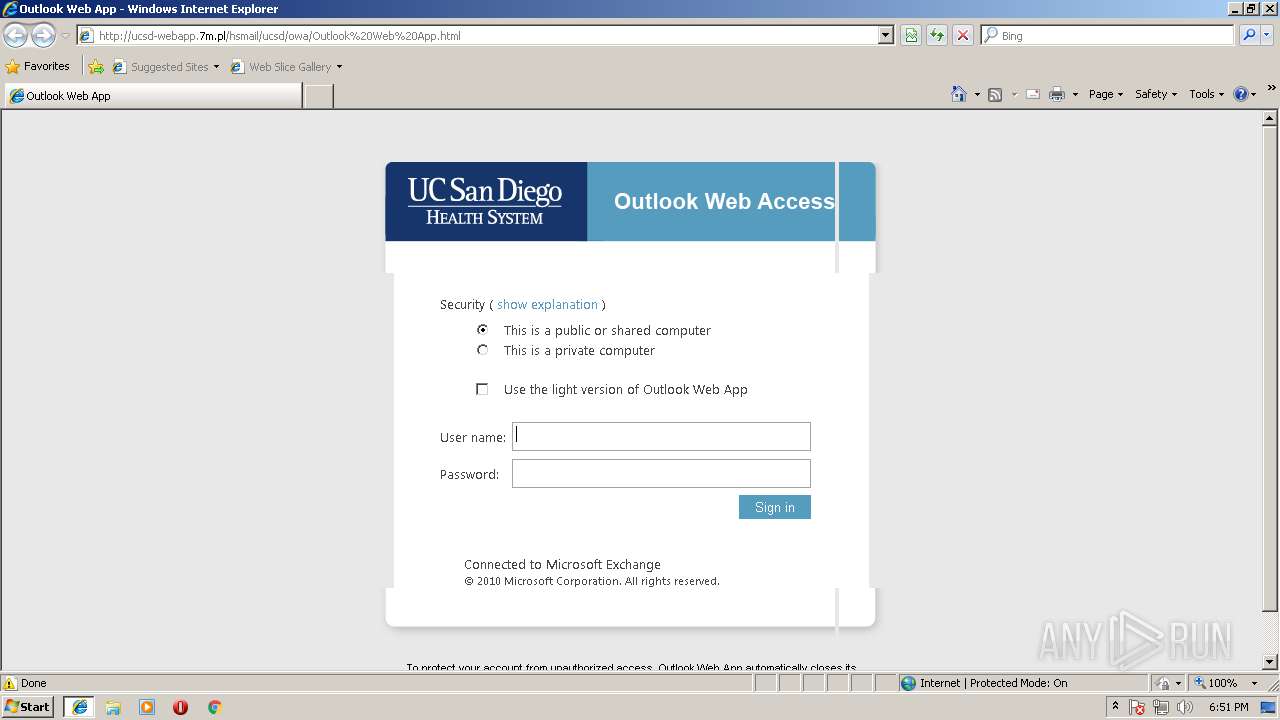
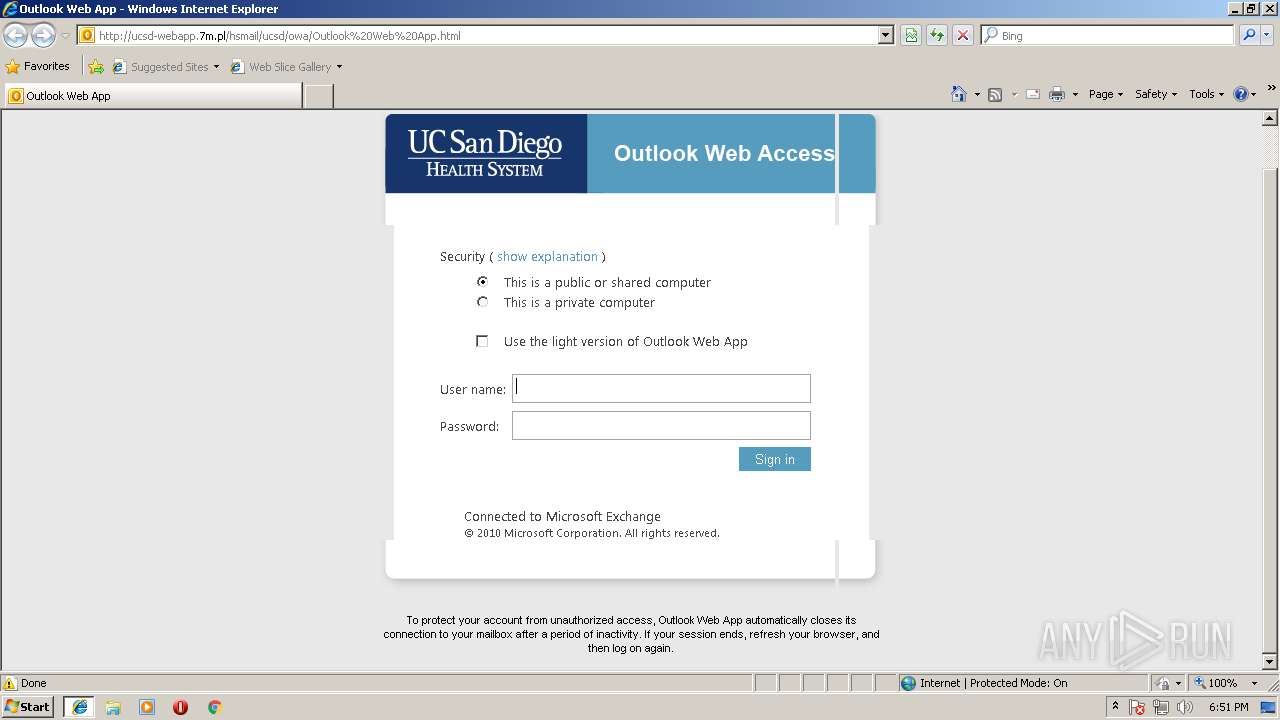
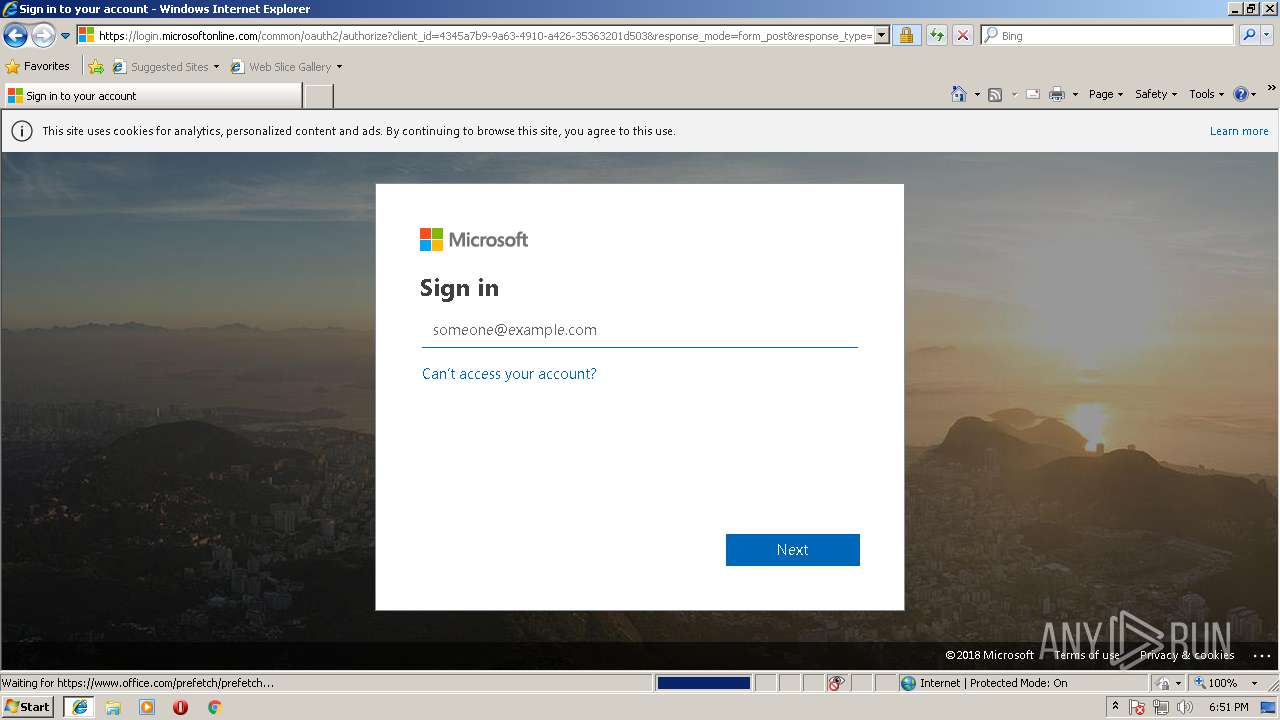
| URL: | http://ucsd-webapp.7m.pl/hsmail/ucsd/owa/Outlook%20Web%20App.html |
| Full analysis: | https://app.any.run/tasks/cc229a8b-d278-4434-99ec-9e66b166b744 |
| Verdict: | Malicious activity |
| Analysis date: | September 07, 2018, 17:50:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E94A6D5A95AD20EF9865F895398D72B1 |
| SHA1: | 46426E2F908DA02B7F0E7735218F7E39A988E626 |
| SHA256: | 0B5A742FDF7522ABA019CED4ABB14B3CA0F11D2AFEE696D61E1E608F092ECFF5 |
| SSDEEP: | 3:N1KL4QDiW5IL3RByOA9gX6V5uJn:CMYHOA9ZVwJn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2172)
Changes internet zones settings
- iexplore.exe (PID: 2120)
Changes settings of System certificates
- iexplore.exe (PID: 2120)
Reads settings of System Certificates
- iexplore.exe (PID: 2172)
Reads internet explorer settings
- iexplore.exe (PID: 2172)
Creates files in the user directory
- iexplore.exe (PID: 2172)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | "C:\Program Files\Internet Explorer\iexplore.exe" http://ucsd-webapp.7m.pl/hsmail/ucsd/owa/Outlook%20Web%20App.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2120 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
505
Read events
416
Write events
84
Delete events
5
Modification events
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000048000000010000000000000000000000000000000000000000000000B096B68868EBD301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000D8BFD602040000000000000000000000000000000000000000000000F4BFD602040000000000000000000000000000000000000000000000D8372A0000000000FFFFFFFF000000000000000000000000010000002E00000000000000000000000000000002000000C0A801640000000000000000D84ED505AC02000005000000010000000000000000000000010000000000000000000000BF060000000000000000000000000000000000001000000088C0D60204000000000000000000000000000000000000000000000000000000C8E40C00000000000C0000000000000000000000 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {900F7B07-B2C6-11E8-ACE5-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 10 | |||
| (PID) Process: | (2120) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207090005000700110032003500CF02 | |||
Executable files
0
Suspicious files
5
Text files
37
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2120 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2120 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2172 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DSILEDM7\logon[1].css | text | |
MD5:— | SHA256:— | |||
| 2172 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MJG226QK\f[1].txt | text | |
MD5:— | SHA256:— | |||
| 2172 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2172 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2091.tmp | — | |
MD5:— | SHA256:— | |||
| 2172 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2092.tmp | — | |
MD5:— | SHA256:— | |||
| 2172 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab20A3.tmp | — | |
MD5:— | SHA256:— | |||
| 2172 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar20A4.tmp | — | |
MD5:— | SHA256:— | |||
| 2172 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\4935IXA8\ucsd-webapp.7m[1].xml | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
29
DNS requests
18
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2172 | iexplore.exe | GET | — | 88.99.33.244:80 | http://ucsd-webapp.7m.pl/hsmail/ucsd/owa/Outlook%20Web%20App_files/logon.css | DE | — | — | malicious |
2172 | iexplore.exe | GET | 200 | 88.99.33.244:80 | http://ucsd-webapp.7m.pl/hsmail/ucsd/owa/Outlook%20Web%20App_files/logon.css | DE | text | 2.77 Kb | malicious |
2172 | iexplore.exe | GET | 200 | 88.99.33.244:80 | http://ucsd-webapp.7m.pl/hsmail/ucsd/owa/Outlook%20Web%20App_files/lgntopl.gif | DE | image | 5.62 Kb | malicious |
2172 | iexplore.exe | GET | 200 | 88.99.33.244:80 | http://ucsd-webapp.7m.pl/hsmail/ucsd/owa/Outlook%20Web%20App_files/flogon.js.download | DE | text | 3.92 Kb | malicious |
2172 | iexplore.exe | GET | 200 | 88.99.33.244:80 | http://ucsd-webapp.7m.pl/hsmail/ucsd/owa/Outlook%20Web%20App_files/lgnbotl.gif | DE | image | 2.25 Kb | malicious |
2172 | iexplore.exe | GET | 200 | 88.99.33.244:80 | http://ucsd-webapp.7m.pl/hsmail/ucsd/owa/Outlook%20Web%20App_files/lgntopr.gif | DE | image | 2.34 Kb | malicious |
— | — | GET | 200 | 216.58.211.98:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 26.6 Kb | whitelisted |
2172 | iexplore.exe | GET | 200 | 88.99.33.244:80 | http://7m.pl/robot.js | DE | text | 28.5 Kb | whitelisted |
2172 | iexplore.exe | GET | 200 | 88.99.33.244:80 | http://ucsd-webapp.7m.pl/hsmail/ucsd/owa/Outlook%20Web%20App_files/lgnbotr.gif | DE | image | 1.77 Kb | malicious |
2120 | iexplore.exe | GET | 200 | 104.17.102.175:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | US | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2172 | iexplore.exe | 88.99.33.244:80 | ucsd-webapp.7m.pl | Hetzner Online GmbH | DE | malicious |
