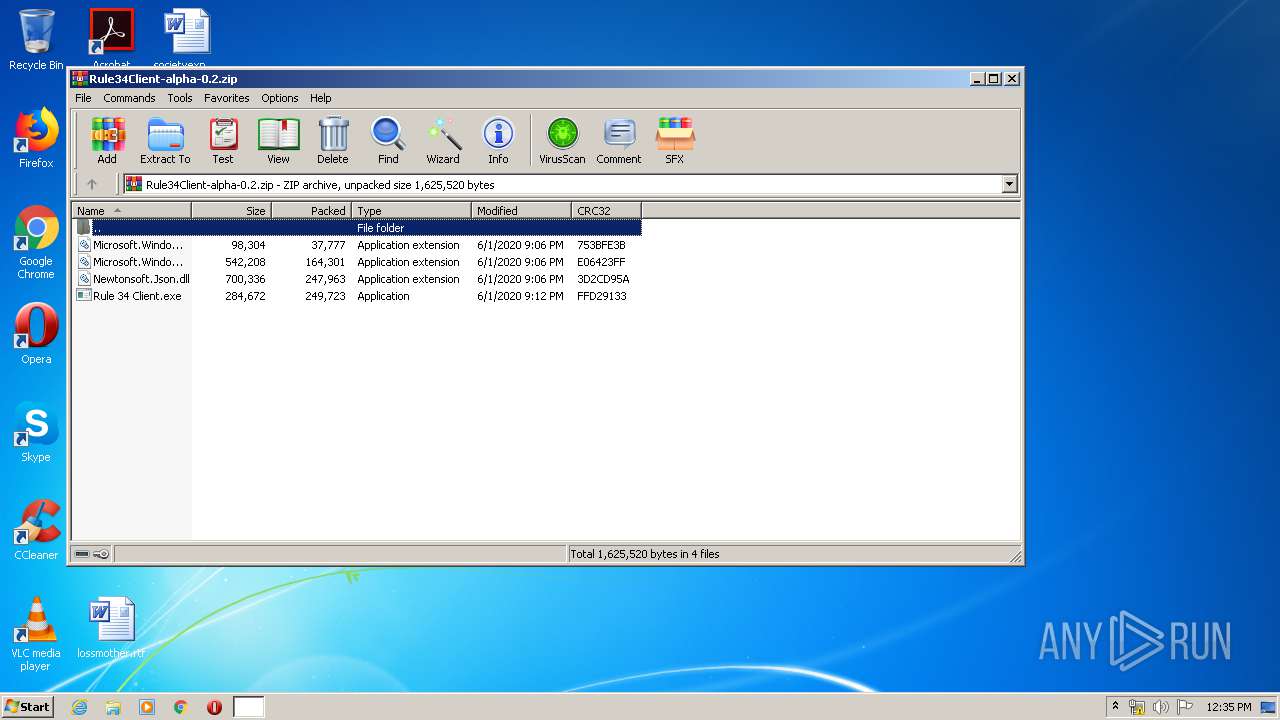
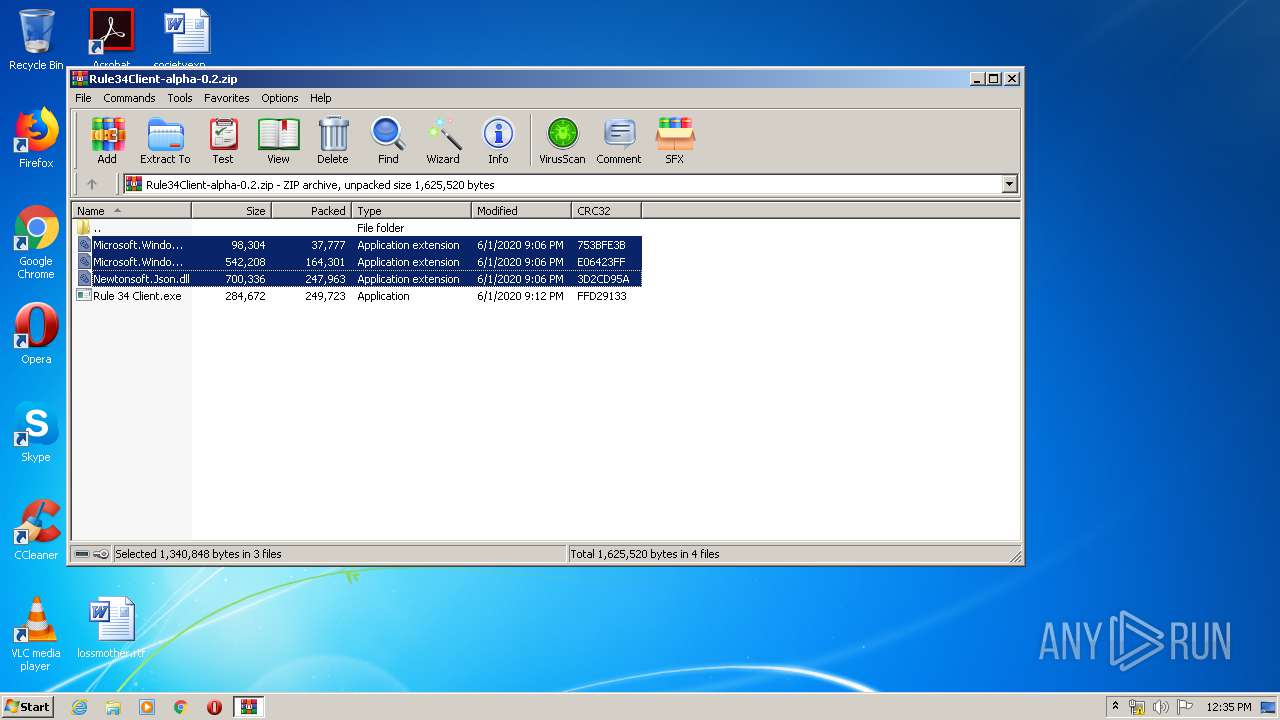
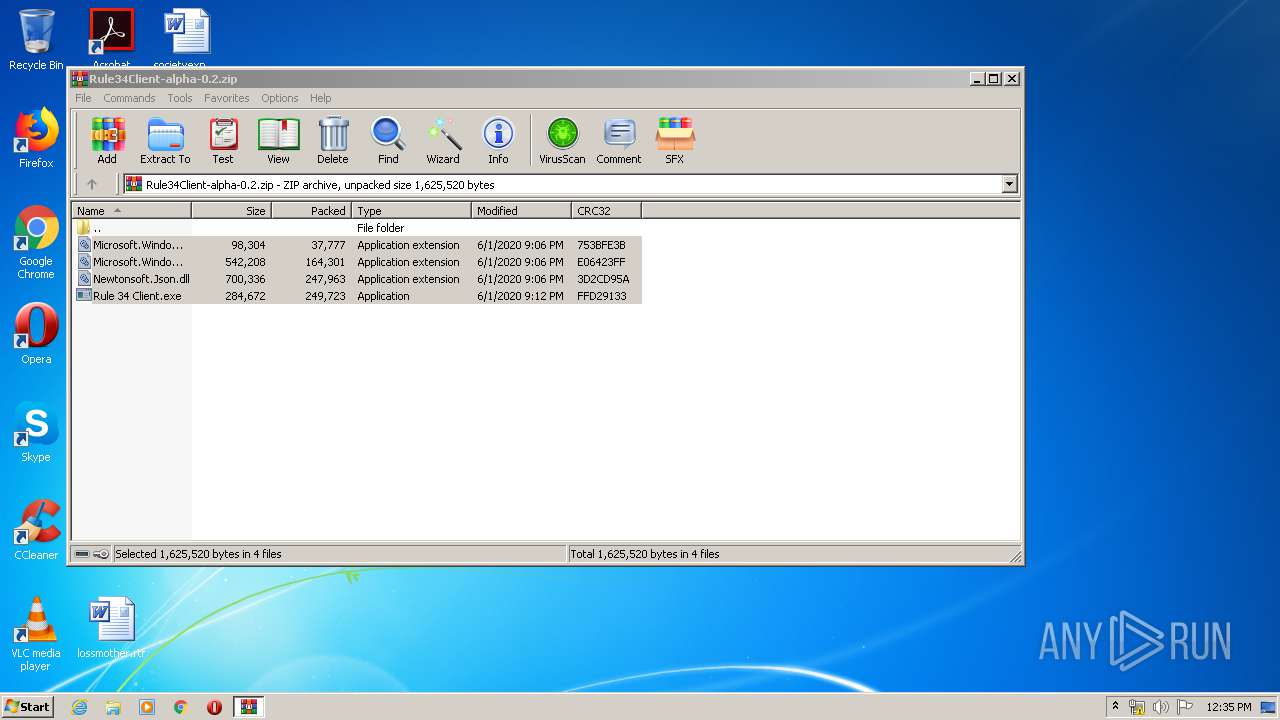
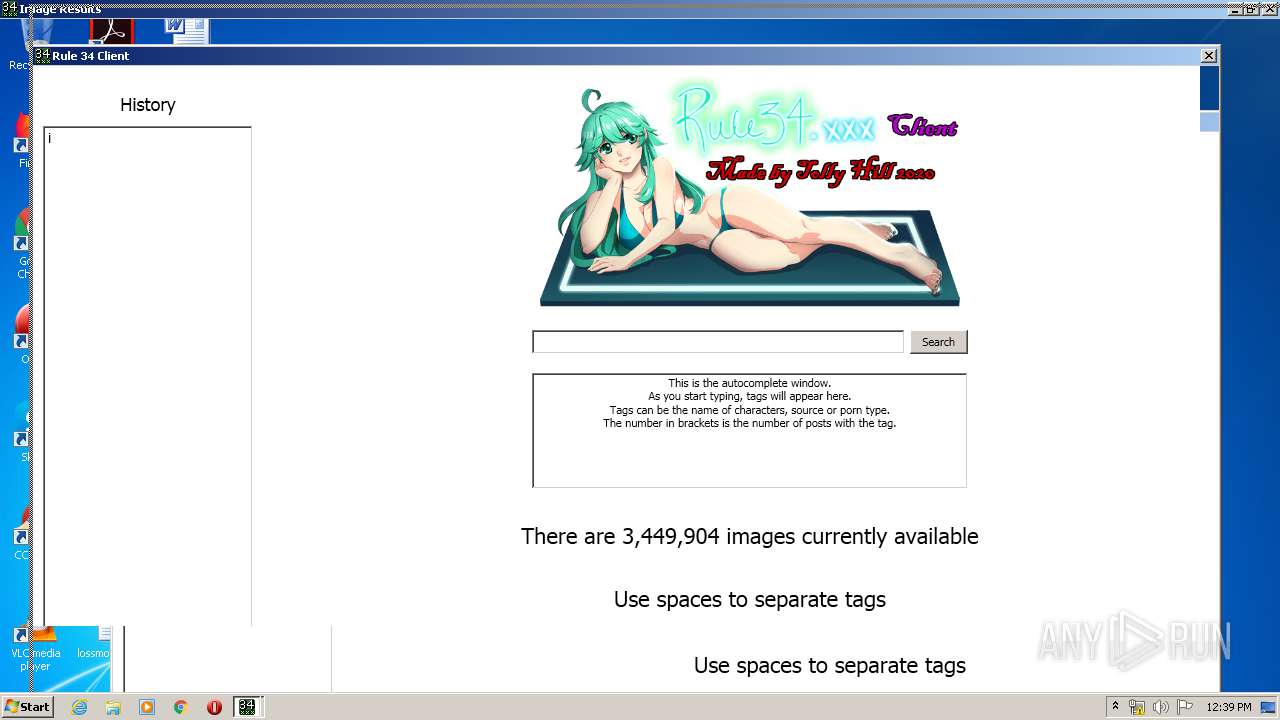
| File name: | Rule34Client-alpha-0.2.zip |
| Full analysis: | https://app.any.run/tasks/b6a7785a-2575-456d-b9f1-00b3082b9b4b |
| Verdict: | Malicious activity |
| Analysis date: | June 02, 2020, 11:35:32 |
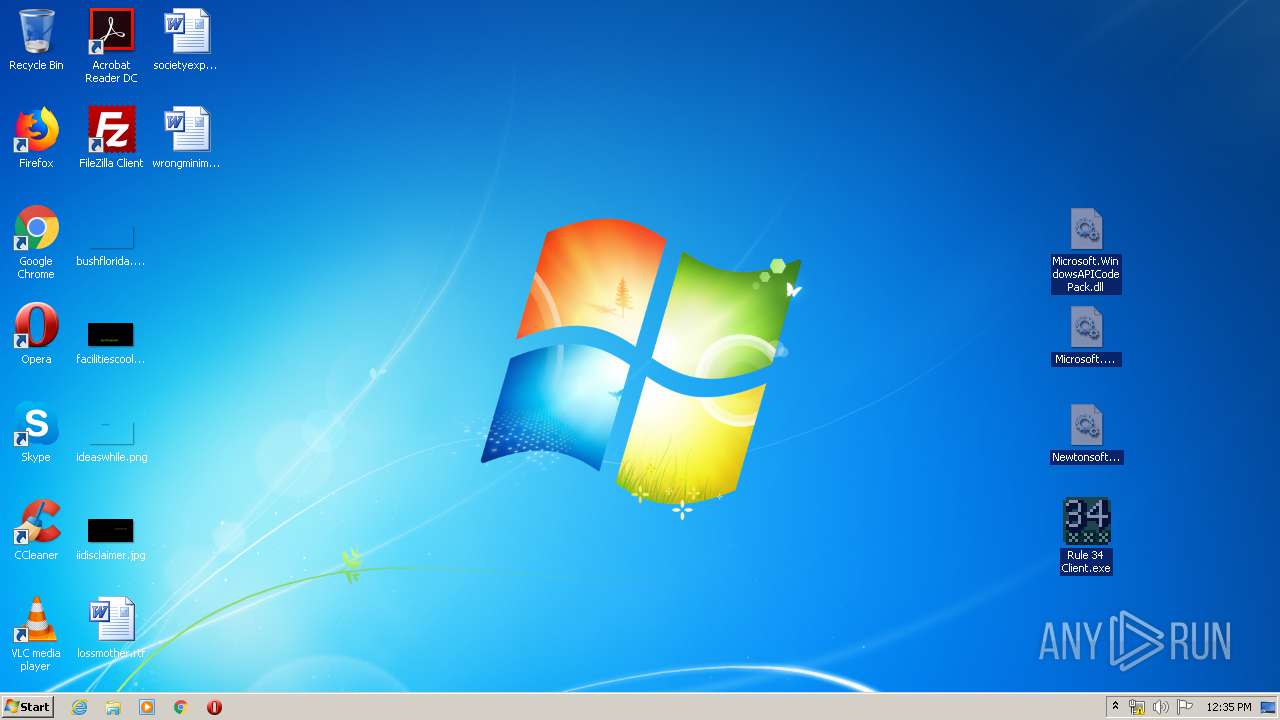
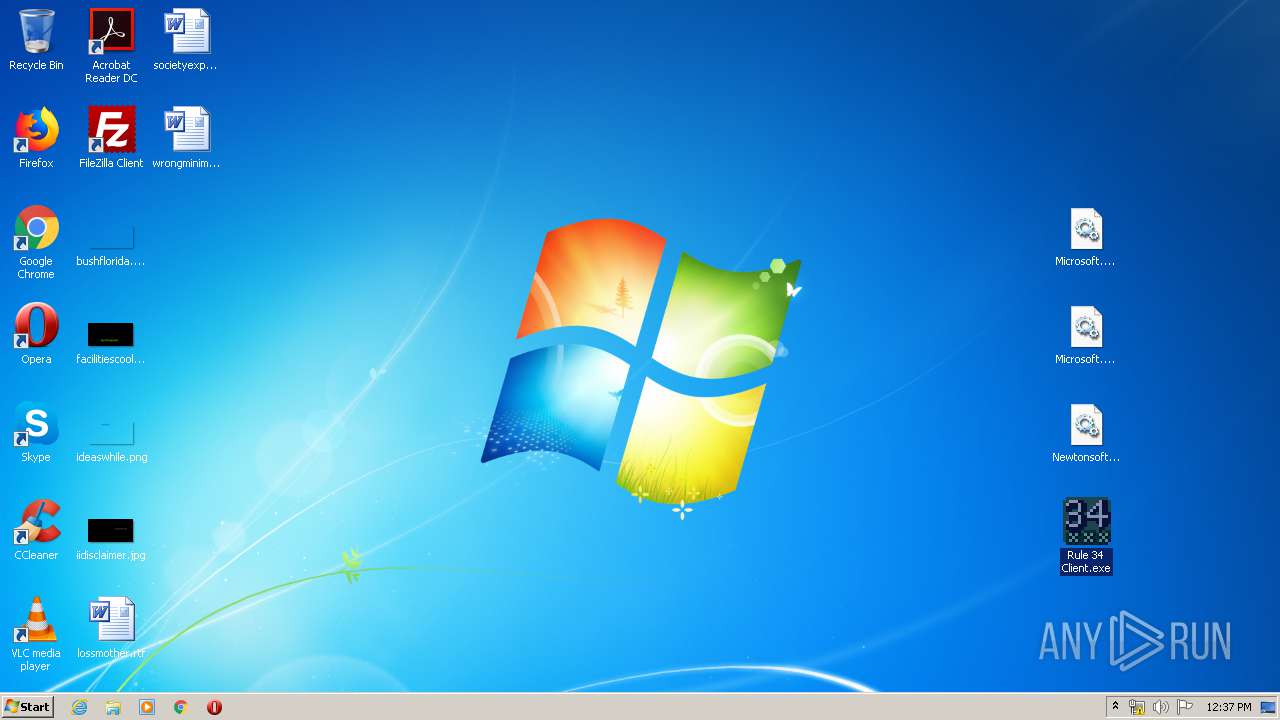
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 40D1E190CDDDEC1B70B312DE776342C4 |
| SHA1: | B0C504C71F1C658F196571FD83D71BD19AF5484D |
| SHA256: | 0B58AEB48DBDFFCDF80D895B2358E72BB3DE2BF133A34164EE802592E2C9ECAE |
