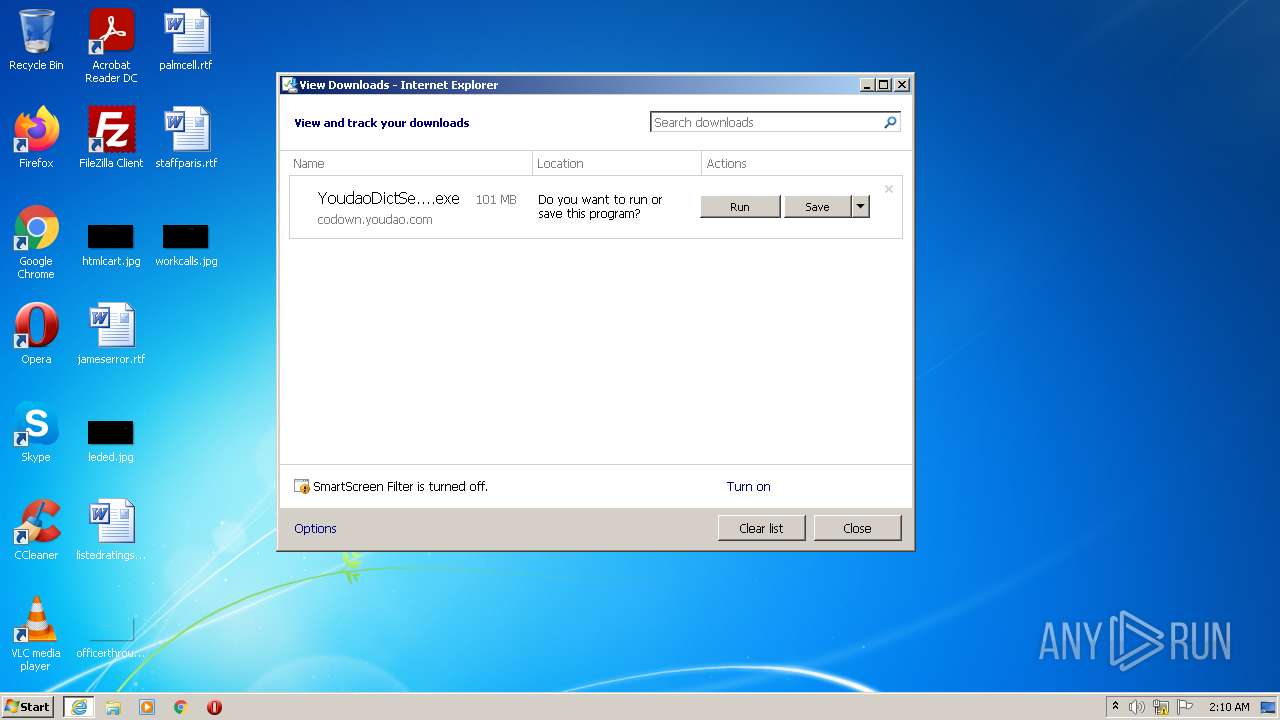
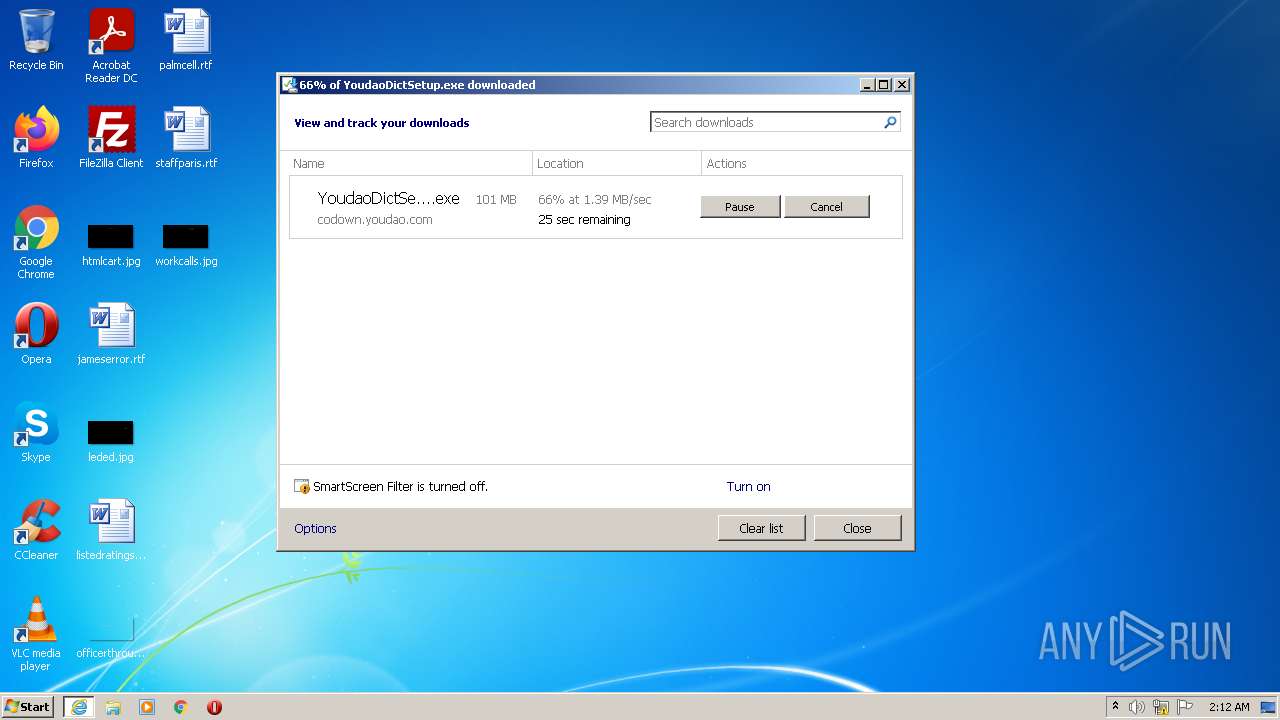
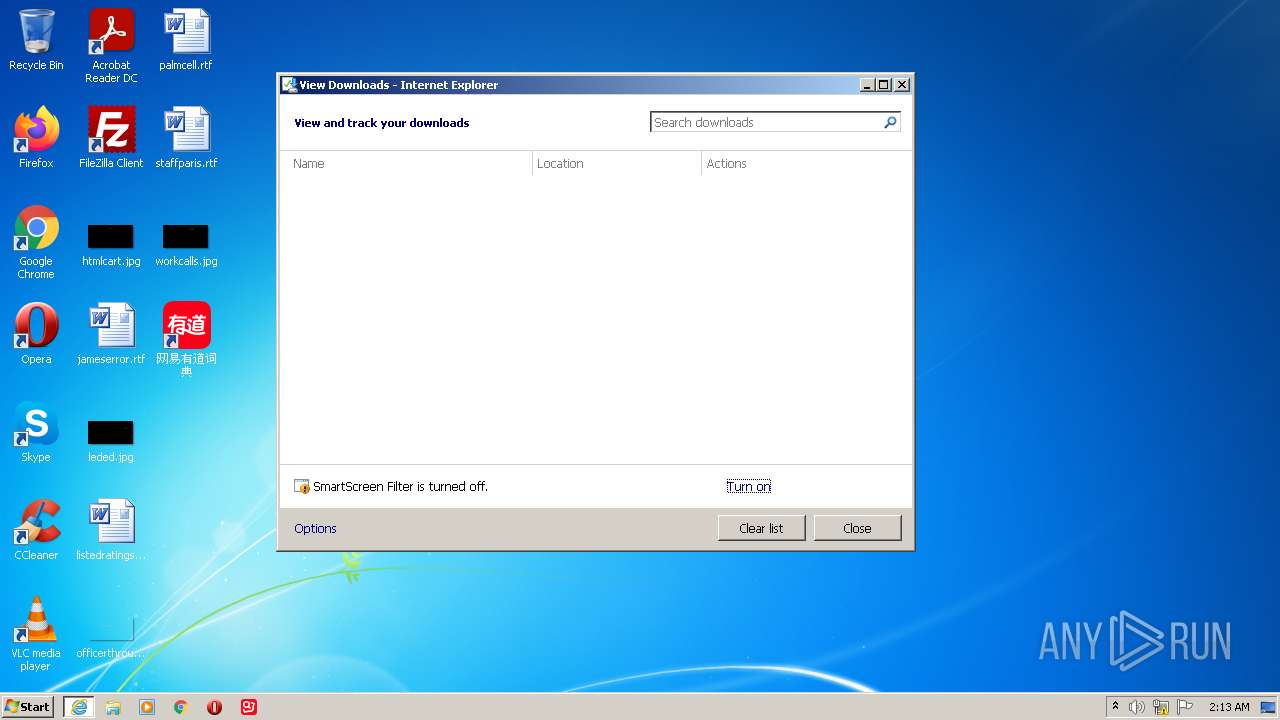
| URL: | http://cidian.youdao.com/download/YoudaoDict.exe |
| Full analysis: | https://app.any.run/tasks/0e94c754-8afb-49dd-a794-12ecdd01f698 |
| Verdict: | Malicious activity |
| Analysis date: | August 02, 2022, 01:10:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D5478D00BEEF8E1FE690455EF72E6DA1 |
| SHA1: | 0E7951CC0BF2320EE44A3B3557DE3F1296648D53 |
| SHA256: | 0B3800C2AA51880DF4D7E3A29D861B6F04AD39C119AA276C8D81528F9FE3F9CE |
| SSDEEP: | 3:N1KdMv/cKQBaLEhxLNn:CObQQi |
MALICIOUS
Application was dropped or rewritten from another process
- YoudaoDictSetup.exe (PID: 2816)
- YoudaoDictInstaller.exe (PID: 2712)
- InstallHelper.exe (PID: 1284)
- InstallHelper.exe (PID: 2732)
- YoudaoDictInstaller.exe (PID: 2868)
- InstallHelper.exe (PID: 1888)
- InstallHelper.exe (PID: 1360)
- InstallHelper.exe (PID: 3208)
- YoudaoDictInstaller.exe (PID: 2992)
- YoudaoDictInstaller.exe (PID: 3728)
- InstallDaemon.exe (PID: 3916)
- YoudaoDictInstaller.exe (PID: 3956)
- YoudaoDictInstaller.exe (PID: 2224)
- YoudaoDictInstaller.exe (PID: 1472)
- YoudaoDict.exe (PID: 2740)
- YoudaoDictHelper.exe (PID: 3608)
- YoudaoDictIcon.exe (PID: 3884)
- YoudaoDictHelper.exe (PID: 2776)
- YoudaoDictHelper.exe (PID: 2644)
- YoudaoDictHelper.exe (PID: 3272)
- YoudaoDictHelper.exe (PID: 2140)
- YoudaoDictHelper.exe (PID: 4036)
- YoudaoDictHelper.exe (PID: 2540)
Drops executable file immediately after starts
- iexplore.exe (PID: 3532)
- YoudaoDictSetup.exe (PID: 2816)
- InstallHelper.exe (PID: 1284)
- InstallHelper.exe (PID: 2732)
- InstallHelper.exe (PID: 1888)
- YoudaoDictInstaller.exe (PID: 3728)
Loads dropped or rewritten executable
- YoudaoDictSetup.exe (PID: 2816)
- regsvr32.exe (PID: 1124)
- YoudaoDict.exe (PID: 2740)
- YoudaoDictHelper.exe (PID: 3272)
- YoudaoDictHelper.exe (PID: 4036)
- YoudaoDictHelper.exe (PID: 2540)
- YoudaoDictHelper.exe (PID: 2140)
- YoudaoDictHelper.exe (PID: 3608)
- YoudaoDictHelper.exe (PID: 2644)
- ctfmon.exe (PID: 1520)
- Explorer.EXE (PID: 2020)
- iexplore.exe (PID: 3164)
- DllHost.exe (PID: 1880)
Changes the autorun value in the registry
- YoudaoDictInstaller.exe (PID: 2992)
- YoudaoDictSetup.exe (PID: 2816)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 3532)
- YoudaoDictSetup.exe (PID: 2816)
- InstallHelper.exe (PID: 1284)
- InstallHelper.exe (PID: 2732)
- InstallHelper.exe (PID: 1888)
- YoudaoDictInstaller.exe (PID: 3728)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3532)
- YoudaoDictSetup.exe (PID: 2816)
Drops a file with a compile date too recent
- iexplore.exe (PID: 3532)
- YoudaoDictSetup.exe (PID: 2816)
- InstallHelper.exe (PID: 2732)
- InstallHelper.exe (PID: 1888)
- InstallHelper.exe (PID: 1284)
- YoudaoDictInstaller.exe (PID: 3728)
Reads the computer name
- YoudaoDictSetup.exe (PID: 2816)
- InstallHelper.exe (PID: 2732)
- InstallHelper.exe (PID: 1888)
- InstallHelper.exe (PID: 1360)
- InstallHelper.exe (PID: 3208)
- YoudaoDictInstaller.exe (PID: 2992)
- YoudaoDictInstaller.exe (PID: 3728)
- InstallDaemon.exe (PID: 3916)
- YoudaoDictInstaller.exe (PID: 3956)
- YoudaoDictInstaller.exe (PID: 2868)
- YoudaoDict.exe (PID: 2740)
- YoudaoDictHelper.exe (PID: 2540)
- YoudaoDictHelper.exe (PID: 2140)
Reads Environment values
- YoudaoDictSetup.exe (PID: 2816)
Checks supported languages
- YoudaoDictSetup.exe (PID: 2816)
- YoudaoDictInstaller.exe (PID: 2712)
- YoudaoDictInstaller.exe (PID: 2868)
- InstallHelper.exe (PID: 1284)
- InstallHelper.exe (PID: 2732)
- YoudaoDictInstaller.exe (PID: 2992)
- InstallHelper.exe (PID: 1888)
- InstallHelper.exe (PID: 3208)
- InstallHelper.exe (PID: 1360)
- cmd.exe (PID: 3204)
- cmd.exe (PID: 1844)
- YoudaoDictInstaller.exe (PID: 3728)
- InstallDaemon.exe (PID: 3916)
- YoudaoDictInstaller.exe (PID: 2224)
- YoudaoDictInstaller.exe (PID: 1472)
