| File name: | Sulfoxide.exe |
| Full analysis: | https://app.any.run/tasks/6e5ae683-2c5c-4c95-abce-bcec90219939 |
| Verdict: | Malicious activity |
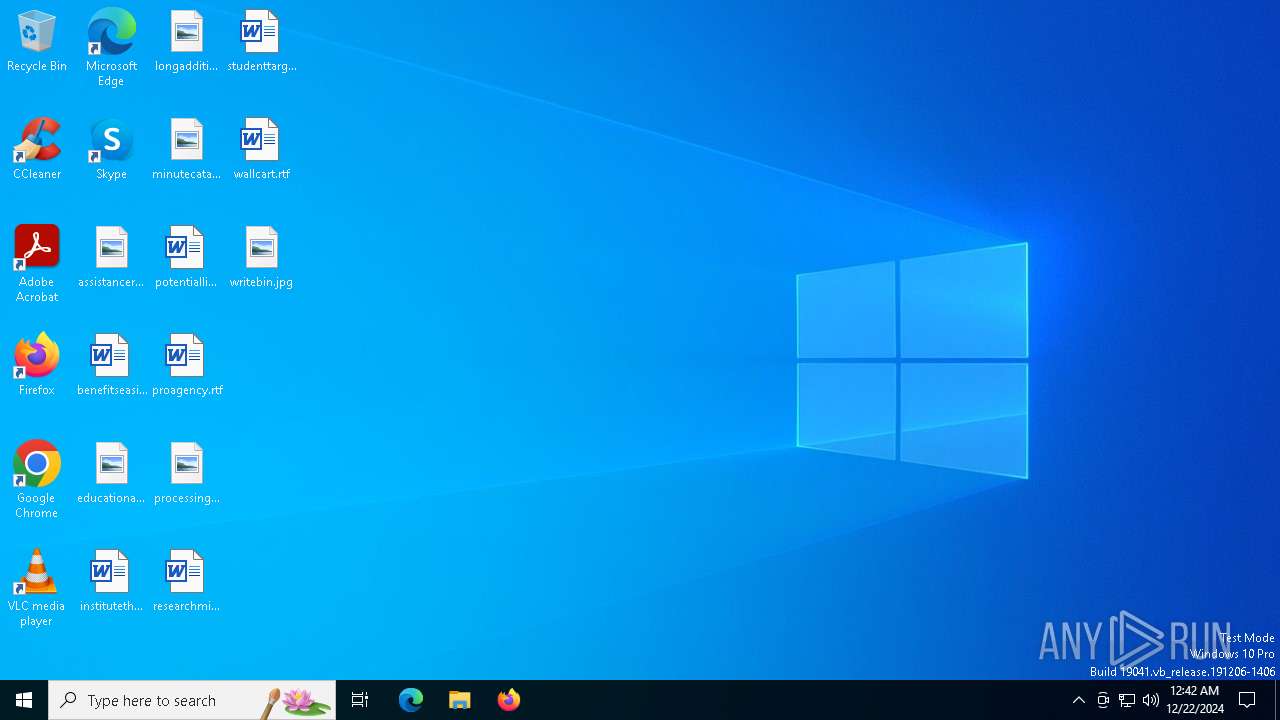
| Analysis date: | December 22, 2024, 00:42:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 1CA9BB97705F05CD9F3A09A96E40E04F |
| SHA1: | 8C594715113F410FB1F221187F708D235BD93AB4 |
| SHA256: | 0B529219AFCC34FDF7FC8DF2F311289B95550B3C2F1B56479B5B9020AAE42BEE |
| SSDEEP: | 6144:Uq+ZXRBznAaif+G0STRenEYg+q/GTqbr4JBBbm:khxEYg+qR0Ra |
MALICIOUS
No malicious indicators.SUSPICIOUS
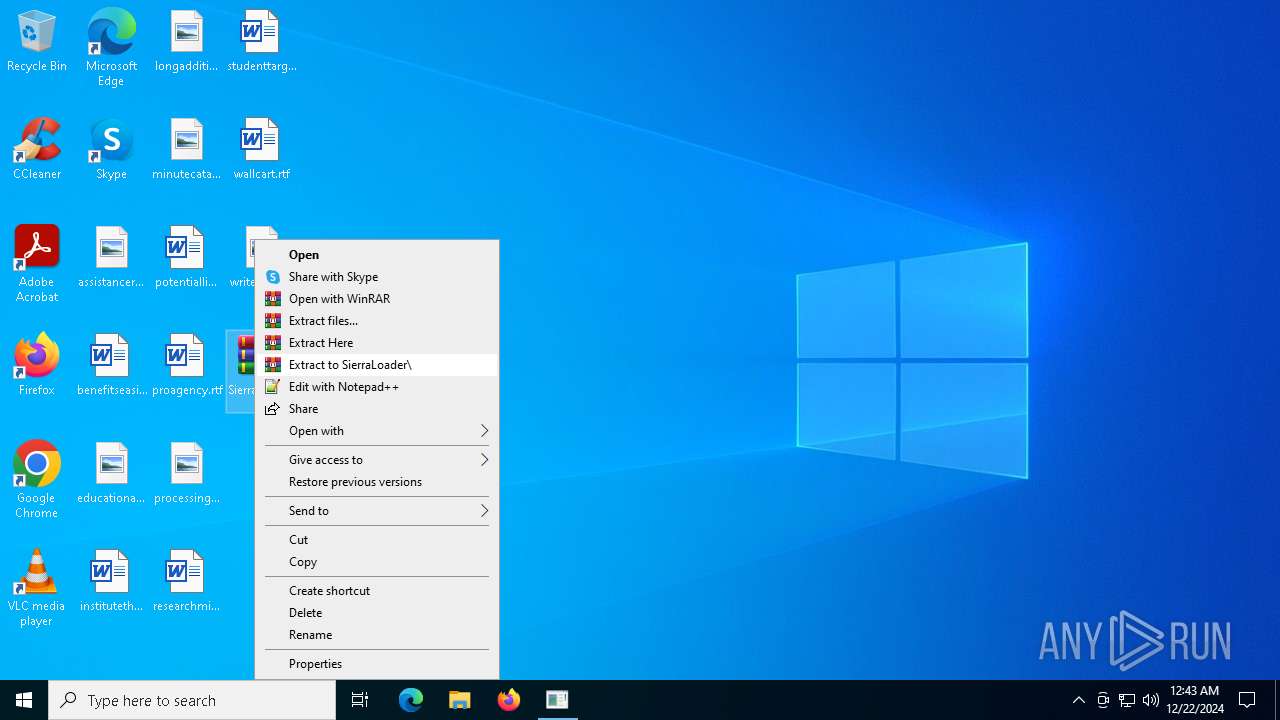
Process drops legitimate windows executable
- WinRAR.exe (PID: 7148)
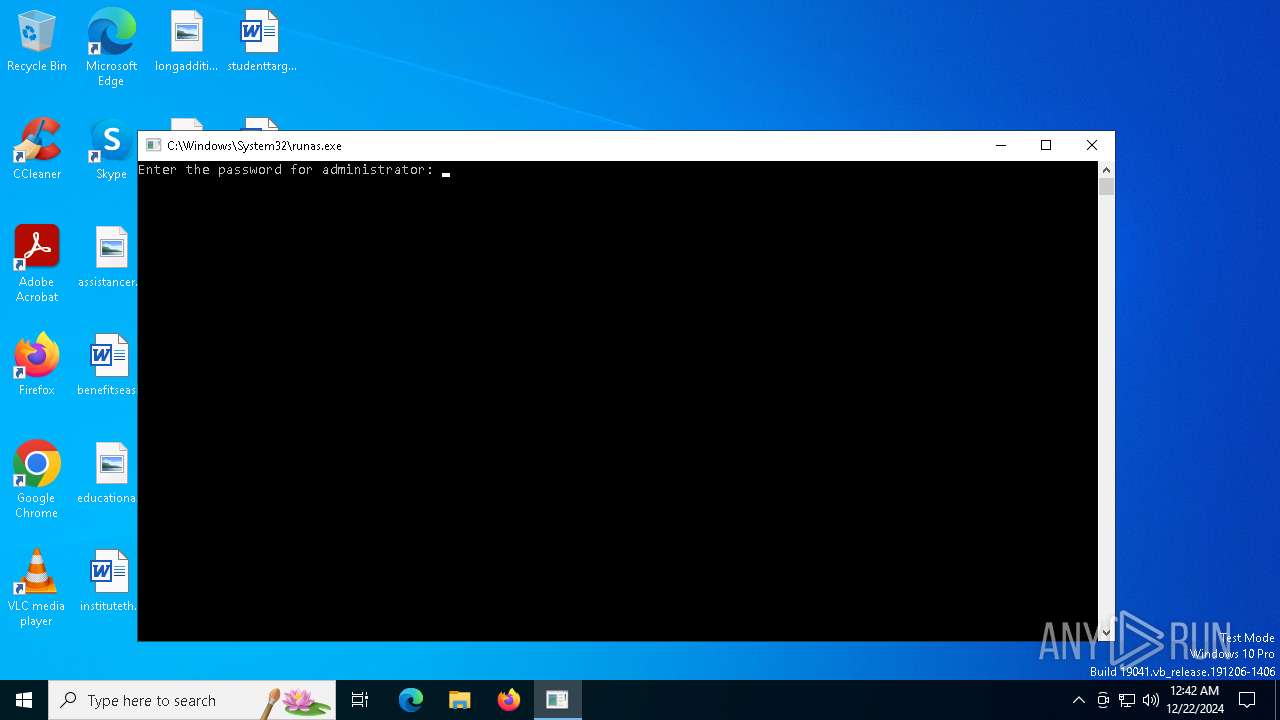
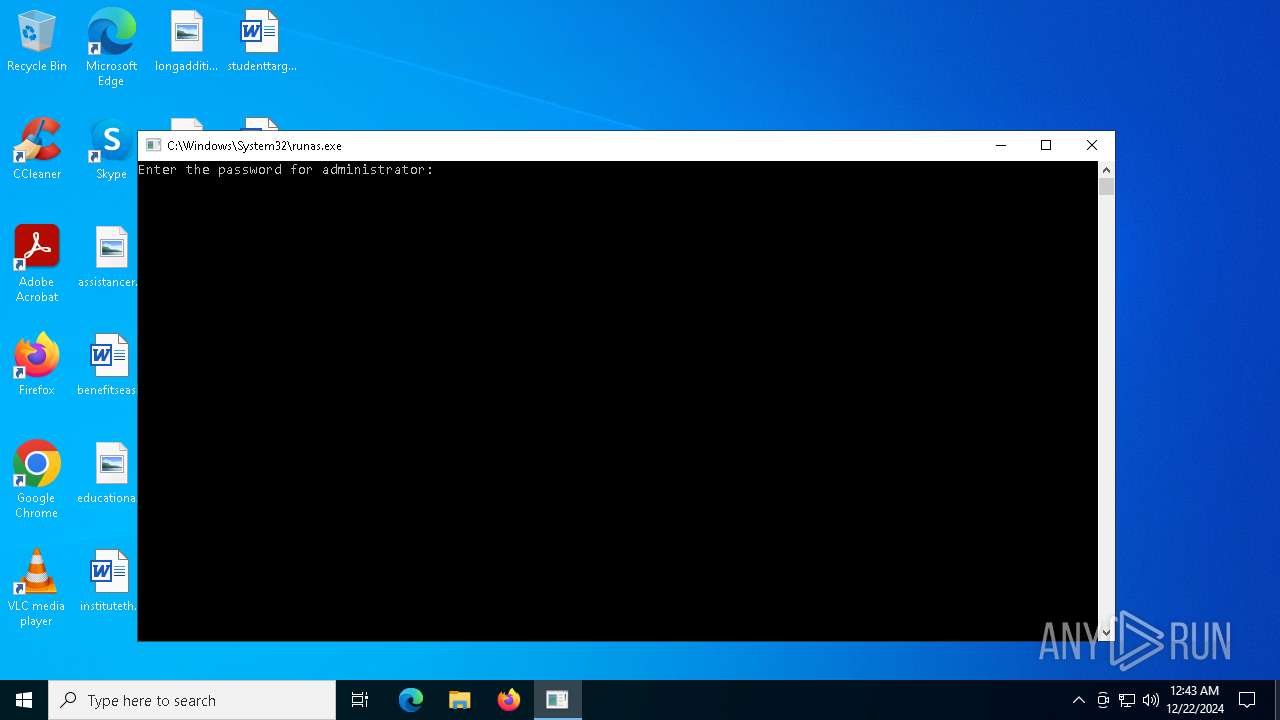
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 3952)
Reads security settings of Internet Explorer
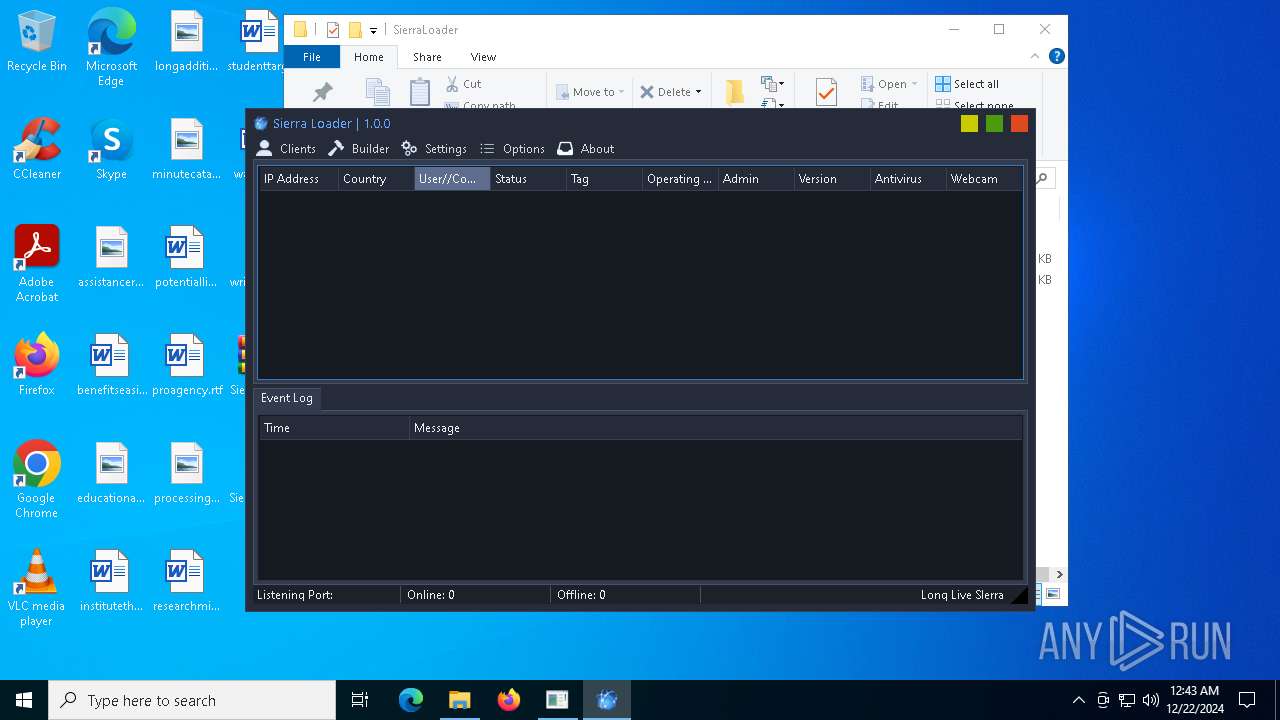
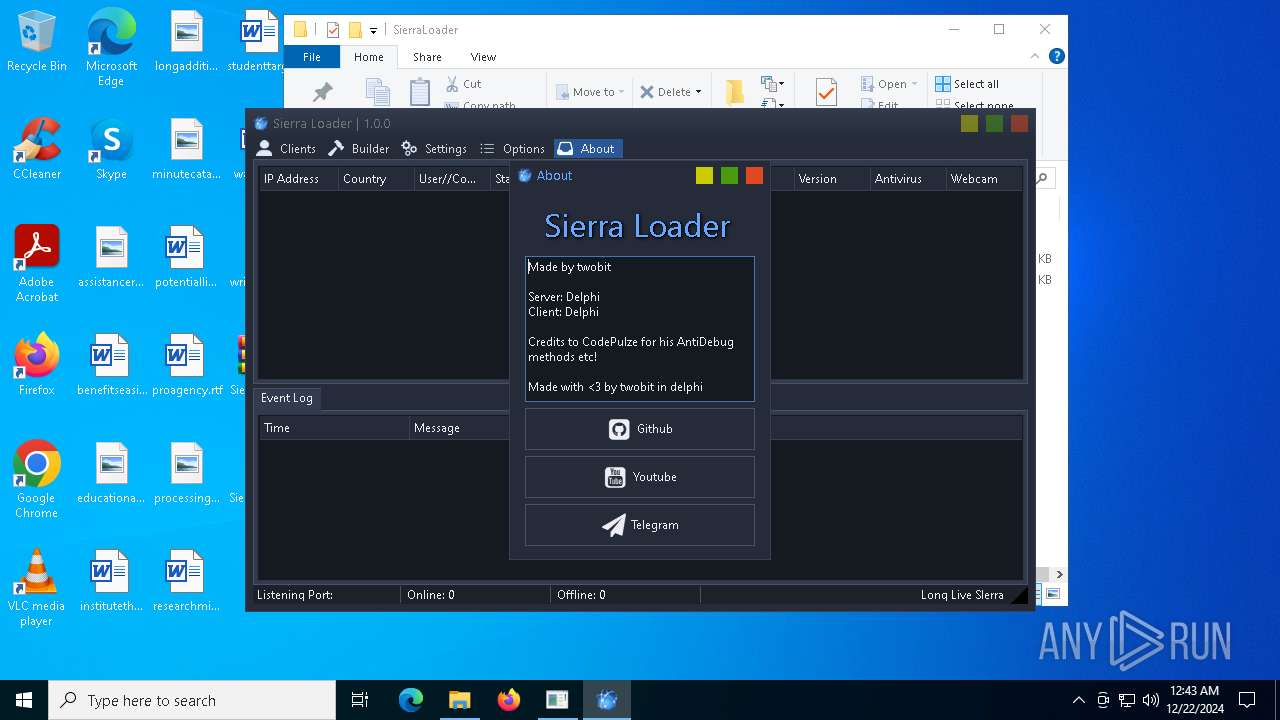