| SSDEEP: | 12288:7wv1mOIORDsormJd2M3wHwGEioXLvzp6SQIsQEI3zEFb680gS8n/5ysOq:7e11JI1JdjywGnoXXp6C3gU87ik |
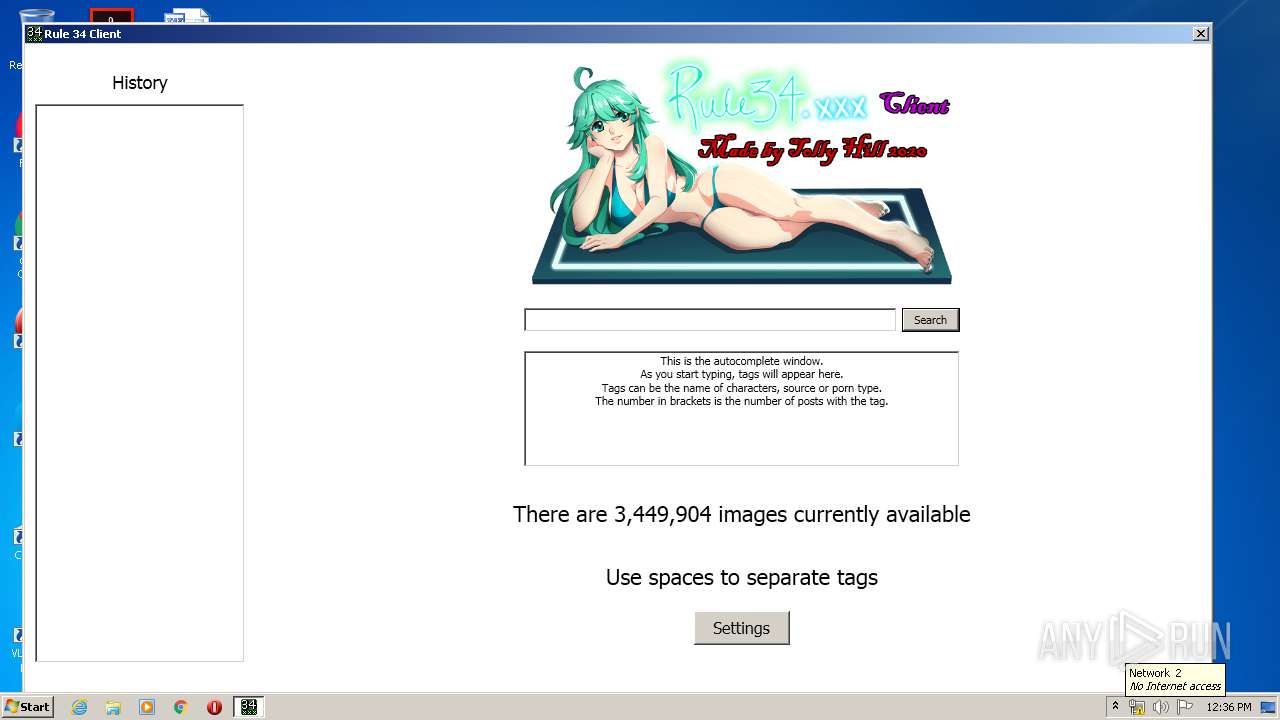
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3372)
- Rule 34 Client.exe (PID: 628)
- Rule 34 Client.exe (PID: 1920)
- Rule 34 Client.exe (PID: 3692)
Application was dropped or rewritten from another process
- Rule 34 Client.exe (PID: 628)
- Rule 34 Client.exe (PID: 3692)
- Rule 34 Client.exe (PID: 1920)
SUSPICIOUS
Reads Environment values
- Rule 34 Client.exe (PID: 628)
- Rule 34 Client.exe (PID: 3692)
- Rule 34 Client.exe (PID: 1920)
INFO
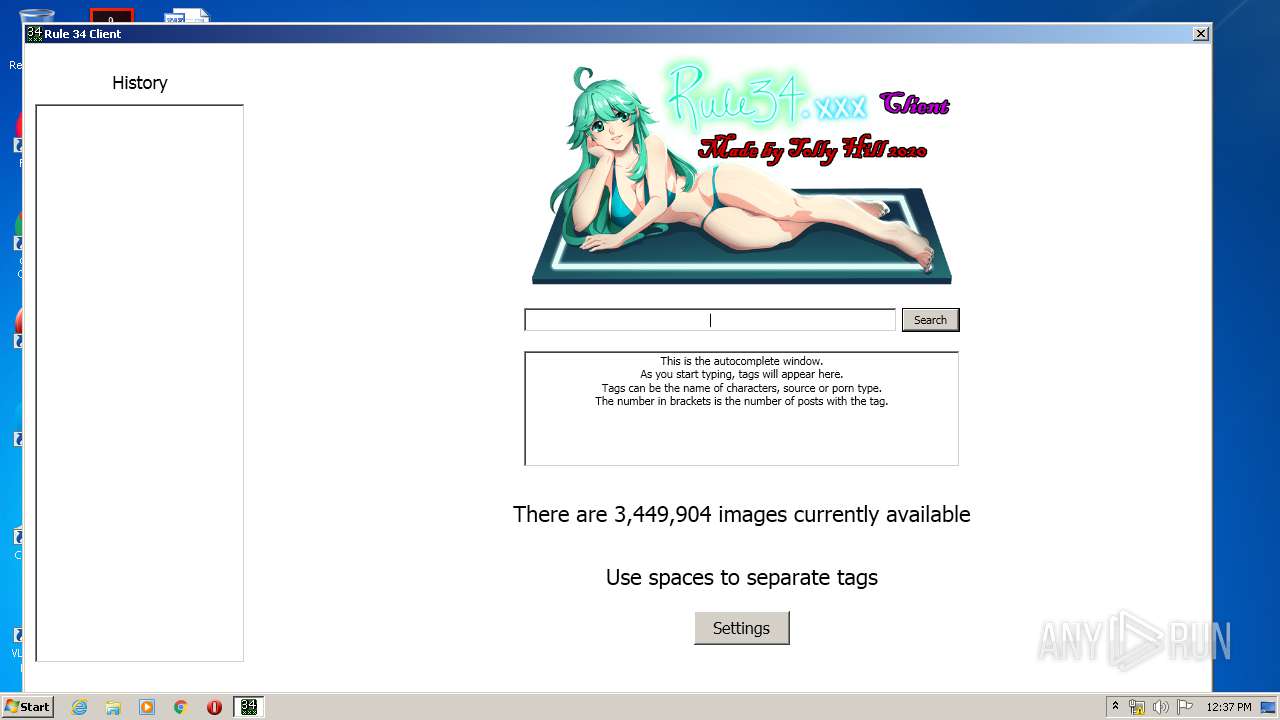
Manual execution by user
