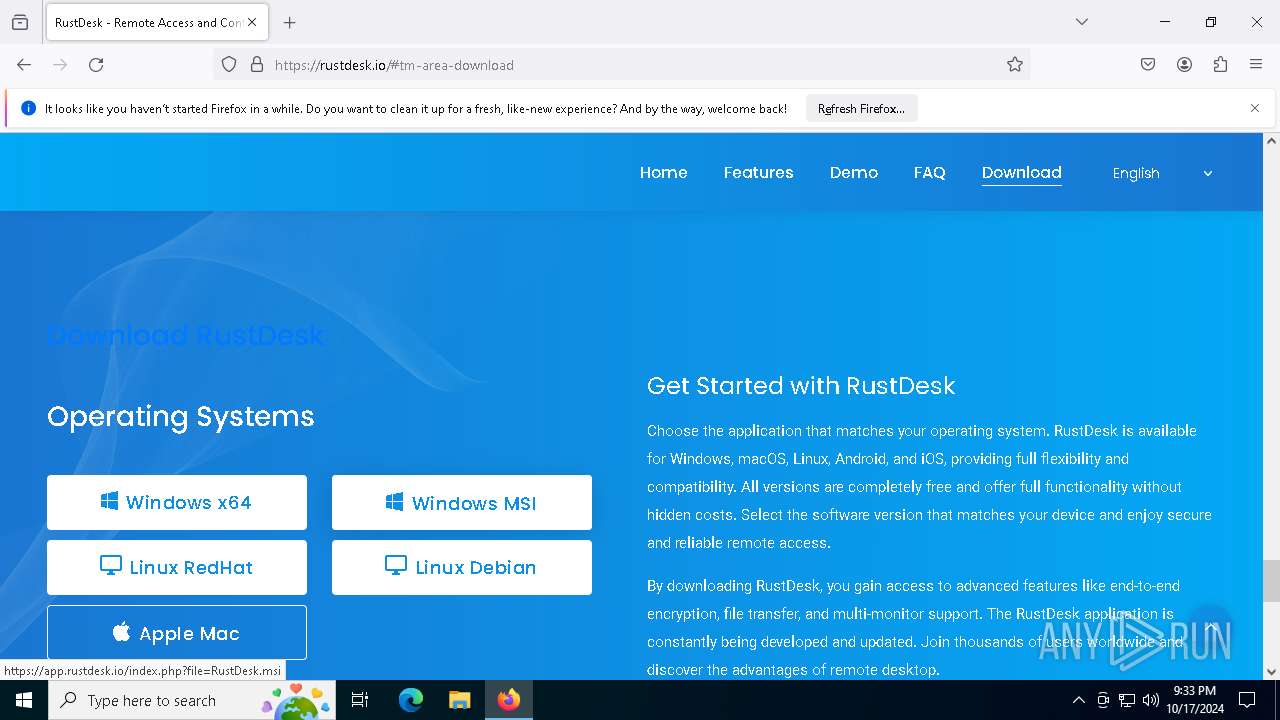
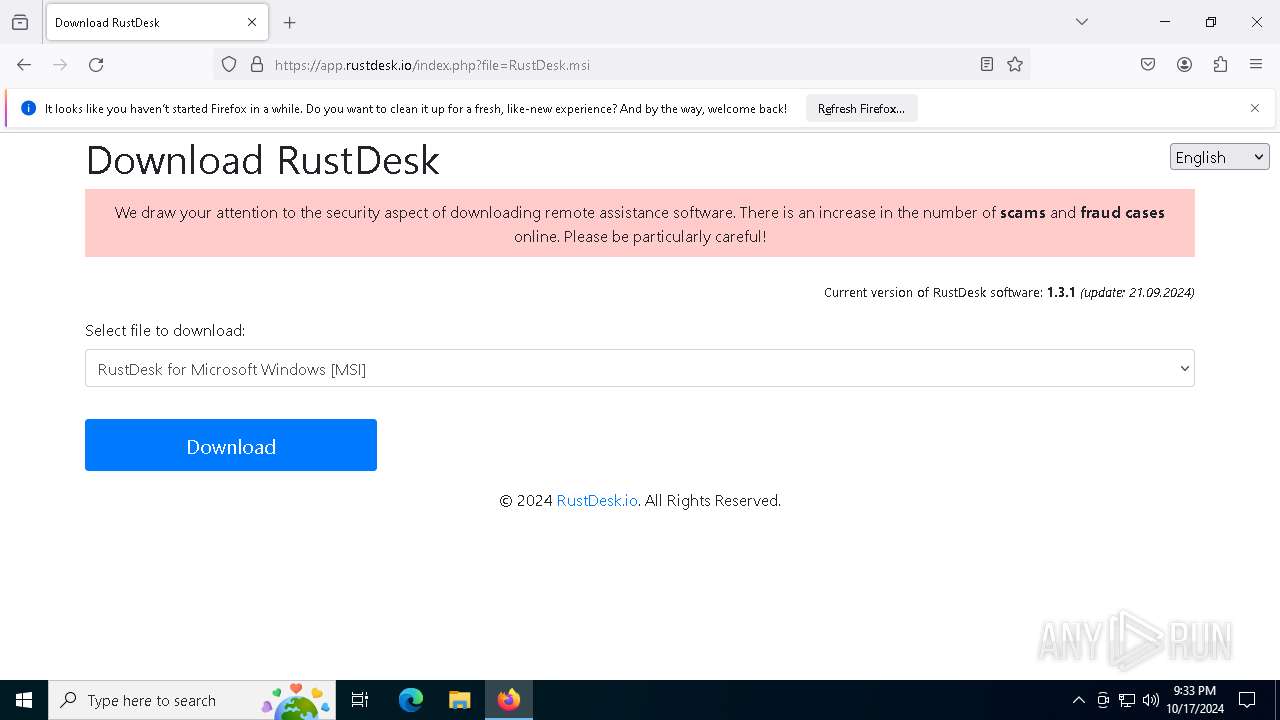
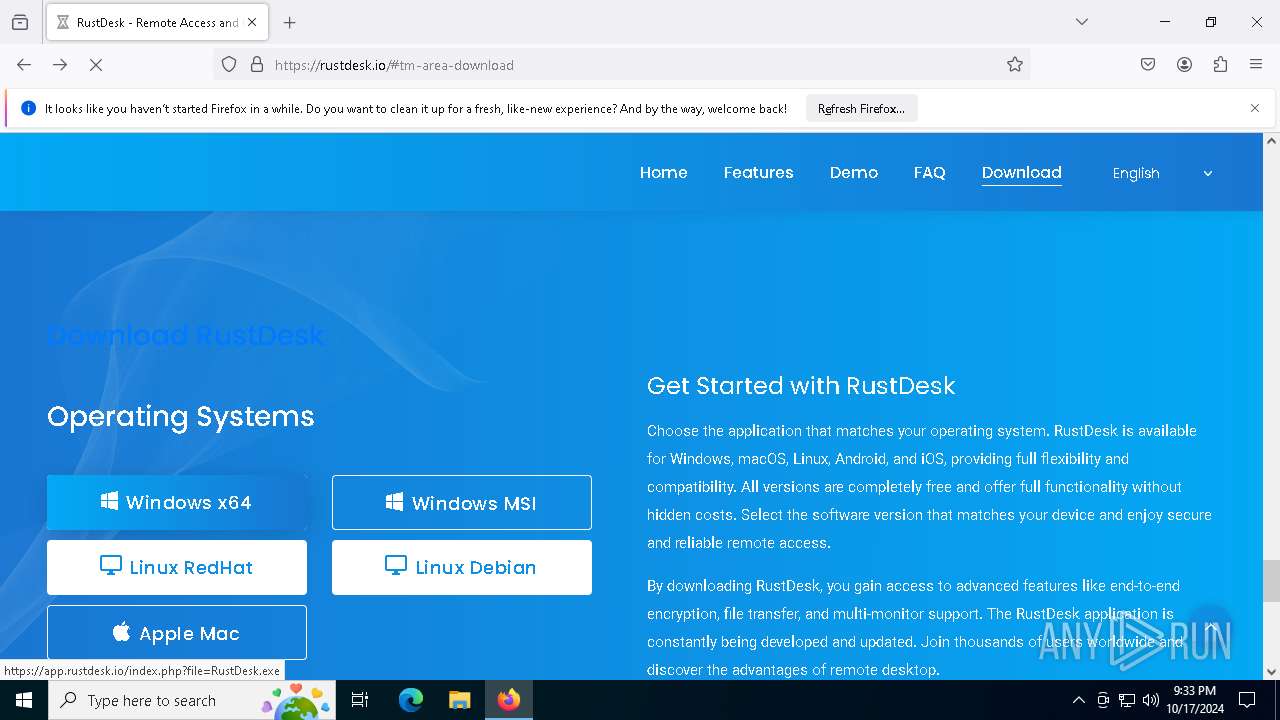
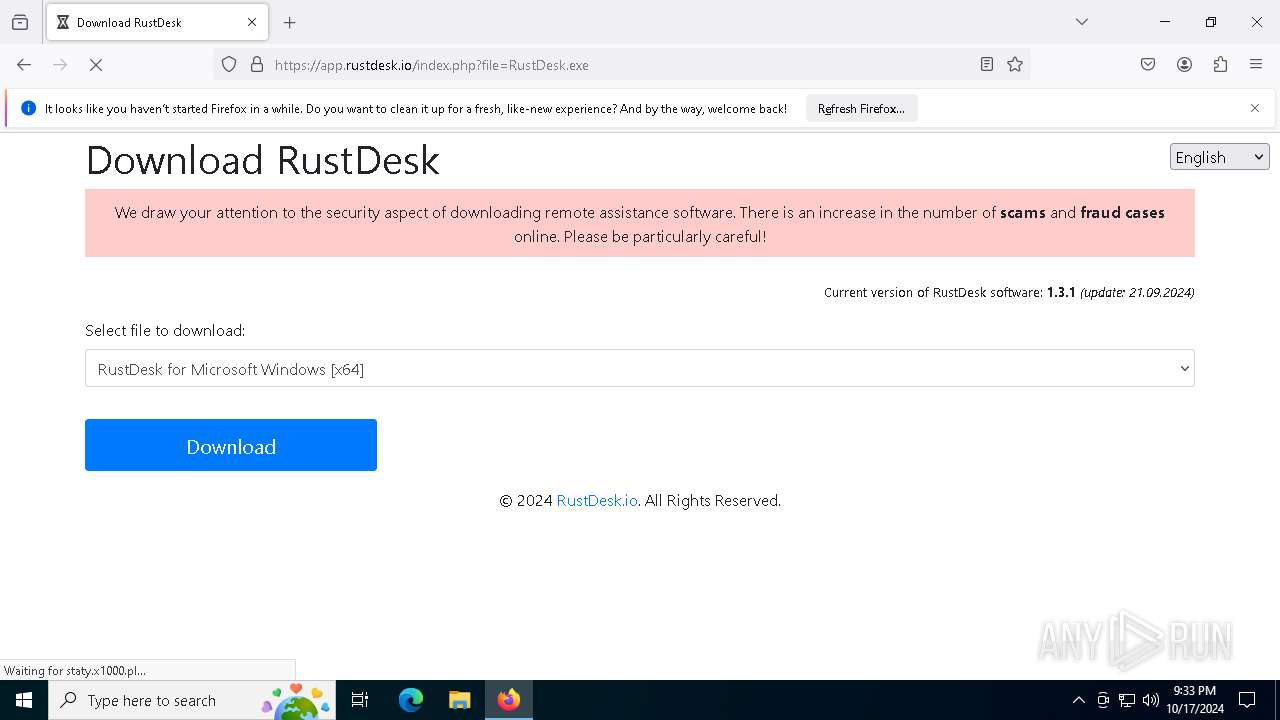
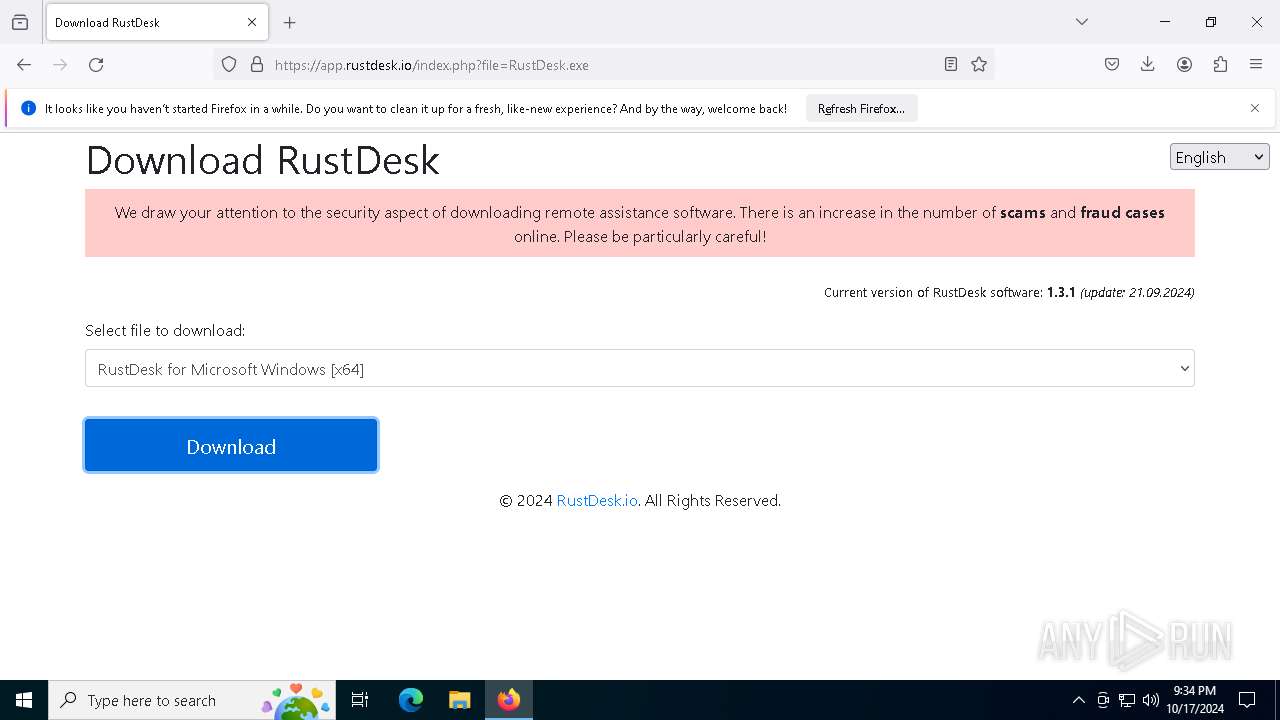
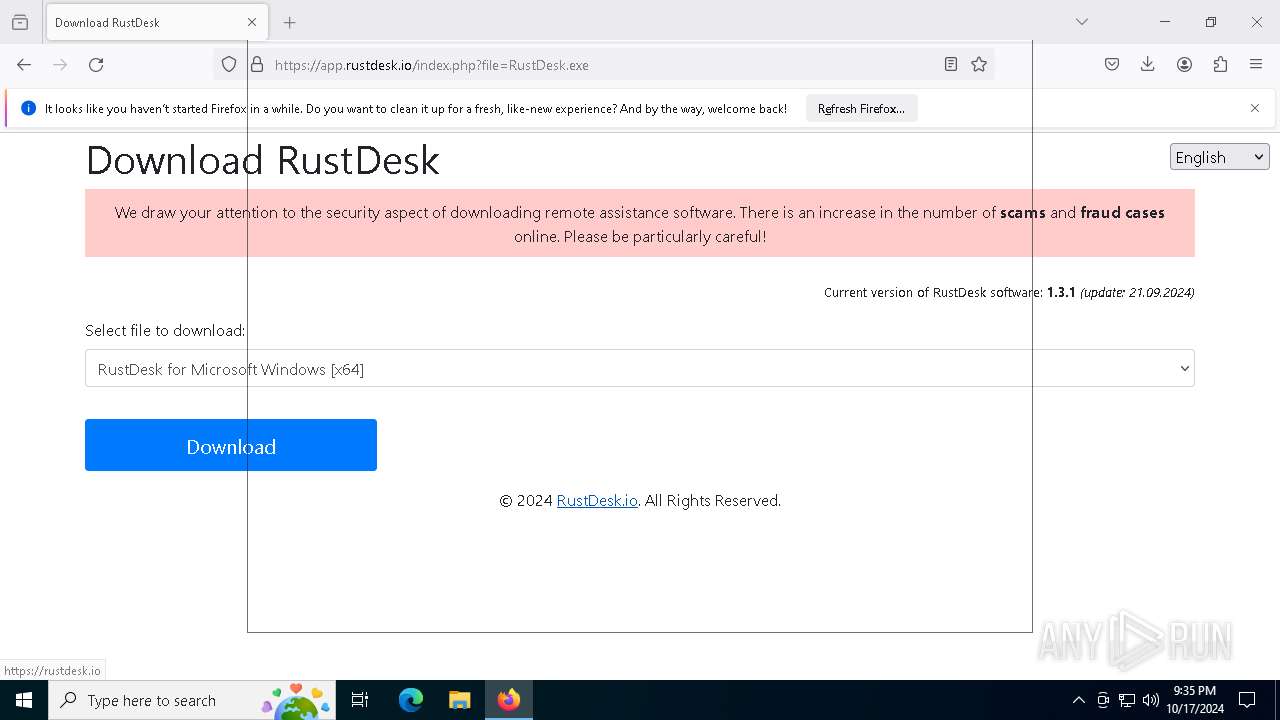
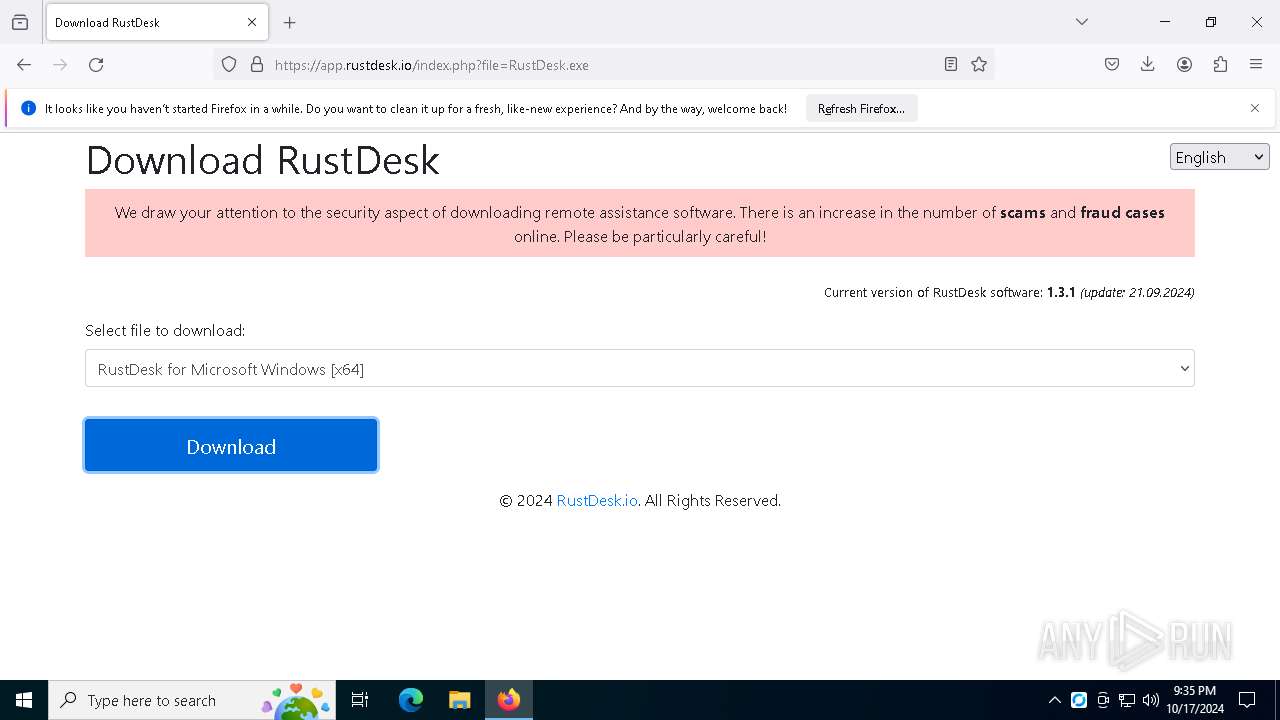
| URL: | https://rustdesk.io/ |
| Full analysis: | https://app.any.run/tasks/c3b9a1a4-1461-4fe0-b2e4-7f7d1468c7a2 |
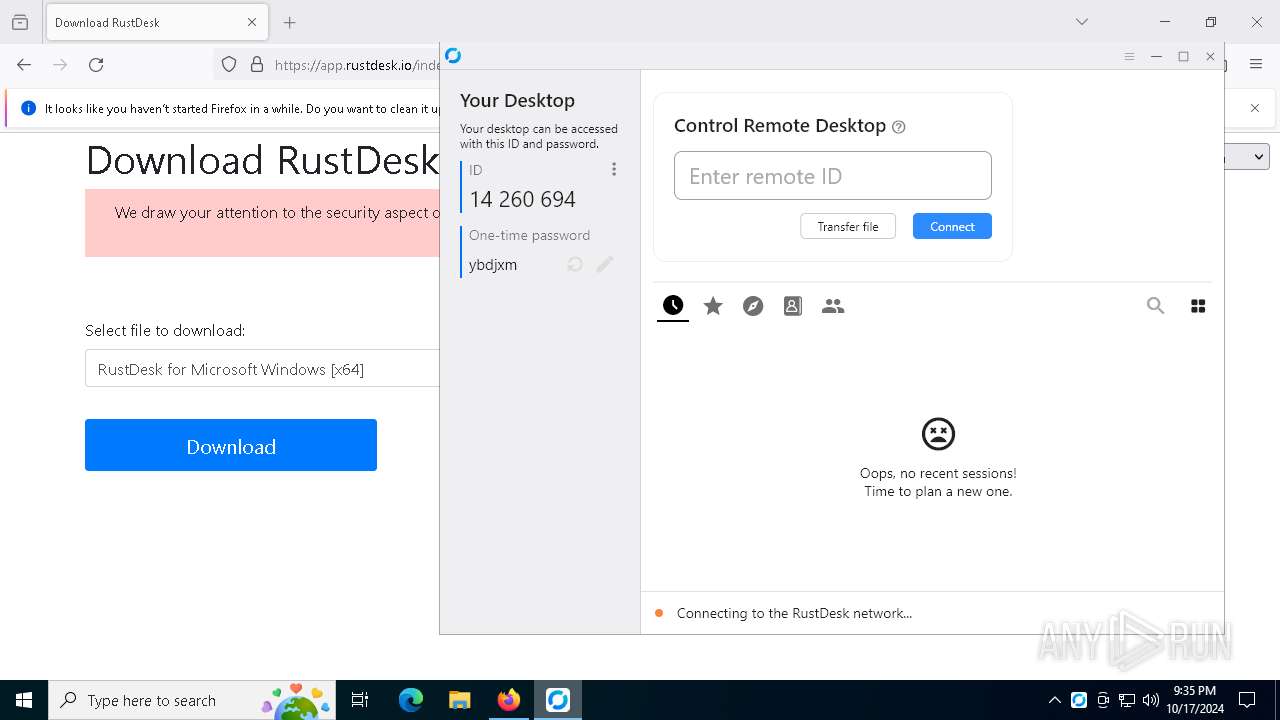
| Verdict: | Malicious activity |
| Analysis date: | October 17, 2024, 21:33:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1B5E30EFDF020BF009F0A985AABFEF84 |
| SHA1: | C60A132DEA802BF97CF082421CEAAF4F4114D5F7 |
| SHA256: | 0B143D6AD708926089166B5F42E5ED04230A9D966798DE1E6AA08519C0851521 |
| SSDEEP: | 3:N85r:2N |
MALICIOUS
No malicious indicators.SUSPICIOUS
Potential Corporate Privacy Violation
- svchost.exe (PID: 2172)
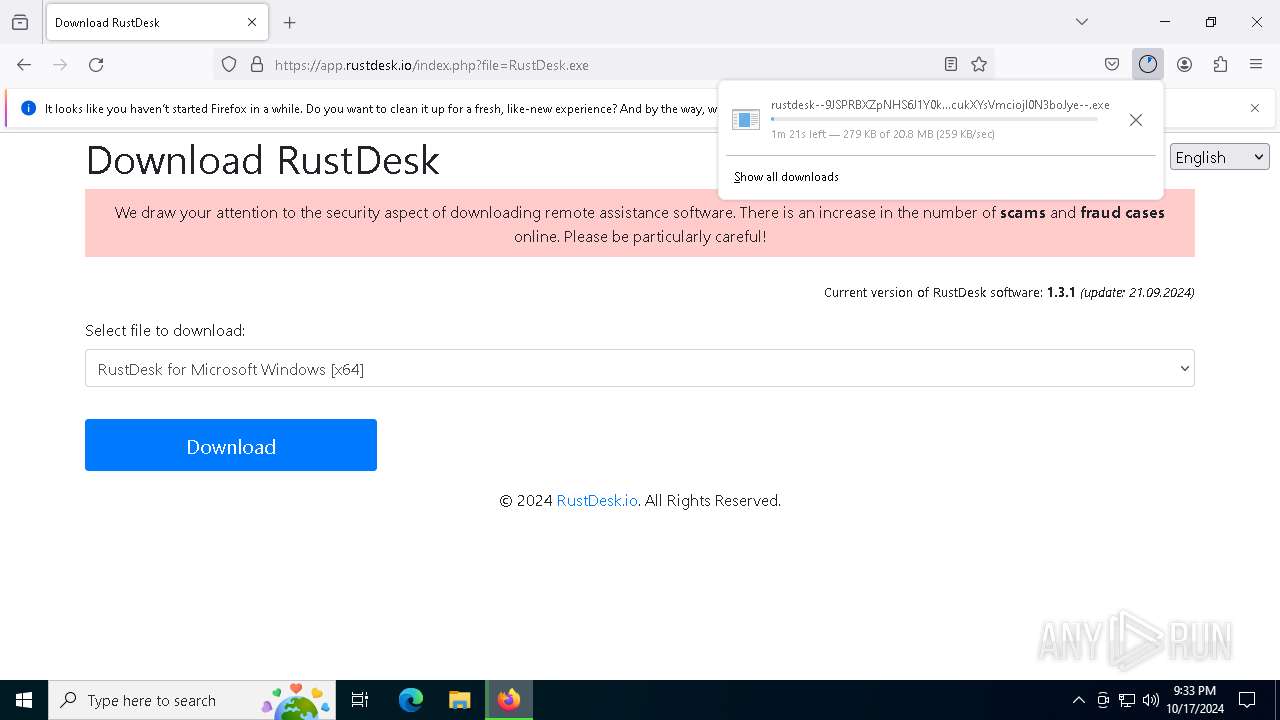
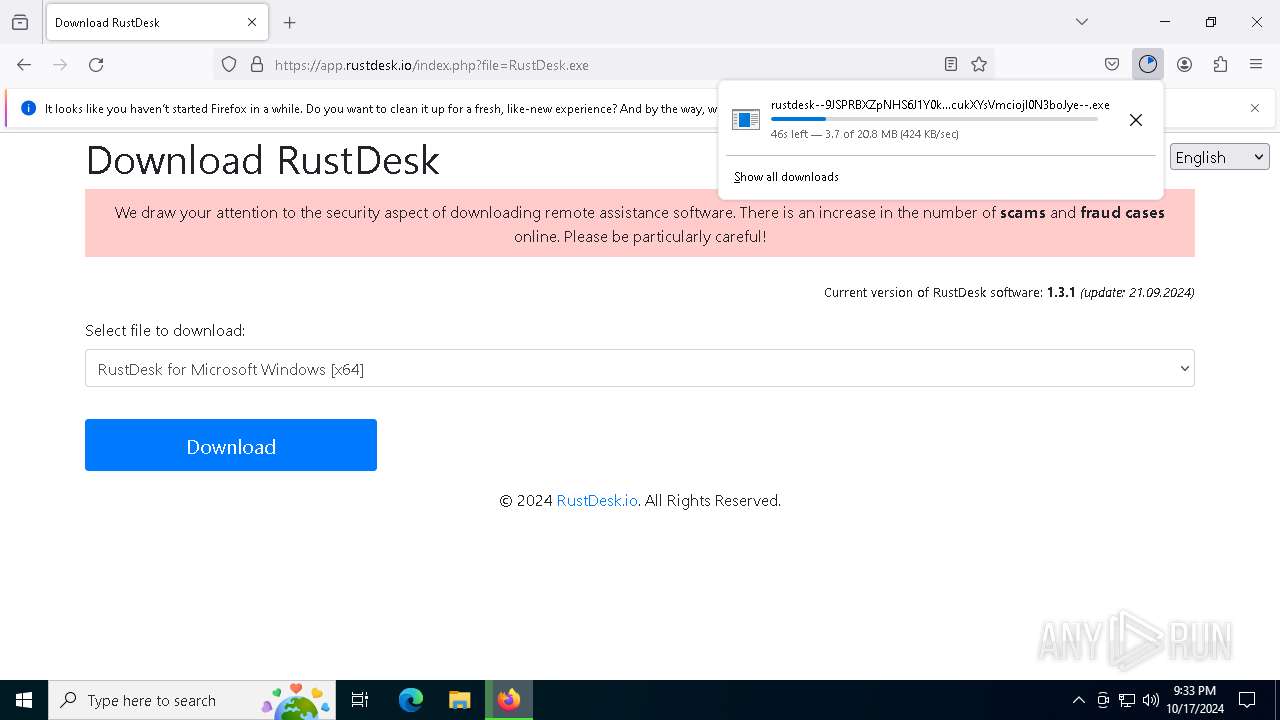
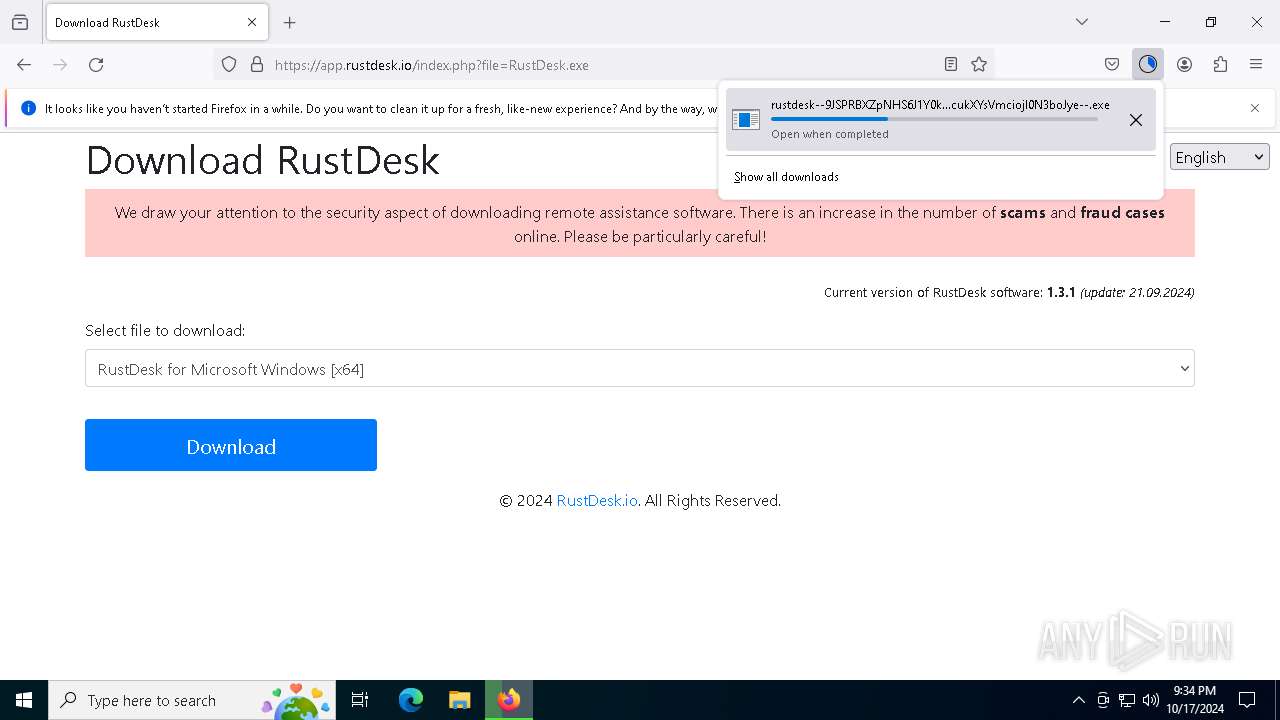
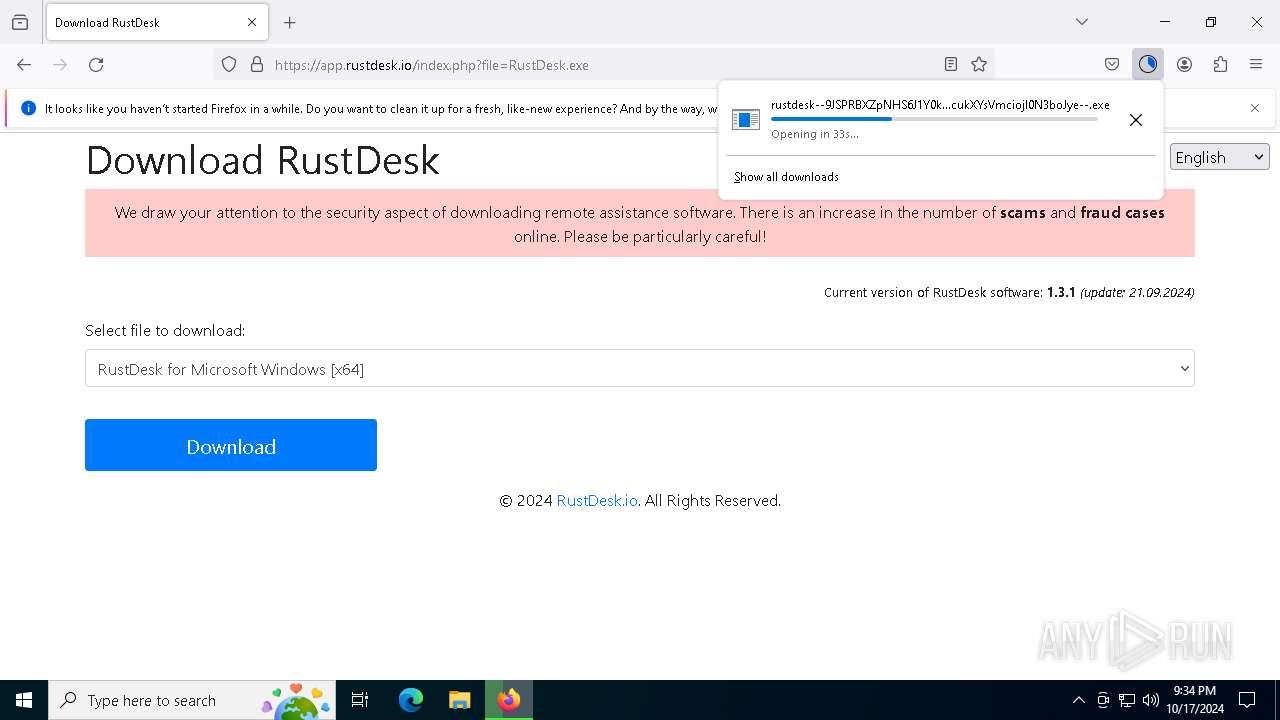
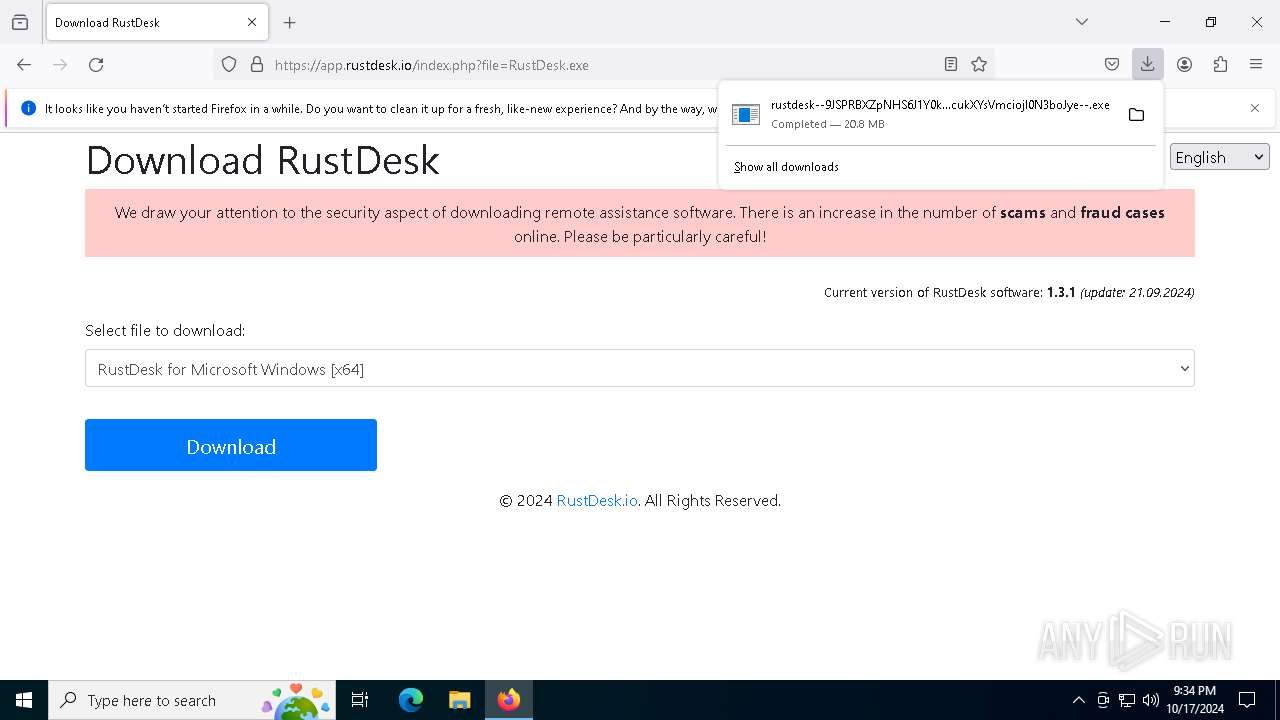
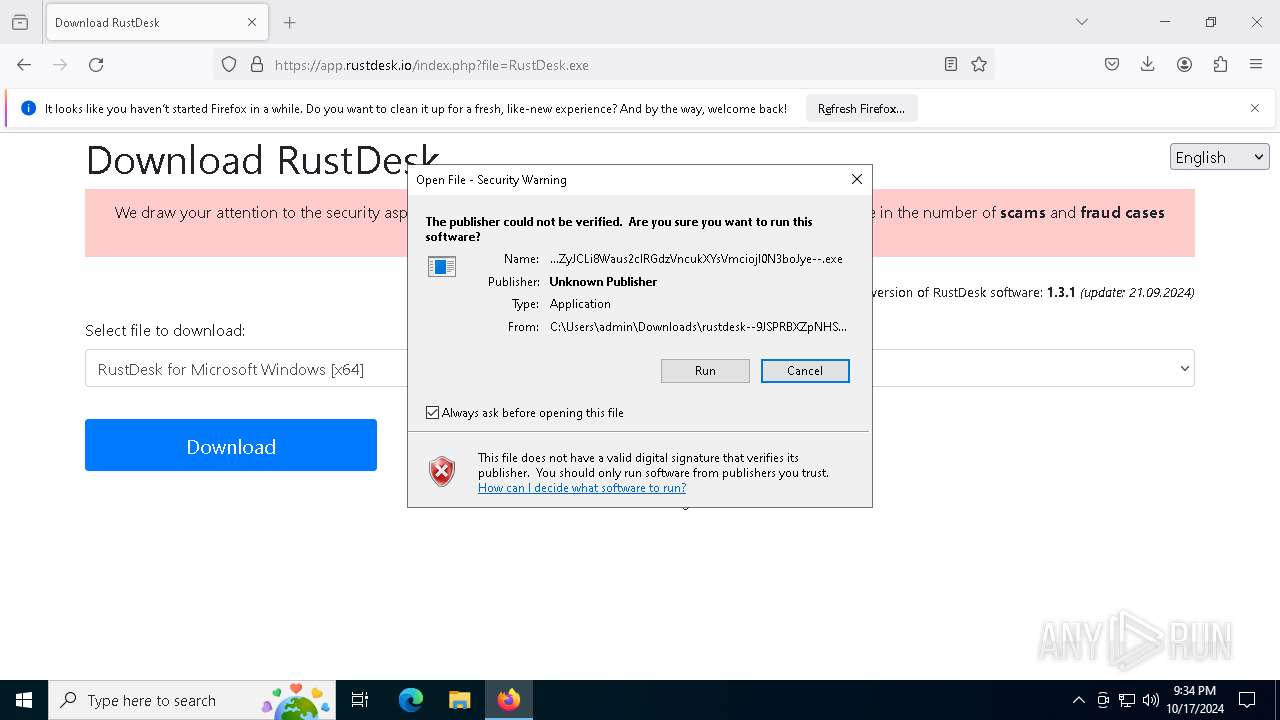
Executable content was dropped or overwritten
- rustdesk--9JSPRBXZpNHS6J1Y0kzbBplb0BjQ1cGRsN0TjlDcxEnS5EnRXNWd0djSvBDaIJiOikXZrJCLi8Waus2clRGdzVncukGch9yL6MHc0RHaiojIpBXYiwiIvlmLrNXZkR3c1JnL5FGblJnI6ISehxWZyJCLi8Waus2clRGdzVncukXYsVmciojI0N3boJye--.exe (PID: 8184)
- xcopy.exe (PID: 6980)
Starts CMD.EXE for commands execution
- rustdesk.exe (PID: 4584)
- rustdesk.exe (PID: 7240)
- rustdesk.exe (PID: 1764)
Process drops legitimate windows executable
- rustdesk--9JSPRBXZpNHS6J1Y0kzbBplb0BjQ1cGRsN0TjlDcxEnS5EnRXNWd0djSvBDaIJiOikXZrJCLi8Waus2clRGdzVncukGch9yL6MHc0RHaiojIpBXYiwiIvlmLrNXZkR3c1JnL5FGblJnI6ISehxWZyJCLi8Waus2clRGdzVncukXYsVmciojI0N3boJye--.exe (PID: 8184)
Uses TASKKILL.EXE to kill process
- rustdesk--9JSPRBXZpNHS6J1Y0kzbBplb0BjQ1cGRsN0TjlDcxEnS5EnRXNWd0djSvBDaIJiOikXZrJCLi8Waus2clRGdzVncukGch9yL6MHc0RHaiojIpBXYiwiIvlmLrNXZkR3c1JnL5FGblJnI6ISehxWZyJCLi8Waus2clRGdzVncukXYsVmciojI0N3boJye--.exe (PID: 8184)
- cmd.exe (PID: 5892)
- cmd.exe (PID: 7048)
- cmd.exe (PID: 6496)
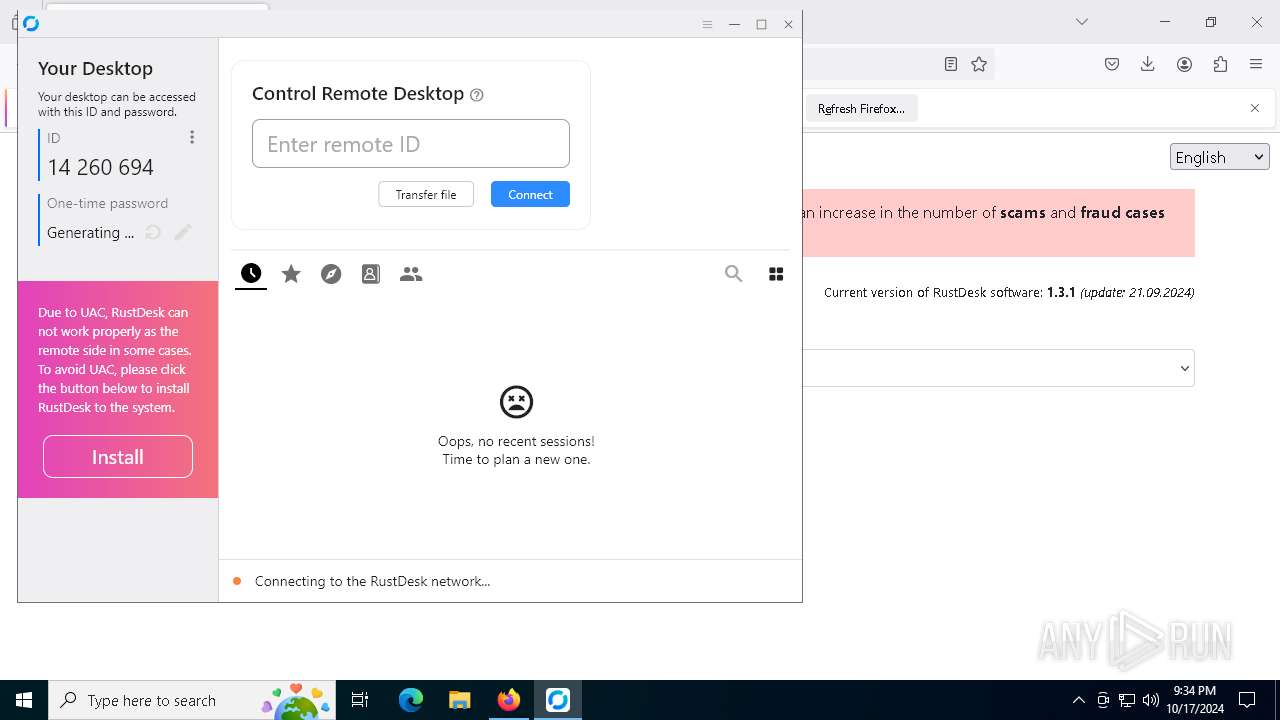
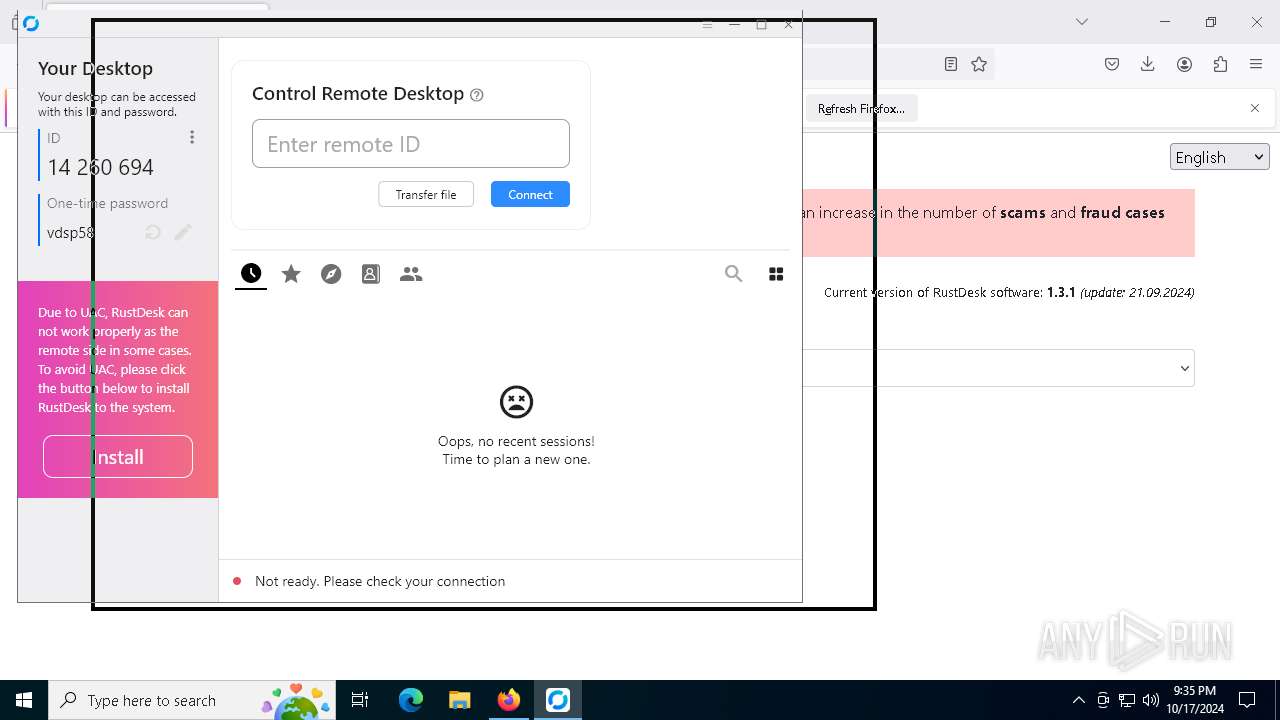
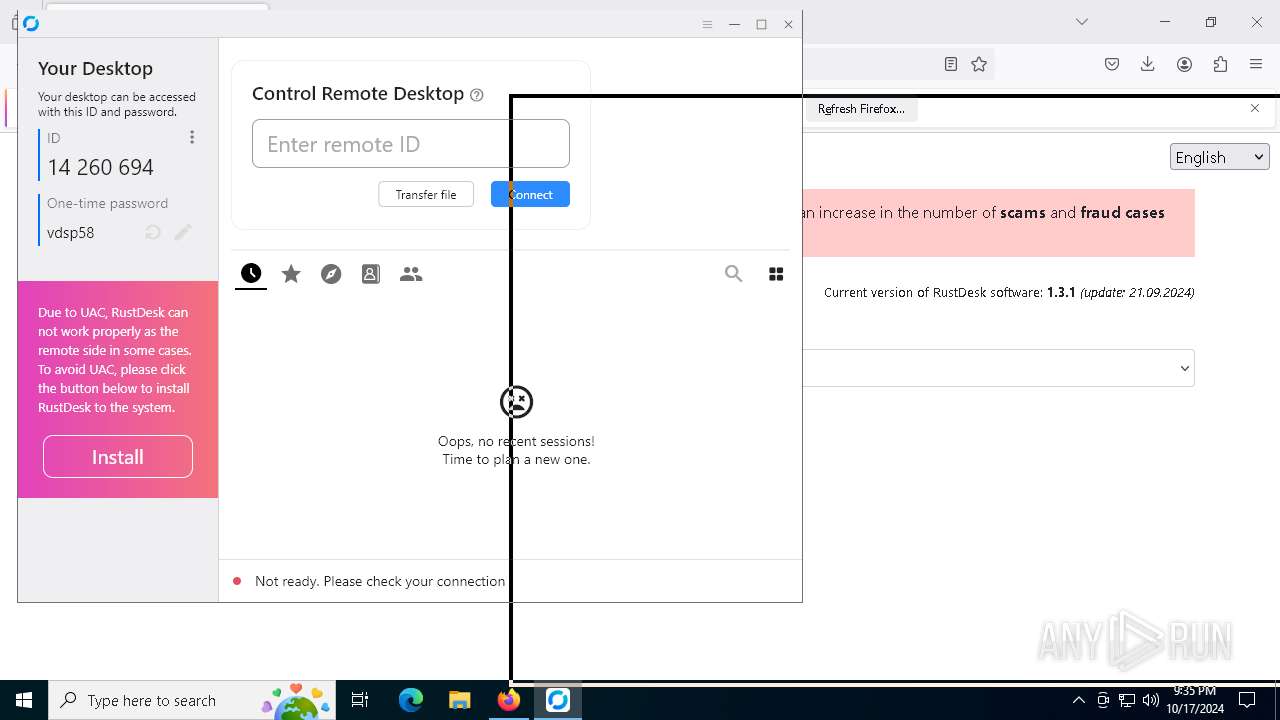
Connects to unusual port
- rustdesk.exe (PID: 4584)
- rustdesk.exe (PID: 1764)
Application launched itself
- rustdesk.exe (PID: 4584)
- rustdesk.exe (PID: 7960)
- rustdesk.exe (PID: 1764)
There is functionality for taking screenshot (YARA)
- rustdesk.exe (PID: 4584)
- rustdesk.exe (PID: 7960)
- rustdesk.exe (PID: 6912)
Executing commands from a ".bat" file
- rustdesk.exe (PID: 7240)
Starts application with an unusual extension
- cmd.exe (PID: 7048)
Starts SC.EXE for service management
- cmd.exe (PID: 7048)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 7048)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7048)
The executable file from the user directory is run by the CMD process
- rustdesk.exe (PID: 7936)
- rustdesk.exe (PID: 5792)
The process executes VB scripts
- cmd.exe (PID: 7048)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 7048)
Executes as Windows Service
- rustdesk.exe (PID: 7960)
- rustdesk.exe (PID: 5952)
Starts itself from another location
- rustdesk.exe (PID: 7240)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6552)
INFO
Application launched itself
- firefox.exe (PID: 6736)
- firefox.exe (PID: 4072)
Executable content was dropped or overwritten
- firefox.exe (PID: 4072)
Changes the display of characters in the console
- cmd.exe (PID: 7048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
220
Monitored processes
92
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | reg add HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Uninstall\RustDesk /f /v DisplayIcon /t REG_SZ /d "C:\Program Files\RustDesk\RustDesk.exe" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1248 | reg add HKEY_CLASSES_ROOT\rustdesk\shell\open\command /f /ve /t REG_SZ /d "\"C:\Program Files\RustDesk\RustDesk.exe\" \"%1\"" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | reg add HKEY_CLASSES_ROOT\.rustdesk\DefaultIcon /f /ve /t REG_SZ /d "\"C:\Program Files\RustDesk\RustDesk.exe\",0" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1376 | cscript "C:\Users\admin\AppData\Local\Temp\RustDesk_tray_shortcut.vbs" | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1432 | netsh advfirewall firewall delete rule name="RustDesk Service" | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1588 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5884 -childID 5 -isForBrowser -prefsHandle 5716 -prefMapHandle 5712 -prefsLen 31108 -prefMapSize 244343 -jsInitHandle 1312 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {dcb1c7ad-76d4-49bd-9c32-aa670f4f0461} 4072 "\\.\pipe\gecko-crash-server-pipe.4072" 2811cc4cf50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\RustDesk\RustDesk.exe" --server | C:\Program Files\RustDesk\rustdesk.exe | rustdesk.exe | ||||||||||||
User: SYSTEM Company: Purslane Ltd Integrity Level: SYSTEM Description: RustDesk Remote Desktop Version: 1.3.1+47 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 832
Read events
25 814
Write events
18
Delete events
0
Modification events
| (PID) Process: | (4072) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (848) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RustDesk |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\RustDesk\RustDesk.exe | |||
| (PID) Process: | (3936) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RustDesk |
| Operation: | write | Name: | DisplayName |
Value: RustDesk | |||
| (PID) Process: | (6796) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RustDesk |
| Operation: | write | Name: | DisplayVersion |
Value: 1.3.1 | |||
| (PID) Process: | (6984) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RustDesk |
| Operation: | write | Name: | Version |
Value: 1.3.1 | |||
| (PID) Process: | (6828) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RustDesk |
| Operation: | write | Name: | BuildDate |
Value: 2024-09-20 14:16 | |||
| (PID) Process: | (6928) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RustDesk |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\RustDesk | |||
| (PID) Process: | (7948) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RustDesk |
| Operation: | write | Name: | Publisher |
Value: RustDesk | |||
| (PID) Process: | (6424) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RustDesk |
| Operation: | write | Name: | VersionMajor |
Value: 1 | |||
| (PID) Process: | (6132) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RustDesk |
| Operation: | write | Name: | VersionMinor |
Value: 3 | |||
Executable files
42
Suspicious files
218
Text files
234
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4072 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 4072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 4072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:8BD997F90ECBED0083C0F3B144B2F721 | SHA256:25EC68792A8D0944AEC3A5C97A589369B3CEF2F6F5F2721E09A1570C270E8255 | |||
| 4072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4072 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:8BD997F90ECBED0083C0F3B144B2F721 | SHA256:25EC68792A8D0944AEC3A5C97A589369B3CEF2F6F5F2721E09A1570C270E8255 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
131
DNS requests
166
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.18.244.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.18.244.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 173.223.117.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4072 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
4072 | firefox.exe | POST | 200 | 95.101.74.224:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
4072 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
4072 | firefox.exe | POST | 200 | 142.251.36.3:80 | http://o.pki.goog/s/wr3/XjA | unknown | — | — | whitelisted |
4072 | firefox.exe | POST | 200 | 95.101.74.224:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
4072 | firefox.exe | POST | 200 | 95.101.74.224:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.18.244.211:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
— | — | 2.18.244.211:80 | crl.microsoft.com | Akamai International B.V. | FR | whitelisted |
— | — | 173.223.117.131:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5488 | MoUsoCoreWorker.exe | 173.223.117.131:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4072 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
rustdesk.io |
| unknown |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
example.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
2172 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query for TOR Hidden Domain .onion Accessible Via TOR |