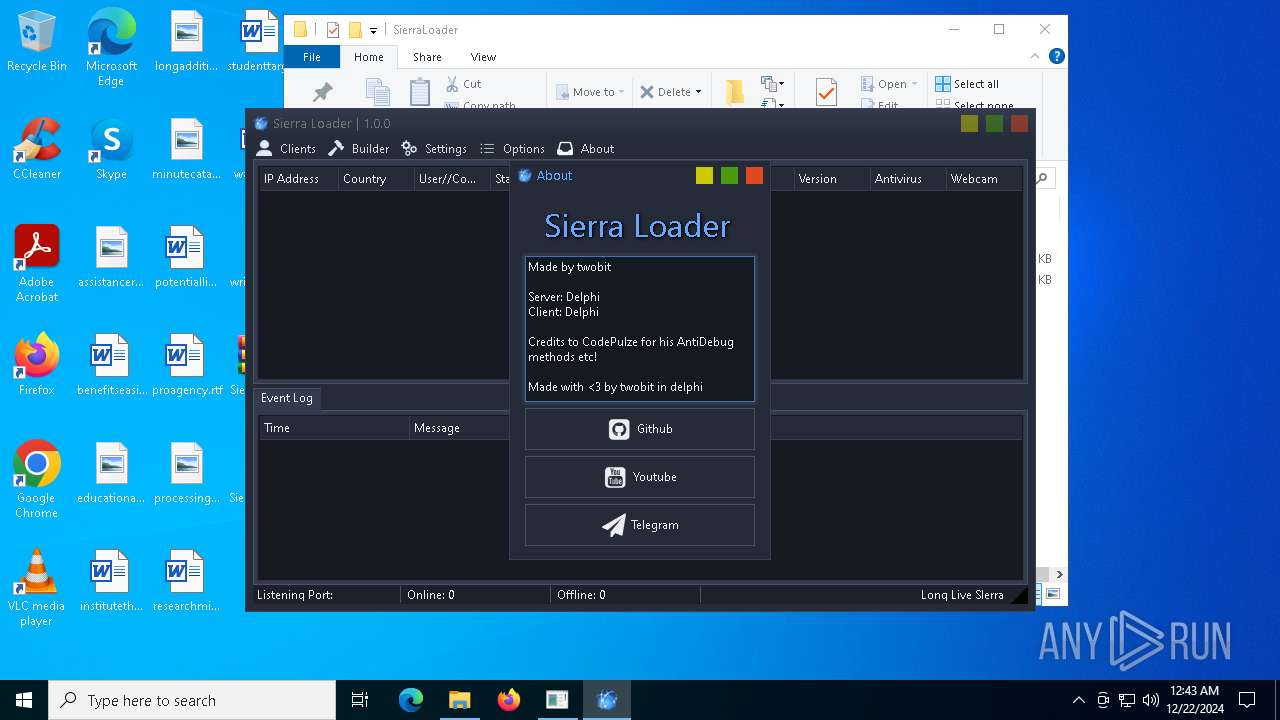
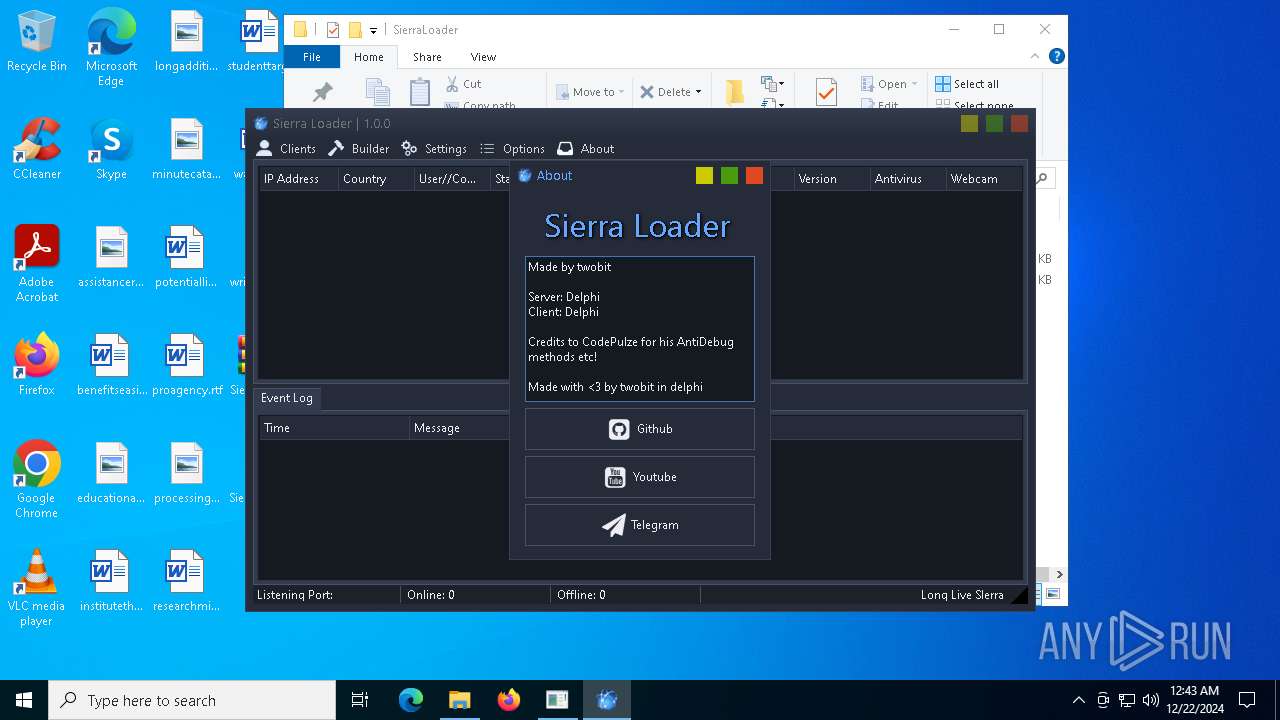
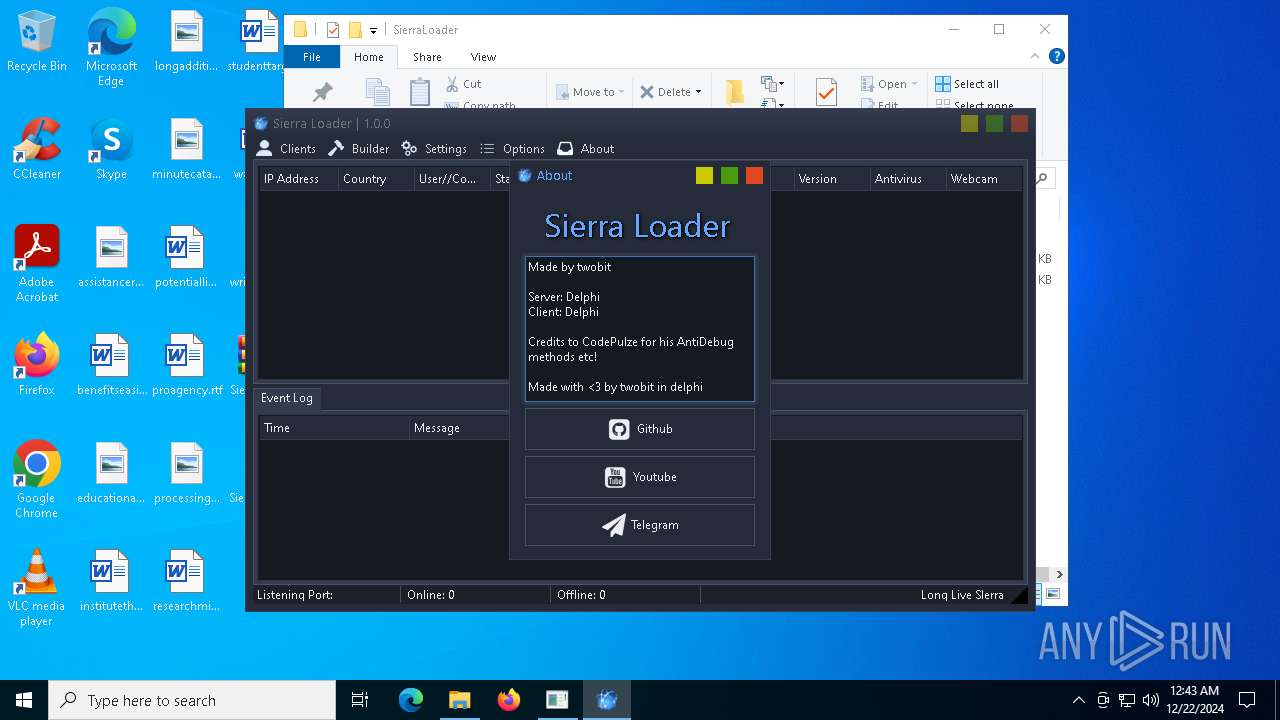
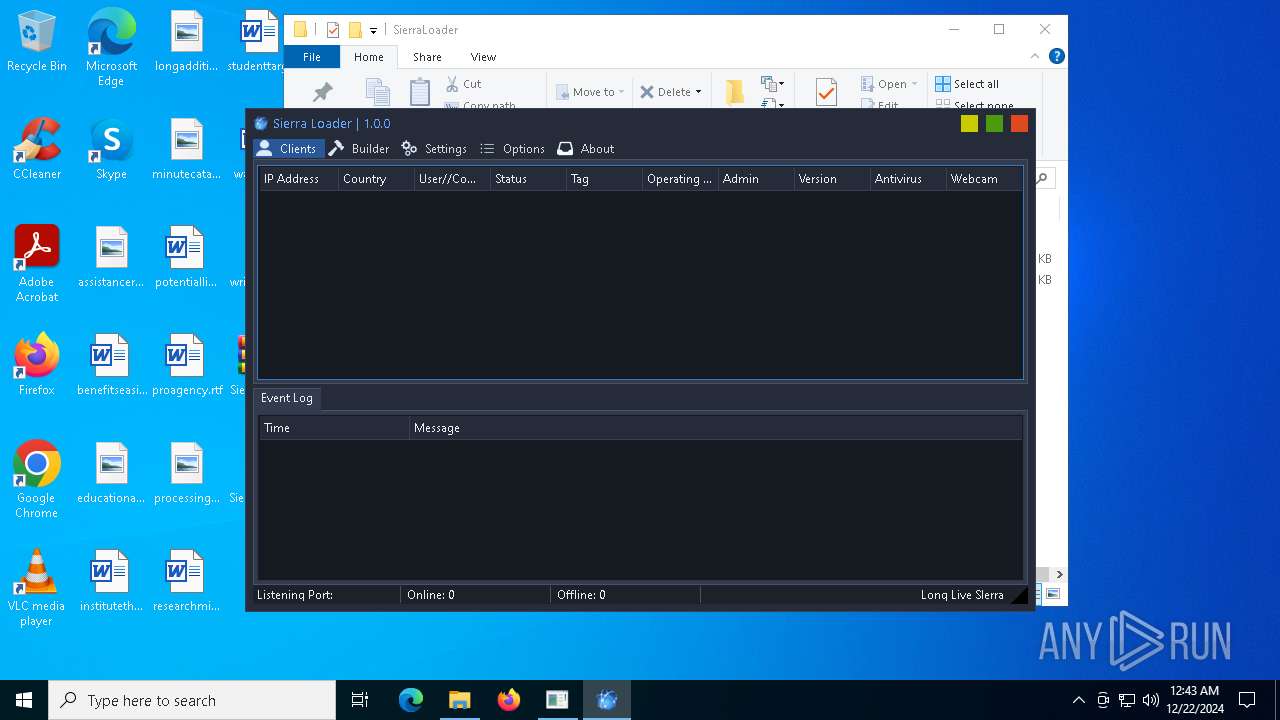
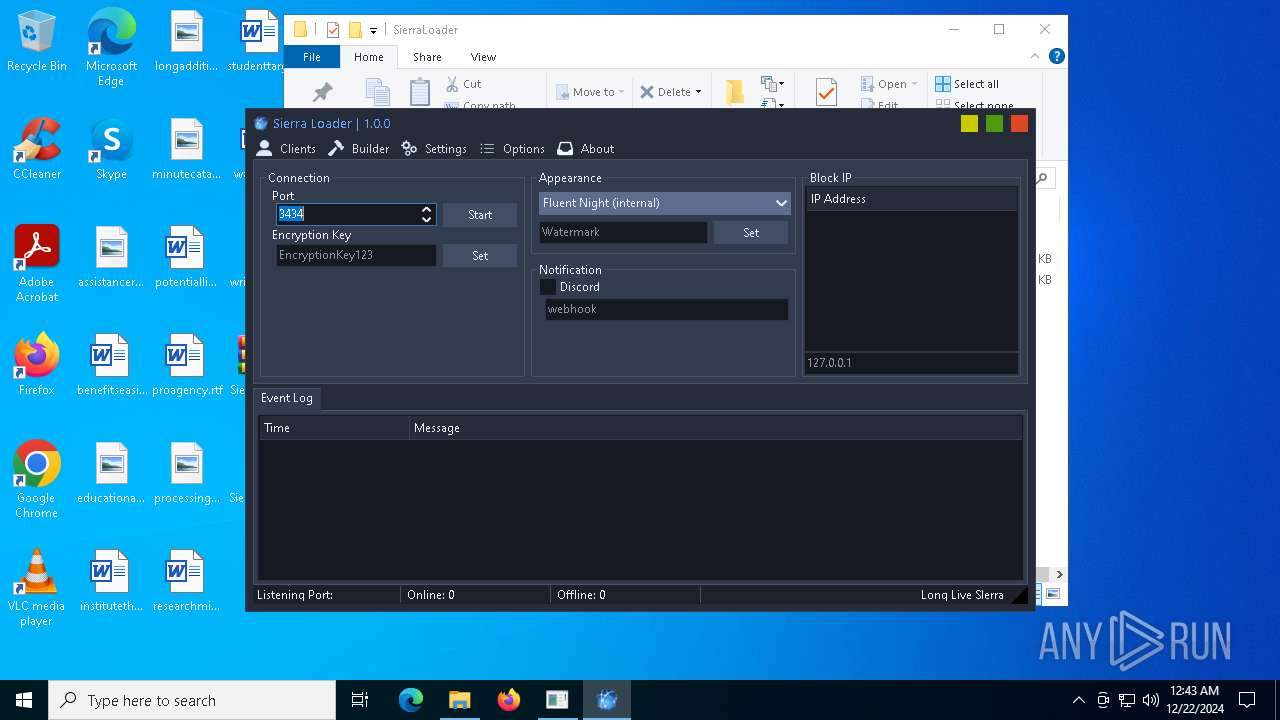
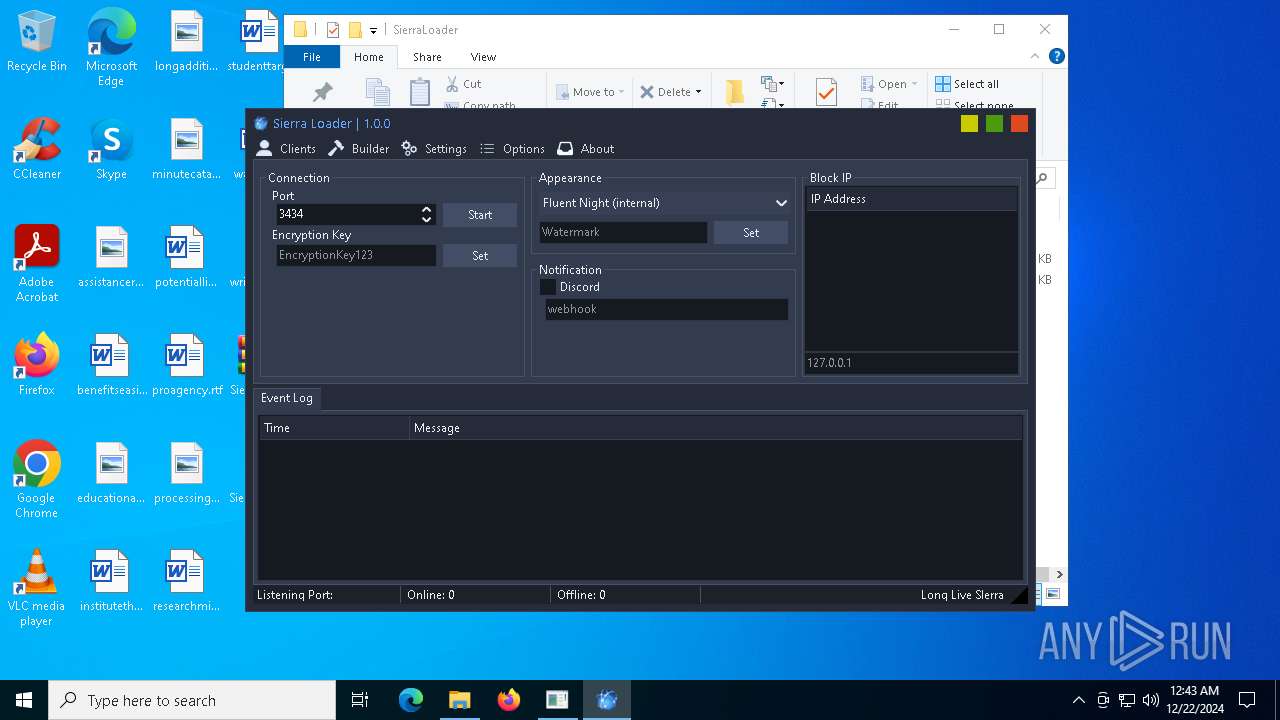
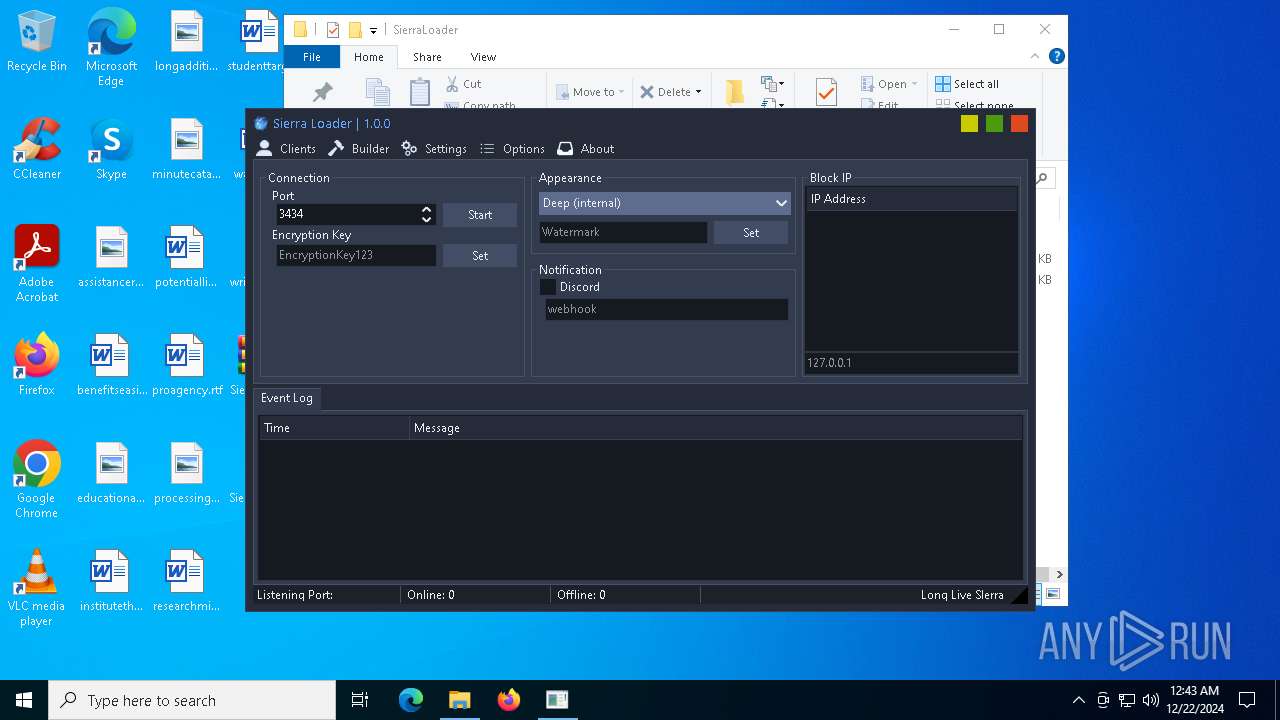
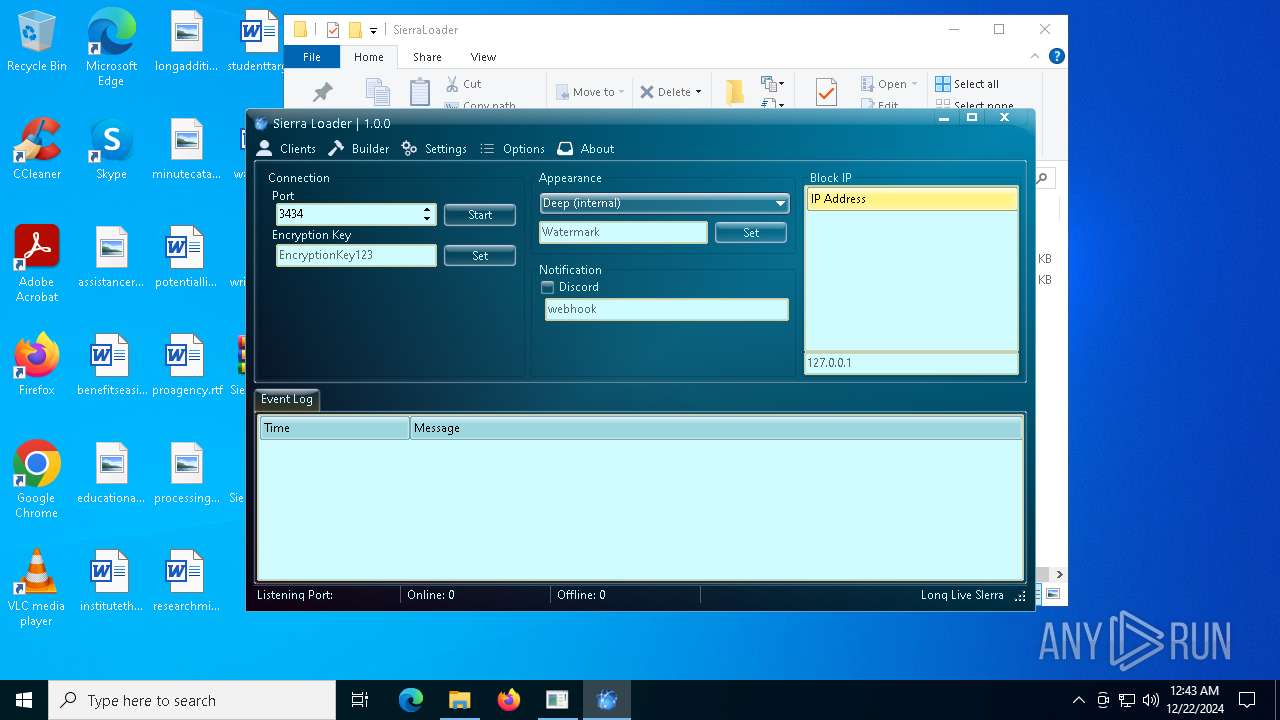
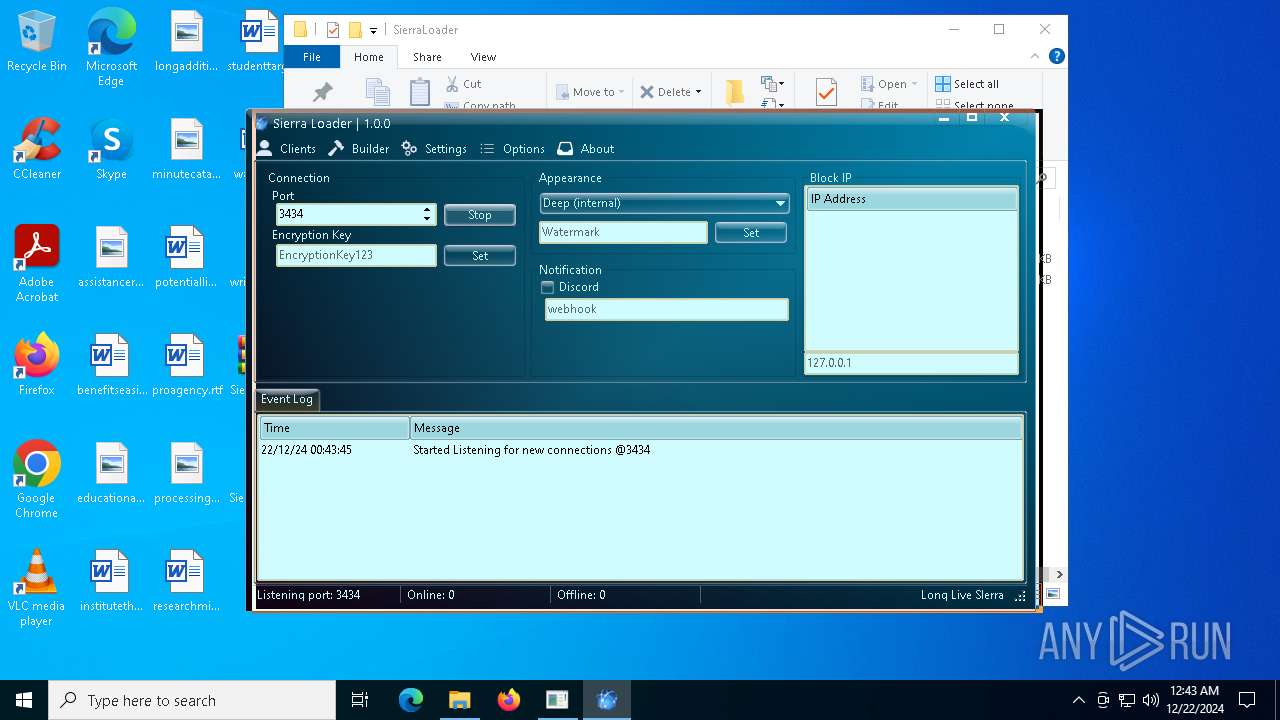
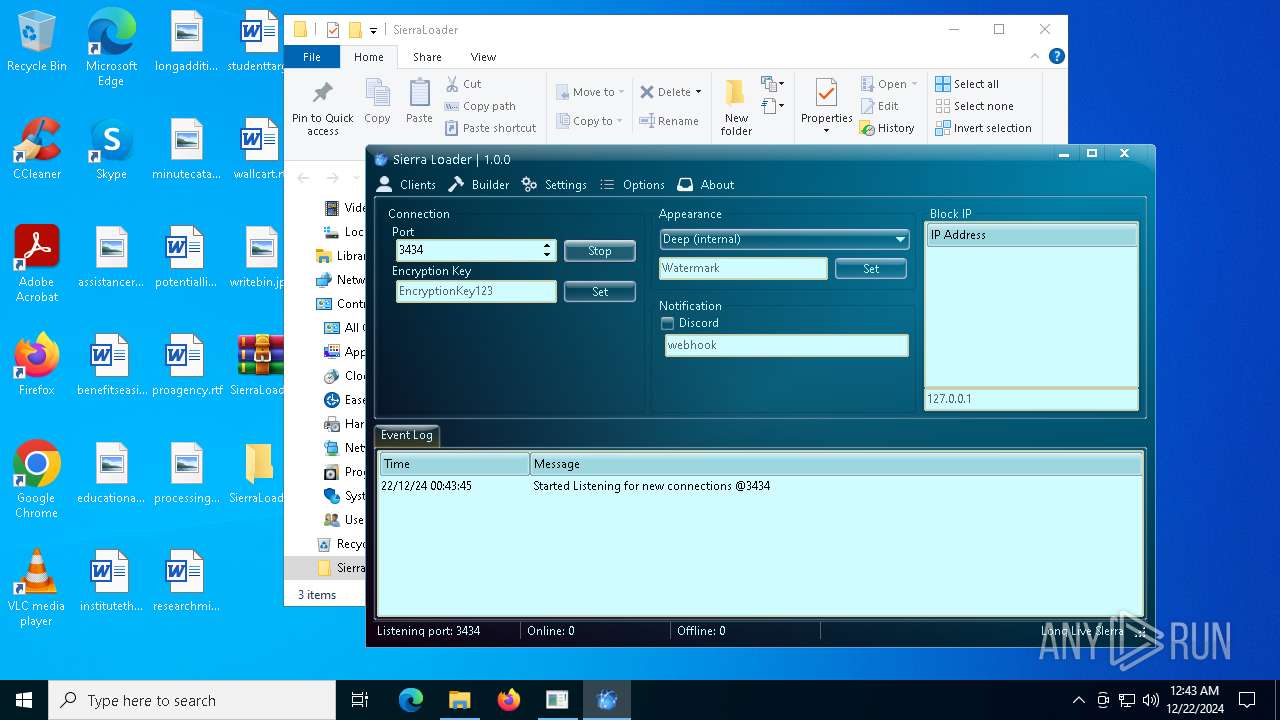
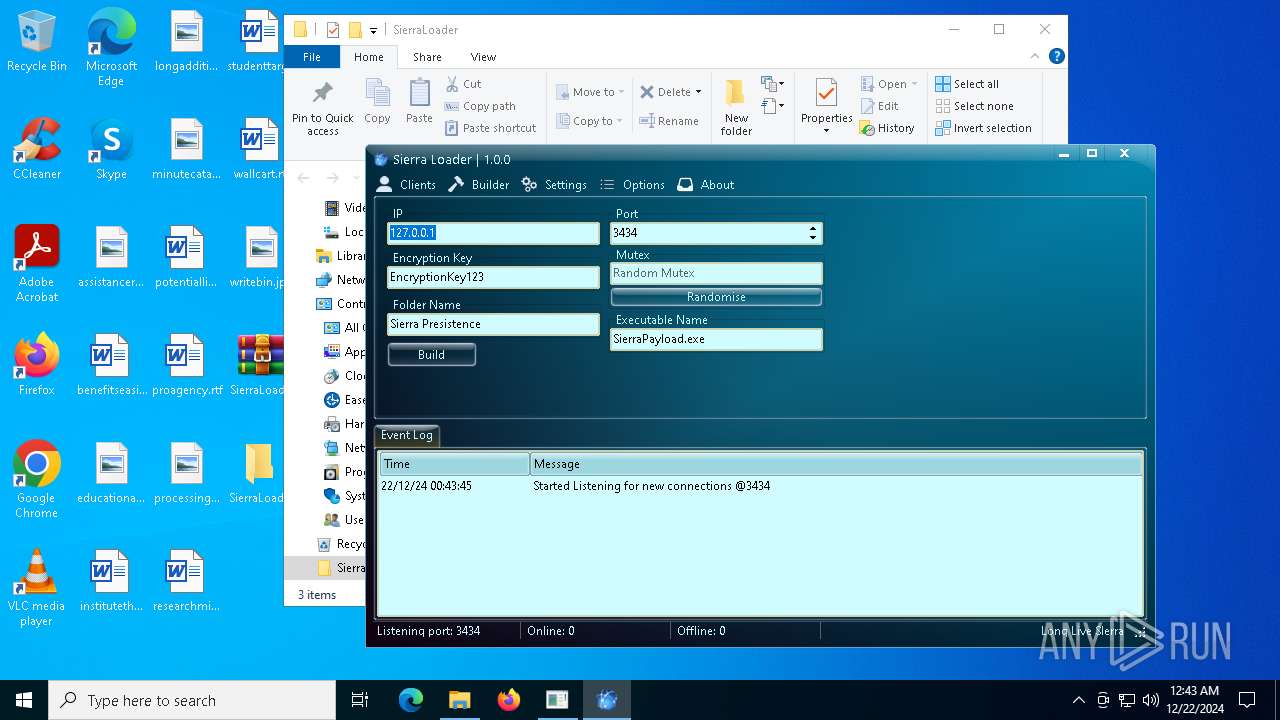
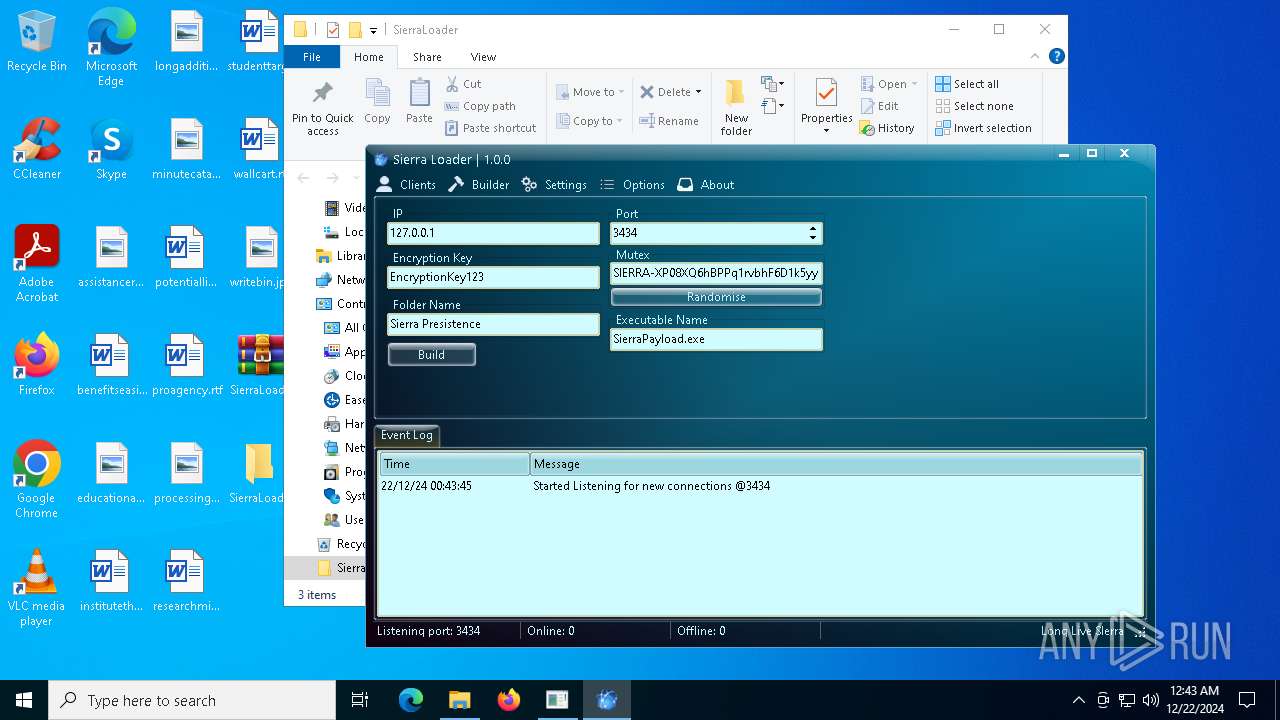
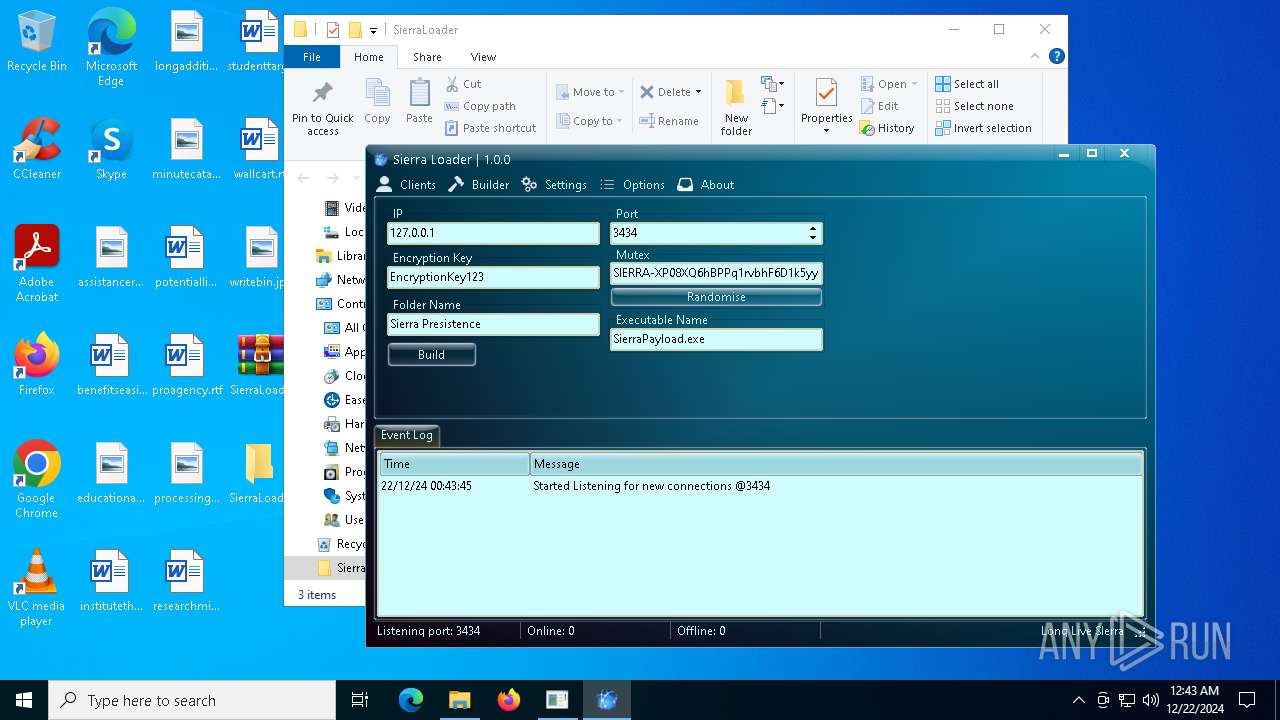
- SierraLoader.exe (PID: 3988)
Starts CMD.EXE for commands execution
- Daemon.exe (PID: 6224)
Executable content was dropped or overwritten
- SierraLoader.exe (PID: 3988)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 3928)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7148)
- SierraLoader.exe (PID: 3988)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7148)
Manual execution by a user
- SierraLoader.exe (PID: 3988)
- WinRAR.exe (PID: 7148)
- Daemon.exe (PID: 6224)
- notepad.exe (PID: 6412)
The process uses the downloaded file
- WinRAR.exe (PID: 7148)
Sends debugging messages
- SierraLoader.exe (PID: 3988)
Checks supported languages
- SierraLoader.exe (PID: 3988)
- Daemon.exe (PID: 6224)
Reads the computer name
- SierraLoader.exe (PID: 3988)
- Daemon.exe (PID: 6224)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6668)
- notepad.exe (PID: 6412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:08:20 21:55:12+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 114688 |
| InitializedDataSize: | 208896 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b13 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
136
Monitored processes
10
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | runas.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
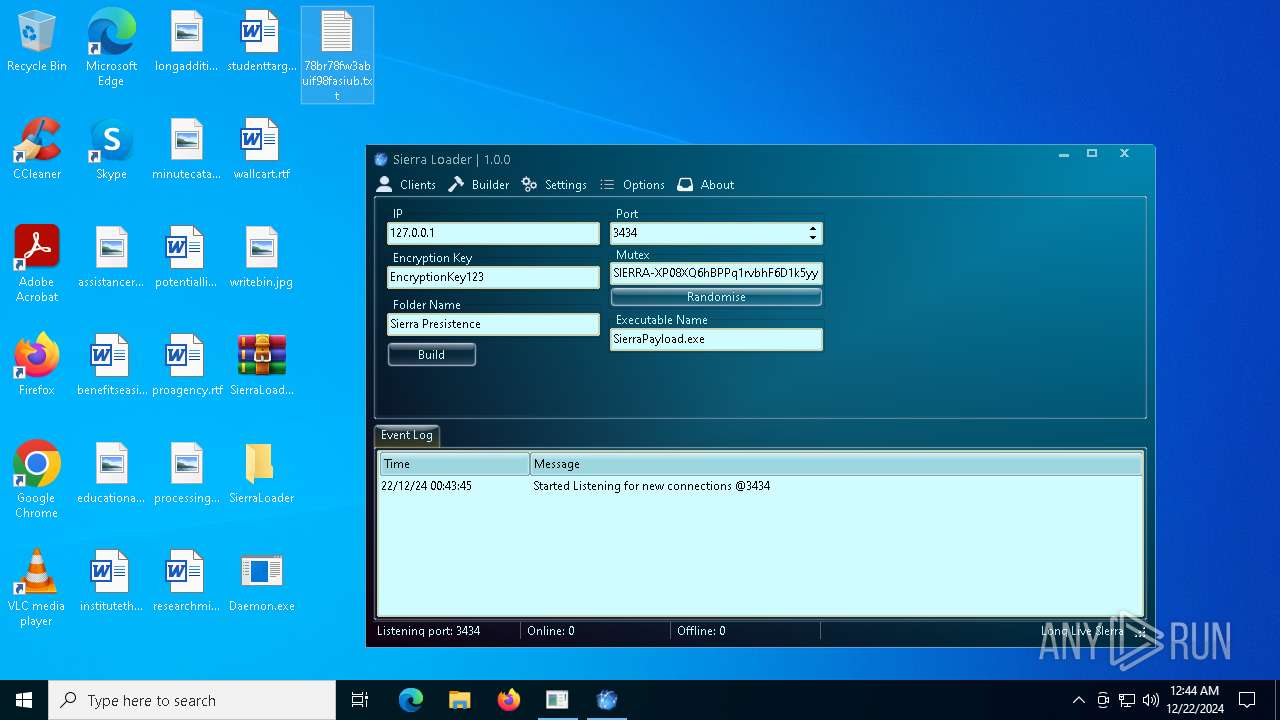
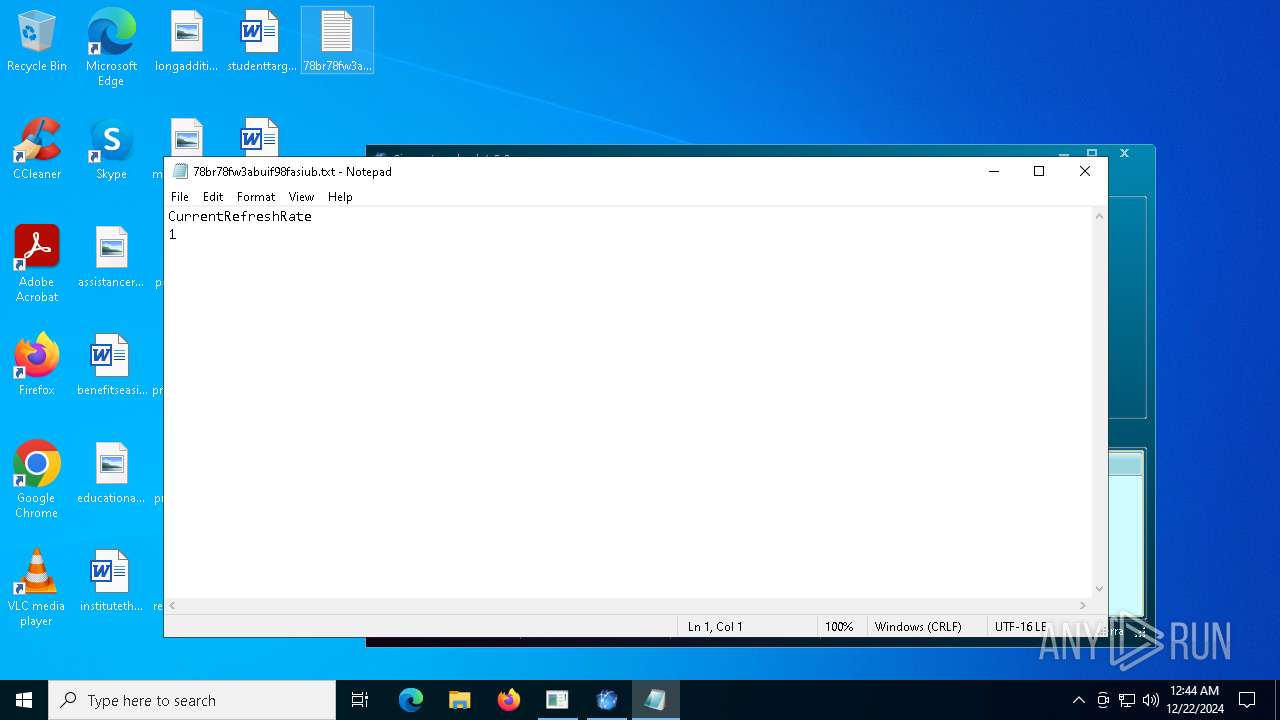
| 3928 | cmd.exe /C wmic path Win32_VideoController get CurrentRefreshRate > "C:\Users\admin\Desktop\78br78fw3abuif98fasiub.txt" | C:\Windows\SysWOW64\cmd.exe | — | Daemon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3952 | "C:\Windows\System32\runas.exe" /user:administrator C:\Sulfoxide.exe | C:\Windows\System32\runas.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
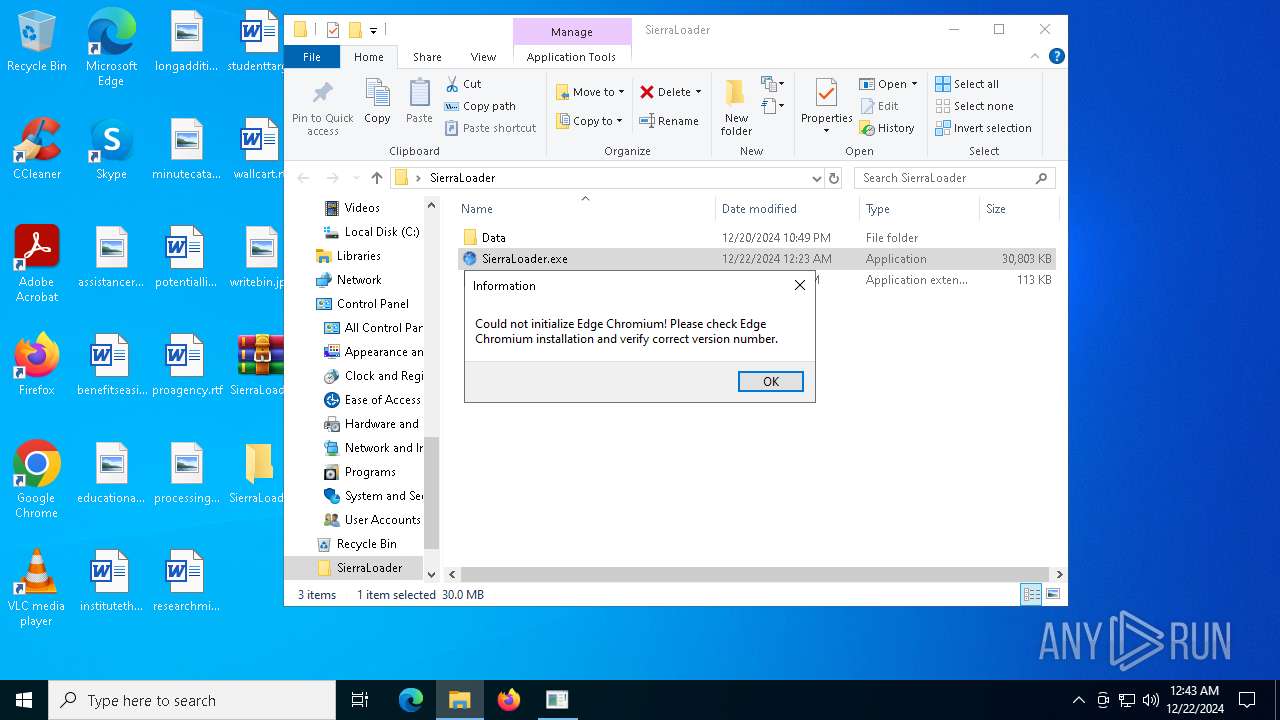
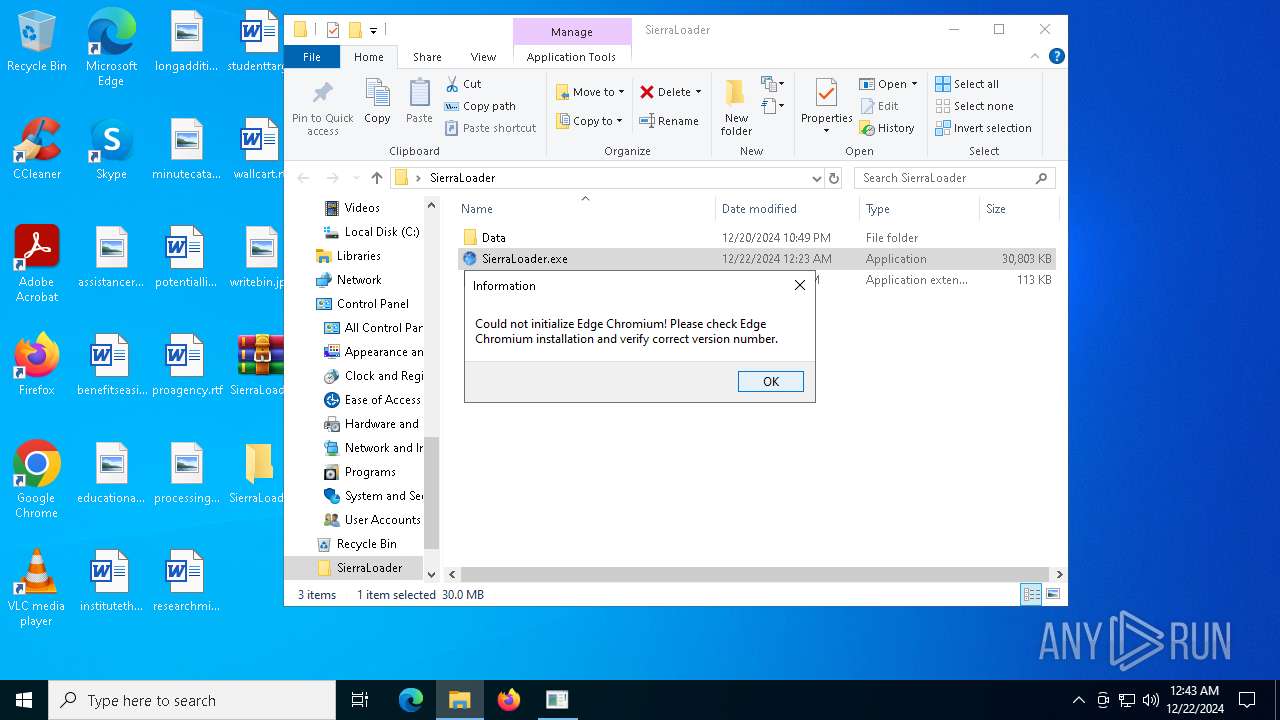
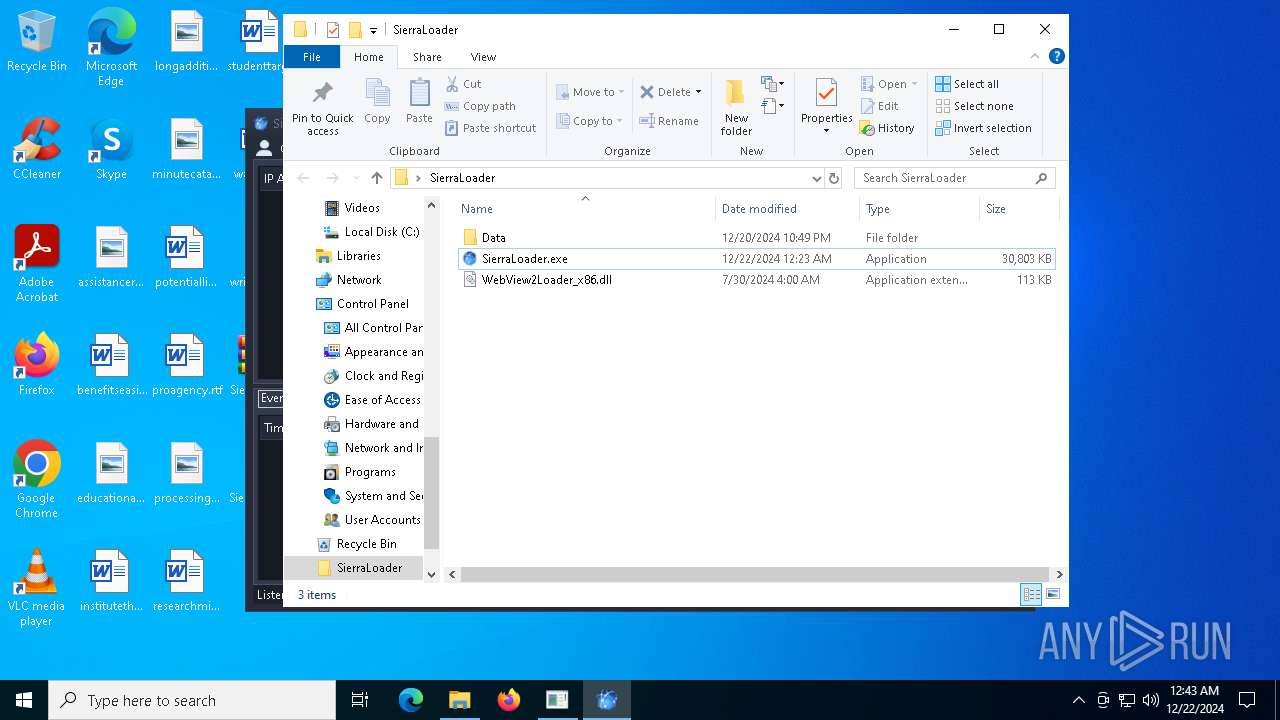
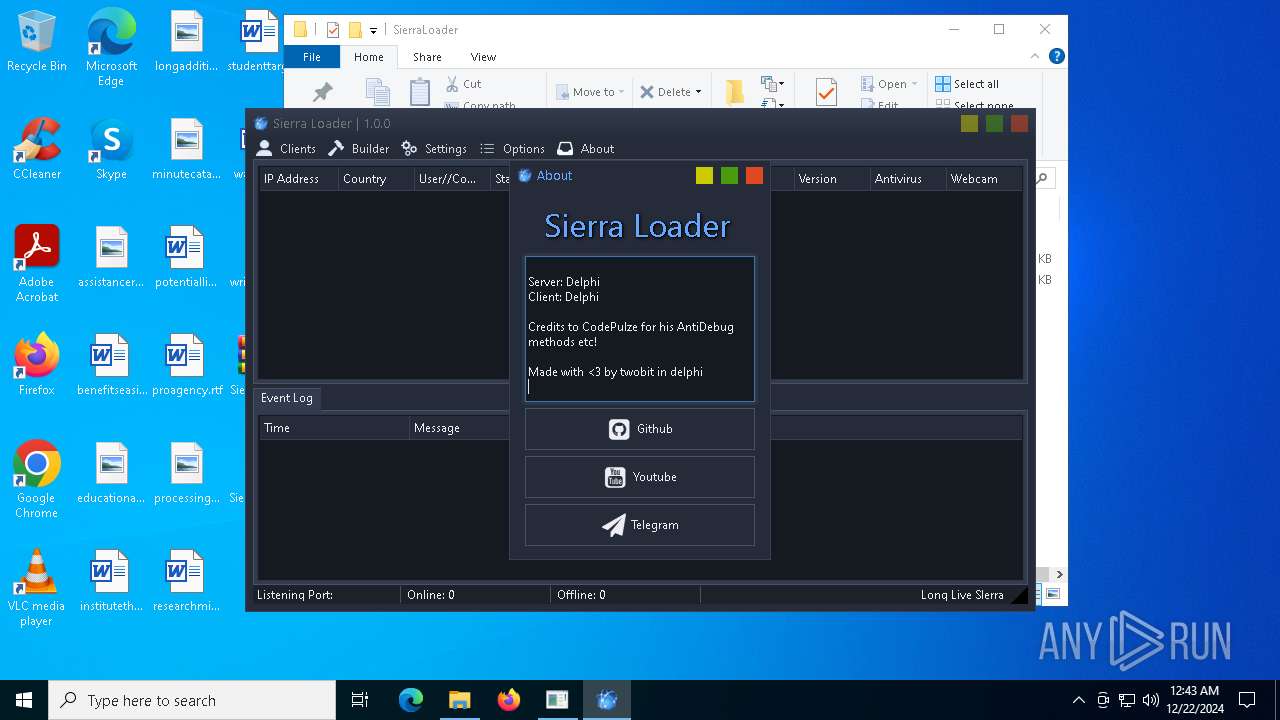
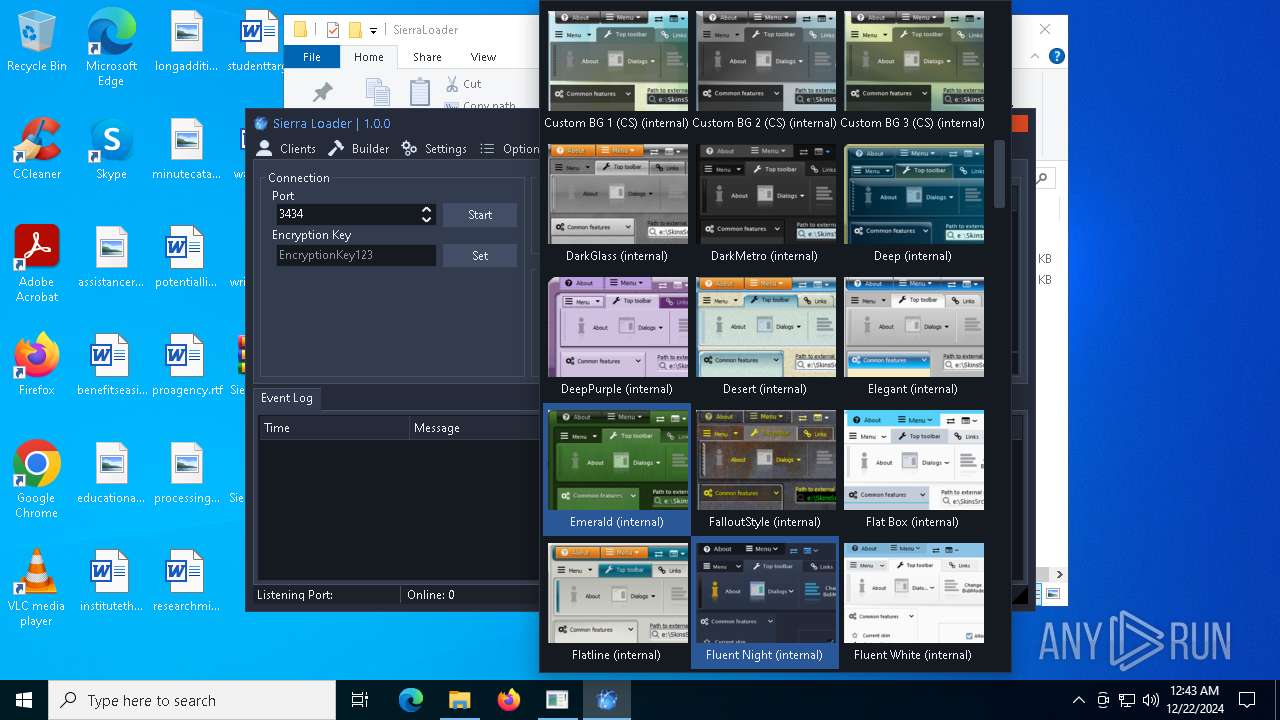
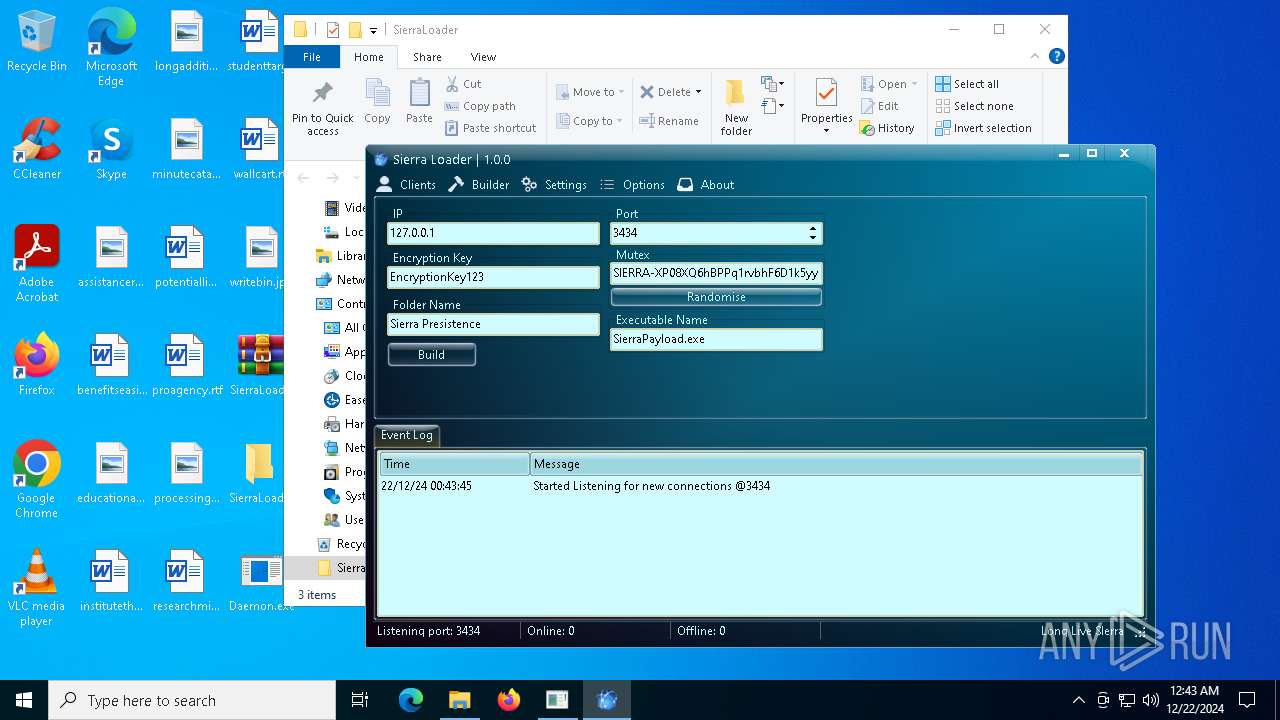
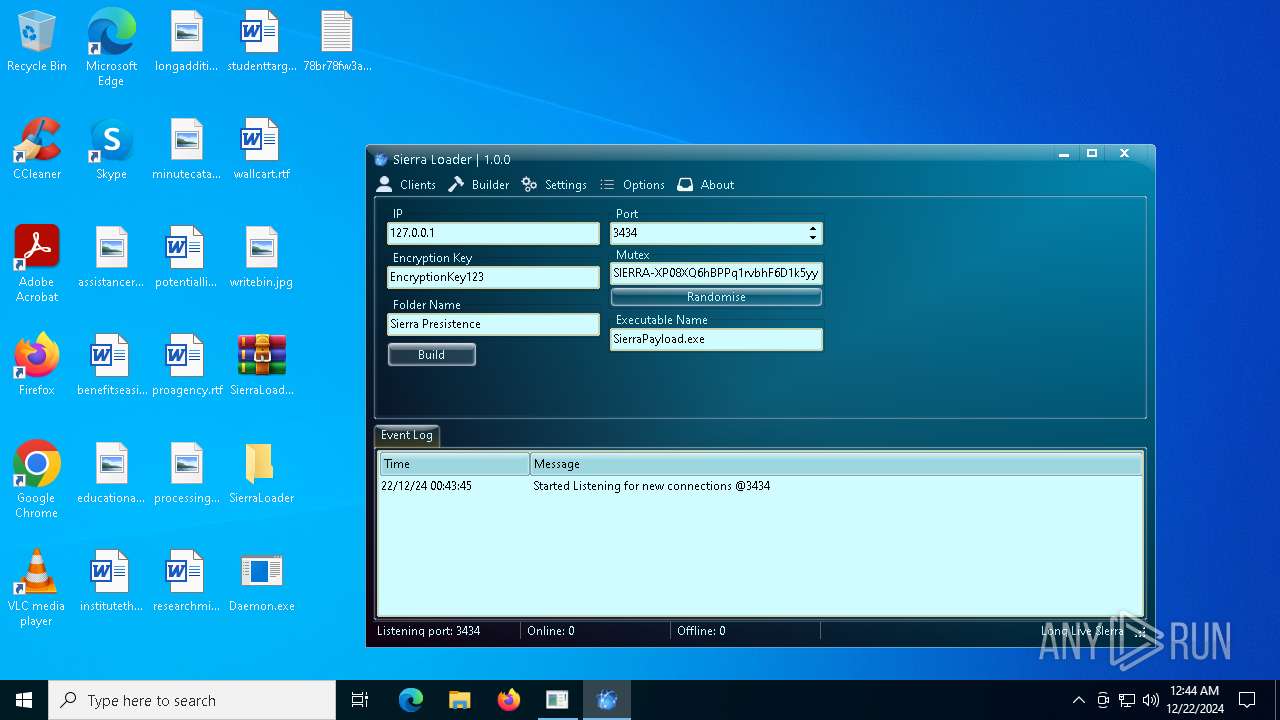
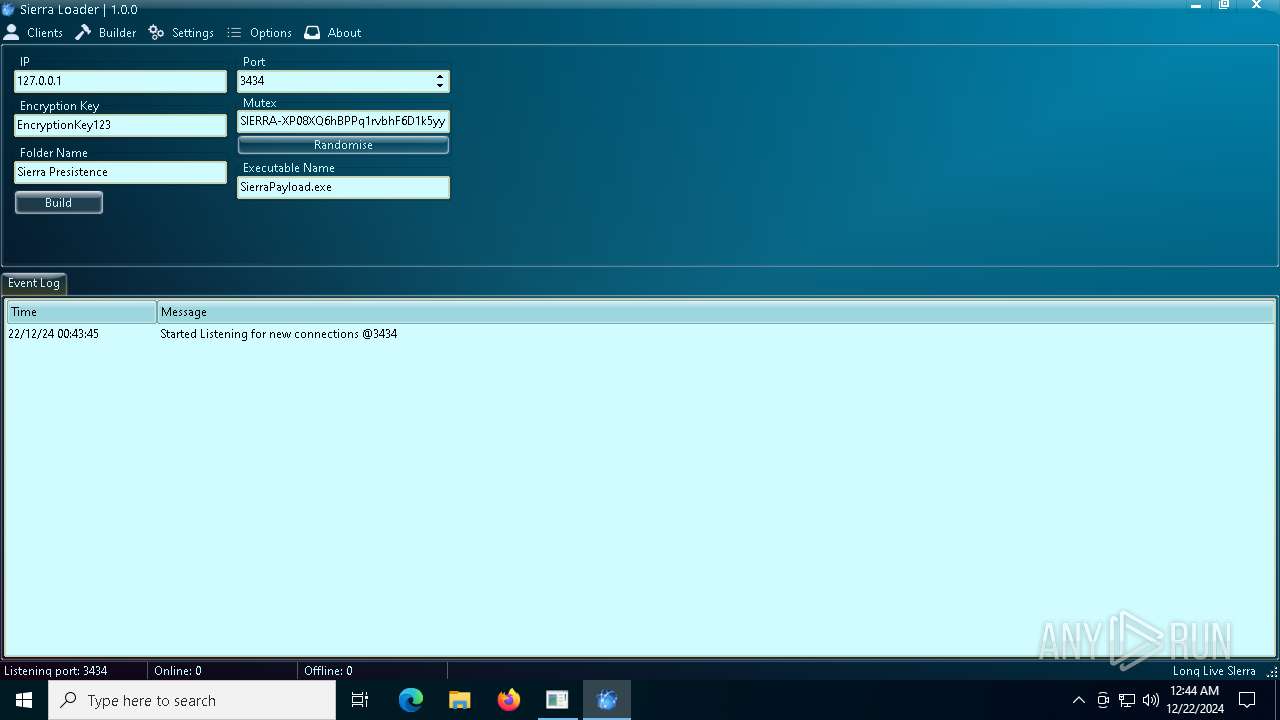
| 3988 | "C:\Users\admin\Desktop\SierraLoader\SierraLoader.exe" | C:\Users\admin\Desktop\SierraLoader\SierraLoader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: SierraLoader Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5588 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
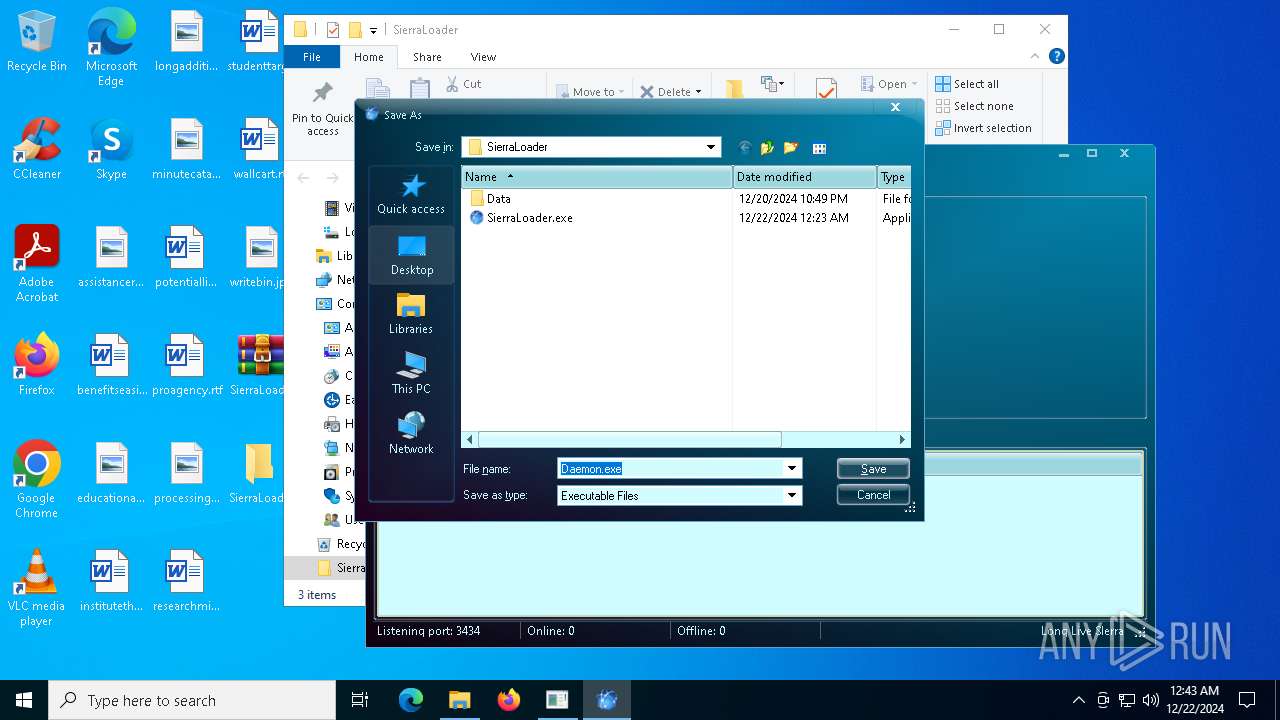
| 6224 | "C:\Users\admin\Desktop\Daemon.exe" | C:\Users\admin\Desktop\Daemon.exe | — | explorer.exe | |||||||||||
User: admin Company: Sierra Integrity Level: MEDIUM Description: Daemon Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6412 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\78br78fw3abuif98fasiub.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6668 | wmic path Win32_VideoController get CurrentRefreshRate | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
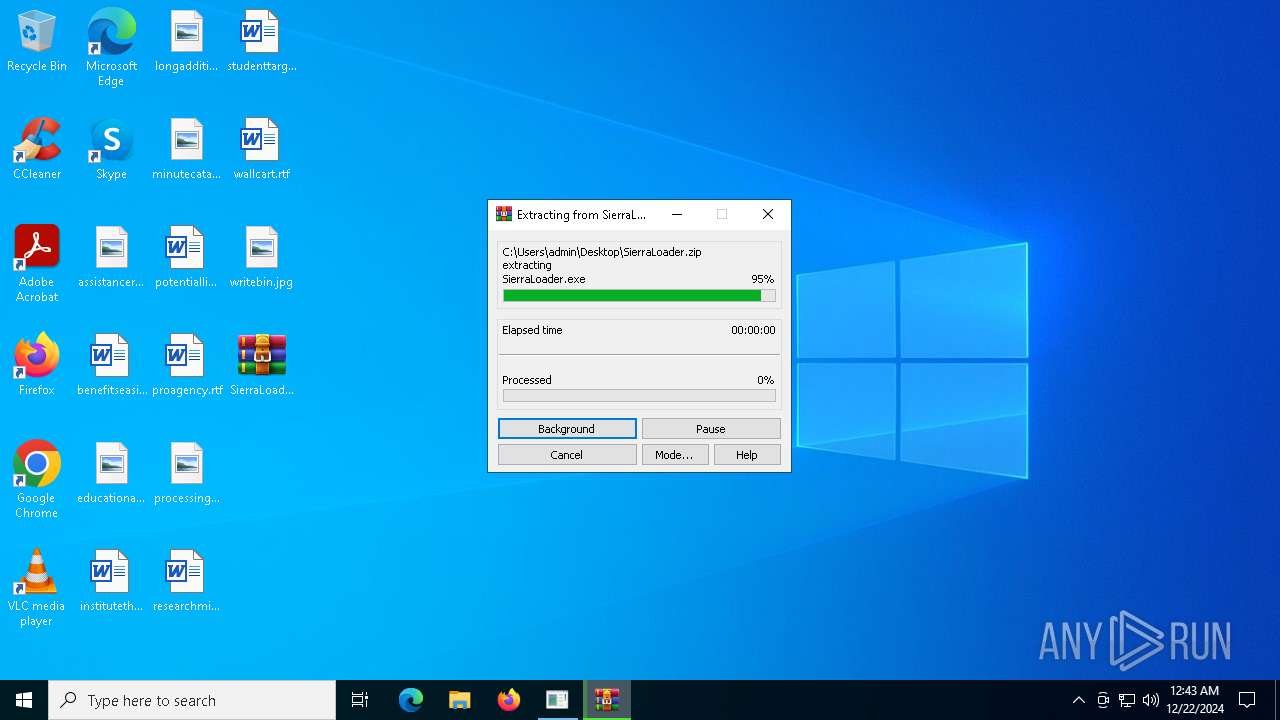
| 7148 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\SierraLoader.zip" C:\Users\admin\Desktop\SierraLoader\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
3 254
Read events
3 181
Write events
70
Delete events
3
Modification events
| (PID) Process: | (7148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3988) SierraLoader.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3988) SierraLoader.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 04000000110000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (3988) SierraLoader.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\1 |
| Operation: | write | Name: | 3 |
Value: 62003100000000009659660510005349455252417E3100004A0009000400EFBE96596505965966052E000000F96300000000230000000000000000000000000000002B55F1005300690065007200720061004C006F006100640065007200000018000000 | |||
| (PID) Process: | (3988) SierraLoader.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\1\3 |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (3988) SierraLoader.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4\1 |
| Operation: | write | Name: | MRUListEx |
Value: 03000000020000000100000000000000FFFFFFFF | |||
| (PID) Process: | (3988) SierraLoader.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
Executable files
5
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3928 | cmd.exe | C:\Users\admin\Desktop\78br78fw3abuif98fasiub.txt | text | |
MD5:A8963EE9E5A34C68EECF90E98210B4FF | SHA256:2DB0D28B0225CE46E5B971796F6B39A3677B88C95EC9DA376C357A528D6F624A | |||
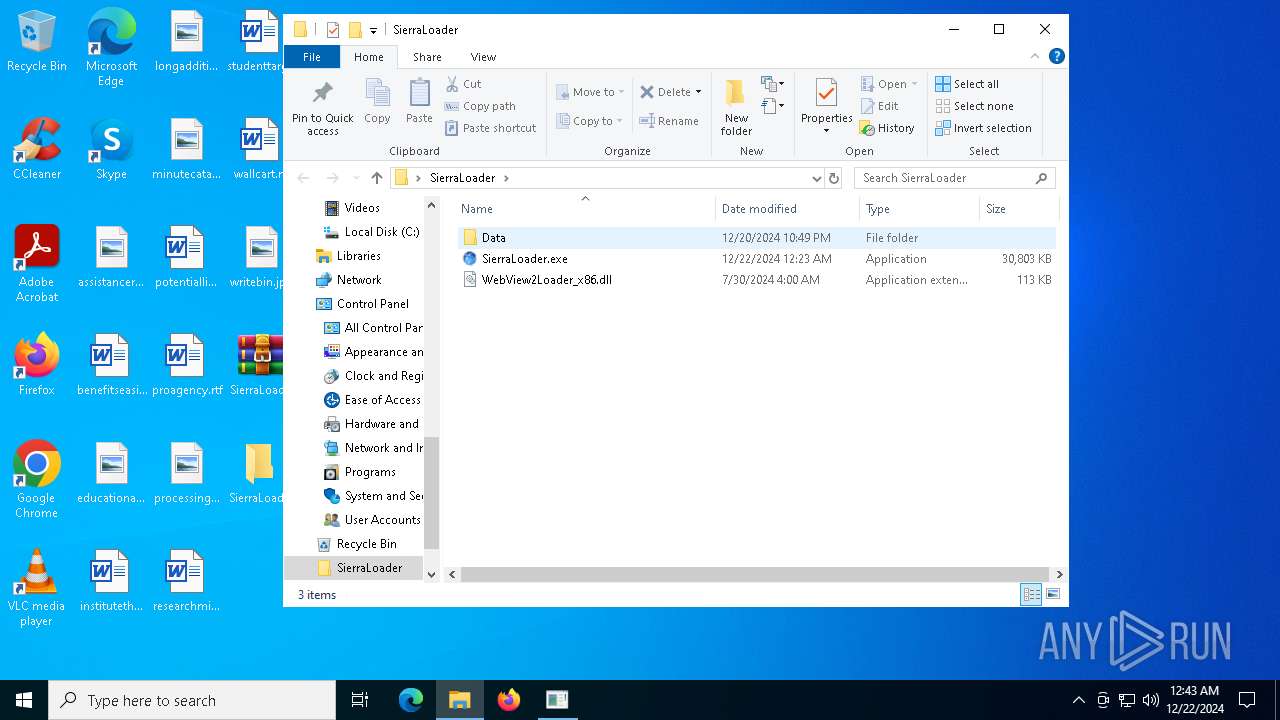
| 7148 | WinRAR.exe | C:\Users\admin\Desktop\SierraLoader\WebView2Loader_x86.dll | executable | |
MD5:6F41749064441B46F3C8AEA1CA5FC63F | SHA256:21294B3BD086EFE5C313CE875716C46B263BC2641B5E7F90961198FE2DCEABDB | |||
| 7148 | WinRAR.exe | C:\Users\admin\Desktop\SierraLoader\SierraLoader.exe | executable | |
MD5:C7E46A85B9987FAC710D6F634ADD0435 | SHA256:A86B9B3D628FA9C995438783F778B4639B49D6BE353672E61842A5201A3D97F3 | |||
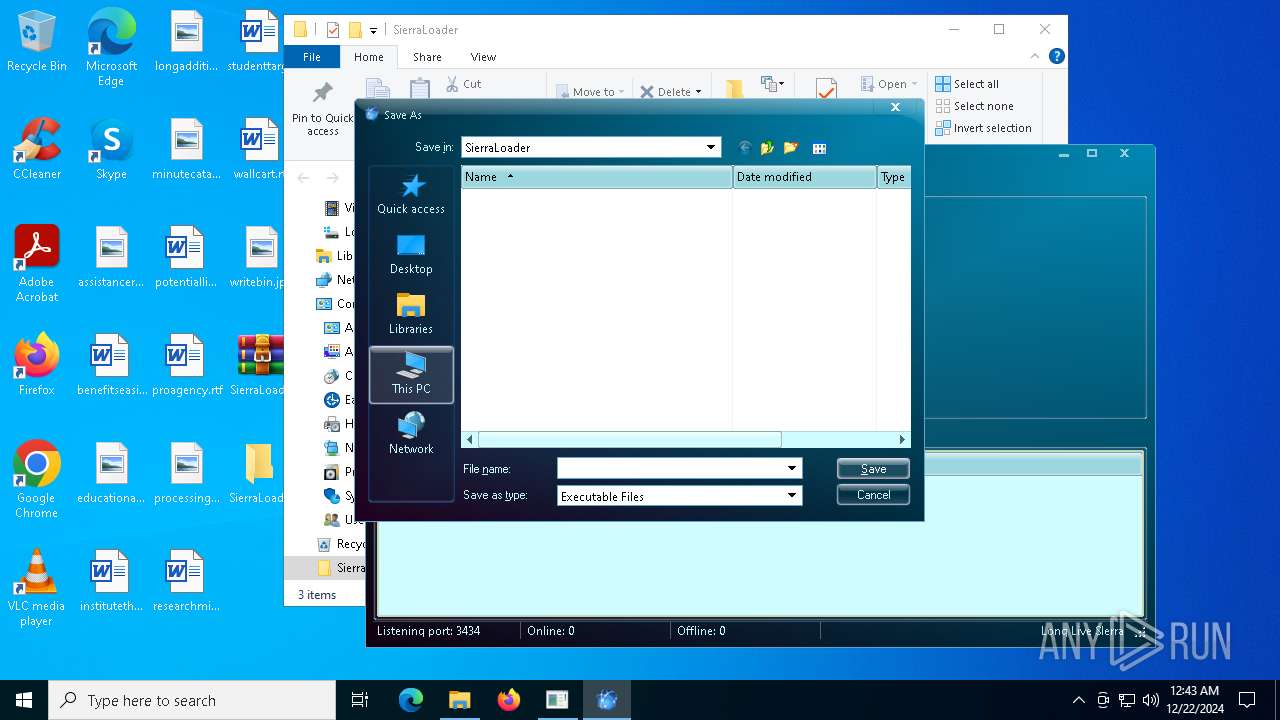
| 3988 | SierraLoader.exe | C:\Users\admin\Desktop\Daemon.exe | executable | |
MD5:5D4CDF5F2F6D2F056D4895A42EA24289 | SHA256:2FFB46F716E11DC434D5CCC410EF3CBBDF749E70F265F009F3F13576F9105D31 | |||
| 3988 | SierraLoader.exe | C:\Users\admin\Desktop\RCXE0BA.tmp | executable | |
MD5:9C73B864F977E88B371EFC55413ED0FC | SHA256:AE58013412C0D37F8BCB75E2F4E04ABD7258364B5D175BCE6793A09C849D8CA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
32
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.21.20.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6940 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
6940 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
6164 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4536 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.21.20.133:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.21.110.146:443 | www.bing.com | AKAMAI-AS | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
SierraLoader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
SierraLoader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
SierraLoader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
SierraLoader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|