- YoudaoDictInstaller.exe (PID: 3956)
- YoudaoDict.exe (PID: 2740)
- YoudaoDictHelper.exe (PID: 3608)
- YoudaoDictHelper.exe (PID: 3272)
- YoudaoDictHelper.exe (PID: 2540)
- YoudaoDictHelper.exe (PID: 4036)
- YoudaoDictHelper.exe (PID: 2140)
- YoudaoDictHelper.exe (PID: 2644)
Application launched itself
- YoudaoDictInstaller.exe (PID: 2992)
- cmd.exe (PID: 1844)
Creates files in the program directory
- YoudaoDictInstaller.exe (PID: 3728)
Reads the date of Windows installation
- YoudaoDictSetup.exe (PID: 2816)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1124)
Searches for installed software
- YoudaoDictInstaller.exe (PID: 3956)
- YoudaoDict.exe (PID: 2740)
- YoudaoDictHelper.exe (PID: 2540)
Creates a software uninstall entry
- YoudaoDictSetup.exe (PID: 2816)
INFO
Checks supported languages
- iexplore.exe (PID: 3164)
- iexplore.exe (PID: 3532)
- regsvr32.exe (PID: 1124)
- regsvr32.exe (PID: 3028)
- cacls.exe (PID: 3592)
- DllHost.exe (PID: 1880)
Reads the computer name
- iexplore.exe (PID: 3164)
- iexplore.exe (PID: 3532)
- cacls.exe (PID: 3592)
- DllHost.exe (PID: 1880)
Changes internet zones settings
- iexplore.exe (PID: 3164)
Application launched itself
- iexplore.exe (PID: 3164)
Checks Windows Trust Settings
- iexplore.exe (PID: 3532)
- iexplore.exe (PID: 3164)
- YoudaoDict.exe (PID: 2740)
Reads settings of System Certificates
- iexplore.exe (PID: 3532)
- iexplore.exe (PID: 3164)
- YoudaoDict.exe (PID: 2740)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3164)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3164)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3164)
Reads the date of Windows installation
- iexplore.exe (PID: 3164)
Changes settings of System certificates
- iexplore.exe (PID: 3164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
33
Malicious processes
14
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1124 | "C:\Windows\System32\regsvr32.exe" "C:\Users\admin\AppData\Local\Youdao\Dict\Application\stable\YoudaoGetWord32.dll" /s | C:\Windows\System32\regsvr32.exe | — | YoudaoDictInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1284 | "C:\Users\admin\AppData\Local\Temp\nsuBC50.tmp\InstallHelper.exe" "exports" "C:\Users\admin\AppData\Local\Temp\nsuBC50.tmp\dict.7z" "C:\Users\admin\AppData\Local\Youdao\Dict\Application\install_9.0.4.0" | C:\Users\admin\AppData\Local\Temp\nsuBC50.tmp\InstallHelper.exe | YoudaoDictSetup.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1360 | "C:\Users\admin\AppData\Local\Temp\nsuBC50.tmp\InstallHelper.exe" "move" "C:\Users\admin\AppData\Local\Youdao\Dict\Application\install_9.0.4.0\9.0.4.0" "C:\Users\admin\AppData\Local\Youdao\Dict\Application\9.0.4.0" | C:\Users\admin\AppData\Local\Temp\nsuBC50.tmp\InstallHelper.exe | — | YoudaoDictSetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1472 | "C:\Users\admin\AppData\Local\Temp\nsuBC50.tmp\YoudaoDictInstaller.exe" "cleanup" "C:\Users\admin\AppData\Local\Youdao\Dict\Application" | C:\Users\admin\AppData\Local\Temp\nsuBC50.tmp\YoudaoDictInstaller.exe | — | YoudaoDictSetup.exe | |||||||||||
User: admin Company: 网易公司 Integrity Level: MEDIUM Description: 网易有道词典安装辅助程序 Exit code: 0 Version: 9.0.4.0 Modules
| |||||||||||||||
| 1520 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1844 | "C:\Windows\System32\cmd.exe" /c echo y| cacls "C:\ProgramData\Youdao\DeskDict\pluginconfig.ini" /c /g everyone:f | C:\Windows\System32\cmd.exe | — | YoudaoDictInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1880 | C:\Windows\system32\DllHost.exe /Processid:{F9717507-6651-4EDB-BFF7-AE615179BCCF} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1888 | "C:\Users\admin\AppData\Local\Temp\nsuBC50.tmp\InstallHelper.exe" "move" "C:\Users\admin\AppData\Local\Youdao\Dict\Application\install_9.0.4.0\YoudaoDict.exe" "C:\Users\admin\AppData\Local\Youdao\Dict\Application\YoudaoDict.exe" | C:\Users\admin\AppData\Local\Temp\nsuBC50.tmp\InstallHelper.exe | YoudaoDictSetup.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2020 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Youdao\Dict\Application\9.0.4.0\YoudaoDictHelper.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=3540,2770192032720461748,13790038279362284449,131072 --disable-features=CalculateNativeWinOcclusion,WinUseBrowserSpellChecker --lang=en-US --service-sandbox-type=none --no-sandbox --locales-dir-path="C:\Users\admin\AppData\Local\Youdao\Dict\Application\9.0.4.0" --log-severity=disable --resources-dir-path="C:\Users\admin\AppData\Local\Youdao\Dict\Application\9.0.4.0" --user-agent="Mozilla/5.0 (Windows NT 6.1.7601; WOW64) Chrome/97.0.4692.99 youdaodict/9.0 (jsbridge/1.0;windowspc) " --lang=en-US --user-data-dir="C:\Users\admin\AppData\Local\CEF\User Data" --disable-logging --log-file="C:\Users\admin\AppData\Local\Youdao\Dict\Application\debug.log" --mojo-platform-channel-handle=3844 /prefetch:8 | C:\Users\admin\AppData\Local\Youdao\Dict\Application\9.0.4.0\YoudaoDictHelper.exe | YoudaoDict.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
52 918
Read events
52 325
Write events
581
Delete events
12
Modification events
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30975500 | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30975500 | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3164) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
58
Suspicious files
44
Text files
677
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\FA0A17BC17FF10008872A7205D0D43E2_608DEF97DFACECDA8E97C6F270153A4F | binary | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\FA0A17BC17FF10008872A7205D0D43E2_608DEF97DFACECDA8E97C6F270153A4F | der | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8F8712BCE78D28F9C5E3E950CD93EADA_47D5C8DFE8283820167BEB0B81B99998 | der | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\YoudaoDictSetup[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3532 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8F8712BCE78D28F9C5E3E950CD93EADA_47D5C8DFE8283820167BEB0B81B99998 | binary | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 3164 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
95
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3956 | YoudaoDictInstaller.exe | GET | 200 | 47.89.225.38:80 | http://cidian.youdao.com/icomplete.html?keyfrom=deskdict.9.0.4.0&client=deskdict&id=87339e1c6a3cafe88&vendor=unknown&in=YoudaoDictSetup&appVer=9.0.4.0&appZengqiang=2&autorun=1&ins_toolbar=&ins_personalhome= | US | — | — | whitelisted |
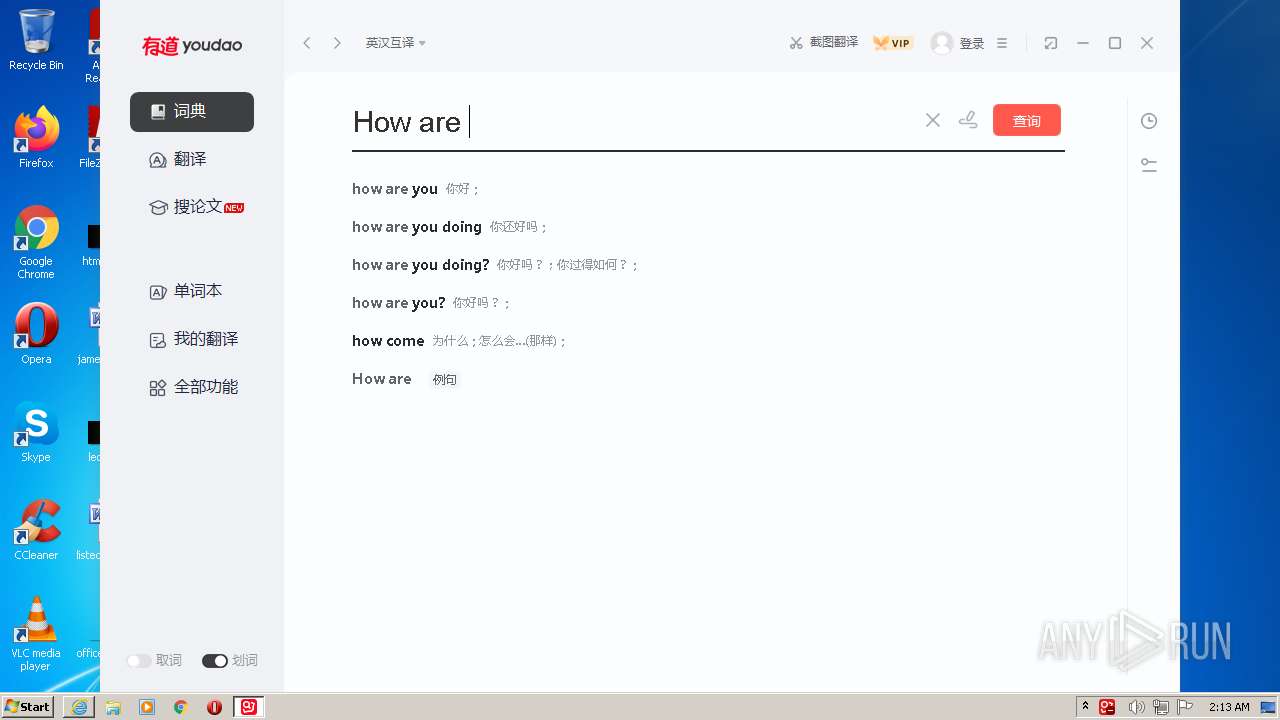
2140 | YoudaoDictHelper.exe | GET | 200 | 103.135.240.15:80 | http://gorgon.youdao.com/gorgon/request.s?udid=87339e1c6a3cafe88&id=0cdb70957a0d6f5b4dbc91abff894eed&q=m_words%3AHo&ct=2&MAGIC_NO=0&reqfrom=web&webos=6&nsv=1.0.5&ran=1&callback=_yad_jsonp_4&_1659402832597 | unknown | text | 14 b | unknown |
3532 | iexplore.exe | GET | 302 | 47.89.225.38:80 | http://cidian.youdao.com/download/YoudaoDict.exe | US | html | 110 b | whitelisted |
3532 | iexplore.exe | GET | 200 | 79.133.177.225:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSmVYFXwi%2FRq9wx3PKhB8lC%2FFYUyAQUkZ9eMRWuEJ%2BtYMH3wcyqSDQvDCYCEAfOyBW0lsno9wKA6I09unc%3D | RU | der | 471 b | whitelisted |
3164 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3532 | iexplore.exe | GET | 200 | 79.133.177.225:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAoEcNCWvIoSyJCm34Ju7Es%3D | RU | der | 471 b | whitelisted |
3164 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2140 | YoudaoDictHelper.exe | GET | 200 | 103.135.240.15:80 | http://gorgon.youdao.com/gorgon/request.s?udid=87339e1c6a3cafe88&id=0cdb70957a0d6f5b4dbc91abff894eed&q=m_words%3AHow%20are%20you&ct=2&MAGIC_NO=0&reqfrom=web&webos=6&nsv=1.0.5&ran=1&callback=_yad_jsonp_8&_1659402837128 | unknown | text | 14 b | unknown |
2140 | YoudaoDictHelper.exe | GET | 200 | 103.135.240.15:80 | http://gorgon.youdao.com/gorgon/request.s?udid=87339e1c6a3cafe88&id=0cdb70957a0d6f5b4dbc91abff894eed&q=m_words%3AHow%20ar&ct=2&MAGIC_NO=0&reqfrom=web&webos=6&nsv=1.0.5&ran=1&callback=_yad_jsonp_7&_1659402834732 | unknown | text | 14 b | unknown |
2140 | YoudaoDictHelper.exe | GET | 200 | 103.135.240.15:80 | http://gorgon.youdao.com/gorgon/request.s?udid=87339e1c6a3cafe88&id=0cdb70957a0d6f5b4dbc91abff894eed&q=m_words%3AHow%20a&ct=2&MAGIC_NO=0&reqfrom=web&webos=6&nsv=1.0.5&ran=1&callback=_yad_jsonp_6&_1659402834588 | unknown | text | 14 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3532 | iexplore.exe | 47.89.225.38:80 | cidian.youdao.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
3532 | iexplore.exe | 58.215.123.244:443 | codown.youdao.com | AS Number for CHINANET jiangsu province backbone | CN | suspicious |
3532 | iexplore.exe | 8.248.145.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3532 | iexplore.exe | 79.133.177.225:80 | ocsp.dcocsp.cn | SOT LINE Limited Company | RU | malicious |
3164 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3164 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3164 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3164 | iexplore.exe | 96.16.143.41:443 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
3164 | iexplore.exe | 20.25.53.147:443 | query.prod.cms.msn.com | — | US | unknown |
2740 | YoudaoDict.exe | 47.89.225.38:443 | cidian.youdao.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cidian.youdao.com |
| unknown |
codown.youdao.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.dcocsp.cn |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
YoudaoDictHelper.exe | Warning: disabling flag --expose_wasm due to conflicting flags
|
YoudaoDictHelper.exe | Warning: disabling flag --expose_wasm due to conflicting flags
|