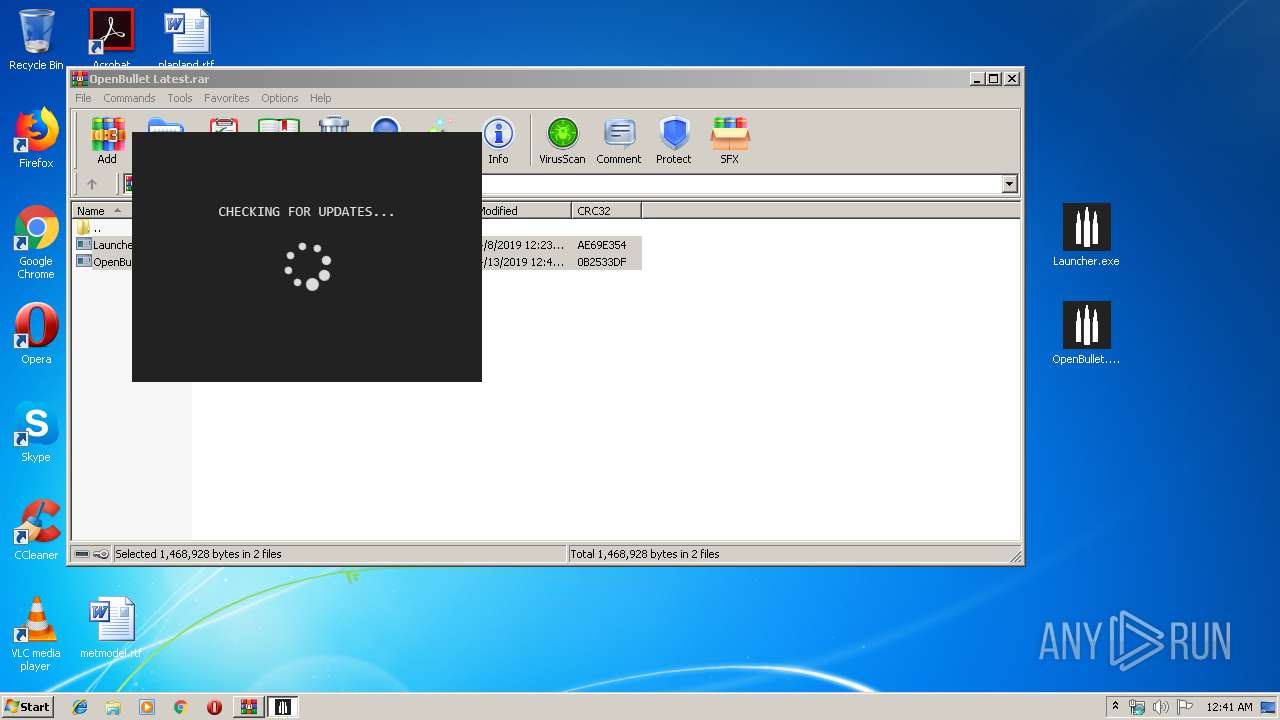
MALICIOUS
Application was dropped or rewritten from another process
- Launcher.exe (PID: 2896)
Changes settings of System certificates
- Launcher.exe (PID: 2896)
SUSPICIOUS
Reads Environment values
- Launcher.exe (PID: 2896)
Adds / modifies Windows certificates
- Launcher.exe (PID: 2896)
INFO
Reads settings of System Certificates
- Launcher.exe (PID: 2896)
Creates files in the user directory
- opera.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
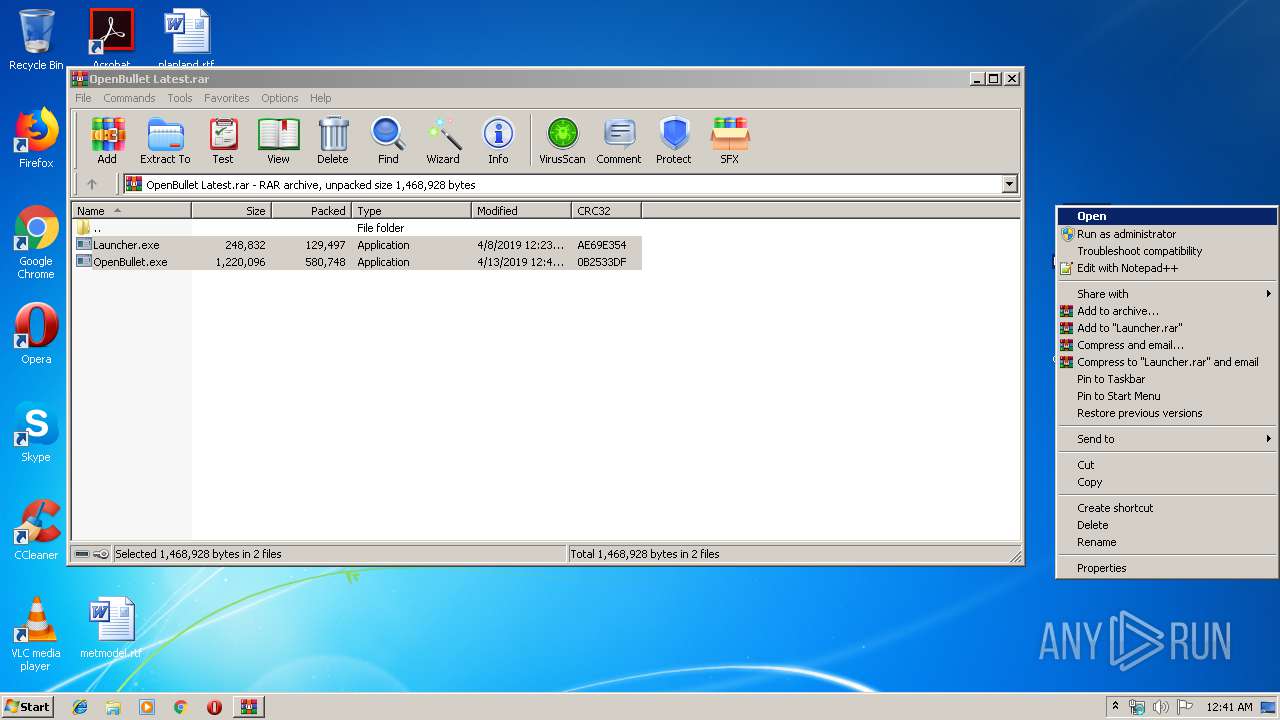
| 2840 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\OpenBullet Latest.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2896 | "C:\Users\admin\Desktop\Launcher.exe" | C:\Users\admin\Desktop\Launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
732
Read events
587
Write events
145
Delete events
0
Modification events
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\OpenBullet Latest.rar | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2840) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2896) Launcher.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Launcher.exe | |||
| (PID) Process: | (2896) Launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Launcher_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
18
Text files
9
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2840.30094\OpenBullet.exe | — | |
MD5:— | SHA256:— | |||
| 2840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2840.30094\Launcher.exe | — | |
MD5:— | SHA256:— | |||
| 3148 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprC19E.tmp | — | |
MD5:— | SHA256:— | |||
| 3148 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprC1CD.tmp | — | |
MD5:— | SHA256:— | |||
| 3148 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Y2FLLPNHVXF1NQ3IHQCK.temp | — | |
MD5:— | SHA256:— | |||
| 3148 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XZEC7E3X82JP8JPA50SX.temp | — | |
MD5:— | SHA256:— | |||
| 3148 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\oprD40E.tmp | — | |
MD5:— | SHA256:— | |||
| 3148 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprD41F.tmp | — | |
MD5:— | SHA256:— | |||
| 3148 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\oprD420.tmp | — | |
MD5:— | SHA256:— | |||
| 3148 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | opera.exe | GET | — | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | — | — | whitelisted |
3148 | opera.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2896 | Launcher.exe | 151.101.132.133:443 | raw.githubusercontent.com | Fastly | US | unknown |
3148 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
3148 | opera.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3148 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |