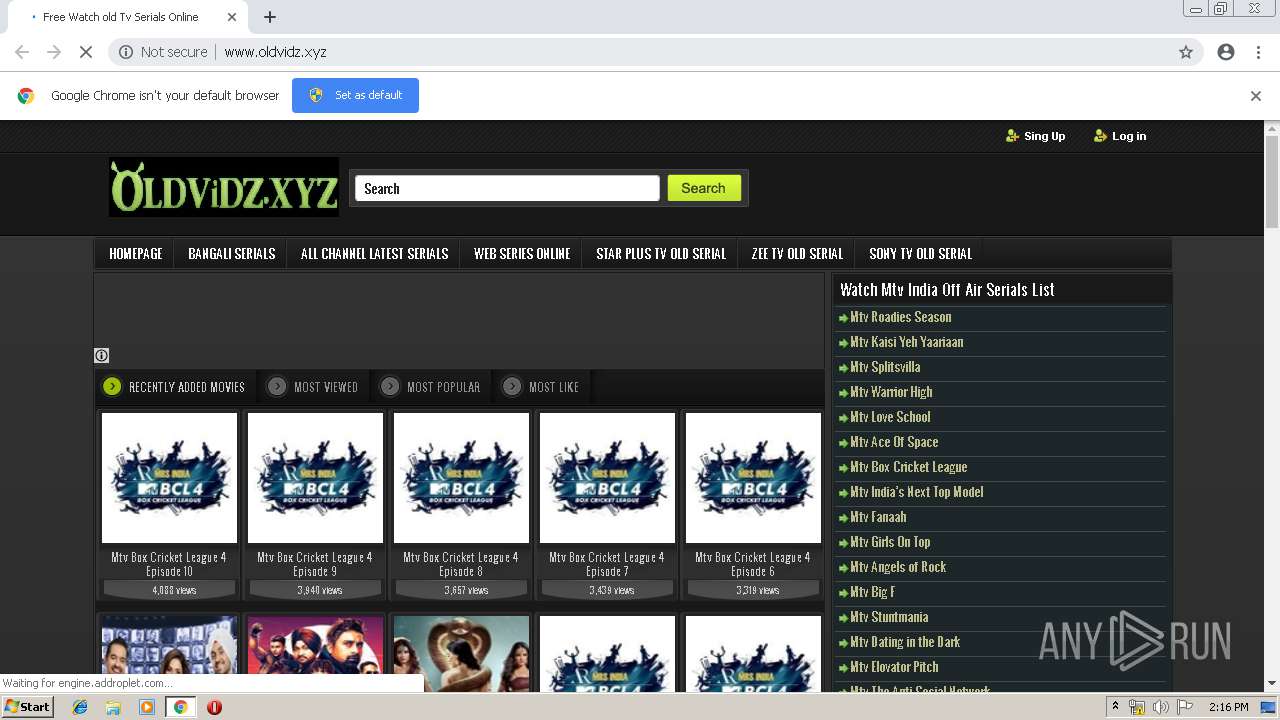
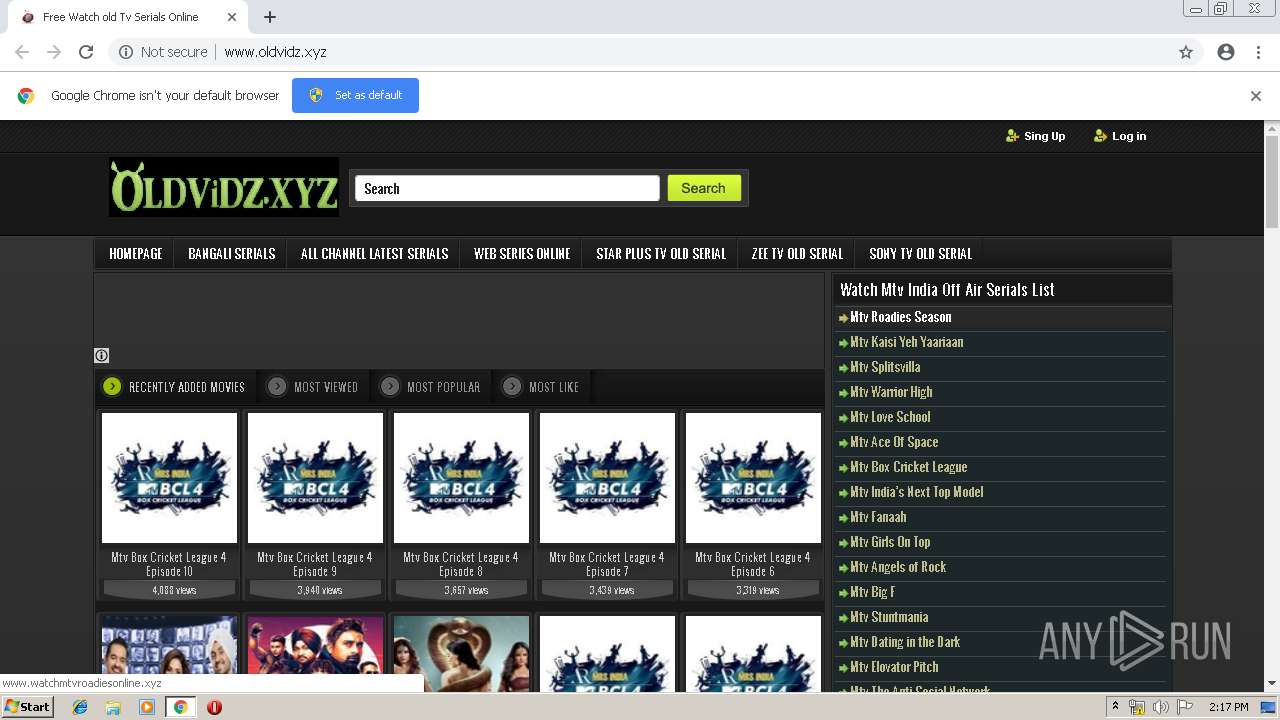
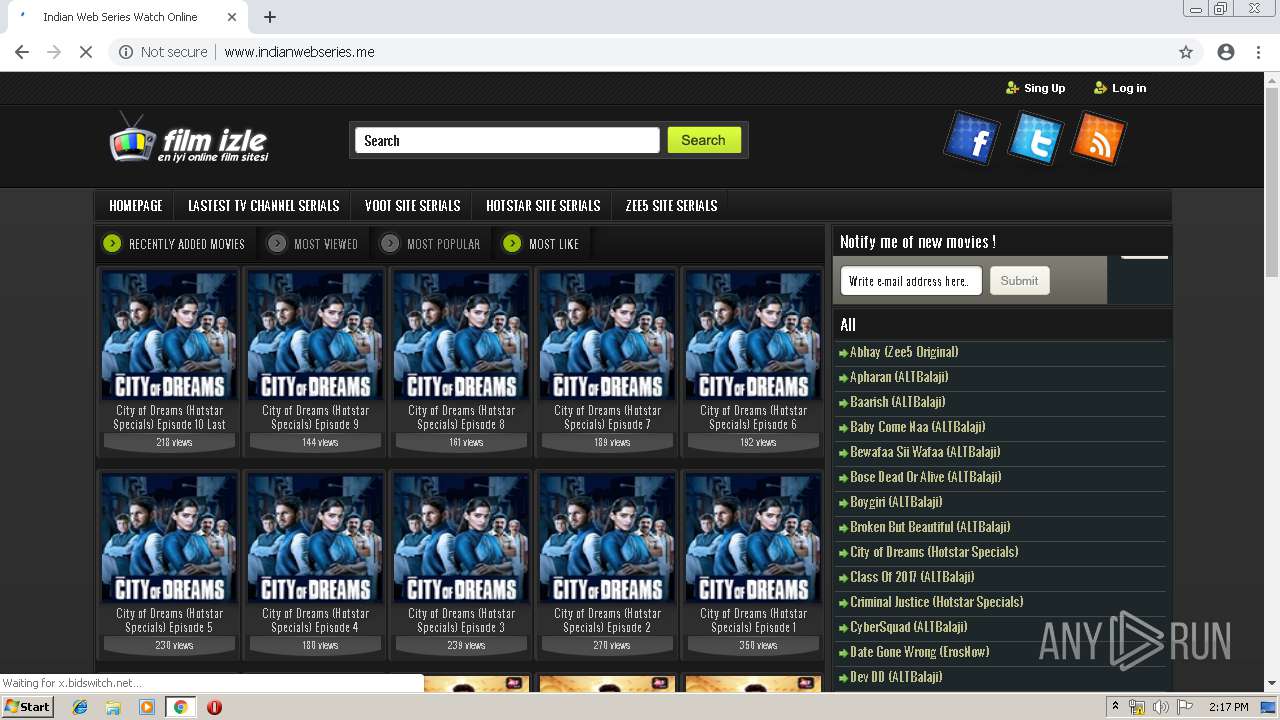
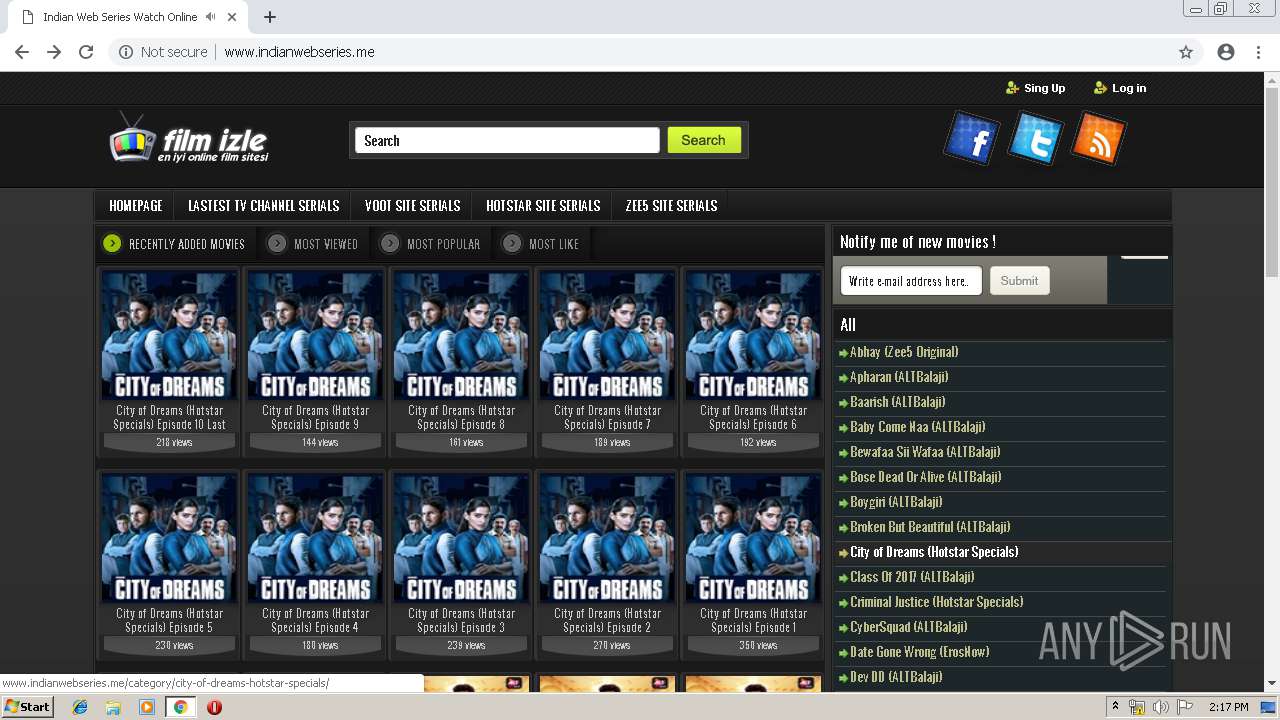
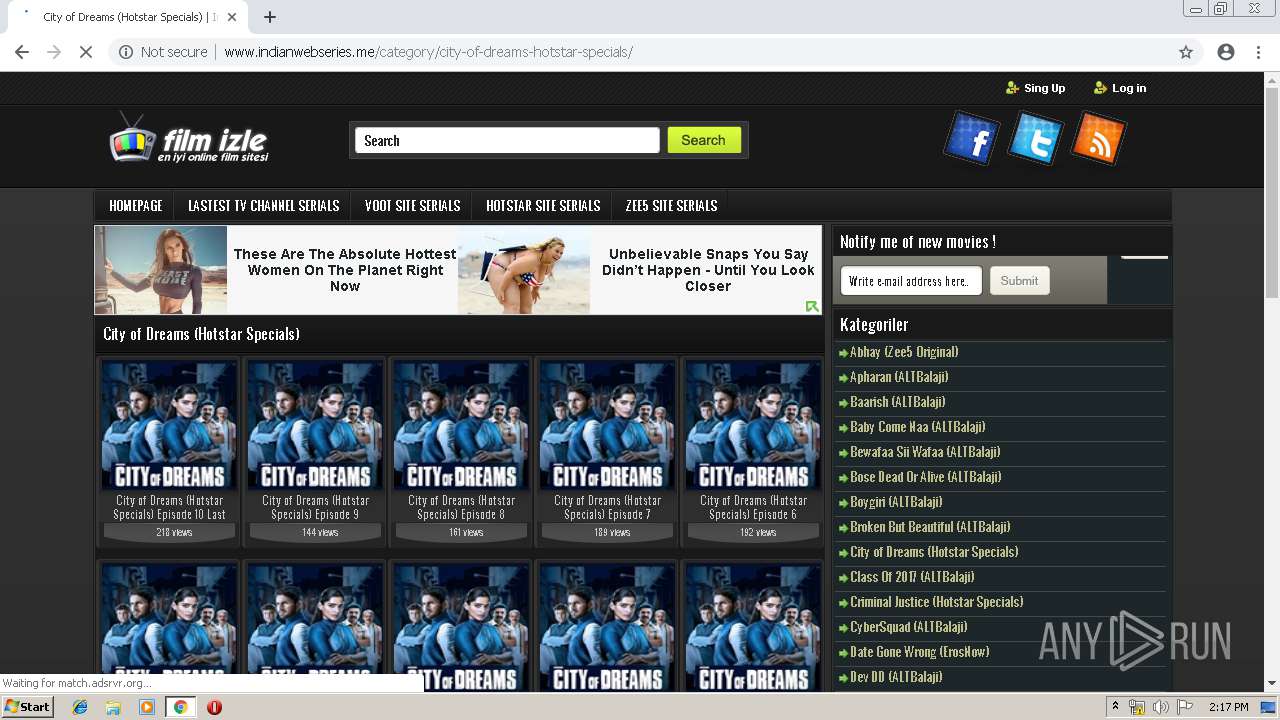
| URL: | http://www.oldvidz.xyz/ |
| Full analysis: | https://app.any.run/tasks/4a9dc231-d6c6-4c87-b785-7a0dae342def |
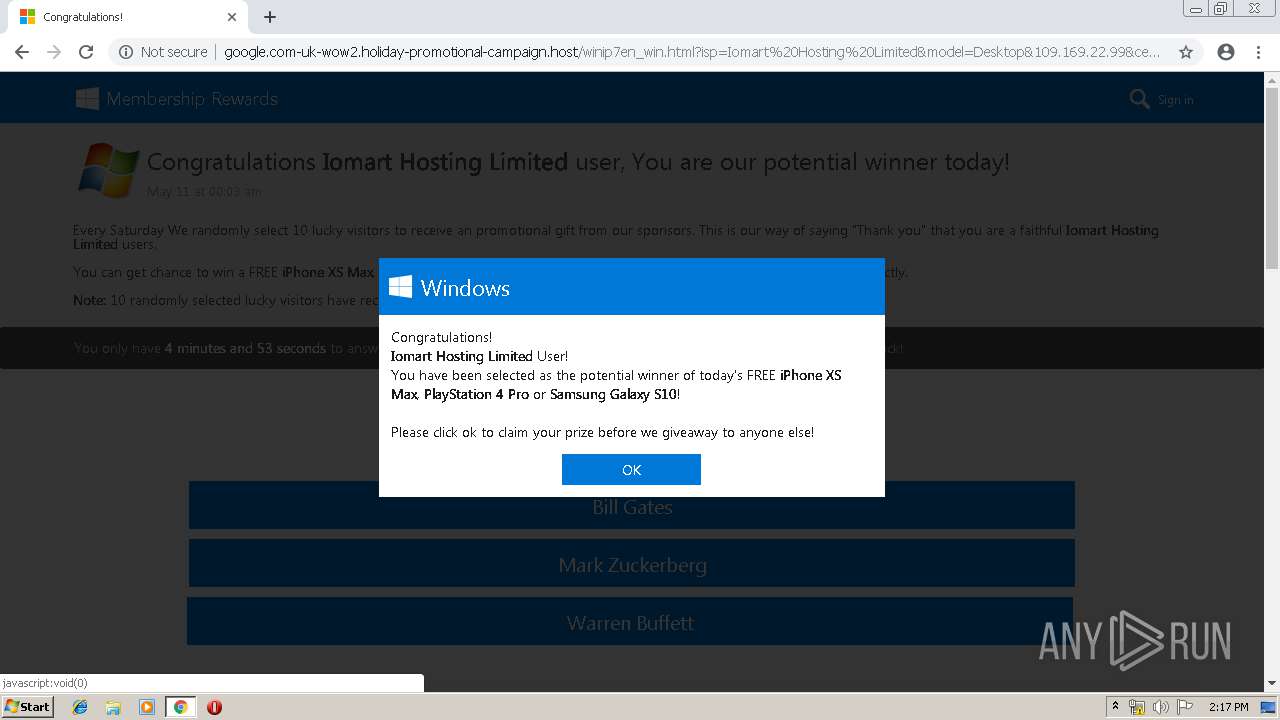
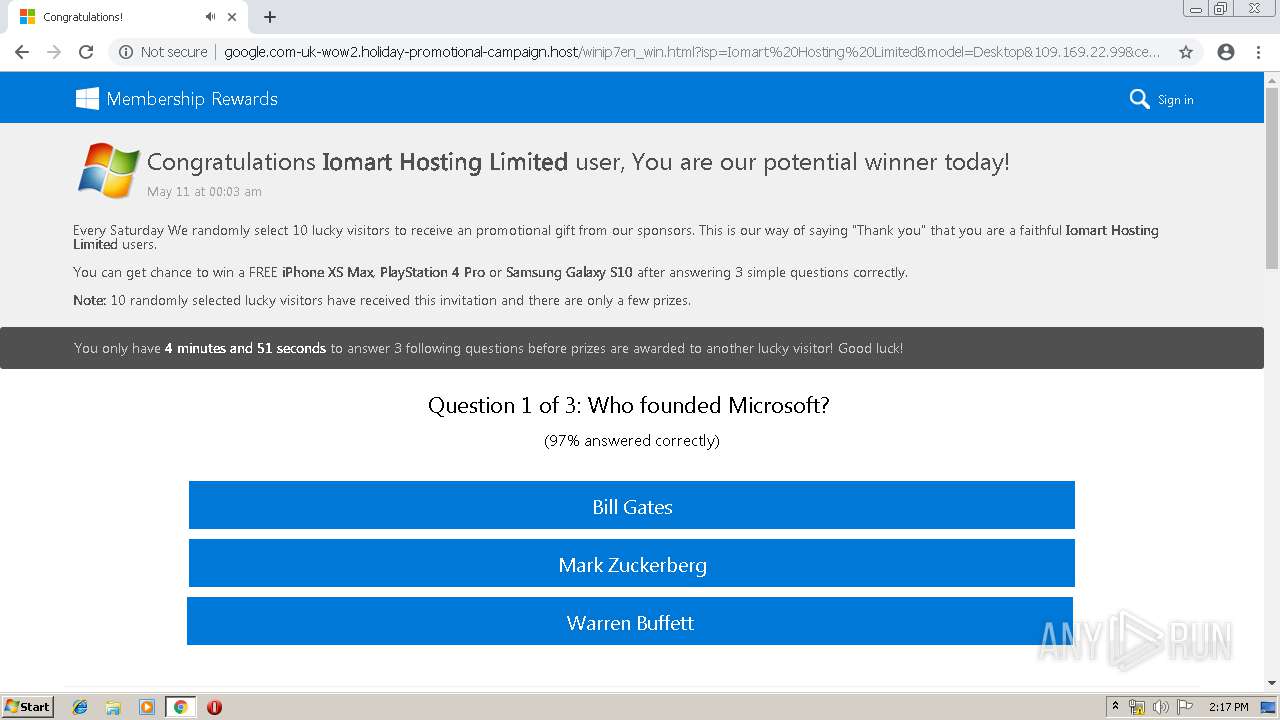
| Verdict: | Malicious activity |
| Analysis date: | May 11, 2019, 13:16:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 93619F4323067C6314934456B10CAAF9 |
| SHA1: | 42335878B985F025693D67137B76F4849D18DCCD |
| SHA256: | 0B2F48D60467940959B3E33FB263596672C68E6C3A714C49084C492408459AEF |
| SSDEEP: | 3:N1KJS4A6L:Cc4r |
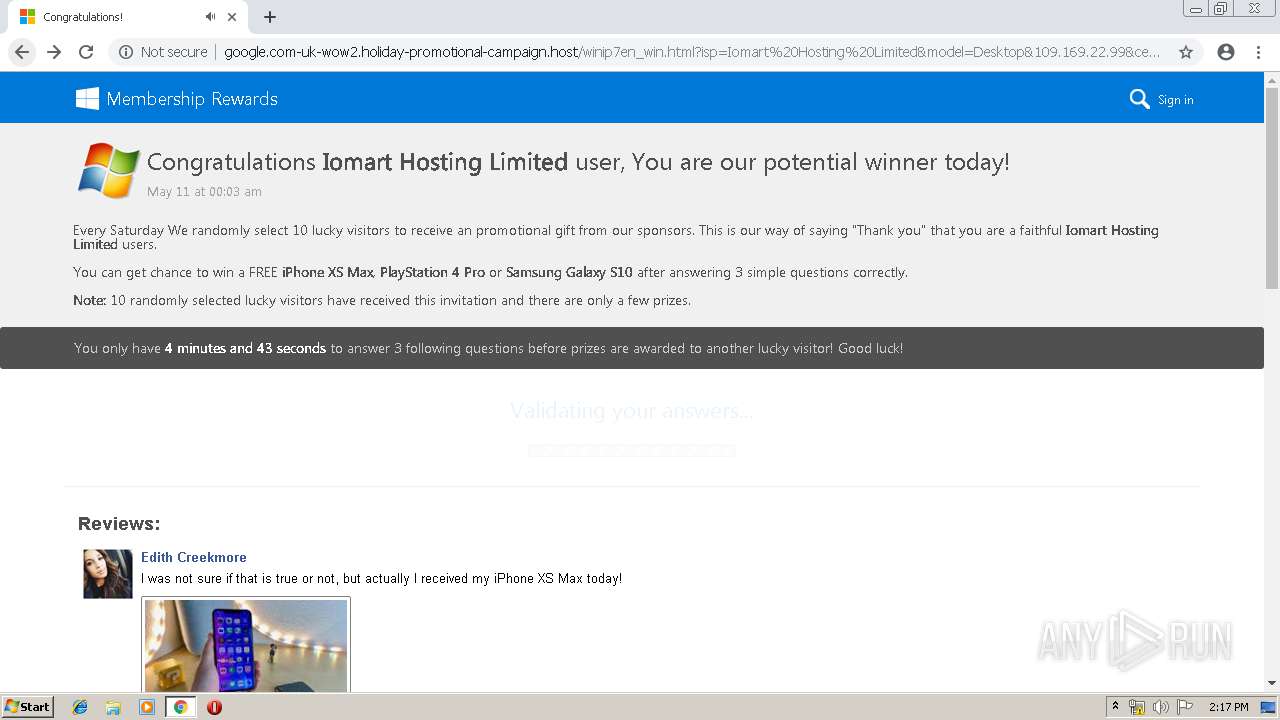
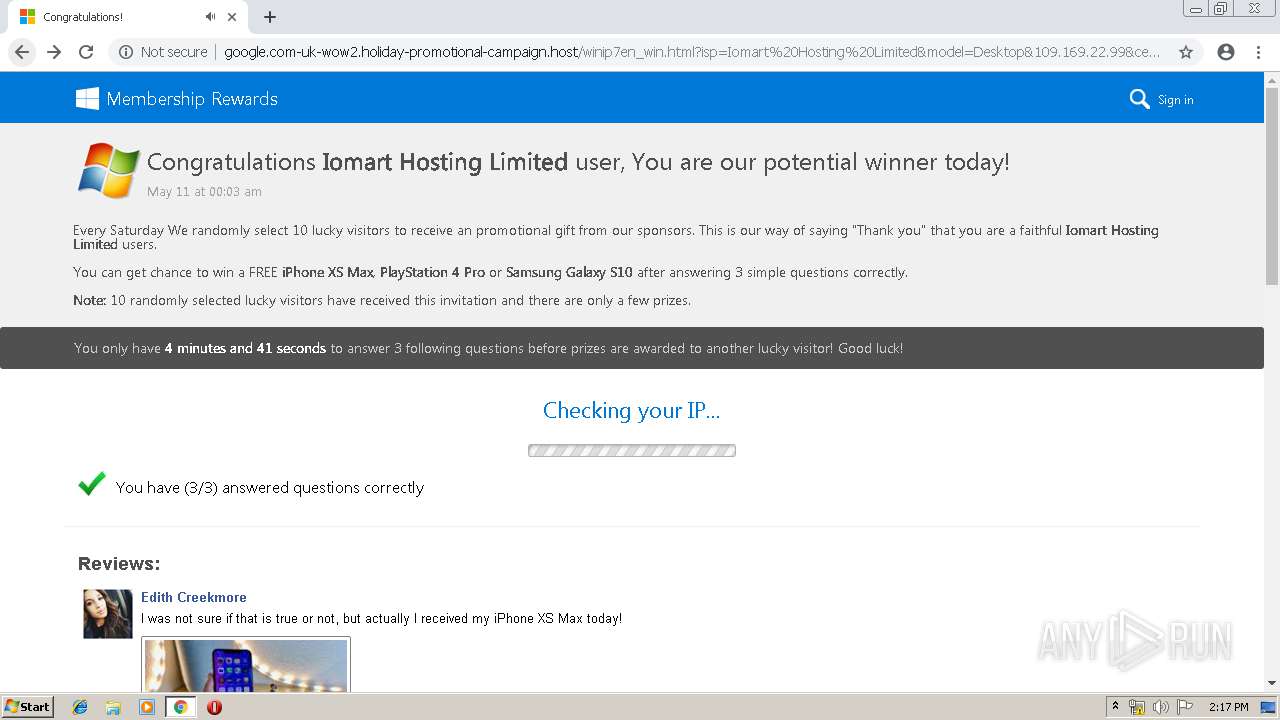
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 456)
INFO
Application launched itself
- chrome.exe (PID: 456)
Reads settings of System Certificates
- chrome.exe (PID: 456)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
44
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://www.oldvidz.xyz/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5753818957550170700 --mojo-platform-channel-handle=4976 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=9202294005994899198 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9202294005994899198 --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13420347249545562989 --mojo-platform-channel-handle=5156 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9223813703728278997 --mojo-platform-channel-handle=4980 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=2896780273237846709 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2896780273237846709 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8018085893081054949 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8018085893081054949 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3048 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1537225661779866687 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1537225661779866687 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11873632505192794783 --mojo-platform-channel-handle=5164 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,11659240946840176554,15815387434956610658,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=18358684108857371524 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18358684108857371524 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4956 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
641
Read events
527
Write events
109
Delete events
5
Modification events
| (PID) Process: | (456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 456-13202054208804375 |
Value: 259 | |||
| (PID) Process: | (456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (456) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
128
Text files
194
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1c9c16f0-a4af-4a1f-84c4-061e8d2effec.tmp | — | |
MD5:— | SHA256:— | |||
| 456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
430
TCP/UDP connections
237
DNS requests
157
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
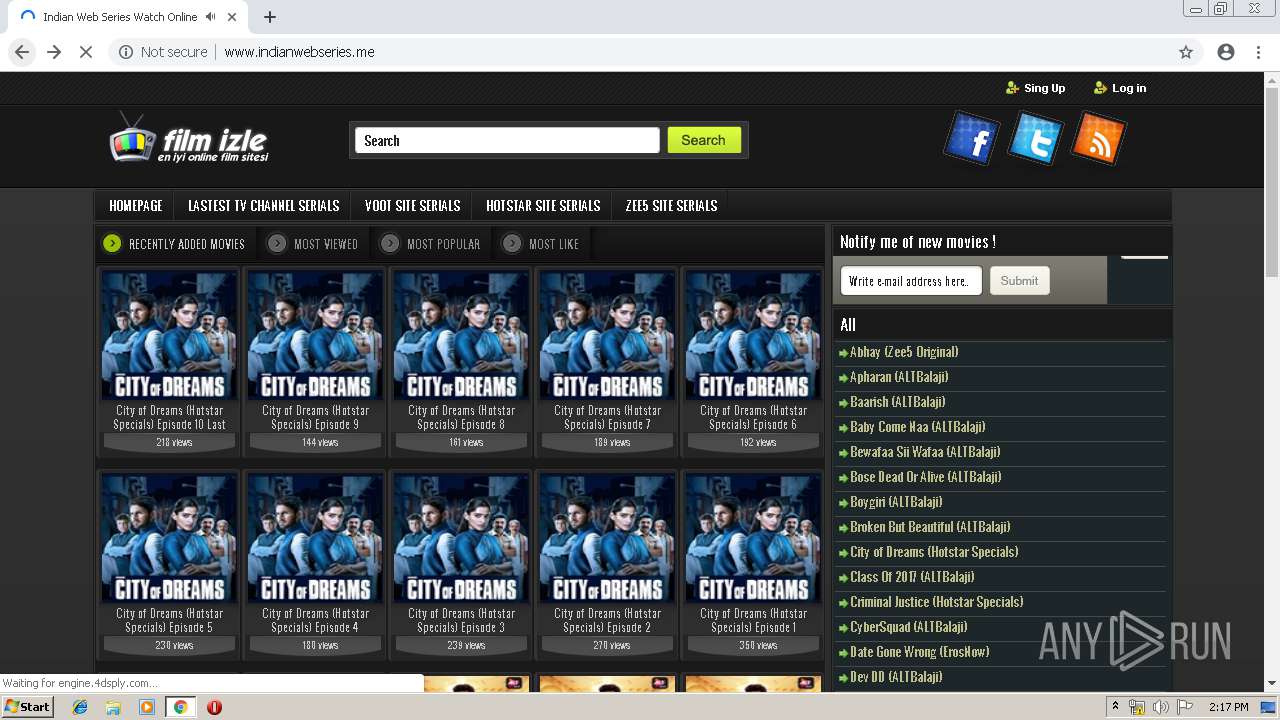
456 | chrome.exe | GET | 200 | 212.83.187.213:80 | http://www.oldvidz.xyz/ | FR | html | 68.3 Kb | unknown |
456 | chrome.exe | GET | 200 | 212.83.187.213:80 | http://www.oldvidz.xyz/wp-includes/css/dist/block-library/style.min.css?ver=5.0.4 | FR | text | 25.0 Kb | unknown |
456 | chrome.exe | GET | 200 | 212.83.187.213:80 | http://www.oldvidz.xyz/wp-content/themes/keremiya/js/jquery.js?ver=1.7.1 | FR | html | 91.6 Kb | unknown |
456 | chrome.exe | GET | 200 | 212.83.187.213:80 | http://www.oldvidz.xyz/wp-content/themes/keremiya/style.css | FR | text | 37.1 Kb | unknown |
456 | chrome.exe | GET | 200 | 212.83.187.213:80 | http://www.oldvidz.xyz/wp-content/themes/keremiya/pagenavi-css.css?ver=2.70 | FR | text | 691 b | unknown |
456 | chrome.exe | GET | 200 | 104.20.49.111:80 | http://cdn.adtrue.com/rtb/async.js | US | html | 2.60 Kb | suspicious |
456 | chrome.exe | GET | 200 | 212.83.187.213:80 | http://www.oldvidz.xyz/wp-content/uploads/2019/03/Rising-Star-3.jpg | FR | image | 18.8 Kb | unknown |
456 | chrome.exe | GET | 200 | 212.83.187.213:80 | http://www.oldvidz.xyz/wp-content/uploads/2018/11/yoo.jpg | FR | image | 14.9 Kb | unknown |
456 | chrome.exe | GET | 200 | 142.91.159.211:80 | http://umekian.pw/rmO67aPseoe/12184 | NL | text | 7.01 Kb | suspicious |
456 | chrome.exe | GET | 200 | 212.83.187.213:80 | http://www.oldvidz.xyz/wp-content/themes/keremiya/js/likesScript.js?ver=3.3.1 | FR | text | 942 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
456 | chrome.exe | 172.217.23.170:80 | imasdk.googleapis.com | Google Inc. | US | whitelisted |
456 | chrome.exe | 172.217.22.72:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
456 | chrome.exe | 18.153.11.27:80 | x.bidswitch.net | — | US | unknown |
456 | chrome.exe | 46.105.201.240:80 | s10.histats.com | OVH SAS | FR | suspicious |
456 | chrome.exe | 216.58.207.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
456 | chrome.exe | 2.16.186.51:80 | b.scorecardresearch.com | Akamai International B.V. | — | whitelisted |
456 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
456 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
456 | chrome.exe | 212.83.187.213:80 | www.oldvidz.xyz | Online S.a.s. | FR | unknown |
456 | chrome.exe | 142.91.159.211:80 | umekian.pw | — | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.oldvidz.xyz |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
umekian.pw |
| suspicious |
cdn.adtrue.com |
| suspicious |
www.google.com |
| malicious |
s.w.org |
| whitelisted |
adserver.reklamstore.com |
| shared |
cdn.engine.addroplet.com |
| whitelisted |
metricfast.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
456 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.pw domain |