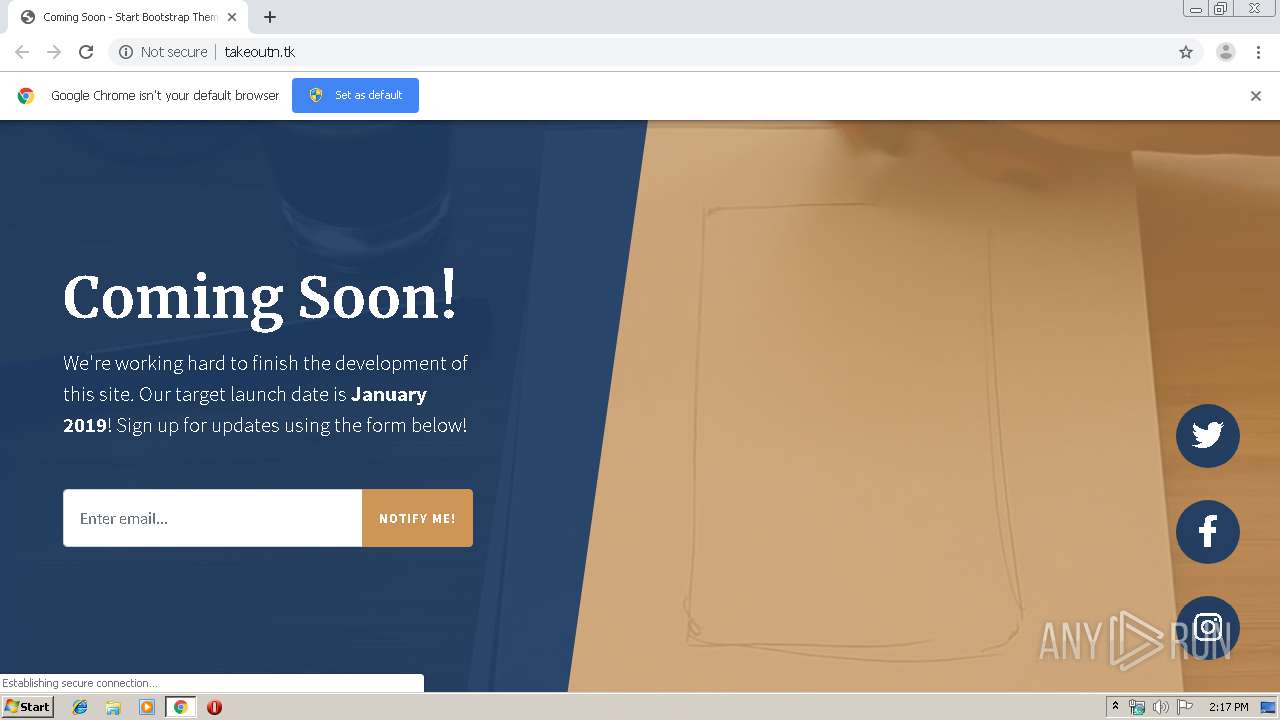
| URL: | http://takeoutn.tk/ |
| Full analysis: | https://app.any.run/tasks/2e236a3d-4b7f-43e3-8175-307afe8006cd |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 13:16:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5BA5755DC1C07C592ED72ADBD8A42106 |
| SHA1: | 2C664DE52A830F0571FC637DC186F3125D2F9362 |
| SHA256: | 0B958B639DD1E9693A0430D8BB0FAB94C22830F35AF8D9915546C5A24DFC0758 |
| SSDEEP: | 3:N1KKESiLoK:CKq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2948)
INFO
Application launched itself
- chrome.exe (PID: 2948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,4252422592653738836,5365006269742353809,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15088834497023880992 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,4252422592653738836,5365006269742353809,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3327317103793495844 --mojo-platform-channel-handle=3492 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4252422592653738836,5365006269742353809,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12276067461608436326 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,4252422592653738836,5365006269742353809,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9490100800753961708 --mojo-platform-channel-handle=2896 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,4252422592653738836,5365006269742353809,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10298641915348527331 --mojo-platform-channel-handle=3728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,4252422592653738836,5365006269742353809,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10317602308801207395 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,4252422592653738836,5365006269742353809,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2960531068360359874 --mojo-platform-channel-handle=3316 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,4252422592653738836,5365006269742353809,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17990259979184059634 --mojo-platform-channel-handle=3380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,4252422592653738836,5365006269742353809,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6899543273924769381 --mojo-platform-channel-handle=3816 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4252422592653738836,5365006269742353809,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12540155454273109433 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2200 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
614
Read events
522
Write events
87
Delete events
5
Modification events
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2948-13207324624022375 |
Value: 259 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
28
Text files
188
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1538ec.TMP | — | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\622a840f-9021-46b7-8366-c4a1ba4fd437.tmp | — | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF153959.TMP | text | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF153978.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
25
DNS requests
15
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2480 | chrome.exe | GET | 200 | 185.50.69.183:80 | http://takeoutn.tk/css/coming-soon.min.css | TR | text | 3.04 Kb | suspicious |
2480 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 512 b | whitelisted |
2480 | chrome.exe | GET | 200 | 185.50.69.183:80 | http://takeoutn.tk/ | TR | html | 2.68 Kb | suspicious |
2480 | chrome.exe | GET | 200 | 185.50.69.183:80 | http://takeoutn.tk/js/coming-soon.min.js | TR | text | 262 b | suspicious |
2480 | chrome.exe | GET | 200 | 185.50.69.183:80 | http://takeoutn.tk/vendor/fontawesome-free/css/all.min.css | TR | text | 54.6 Kb | suspicious |
2480 | chrome.exe | GET | 200 | 185.50.69.183:80 | http://takeoutn.tk/vendor/fontawesome-free/webfonts/fa-brands-400.woff2 | TR | woff2 | 72.7 Kb | suspicious |
2480 | chrome.exe | GET | 200 | 185.50.69.183:80 | http://takeoutn.tk/vendor/bootstrap/js/bootstrap.bundle.min.js | TR | text | 76.7 Kb | suspicious |
2480 | chrome.exe | GET | 200 | 173.194.7.89:80 | http://r3---sn-p5qs7n7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.5&mm=28&mn=sn-p5qs7n7e&ms=nvh&mt=1562850937&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2480 | chrome.exe | GET | 206 | 185.50.69.183:80 | http://takeoutn.tk/mp4/bg.mp4 | TR | 3g2 | 6.09 Mb | suspicious |
2480 | chrome.exe | GET | 200 | 185.50.69.183:80 | http://takeoutn.tk/vendor/jquery/jquery.min.js | TR | text | 86.0 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2480 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2480 | chrome.exe | 185.50.69.183:80 | takeoutn.tk | Istanbuldc Veri Merkezi Ltd. Sti | TR | suspicious |
2480 | chrome.exe | 172.217.21.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
2480 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2480 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2480 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
2480 | chrome.exe | 172.217.16.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2480 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2480 | chrome.exe | 173.194.7.89:80 | r3---sn-p5qs7n7e.gvt1.com | Google Inc. | US | whitelisted |
— | — | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
takeoutn.tk |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2480 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2480 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2480 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2480 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2480 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2480 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2480 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2480 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2480 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2480 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |