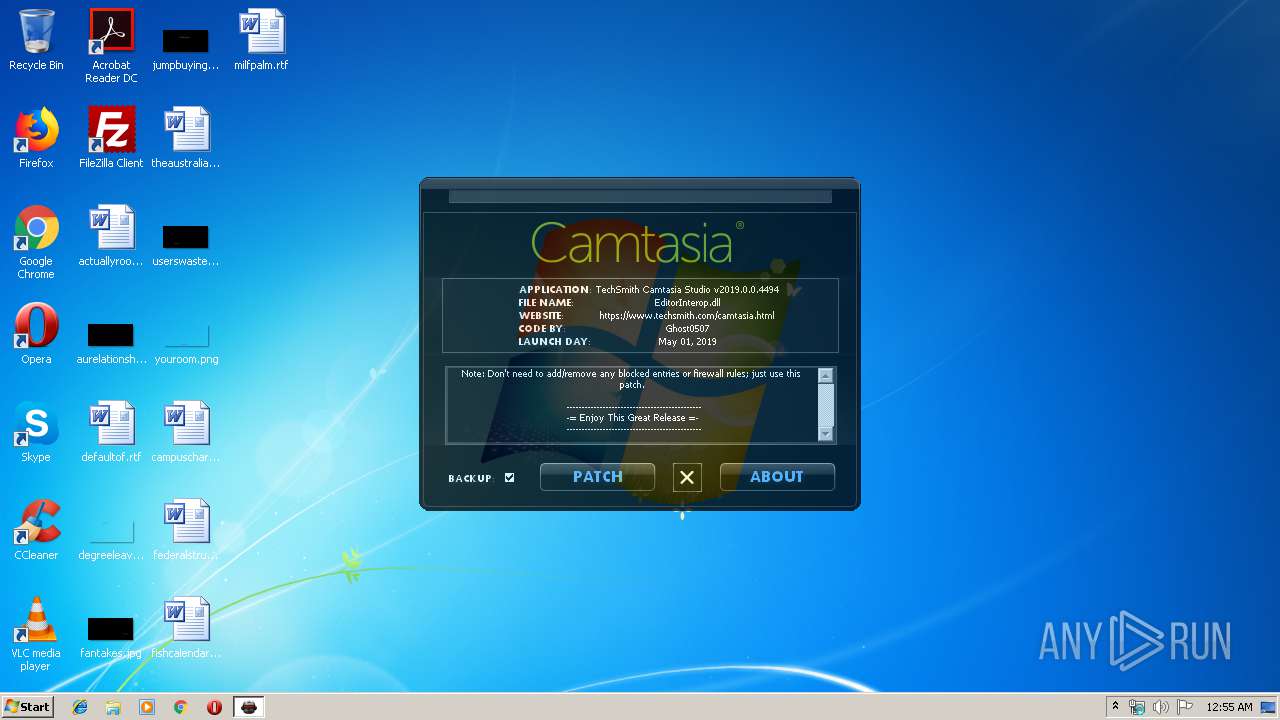
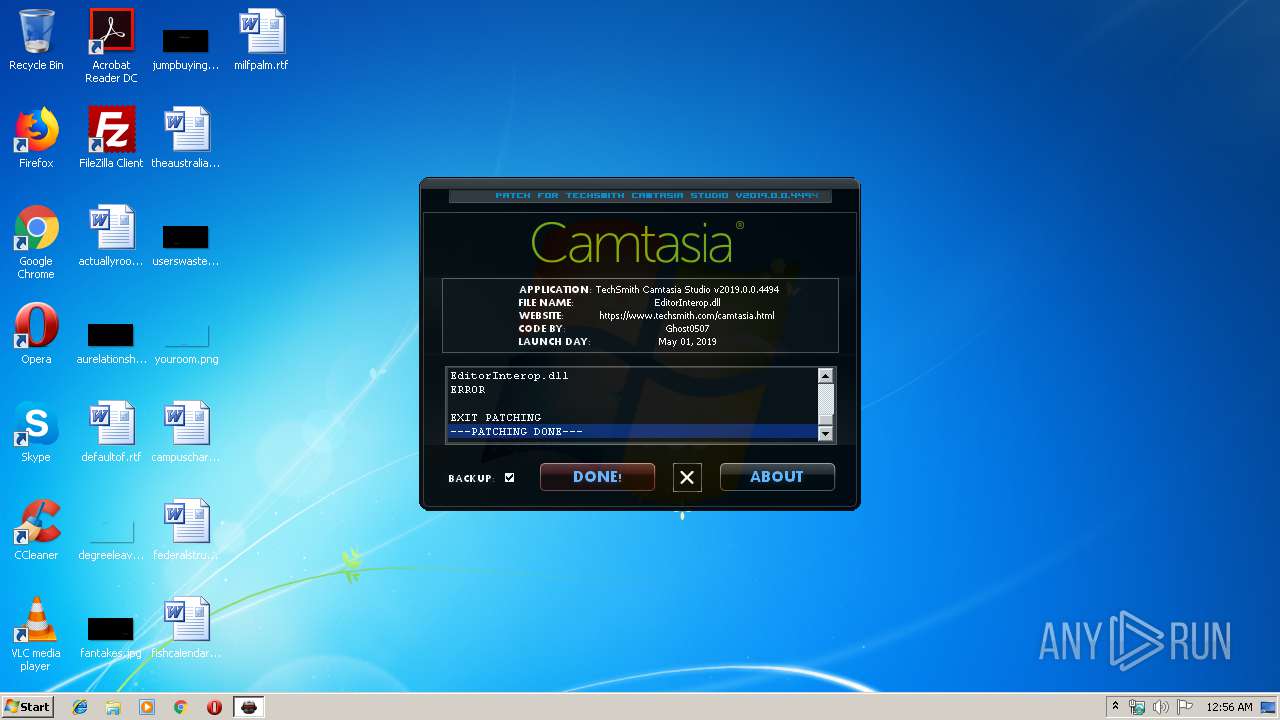
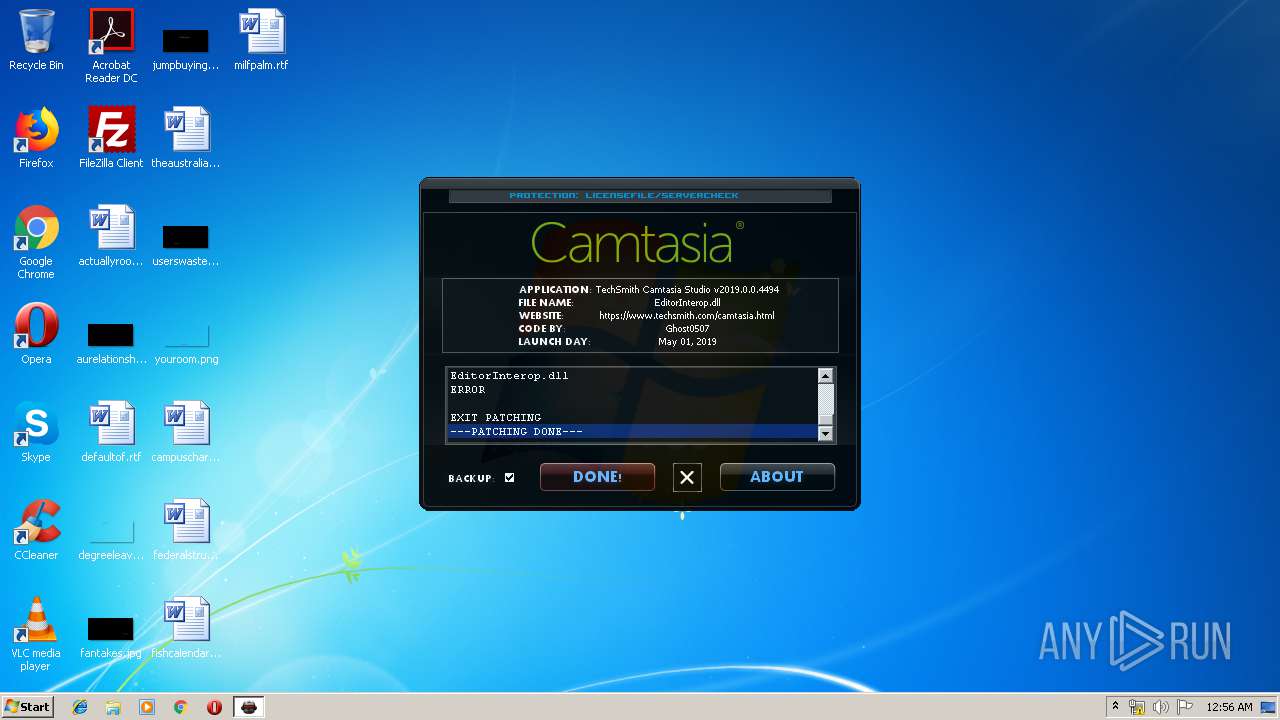
| File name: | techsmith.camtasia.studio.v2019.0.0.4494.patch.exe |
| Full analysis: | https://app.any.run/tasks/6af98306-39fc-4cf2-9706-22309b5f19eb |
| Verdict: | Suspicious activity |
| Analysis date: | October 29, 2019, 00:55:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 996D50B5DAD8333847BE5974CE4A658A |
| SHA1: | 719F5DCA80E4E42468C9664B535E9F24D8FC65D3 |
| SHA256: | 0B09A5BB086752AD641261F8447272D6651B3C402B07C2495FAC3921EDDB6F0F |
| SSDEEP: | 24576:8ts2NeicTERyyo3sBfxEOk7lV9kJs+D44M:8tkTEEWG5Syc |
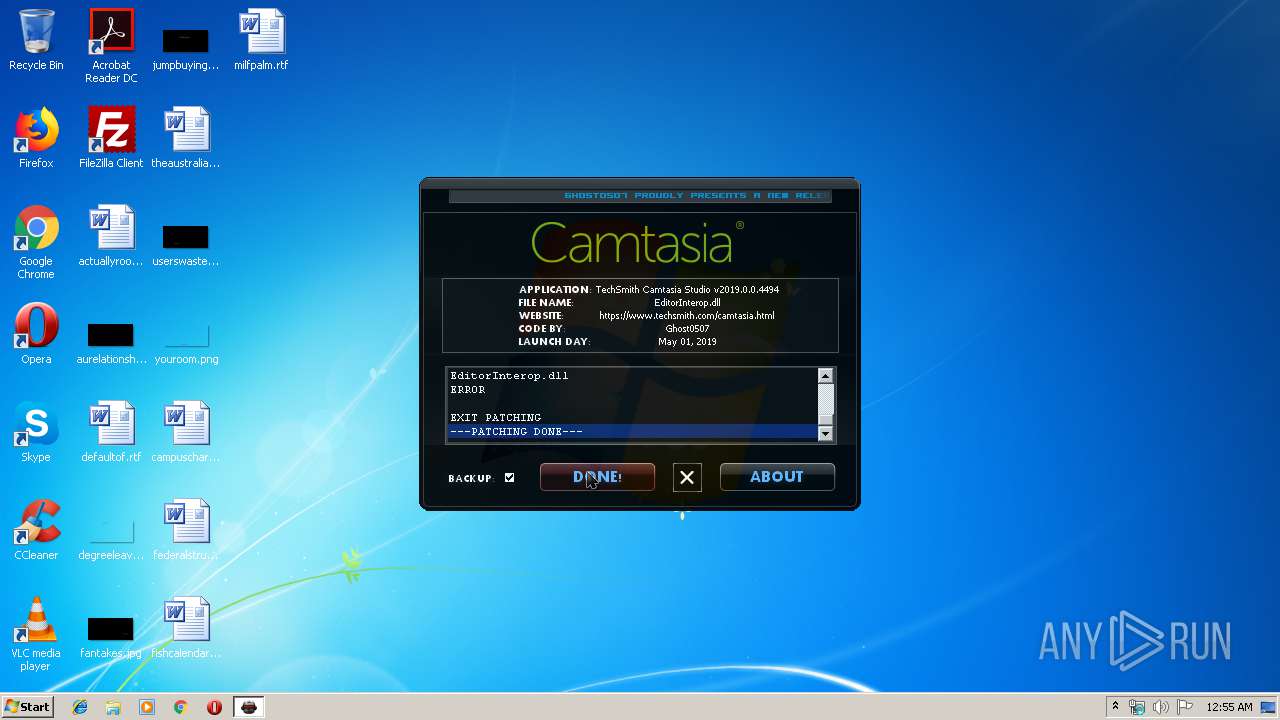
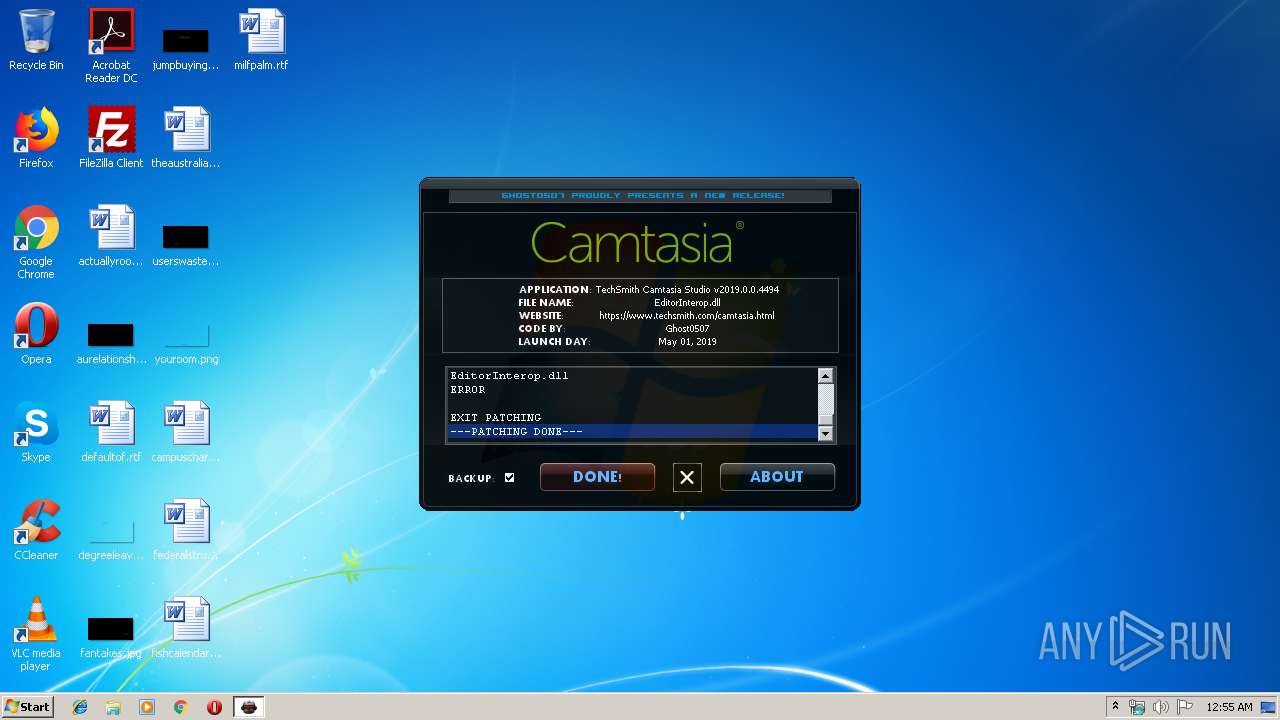
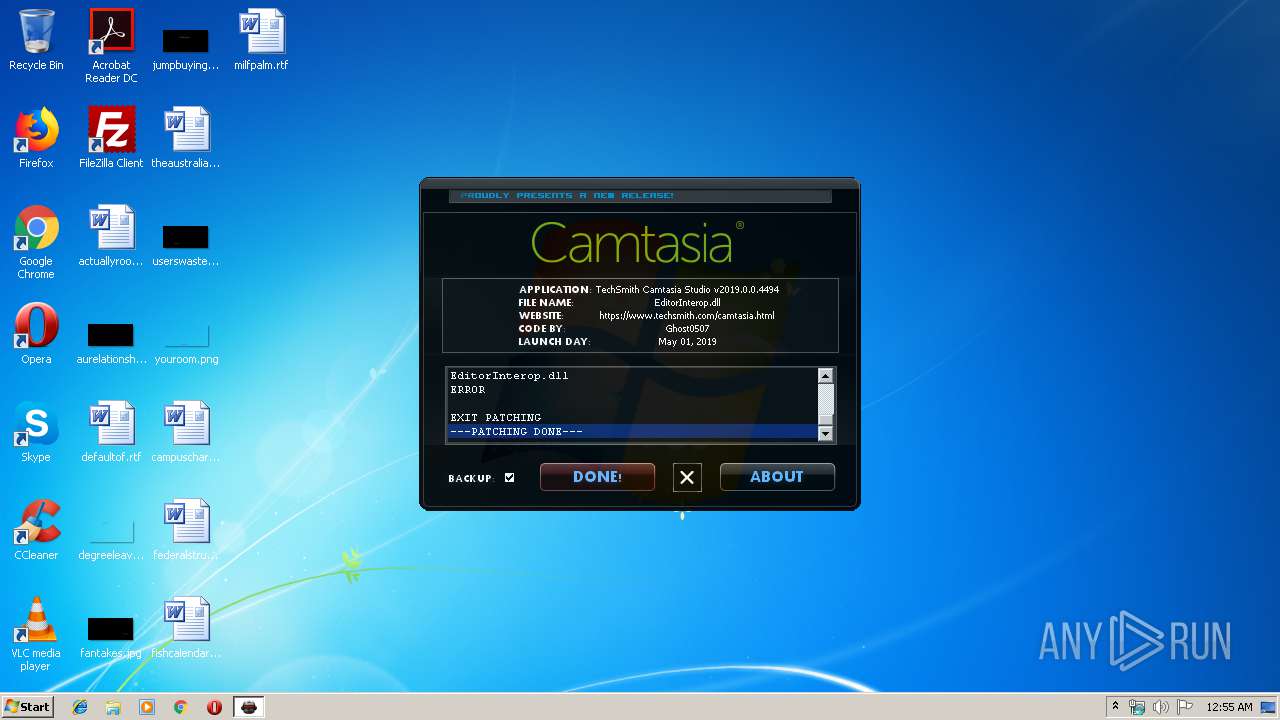
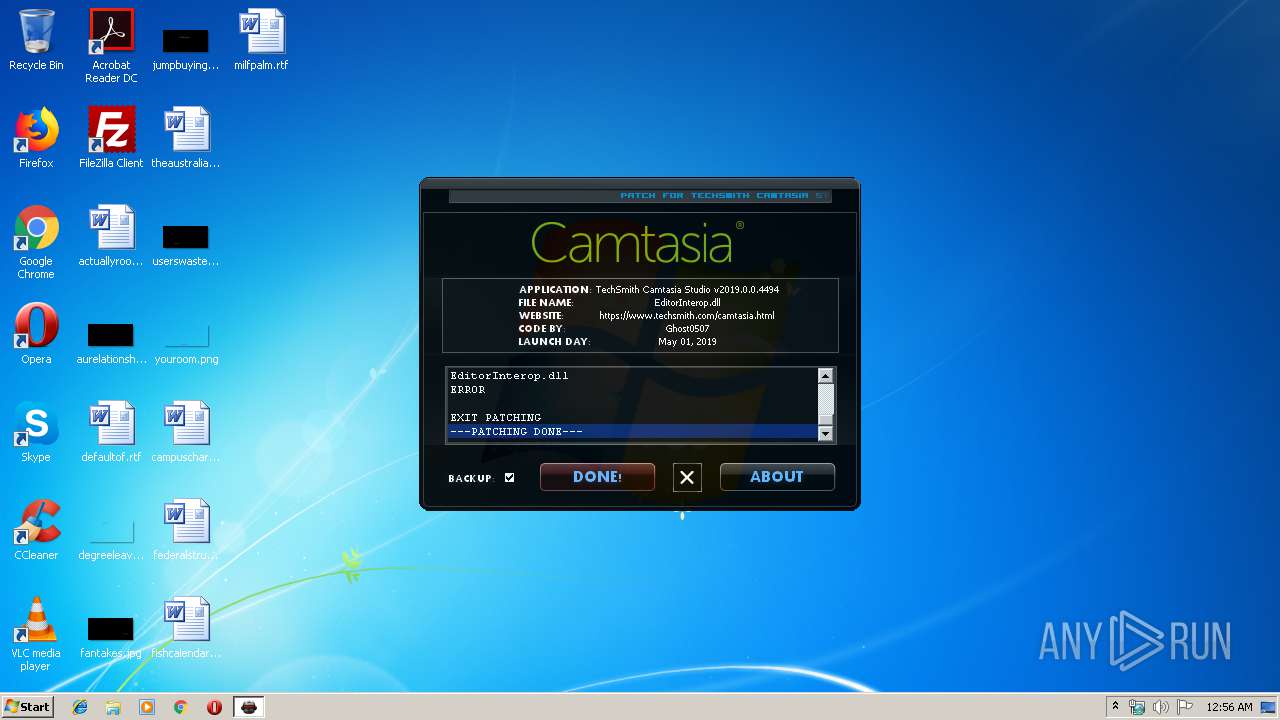
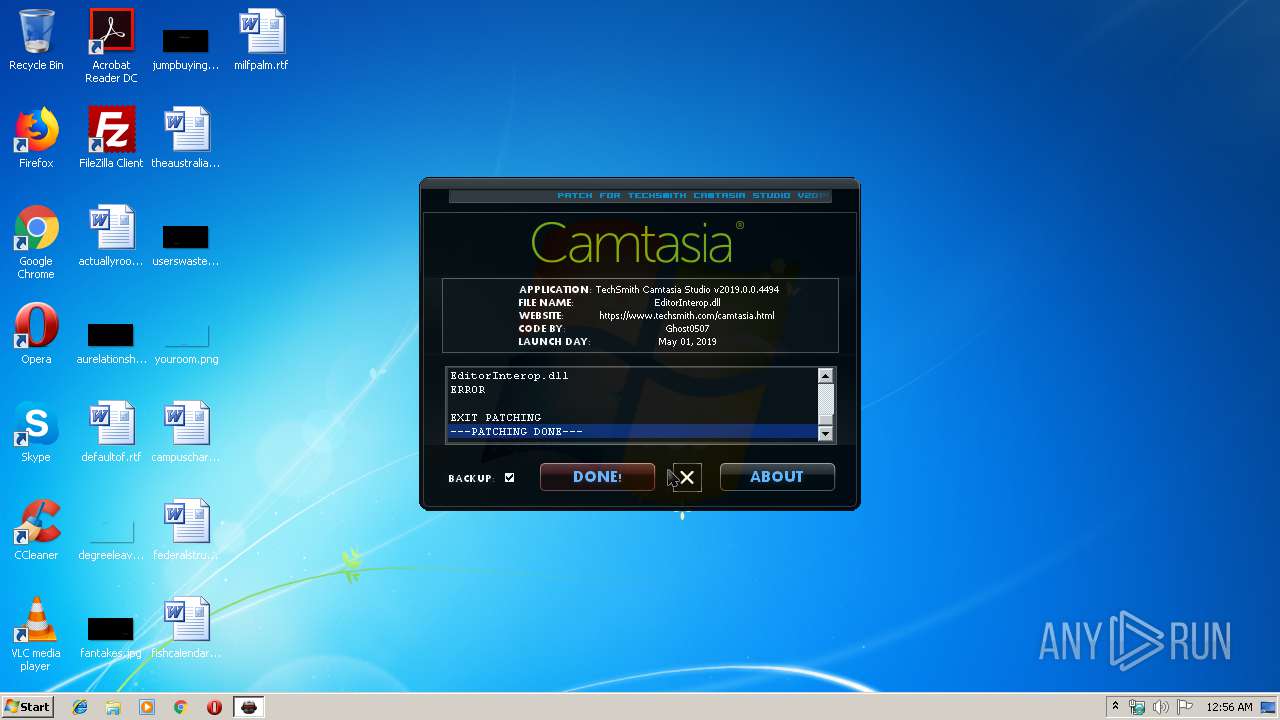
MALICIOUS
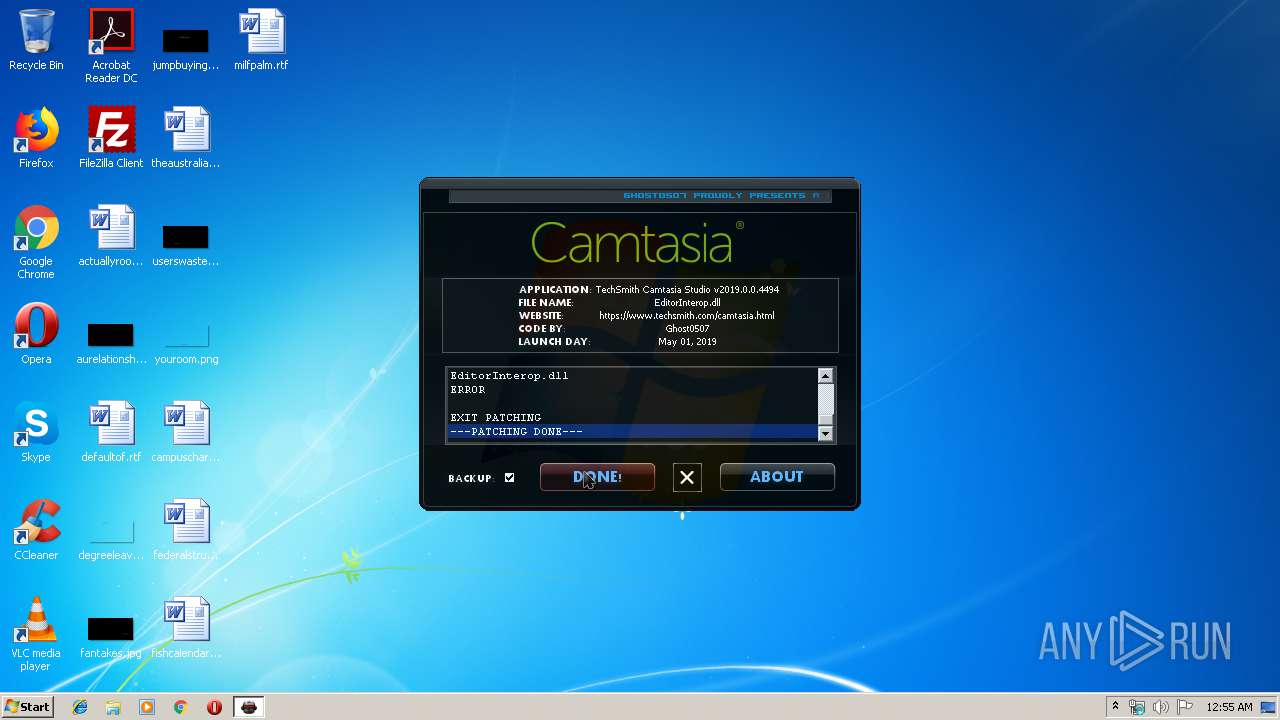
Loads dropped or rewritten executable
- techsmith.camtasia.studio.v2019.0.0.4494.patch.exe (PID: 2960)
SUSPICIOUS
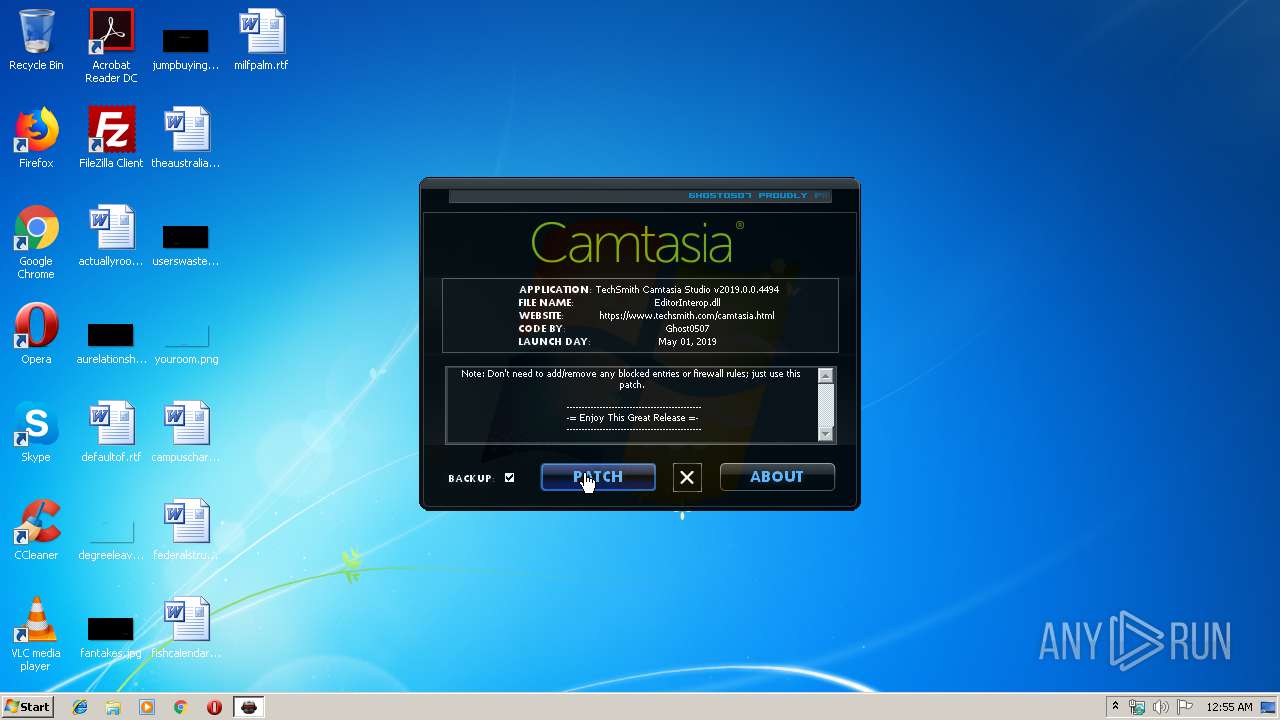
Starts CMD.EXE for commands execution
- techsmith.camtasia.studio.v2019.0.0.4494.patch.exe (PID: 2960)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3028)
Executable content was dropped or overwritten
- techsmith.camtasia.studio.v2019.0.0.4494.patch.exe (PID: 2960)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 916992 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x000DF6D8 | 0x000DF800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.90248 |
.reloc | 0x000E4000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.02842 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.14661 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.2615 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.35684 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
500 | 2.70758 | 76 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
DLL | 7.99976 | 747008 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
Total processes
43
Monitored processes
5
Malicious processes
0
Suspicious processes
1
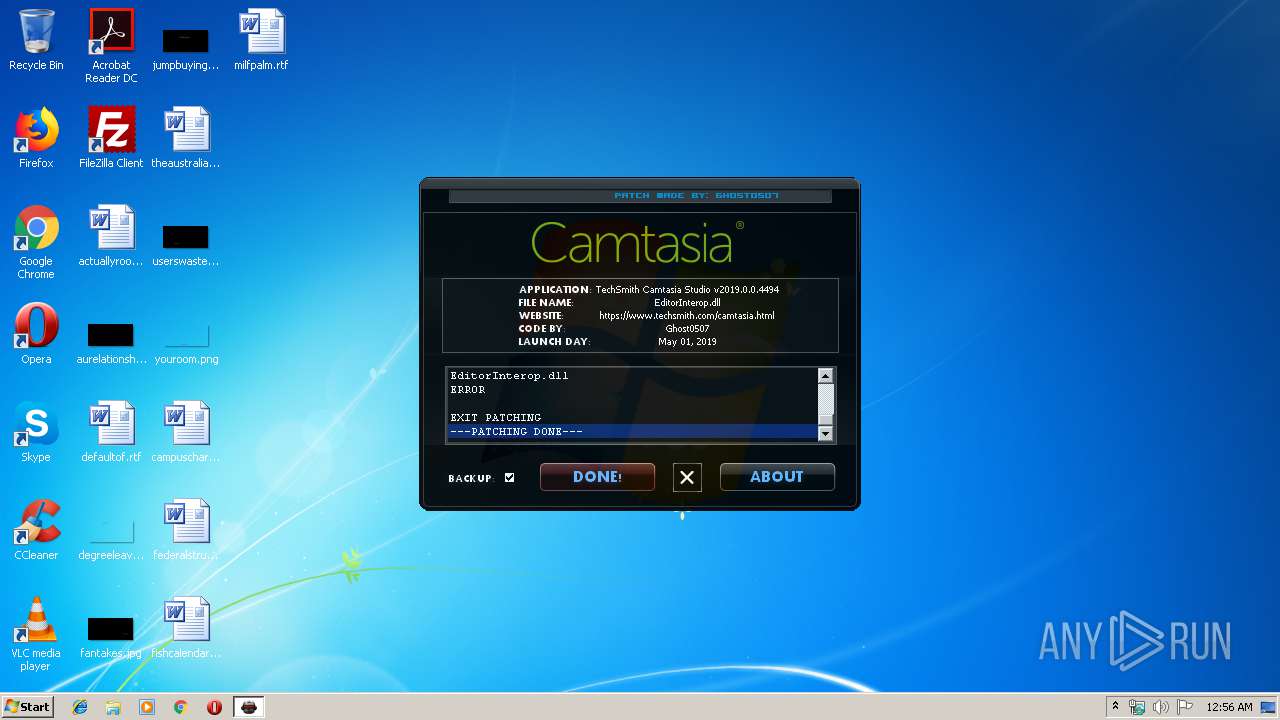
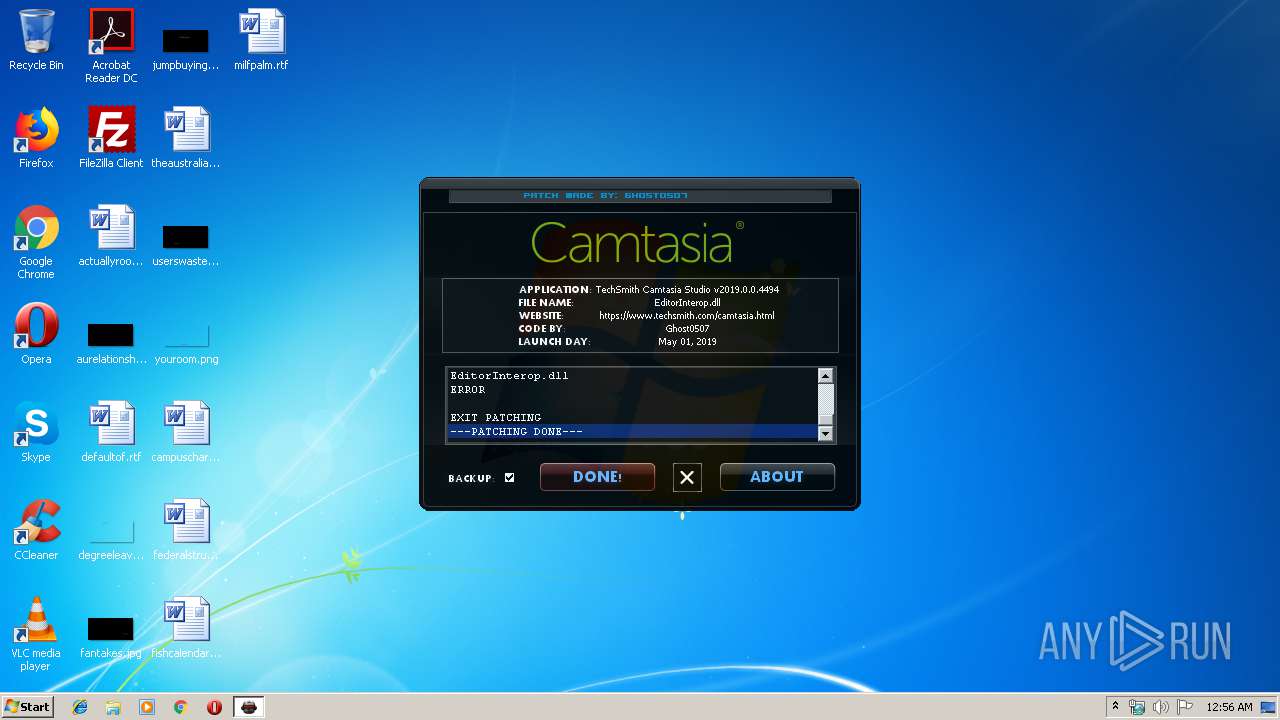
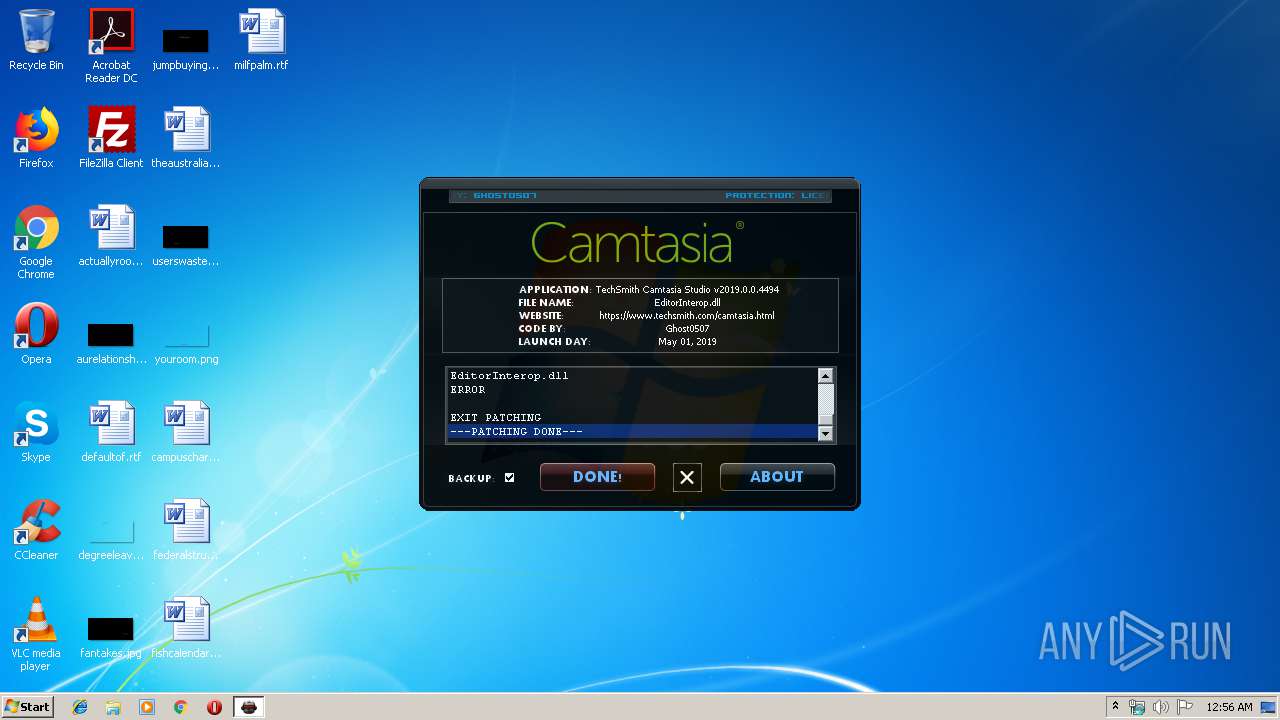
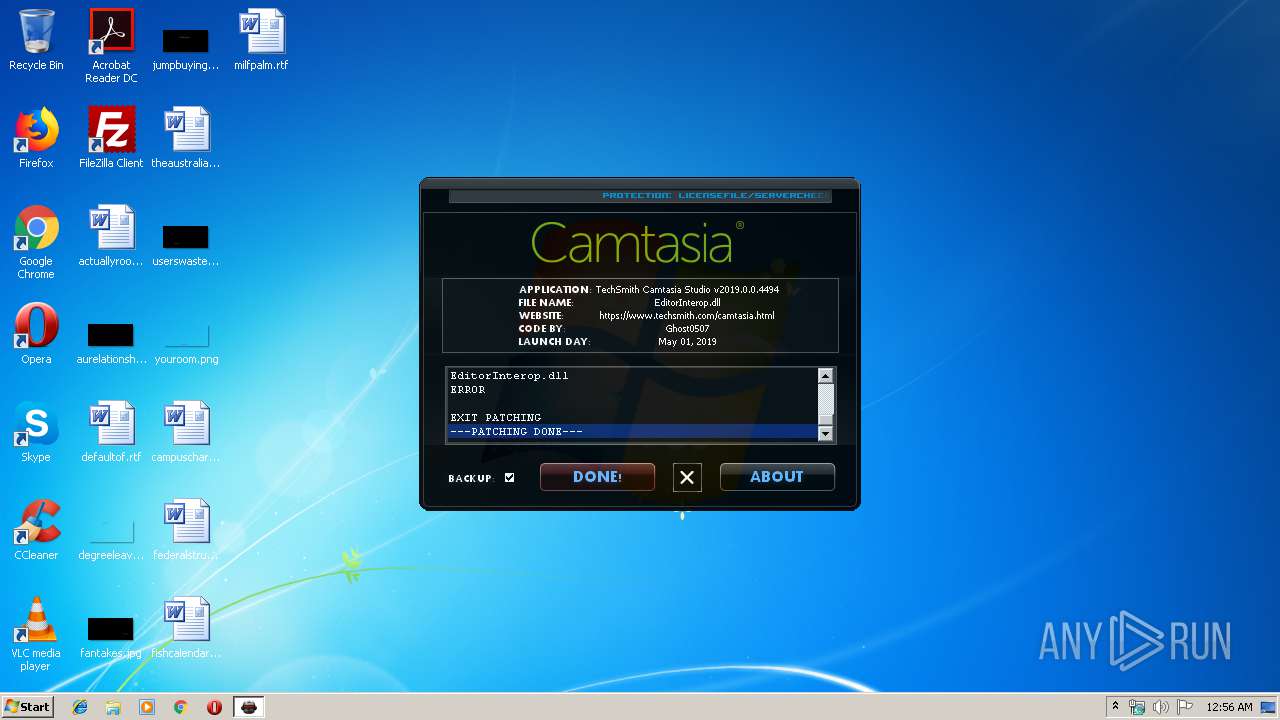
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1536 | "C:\Users\admin\AppData\Local\Temp\techsmith.camtasia.studio.v2019.0.0.4494.patch.exe" | C:\Users\admin\AppData\Local\Temp\techsmith.camtasia.studio.v2019.0.0.4494.patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1756 | taskkill /f /im CamtasiaStudio.exe /t | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1932 | taskkill /f /im CamRecorder.exe /t | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\AppData\Local\Temp\techsmith.camtasia.studio.v2019.0.0.4494.patch.exe" | C:\Users\admin\AppData\Local\Temp\techsmith.camtasia.studio.v2019.0.0.4494.patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
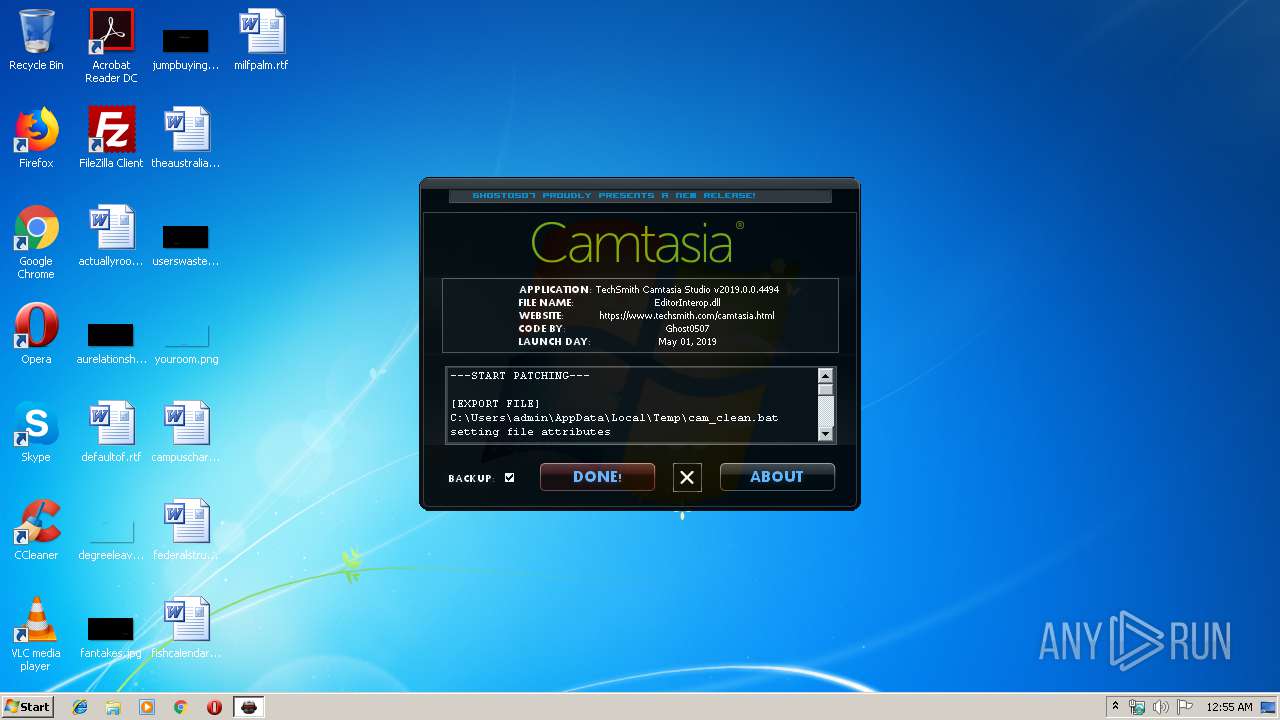
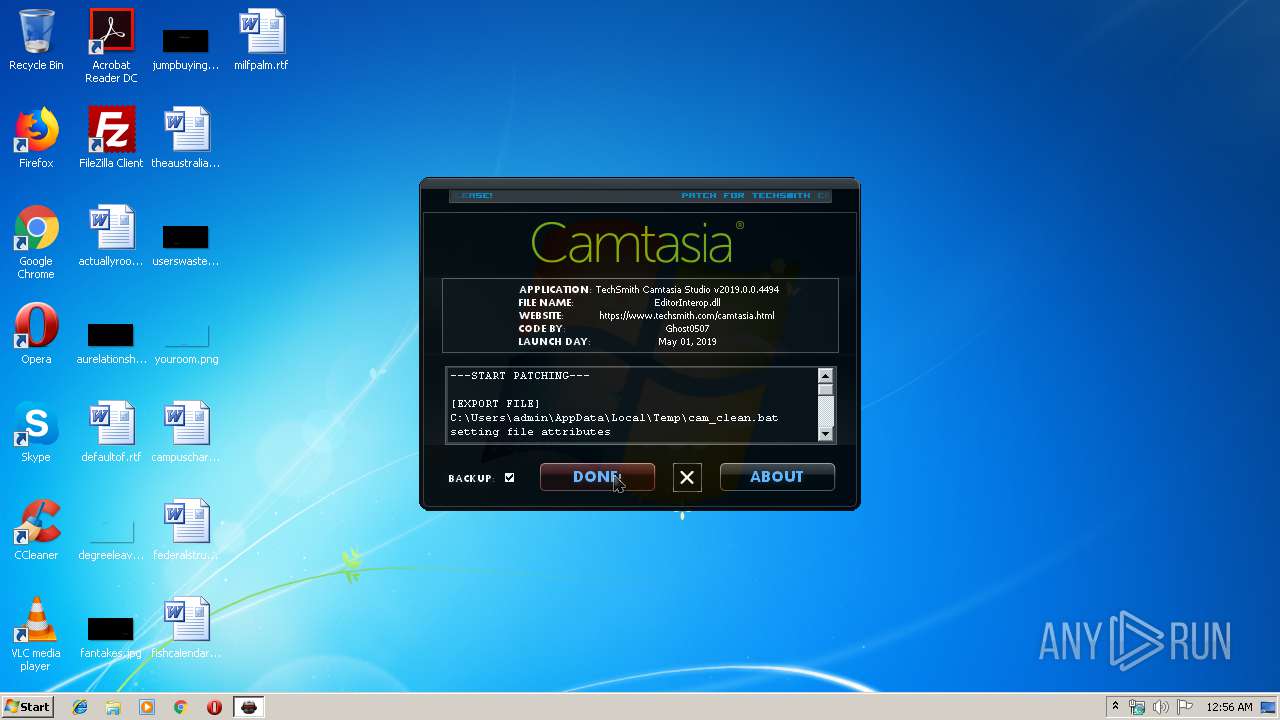
| 3028 | cmd /c "C:\Users\admin\AppData\Local\Temp\cam_clean.bat" | C:\Windows\system32\cmd.exe | — | techsmith.camtasia.studio.v2019.0.0.4494.patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
27
Read events
27
Write events
0
Delete events
0
Modification events
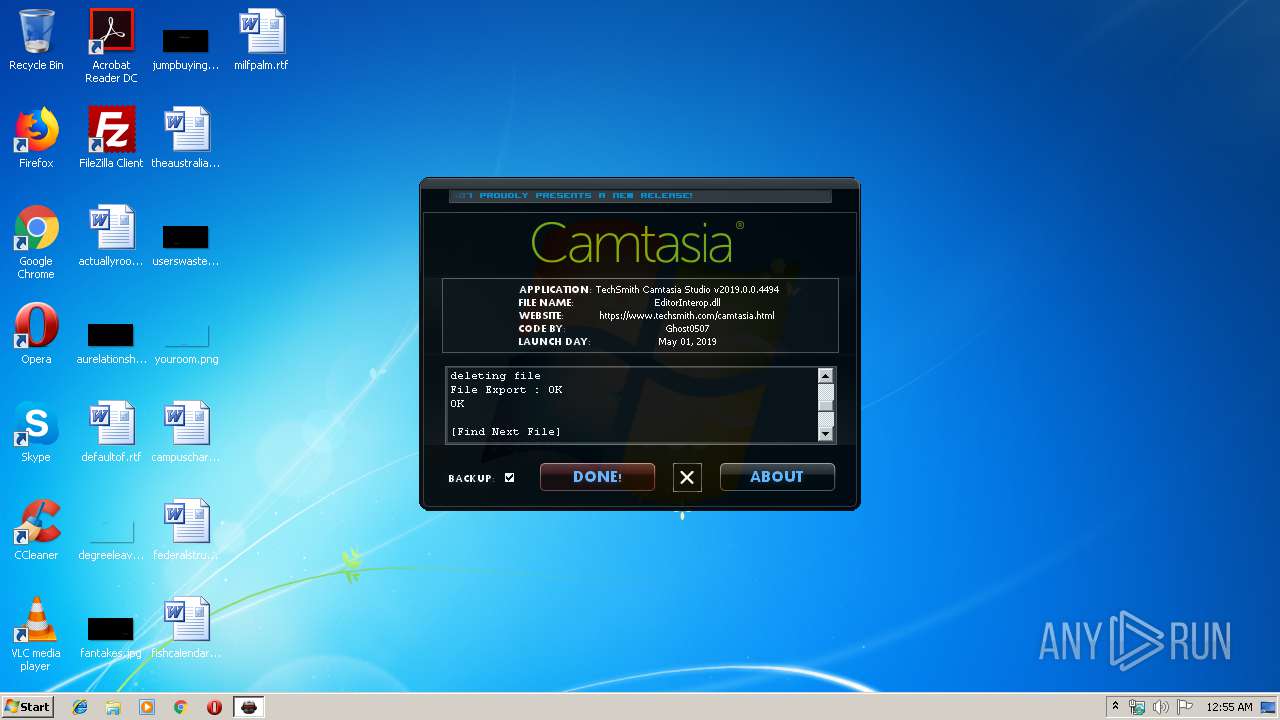
Executable files
5
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2960 | techsmith.camtasia.studio.v2019.0.0.4494.patch.exe | C:\Users\admin\AppData\Local\Temp\64F4EA4C8142CAC73E06647D59A699D1.dll | executable | |
MD5:14DD1F05C6BD3CE4ACAB3EBDB9F0903B | SHA256:9A9296A1CC6C243E166B301346C4CD9DEC45028BBC80FDE3903B6C3740C6A239 | |||
| 2960 | techsmith.camtasia.studio.v2019.0.0.4494.patch.exe | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
| 2960 | techsmith.camtasia.studio.v2019.0.0.4494.patch.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:70A3AA7FABEC7CC57DA47664A588EEB8 | SHA256:399B5B2E2F9D90BF193A434ECA2FA5B86D21E0CFA43AFA9885330030DF267E99 | |||
| 2960 | techsmith.camtasia.studio.v2019.0.0.4494.patch.exe | C:\Users\admin\AppData\Local\Temp\cam_clean.bat | text | |
MD5:7D452D12E9FB697265B9B7C705DC1FD9 | SHA256:76DF1B1BB44FAD06A706894351740962FC94A7AC8536A635DE87F1E522583CC1 | |||
| 2960 | techsmith.camtasia.studio.v2019.0.0.4494.patch.exe | C:\Users\admin\AppData\Local\Temp\Visitor -BRK-.FON | executable | |
MD5:91C8190CC9ADDCE1C97D99A5DD1EB58D | SHA256:6DF64B87A81293201AABF6B1C1B29958BDE38CEDF74966A075BC018C985AEF37 | |||
| 2960 | techsmith.camtasia.studio.v2019.0.0.4494.patch.exe | C:\Users\admin\AppData\Local\Temp\C5E3399ED9A072FE864748D49BA96094.dll | executable | |
MD5:13249BC6AA781475CDE4A1C90F95EFD4 | SHA256:3922A8C1B0F58B74FC3D89D7EEC3FE5C5B0E8BDA6B36491D2380431DD8E8284A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report