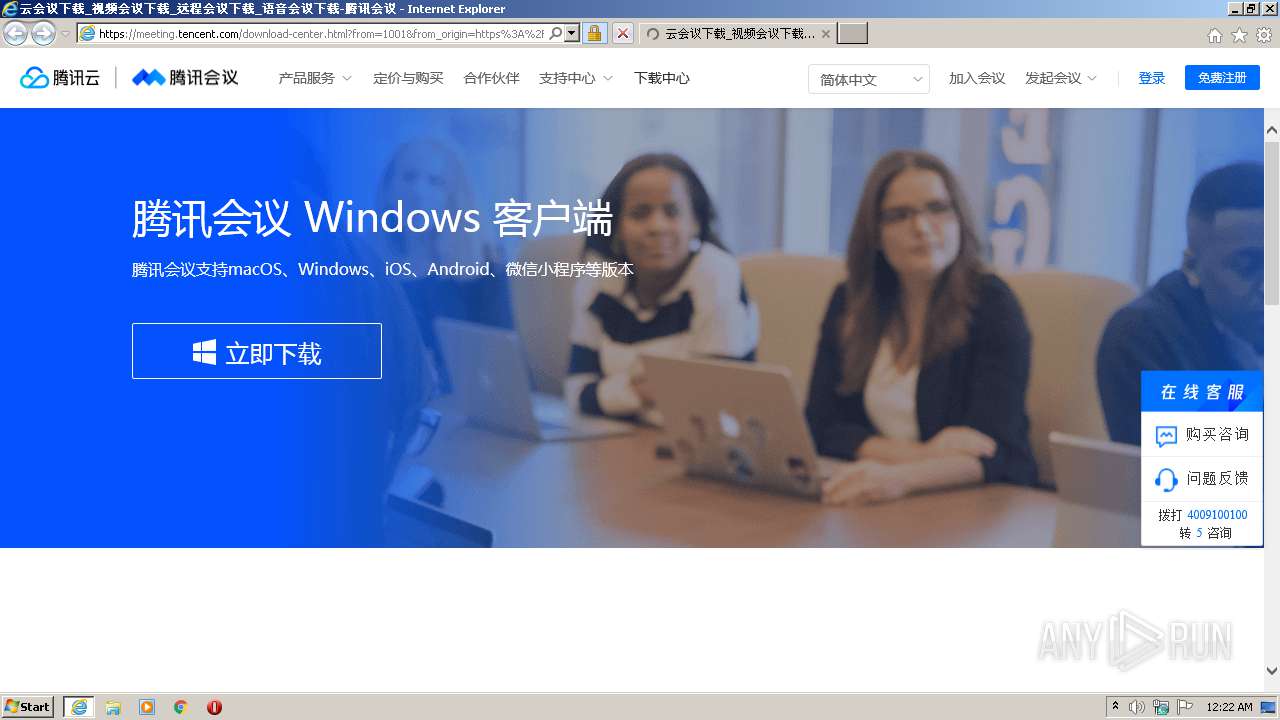
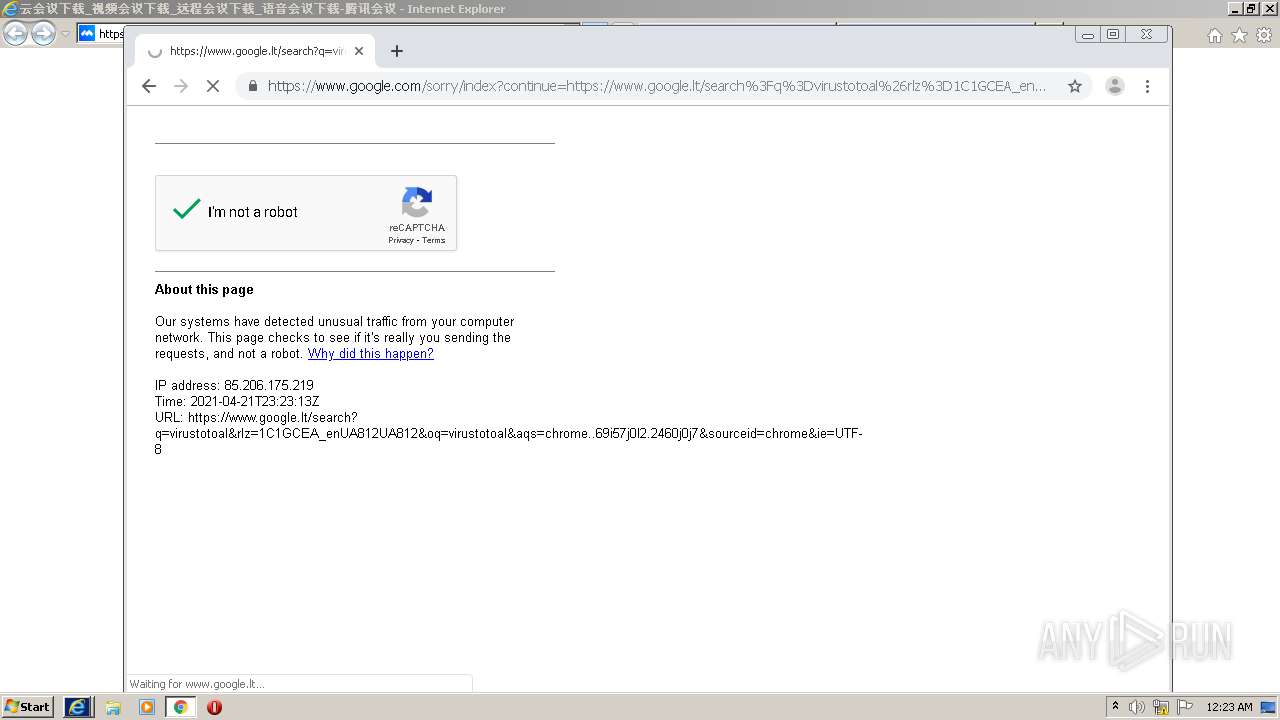
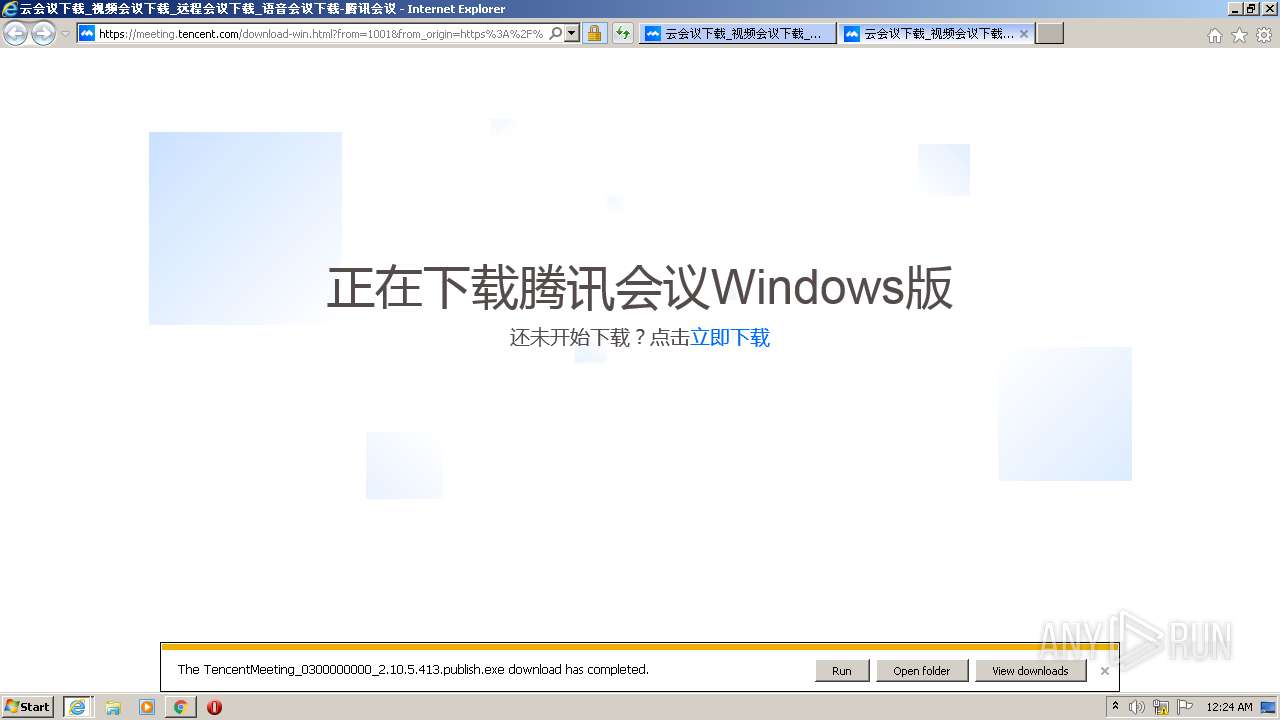
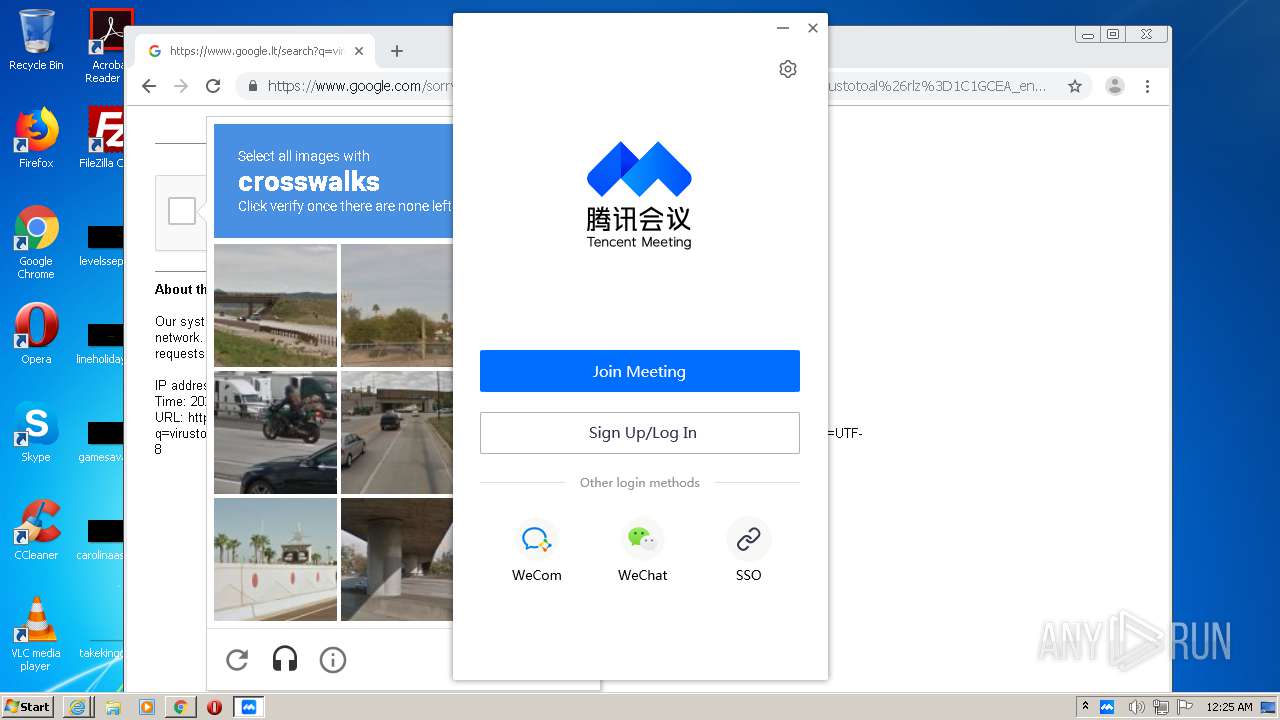
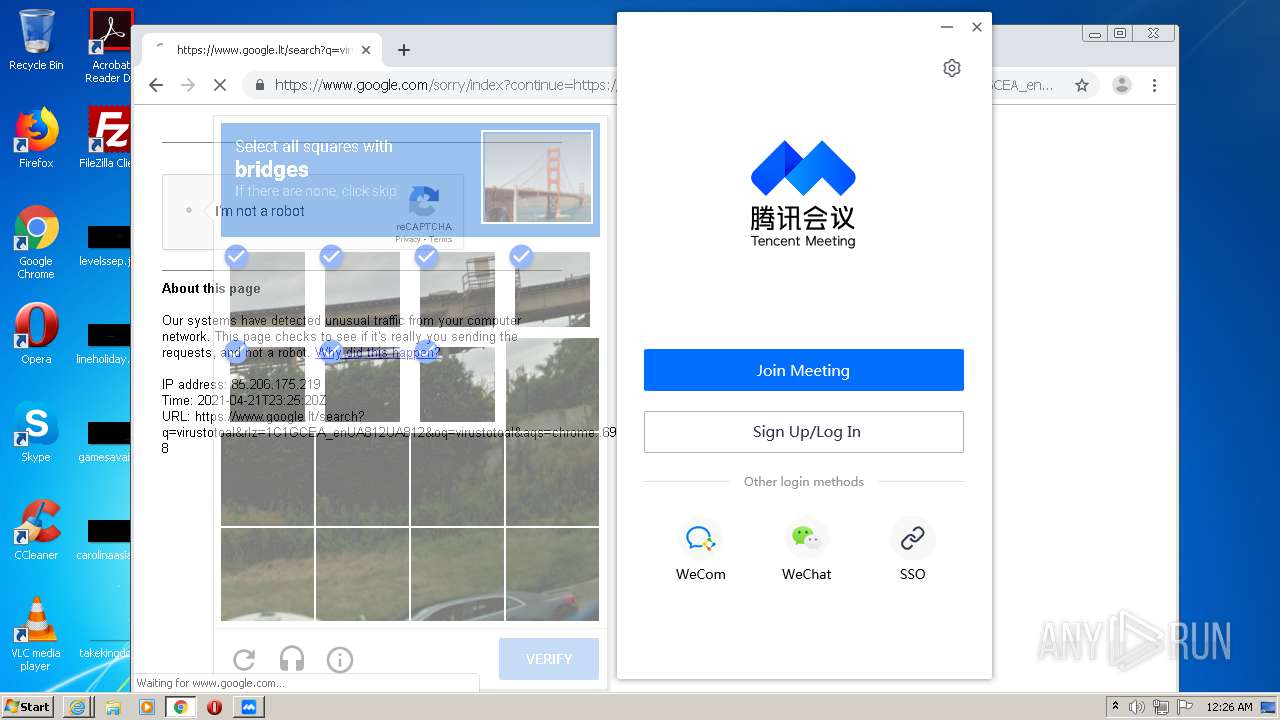
| URL: | https://meeting.tencent.com/download-center.html?from=1001&from_origin=https%3A%2F%2Fmeeting.tencent.com&from_pathname=%2F |
| Full analysis: | https://app.any.run/tasks/e89c7931-98b7-4eae-8906-c8276d642ce8 |
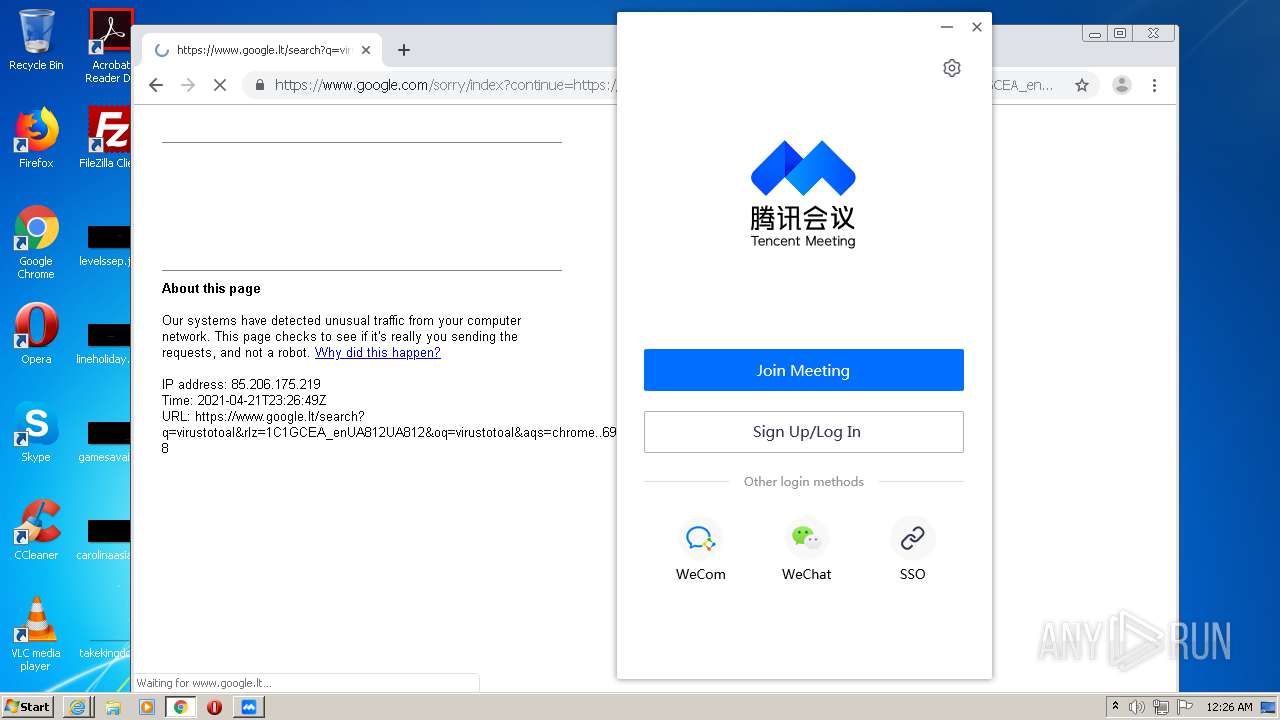
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2021, 23:21:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6DEE37433F76CCA80C99D1312341BC87 |
| SHA1: | 3E0B65647676D47E474A1420CA666E4745051519 |
| SHA256: | 0B0C9ABE50B3F93AA62ECDC483BB75A29D1E17FE37871AFF1536542D24935B96 |
| SSDEEP: | 3:N8ykRZIBJGAlyLNRIaall1egBWCXjiwskRZI/XRZErXj:27zMIAlYNMll8gnziwlz86rXj |
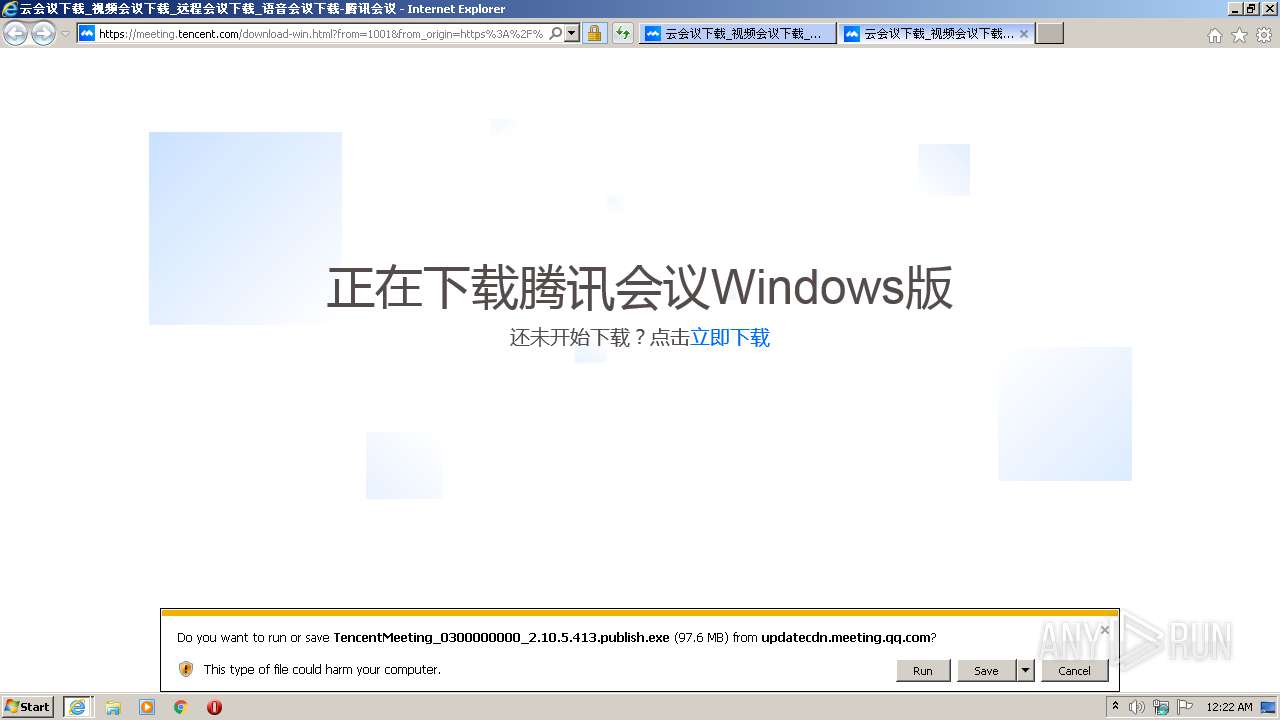
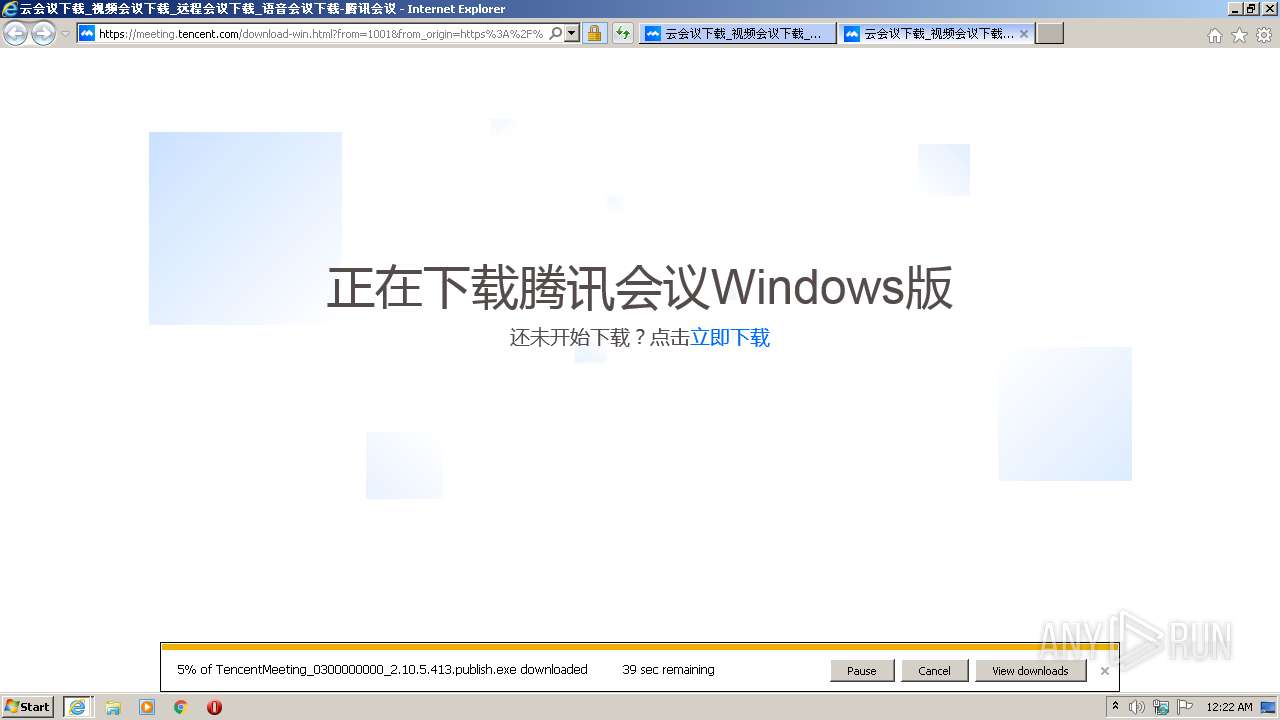
MALICIOUS
Loads dropped or rewritten executable
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 3636)
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
- wemeetapp.exe (PID: 2476)
- wemeetapp.exe (PID: 3600)
- wemeetapp.exe (PID: 3504)
- wemeetapp.exe (PID: 3124)
- hw_check.exe (PID: 1812)
- wemeetapp.exe (PID: 3756)
Application was dropped or rewritten from another process
- WemeetUpdateSvc.exe (PID: 3048)
- wemeetapp.exe (PID: 3756)
- wemeetapp.exe (PID: 2476)
- wemeetapp.exe (PID: 3600)
- wemeetapp.exe (PID: 3504)
- wemeetapp.exe (PID: 3124)
- hw_check.exe (PID: 1812)
Drops executable file immediately after starts
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Changes the autorun value in the registry
- ie4uinit.exe (PID: 2160)
Changes settings of System certificates
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2236)
Executable content was dropped or overwritten
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 3636)
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2804)
Application launched itself
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 3636)
- wemeetapp.exe (PID: 2476)
Changes default file association
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
- ie4uinit.exe (PID: 2160)
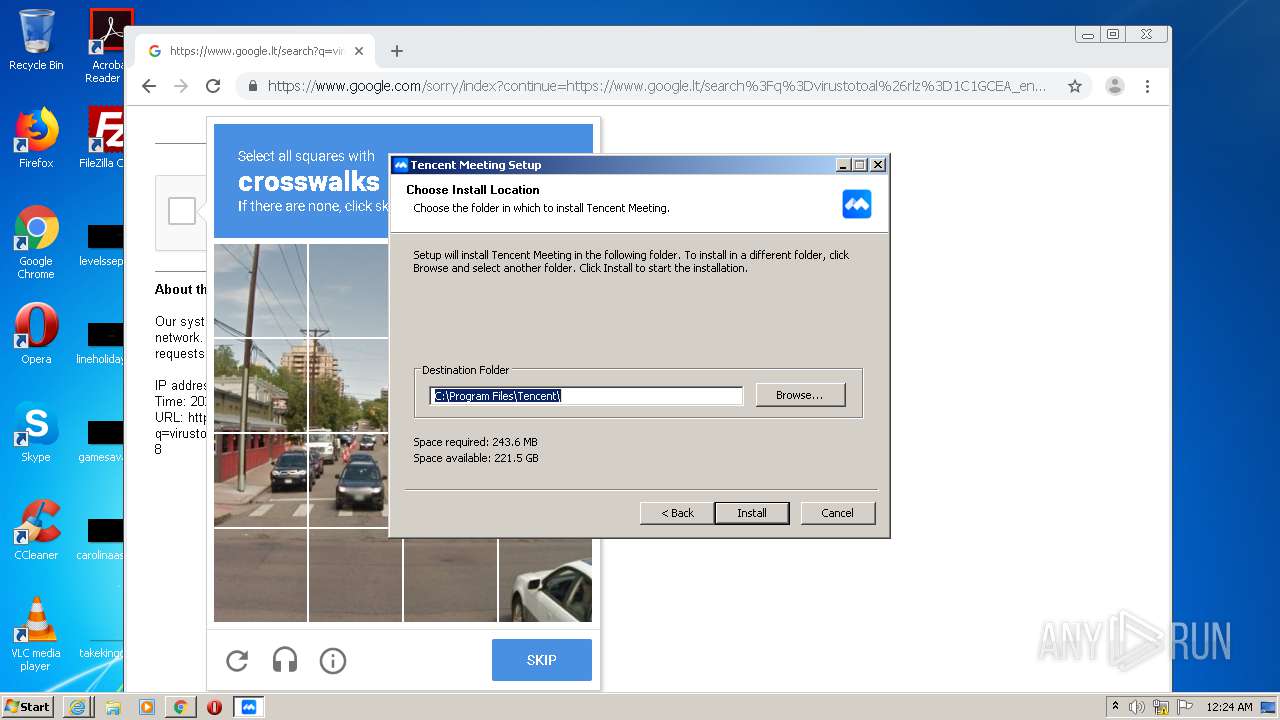
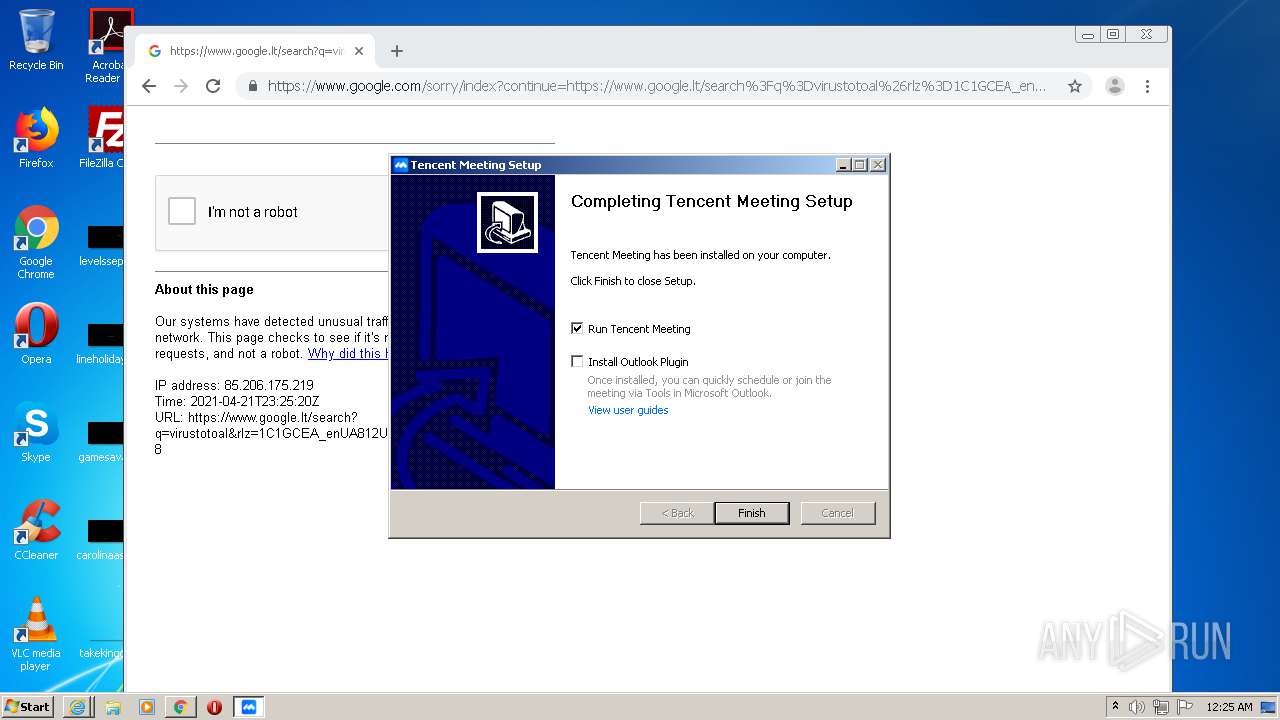
Creates a software uninstall entry
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Creates files in the Windows directory
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Creates files in the user directory
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
- wemeetapp.exe (PID: 2476)
- wemeetapp.exe (PID: 3124)
- wemeetapp.exe (PID: 3600)
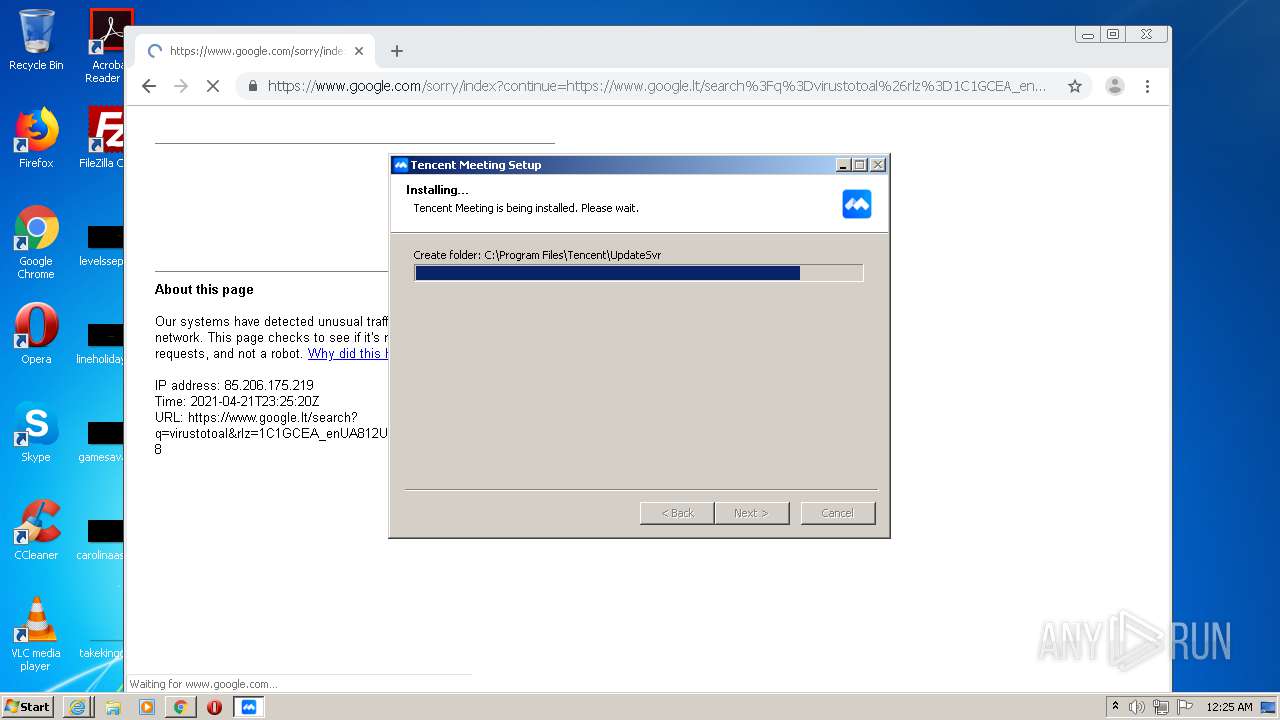
Creates a directory in Program Files
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Uses ICACLS.EXE to modify access control list
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Adds / modifies Windows certificates
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Low-level read access rights to disk partition
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Drops a file with a compile date too recent
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Drops a file with too old compile date
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Creates or modifies windows services
- WemeetUpdateSvc.exe (PID: 3048)
Reads CPU info
- wemeetapp.exe (PID: 3600)
- wemeetapp.exe (PID: 3124)
Drops a file that was compiled in debug mode
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Creates files in the program directory
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2880)
Reads internet explorer settings
- iexplore.exe (PID: 2856)
Creates files in the user directory
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2236)
- iexplore.exe (PID: 2880)
- iexplore.exe (PID: 2856)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2880)
Reads settings of System Certificates
- iexplore.exe (PID: 2880)
- iexplore.exe (PID: 2856)
Application launched itself
- iexplore.exe (PID: 2880)
- chrome.exe (PID: 2804)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2880)
Manual execution by user
- chrome.exe (PID: 2804)
- wemeetapp.exe (PID: 2476)
- wemeetapp.exe (PID: 3756)
- wemeetapp.exe (PID: 3504)
Changes settings of System certificates
- iexplore.exe (PID: 2880)
Reads the hosts file
- chrome.exe (PID: 2804)
- chrome.exe (PID: 2180)
Dropped object may contain Bitcoin addresses
- TencentMeeting_0300000000_2.10.5.413.publish.exe (PID: 564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
102
Monitored processes
52
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Users\admin\Downloads\TencentMeeting_0300000000_2.10.5.413.publish.exe" /UAC:50208 /NCRC | C:\Users\admin\Downloads\TencentMeeting_0300000000_2.10.5.413.publish.exe | TencentMeeting_0300000000_2.10.5.413.publish.exe | ||||||||||||
User: admin Company: Tencent Integrity Level: HIGH Description: 腾讯会议 Exit code: 0 Version: 2.10.5.413 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18072502549299362028,13358013296369994499,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12564413029633289557 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2460 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18072502549299362028,13358013296369994499,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14406881027507017479 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3988 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,18072502549299362028,13358013296369994499,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=254650366282865056 --mojo-platform-channel-handle=3664 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | hw_check.exe --check_hwdecode=1 --file_path="C:\Users\admin\AppData\Roaming\Tencent\WeMeet\Resource\519677942b9ffacaec4945360a15f8df\1617718924.jpg" | C:\Program Files\Tencent\WeMeet\2.10.5.413\hw_check.exe | — | wemeetapp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 腾讯会议 Exit code: 0 Version: 2.10.5.413 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,18072502549299362028,13358013296369994499,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=876564157960253035 --mojo-platform-channel-handle=3792 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18072502549299362028,13358013296369994499,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8562868765205894479 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,18072502549299362028,13358013296369994499,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14497587562061172246 --mojo-platform-channel-handle=3792 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | "ie4uinit.exe" -show | C:\Windows\system32\ie4uinit.exe | TencentMeeting_0300000000_2.10.5.413.publish.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2352 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 412
Read events
2 628
Write events
715
Delete events
69
Modification events
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 811470614 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30881541 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A6000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2880) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
166
Suspicious files
468
Text files
977
Unknown types
73
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF461.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF462.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3FE2BD01AB6BC312BF0DADE7F797388F_896832C6BC857CFAEA9E59E166B13E2C | binary | |
MD5:C639D823F76F9F67138773E7D6F80DE9 | SHA256:6C45C55AF0DAA412EEF5CEBBC5017CA38D9C853167C1B350A6CB065A0E2B291A | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\download-center-2a1f604f47[1].css | text | |
MD5:0764A29E9BB4A5C48D254A39F63BD906 | SHA256:D41512018E0A9519CBFB593AD65E7D494415BF0A40D1E45F903650207B183EA0 | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download-center[1].htm | html | |
MD5:92B166F53D6256E6ADB96FBF27A38BBD | SHA256:37906F68BFCFFD7600ED46391C84000146D76537B02FF657A38F979A05A94A4E | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\AD5F118F7897046E8CA970AE6A6AB70B_149BD358EB1B98A28F5D8A8DB19271CA | binary | |
MD5:38383DBD0A9A492A779DE090EACB254F | SHA256:5CA3C0C64BC84D220FDEC49AD7CB0FB3CD9C25D250D9DE478220F66052192F2D | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\up_arrow_1x[1].png | image | |
MD5:BEBB7DE0E601EA2C7C0F1411FB103C83 | SHA256:946B2726AC014D3DB90D1054C91BF20A0D4A493231F38FE0037348CC48C08CFA | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\code-miniapp-9949b26cea[1].png | image | |
MD5:AA021F6AAA1FE78DB93322B1BED4C4BA | SHA256:A35628CE0C373161DEB5CB662A6658A64D4B8331B1F9E929729CF8A618A87265 | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\qr_code_bilibili_1x-e2ef97554a[1].png | image | |
MD5:6989BB505C8111830469DF4D6DA69DB8 | SHA256:994914884C256CFC0B324821966BB530A8EB8B334066D16CB7847C3476827A47 | |||
| 2856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\download-center-709390e048[1].js | text | |
MD5:709390E048E6346A2D6B75A2ED0EF61F | SHA256:DED536CB3DE72BF24C2FBC1FD81D87FAF8444B27D9EDC97D0651E253C47A1BB6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
210
DNS requests
57
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2856 | iexplore.exe | GET | 200 | 163.181.56.211:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbJNRrm8KxusAb7DCqnMkE%3D | US | der | 471 b | whitelisted |
2856 | iexplore.exe | GET | 200 | 163.181.56.211:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQhnxEBNL9LgIhfSsTcHsrTt204QgQURNnISjOO01KNp5KUYR%2BayKW37MsCEA8ejJ%2FixbNvve0Nnd99kaQ%3D | US | der | 471 b | whitelisted |
2856 | iexplore.exe | GET | 200 | 163.181.56.211:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQhnxEBNL9LgIhfSsTcHsrTt204QgQURNnISjOO01KNp5KUYR%2BayKW37MsCEAL3xGKWy9ht5pq%2Bh81pQXQ%3D | US | der | 471 b | whitelisted |
2856 | iexplore.exe | GET | 200 | 163.181.56.211:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbJNRrm8KxusAb7DCqnMkE%3D | US | der | 471 b | whitelisted |
2856 | iexplore.exe | GET | 200 | 47.246.43.225:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAh%2BGPuPqpJ%2B6HYKDYmC9RI%3D | US | der | 471 b | whitelisted |
2856 | iexplore.exe | GET | 200 | 163.181.56.211:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQhnxEBNL9LgIhfSsTcHsrTt204QgQURNnISjOO01KNp5KUYR%2BayKW37MsCEAL3xGKWy9ht5pq%2Bh81pQXQ%3D | US | der | 471 b | whitelisted |
2856 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAZ6f01ckvOZts%2BrkejawoA%3D | US | der | 471 b | whitelisted |
2856 | iexplore.exe | GET | 200 | 47.246.43.226:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAh%2BGPuPqpJ%2B6HYKDYmC9RI%3D | US | der | 471 b | whitelisted |
2856 | iexplore.exe | GET | 200 | 163.181.56.211:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQhnxEBNL9LgIhfSsTcHsrTt204QgQURNnISjOO01KNp5KUYR%2BayKW37MsCEA8ejJ%2FixbNvve0Nnd99kaQ%3D | US | der | 471 b | whitelisted |
2856 | iexplore.exe | GET | 200 | 47.246.43.226:80 | http://ocsp.dcocsp.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHv1Dj%2BciPJEWH5JNtwL5Y07mRqwQUxBF%2BiECGwkG%2FZfMa4bRTQKOr7H0CEAjJ8oSDRM6qdktKEgBc%2Bro%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2856 | iexplore.exe | 150.109.206.154:443 | meeting.tencent.com | — | US | suspicious |
2856 | iexplore.exe | 163.181.56.211:80 | ocsp.digicert.cn | — | US | suspicious |
2856 | iexplore.exe | 203.205.219.90:443 | open.work.weixin.qq.com | — | CN | unknown |
2856 | iexplore.exe | 101.33.10.108:443 | mat1.gtimg.com | — | CN | unknown |
2856 | iexplore.exe | 150.109.206.166:443 | meeting.tencent.com | — | US | suspicious |
2880 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2856 | iexplore.exe | 47.246.43.225:80 | ocsp.dcocsp.cn | — | US | malicious |
2856 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2856 | iexplore.exe | 47.246.43.226:80 | ocsp.dcocsp.cn | — | US | malicious |
2856 | iexplore.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
meeting.tencent.com |
| suspicious |
ocsp.digicert.cn |
| whitelisted |
mat1.gtimg.com |
| whitelisted |
res.wx.qq.com |
| whitelisted |
open.work.weixin.qq.com |
| unknown |
pingjs.qq.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.dcocsp.cn |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
TencentMeeting_0300000000_2.10.5.413.publish.exe | ExecShellAsUser: got desktop |
TencentMeeting_0300000000_2.10.5.413.publish.exe | ExecShellAsUser: elevated process detected |
TencentMeeting_0300000000_2.10.5.413.publish.exe | ExecShellAsUser: thread finished |
TencentMeeting_0300000000_2.10.5.413.publish.exe | ExecShellAsUser: DLL_PROCESS_DETACH |
wemeetapp.exe | reg path:C:\Program Files\Tencent\WeMeet\2.10.5.413 |
wemeetapp.exe | check certificate:C:\Program Files\Tencent\WeMeet\wemeetapp.exe |
wemeetapp.exe |
=========== mem dump after here is valid ========
|
wemeetapp.exe | reg path:C:\Program Files\Tencent\WeMeet\2.10.5.413 |
wemeetapp.exe | d:\qci_workspace\root-workspaces\__qci-pipeline-166541-1\sdk\base\common\mmap\win\../memory_mapping_impl.h(97): 2021/04/22 07:25:33.736|info |2476 |784 |memory_mapping_impl.h:97 |base::mmap_file::MemoryMappingImpl::IncreaseFileIfNeeded|increase file from 0 to 153600
|
wemeetapp.exe | D:\qci_workspace\root-workspaces\__qci-pipeline-166541-1\sdk\base\common\mmap\win\memory_mapping_impl.cc(85): 2021/04/22 07:25:33.736|info |2476 |784 |memory_mapping_impl.cc:85 |base::mmap_file::MemoryMappingImpl::Map|mmap: fd = 00000354, size = 153600, data = 26083328
|