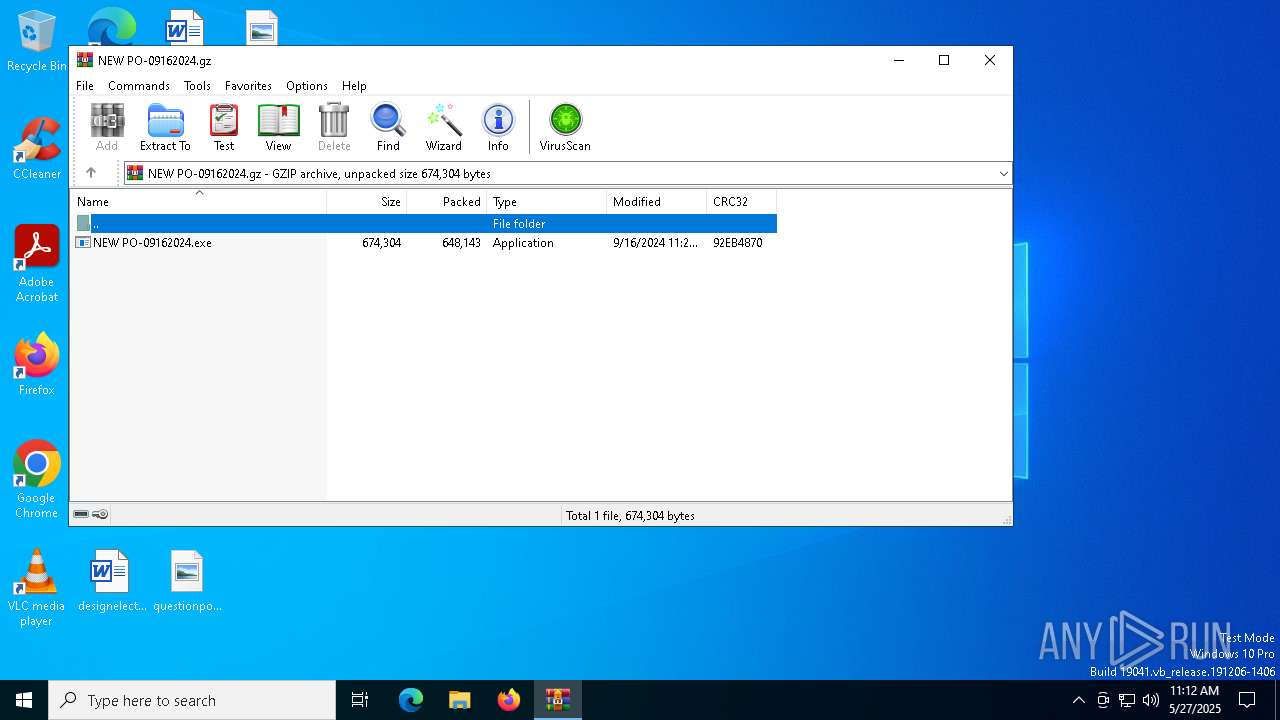
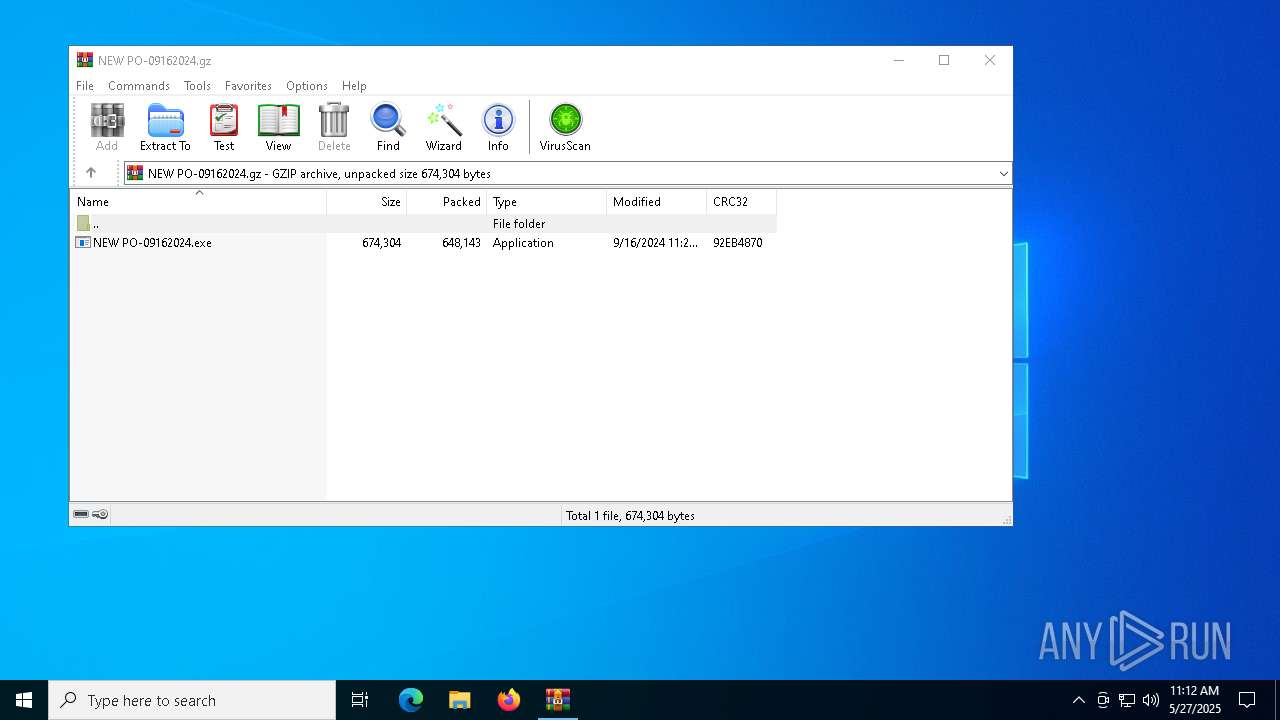
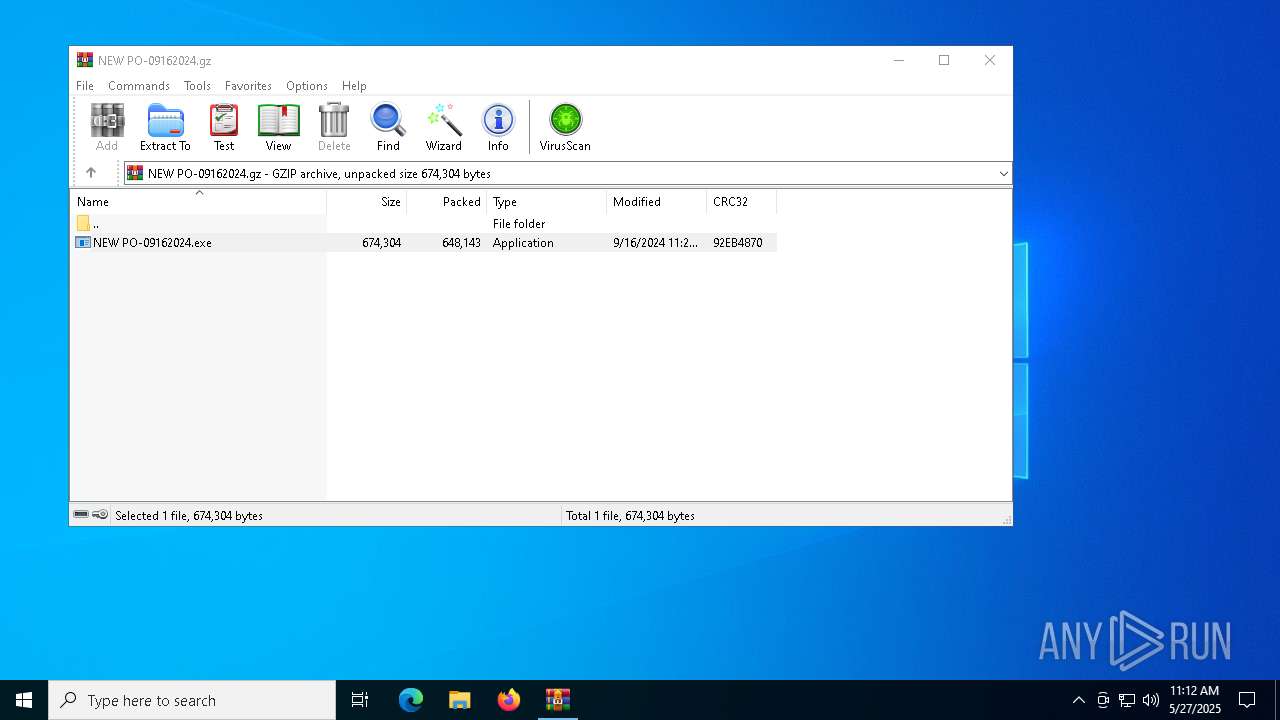
| File name: | NEW PO-09162024.gz |
| Full analysis: | https://app.any.run/tasks/322f97e1-9d41-4efe-a080-d17ccacaa797 |
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2025, 11:12:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/gzip |
| File info: | gzip compressed data, was "NEW PO-09162024.exe", last modified: Mon Sep 16 11:28:52 2024, from FAT filesystem (MS-DOS, OS/2, NT), original size modulo 2^32 674304 |
| MD5: | 0588A0133C63D1A35188F671FCB73F45 |
| SHA1: | 209D89B9C5012E433BC85917979D621E20107776 |
| SHA256: | 0B2BD3030ABD0361C0FCBE27EFCB9FF9DA2320A5025001EA06F4530446D09EAD |
| SSDEEP: | 24576:8UXkm9OmFlFd4xvlNNoePqxaokzZcOUiJvCl0P8M2WzXq+Zw9ukck:8UXkm9Oal/4xvlNNXPqx1kzZcOUiJvCd |
MALICIOUS
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 1472)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 1472)
SUSPICIOUS
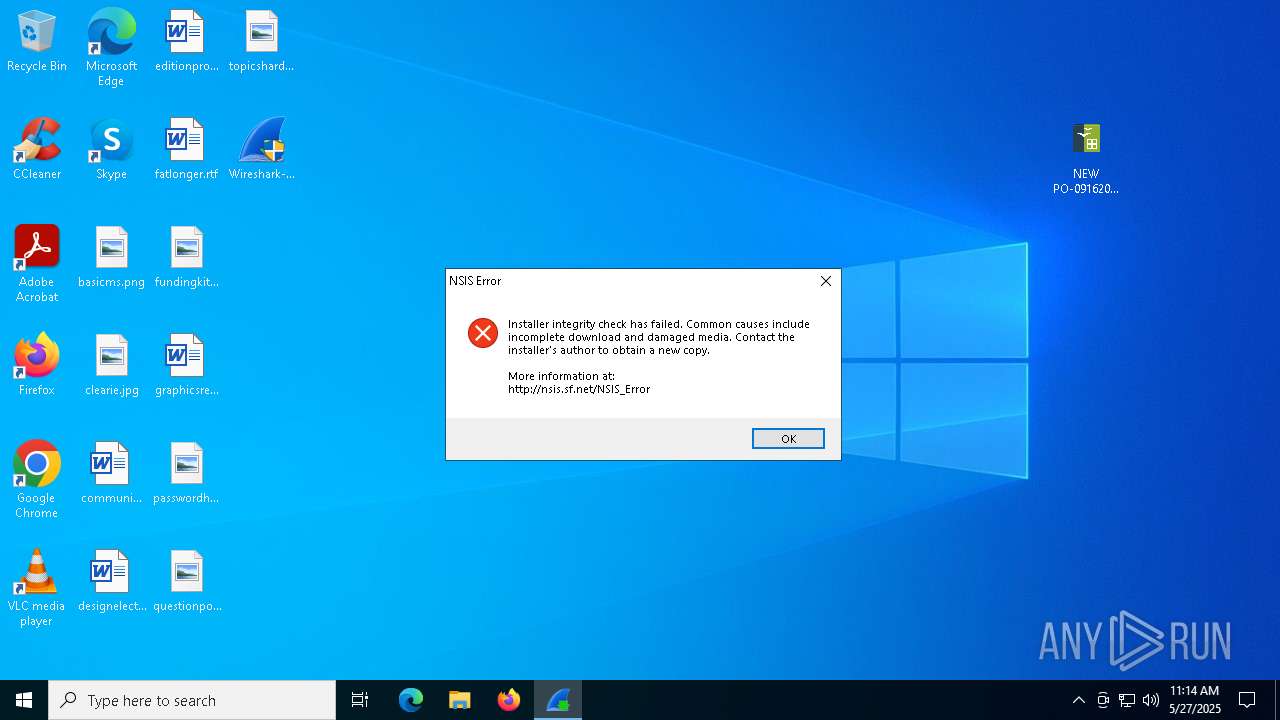
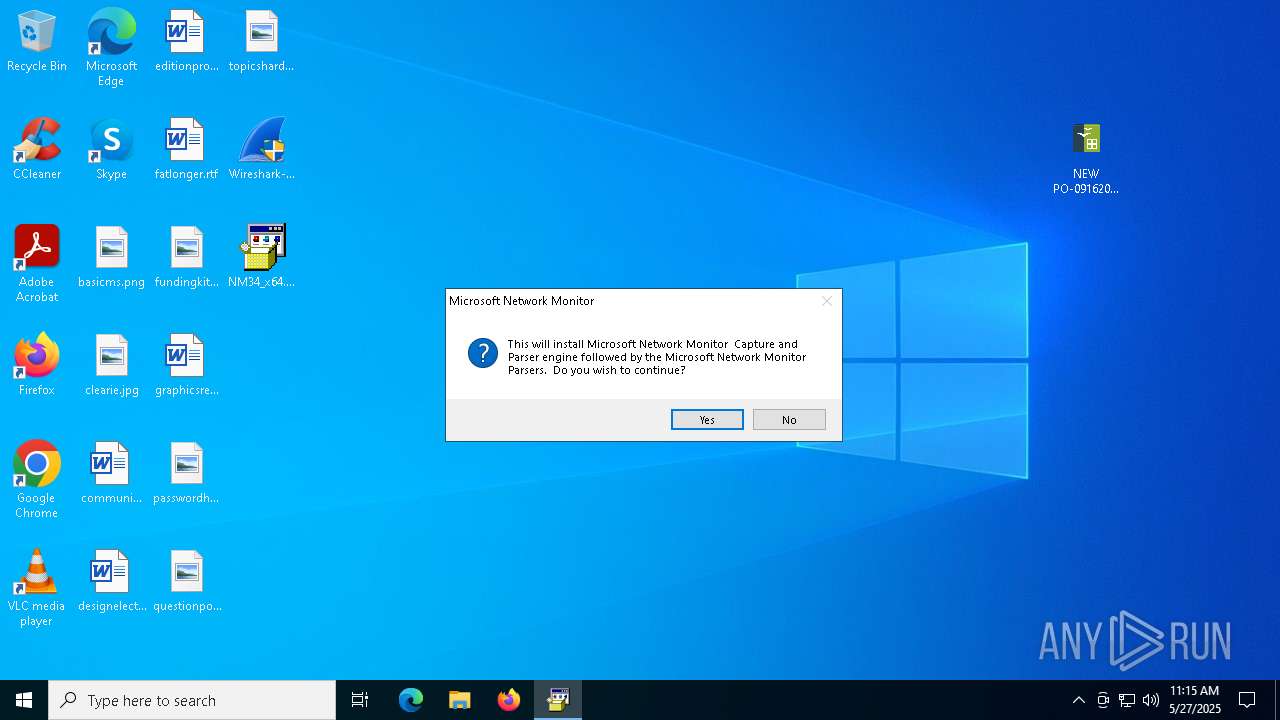
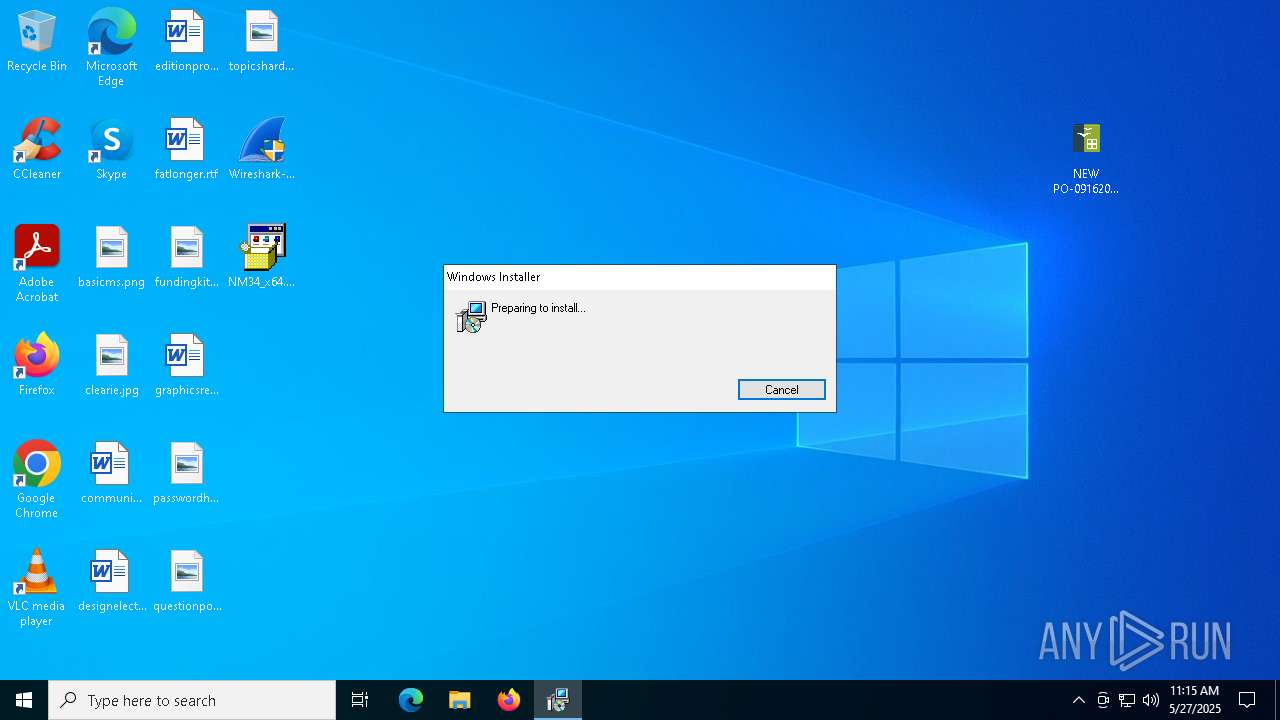
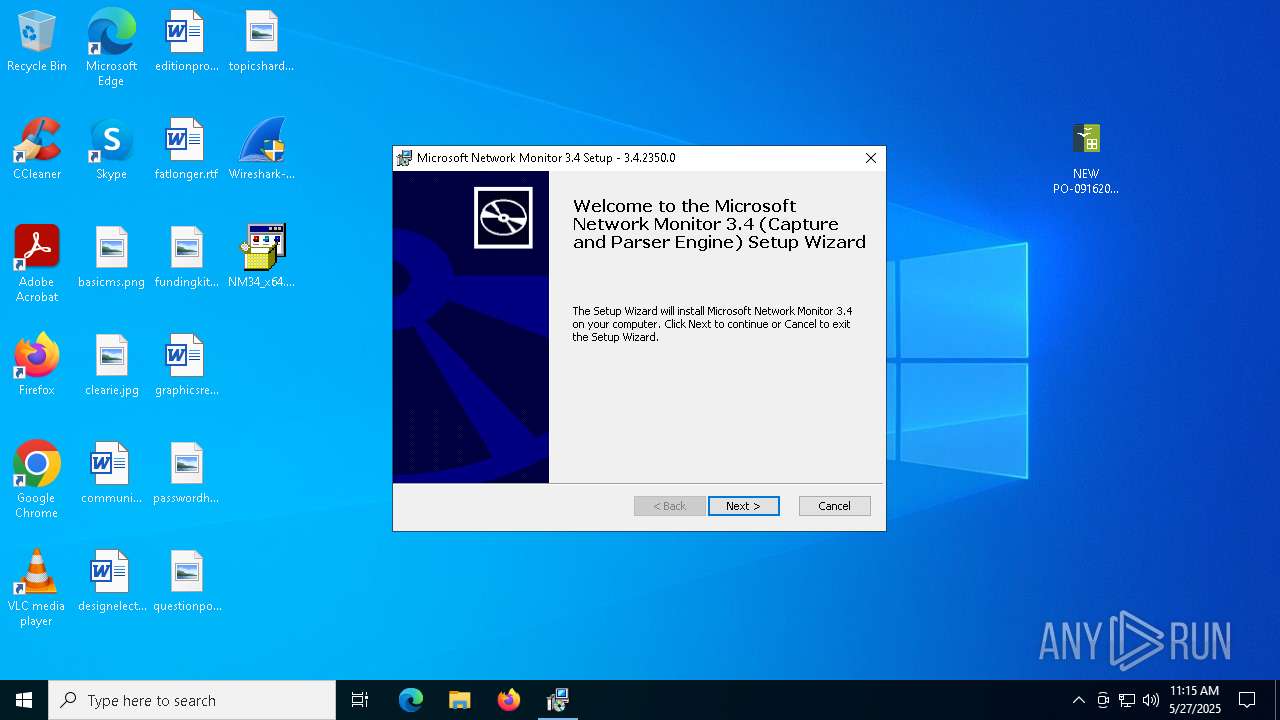
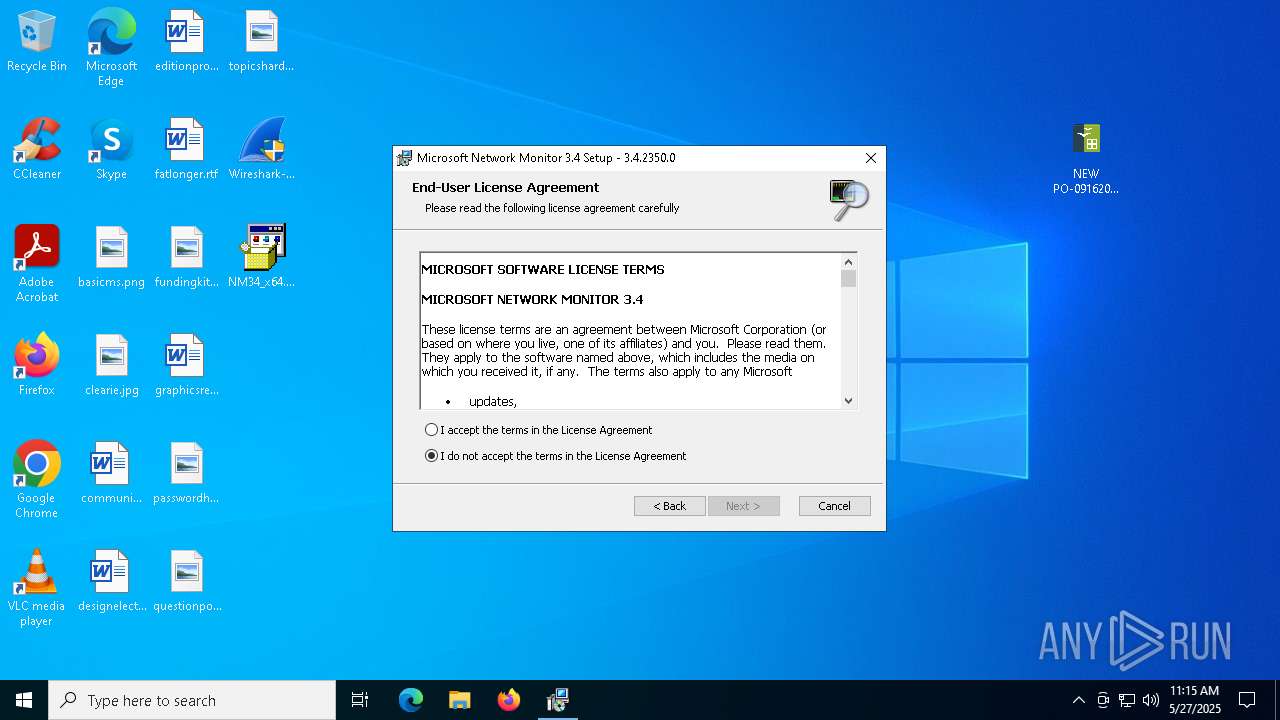
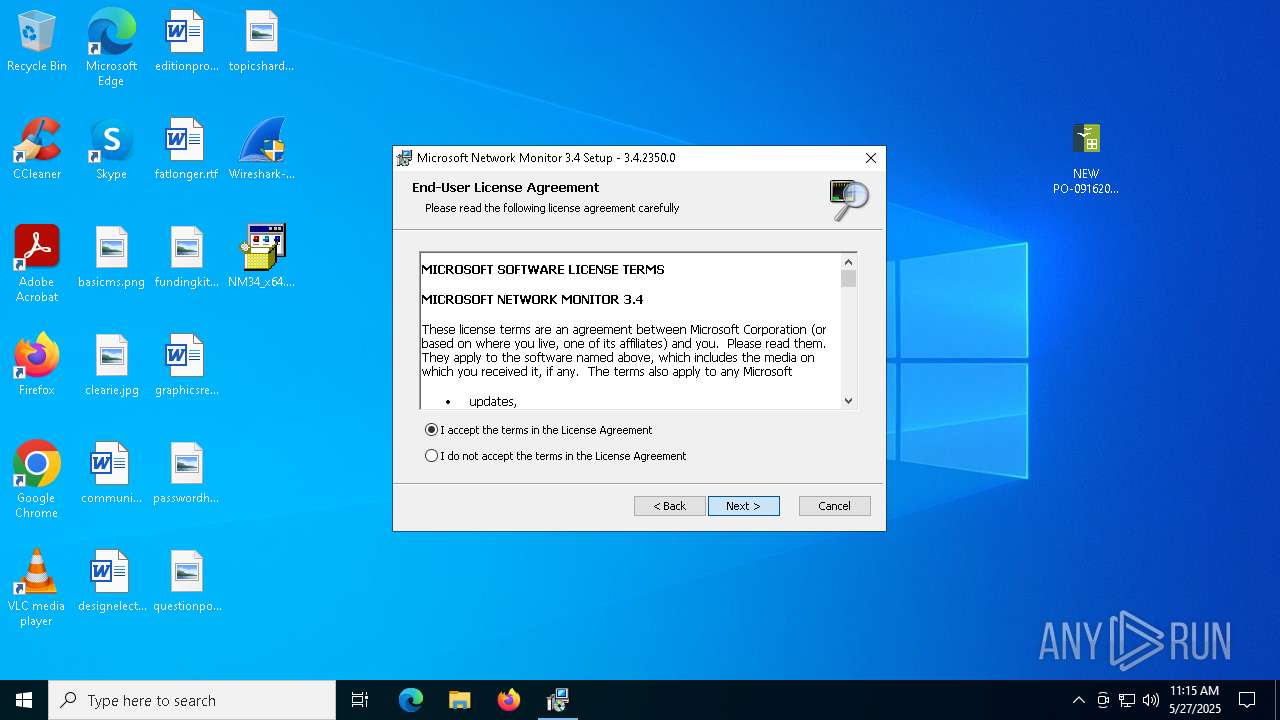
Starts a Microsoft application from unusual location
- NM34_x64.exe (PID: 6560)
The process executes VB scripts
- NM34_x64.exe (PID: 6560)
Executable content was dropped or overwritten
- NM34_x64.exe (PID: 6560)
- wscript.exe (PID: 1472)
Runs WScript without displaying logo
- wscript.exe (PID: 1472)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 1472)
Application launched itself
- msiexec.exe (PID: 4000)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7020)
- msiexec.exe (PID: 1348)
Reads the software policy settings
- slui.exe (PID: 4652)
- slui.exe (PID: 6208)
- msiexec.exe (PID: 1348)
Manual execution by a user
- Wireshark-4.4.6-x64.exe (PID: 1616)
- Wireshark-4.4.6-x64.exe (PID: 6512)
- NM34_x64.exe (PID: 6560)
Reads the computer name
- Wireshark-4.4.6-x64.exe (PID: 6512)
- NM34_x64.exe (PID: 6560)
- msiexec.exe (PID: 4000)
- msiexec.exe (PID: 772)
Checks supported languages
- Wireshark-4.4.6-x64.exe (PID: 6512)
- NM34_x64.exe (PID: 6560)
- msiexec.exe (PID: 4000)
- msiexec.exe (PID: 772)
Checks proxy server information
- slui.exe (PID: 6208)
- msiexec.exe (PID: 1348)
Create files in a temporary directory
- NM34_x64.exe (PID: 6560)
- msiexec.exe (PID: 1348)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1348)
Creates files or folders in the user directory
- msiexec.exe (PID: 1348)
The sample compiled with english language support
- msiexec.exe (PID: 1348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | FileName |
| ModifyDate: | 2024:09:16 11:28:52+00:00 |
| ExtraFlags: | (none) |
| OperatingSystem: | FAT filesystem (MS-DOS, OS/2, NT/Win32) |
| ArchivedFileName: | NEW PO-09162024.exe |
Total processes
143
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 772 | C:\Windows\System32\MsiExec.exe -Embedding 425518D25456F052692067B013A0E7DF C | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1268 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | "C:\Windows\System32\msiexec.exe" /l*v "C:\Users\admin\AppData\Local\Temp\NetmonInstall.log" /i netmon.msi BUILDPROFILES=No | C:\Windows\SysWOW64\msiexec.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1472 | wscript.exe //B //NoLogo nmsetup.vbs | C:\Windows\SysWOW64\wscript.exe | NM34_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1616 | "C:\Users\admin\Desktop\Wireshark-4.4.6-x64.exe" | C:\Users\admin\Desktop\Wireshark-4.4.6-x64.exe | — | explorer.exe | |||||||||||
User: admin Company: Wireshark development team Integrity Level: MEDIUM Description: Wireshark installer for Windows on x64 Exit code: 3221226540 Version: 4.4.6.0 Modules
| |||||||||||||||
| 4000 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4652 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6208 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6512 | "C:\Users\admin\Desktop\Wireshark-4.4.6-x64.exe" | C:\Users\admin\Desktop\Wireshark-4.4.6-x64.exe | explorer.exe | ||||||||||||
User: admin Company: Wireshark development team Integrity Level: HIGH Description: Wireshark installer for Windows on x64 Exit code: 2 Version: 4.4.6.0 Modules
| |||||||||||||||
| 6560 | "C:\Users\admin\Desktop\NM34_x64.exe" | C:\Users\admin\Desktop\NM34_x64.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Version: 8.00.6001.18702 (longhorn_ie8_rtm(wmbla).090308-0339) Modules
| |||||||||||||||
Total events
6 933
Read events
6 915
Write events
18
Delete events
0
Modification events
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\NEW PO-09162024.gz | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7020) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
4
Suspicious files
4
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6560 | NM34_x64.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\netmon.msi | — | |
MD5:— | SHA256:— | |||
| 1348 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A1377F7115F1F126A15360369B165211 | binary | |
MD5:9311B3EE7EEF967589A7A7FB2221CAB1 | SHA256:F9083796849C86AE2FFB21AFC6B68C8ACBFCA65CC75D3E7463FC213D6635405D | |||
| 6560 | NM34_x64.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\nmsetup.vbs | text | |
MD5:E6B8136151BF4066694CEE0BF43E3F83 | SHA256:62ACBB3DEF015A92B78AB3298E11F7182735227EC50AD959746C5EBBD885197D | |||
| 7020 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7020.15399\NEW PO-09162024.exe | executable | |
MD5:B2B44061F8271AD0F7D3A4FEBEB07751 | SHA256:BC5EE788C33389A426C9B5B10405A41A83F6875864BF09B0DE6DF15AB88CFBDA | |||
| 6560 | NM34_x64.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\NetworkMonitor_Parsers.msi | executable | |
MD5:576DFFDAACFFA4239364052416CBA8FE | SHA256:431582BB01F000118222E58F9F7A0B6C8FEA39CDCEFE821F90BCF22E8693663F | |||
| 1472 | wscript.exe | C:\Users\admin\AppData\Local\Temp\NetworkMonitor_Parsers.msi | executable | |
MD5:576DFFDAACFFA4239364052416CBA8FE | SHA256:431582BB01F000118222E58F9F7A0B6C8FEA39CDCEFE821F90BCF22E8693663F | |||
| 1348 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:ED1EF01C760A506DAA3A34963D9CF874 | SHA256:D6CA0BB62AD7B03AE55C7945FD214D37F5E4FBE0D8C74DE2DFAB6D80F2348679 | |||
| 1348 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIA674.tmp | executable | |
MD5:4709FC18727B499F16FE989007E91C9F | SHA256:F47199027A4F54671C1B64E7A7AC3A87EE9F630859E3F70D1129D62AAC7DA6E6 | |||
| 1348 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A1377F7115F1F126A15360369B165211 | binary | |
MD5:5CEA4AC57BD53F714D95BB57EF5BCAEF | SHA256:24A3CA790CDCA5DC9014BD6397B07F25DC33BB58D4B2A676D4C304BD397A9CC5 | |||
| 1348 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:6872FAE8288DB34207D9E7EE350157F4 | SHA256:50795B027E2BC566D3B7ACB89913F8EFD23B70615C9DB9BF5B23323AD3132A7D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
22
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2284 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2284 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1348 | msiexec.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
1348 | msiexec.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/CodeSigPCA.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5008 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5796 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |