| File name: | 2e6911c8671457dbb08a047264064f28d3ecb042.exe |
| Full analysis: | https://app.any.run/tasks/fa5481a1-431a-4f23-86e4-49de06df97fa |
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2019, 08:32:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D71390EDBA889A8BD1D410AE8F61FCC4 |
| SHA1: | 2E6911C8671457DBB08A047264064F28D3ECB042 |
| SHA256: | 0B4BD88B3D6042D11C39208E96AAC3B6BE02067F7B225F0EF1C5B35D8CF413D1 |
| SSDEEP: | 49152:I7koKj34SeUatpcpY5SHfDoEtxM2CEqZsP6LkJTUTLjnbIS:I7koKbJLoE7SkJ6jbT |
MALICIOUS
Application was dropped or rewritten from another process
- cookieman.exe (PID: 3676)
SUSPICIOUS
Reads the cookies of Mozilla Firefox
- 2e6911c8671457dbb08a047264064f28d3ecb042.exe (PID: 2516)
Executable content was dropped or overwritten
- 2e6911c8671457dbb08a047264064f28d3ecb042.exe (PID: 2516)
Reads the cookies of Google Chrome
- 2e6911c8671457dbb08a047264064f28d3ecb042.exe (PID: 2516)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:08 22:30:51+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 1081856 |
| InitializedDataSize: | 519168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe8ec |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.128.0.0 |
| ProductVersionNumber: | 2.128.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | InstallX, LLC |
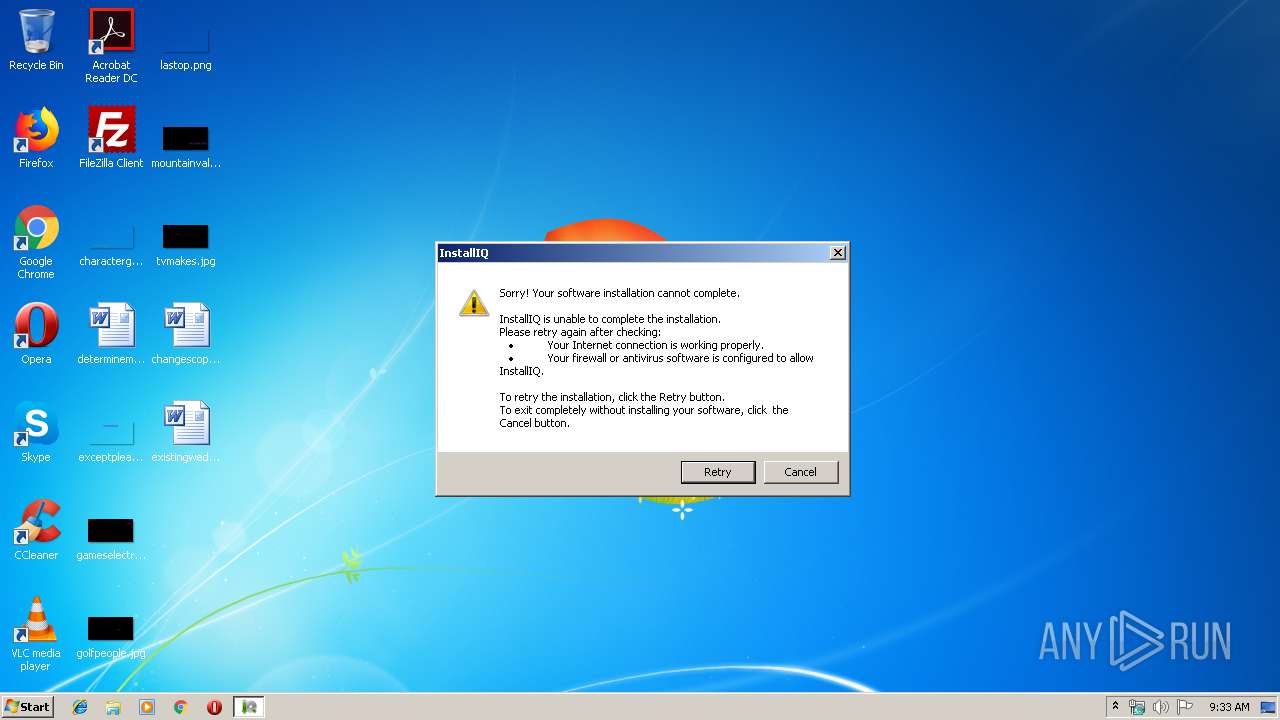
| FileDescription: | InstallIQ Installation Utility |
| FileVersion: | 2.128.0.0 |
| InternalName: | InstallIQ.exe |
| LegalCopyright: | Copyright ©2013 InstallX, LLC. All rights reserved. |
| OriginalFileName: | InstallIQ.exe |
| ProductName: | InstallIQ Installation Utility |
| ProductVersion: | 2.128.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Apr-2013 20:30:51 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | InstallX, LLC |
| FileDescription: | InstallIQ Installation Utility |
| FileVersion: | 2.128.0.0 |
| InternalName: | InstallIQ.exe |
| LegalCopyright: | Copyright ©2013 InstallX, LLC. All rights reserved. |
| OriginalFilename: | InstallIQ.exe |
| ProductName: | InstallIQ Installation Utility |
| ProductVersion: | 2.128.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 40 |
| Time date stamp: | 08-Apr-2013 20:30:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00024973 | 0x00024A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.72771 |
.text-co\x89m\x01 | 0x00026000 | 0x00016D89 | 0x00016E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43603 |
.text-co\xcb\x8e\x01 | 0x0003D000 | 0x00018ECB | 0x00019000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.35277 |
.text-co\x10\xa3 | 0x00056000 | 0x0000A310 | 0x0000A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.30603 |
.text-co\x97l | 0x00061000 | 0x00006C97 | 0x00006E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31245 |
.text-co\xf74 | 0x00068000 | 0x000034F7 | 0x00003600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.27673 |
.text-co\x94\xe2\x03 | 0x0006C000 | 0x0003E294 | 0x0003E400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6023 |
.text-co\xa1M | 0x000AB000 | 0x00004DA1 | 0x00004E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31333 |
.text-co\xef4 | 0x000B0000 | 0x000034EF | 0x00003600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.28877 |
.text-co\x16_ | 0x000B4000 | 0x00005F16 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.26192 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26074 | 951 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.41351 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.62084 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.7081 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.14122 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.34185 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.26148 | 2664 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 3.2222 | 3462 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 3.13638 | 696 | Latin 1 / Western European | English - United States | RT_STRING |
101 | 2.81158 | 118 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
PSAPI.DLL |
RPCRT4.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2516 | "C:\Users\admin\AppData\Local\Temp\2e6911c8671457dbb08a047264064f28d3ecb042.exe" /wrapper /dir="C:\Users\admin\AppData\Local\Temp\pkg_8203b2fb0" /pproc="Explorer.EXE" | C:\Users\admin\AppData\Local\Temp\2e6911c8671457dbb08a047264064f28d3ecb042.exe | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | ||||||||||||
User: admin Company: InstallX, LLC Integrity Level: HIGH Description: InstallIQ Installation Utility Exit code: 0 Version: 2.128.0.0 Modules
| |||||||||||||||
| 3088 | "C:\Users\admin\AppData\Local\Temp\2e6911c8671457dbb08a047264064f28d3ecb042.exe" | C:\Users\admin\AppData\Local\Temp\2e6911c8671457dbb08a047264064f28d3ecb042.exe | — | explorer.exe | |||||||||||
User: admin Company: InstallX, LLC Integrity Level: MEDIUM Description: InstallIQ Installation Utility Exit code: 3221226540 Version: 2.128.0.0 Modules
| |||||||||||||||
| 3644 | "C:\Users\admin\AppData\Local\Temp\2e6911c8671457dbb08a047264064f28d3ecb042.exe" | C:\Users\admin\AppData\Local\Temp\2e6911c8671457dbb08a047264064f28d3ecb042.exe | explorer.exe | ||||||||||||
User: admin Company: InstallX, LLC Integrity Level: HIGH Description: InstallIQ Installation Utility Exit code: 0 Version: 2.128.0.0 Modules
| |||||||||||||||
| 3676 | "C:\Users\admin\AppData\LocalLow\cookieman.exe" /mode=read installiq.com | C:\Users\admin\AppData\LocalLow\cookieman.exe | — | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | |||||||||||
User: admin Integrity Level: LOW Exit code: 0 Modules
| |||||||||||||||
Total events
71
Read events
50
Write events
19
Delete events
2
Modification events
| (PID) Process: | (2516) 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\InstallIQ |
| Operation: | write | Name: | test |
Value: 1 | |||
| (PID) Process: | (2516) 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\InstallIQ |
| Operation: | delete value | Name: | test |
Value: 1 | |||
| (PID) Process: | (2516) 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\InstallIQ |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2516) 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2e6911c8671457dbb08a047264064f28d3ecb042_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2516) 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2e6911c8671457dbb08a047264064f28d3ecb042_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2516) 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2e6911c8671457dbb08a047264064f28d3ecb042_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2516) 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2e6911c8671457dbb08a047264064f28d3ecb042_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2516) 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2e6911c8671457dbb08a047264064f28d3ecb042_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2516) 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2e6911c8671457dbb08a047264064f28d3ecb042_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2516) 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\2e6911c8671457dbb08a047264064f28d3ecb042_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3676 | cookieman.exe | C:\Users\admin\AppData\LocalLow\cookie.ini | — | |
MD5:— | SHA256:— | |||
| 2516 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | C:\Users\admin\AppData\Local\Temp\ccd4E1A.tmp | — | |
MD5:— | SHA256:— | |||
| 2516 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | C:\Users\admin\AppData\Local\Temp\ccd4E1A.tmp-shm | — | |
MD5:— | SHA256:— | |||
| 2516 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | C:\Users\admin\AppData\Local\Temp\ccd4E2A.tmp | — | |
MD5:— | SHA256:— | |||
| 3644 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | C:\Users\admin\AppData\Local\Temp\pkg_8203b2fb0\stub.log | text | |
MD5:— | SHA256:— | |||
| 2516 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | C:\Users\admin\AppData\LocalLow\cookieman.exe | executable | |
MD5:— | SHA256:— | |||
| 3644 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | C:\Users\admin\AppData\Local\Temp\pkg_8203b2fb0\timings.txt | text | |
MD5:— | SHA256:— | |||
| 2516 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | C:\Users\admin\AppData\Local\Temp\pkg_8203b2fb0\detectionrules.dat | html | |
MD5:— | SHA256:— | |||
| 3644 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | C:\Users\admin\AppData\Local\Temp\pkg_8203b2fb0\autorun.txt | ini | |
MD5:— | SHA256:— | |||
| 3644 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | C:\Users\admin\AppData\Local\Temp\pkg_8203b2fb0\wrapper.xml | text | |
MD5:44601E00FF712607D2A0B64DE786D843 | SHA256:424EF303F88BCD0C6AF1858CDACC0E3225545957FCB6C49110E39FF39B26B7F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2516 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | GET | 302 | 37.48.65.145:80 | http://dl.installiq.com/api/detectionrequest.aspx?keyid=1&shortname=freefileviewer&langid=0x0409 | NL | text | 11 b | malicious |
2516 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | GET | 200 | 208.91.196.145:80 | http://ww1.installiq.com/ | VG | html | 1.83 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 37.48.65.145:80 | dl.installiq.com | LeaseWeb Netherlands B.V. | NL | malicious |
2516 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | 208.91.196.145:80 | ww1.installiq.com | Confluence Networks Inc | VG | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.installiq.com |
| malicious |
ww1.installiq.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2516 | 2e6911c8671457dbb08a047264064f28d3ecb042.exe | Potential Corporate Privacy Violation | ET POLICY InstallIQ Updater Software request |