2120 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 216.58.211.98:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2172 | iexplore.exe | 172.217.17.34:443 | adservice.google.com | Google Inc. | US | whitelisted |
2172 | iexplore.exe | 216.58.212.162:443 | adservice.google.fr | Google Inc. | US | whitelisted |
2120 | iexplore.exe | 132.239.82.186:443 | hsmail.ucsd.edu | University of California, San Diego | US | unknown |
2120 | iexplore.exe | 104.17.102.175:80 | crt.usertrust.com | Cloudflare Inc | US | shared |
2172 | iexplore.exe | 104.40.240.52:443 | login.microsoftonline.com | Microsoft Corporation | NL | whitelisted |
2120 | iexplore.exe | 2.20.23.219:443 | secure.aadcdn.microsoftonline-p.com | Akamai International B.V. | — | whitelisted |
2172 | iexplore.exe | 52.97.131.178:443 | outlook.office365.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ucsd-webapp.7m.pl |
| malicious |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
adservice.google.fr |
| whitelisted |
adservice.google.com |
| whitelisted |
7m.pl |
| whitelisted |
hsmail.ucsd.edu |
| unknown |
crt.usertrust.com |
| whitelisted |
www.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | iexplore.exe | Potentially Bad Traffic | ET INFO Possible Phish - Saved Website Comment Observed |
2172 | iexplore.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible OWA Mail Phishing Landing - Title over non SSL |
2172 | iexplore.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Likely Cloned .EDU Website Phishing Landing 2018-02-02 |
2172 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible Successful Generic Phish Jan 14 2016 |
2 ETPRO signatures available at the full report