analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
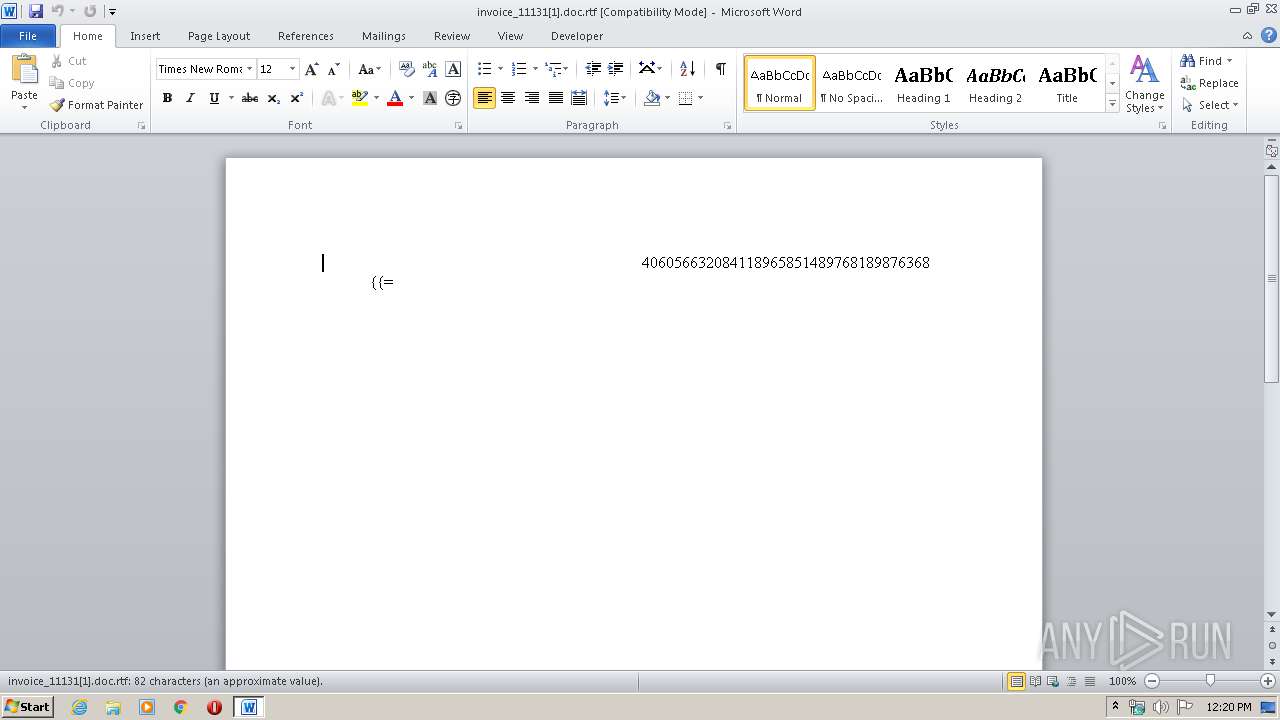
| File name: | invoice_11131[1].doc |
| Full analysis: | https://app.any.run/tasks/e829af3e-1375-4113-bbba-499153471faa |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 12:19:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, unknown version |
| MD5: | 4AD2FD14FBEA7C39DD4204FCDF70D183 |
| SHA1: | 752A04422193DA0CFFEF311DD24A1726F2FD5067 |
| SHA256: | 0B06759DA08B10F24DB27F939AC1C3FEF9C3575E59A71BD81321858566BD7D60 |
| SSDEEP: | 1536:yLMXdYTqSBprB4+YdTLJlyDM+RATwA8Pu+OgguDuntC+4ZhU7WrbydwhkQsZPrCX:raB4Cm49tZprO/aEoPCeSzXwWC |
MALICIOUS
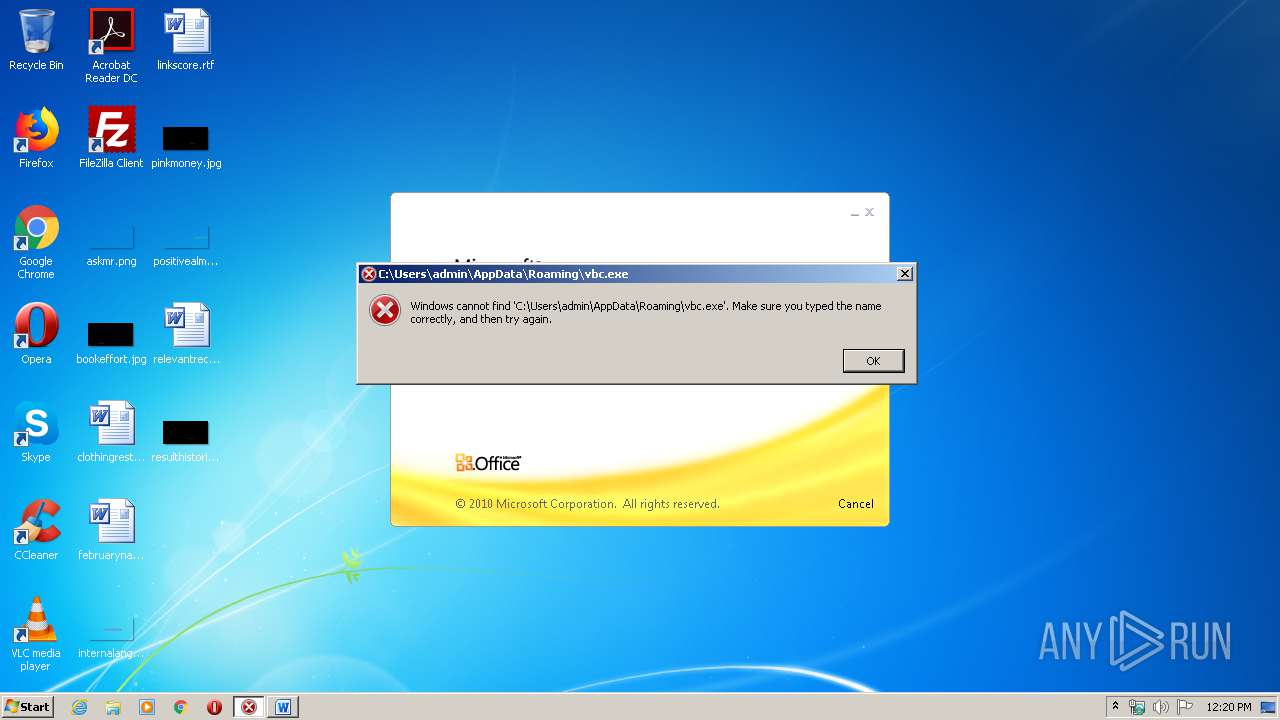
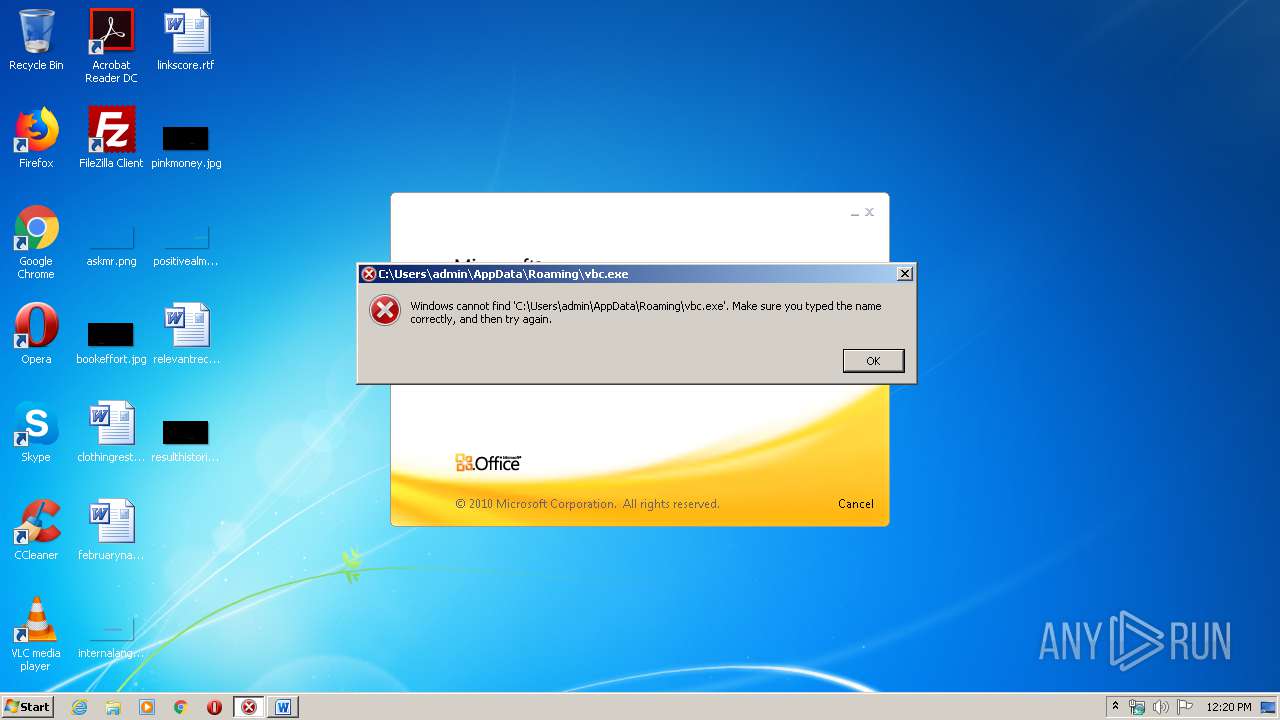
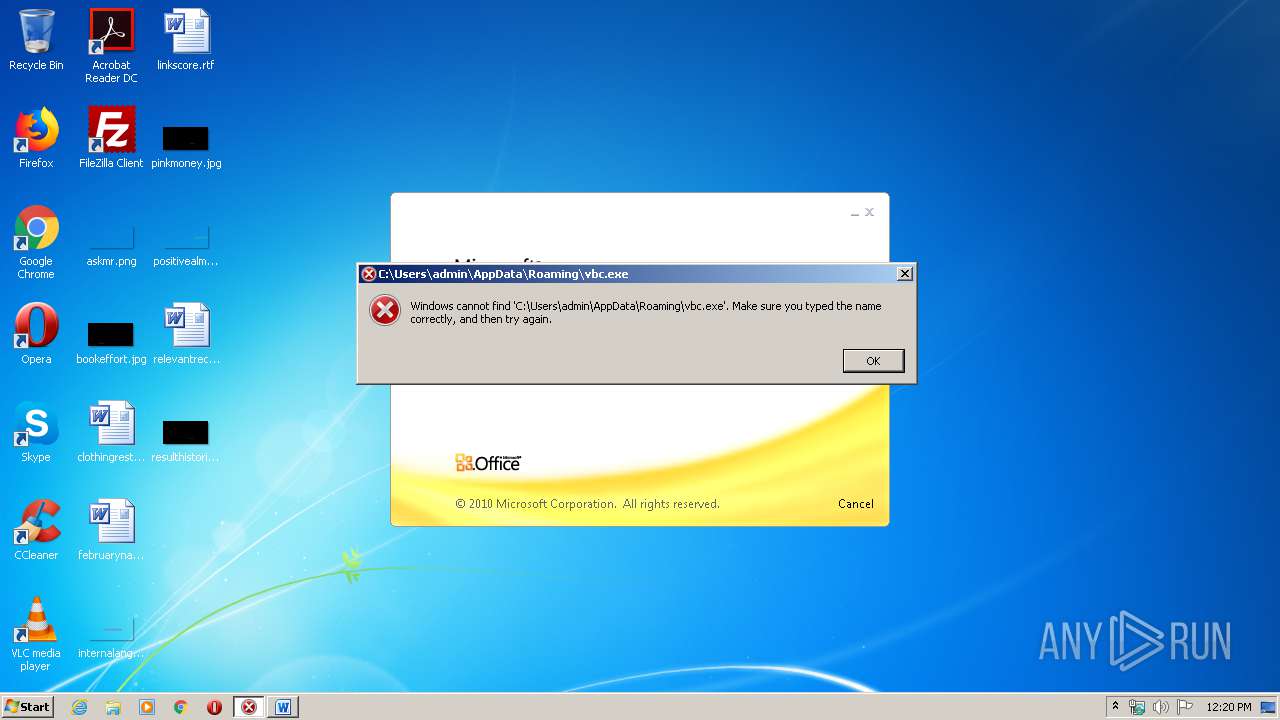
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 2968)
SUSPICIOUS
Reads Internet Cache Settings
- EQNEDT32.EXE (PID: 2968)
Executed via COM
- EQNEDT32.EXE (PID: 2968)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2872)
Creates files in the user directory
- WINWORD.EXE (PID: 2872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2872 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\invoice_11131[1].doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 | ||||
| 2968 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | |
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 | ||||
Total events
1 673
Read events
977
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5D6A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2872 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2872 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRL0001.tmp | text | |
MD5:3E0165040FD1841D4F22F56683C5FBAF | SHA256:E1E923CB92E8790B75D0583B248B742A896FB2E9261891434E9A8972EA62CA9B | |||
| 2872 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:2672B613CBF08CF3A38F3E7109100FC3 | SHA256:1A1402DF8C33B8149EB4FC581287D0A429EB5A85787BBE5BCC0EADAD67BB0E13 | |||
| 2872 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\invoice_11131[1].doc.rtf | text | |
MD5:3E0165040FD1841D4F22F56683C5FBAF | SHA256:E1E923CB92E8790B75D0583B248B742A896FB2E9261891434E9A8972EA62CA9B | |||
| 2872 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$voice_11131[1].doc.rtf | pgc | |
MD5:8C66806A9F2A9C8F1DD1788C43310F61 | SHA256:4C803C965E614CCC3F03C2839FBCF1EA17DCB28FE3A04EDCCBF04BAE40B95EC5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2968 | EQNEDT32.EXE | GET | — | 192.169.69.25:80 | http://kung2globalinvestmentwsdygoogledngaddres.duckdns.org/kungdoc/winlog.exe | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | EQNEDT32.EXE | 192.169.69.25:80 | kung2globalinvestmentwsdygoogledngaddres.duckdns.org | Wowrack.com | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kung2globalinvestmentwsdygoogledngaddres.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2968 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS SUSPICIOUS winlog.exe in URI Probable Process Dump/Trojan Download |