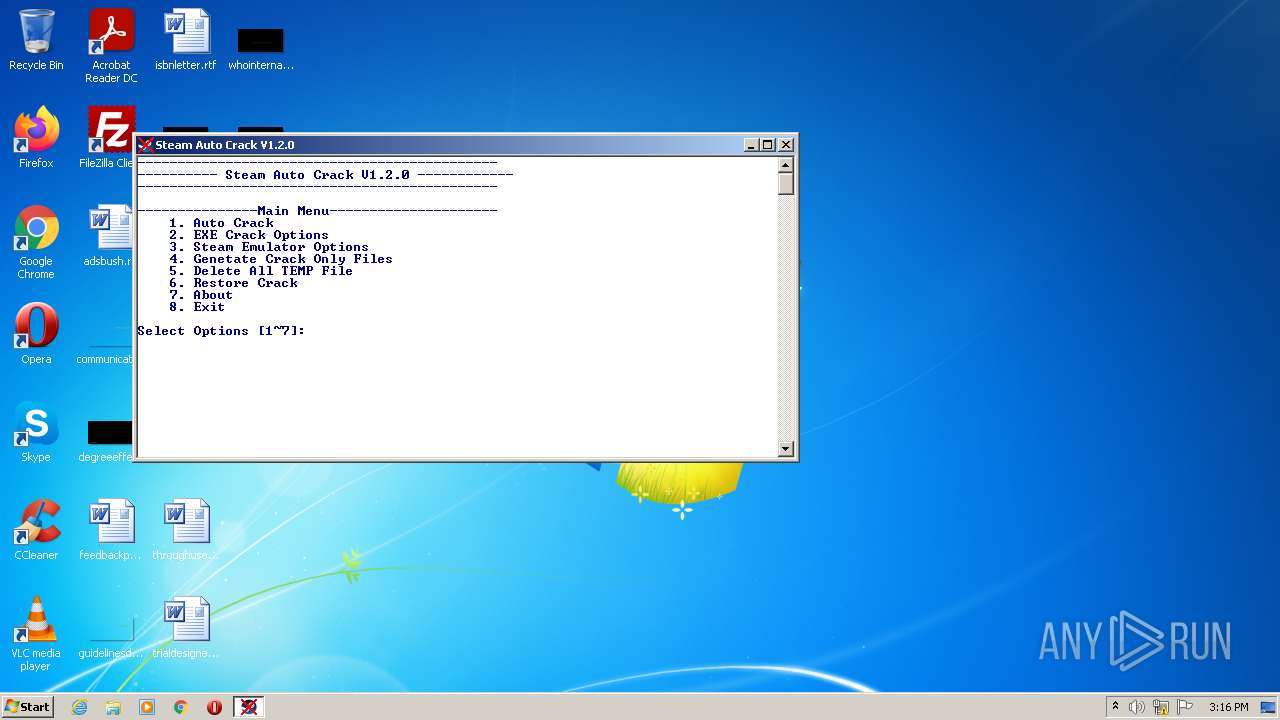
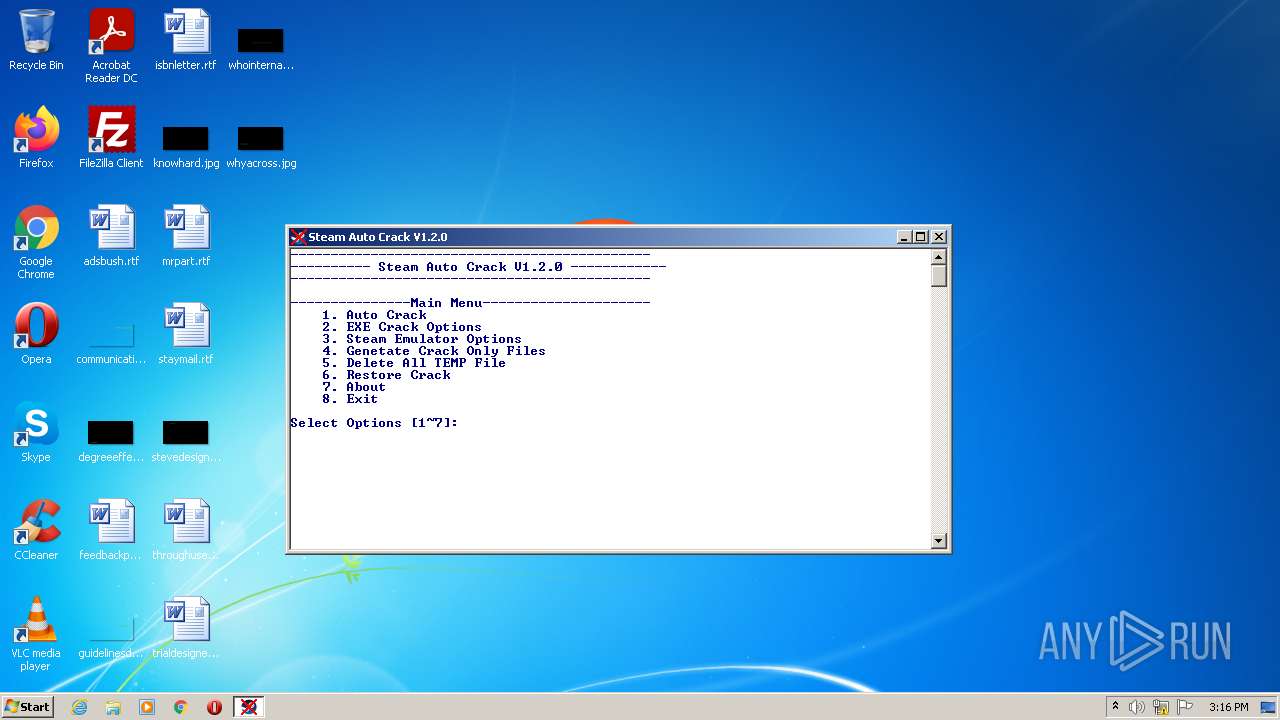
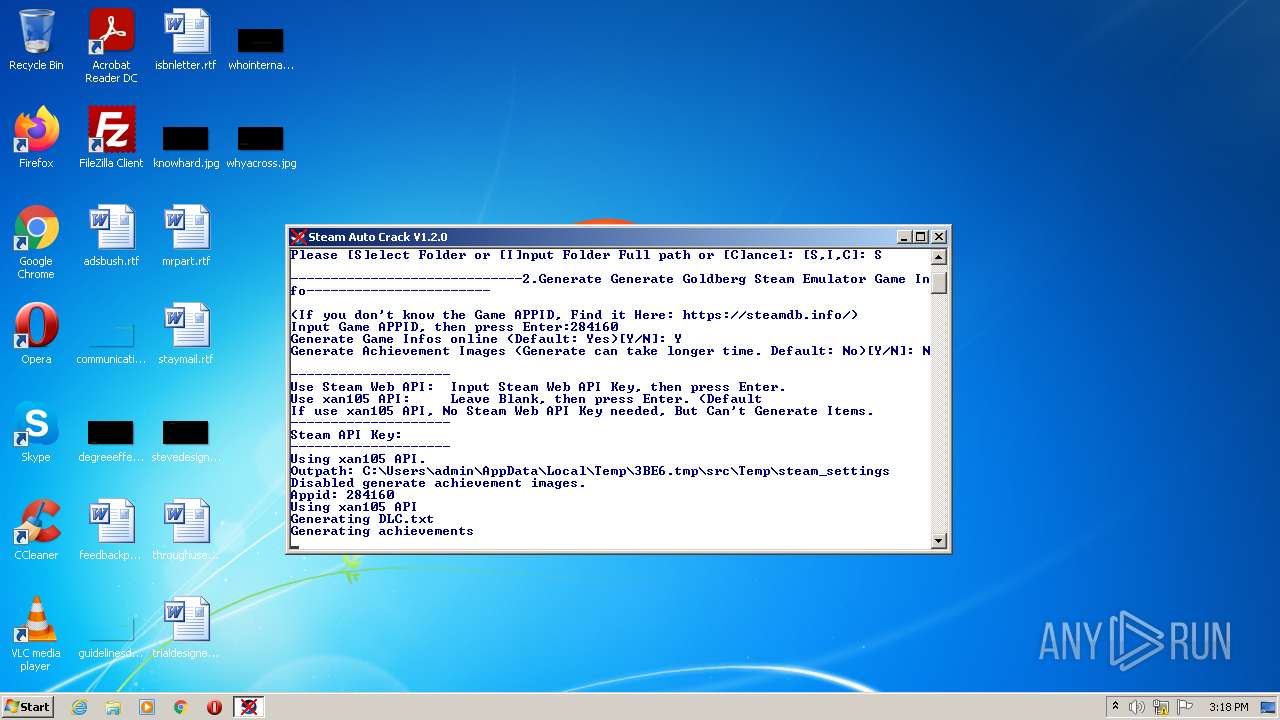
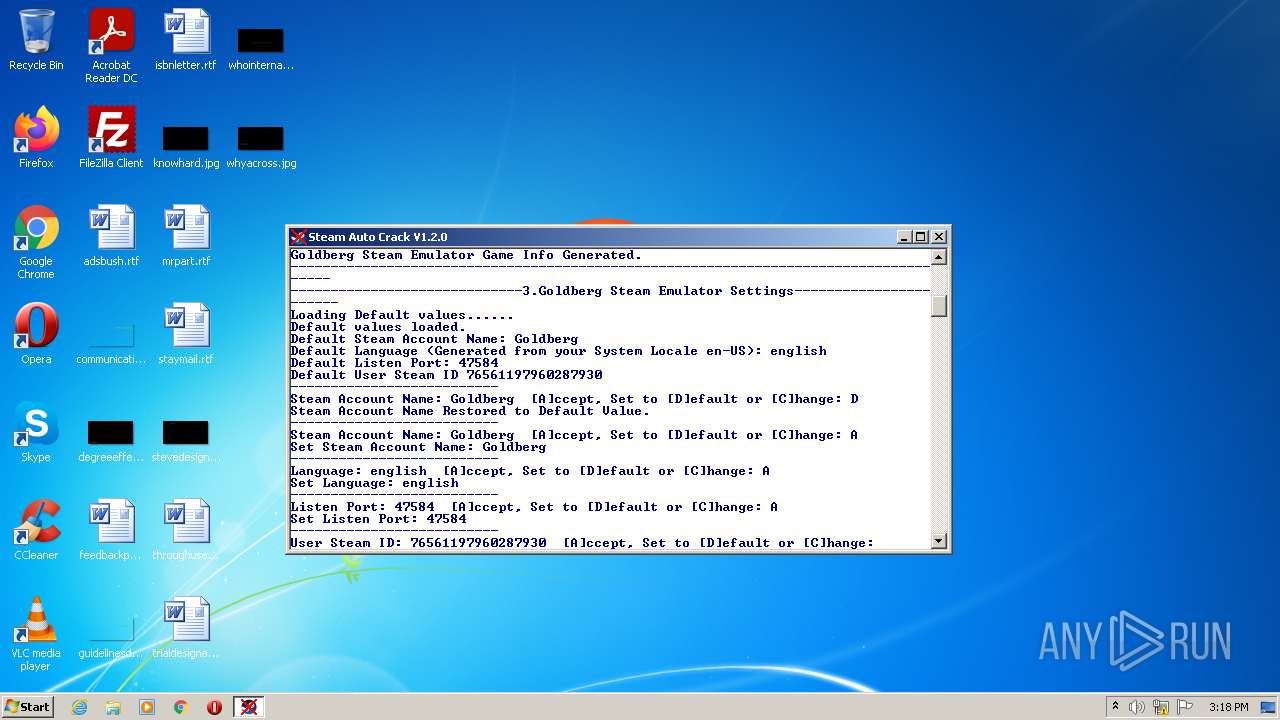
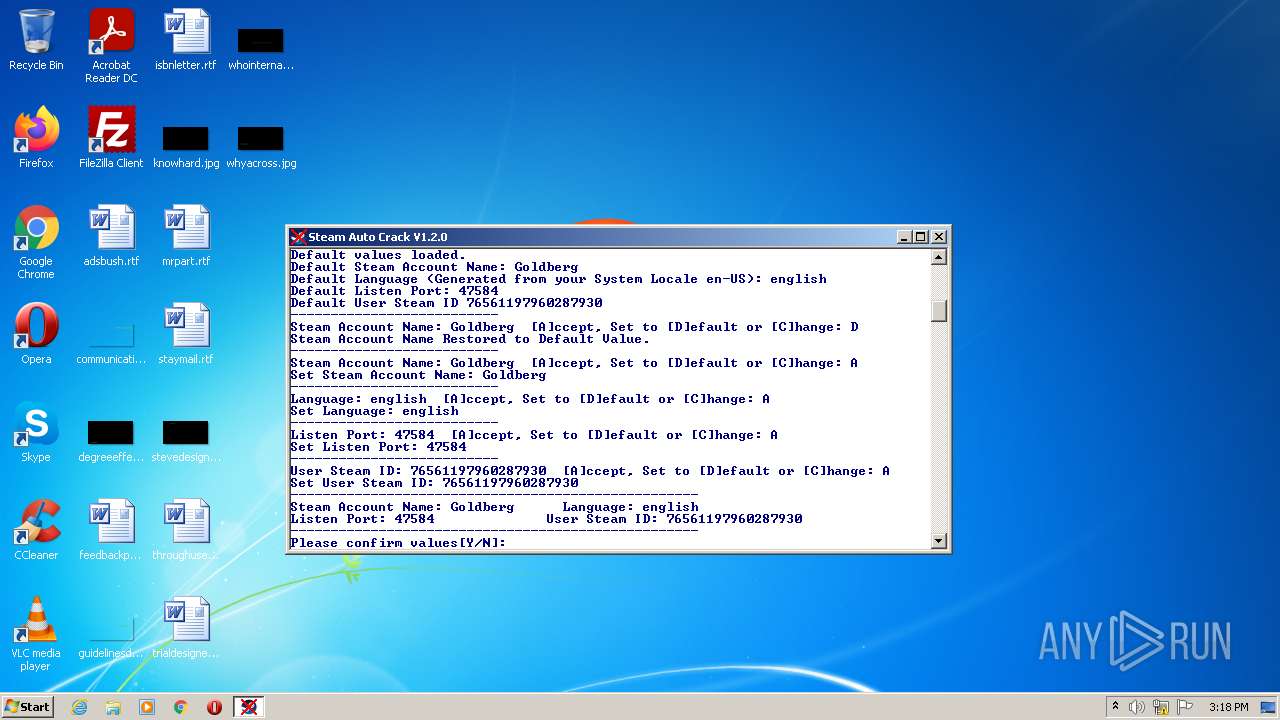
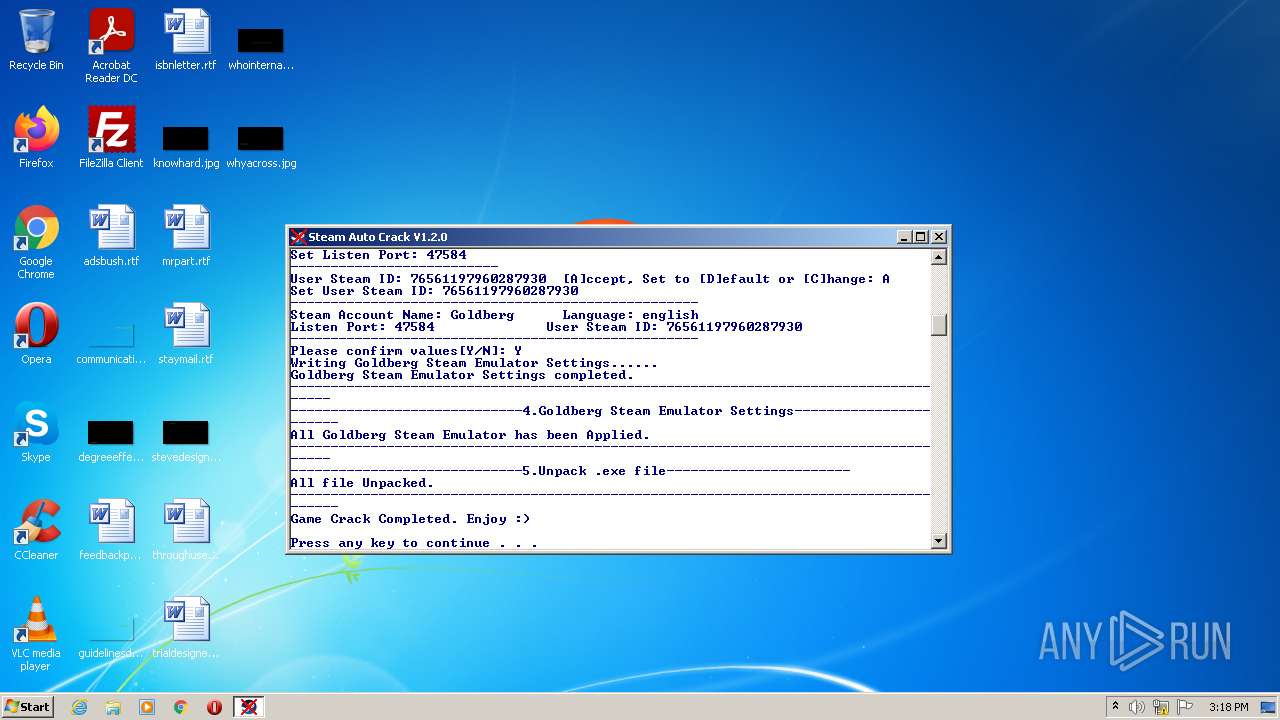
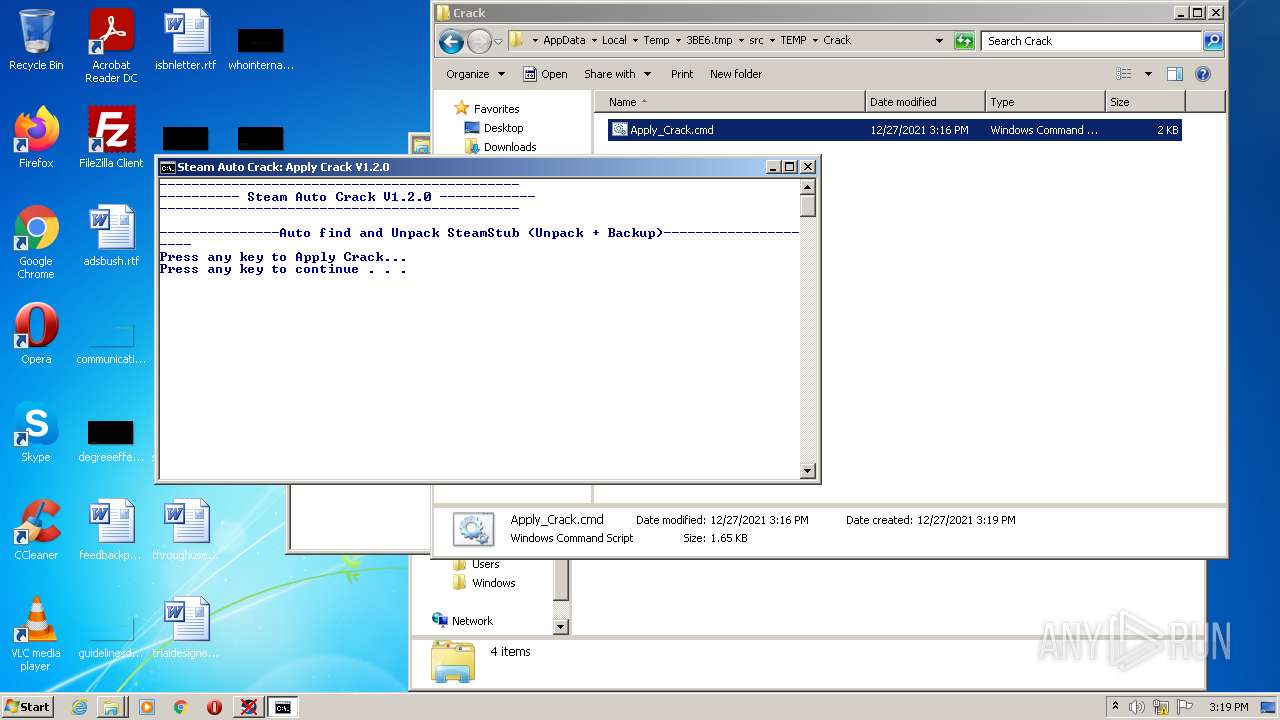
| download: | SteamAutoCrack.exe |
| Full analysis: | https://app.any.run/tasks/a97df5f3-b538-4f9e-b9ef-837d2fbbd826 |
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2021, 15:16:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | ABF42EE2908B3DFCC3E981B276B1CAB4 |
| SHA1: | C90C54226DDEBFF0899BB5B70E629BF7FDC46DD1 |
| SHA256: | 0B70AF2587F0D308C1278609FE2A25126C80474AFEBE8DACE4270A8A61961918 |
| SSDEEP: | 196608:1vHylWw3loN2Fdbrnt+PRUUOWMUdOgwROncQXzZGIvT16BWZCoAS:Q4waNWdvt+JxOWMUdQ0nZXzZGU6BWAS |
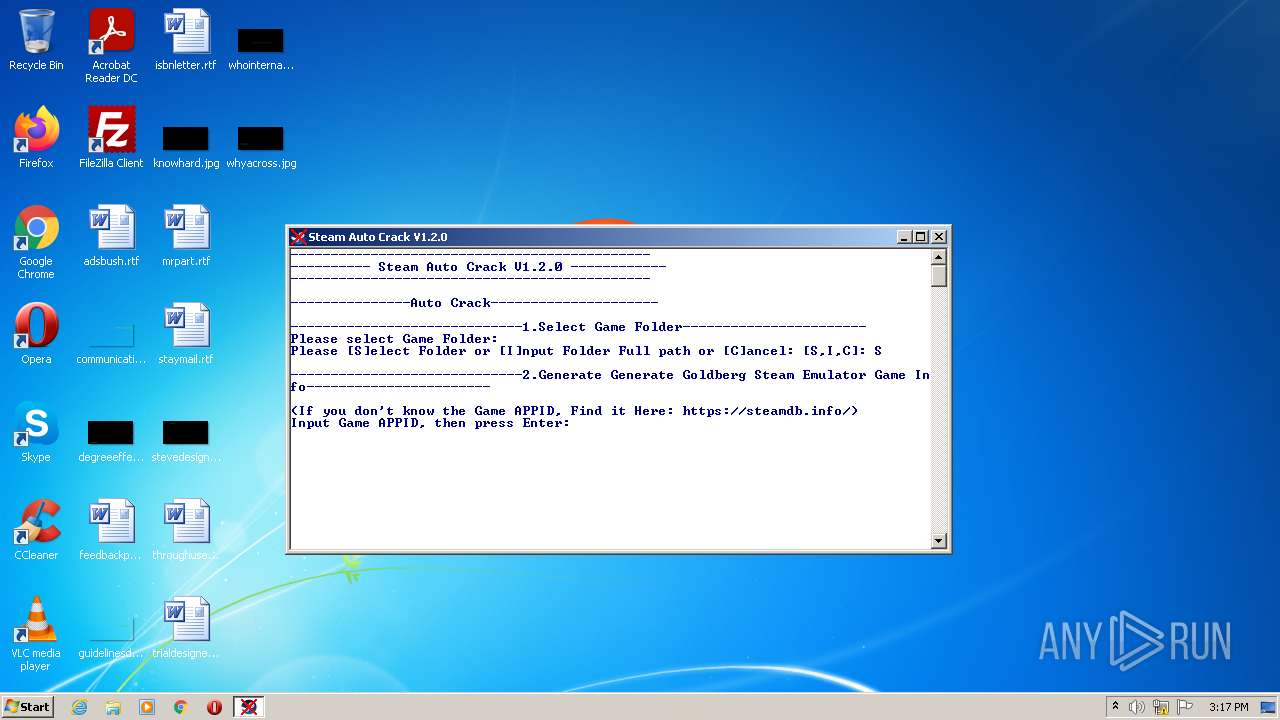
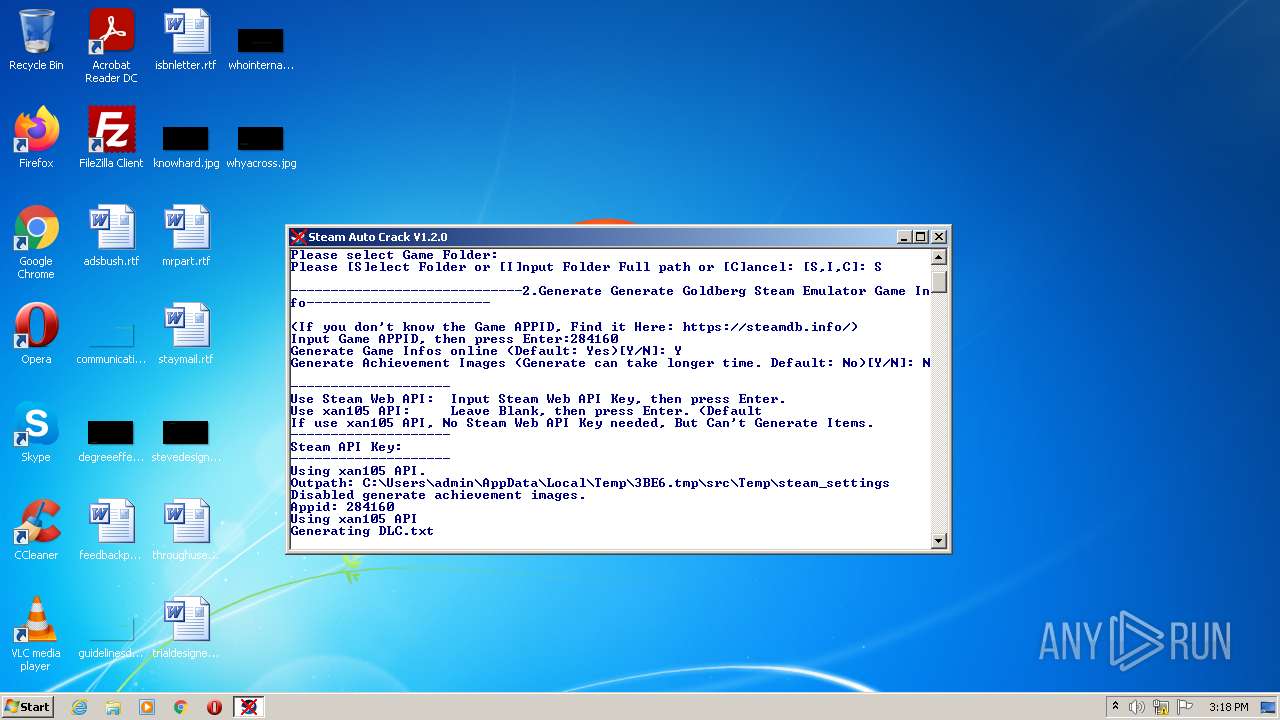
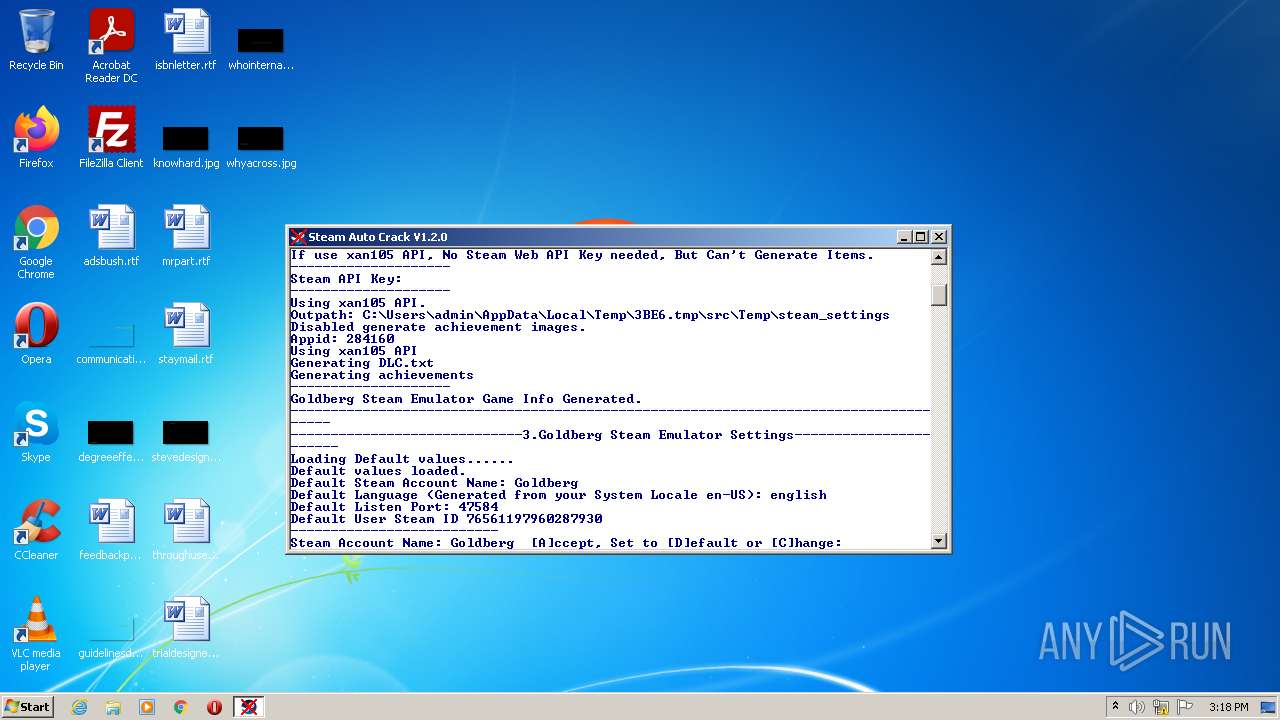
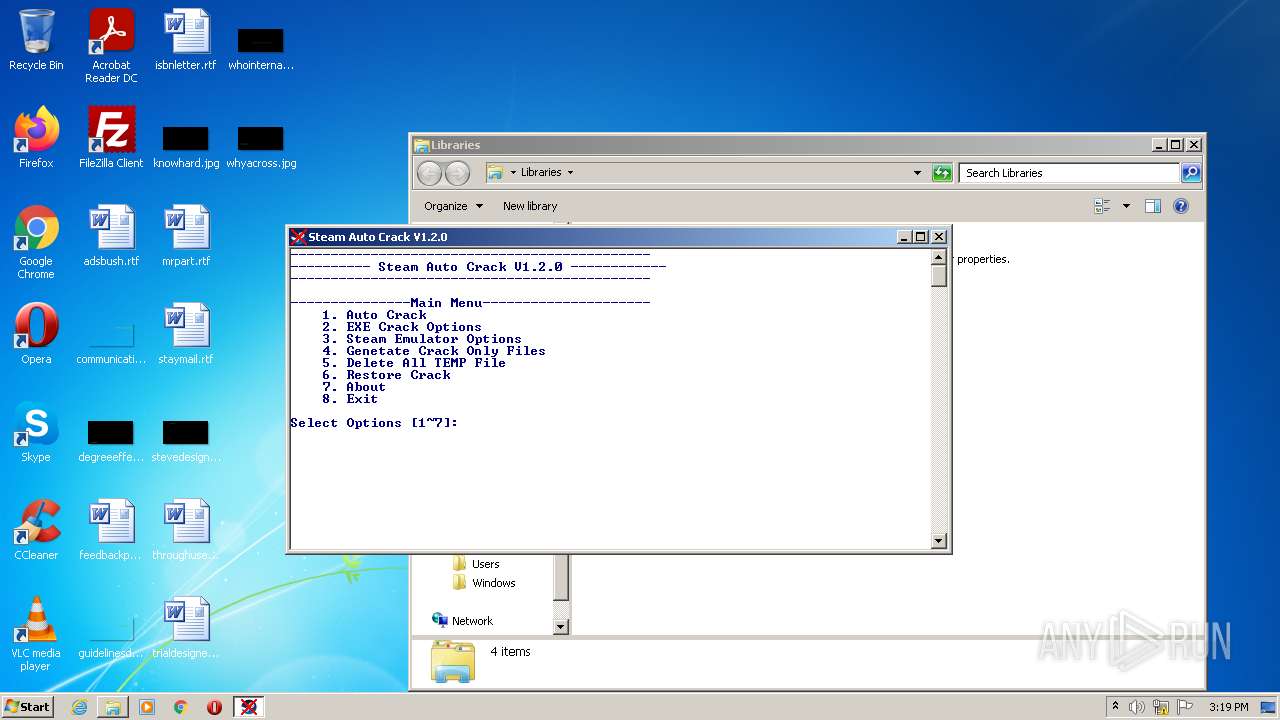
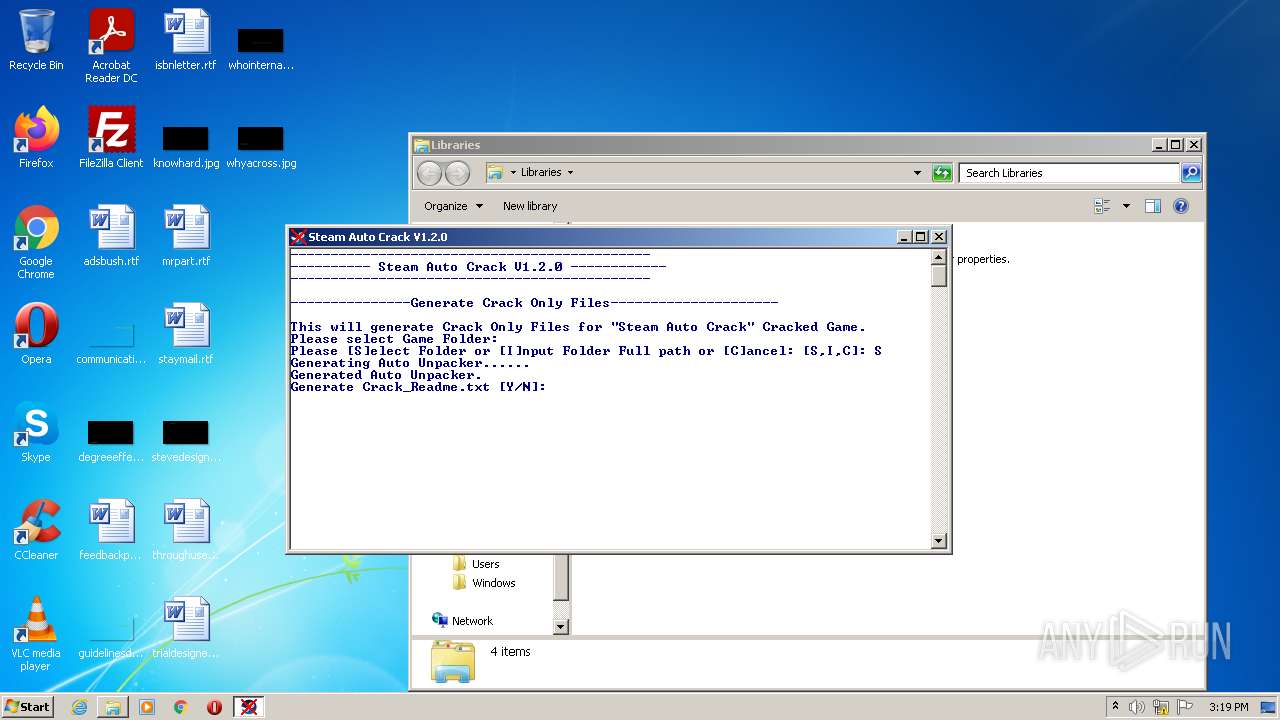
MALICIOUS
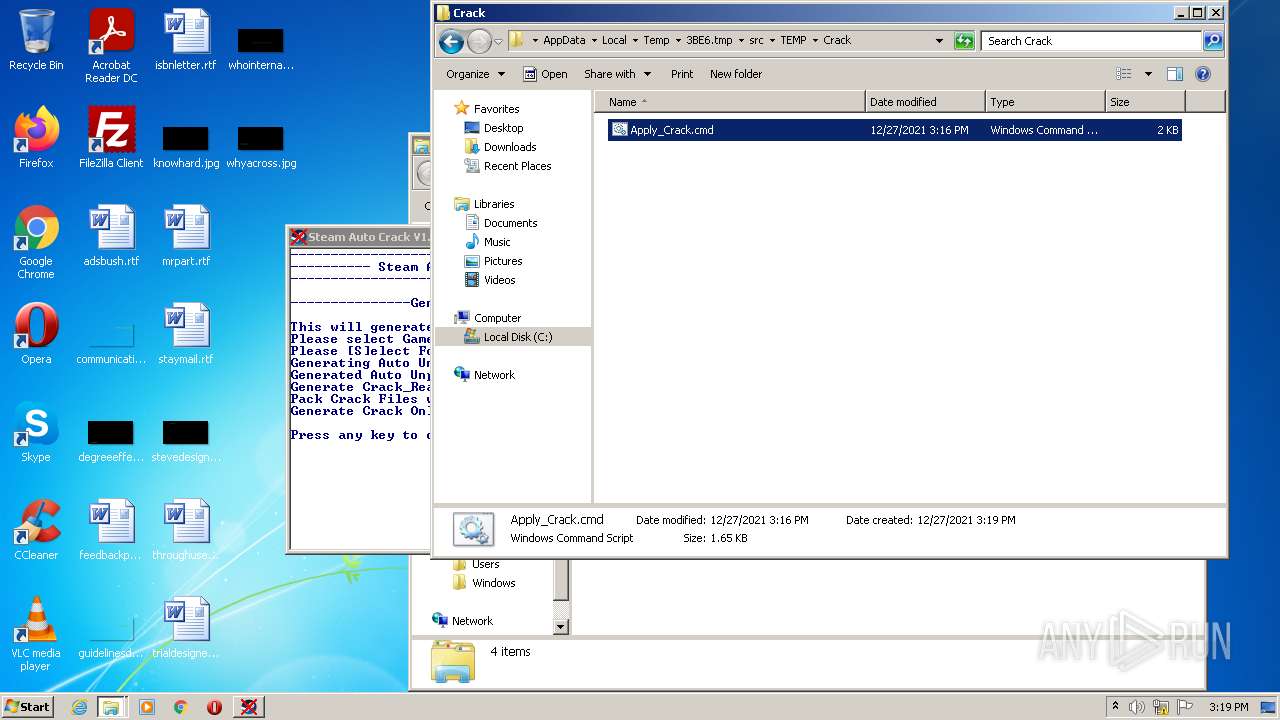
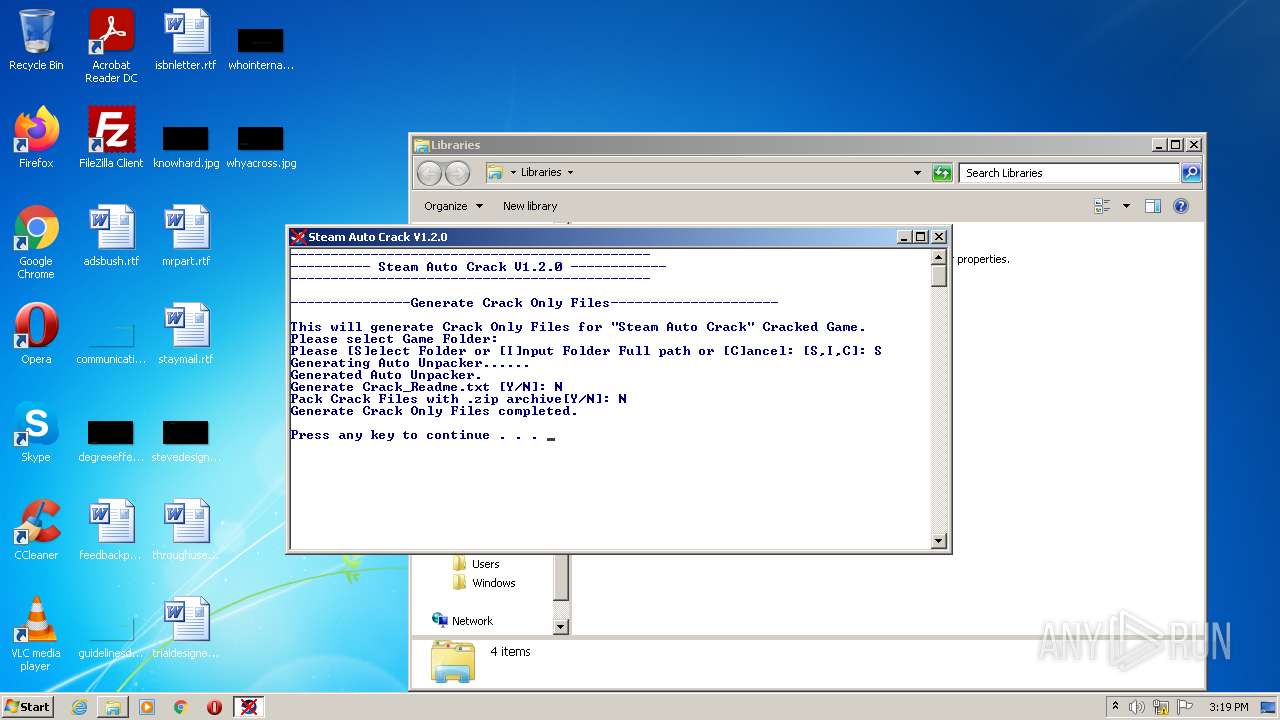
Drops executable file immediately after starts
- SteamAutoCrack.exe (PID: 3224)
Executes PowerShell scripts
- cmd.exe (PID: 2840)
- cmd.exe (PID: 3064)
Loads dropped or rewritten executable
- generate_game_infos.exe (PID: 2280)
Application was dropped or rewritten from another process
- generate_game_infos.exe (PID: 2280)
SUSPICIOUS
Checks supported languages
- SteamAutoCrack.exe (PID: 3224)
- cmd.exe (PID: 3576)
- chcp.com (PID: 1040)
- cmd.exe (PID: 2840)
- powershell.exe (PID: 3736)
- cmd.exe (PID: 3332)
- generate_game_infos.exe (PID: 2280)
- cmd.exe (PID: 3904)
- cmd.exe (PID: 336)
- cmd.exe (PID: 3460)
- cmd.exe (PID: 3072)
- cmd.exe (PID: 3484)
- cmd.exe (PID: 1332)
- cmd.exe (PID: 2056)
- cmd.exe (PID: 764)
- cmd.exe (PID: 1988)
- cmd.exe (PID: 476)
- cmd.exe (PID: 448)
- cmd.exe (PID: 2484)
- cmd.exe (PID: 3832)
- cmd.exe (PID: 2472)
- cmd.exe (PID: 3976)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 3084)
- cmd.exe (PID: 3540)
- cmd.exe (PID: 4028)
- cmd.exe (PID: 3348)
- cmd.exe (PID: 2628)
- cmd.exe (PID: 3000)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 1516)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 2536)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3812)
- cmd.exe (PID: 1488)
- cmd.exe (PID: 2396)
- cmd.exe (PID: 2272)
- cmd.exe (PID: 2652)
- cmd.exe (PID: 2756)
- cmd.exe (PID: 2604)
- cmd.exe (PID: 2508)
- cmd.exe (PID: 1488)
- cmd.exe (PID: 3716)
- cmd.exe (PID: 3940)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 3064)
- powershell.exe (PID: 300)
- cmd.exe (PID: 2768)
- chcp.com (PID: 2772)
Drops a file with too old compile date
- SteamAutoCrack.exe (PID: 3224)
Executable content was dropped or overwritten
- SteamAutoCrack.exe (PID: 3224)
Drops a file that was compiled in debug mode
- SteamAutoCrack.exe (PID: 3224)
Drops a file with a compile date too recent
- SteamAutoCrack.exe (PID: 3224)
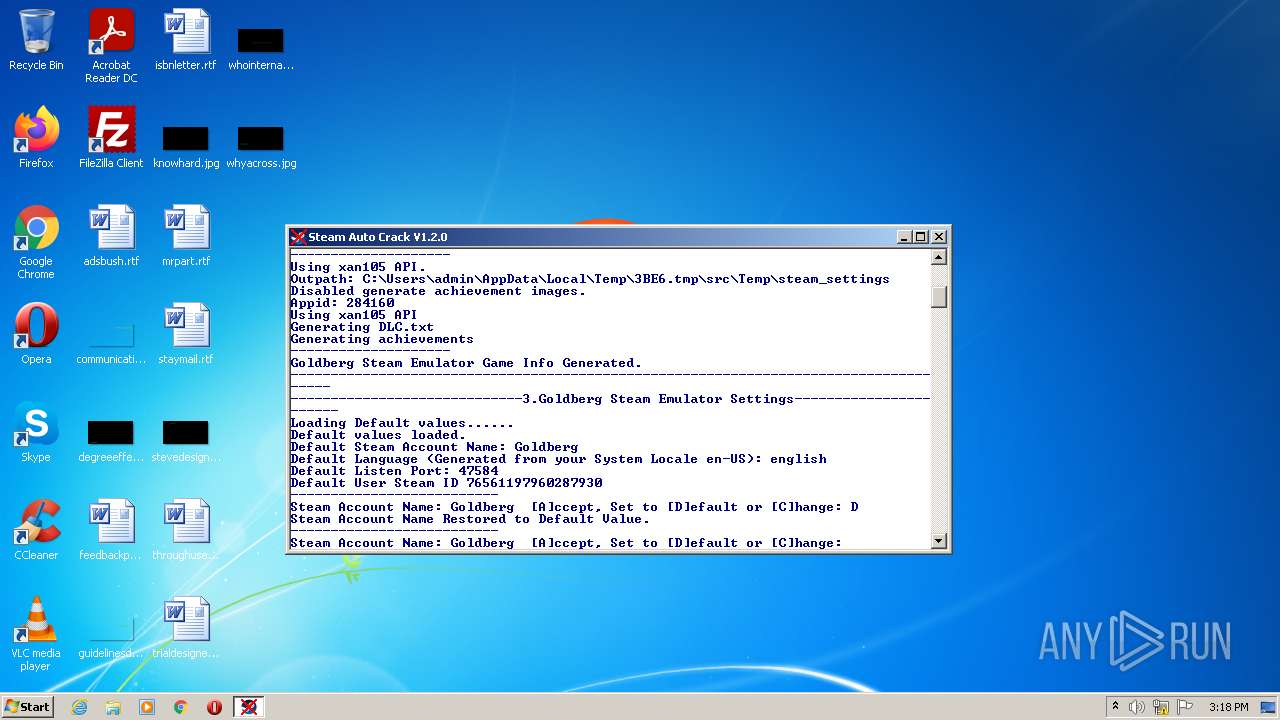
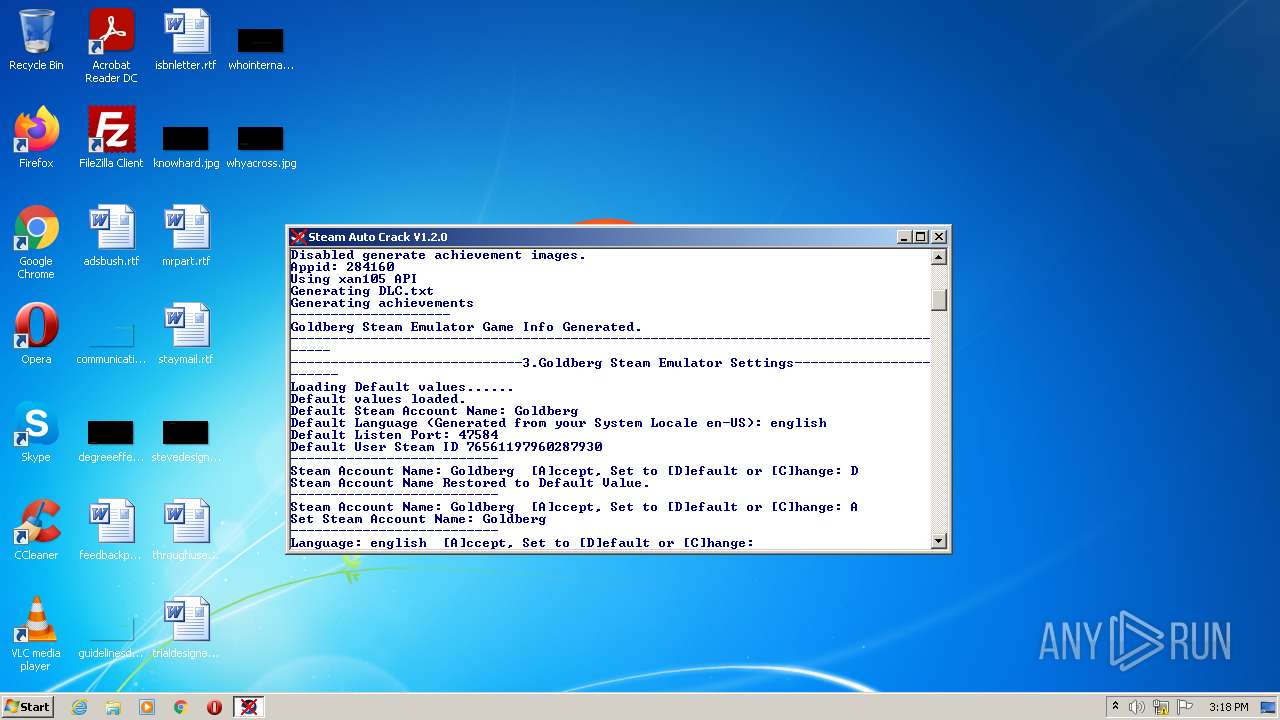
