| File name: | finfisher.2.exe |
| Full analysis: | https://app.any.run/tasks/3cb96b15-b8cc-4b64-8ae0-15d81ec8972f |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 04:57:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1D8EA40A41988B9C3DB9EFF5FCE3ABE5 |
| SHA1: | 58EFD5F3994A4C3A42590B1C24032B89C4ECEDDA |
| SHA256: | 0B465877A998A993A64A146C80BEAEA2ADF8E854644709706C6173A853EC8DBA |
| SSDEEP: | 12288:Y1kfgjdkA/+x8NfO3Menn/O1XxoAPKrVNKpHyR4NBnpNhi3BSv2:zgjT/+x8NAMwnGBxoVxNuH3uI2 |
MALICIOUS
Application was dropped or rewritten from another process
- finfisher.2.exe (PID: 3204)
Changes the autorun value in the registry
- explorer.exe (PID: 124)
Loads dropped or rewritten executable
- finfisher.2.exe (PID: 2096)
- DllHost.exe (PID: 2272)
- ctfmon.exe (PID: 304)
- explorer.exe (PID: 124)
- SearchProtocolHost.exe (PID: 4060)
SUSPICIOUS
Executable content was dropped or overwritten
- finfisher.2.exe (PID: 2096)
- finfisher.2.exe (PID: 3484)
- explorer.exe (PID: 124)
Starts Internet Explorer
- explorer.exe (PID: 124)
Executed via COM
- DllHost.exe (PID: 2272)
Creates files in the user directory
- explorer.exe (PID: 124)
INFO
Manual execution by user
- iexplore.exe (PID: 1024)
Reads Microsoft Office registry keys
- SearchProtocolHost.exe (PID: 4060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:08:05 11:59:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 11264 |
| InitializedDataSize: | 622080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x29b9 |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Aug-2010 09:59:56 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 05-Aug-2010 09:59:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00002A70 | 0x00002C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.146 |
.data | 0x00004000 | 0x00000C84 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.7986 |
.rsrc | 0x00005000 | 0x000978A0 | 0x00097A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.97308 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.99764 | 480256 | Latin 1 / Western European | English - United States | RT_DIALOG |
2 | 7.99647 | 56139 | Latin 1 / Western European | English - United States | RT_DIALOG |
3 | 0.811278 | 4 | Latin 1 / Western European | English - United States | RT_DIALOG |
101 | 3.29705 | 146 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
710 | 3.62685 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
711 | 3.76742 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
712 | 3.05919 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
713 | 5.6234 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
714 | 5.90005 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
715 | 3.80536 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
ntdll.dll |
Total processes
42
Monitored processes
9
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Temp\\TMPB894F78F\finfisher.2.exe" | C:\Users\admin\AppData\Local\Temp\TMPB894F78F\finfisher.2.exe | finfisher.2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2272 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3204 | "C:\Users\admin\AppData\Local\Temp\finfisher.2.exe" | C:\Users\admin\AppData\Local\Temp\finfisher.2.exe | — | finfisher.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Service Provider Exit code: 0 Version: 5.3.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3484 | "C:\Users\admin\AppData\Local\Temp\finfisher.2.exe" | C:\Users\admin\AppData\Local\Temp\finfisher.2.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Service Provider Exit code: 0 Version: 5.3.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3864 | explorer.exe | C:\Windows\explorer.exe | — | finfisher.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4060 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10009_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10009 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
516
Read events
495
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2096) finfisher.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2096) finfisher.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2096) finfisher.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {FFE2A43C-56B9-4BF5-9A79-CC6D4285608A} {00000122-0000-0000-C000-000000000046} 0xFFFF |
Value: 010000000000000000B0A548253DD501 | |||
| (PID) Process: | (2096) finfisher.2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: finfisher.2.exe | |||
| (PID) Process: | (2272) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: DllHost.exe | |||
| (PID) Process: | (124) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | rundll32 |
Value: C:\Windows\system32\rundll32.exe "C:\Users\admin\AppData\Roaming\Installer\{69067ECB-1199-4DFE-328D-23CF018B351C}\shell32.dll",Control_RunDLL | |||
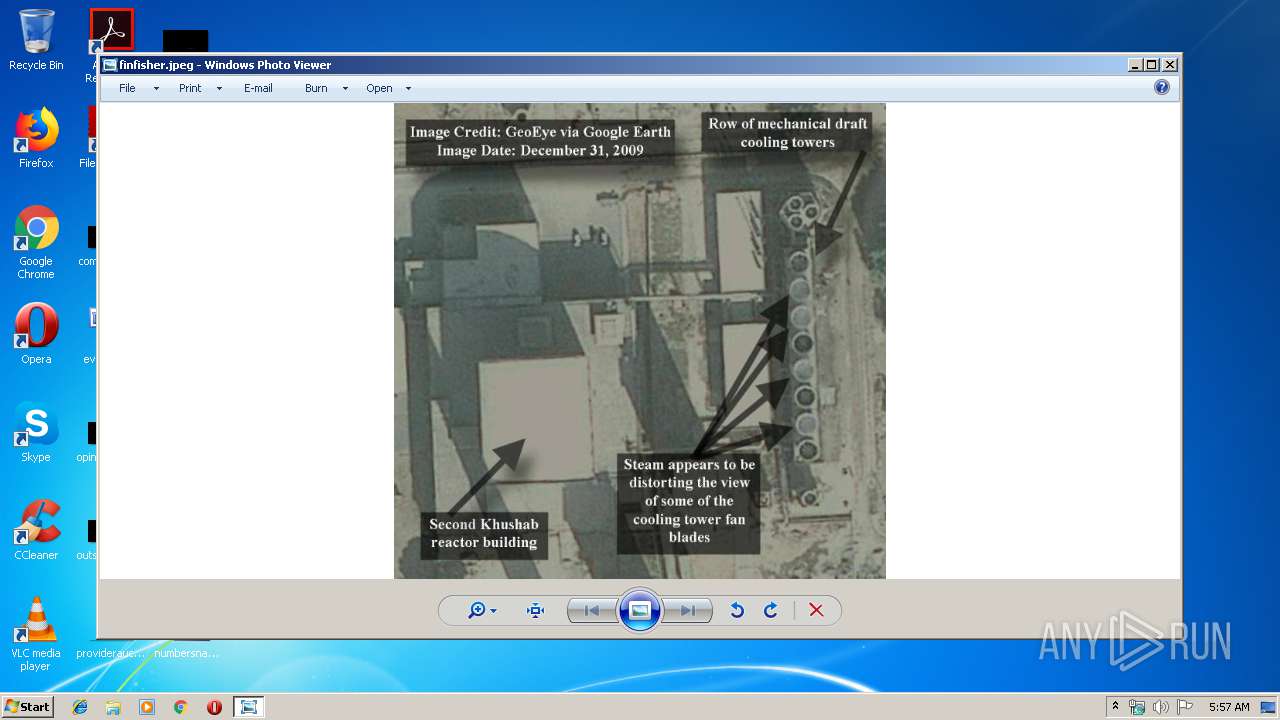
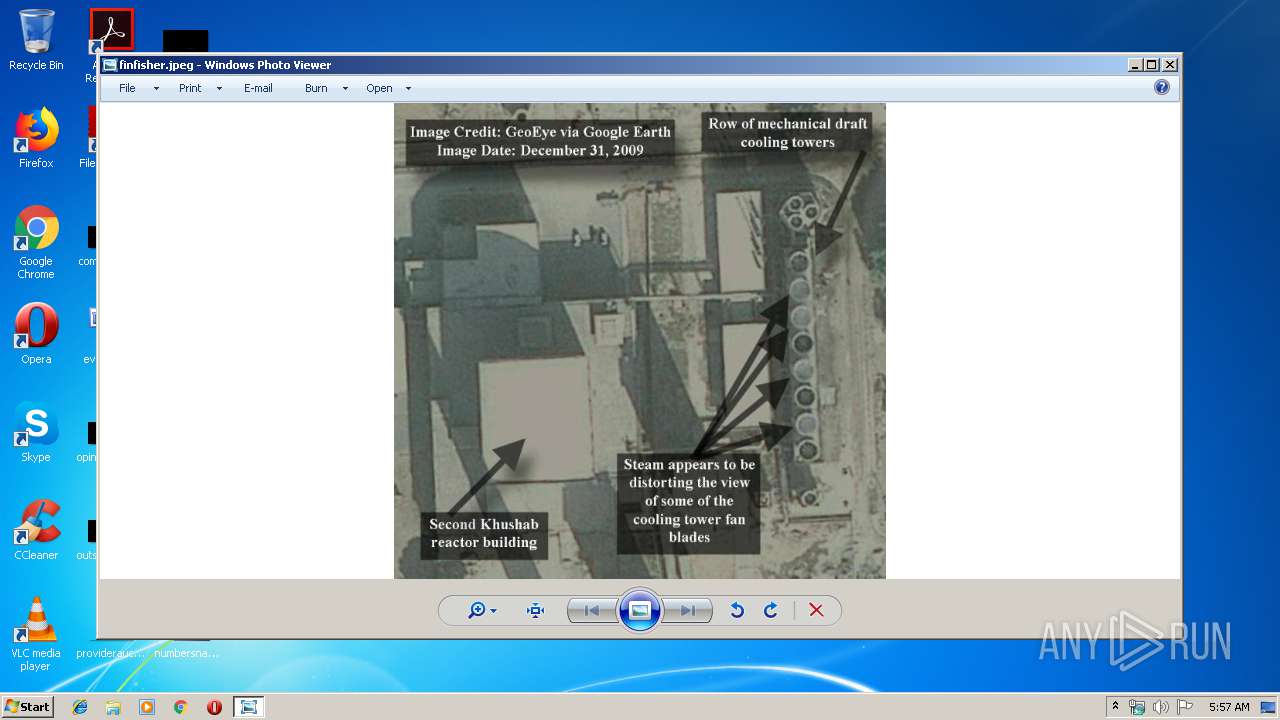
| (PID) Process: | (124) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jpeg\OpenWithList |
| Operation: | write | Name: | a |
Value: DllHost.exe | |||
| (PID) Process: | (124) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jpeg\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
| (PID) Process: | (2272) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000034000000A00400008002000000000000 | |||
| (PID) Process: | (124) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | Zvpebfbsg.Jvaqbjf.CubgbIvrjre |
Value: 00000000000000000000000047640000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
Executable files
4
Suspicious files
9
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 124 | explorer.exe | C:\Users\admin\AppData\Local\Temp\tntD253.tmp | — | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\AppData\Local\Temp\RCXD254.tmp | — | |
MD5:— | SHA256:— | |||
| 4060 | SearchProtocolHost.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\AppData\Roaming\Installer\{69067ECB-1199-4DFE-328D-23CF018B351C}\80C.dat | binary | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\AppData\Roaming\Installer\{69067ECB-1199-4DFE-328D-23CF018B351C}\02.dat | binary | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\AppData\Roaming\Installer\{69067ECB-1199-4DFE-328D-23CF018B351C}\02C.dat | binary | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\AppData\Roaming\Installer\{69067ECB-1199-4DFE-328D-23CF018B351C}\7F.dat | binary | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\AppData\Roaming\Installer\{69067ECB-1199-4DFE-328D-23CF018B351C}\shell32.dll | executable | |
MD5:— | SHA256:— | |||
| 124 | explorer.exe | C:\Users\admin\AppData\Roaming\Installer\{69067ECB-1199-4DFE-328D-23CF018B351C}\ShellExtensionEx.dll | executable | |
MD5:— | SHA256:— | |||
| 4060 | SearchProtocolHost.exe | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | pst | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
mafaque.webhop.net |
| unknown |