| File name: | 1.exe |
| Full analysis: | https://app.any.run/tasks/0a4c8879-5168-4aa7-8858-9ac153363a9e |
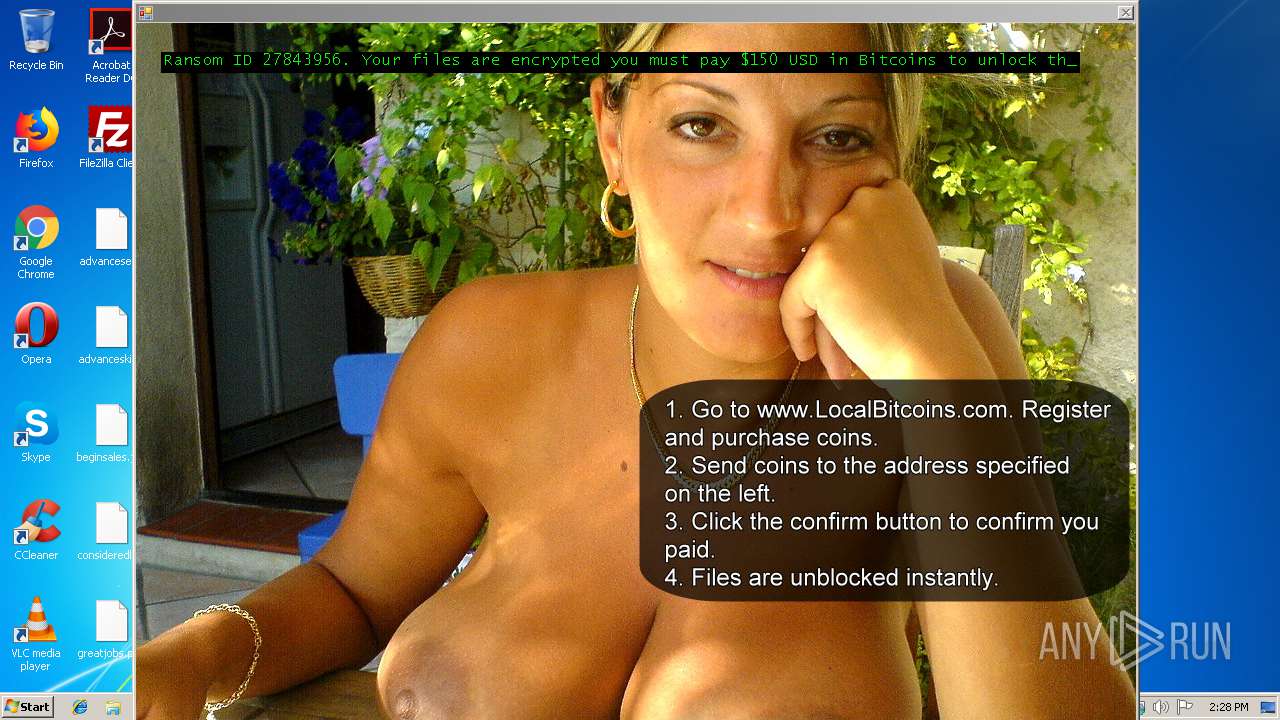
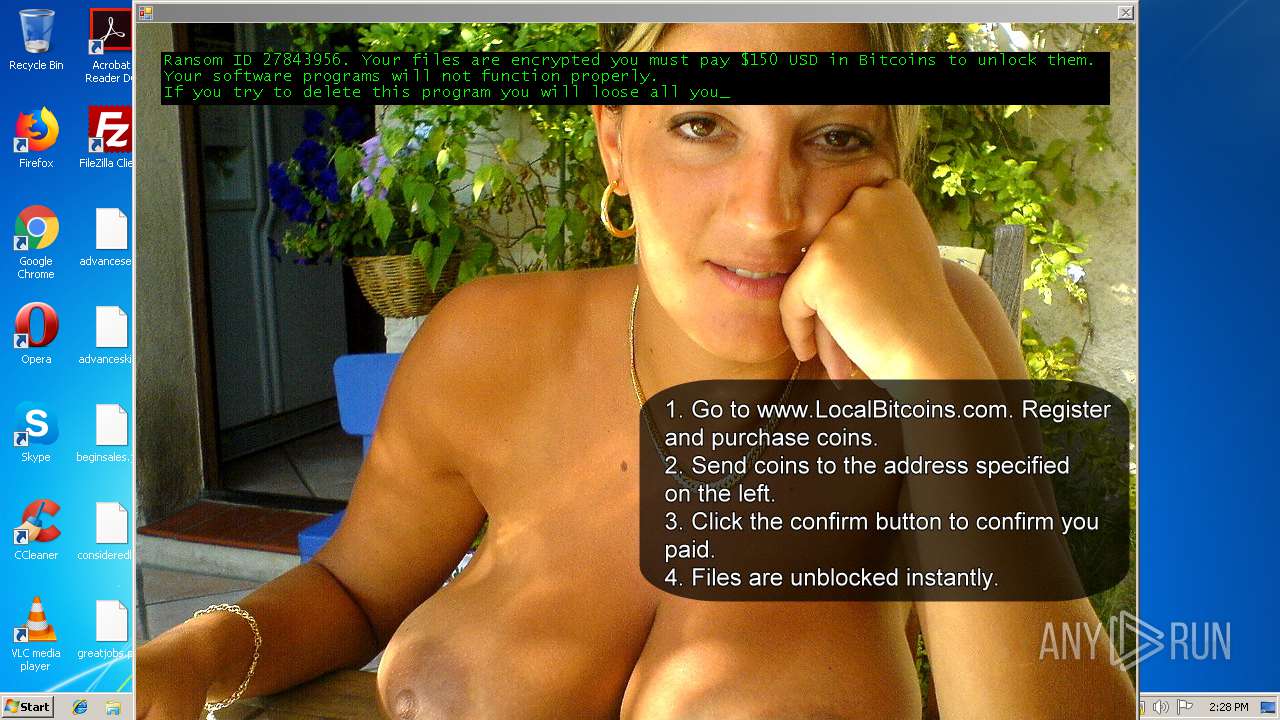
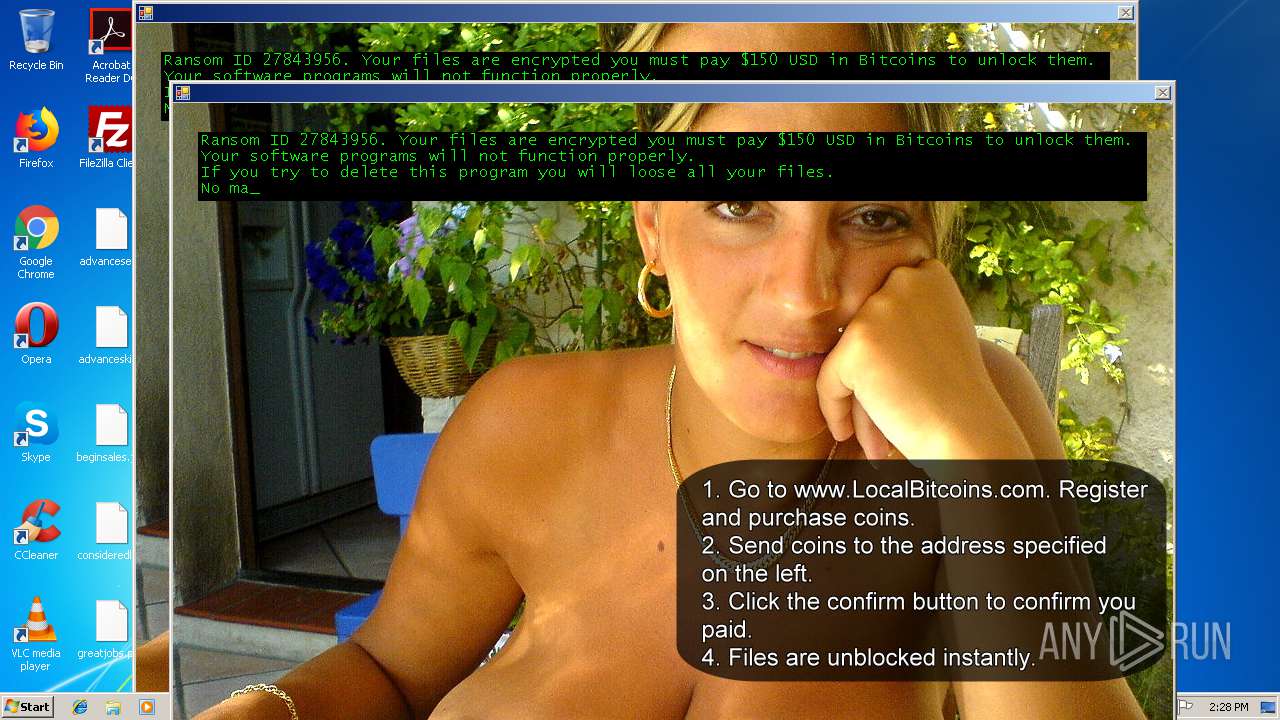
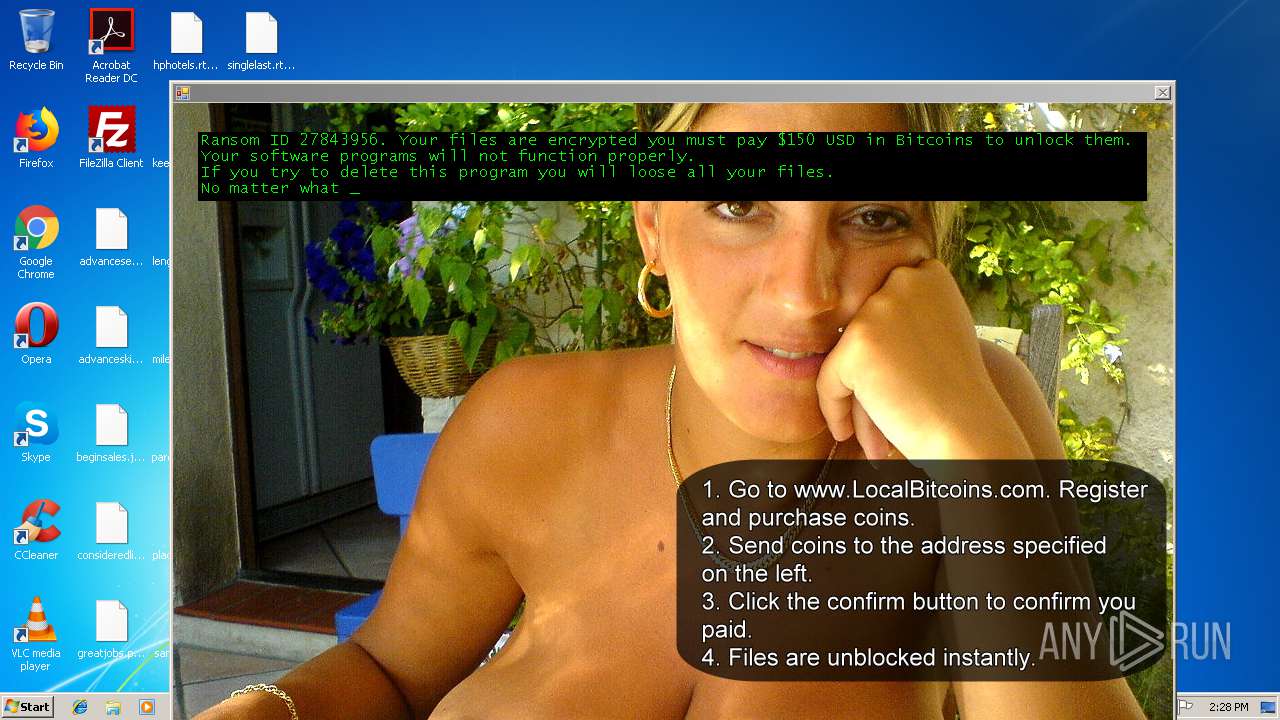
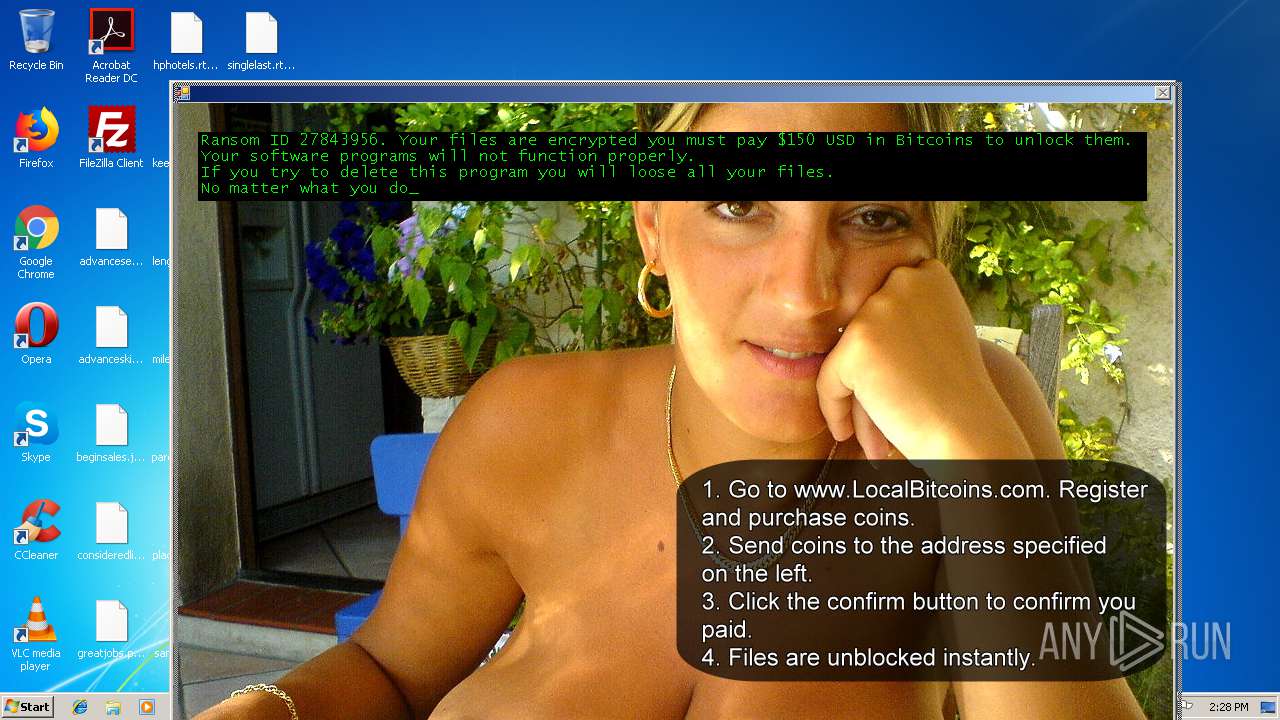
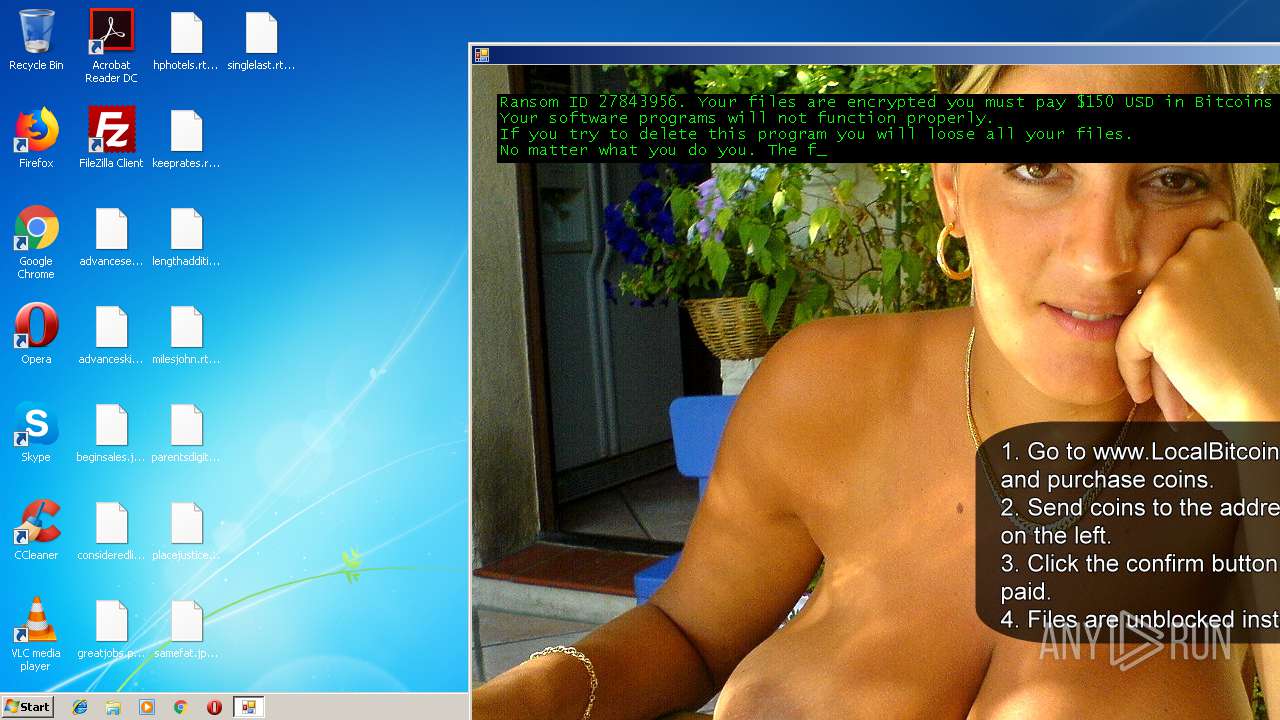
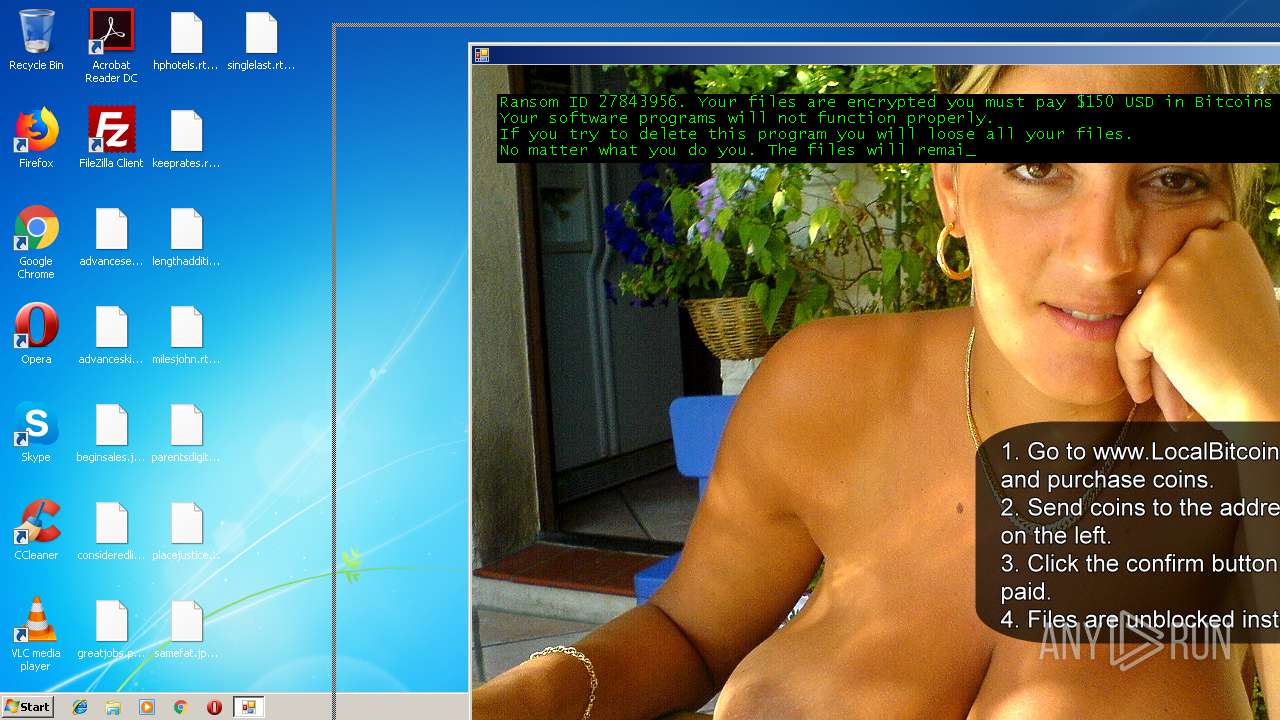
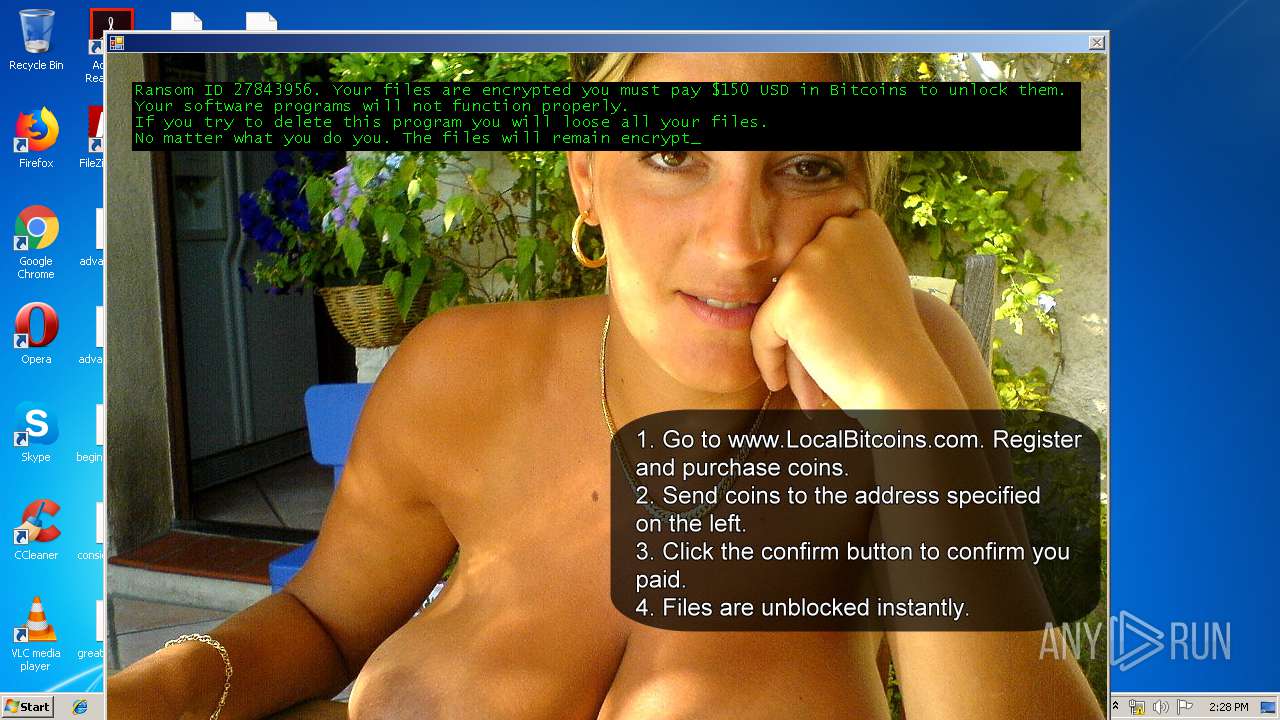
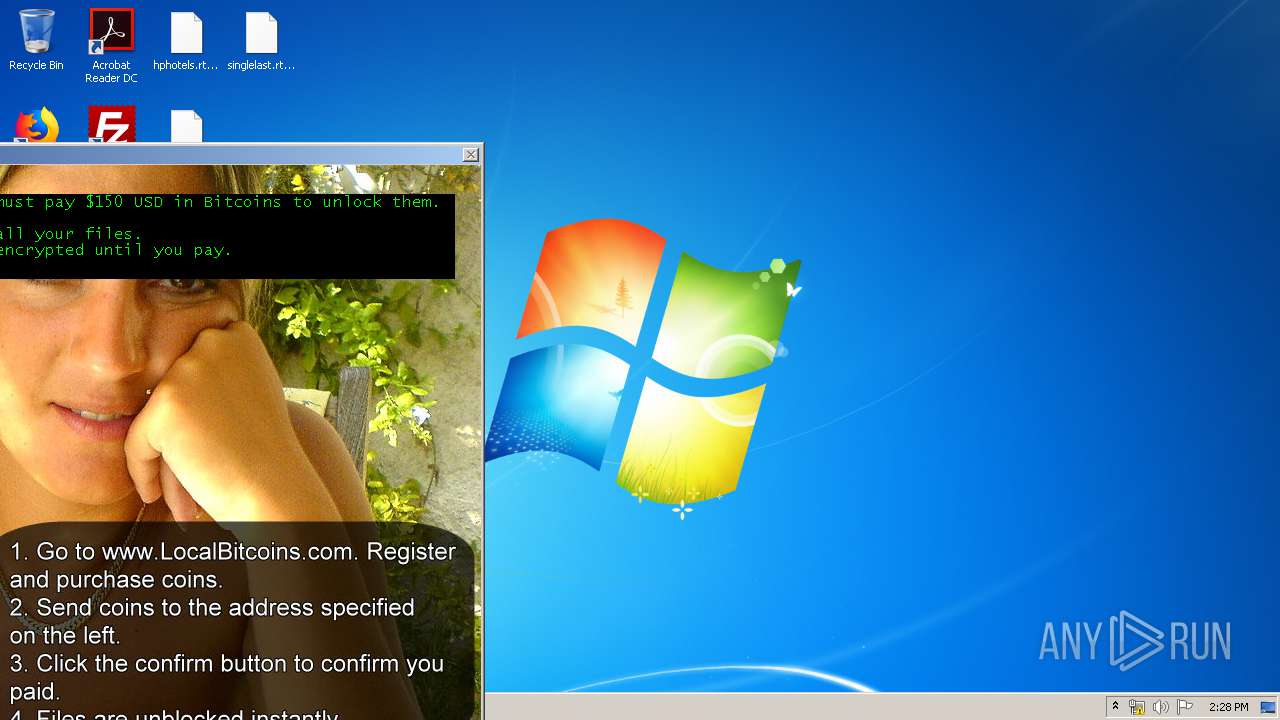
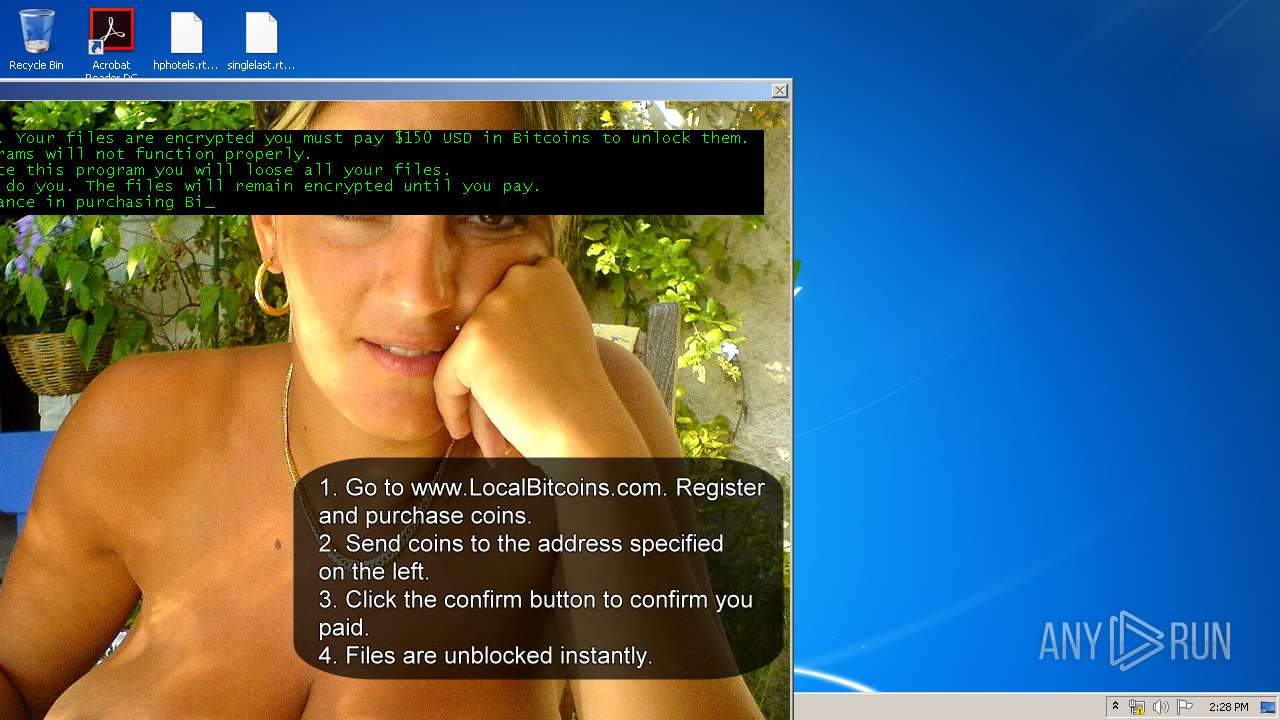
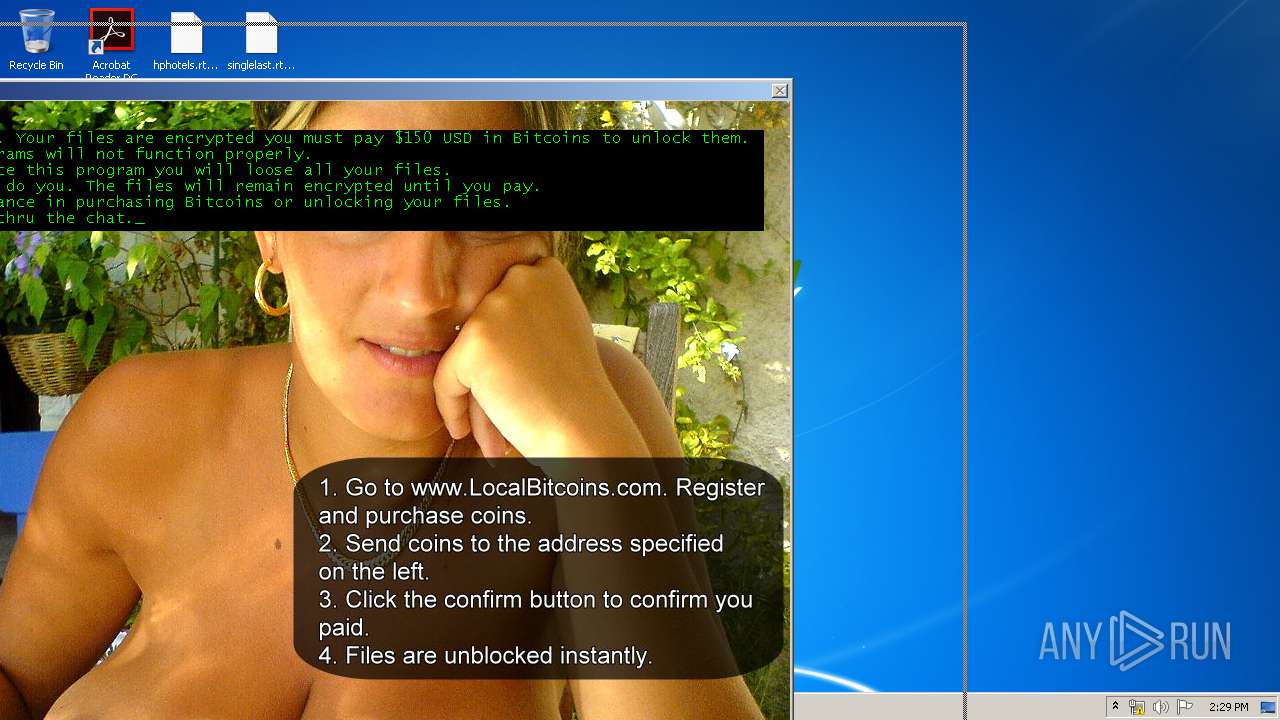
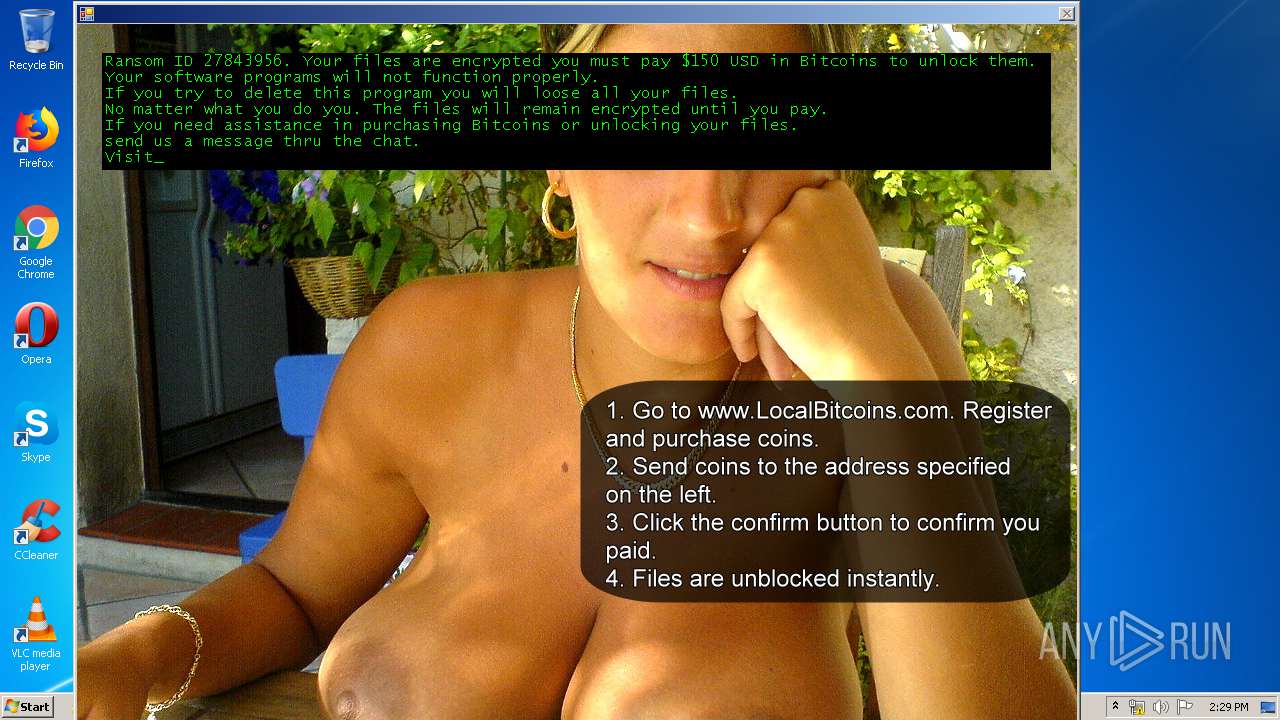
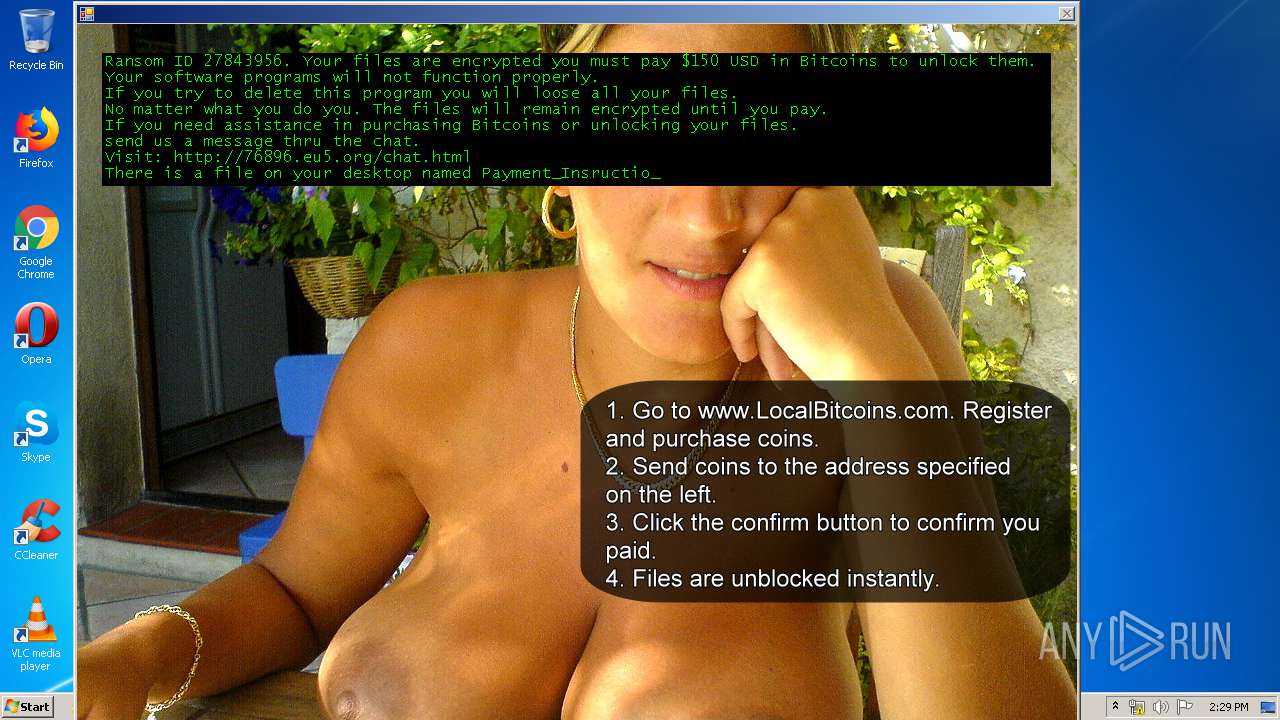
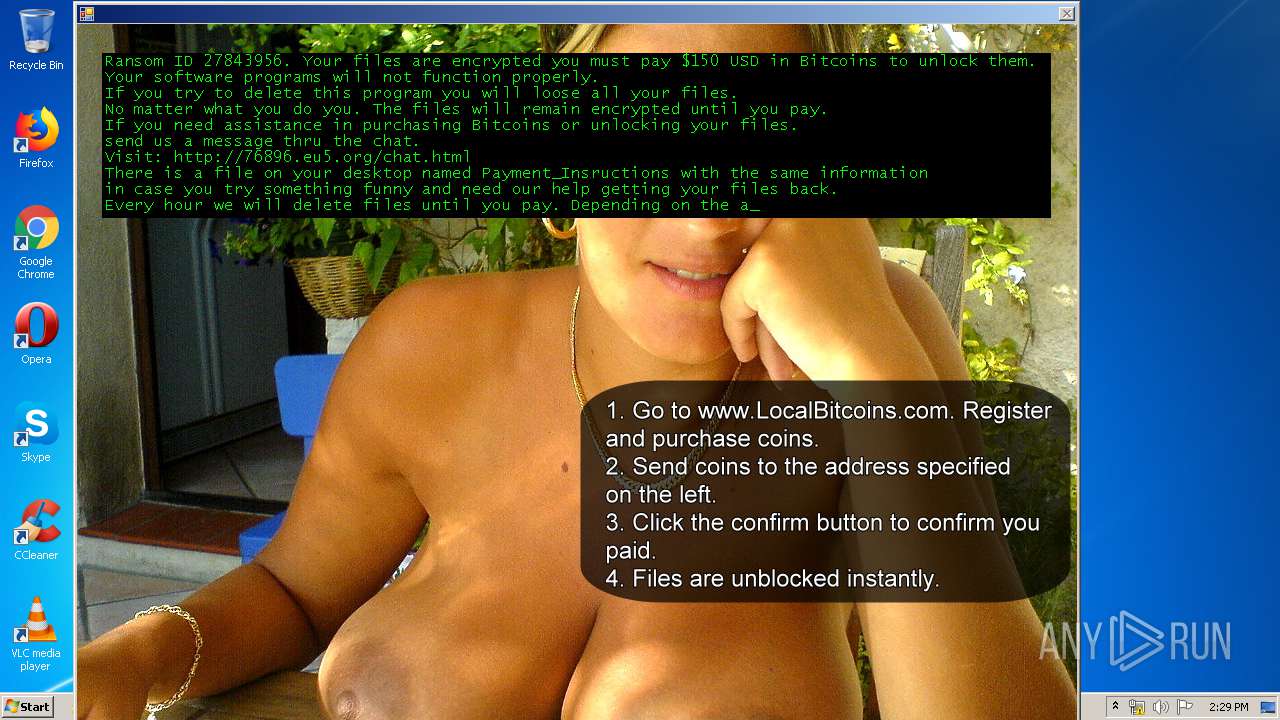
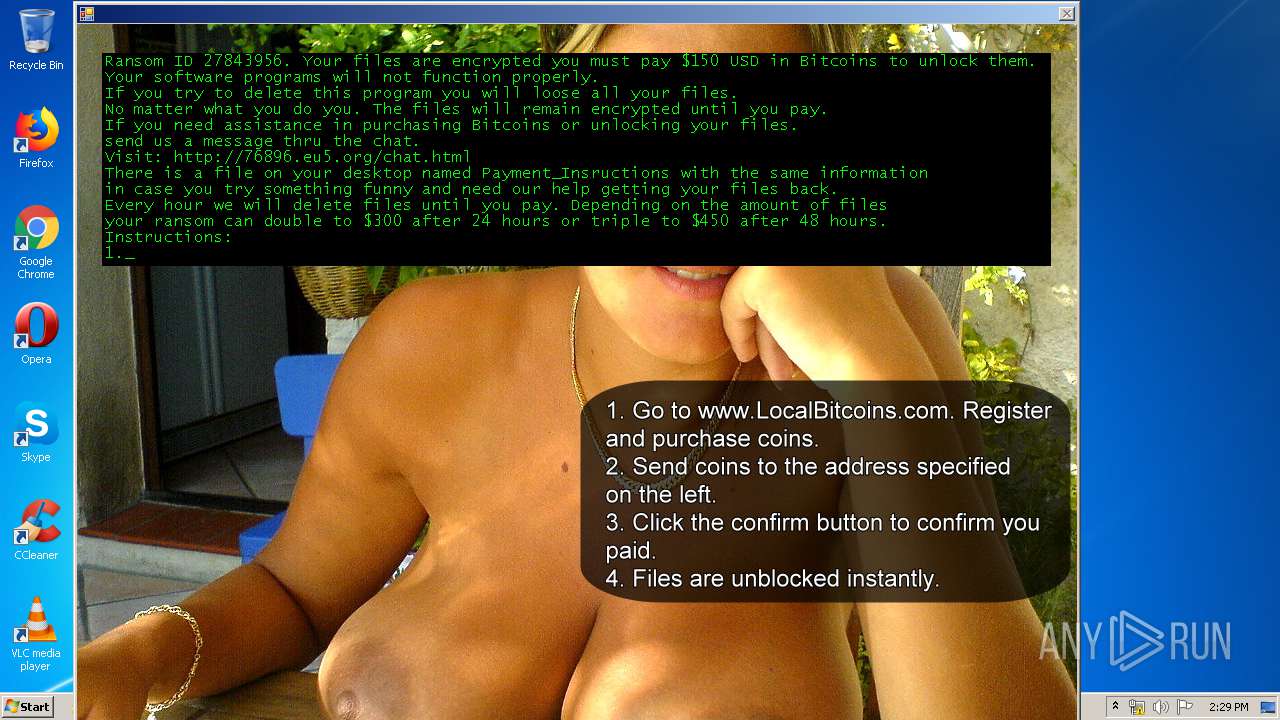
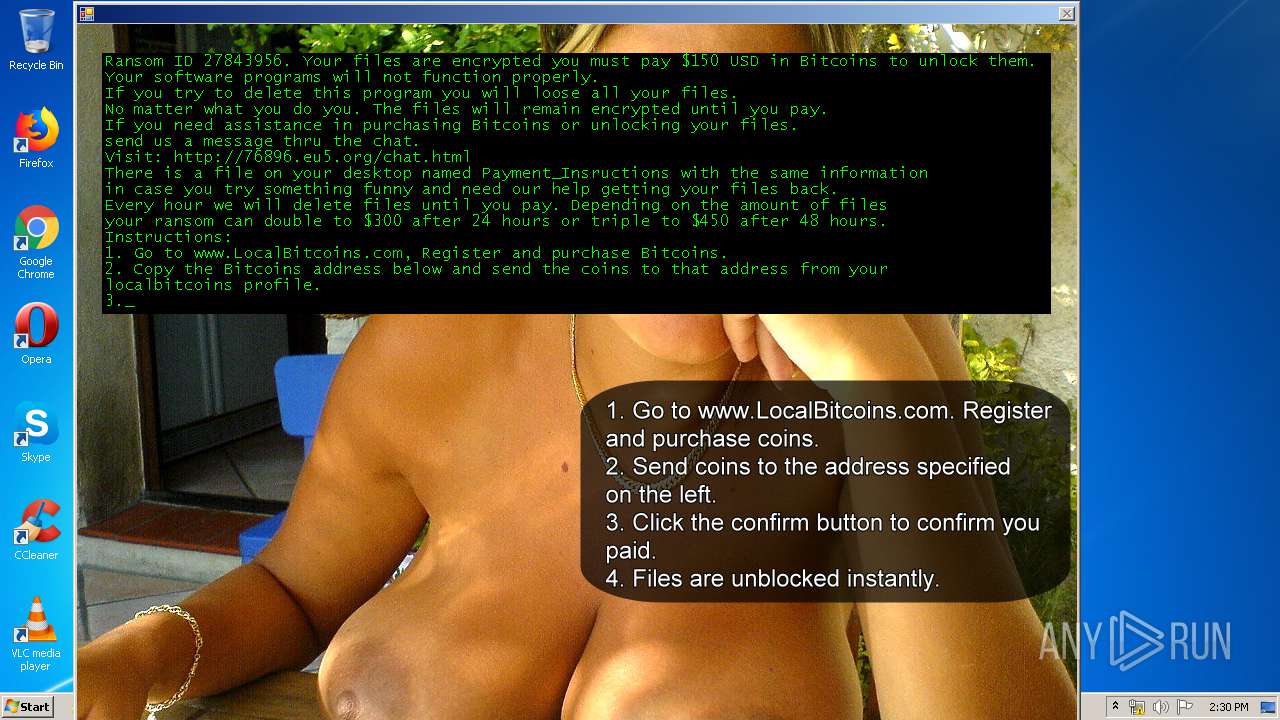
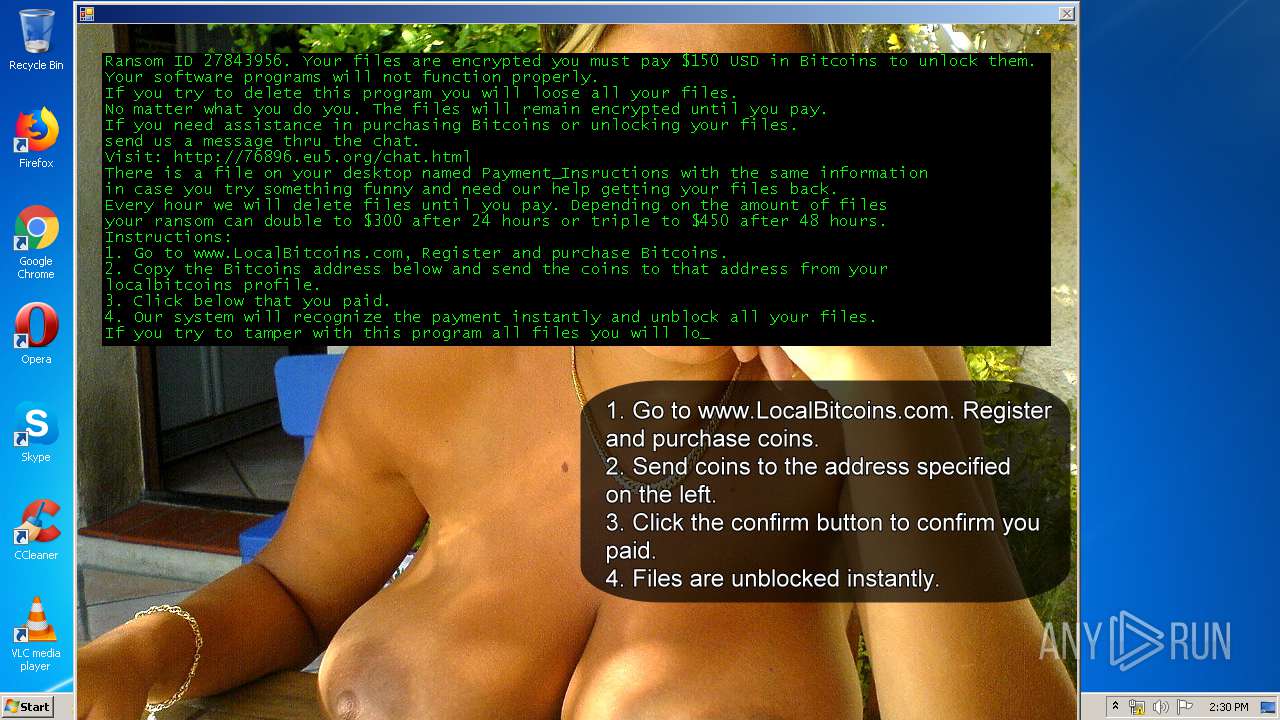
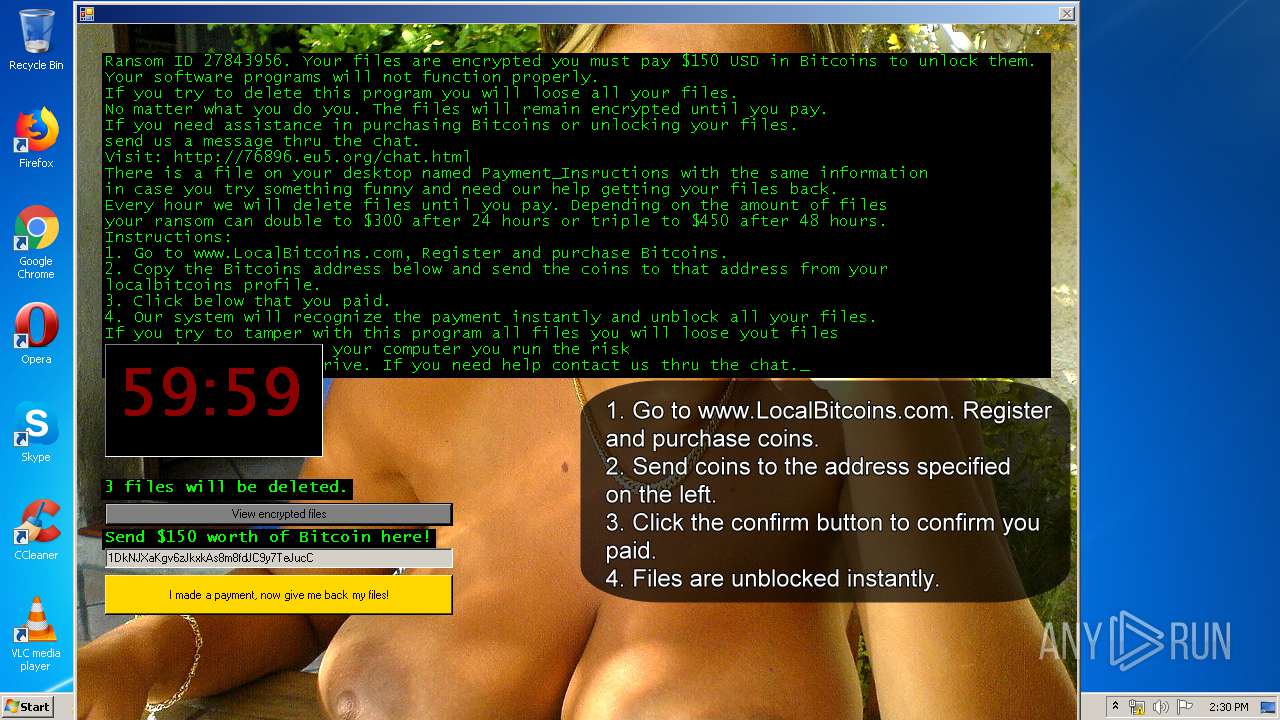
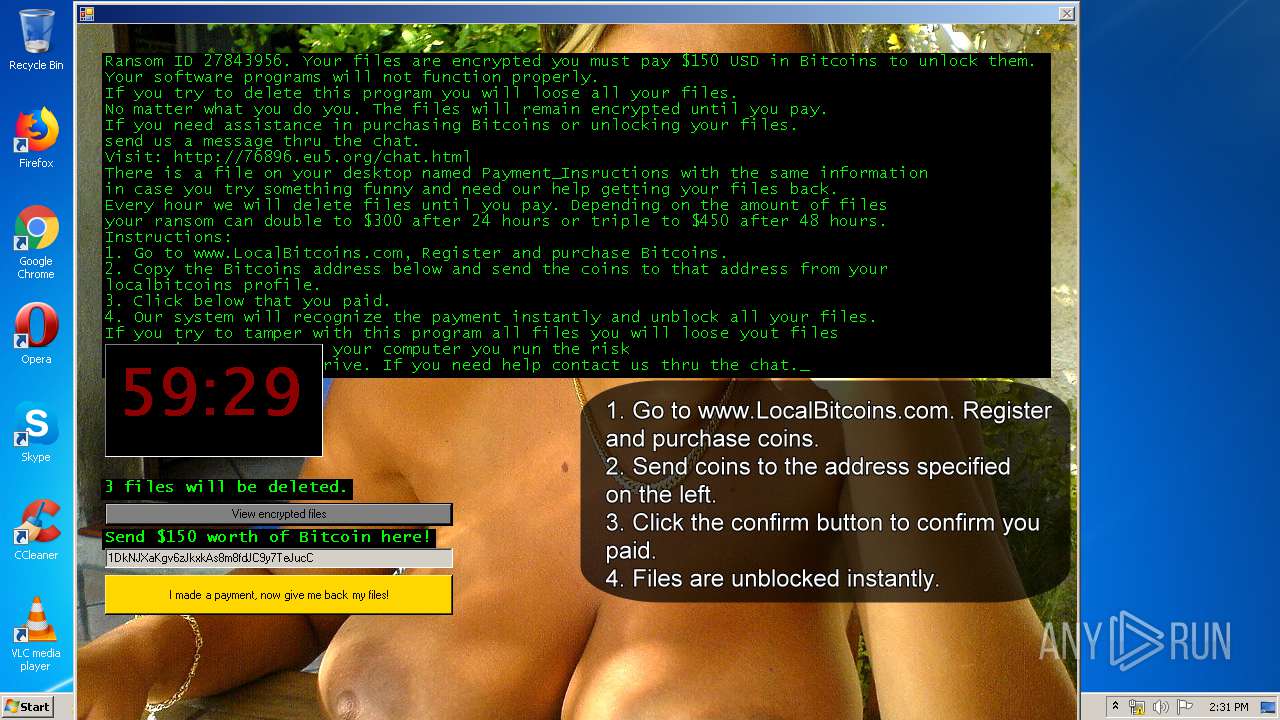
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 14:27:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 26B3DB3AC5BD9DCFCB485C9E0C200A80 |
| SHA1: | DDC3A547711FE0A4CD3AFFB3924BEEBA87B9F60B |
| SHA256: | 0B164FC0270C83F0D5C3AC554421CFBCCD0404AE7C79F700AA485FDF86912EF4 |
| SSDEEP: | 12288:SlM0k4H7DEUhNfHXQn+yR/3RHzsmP+agVznWqZa/Cr78:MjMUh1HXQL/BHzsmGTGK |
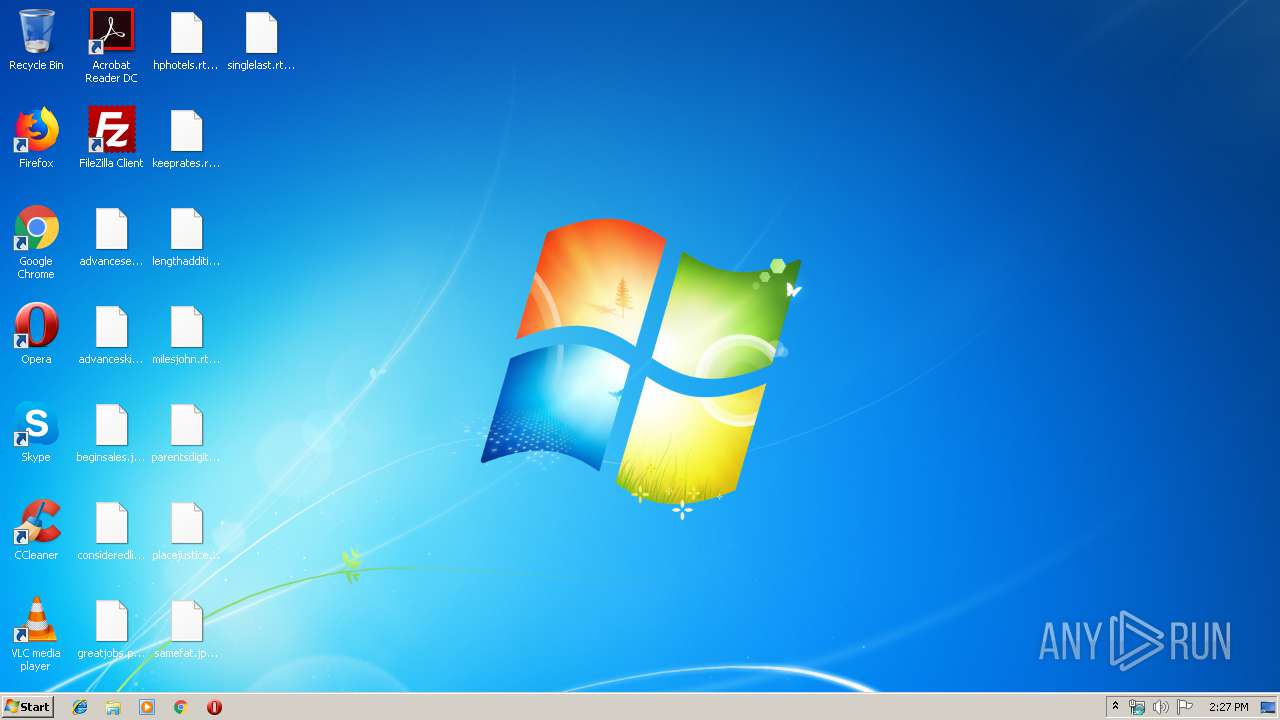
MALICIOUS
Changes the autorun value in the registry
- 1.exe (PID: 1052)
Modifies files in Chrome extension folder
- Vistmp.exe (PID: 4028)
Actions looks like stealing of personal data
- Vistmp.exe (PID: 4028)
SUSPICIOUS
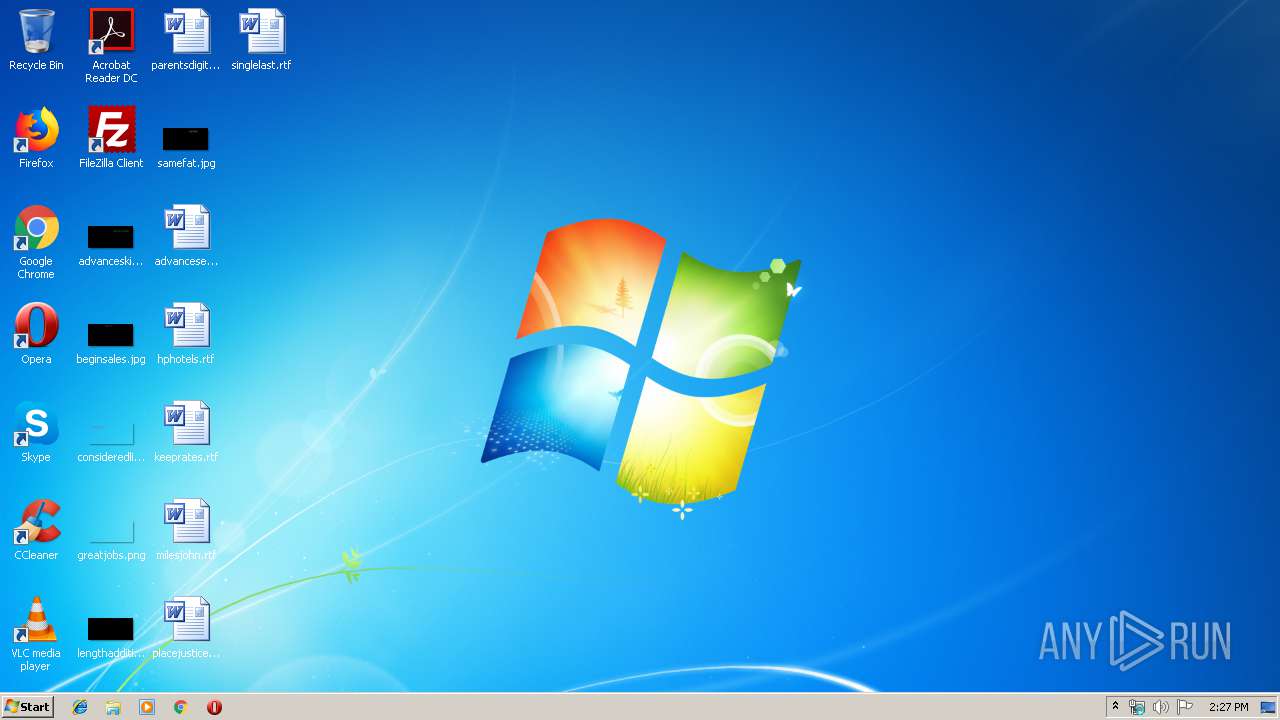
Creates files in the user directory
- 1.exe (PID: 1052)
- Vistmp.exe (PID: 4028)
Starts itself from another location
- 1.exe (PID: 1052)
Executable content was dropped or overwritten
- 1.exe (PID: 1052)
Creates files in the program directory
- Vistmp.exe (PID: 4028)
INFO
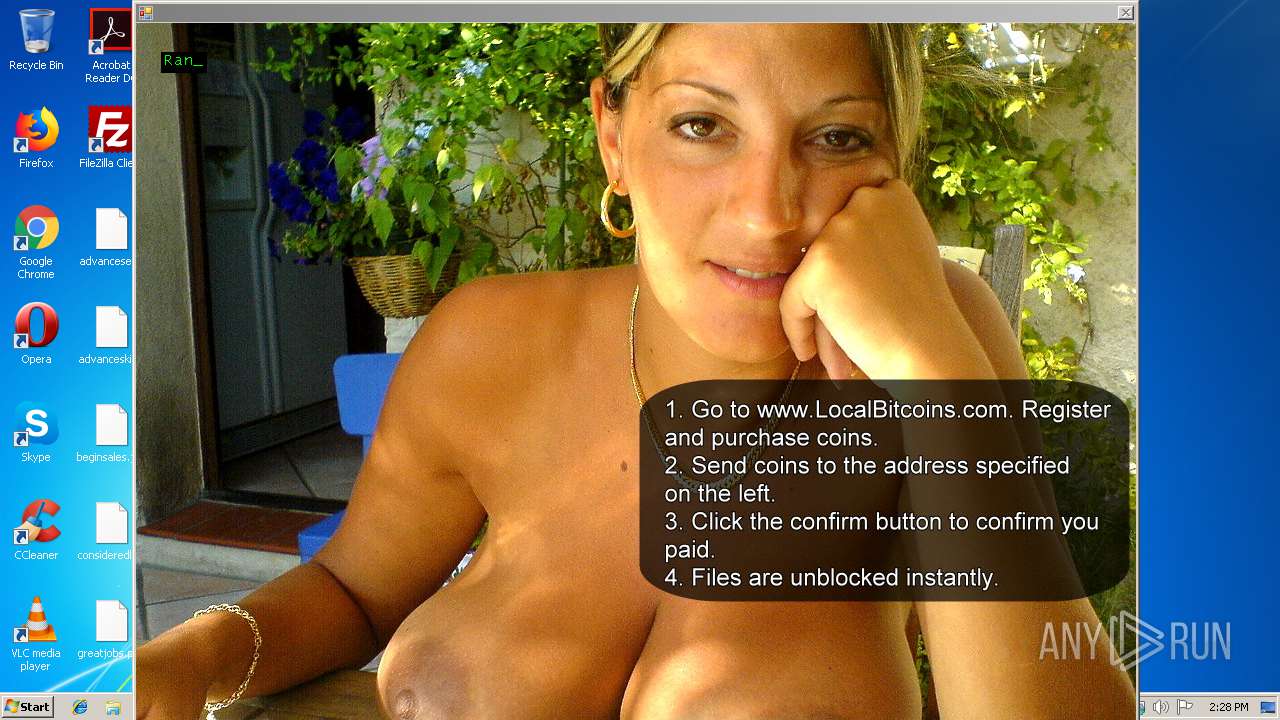
Dropped object may contain Bitcoin addresses
- Vistmp.exe (PID: 4028)
- 1.exe (PID: 1052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:06:03 21:43:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 531456 |
| InitializedDataSize: | 533504 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x83b72 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.0.16 |
| ProductVersionNumber: | 3.5.0.16 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | VirtuMalks |
| CompanyName: | VirtuMalks Corporation |
| FileDescription: | VirtuMalks |
| FileVersion: | 3.5.00.16 |
| InternalName: | BitcoinBlackmailer.exe |
| LegalCopyright: | Copyright (C) 2010-2016 VirtuMalks Corp. All rights reserved. |
| LegalTrademarks: | Copyright (C) 2010-2016 VirtualMaller Corporation. All rights reserved. |
| OriginalFileName: | BitcoinBlackmailer.exe |
| ProductName: | VirtuMalks |
| ProductVersion: | 3.5.00.16 |
| AssemblyVersion: | 2.4.5.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jun-2016 19:43:00 |
| Debug artifacts: |
|
| Comments: | VirtuMalks |
| CompanyName: | VirtuMalks Corporation |
| FileDescription: | VirtuMalks |
| FileVersion: | 3.5.00.16 |
| InternalName: | BitcoinBlackmailer.exe |
| LegalCopyright: | Copyright (C) 2010-2016 VirtuMalks Corp. All rights reserved. |
| LegalTrademarks: | Copyright (C) 2010-2016 VirtualMaller Corporation. All rights reserved. |
| OriginalFilename: | BitcoinBlackmailer.exe |
| ProductName: | VirtuMalks |
| ProductVersion: | 3.5.00.16 |
| Assembly Version: | 2.4.5.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 03-Jun-2016 19:43:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00081B78 | 0x00081C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.82567 |
.reloc | 0x00084000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
.rsrc | 0x00086000 | 0x00000704 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.79731 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
32
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1052 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | explorer.exe | ||||||||||||
User: admin Company: VirtuMalks Corporation Integrity Level: MEDIUM Description: VirtuMalks Exit code: 0 Version: 3.5.00.16 Modules
| |||||||||||||||
| 4028 | "C:\Users\admin\AppData\Local\Vistmp\Vistmp.exe" C:\Users\admin\AppData\Local\Temp\1.exe | C:\Users\admin\AppData\Local\Vistmp\Vistmp.exe | 1.exe | ||||||||||||
User: admin Company: VirtuMalks Corporation Integrity Level: MEDIUM Description: VirtuMalks Exit code: 0 Version: 3.5.00.16 Modules
| |||||||||||||||
Total events
365
Read events
360
Write events
5
Delete events
0
Modification events
| (PID) Process: | (1052) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Mainsdc.exe |
Value: C:\Users\admin\AppData\Roaming\Mainsdc\Mainsdc.exe | |||
| (PID) Process: | (1052) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1052) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
489
Text files
10
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4028 | Vistmp.exe | C:\Users\admin\Desktop\beginsales.jpg.paym | binary | |
MD5:— | SHA256:— | |||
| 4028 | Vistmp.exe | C:\Users\admin\Desktop\advanceseen.rtf.paym | binary | |
MD5:— | SHA256:— | |||
| 4028 | Vistmp.exe | C:\Users\admin\Desktop\advanceskip.jpg.paym | binary | |
MD5:— | SHA256:— | |||
| 1052 | 1.exe | C:\Users\admin\AppData\Roaming\Mainsdc\Mainsdc.exe | executable | |
MD5:— | SHA256:— | |||
| 4028 | Vistmp.exe | C:\Users\admin\Desktop\lengthadditional.jpg.paym | binary | |
MD5:— | SHA256:— | |||
| 4028 | Vistmp.exe | C:\ProgramData\Microsoft\User Account Pictures\admin.dat.paym | text | |
MD5:121979B4A4E2C587C2C831789E9755A5 | SHA256:94521D1368290FCEBA753ACE00B211DE549B18CE9AE264BE89CE75D6CDA02F98 | |||
| 1052 | 1.exe | C:\Users\admin\AppData\Local\Vistmp\Vistmp.exe | executable | |
MD5:— | SHA256:— | |||
| 4028 | Vistmp.exe | C:\Users\admin\Desktop\greatjobs.png.paym | binary | |
MD5:— | SHA256:— | |||
| 4028 | Vistmp.exe | C:\Users\admin\Desktop\placejustice.rtf.paym | binary | |
MD5:— | SHA256:— | |||
| 4028 | Vistmp.exe | C:\Users\admin\Desktop\keeprates.rtf.paym | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report