Starts CMD.EXE for commands execution
- SteamAutoCrack.exe (PID: 3224)
- cmd.exe (PID: 3576)
- explorer.exe (PID: 3876)
Starts application with an unusual extension
- cmd.exe (PID: 3576)
- cmd.exe (PID: 2768)
Reads the computer name
- powershell.exe (PID: 3736)
- generate_game_infos.exe (PID: 2280)
- powershell.exe (PID: 300)
Application launched itself
- cmd.exe (PID: 3576)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 3576)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3904)
Executed via COM
- explorer.exe (PID: 3876)
Reads the date of Windows installation
- explorer.exe (PID: 3876)
INFO
Dropped object may contain Bitcoin addresses
- SteamAutoCrack.exe (PID: 3224)
Checks supported languages
- choice.exe (PID: 3068)
- choice.exe (PID: 1472)
- choice.exe (PID: 588)
- choice.exe (PID: 2388)
- findstr.exe (PID: 1772)
- reg.exe (PID: 3152)
- findstr.exe (PID: 3284)
- findstr.exe (PID: 2392)
- findstr.exe (PID: 4000)
- findstr.exe (PID: 3644)
- findstr.exe (PID: 1016)
- findstr.exe (PID: 3236)
- findstr.exe (PID: 1700)
- findstr.exe (PID: 2208)
- findstr.exe (PID: 1276)
- findstr.exe (PID: 3620)
- findstr.exe (PID: 3784)
- findstr.exe (PID: 3708)
- findstr.exe (PID: 2516)
- findstr.exe (PID: 1200)
- findstr.exe (PID: 3552)
- findstr.exe (PID: 3112)
- findstr.exe (PID: 3160)
- findstr.exe (PID: 3432)
- findstr.exe (PID: 4040)
- findstr.exe (PID: 268)
- findstr.exe (PID: 3196)
- findstr.exe (PID: 3052)
- findstr.exe (PID: 740)
- findstr.exe (PID: 2232)
- findstr.exe (PID: 2800)
- findstr.exe (PID: 3524)
- findstr.exe (PID: 1992)
- findstr.exe (PID: 2816)
- findstr.exe (PID: 2320)
- findstr.exe (PID: 2648)
- choice.exe (PID: 2624)
- choice.exe (PID: 588)
- choice.exe (PID: 940)
- choice.exe (PID: 3000)
- findstr.exe (PID: 1196)
- choice.exe (PID: 1832)
- choice.exe (PID: 2200)
- choice.exe (PID: 976)
- explorer.exe (PID: 3960)
- choice.exe (PID: 1092)
- choice.exe (PID: 2520)
- xcopy.exe (PID: 2104)
- choice.exe (PID: 3176)
- explorer.exe (PID: 2392)
- explorer.exe (PID: 3876)
Checks Windows Trust Settings
- powershell.exe (PID: 3736)
- powershell.exe (PID: 300)
Manual execution by user
- explorer.exe (PID: 3960)
Reads the computer name
- explorer.exe (PID: 3960)
- explorer.exe (PID: 2392)
- explorer.exe (PID: 3876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 10168832 |
| CodeSize: | 70656 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| TimeStamp: | 2019:07:30 10:52:45+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 30-Jul-2019 08:52:45 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jul-2019 08:52:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x0000387E | 0x00003A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.52922 |
.text | 0x00005000 | 0x0000D962 | 0x0000DA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56249 |
.rdata | 0x00013000 | 0x000033A5 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.11184 |
.data | 0x00017000 | 0x0000178C | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.10108 |
.rsrc | 0x00019000 | 0x009AE31C | 0x009AE400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.95837 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.92322 | 611 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.98905 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.17709 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.82272 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.83018 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 3.76103 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.63747 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 3.58578 | 270376 | Latin 1 / Western European | UNKNOWN | RT_ICON |
02B3EA5852660905BA864512367E4D5F669CF84B | 7.99862 | 126013 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
03773481271099FC7AE57135B072FBC88BCE5A15 | 7.94789 | 3635 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
139
Monitored processes
102
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | findstr /C:it | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 300 | powershell -sta "Add-Type -AssemblyName System.windows.forms|Out-Null;$f=New-Object System.Windows.Forms.FolderBrowserDialog;$f.ShowNewFolderButton=$true;$f.ShowDialog();$f.SelectedPath" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 336 | C:\Windows\system32\cmd.exe /S /D /c" echo en-US " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 448 | C:\Windows\system32\cmd.exe /S /D /c" echo en-US " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 476 | C:\Windows\system32\cmd.exe /S /D /c" echo en-US " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 588 | choice /N /M "Generate Achievement Images (Generate can take longer time. Default: No)[Y/N]:" | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 588 | choice /N /C CDA /M "Steam Account Name: Goldberg [A]ccept, Set to [D]efault or [C]hange:" | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 740 | findstr /C:fi | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | C:\Windows\system32\cmd.exe /S /D /c" echo en-US " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 940 | choice /N /C CDA /M "Language: english [A]ccept, Set to [D]efault or [C]hange:" | C:\Windows\system32\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 713
Read events
8 546
Write events
167
Delete events
0
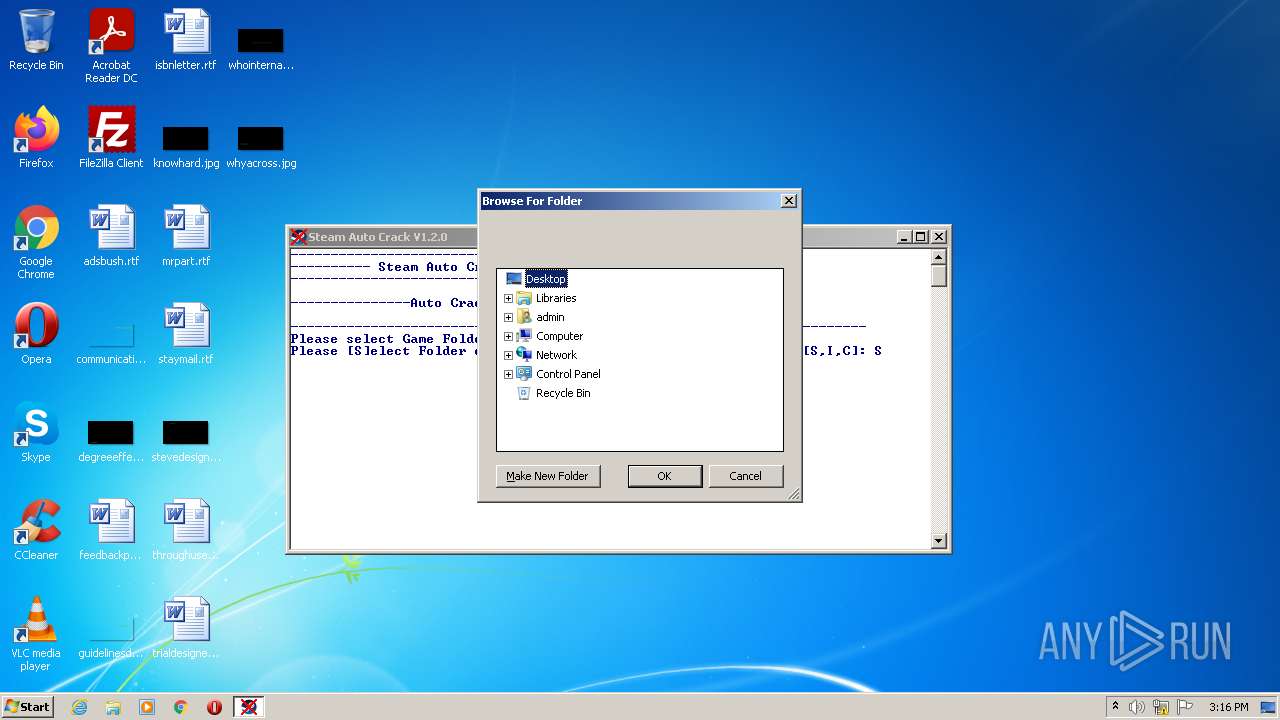
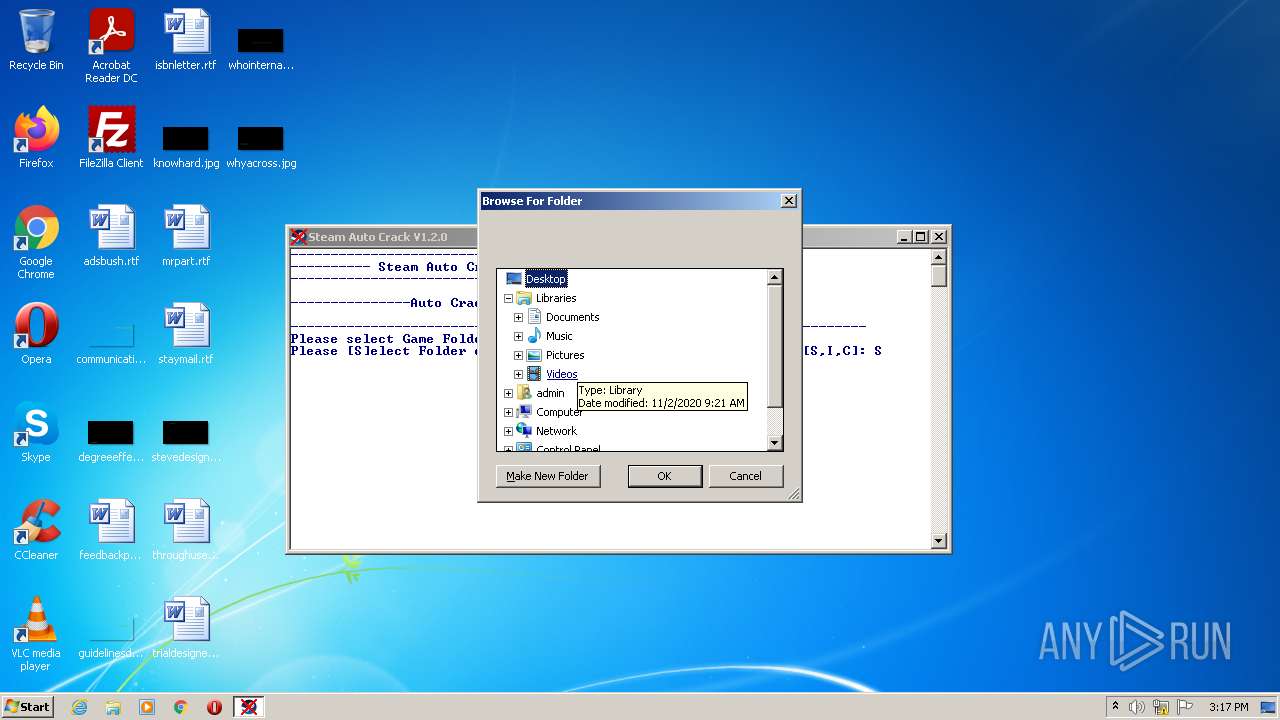
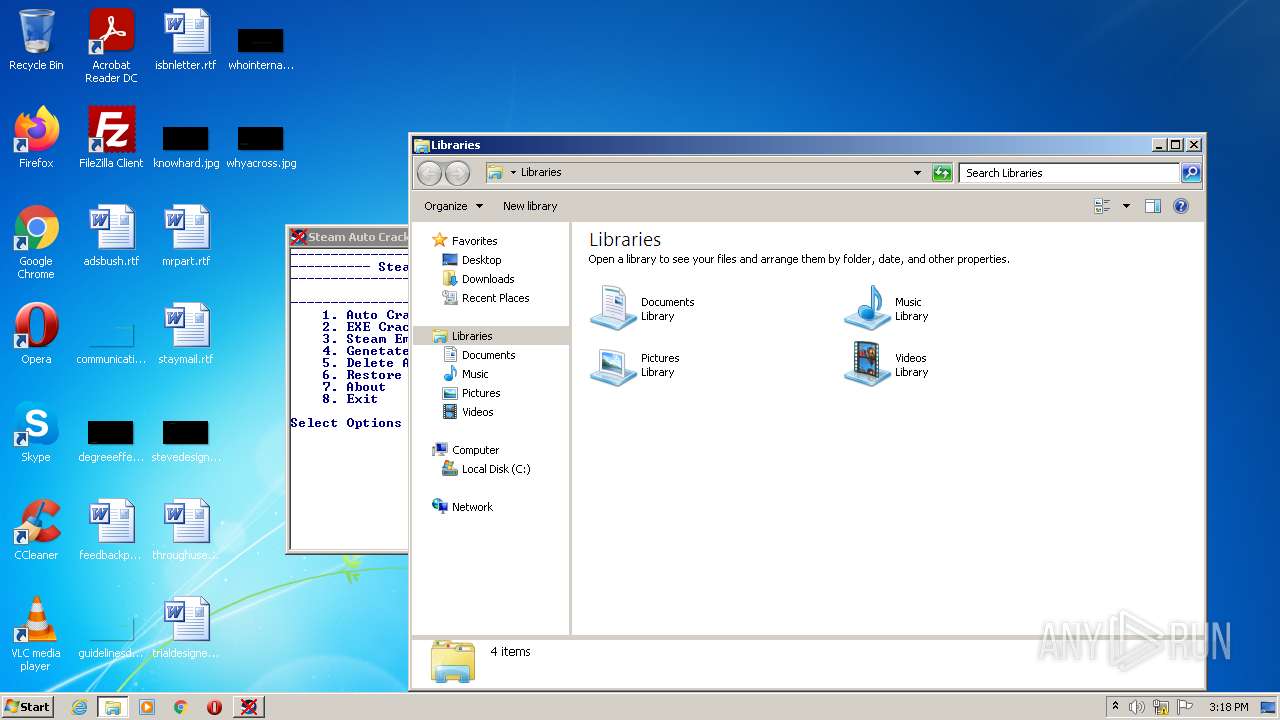
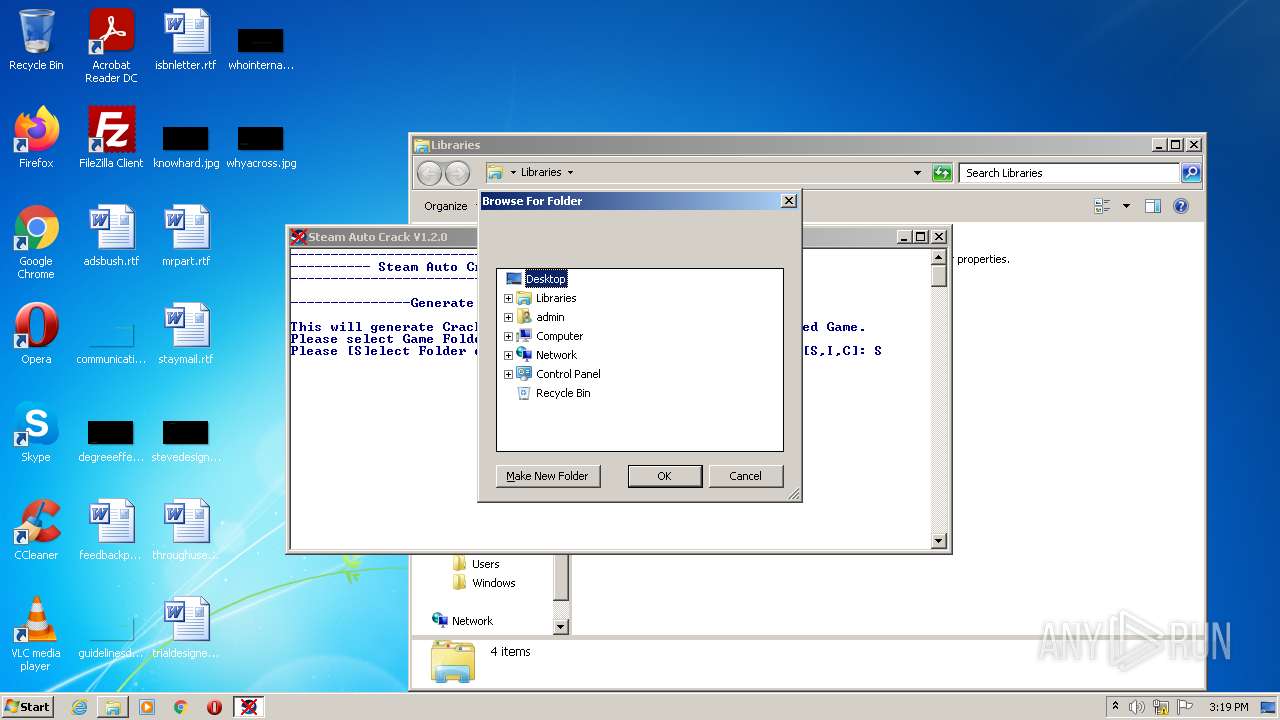
Modification events
| (PID) Process: | (3736) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3736) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-2 |
Value: Access the computers and devices that are on your network. | |||
| (PID) Process: | (3736) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (3736) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (300) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (300) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Width |
Value: 318 | |||
| (PID) Process: | (300) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | Browse For Folder Height |
Value: 288 | |||
| (PID) Process: | (3876) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3876) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000020000000D0000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3876) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\1\0\0\0\0 |
| Operation: | write | Name: | MRUListEx |
Value: 0100000000000000FFFFFFFF | |||
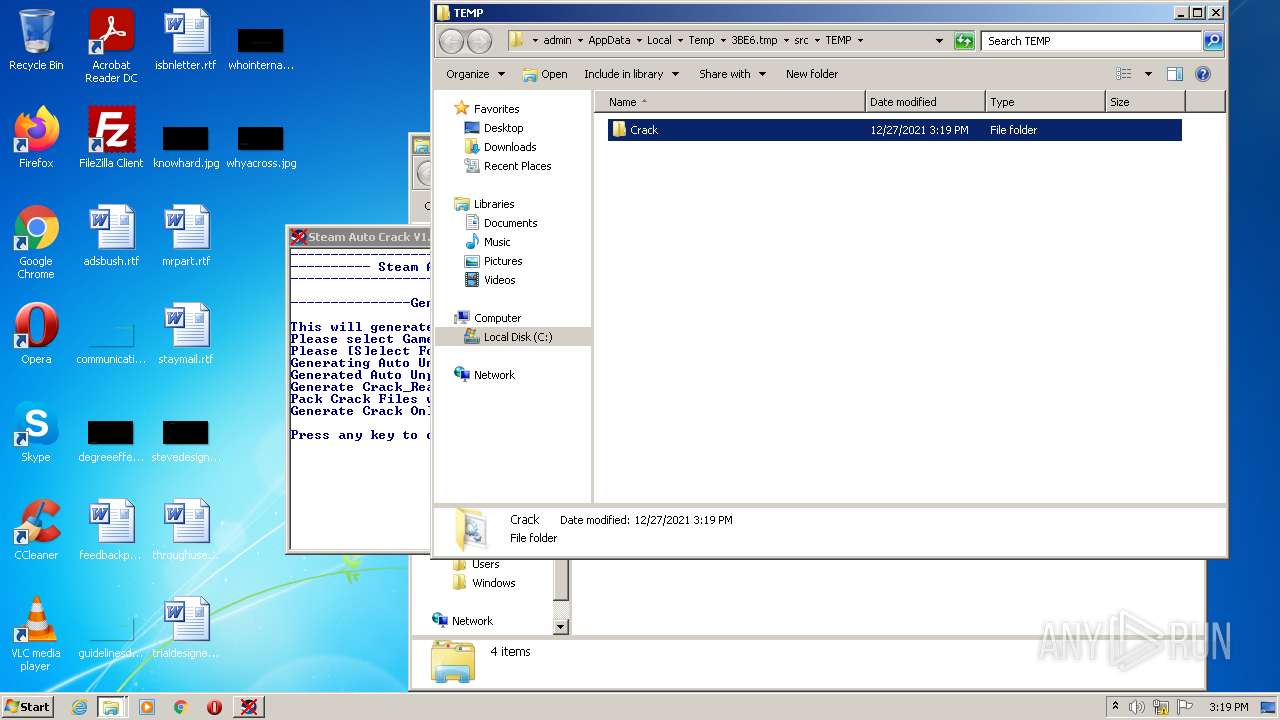
Executable files
24
Suspicious files
6
Text files
63
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3224 | SteamAutoCrack.exe | C:\Users\admin\AppData\Local\Temp\3BE6.tmp\src\bin\Apply_Crack\Apply_Crack.cmd | text | |
MD5:— | SHA256:— | |||
| 3224 | SteamAutoCrack.exe | C:\Users\admin\AppData\Local\Temp\3BE6.tmp\src\bin\7z\7za.dll | executable | |
MD5:3107CAECF7EC7A7CE12D05F9C3AB078F | SHA256:BD377BA96FF8D3CBAEA98190C8A60F32DC9D64DD44EED9AADE05D3A74D935701 | |||
| 3224 | SteamAutoCrack.exe | C:\Users\admin\AppData\Local\Temp\3BE6.tmp\src\bin\7z\7zxa.dll | executable | |
MD5:786D4C74C05832A652BE5C0A559BE1E6 | SHA256:D0680AC62E94F953DF031533ACD0ACB718AD8494F938D84198C655507709E5DF | |||
| 3224 | SteamAutoCrack.exe | C:\Users\admin\AppData\Local\Temp\3BE6.tmp\src\bin\7z\history.txt | text | |
MD5:5F52BFA6CEEF1C820F87DC3D4BEFD535 | SHA256:93C2A57A960772AD1BF4D0C85C37B1B5FD29F43A89F127F5AB958BBCBB28727F | |||
| 3224 | SteamAutoCrack.exe | C:\Users\admin\AppData\Local\Temp\3BE6.tmp\3BF7.tmp\3BF8.bat | text | |
MD5:916F473FA438385FDF60C1C4995C5276 | SHA256:F1C038862C7E8FAFE832962211C9B03C0C277385E26D37659E22AFA6F35F898F | |||
| 3224 | SteamAutoCrack.exe | C:\Users\admin\AppData\Local\Temp\3BE6.tmp\src\bin\7z\7za.exe | executable | |
MD5:43141E85E7C36E31B52B22AB94D5E574 | SHA256:EA308C76A2F927B160A143D94072B0DCE232E04B751F0C6432A94E05164E716D | |||
| 3224 | SteamAutoCrack.exe | C:\Users\admin\AppData\Local\Temp\3BE6.tmp\src\bin\Goldberg\Example\Readme.txt | text | |
MD5:— | SHA256:— | |||
| 3224 | SteamAutoCrack.exe | C:\Users\admin\AppData\Local\Temp\3BE6.tmp\src\bin\generate_game_infos\libcurl.dll | executable | |
MD5:9DE608D840E160896E9093C1A2D53C1A | SHA256:81942F619954D1AD7481D1B8CF32E110F5BD3D04286BA27A3765C59F375B2E6E | |||
| 3224 | SteamAutoCrack.exe | C:\Users\admin\AppData\Local\Temp\3BE6.tmp\src\bin\Goldberg\Example\steam_interfaces.EXAMPLE.txt | text | |
MD5:06A47A21F1AF5A7FB5A0623C5F92325D | SHA256:F32A58870B3DA4214E4D9C132783E6E8F2F277AA9025CF3211DDFEF9A3BECD5E | |||
| 3224 | SteamAutoCrack.exe | C:\Users\admin\AppData\Local\Temp\3BE6.tmp\src\bin\curl\libcurl.dll | executable | |
MD5:63B09A70418A7DD51353F738995E6C8B | SHA256:FA477933A613B03652EA2A787527486D0E9225BF1D208AE77D065E35405B4FF6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2280 | generate_game_infos.exe | 104.79.88.52:443 | store.steampowered.com | Time Warner Cable Internet LLC | US | suspicious |
2280 | generate_game_infos.exe | 51.75.195.74:443 | api.xan105.com | — | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
store.steampowered.com |
| whitelisted |
api.xan105.com |
| unknown |