- Rule 34 Client.exe (PID: 628)
- Rule 34 Client.exe (PID: 1920)
- Rule 34 Client.exe (PID: 3692)
Reads settings of System Certificates
- Rule 34 Client.exe (PID: 628)
- Rule 34 Client.exe (PID: 1920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:06:01 21:06:12 |
| ZipCRC: | 0x753bfe3b |
| ZipCompressedSize: | 37777 |
| ZipUncompressedSize: | 98304 |
| ZipFileName: | Microsoft.WindowsAPICodePack.dll |
Total processes
40
Monitored processes
5
Malicious processes
4
Suspicious processes
0
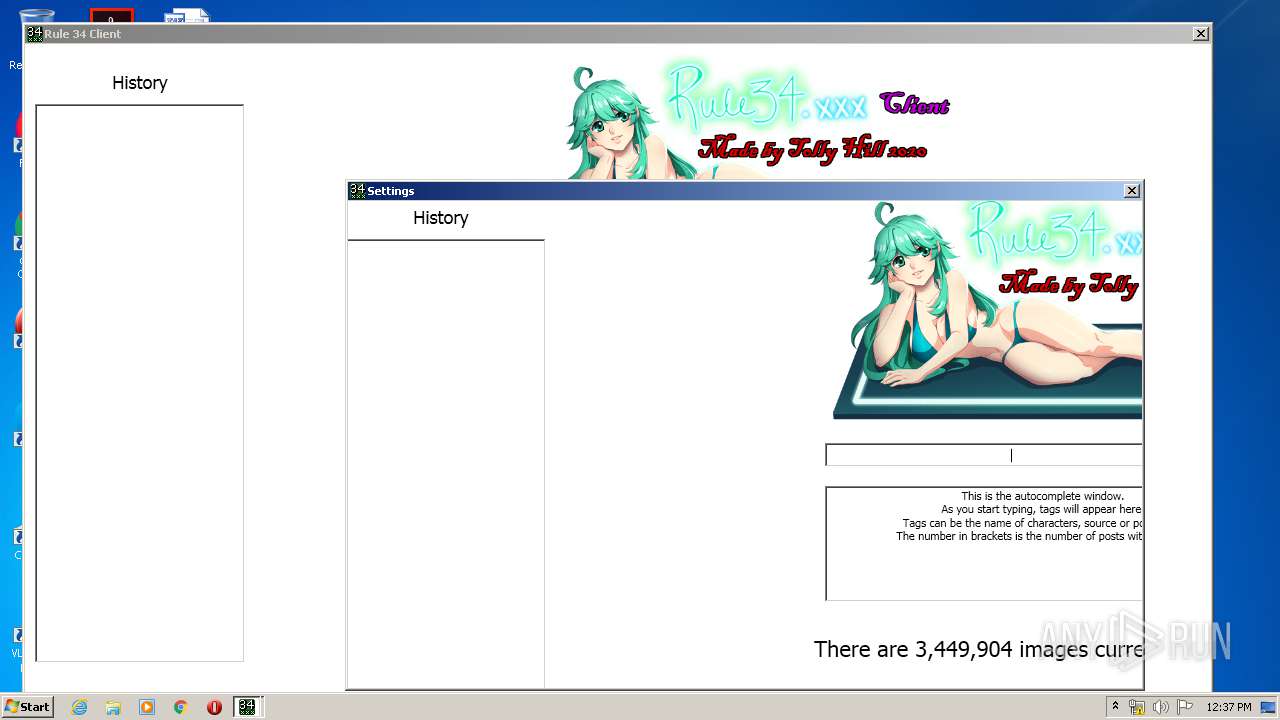
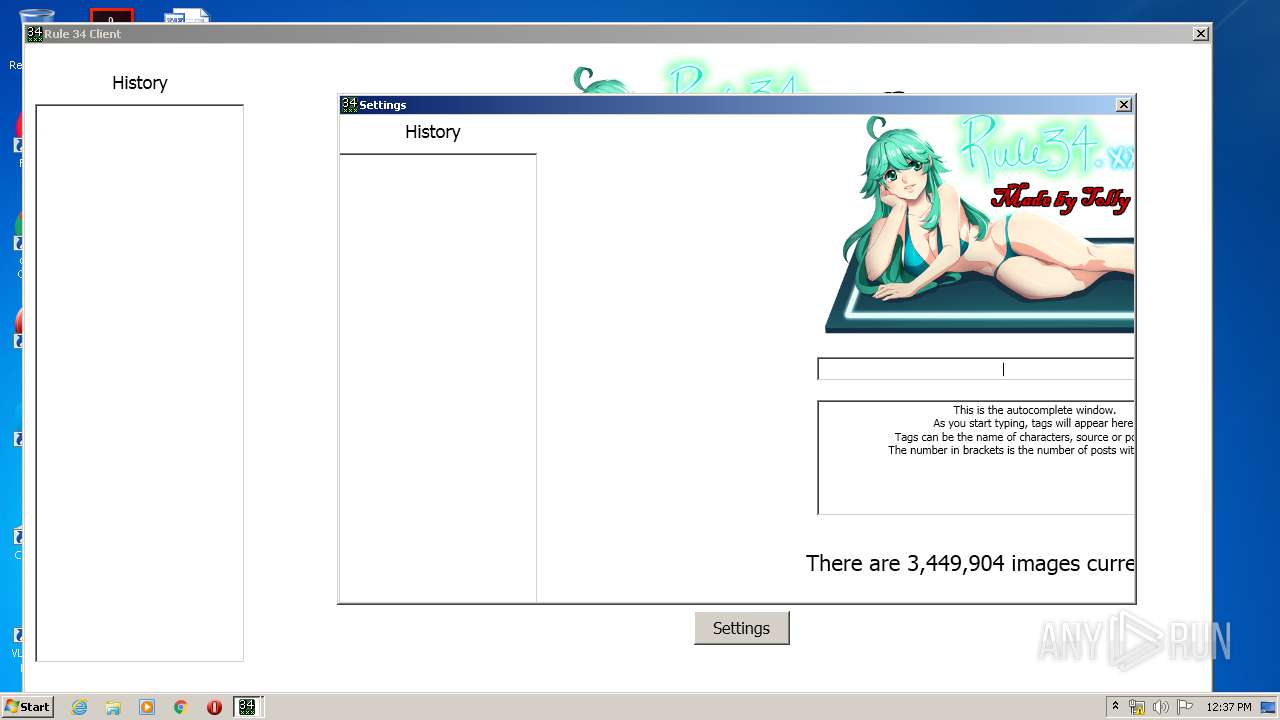
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rule34Client-alpha-0.2.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
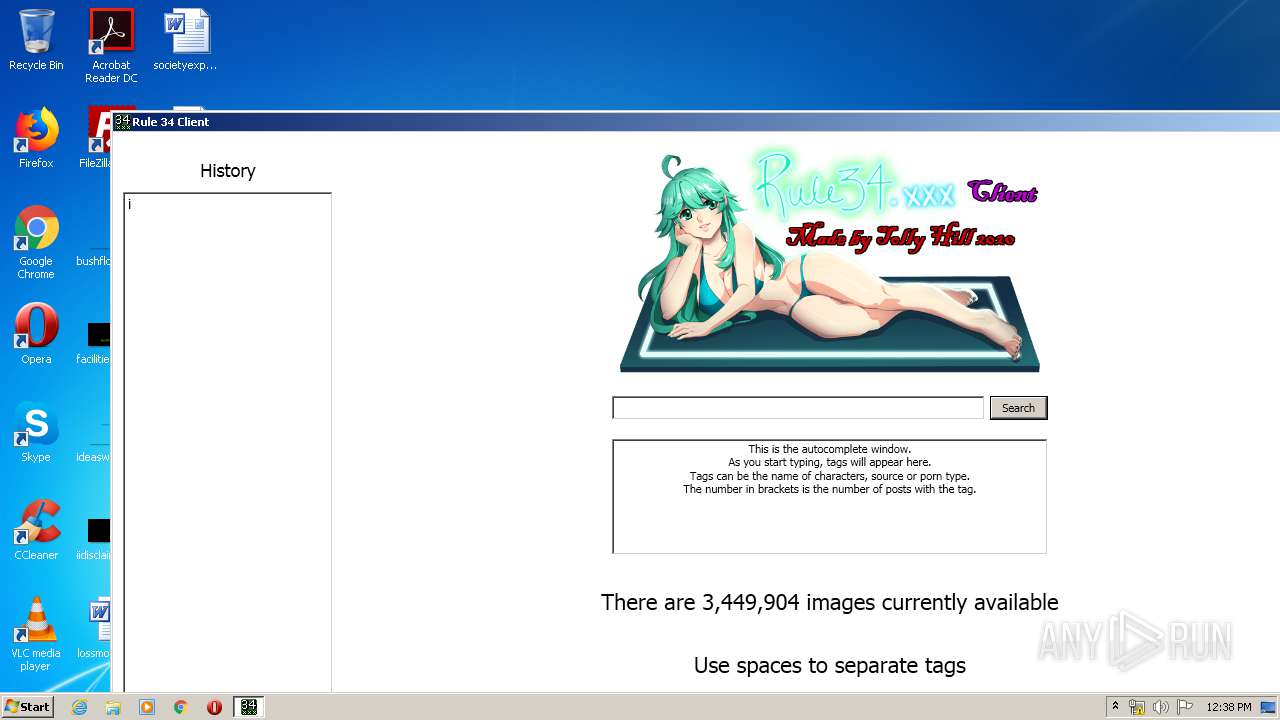
| 628 | "C:\Users\admin\Desktop\Rule 34 Client.exe" | C:\Users\admin\Desktop\Rule 34 Client.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Rule 34 Client Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1920 | "C:\Users\admin\Desktop\Rule 34 Client.exe" | C:\Users\admin\Desktop\Rule 34 Client.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Rule 34 Client Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3372 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3692 | "C:\Users\admin\Desktop\Rule 34 Client.exe" | C:\Users\admin\Desktop\Rule 34 Client.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Rule 34 Client Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
973
Read events
893
Write events
80
Delete events
0
Modification events
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Rule34Client-alpha-0.2.zip | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
0
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.8623\Microsoft.WindowsAPICodePack.dll | — | |
MD5:— | SHA256:— | |||
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.8623\Microsoft.WindowsAPICodePack.Shell.dll | — | |
MD5:— | SHA256:— | |||
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.8623\Newtonsoft.Json.dll | — | |
MD5:— | SHA256:— | |||
| 564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa564.8623\Rule 34 Client.exe | — | |
MD5:— | SHA256:— | |||
| 1920 | Rule 34 Client.exe | C:\Users\admin\AppData\Local\Temp\rule34client\3b83a7911885fe37d4743b3b97142f40.png | — | |
MD5:— | SHA256:— | |||
| 1920 | Rule 34 Client.exe | C:\Users\admin\rule34client\settings.json | text | |
MD5:— | SHA256:— | |||
| 3692 | Rule 34 Client.exe | C:\Users\admin\AppData\Local\Temp\rule34client\f58fd9a04be934824725074c4a1ce748.png | image | |
MD5:— | SHA256:— | |||
| 628 | Rule 34 Client.exe | C:\Users\admin\rule34client\history.json | text | |
MD5:D751713988987E9331980363E24189CE | SHA256:4F53CDA18C2BAA0C0354BB5F9A3ECBE5ED12AB4D8E11BA873C2F11161202B945 | |||
| 1920 | Rule 34 Client.exe | C:\Users\admin\rule34client\history.json | text | |
MD5:68952FD3EB76D7C7D75F5C8C8352C382 | SHA256:CEE059389C67FF991DBD93934ADC5A3A7442085766C2EE23AB85877398CF41B1 | |||
| 628 | Rule 34 Client.exe | C:\Users\admin\rule34client\settings.json | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
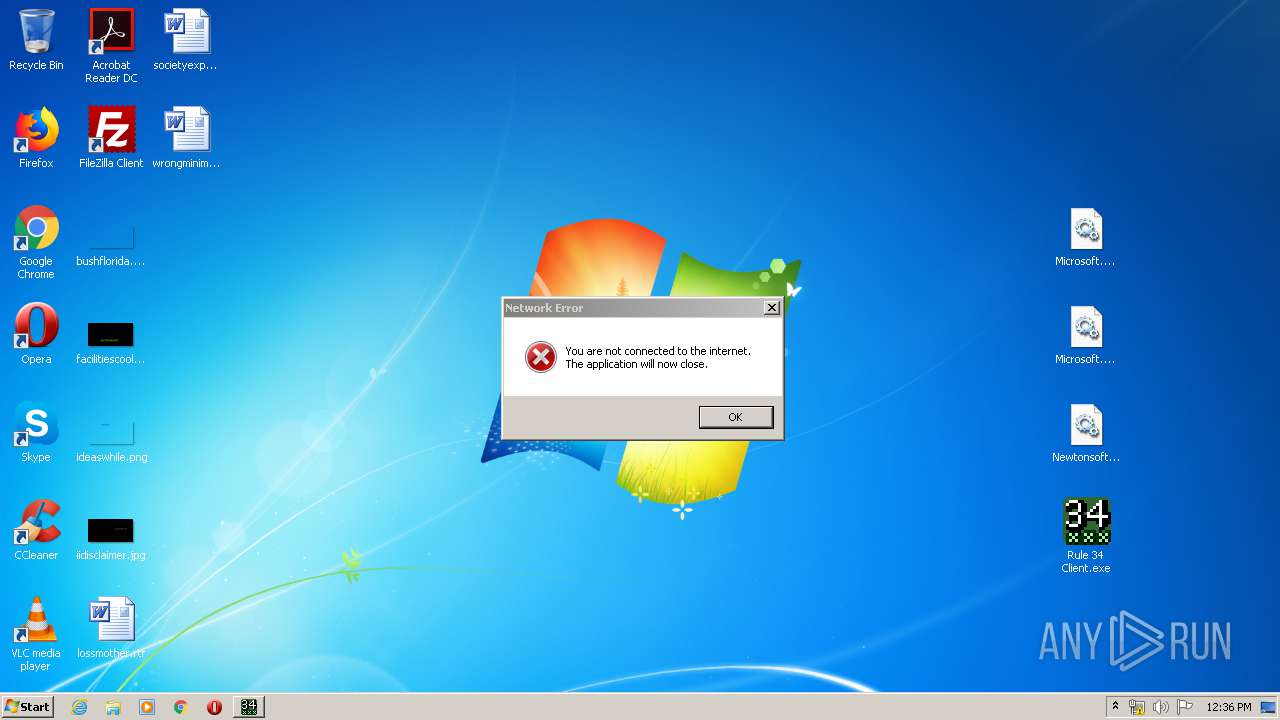
HTTP(S) requests
0
TCP/UDP connections
16
DNS requests
6
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
628 | Rule 34 Client.exe | 3.10.252.136:443 | tollyhill.co.uk | — | US | unknown |
628 | Rule 34 Client.exe | 104.26.1.234:443 | rule34.xxx | Cloudflare Inc | US | shared |
1920 | Rule 34 Client.exe | 3.10.252.136:443 | tollyhill.co.uk | — | US | unknown |
1920 | Rule 34 Client.exe | 104.26.1.234:443 | rule34.xxx | Cloudflare Inc | US | shared |
— | — | 3.10.252.136:443 | tollyhill.co.uk | — | US | unknown |
3692 | Rule 34 Client.exe | 172.67.68.251:443 | rule34.xxx | — | US | suspicious |
3692 | Rule 34 Client.exe | 104.26.1.234:443 | rule34.xxx | Cloudflare Inc | US | shared |
— | — | 172.67.68.251:443 | rule34.xxx | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tollyhill.co.uk |
| unknown |
dns.msftncsi.com |
| shared |
rule34.xxx |
| whitelisted |
img.rule34.xxx |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |