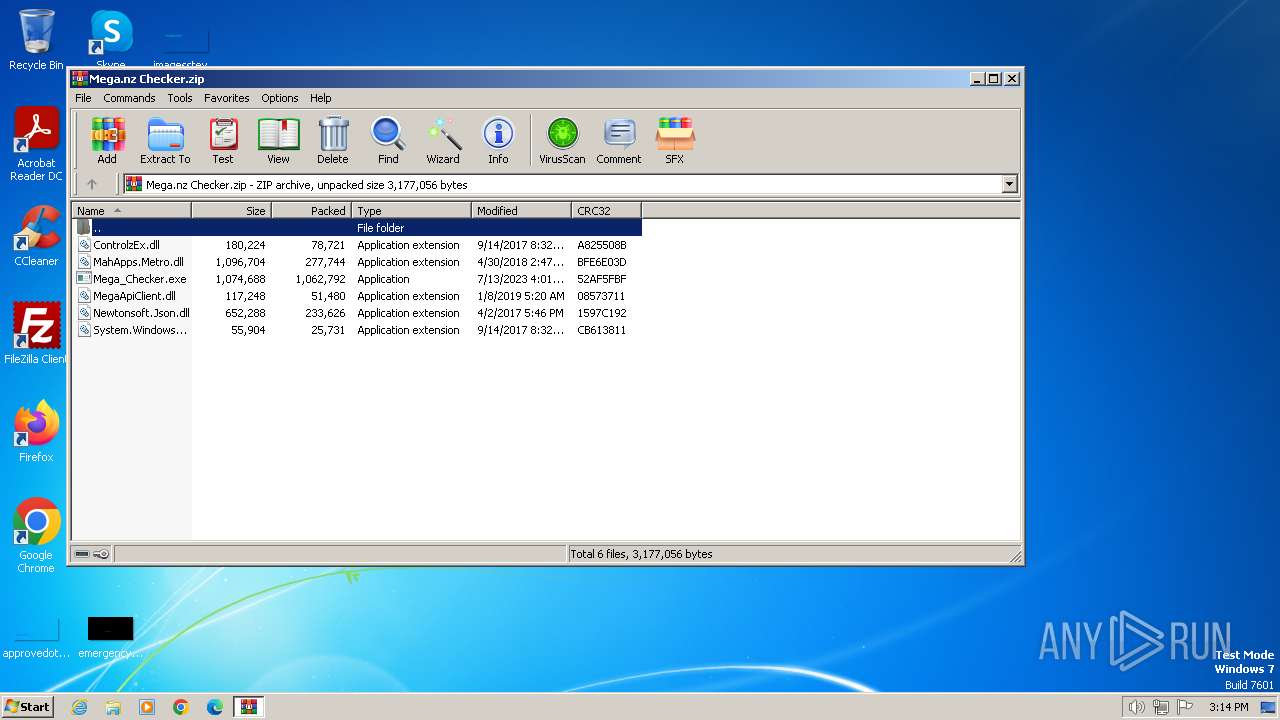
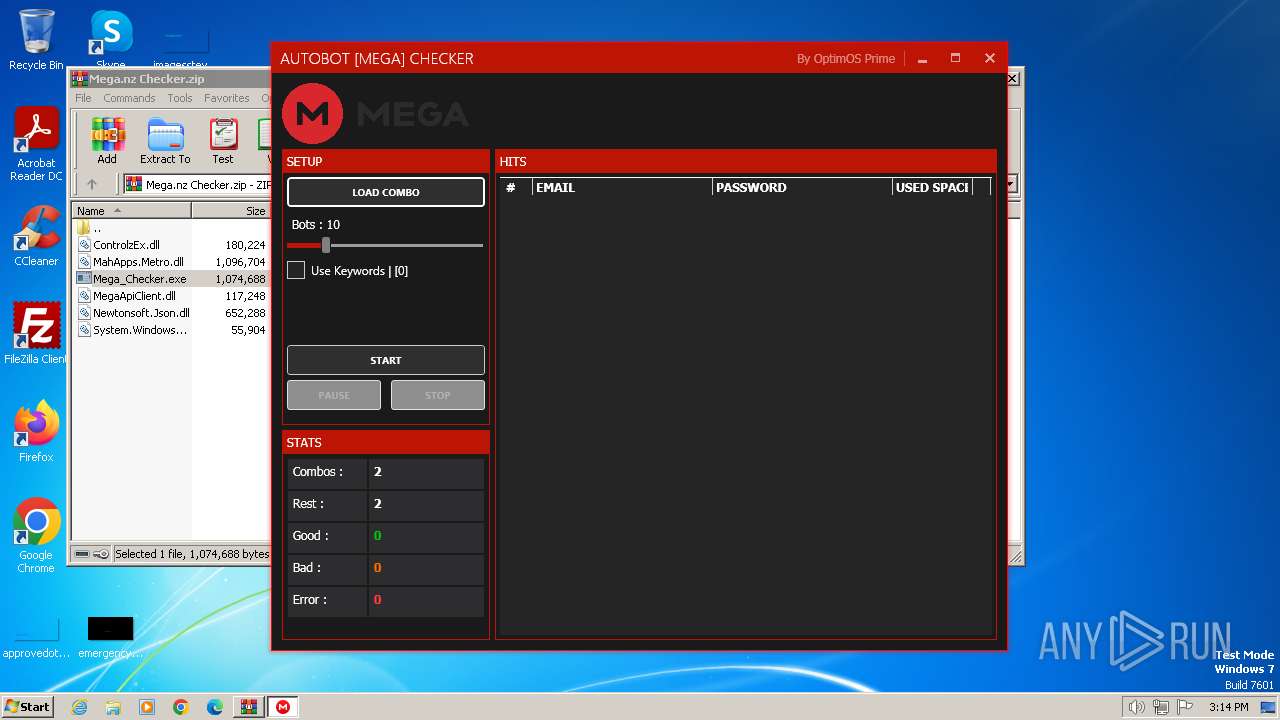
| File name: | Mega.nz Checker.zip |
| Full analysis: | https://app.any.run/tasks/fd1bc0c7-eaf5-4b85-afe4-894614d9f521 |
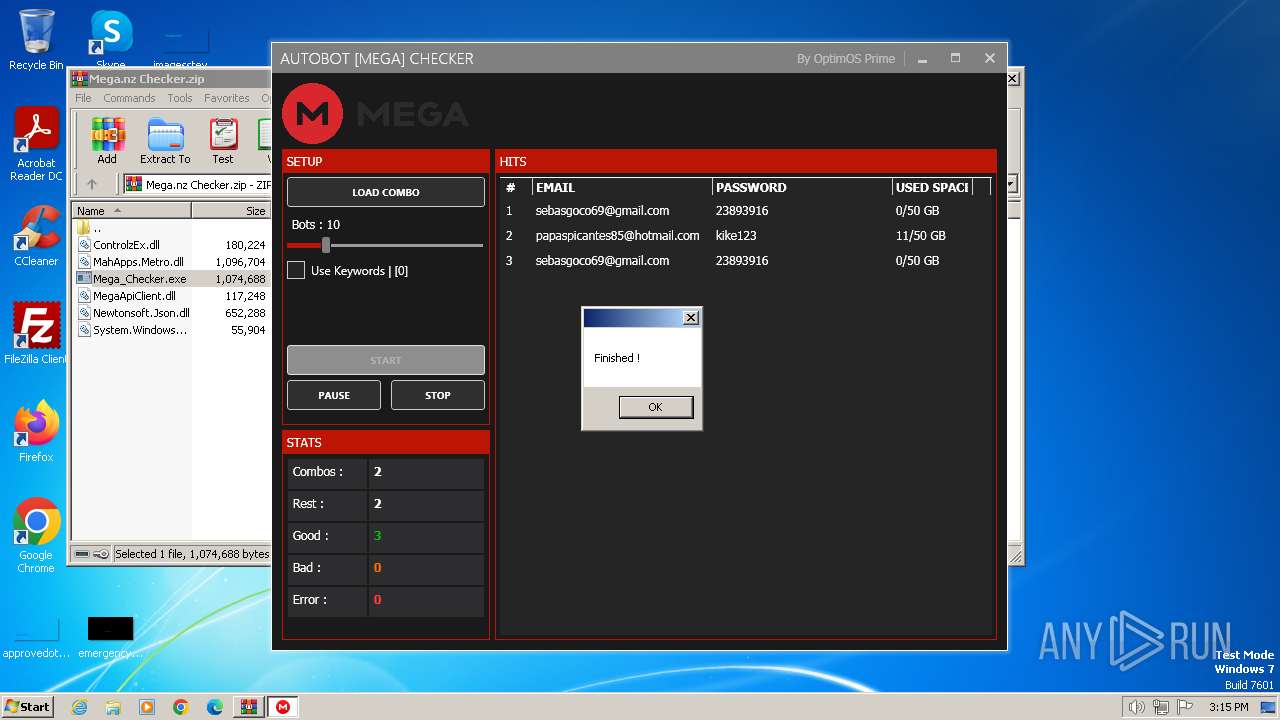
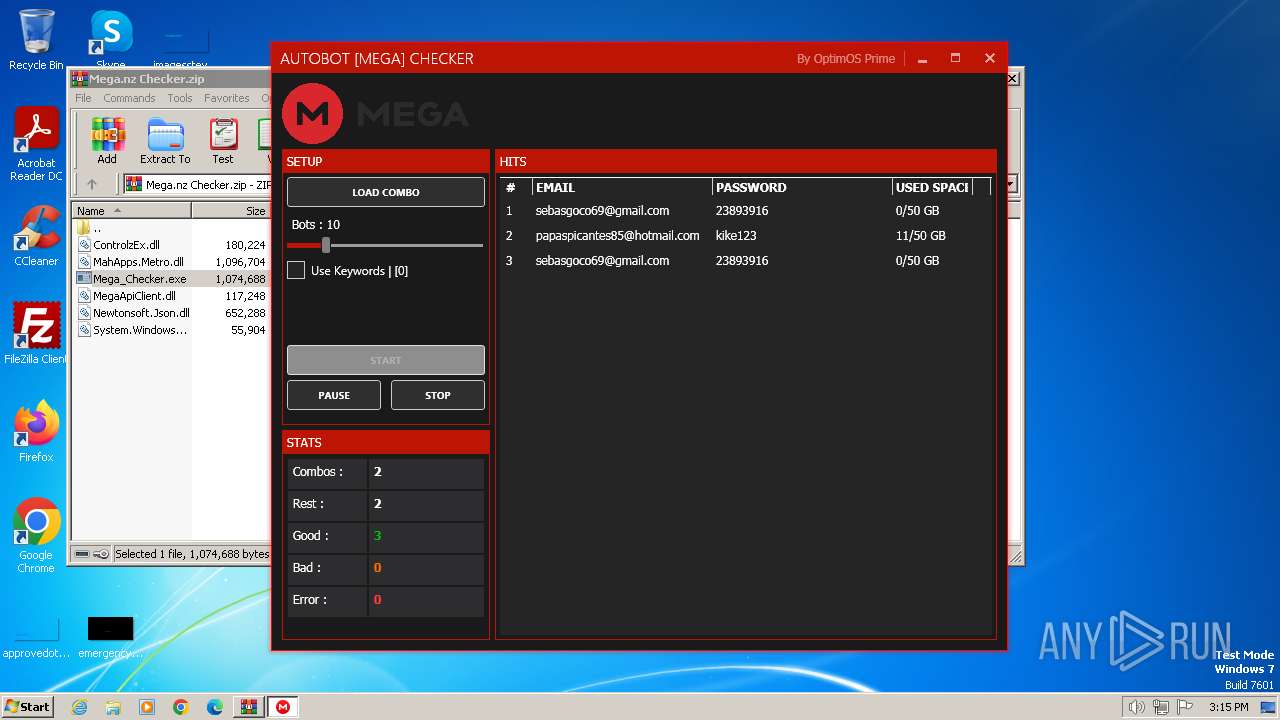
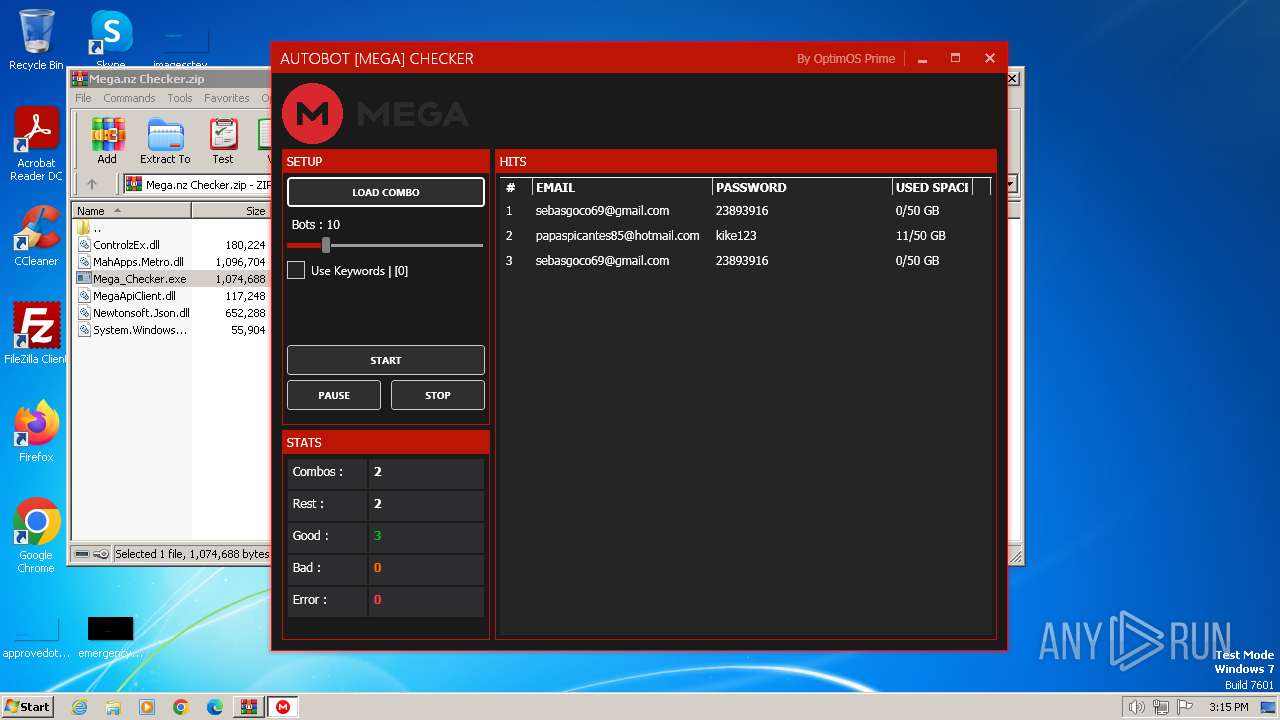
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2024, 15:14:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 4A71F4D3984BBBB59ADB68A0DF5EC236 |
| SHA1: | 55678C7250CAF2B2E0FFBAC34651061979F9E404 |
| SHA256: | 0B532F298D72EDC779F7F5982487F3BF4E48EEF3BFC0D24E0A4B0A7469217756 |
| SSDEEP: | 98304:TqEM9zWtwNj0gRL9DcybisL8eX3Qj/Jzhumwmhnt4m1yenxP2H/059ufDiz1MRCC:/iP |
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1392)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 1392)
Reads the Internet Settings
- Mega_Checker.exe (PID: 896)
Reads settings of System Certificates
- Mega_Checker.exe (PID: 896)
INFO
Checks supported languages
- Mega_Checker.exe (PID: 896)
Reads the computer name
- Mega_Checker.exe (PID: 896)
Reads the machine GUID from the registry
- Mega_Checker.exe (PID: 896)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1392)
Create files in a temporary directory
- Mega_Checker.exe (PID: 896)
Reads Environment values
- Mega_Checker.exe (PID: 896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2017:09:14 22:32:52 |
| ZipCRC: | 0xa825508b |
| ZipCompressedSize: | 78721 |
| ZipUncompressedSize: | 180224 |
| ZipFileName: | ControlzEx.dll |
Total processes
38
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
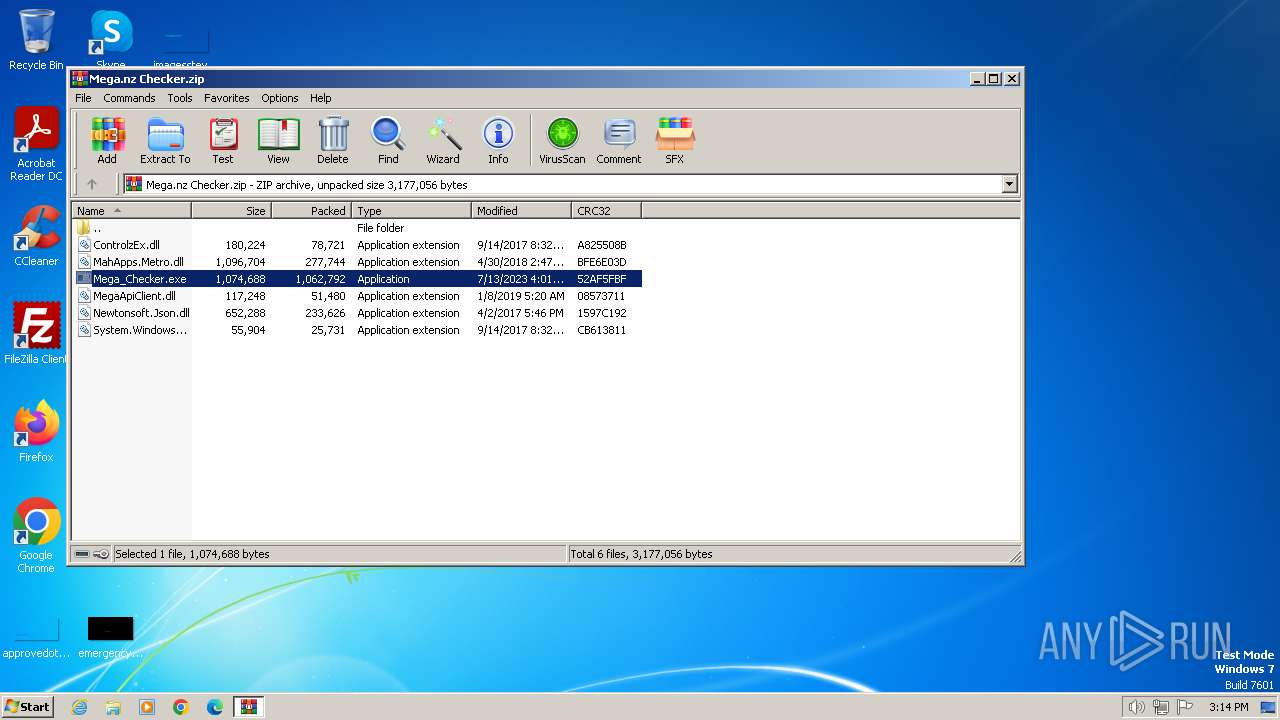
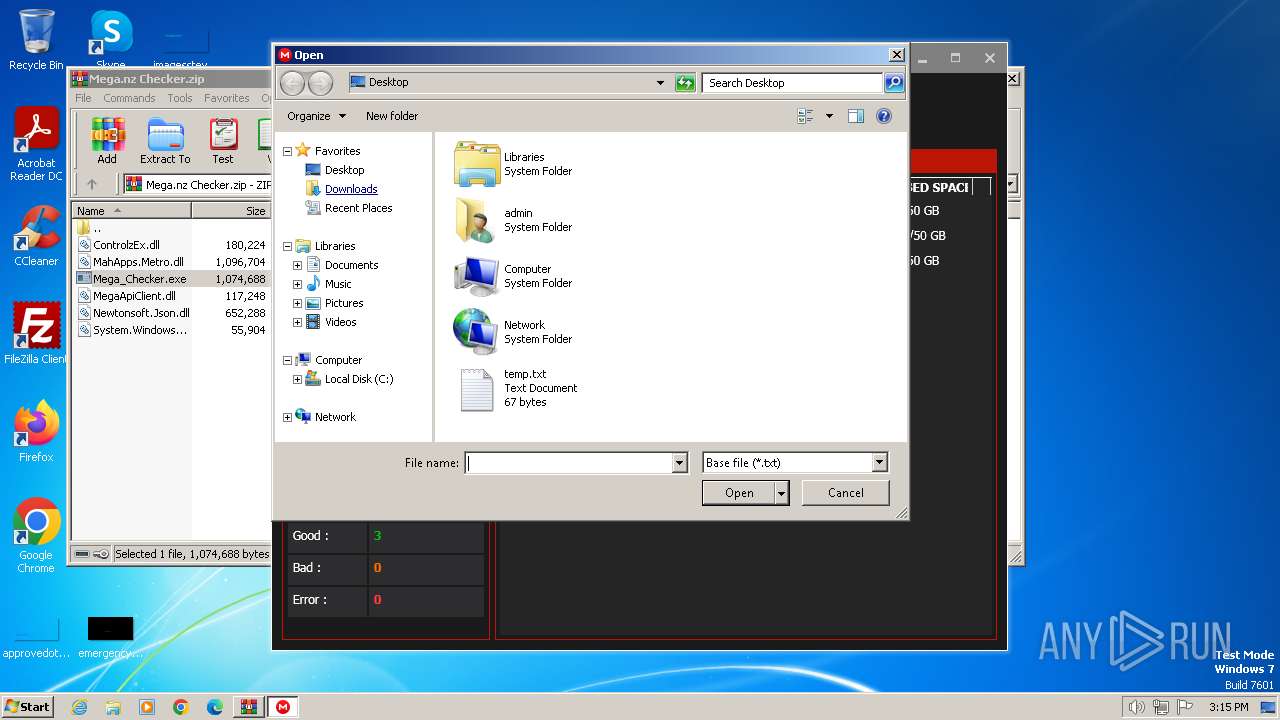
| 896 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\Mega_Checker.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\Mega_Checker.exe | WinRAR.exe | ||||||||||||
User: admin Company: Optim OS Prime (fb : @med.ah.101) Integrity Level: MEDIUM Description: AutoBot [Mega] Checker By Optim OS Prime Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Mega.nz Checker.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
9 159
Read events
9 029
Write events
123
Delete events
7
Modification events
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
6
Suspicious files
1
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
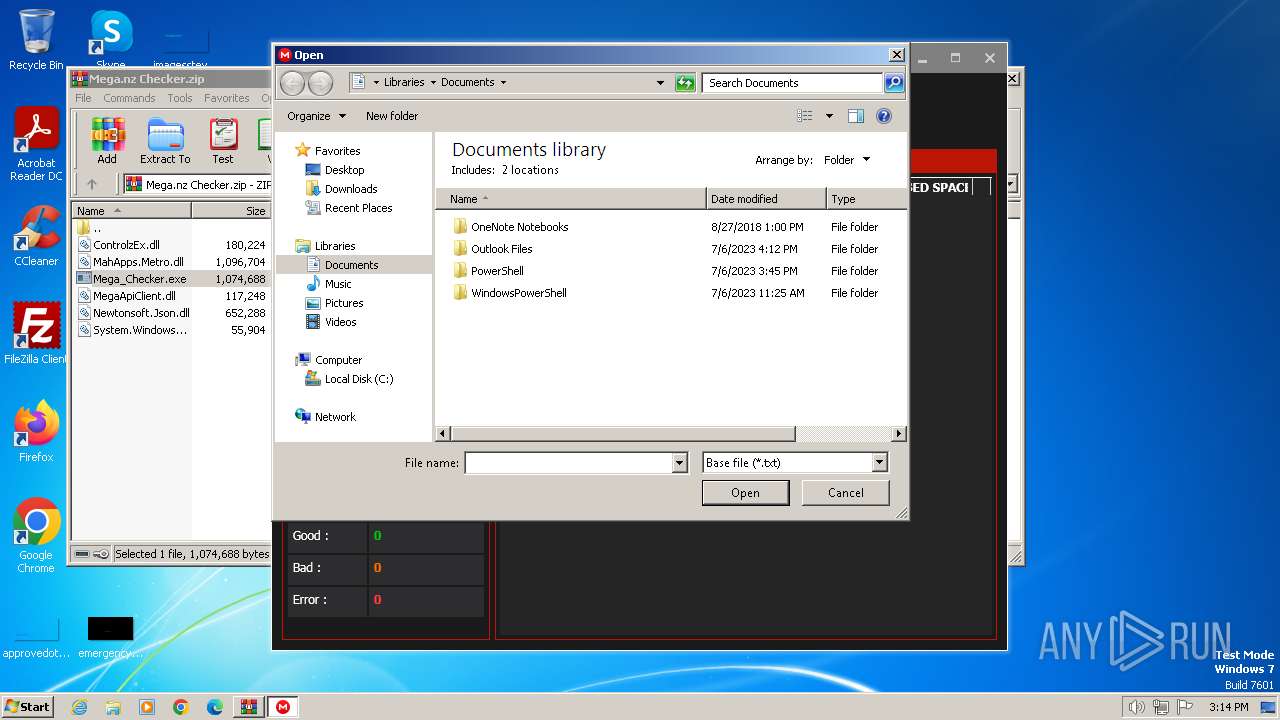
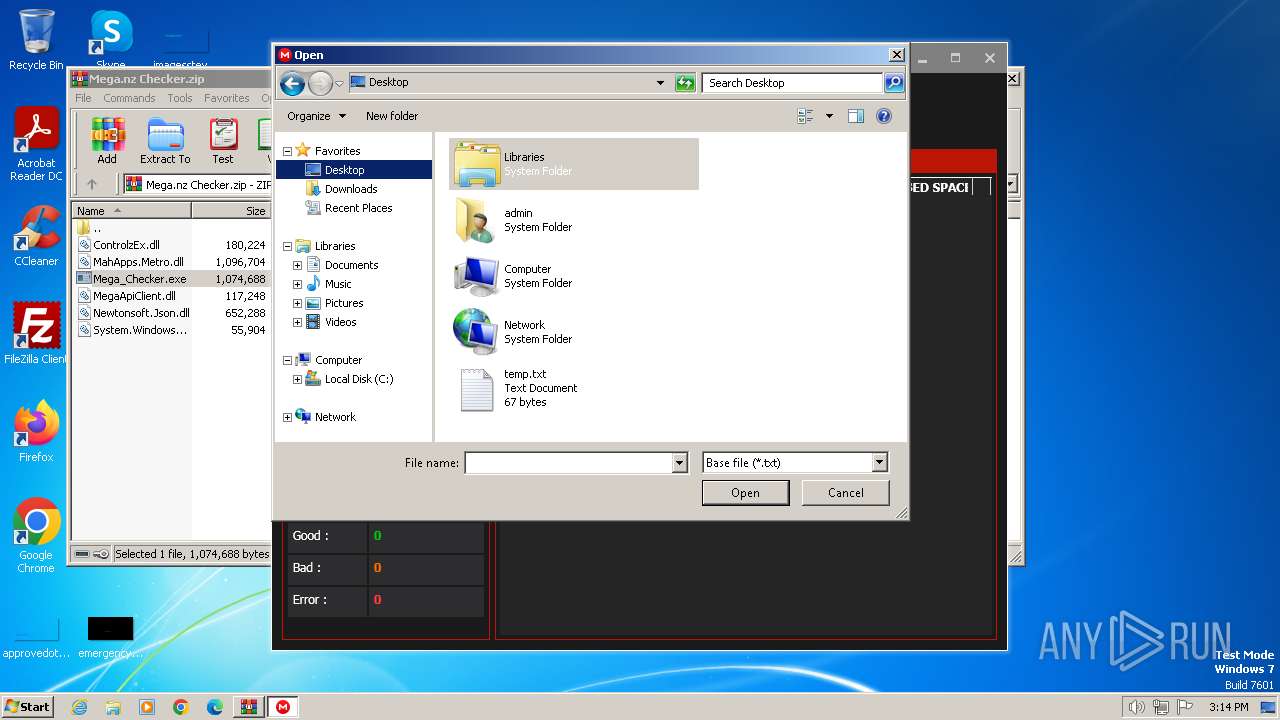
| 896 | Mega_Checker.exe | C:\Users\admin\AppData\Local\Temp\WPF\3gkgseuj.q2r | binary | |
MD5:825AB5E8C725411B8B9C319BDCC8EA4E | SHA256:2E3A2C34CC9728CB3C1915E1C778FD0D63D46AC8E238C90726C96E4A31042357 | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\System.Windows.Interactivity.dll | executable | |
MD5:580244BC805220253A87196913EB3E5E | SHA256:93FBC59E4880AFC9F136C3AC0976ADA7F3FAA7CACEDCE5C824B337CBCA9D2EBF | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\MegaApiClient.dll | executable | |
MD5:58558366833DA7E207F6B3C4B4E757E8 | SHA256:17D65F244CCD360A74531B93226AAE93E730597973F459CF18E6EF0B2BD12A4B | |||
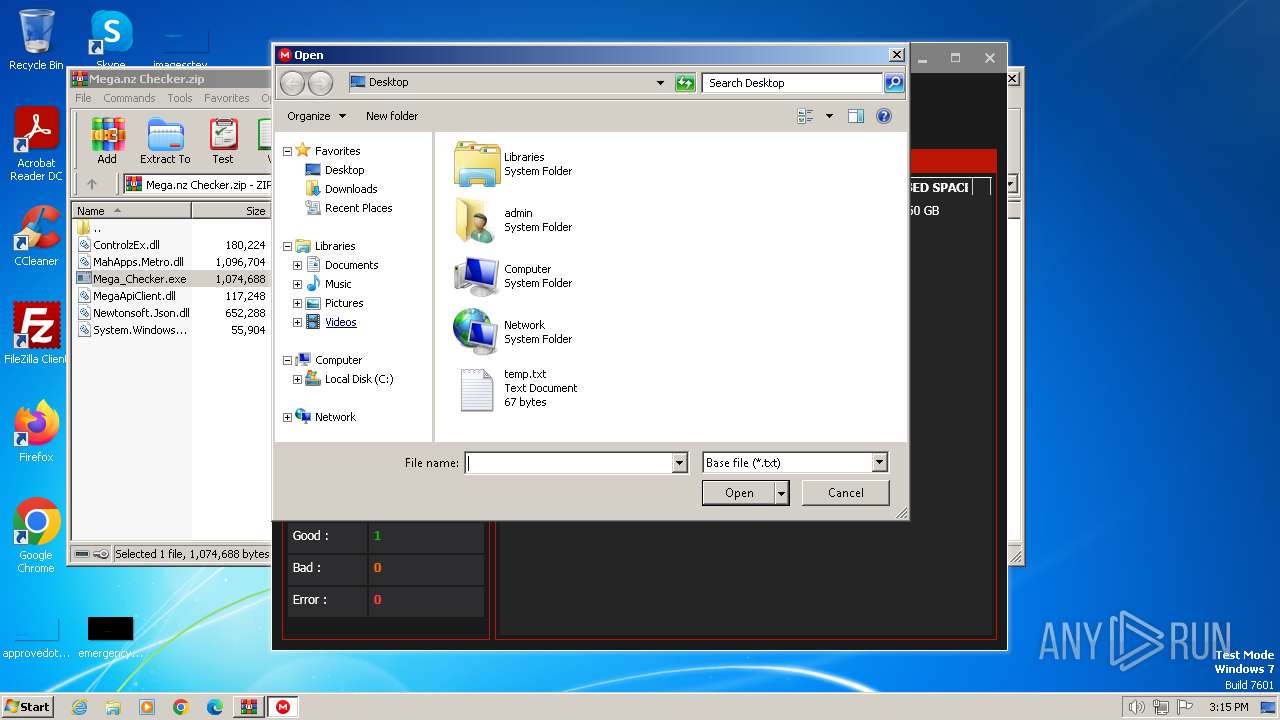
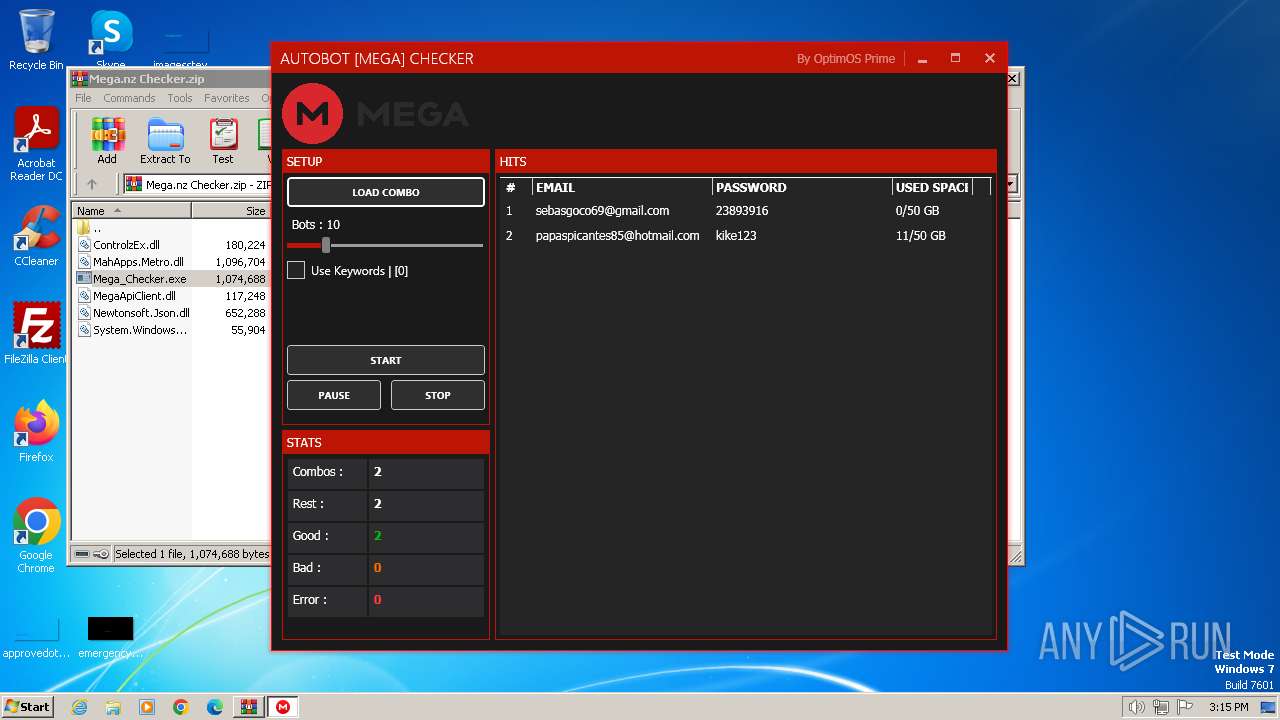
| 896 | Mega_Checker.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\Results_2024-02-03 15.14.57\Accounts\Account_1.txt | text | |
MD5:0BA7A568191FBDCCEA875BCD70BEA9D4 | SHA256:F76FDE76B9ABB9F3499640AFAA87FA0398CF64EFF11819D25C7E45CD9C9951DE | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\Newtonsoft.Json.dll | executable | |
MD5:A6BE9EFDAA744E9947F4EE18DE5423BD | SHA256:6CC0CBCD5C4709C6A1C97F5581C347D93E586E7CC0D64BFFB4D32C6E753476A4 | |||
| 896 | Mega_Checker.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\Results_2024-02-03 15.15.25\Accounts\Account_2.txt | text | |
MD5:0BA7A568191FBDCCEA875BCD70BEA9D4 | SHA256:F76FDE76B9ABB9F3499640AFAA87FA0398CF64EFF11819D25C7E45CD9C9951DE | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\MahApps.Metro.dll | executable | |
MD5:B27F427DAE3158EE0870E9FE0CC06BC5 | SHA256:AE4CA9EA3985B34A568AFEB6E1C0DFE66A20F7498E35C17CC1B19F09581EBD8D | |||
| 896 | Mega_Checker.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\Results_2024-02-03 15.15.25\Good.txt | text | |
MD5:F9406E5D381CCDD54BE65CD29CCECD8C | SHA256:ED5D74665C6581B821A152CB7E2872C3DABE0AF0C04FD3B4C47E65EBE1359AAE | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\ControlzEx.dll | executable | |
MD5:5CF2837021516334344629CB679D40B5 | SHA256:55CAE0AF8517AC2D787B210AC6F79C9AAC7F58035B69FAAF620A90F33E2676FC | |||
| 896 | Mega_Checker.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1392.26372\Results_2024-02-03 15.14.57\Accounts\Account_3.txt | text | |
MD5:0BA7A568191FBDCCEA875BCD70BEA9D4 | SHA256:F76FDE76B9ABB9F3499640AFAA87FA0398CF64EFF11819D25C7E45CD9C9951DE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
2
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
896 | Mega_Checker.exe | 66.203.125.11:443 | g.api.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
g.api.mega.co.nz |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
1080 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |