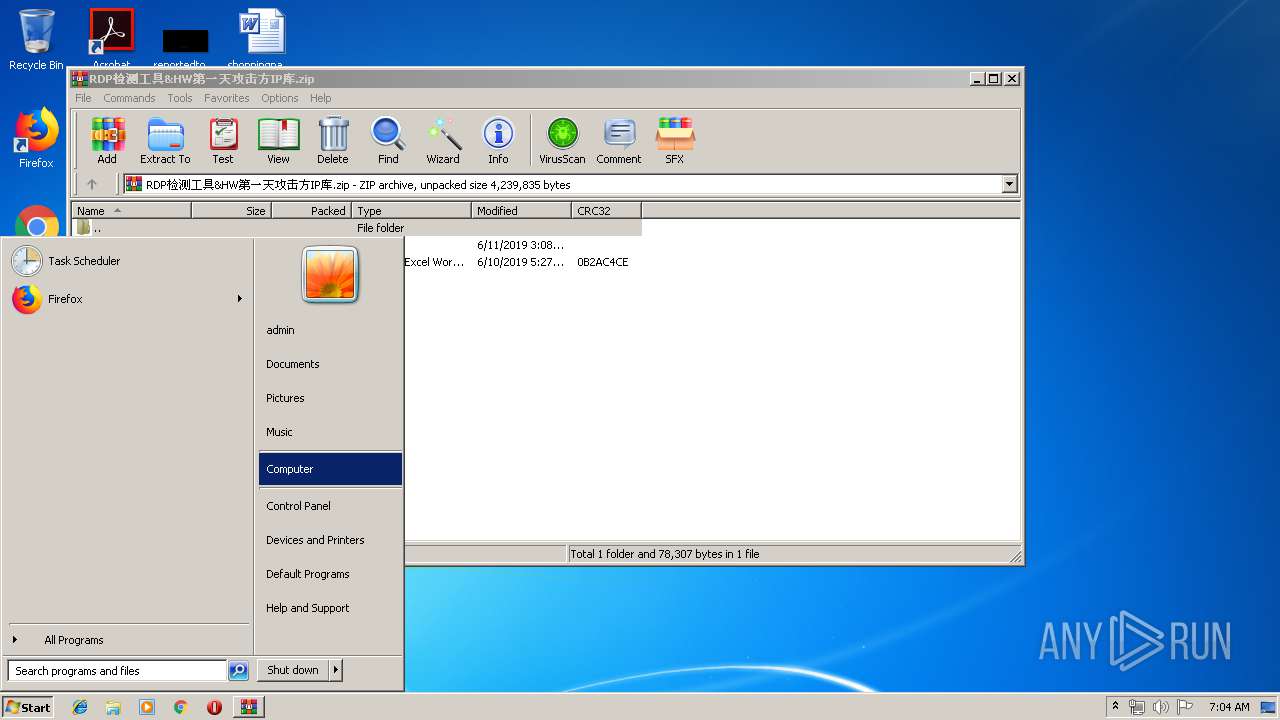
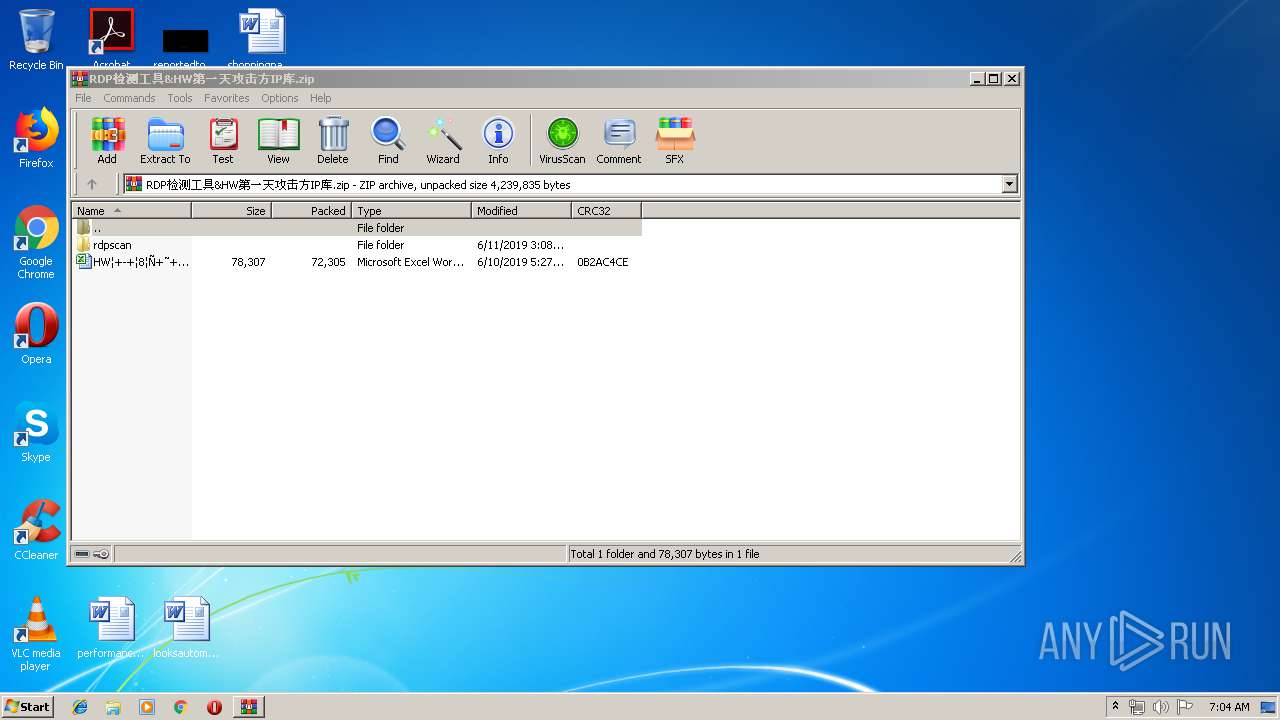
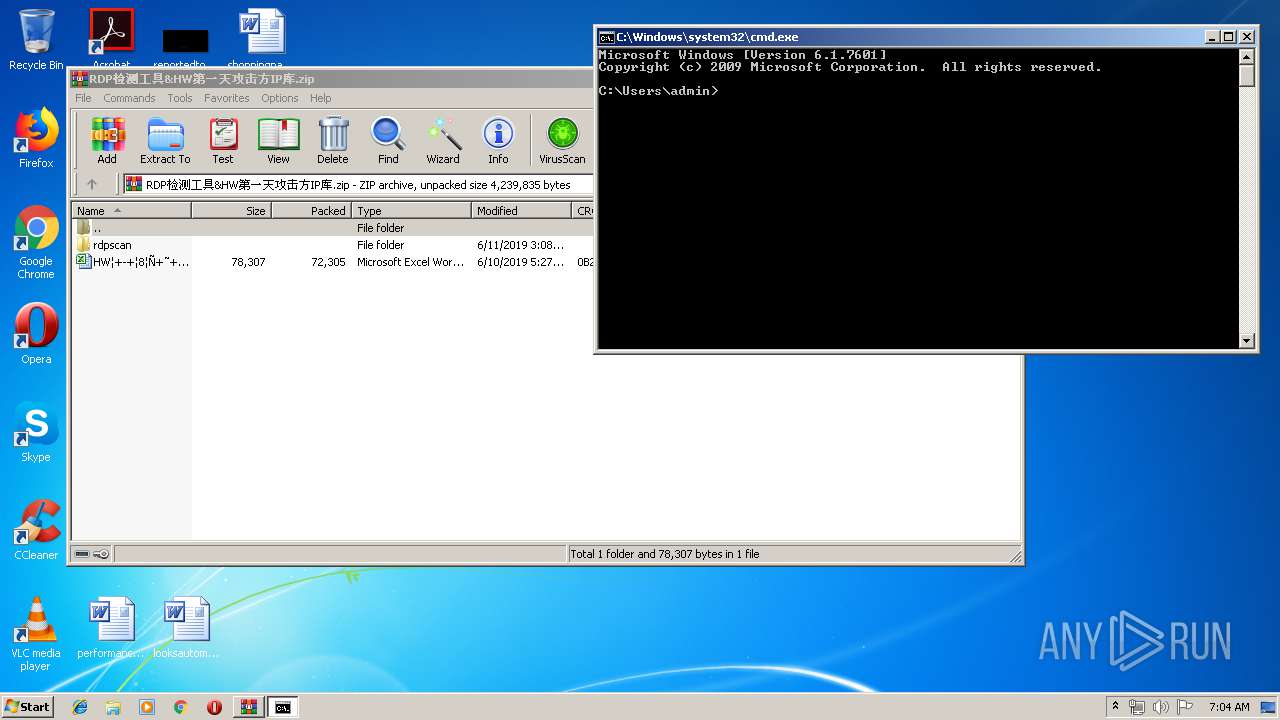
| File name: | RDP检测工具&HW第一天攻击方IP库.zip |
| Full analysis: | https://app.any.run/tasks/de003609-9c7f-4078-a914-25ca453d58b9 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 06:04:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 77E929095D57C044F18AB259023C9EA5 |
| SHA1: | 8A81D022E895EF6F3FC5C1DFD31F2E2BA142DE23 |
| SHA256: | 0B5A6F745A47E2CB83C167E1F53F92DB38F21E07A73F8600FC58DBC73CD927A7 |
| SSDEEP: | 24576:LUZ0zcmAg0BGsBjLIOqOywjYZY5JjzReZQIgJMths3m1gp7wsWx6YSkHwrBg+kNF:LzUS0Llhdz34Zbz88TSkHwrBgfXxlD |
MALICIOUS
Runs app for hidden code execution
- explorer.exe (PID: 2044)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2920)
- rdpscan.exe (PID: 2452)
- explorer.exe (PID: 2044)
- rdpscan.exe (PID: 1920)
Application was dropped or rewritten from another process
- rdpscan.exe (PID: 2452)
- rdpscan.exe (PID: 1920)
- rdpscan.exe (PID: 2036)
SUSPICIOUS
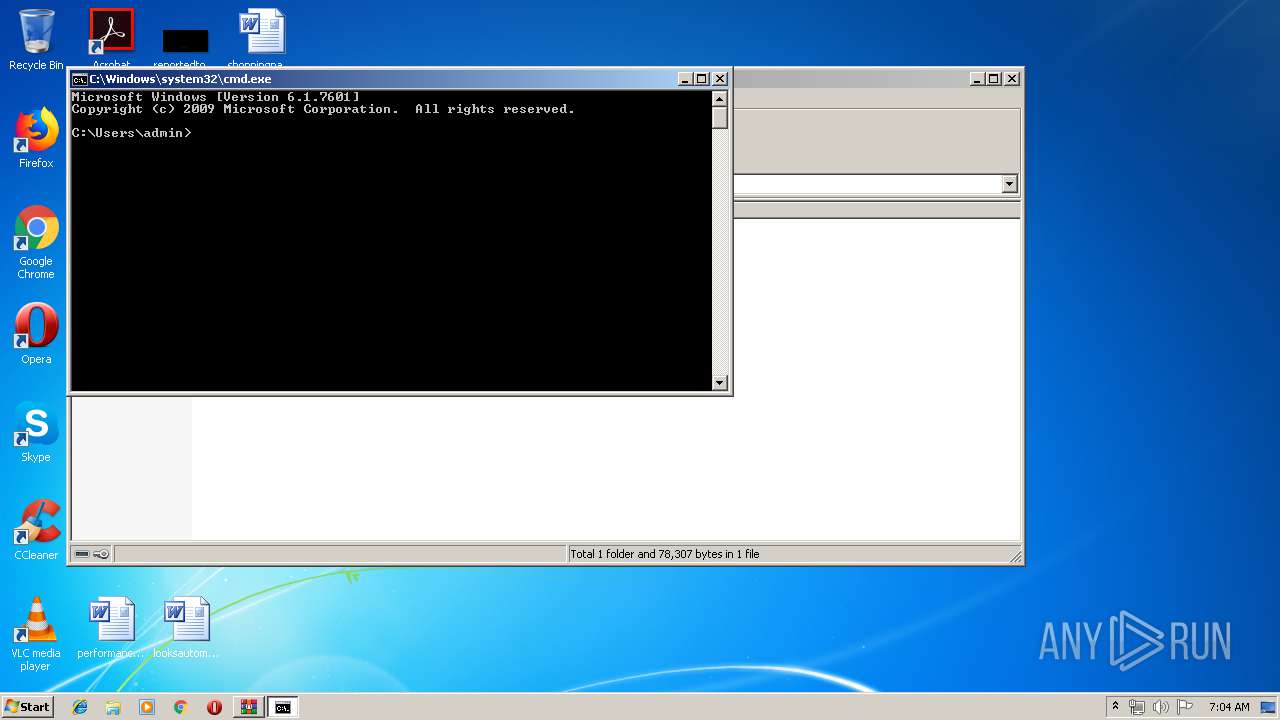
Starts CMD.EXE for commands execution
- explorer.exe (PID: 2044)
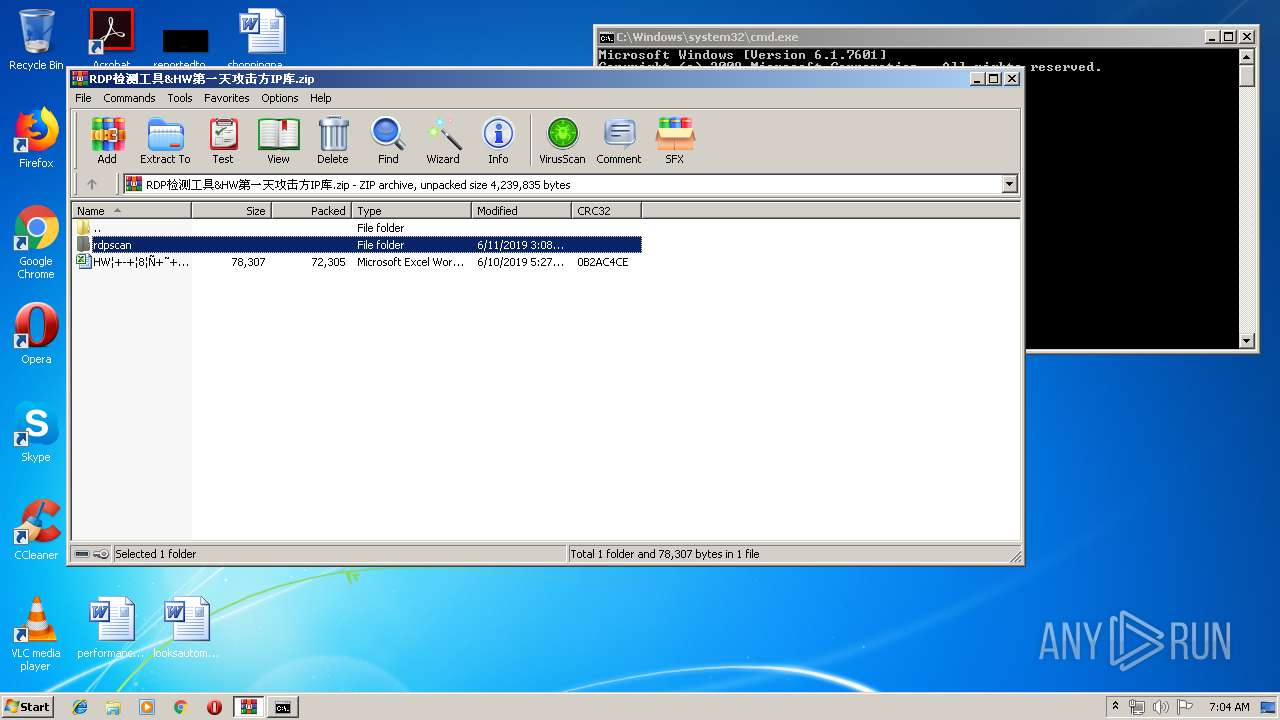
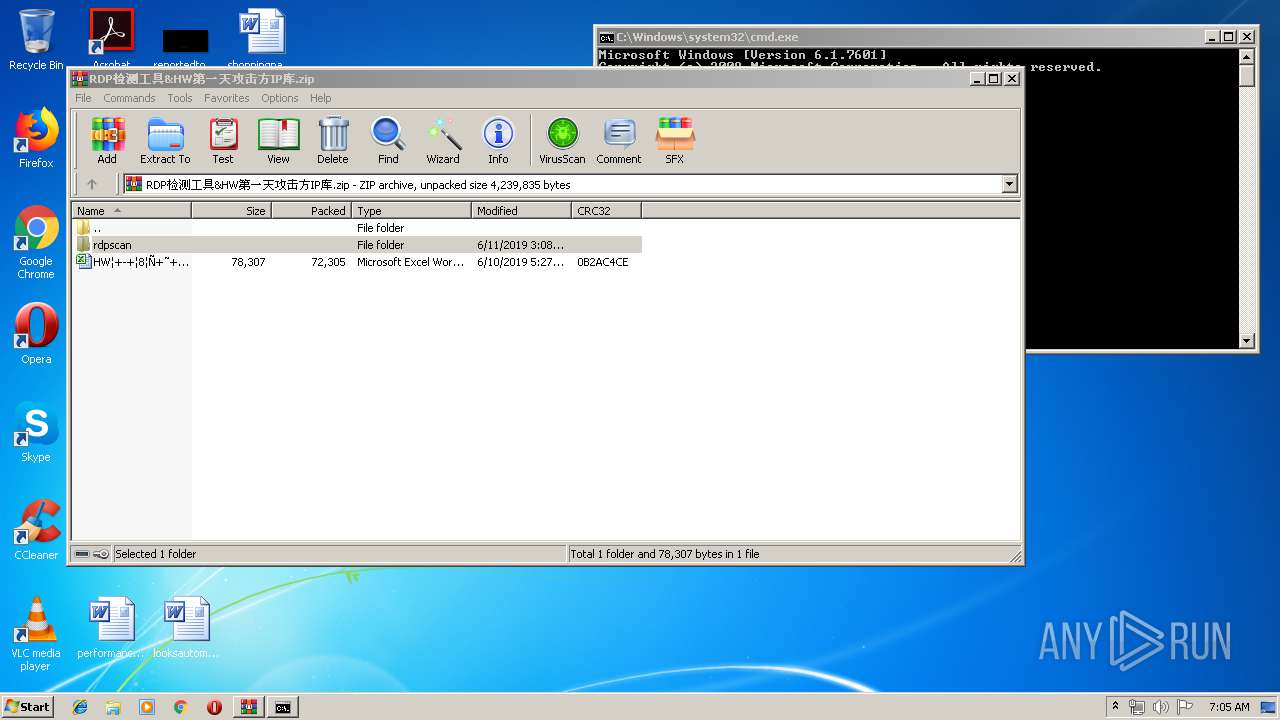
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3984)
INFO
Manual execution by user
- cmd.exe (PID: 1224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
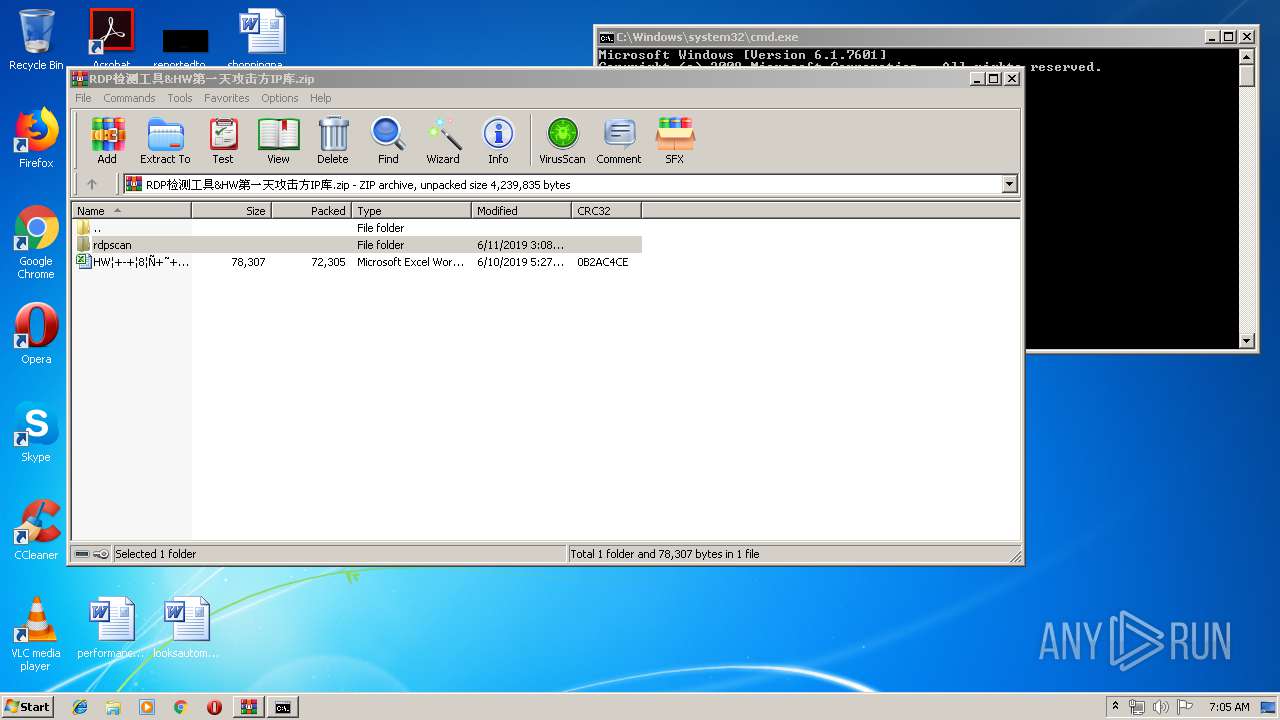
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:06:11 00:27:26 |
| ZipCRC: | 0x0b2ac4ce |
| ZipCompressedSize: | 72305 |
| ZipUncompressedSize: | 78307 |
| ZipFileName: | HW??һ?칥????IP??.xlsx |
Total processes
39
Monitored processes
7
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
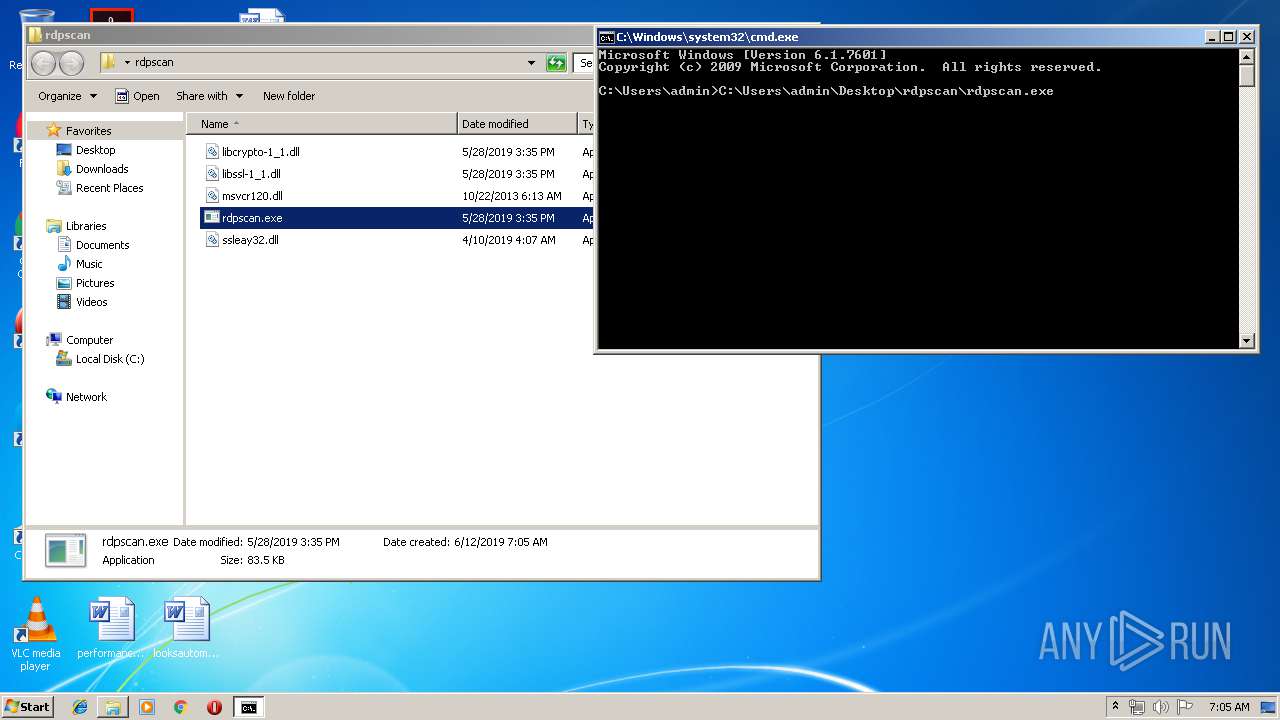
| 1224 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
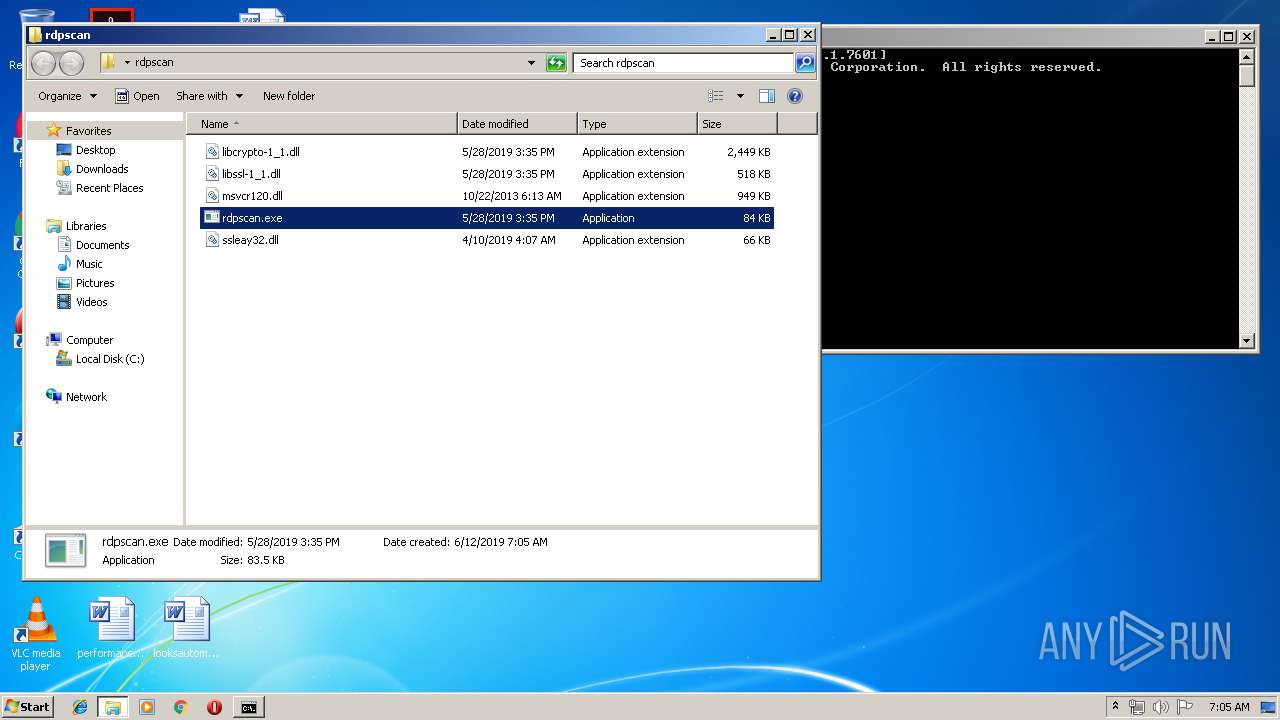
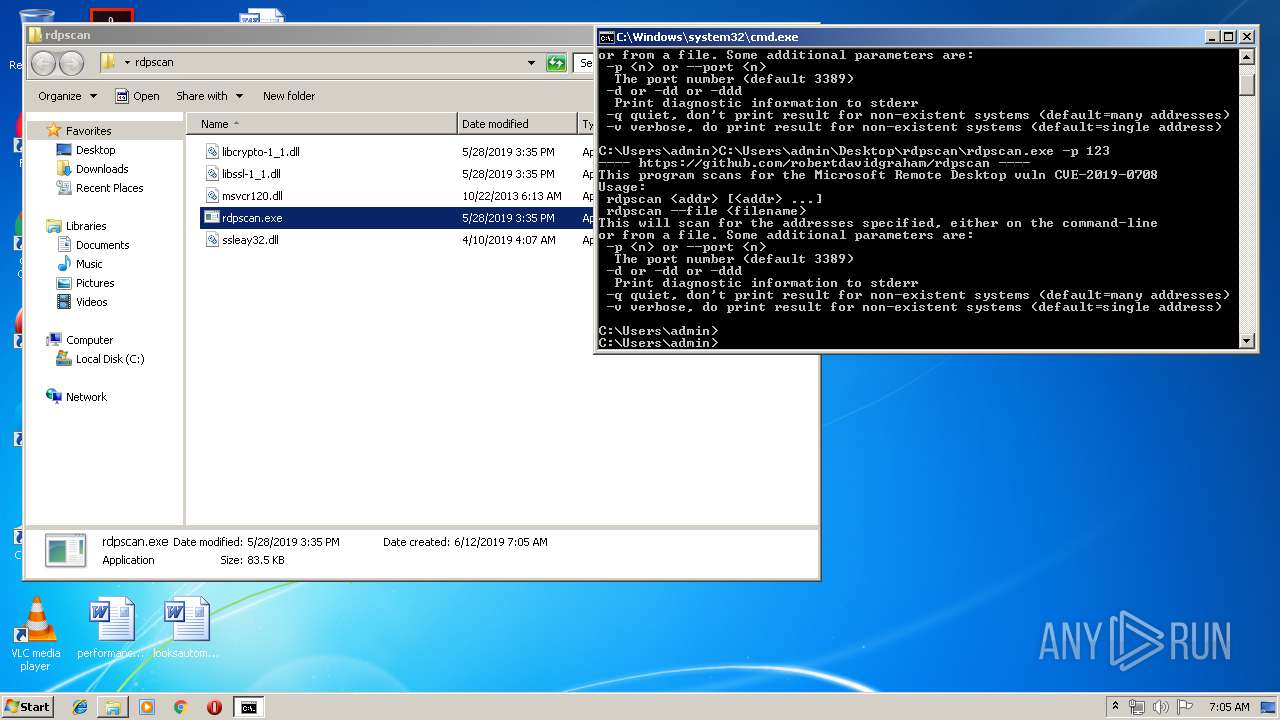
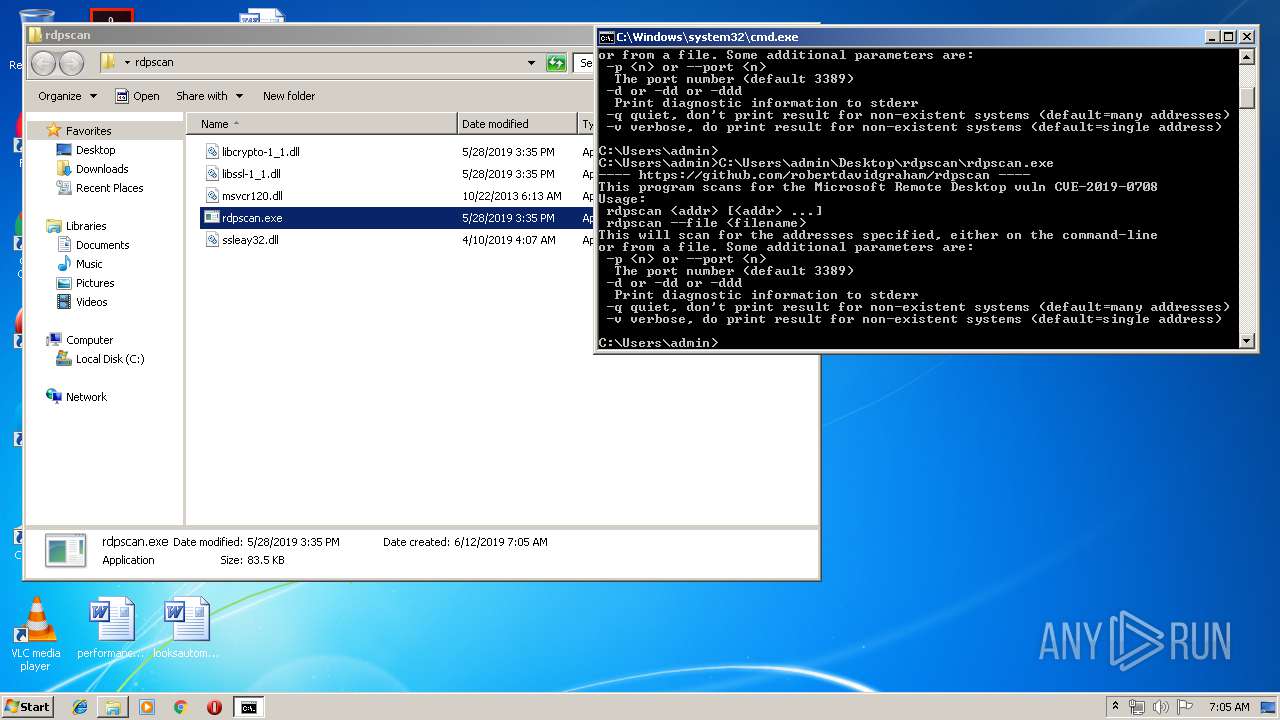
| 1920 | C:\Users\admin\Desktop\rdpscan\rdpscan.exe -p 123 | C:\Users\admin\Desktop\rdpscan\rdpscan.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2036 | C:\Users\admin\Desktop\rdpscan\rdpscan.exe | C:\Users\admin\Desktop\rdpscan\rdpscan.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2044 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2452 | C:\Users\admin\Desktop\rdpscan\rdpscan.exe | C:\Users\admin\Desktop\rdpscan\rdpscan.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2920 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
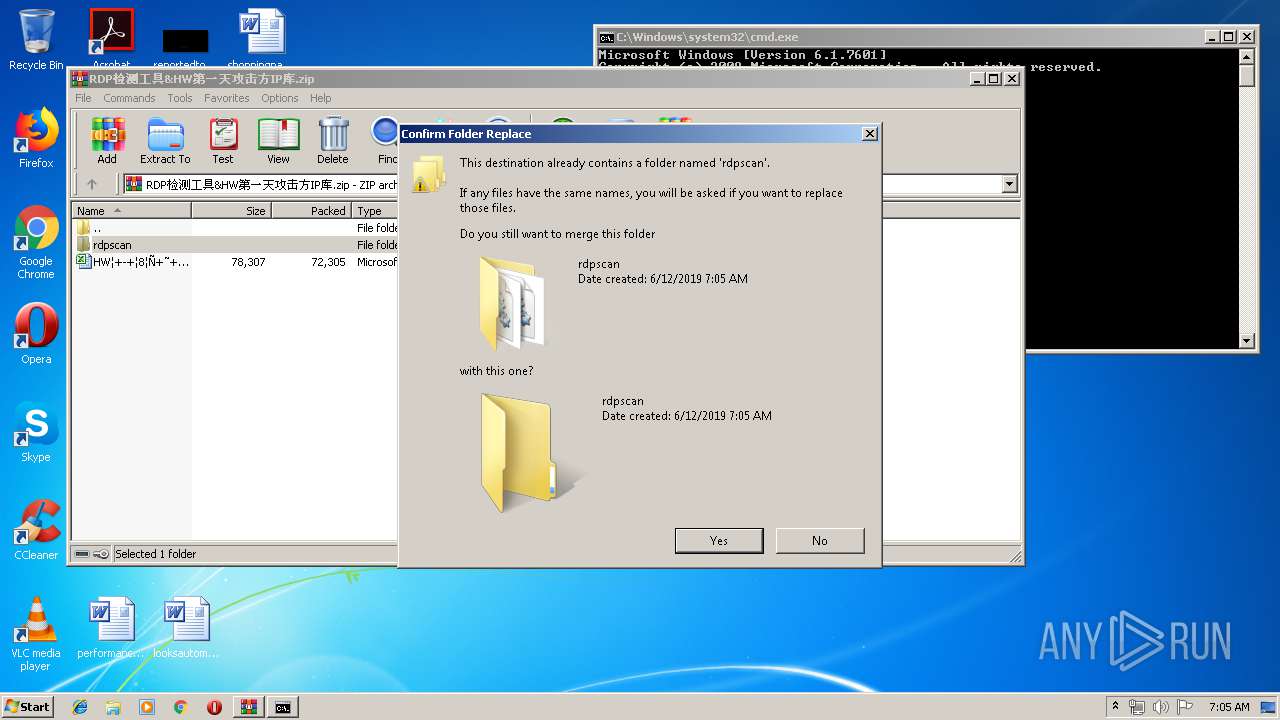
| 3984 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\RDP检测工具&HW第一天攻击方IP库.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 207
Read events
1 931
Write events
276
Delete events
0
Modification events
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\RDP检测工具&HW第一天攻击方IP库.zip | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3984) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (2044) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
4
Suspicious files
1
Text files
0
Unknown types
0
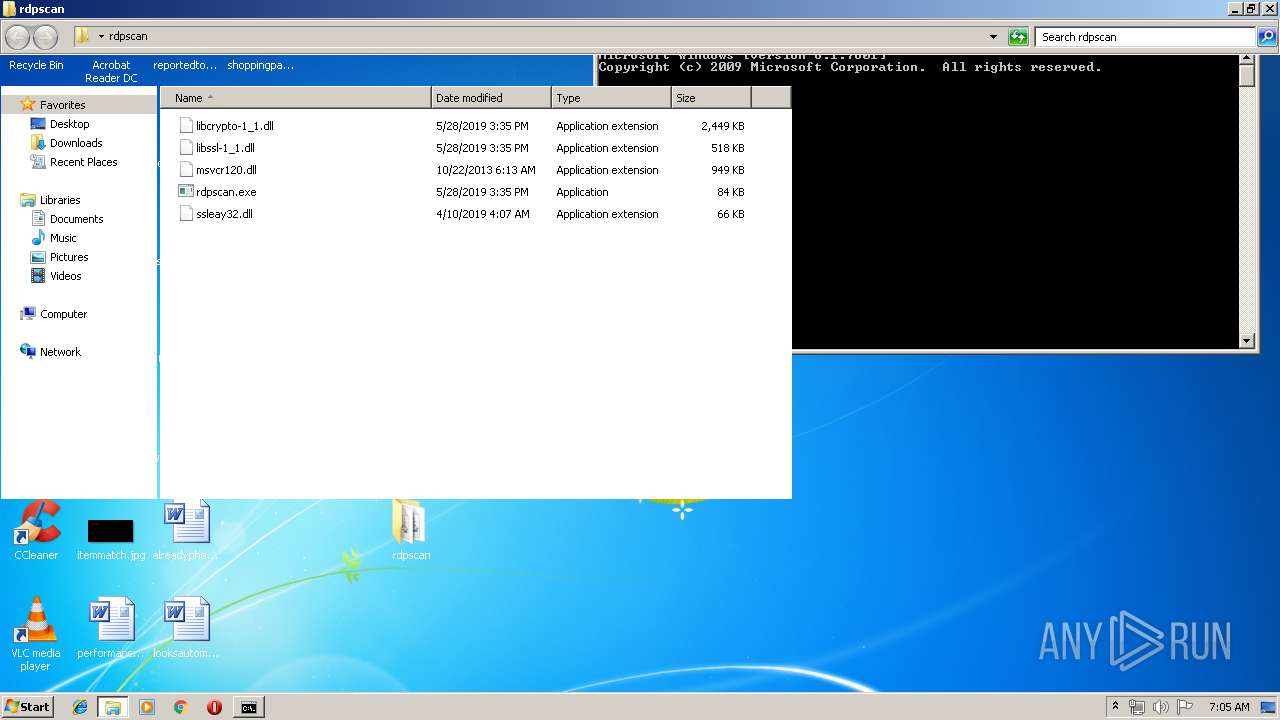
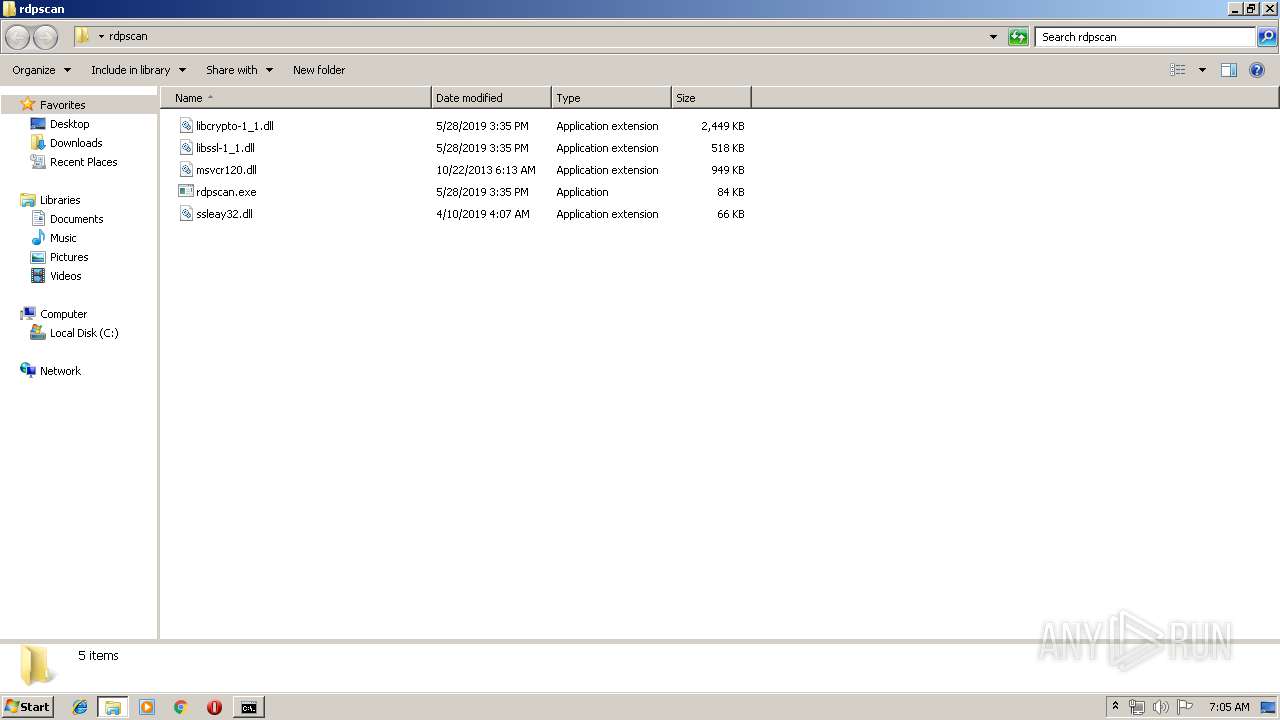
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3984.245\rdpscan\libcrypto-1_1.dll | — | |
MD5:— | SHA256:— | |||
| 3984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3984.245\rdpscan\libssl-1_1.dll | — | |
MD5:— | SHA256:— | |||
| 3984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3984.245\rdpscan\msvcr120.dll | — | |
MD5:— | SHA256:— | |||
| 3984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3984.245\rdpscan\rdpscan.exe | — | |
MD5:— | SHA256:— | |||
| 3984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3984.245\rdpscan\ssleay32.dll | — | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\Desktop\rdpscan | — | |
MD5:— | SHA256:— | |||
| 3984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3984.1267\rdpscan\ssleay32.dll | binary | |
MD5:— | SHA256:— | |||
| 3984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3984.1267\rdpscan\rdpscan.exe | executable | |
MD5:— | SHA256:— | |||
| 3984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3984.1267\rdpscan\libssl-1_1.dll | executable | |
MD5:0BC4DF79B2752DD03C2E04C0D3F4AEA1 | SHA256:71B19452B5FD7A389CDE0C588B21F3F03EE443F57A1E42A7670671988BE908CF | |||
| 3984 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3984.1267\rdpscan\msvcr120.dll | executable | |
MD5:034CCADC1C073E4216E9466B720F9849 | SHA256:86E39B5995AF0E042FCDAA85FE2AEFD7C9DDC7AD65E6327BD5E7058BC3AB615F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report