| URL: | https://go.microsoft.com/fwlink/?linkid=2126594&pc=w045&icid=mscom_marcom_dlc |
| Full analysis: | https://app.any.run/tasks/a5944016-d699-4d4b-9a5e-d499107df0e3 |
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2021, 16:38:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 818E52DD4BBF7241A448C43A95AC9D96 |
| SHA1: | C75C854136D23AF97803B28FB211925C29B8E581 |
| SHA256: | 0B0A3ED21566C7962A572A3705FD45967A943287AFBAD036F6CCB1712BEA7A20 |
| SSDEEP: | 3:N8r8etR7LO+BYsw/7QTM2dp4n:2geDPO+YfQTtdp4n |
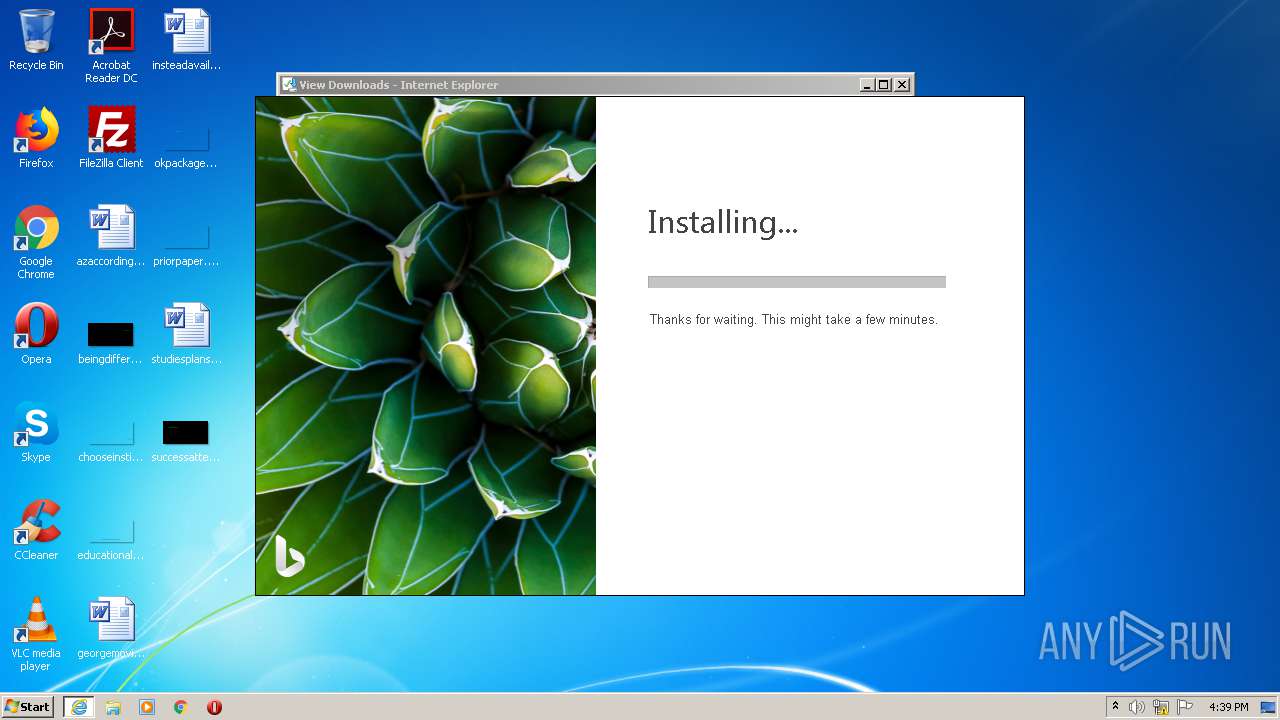
MALICIOUS
Application was dropped or rewritten from another process
- BingWallpaper.exe (PID: 2012)
- BWInstaller.exe (PID: 2396)
- StartupInstaller.exe (PID: 4000)
- BingWallpaperApp.exe (PID: 3136)
Drops executable file immediately after starts
- BingWallpaper.exe (PID: 2012)
- rundll32.exe (PID: 3504)
- rundll32.exe (PID: 2212)
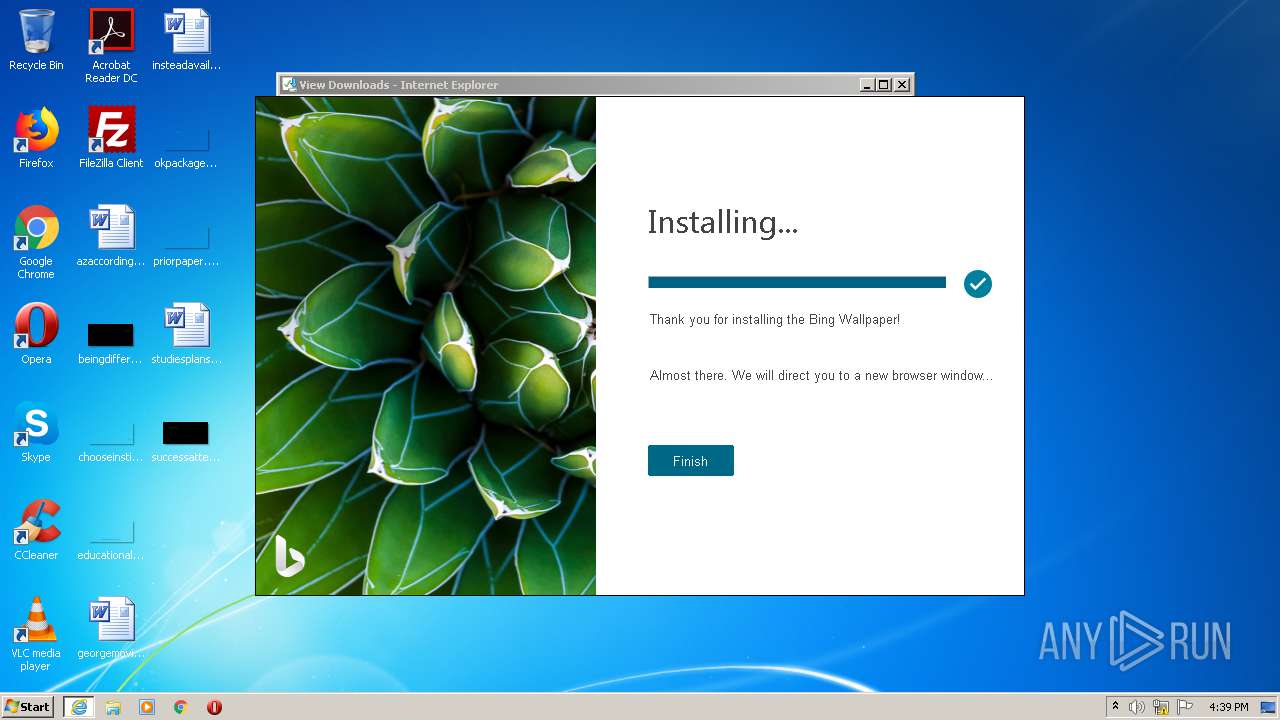
Steals credentials from Web Browsers
- BWInstaller.exe (PID: 2396)
- DefaultSetup.exe (PID: 3240)
Loads dropped or rewritten executable
- BWInstaller.exe (PID: 2396)
- rundll32.exe (PID: 3504)
- rundll32.exe (PID: 2384)
- rundll32.exe (PID: 2212)
- BingWallpaperApp.exe (PID: 3136)
Actions looks like stealing of personal data
- BWInstaller.exe (PID: 2396)
- DefaultSetup.exe (PID: 3240)
Changes the autorun value in the registry
- BWInstaller.exe (PID: 2396)
SUSPICIOUS
Executable content was dropped or overwritten
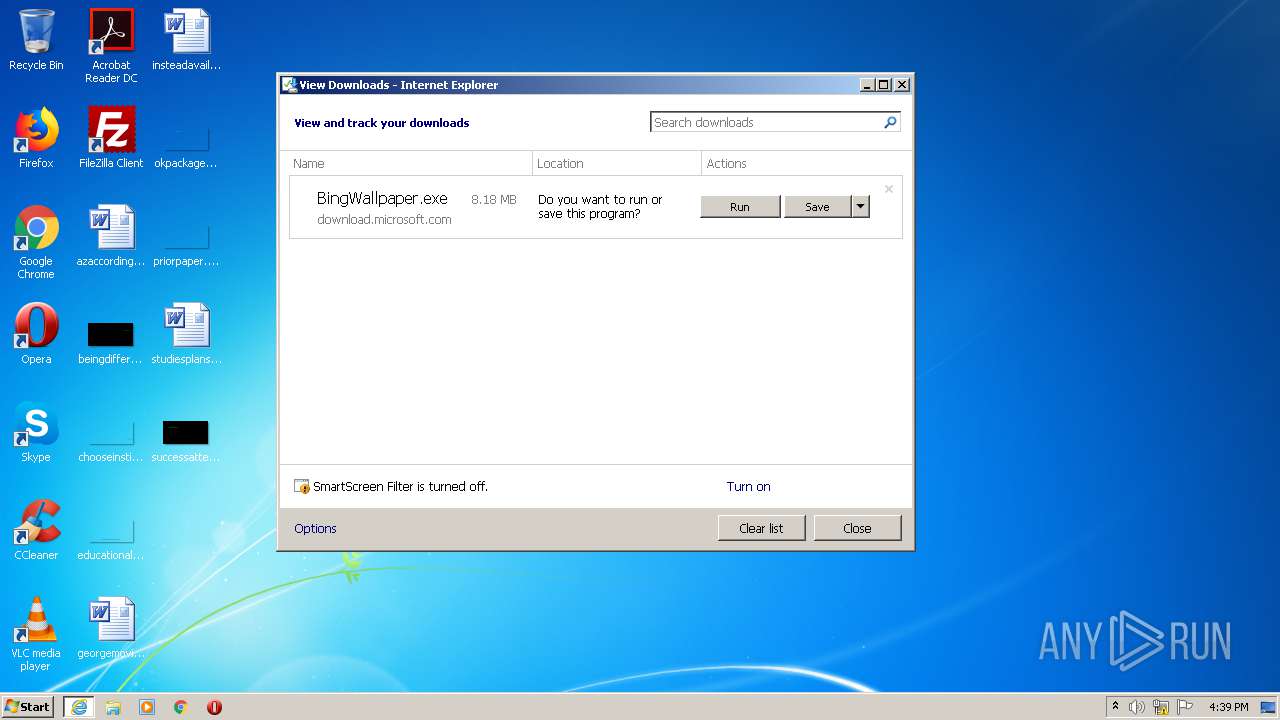
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 2420)
- BingWallpaper.exe (PID: 2012)
- rundll32.exe (PID: 3504)
- msiexec.exe (PID: 3520)
- rundll32.exe (PID: 2212)
- BingWallpaperApp.exe (PID: 3136)
Drops a file with too old compile date
- iexplore.exe (PID: 2420)
- iexplore.exe (PID: 2540)
- BingWallpaper.exe (PID: 2012)
- msiexec.exe (PID: 3520)
Drops a file that was compiled in debug mode
- iexplore.exe (PID: 2420)
- iexplore.exe (PID: 2540)
- BingWallpaper.exe (PID: 2012)
- msiexec.exe (PID: 3520)
- rundll32.exe (PID: 3504)
- rundll32.exe (PID: 2212)
- BingWallpaperApp.exe (PID: 3136)
Drops a file with a compile date too recent
- BingWallpaper.exe (PID: 2012)
- msiexec.exe (PID: 3520)
- rundll32.exe (PID: 3504)
- rundll32.exe (PID: 2212)
Reads Environment values
- BWInstaller.exe (PID: 2396)
- BingWallpaperApp.exe (PID: 3136)
Creates files in the user directory
- msiexec.exe (PID: 3520)
- DefaultSetup.exe (PID: 3240)
Changes the autorun value in the registry
- msiexec.exe (PID: 3520)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 3224)
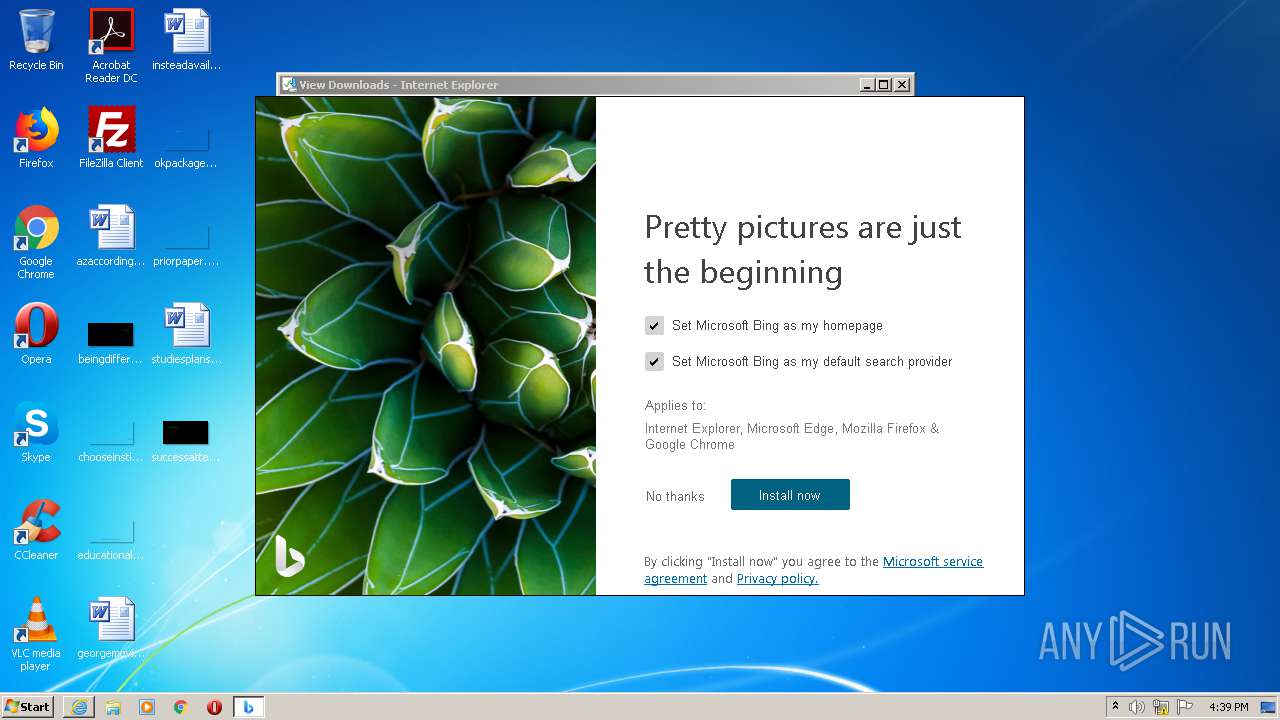
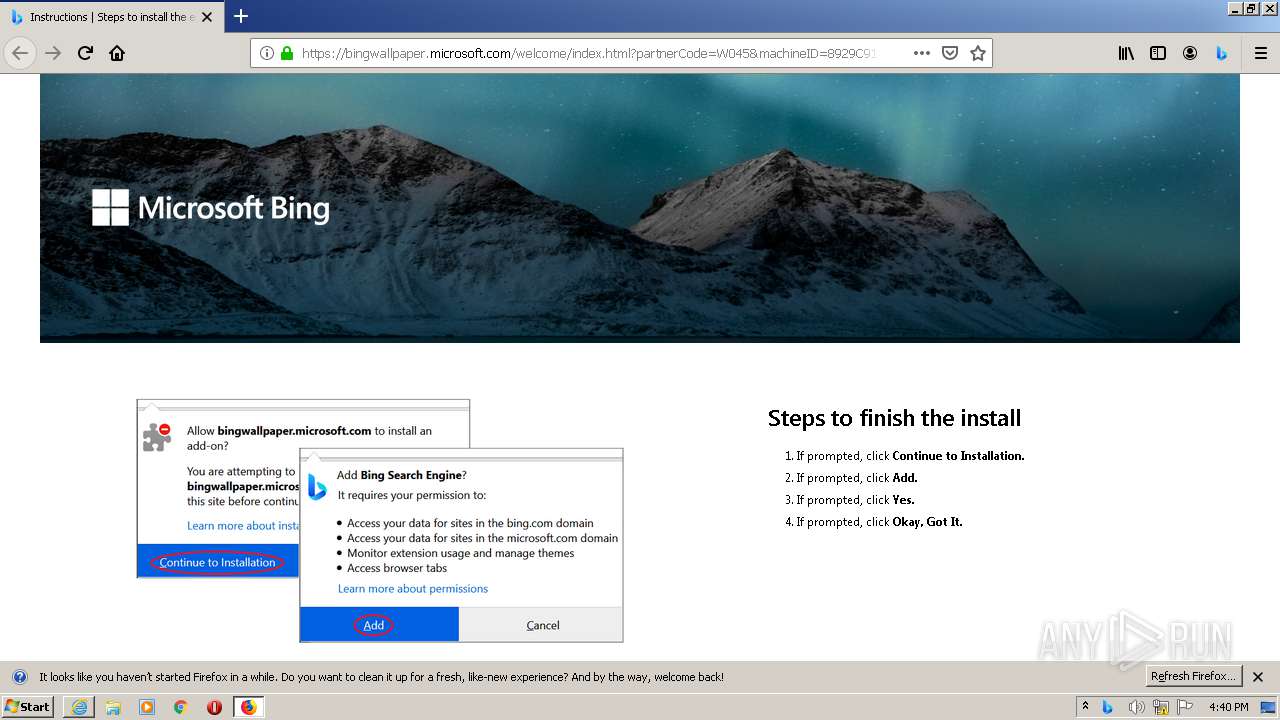
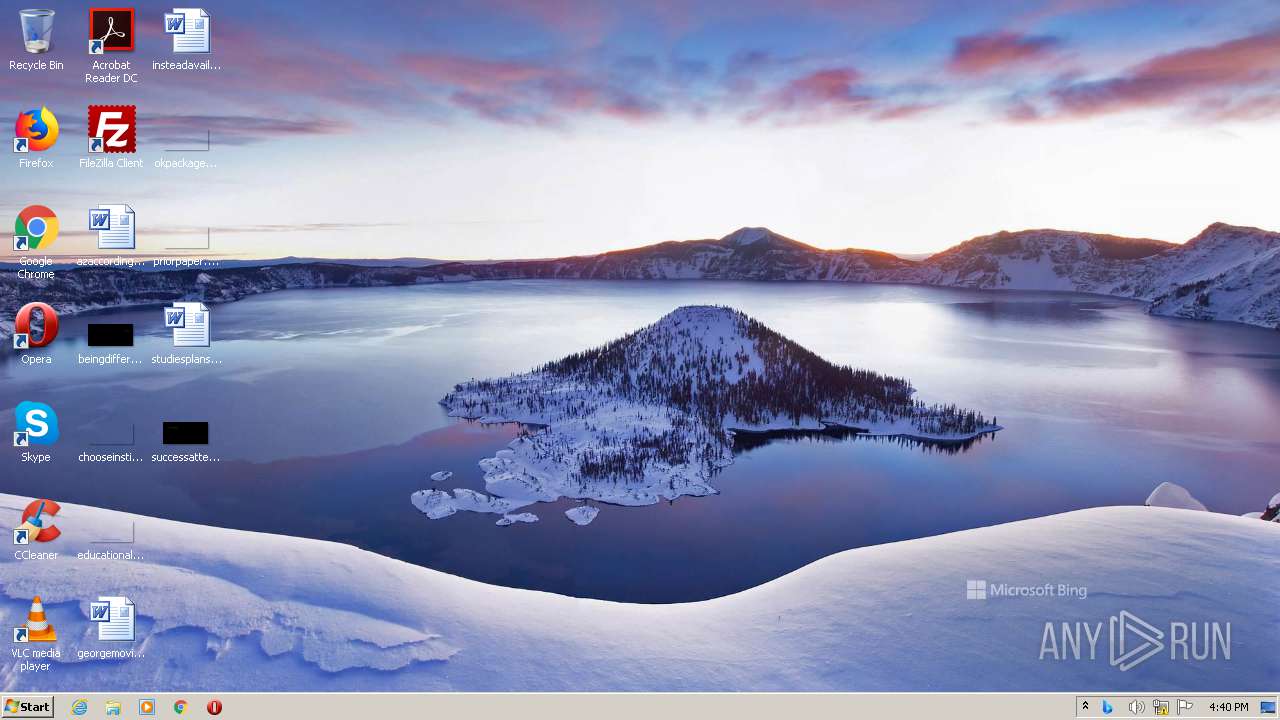
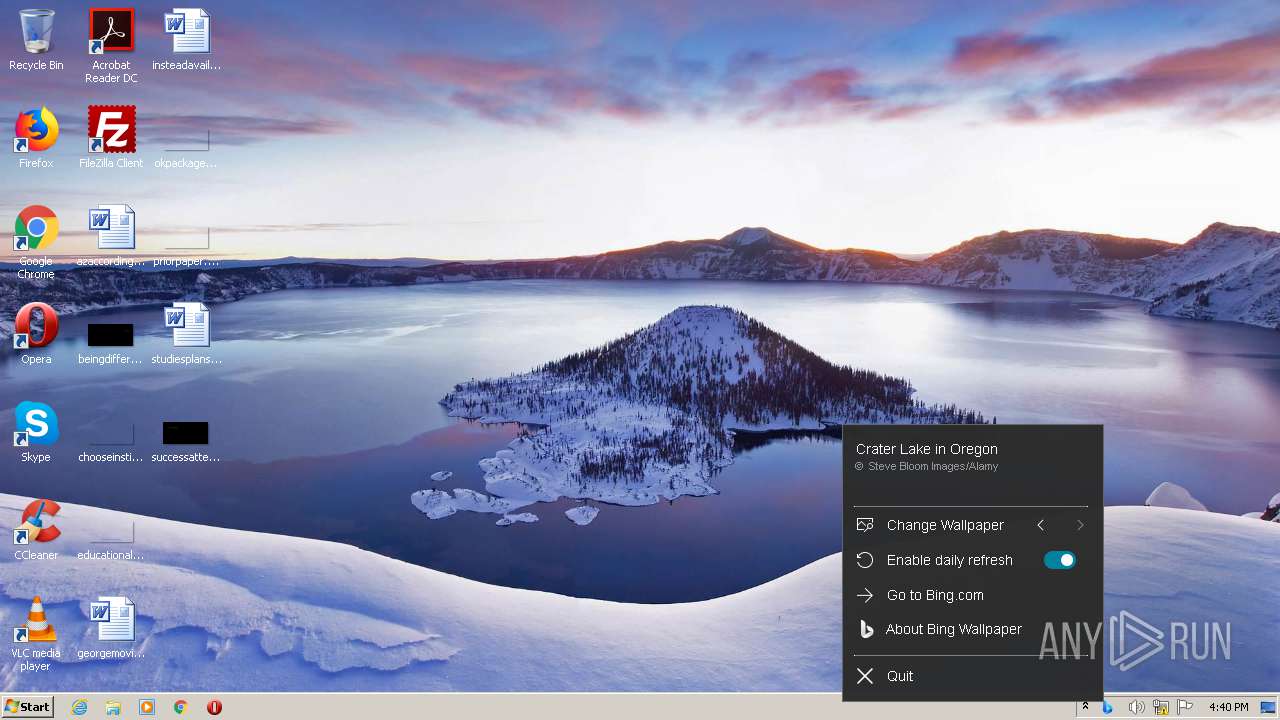
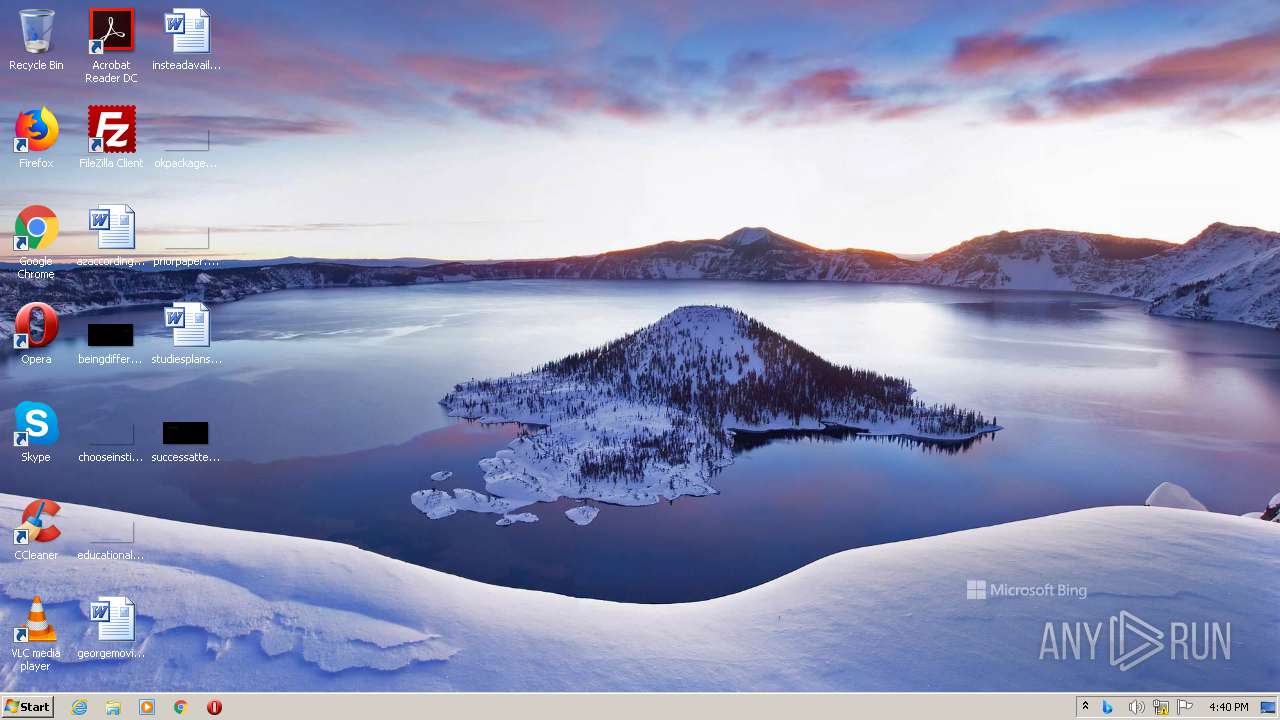
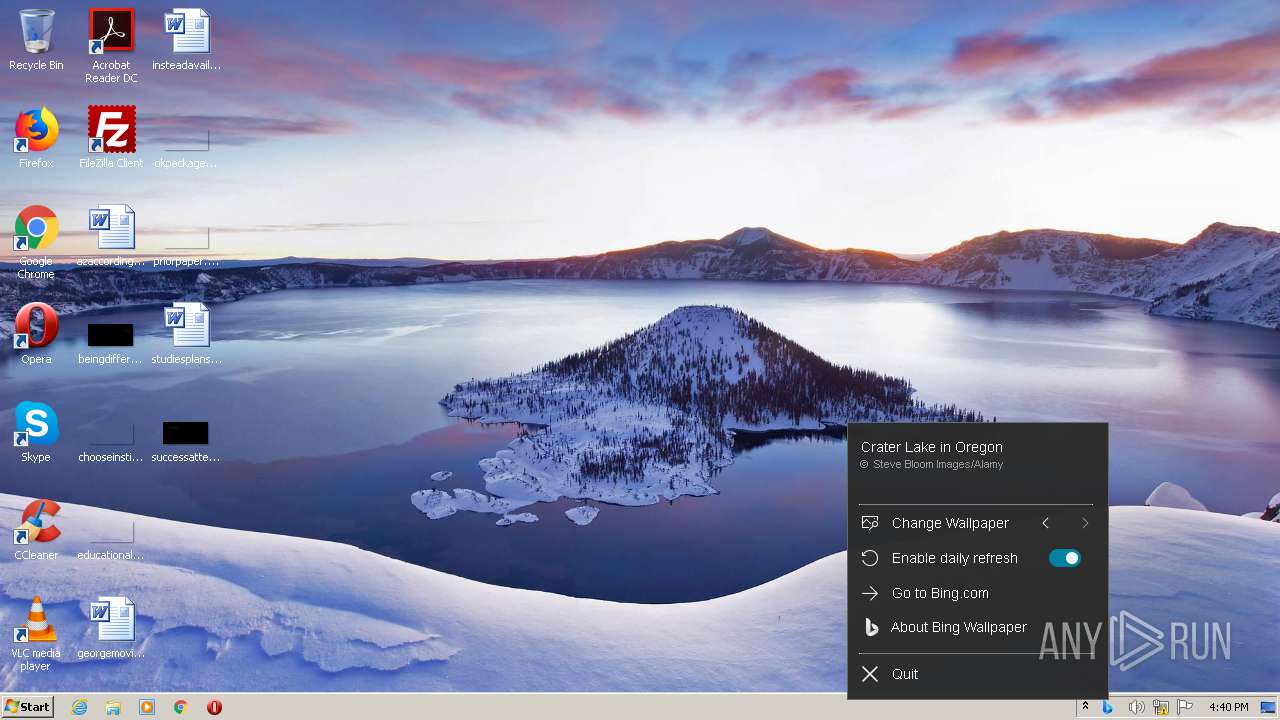
Changes the desktop background image
- BingWallpaperApp.exe (PID: 3136)
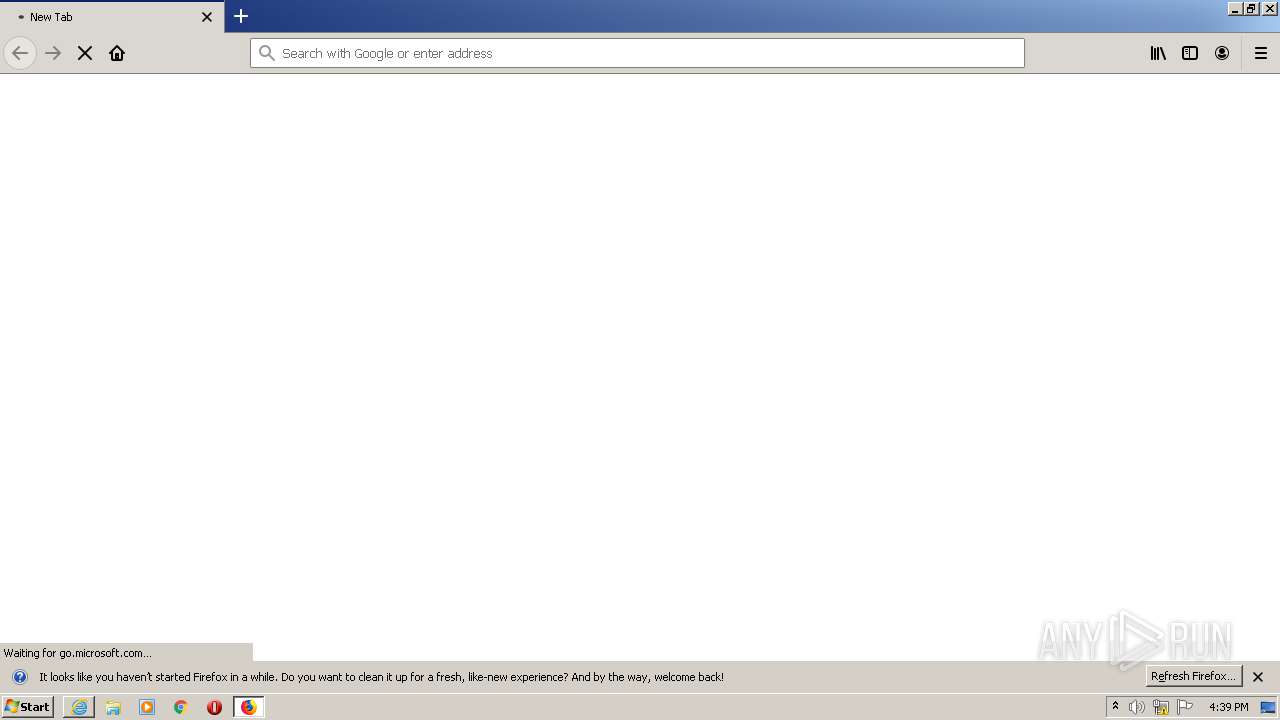
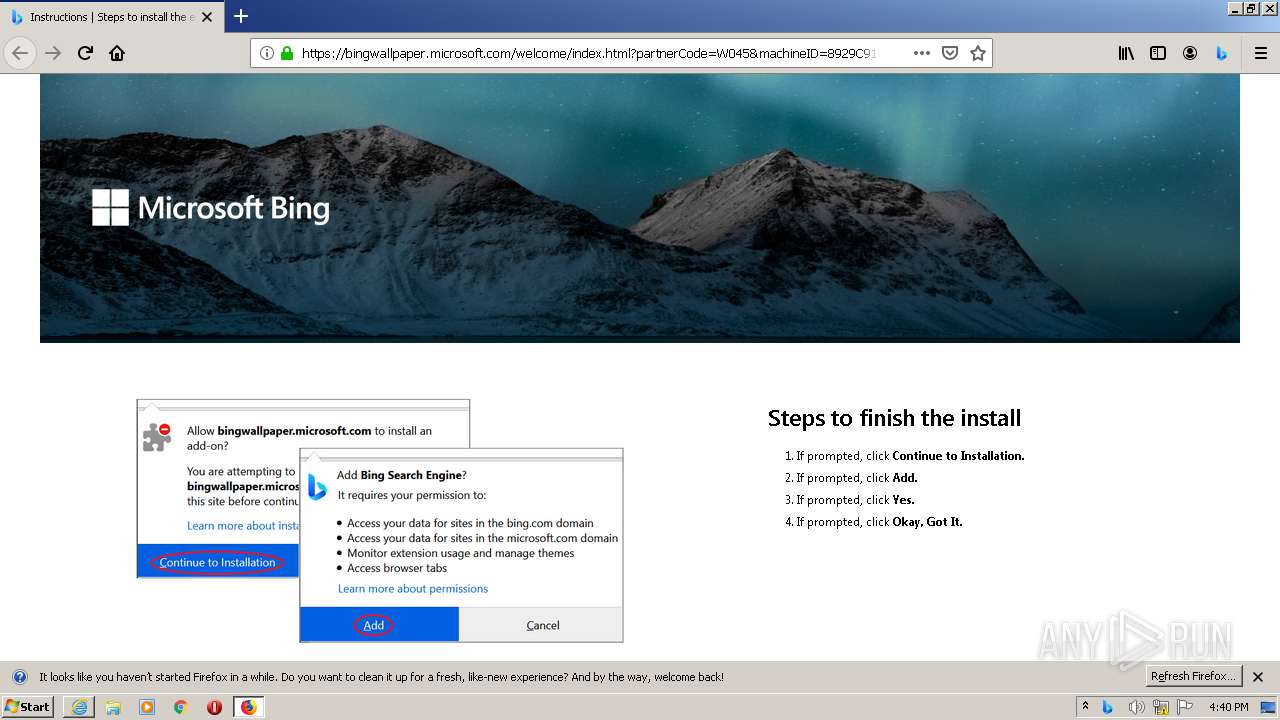
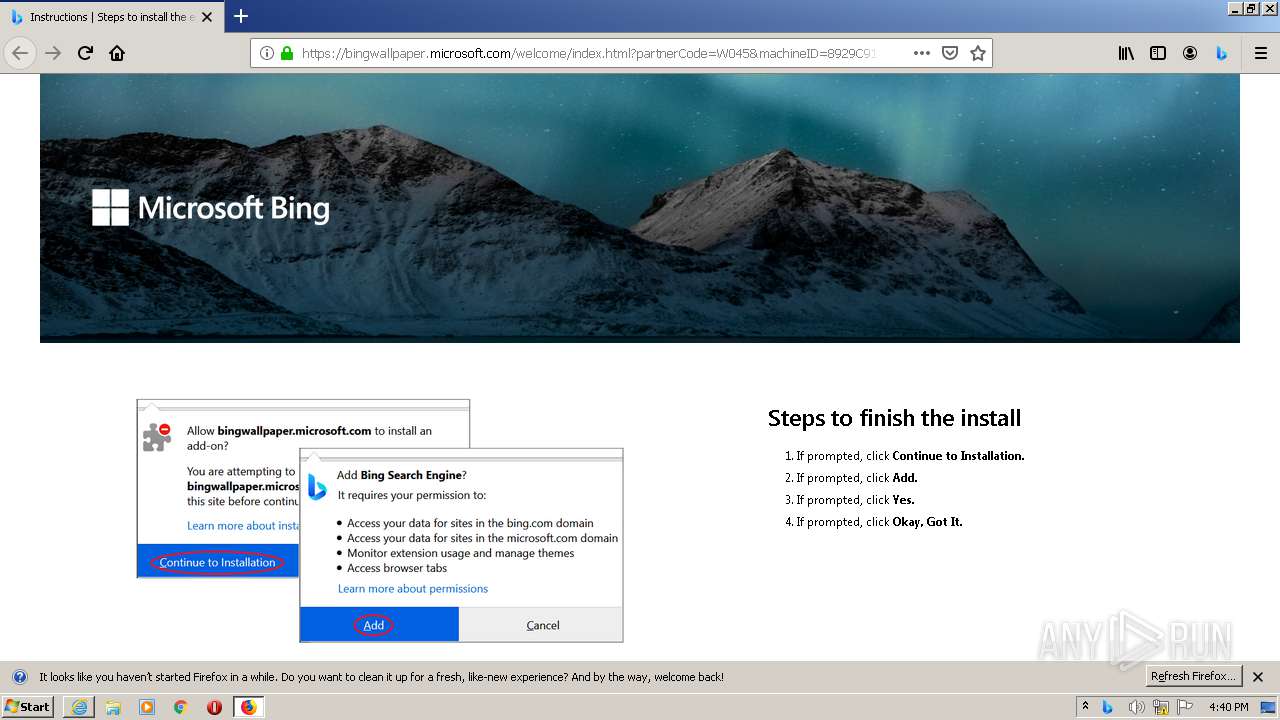
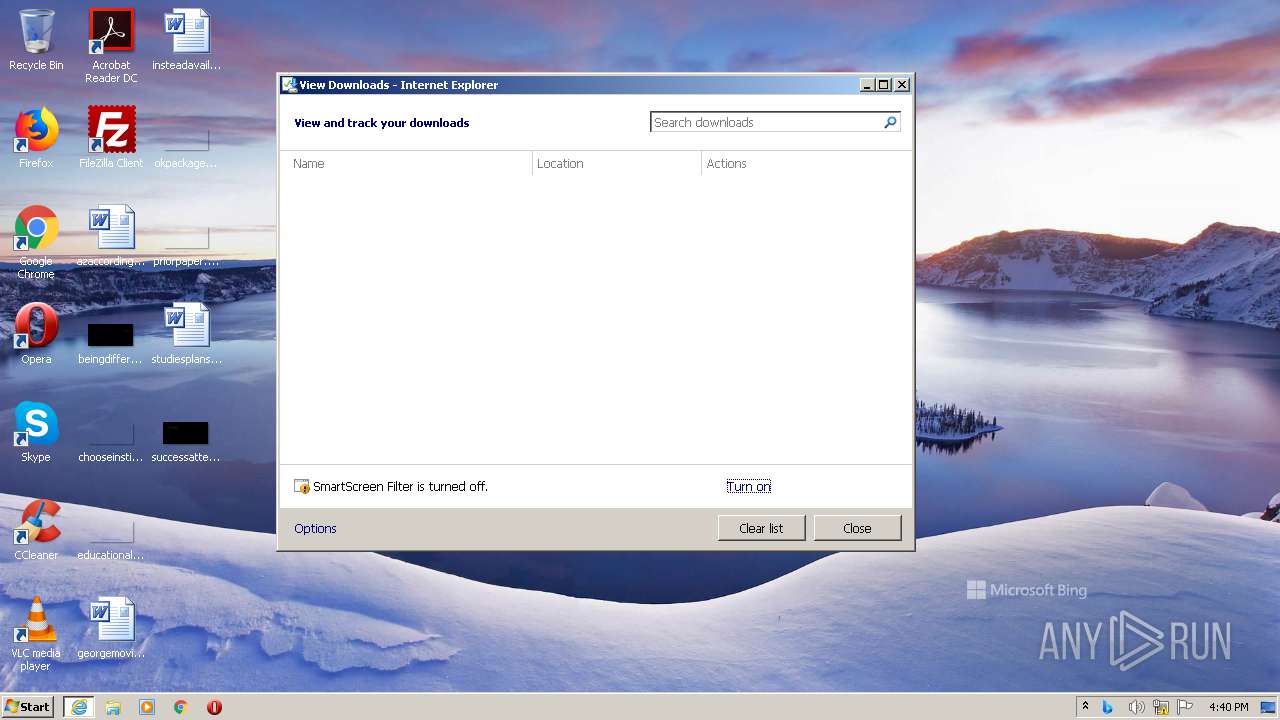
Starts Internet Explorer
- BingWallpaperApp.exe (PID: 3136)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 3016)
Application launched itself
- iexplore.exe (PID: 2540)
- msiexec.exe (PID: 3520)
- firefox.exe (PID: 3980)
- firefox.exe (PID: 3028)
- iexplore.exe (PID: 3016)
Reads settings of System Certificates
- iexplore.exe (PID: 2420)
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 300)
- iexplore.exe (PID: 3016)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2540)
Changes settings of System certificates
- iexplore.exe (PID: 2540)
- pingsender.exe (PID: 3816)
- iexplore.exe (PID: 3016)
- pingsender.exe (PID: 3420)
- pingsender.exe (PID: 2616)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 3016)
- pingsender.exe (PID: 3816)
- pingsender.exe (PID: 2616)
- pingsender.exe (PID: 3420)
Creates a software uninstall entry
- msiexec.exe (PID: 3520)
Reads CPU info
- firefox.exe (PID: 3028)
Creates files in the user directory
- firefox.exe (PID: 3028)
- iexplore.exe (PID: 2540)
Creates files in the program directory
- firefox.exe (PID: 3028)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3028)
- iexplore.exe (PID: 3016)
Reads internet explorer settings
- iexplore.exe (PID: 300)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
25
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3016 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 692 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3028.27.164687748\1187120801" -childID 4 -isForBrowser -prefsHandle 3520 -prefMapHandle 3516 -prefsLen 9730 -prefMapSize 191870 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3028 "\\.\pipe\gecko-crash-server-pipe.3028" 3056 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2012 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\BingWallpaper.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\BingWallpaper.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BingWallpaper Exit code: 0 Version: 1.0.8.2 Modules
| |||||||||||||||
| 2212 | rundll32.exe "C:\Windows\Installer\MSIA278.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1417859 12 CustomActions!CustomActions.CustomActions.CleanBingService | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2220 | "C:\Windows\System32\msiexec.exe" /q /i BWCInstaller.msi /norestart | C:\Windows\System32\msiexec.exe | — | BWInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3028.13.82824160\1378870470" -childID 2 -isForBrowser -prefsHandle 2832 -prefMapHandle 2836 -prefsLen 5996 -prefMapSize 191870 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3028 "\\.\pipe\gecko-crash-server-pipe.3028" 2848 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2384 | rundll32.exe "C:\Windows\Installer\MSIA110.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1417515 7 CustomActions!CustomActions.CustomActions.VSRegisterCheck | C:\Windows\system32\rundll32.exe | — | MsiExec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3028.3.1827527527\877751511" -childID 1 -isForBrowser -prefsHandle 1772 -prefMapHandle 1768 -prefsLen 1 -prefMapSize 191870 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3028 "\\.\pipe\gecko-crash-server-pipe.3028" 1792 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 2396 | "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\BWInstaller.exe" | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\BWInstaller.exe | StartupInstaller.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: BWInstaller Exit code: 0 Version: 1.0.8.2 Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2540 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
3 079
Read events
2 677
Write events
379
Delete events
23
Modification events
| (PID) Process: | (2420) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2420) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2420) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 33515748 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30864587 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
23
Suspicious files
220
Text files
127
Unknown types
84
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3E89.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar3E8A.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\BingWallpaper[1].exe | — | |
MD5:— | SHA256:— | |||
| 2540 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD5F8337DE9CB21FF.TMP | — | |
MD5:— | SHA256:— | |||
| 2540 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\BingWallpaper.exe.glxi45t.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2012 | BingWallpaper.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\BWCInstaller.msi | — | |
MD5:— | SHA256:— | |||
| 2420 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2396 | BWInstaller.exe | C:\Users\admin\AppData\Local\Temp\ZMG721C.tmp | — | |
MD5:— | SHA256:— | |||
| 2396 | BWInstaller.exe | C:\Users\admin\AppData\Local\Temp\ZMG724C.tmp | — | |
MD5:— | SHA256:— | |||
| 2396 | BWInstaller.exe | C:\Users\admin\AppData\Local\Temp\ZMG725D.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
137
TCP/UDP connections
103
DNS requests
144
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2396 | BWInstaller.exe | GET | 200 | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=8929C91FFFA147AE9FCB2CB59F391AB9&LV=1.0.8.2&OS=6.1.7601.1&TE=40&TV=isW045%7cpkBWInstaller%7ctmen-us%7chdIE2%2cMF1%2cGC1%7csdIE2%2cMF1%2cGC1%7chpBing%7cdbIE%7crt2%7cpt1 | US | — | — | suspicious |
3240 | DefaultSetup.exe | GET | 200 | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=8929C91FFFA147AE9FCB2CB59F391AB9&LV=1.7.74.0&OS=6.1.7601.1&TE=24&TV=isW045%7cpkBrowserDefMgr%7crt1%7ctmen-us%7chdGC75.0.3770.100%2c1%7csdGC75.0.3770.100%2c1%7cseGC75.0.3770.100%2c1%7chpGC75.0.3770.100%2c1%7ccd2021-01-27%7cct16:39:55:540 | US | — | — | suspicious |
3240 | DefaultSetup.exe | GET | 200 | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=8929C91FFFA147AE9FCB2CB59F391AB9&LV=1.7.74.0&OS=6.1.7601.1&TE=23&TV=isW045%7cpkBrowserDefMgr%7crt1%7ctmen-us%7chdMF68.0.0.0%2c1%7csdMF68.0.0.0%2c1%7cseMF68.0.0.0%2c1%7chpMF68.0.0.0%2c1%7ccd2021-01-27%7cct16:39:55:540 | US | — | — | suspicious |
3028 | firefox.exe | GET | 200 | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=B3D6ECDB15E7850D69246872CDD0B741&LV=0.0.0.9&OS=WindowsNT6.1;rv:68.0&TE=37&TV=isW045%7CpkMicrosoftBingSearchEngine%7Ctmen-US%7CbvFirefox68.0%7Cexbingwallpaperdse@microsoft.com%7Ces1 | US | — | — | suspicious |
2420 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3028 | firefox.exe | POST | 200 | 104.18.24.243:80 | http://ocsp.msocsp.com/ | US | der | 1.71 Kb | whitelisted |
3028 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3028 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3028 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2540 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
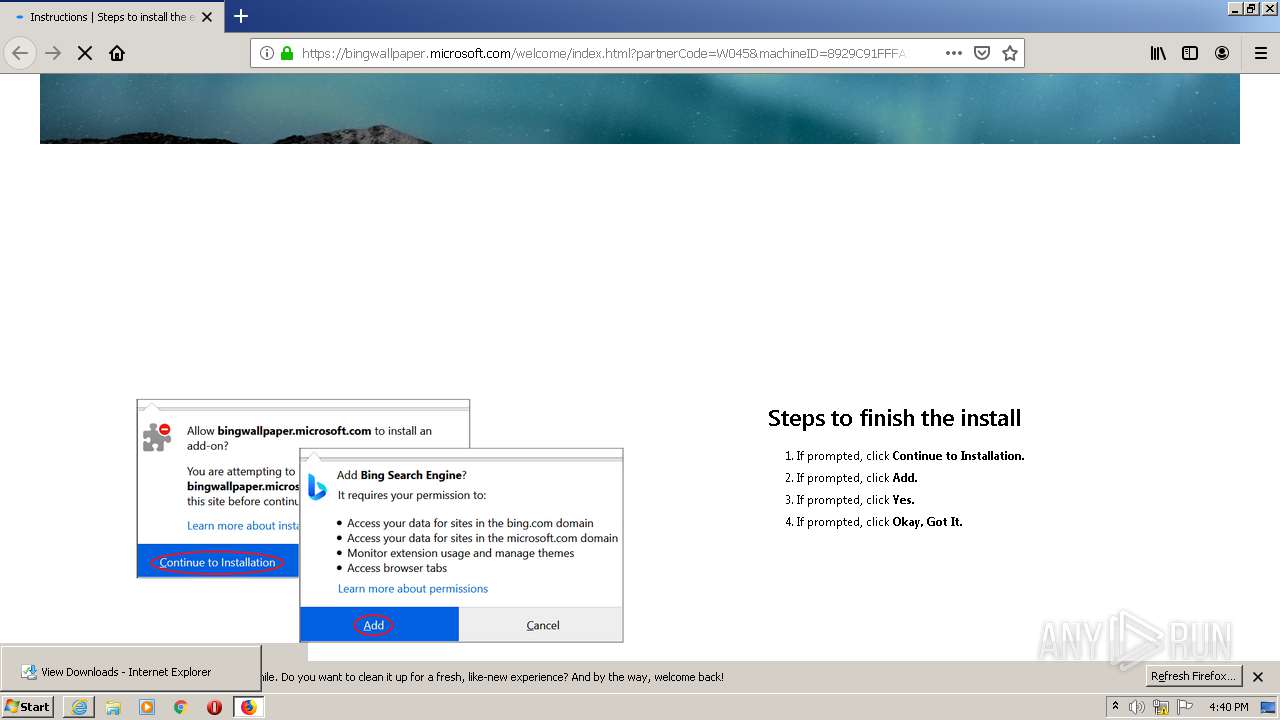
2420 | iexplore.exe | 23.205.239.104:443 | go.microsoft.com | GTT Communications Inc. | NL | unknown |
2420 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2420 | iexplore.exe | 52.173.134.115:443 | bingwallpaper.microsoft.com | Microsoft Corporation | US | unknown |
2396 | BWInstaller.exe | 20.41.62.11:80 | g.ceipmsn.com | — | US | suspicious |
3028 | firefox.exe | 92.123.16.55:443 | go.microsoft.com | Telia Company AB | FR | malicious |
3028 | firefox.exe | 34.213.158.239:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3028 | firefox.exe | 34.212.188.196:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3028 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3028 | firefox.exe | 143.204.209.27:443 | snippets.cdn.mozilla.net | — | US | unknown |
3028 | firefox.exe | 52.173.134.115:443 | bingwallpaper.microsoft.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
bingwallpaper.microsoft.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
download.microsoft.com |
| whitelisted |
g.ceipmsn.com |
| suspicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1064 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1064 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1064 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1064 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |