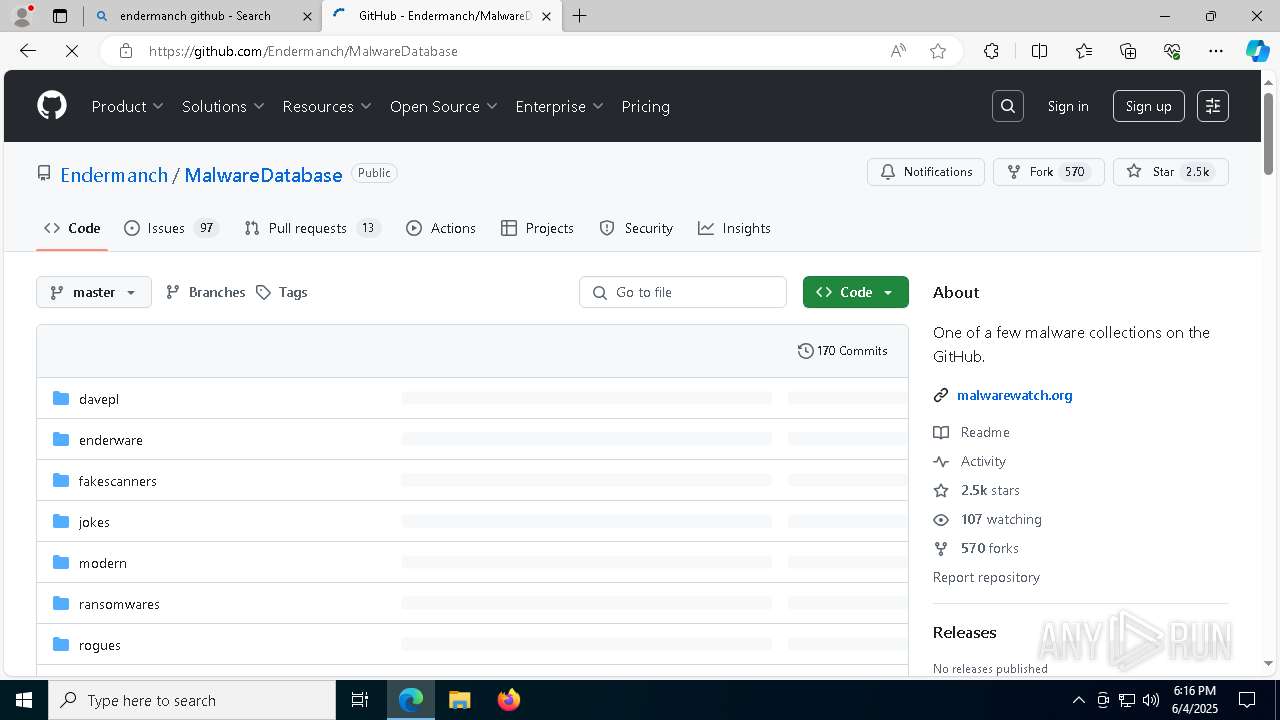
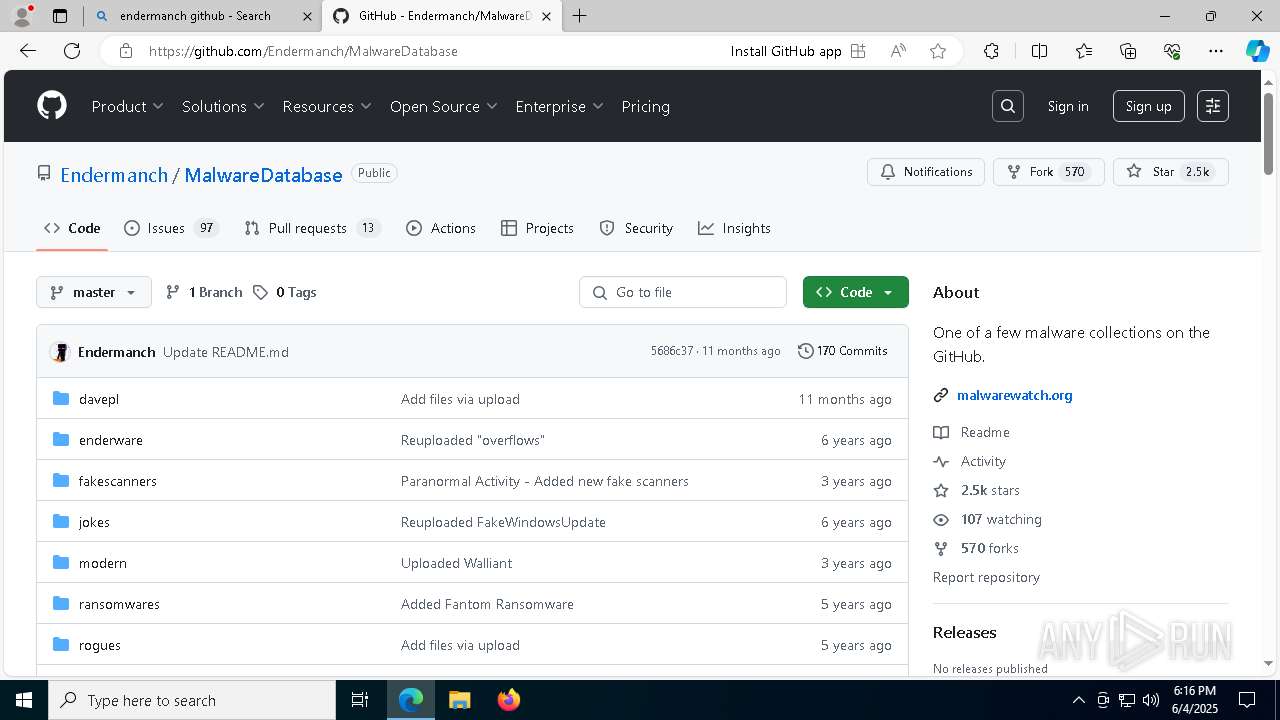
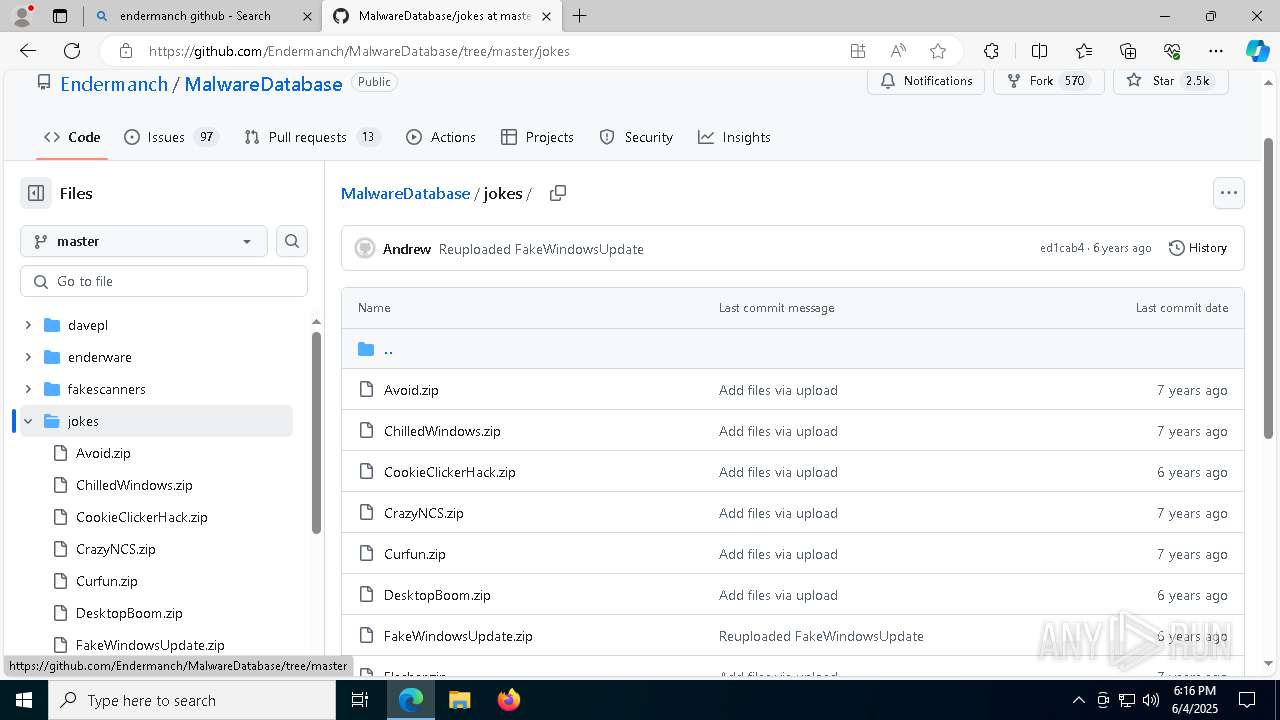
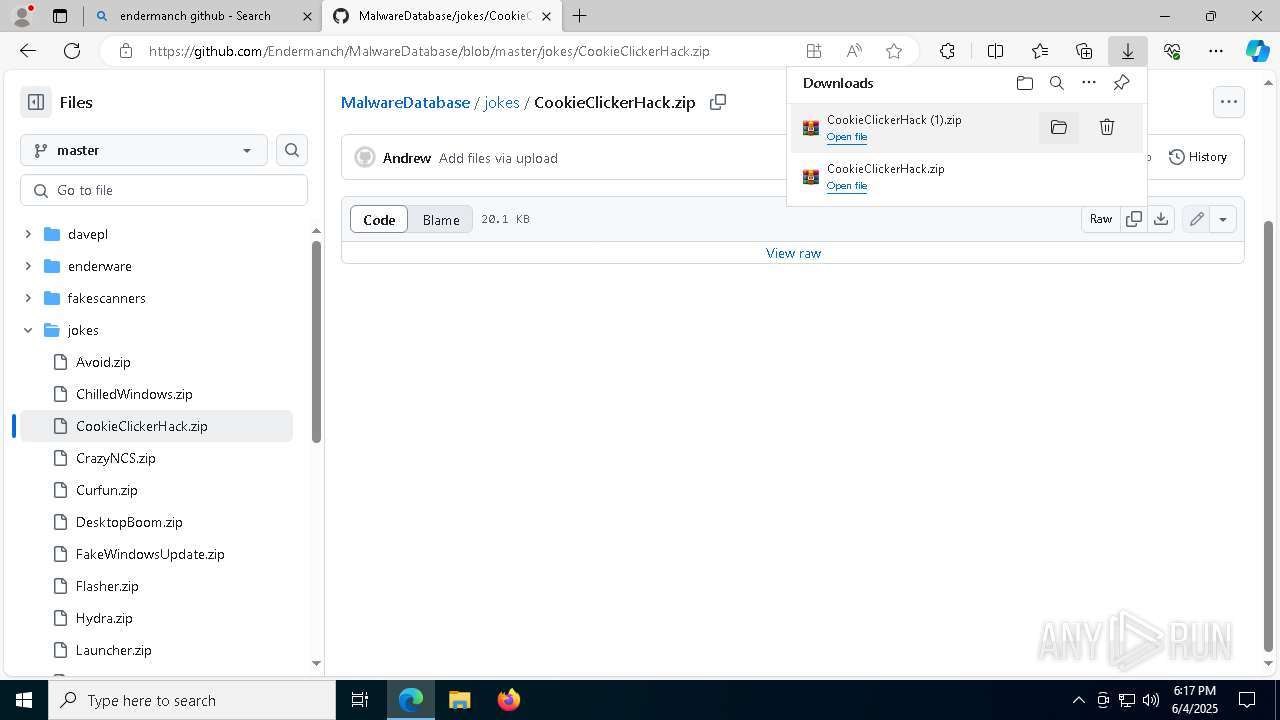
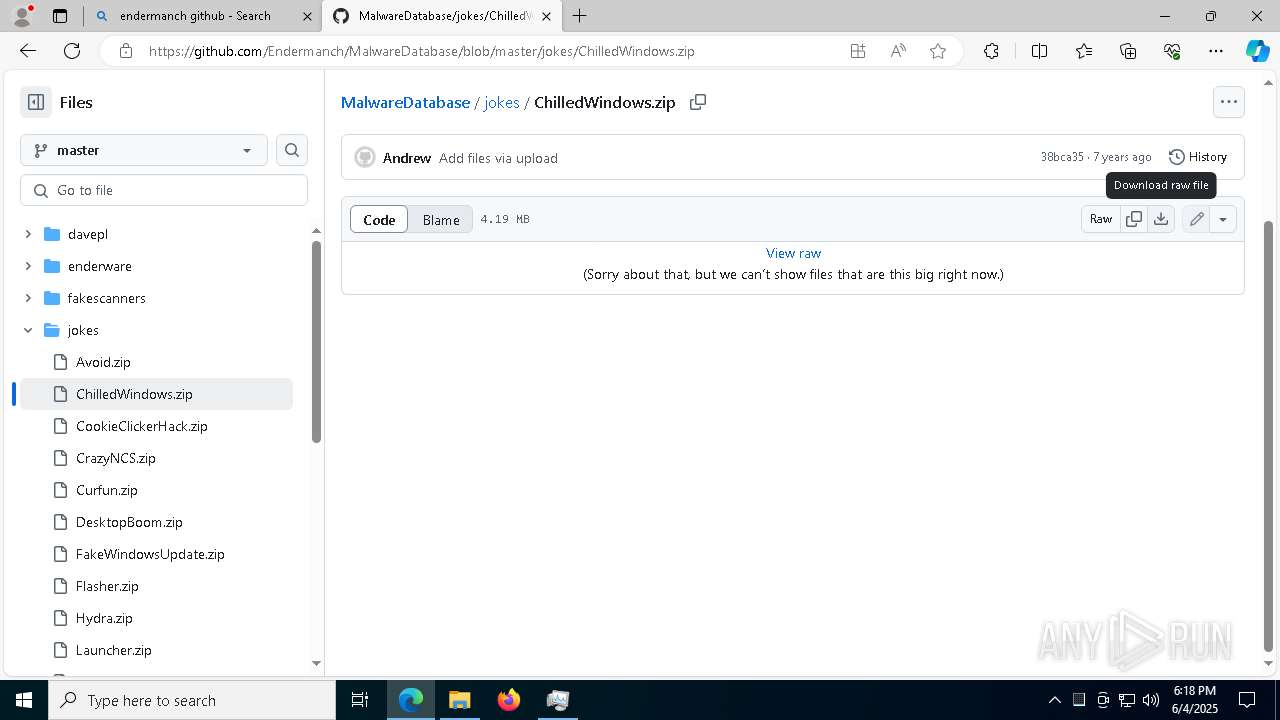
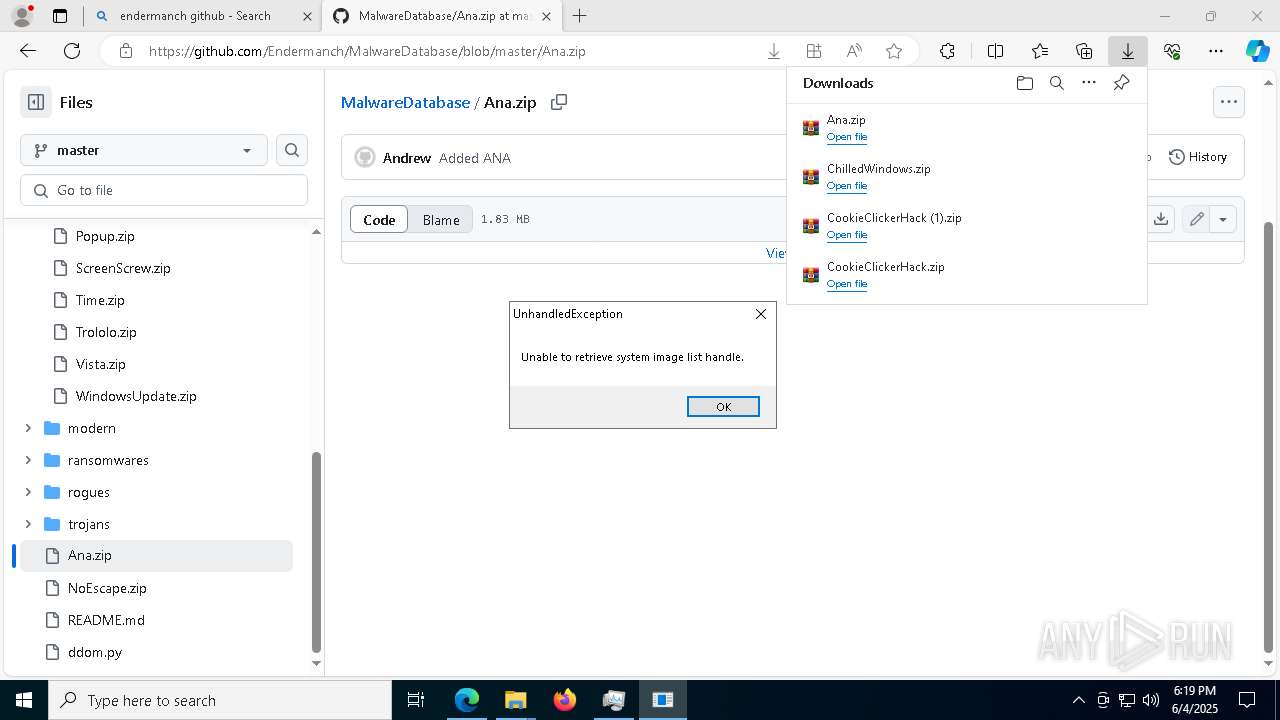
| URL: | https://www.bing.com/search?q=endermanch+github&pc=GD06&form=GDNSBR&ptag=29437 |
| Full analysis: | https://app.any.run/tasks/0de3d4d8-dc9b-4156-bc56-1c281e222fbd |
| Verdict: | Malicious activity |
| Analysis date: | June 04, 2025, 18:16:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B1DA12C7F9107540CC2B0679B124EB52 |
| SHA1: | B943B77931A53E8BDC1112F2192E2B62356CBF96 |
| SHA256: | 0AF9E99300C4DFFF8E1ABD4260985FDC7C63F9861285947F266000C0F4034CA1 |
| SSDEEP: | 3:N8DSLsBAEXGpolaOjSD8h5DdZEzVhYMwS:2OLsBBGKlNwEdZc3 |
MALICIOUS
PONMOCUP has been detected (SURICATA)
- DB.EXE (PID: 1240)
Connects to the CnC server
- DB.EXE (PID: 1240)
SUSPICIOUS
Hides command output
- cmd.exe (PID: 1052)
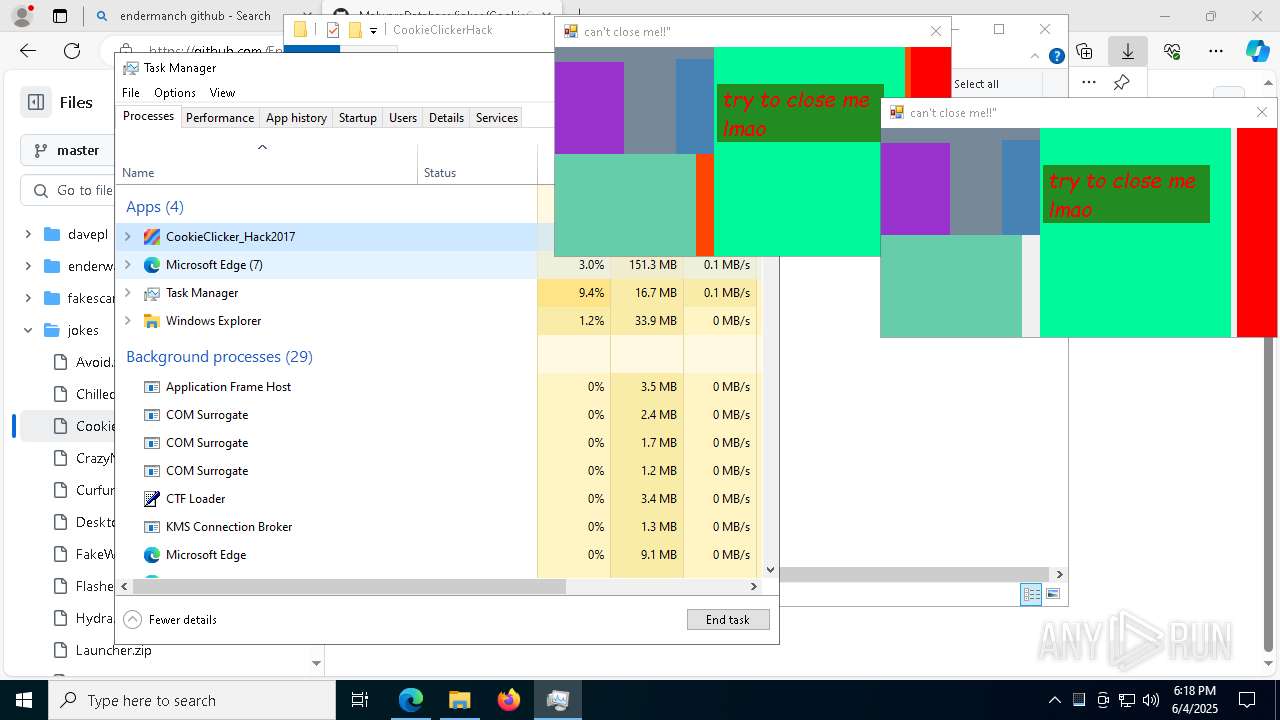
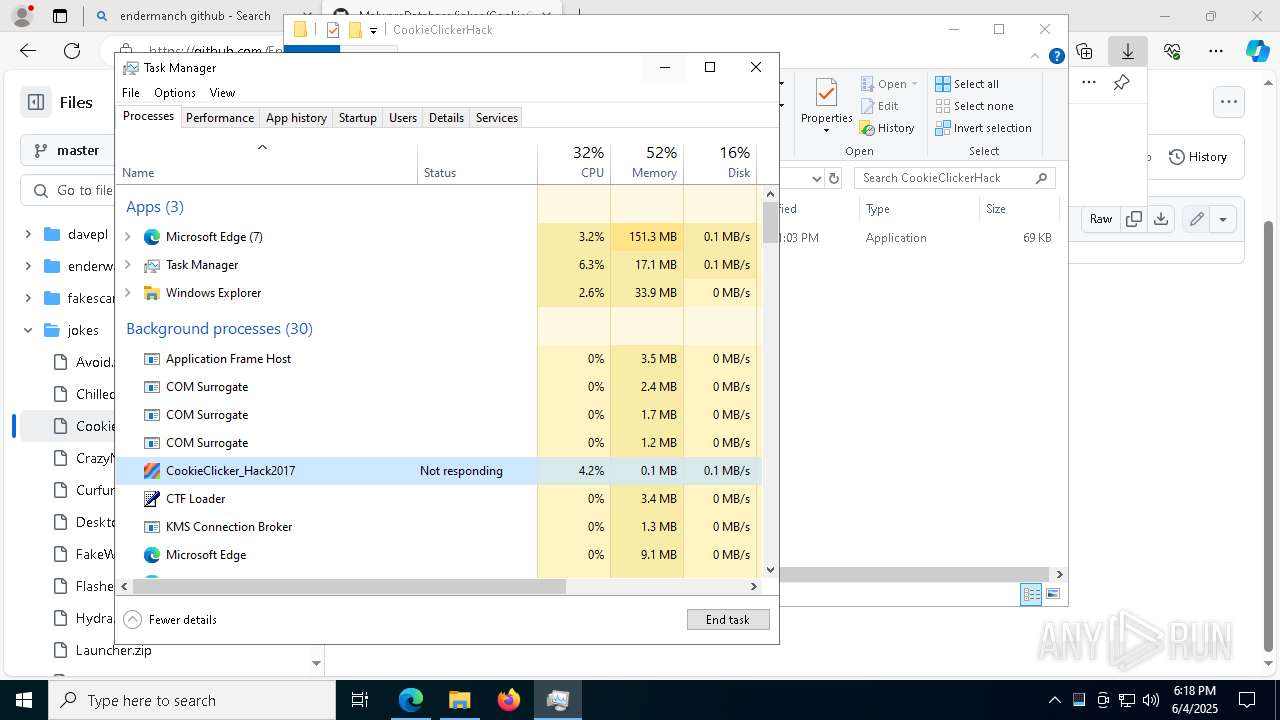
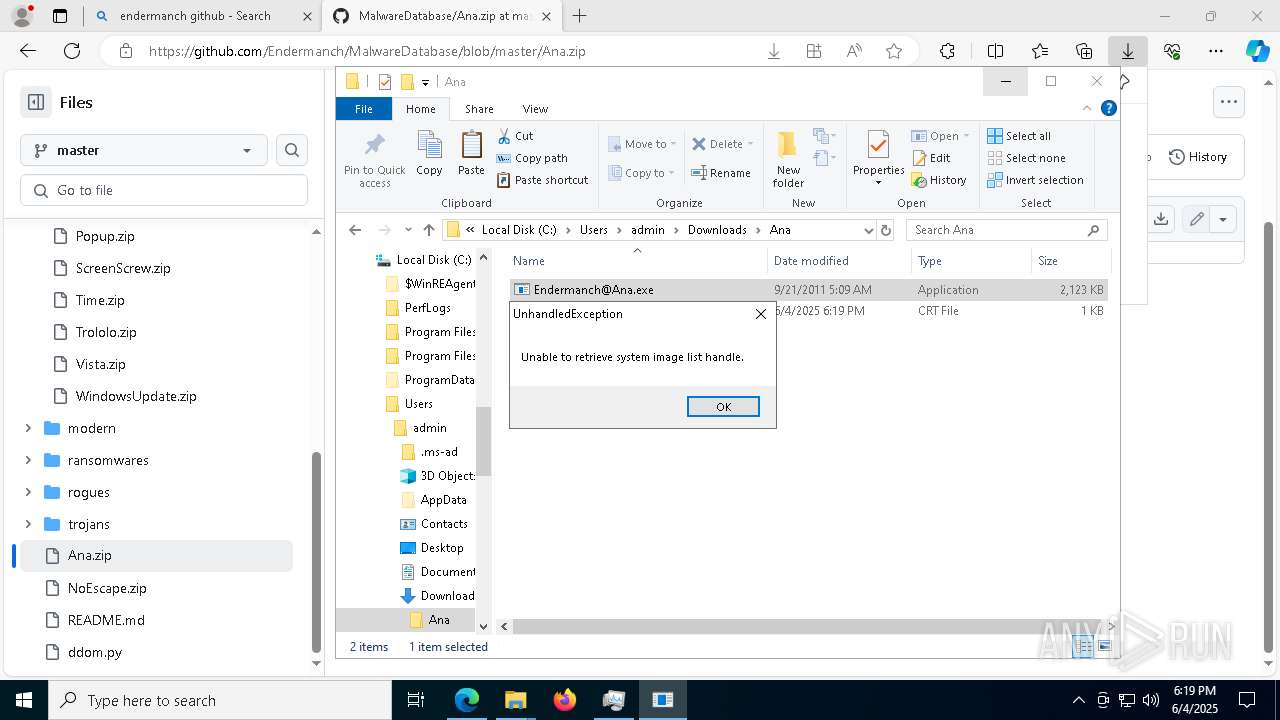
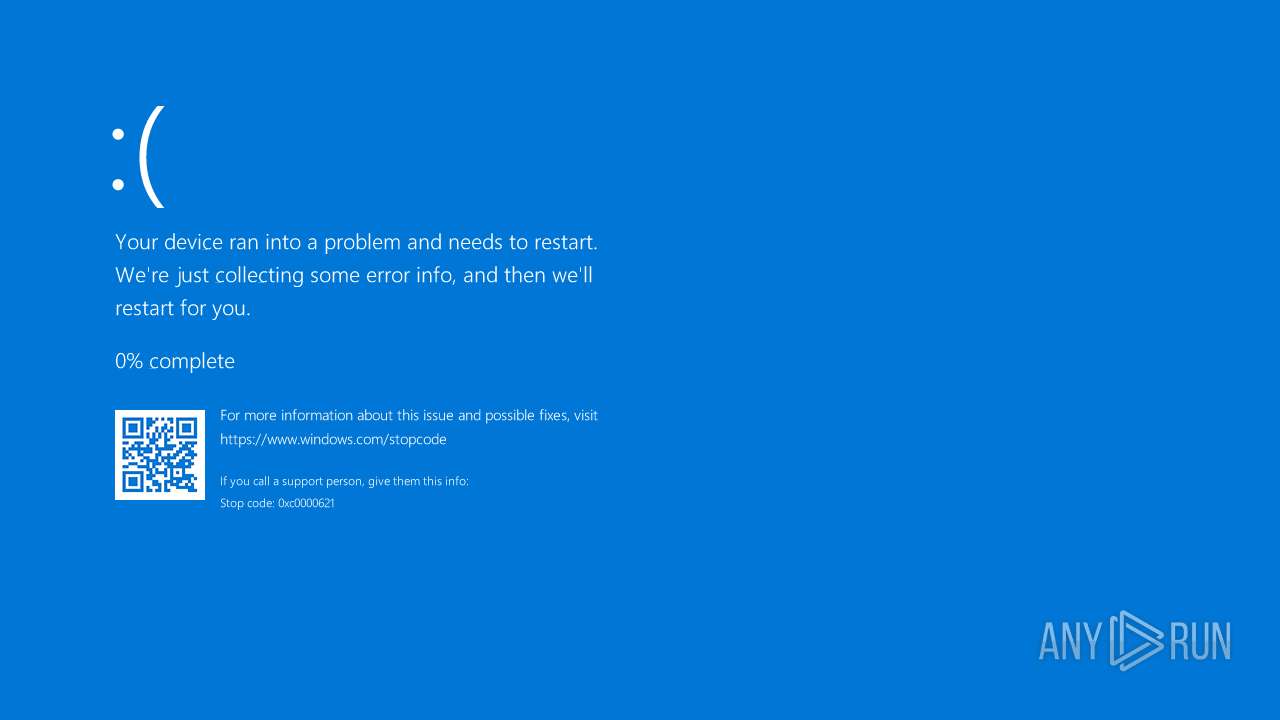
Executes application which crashes
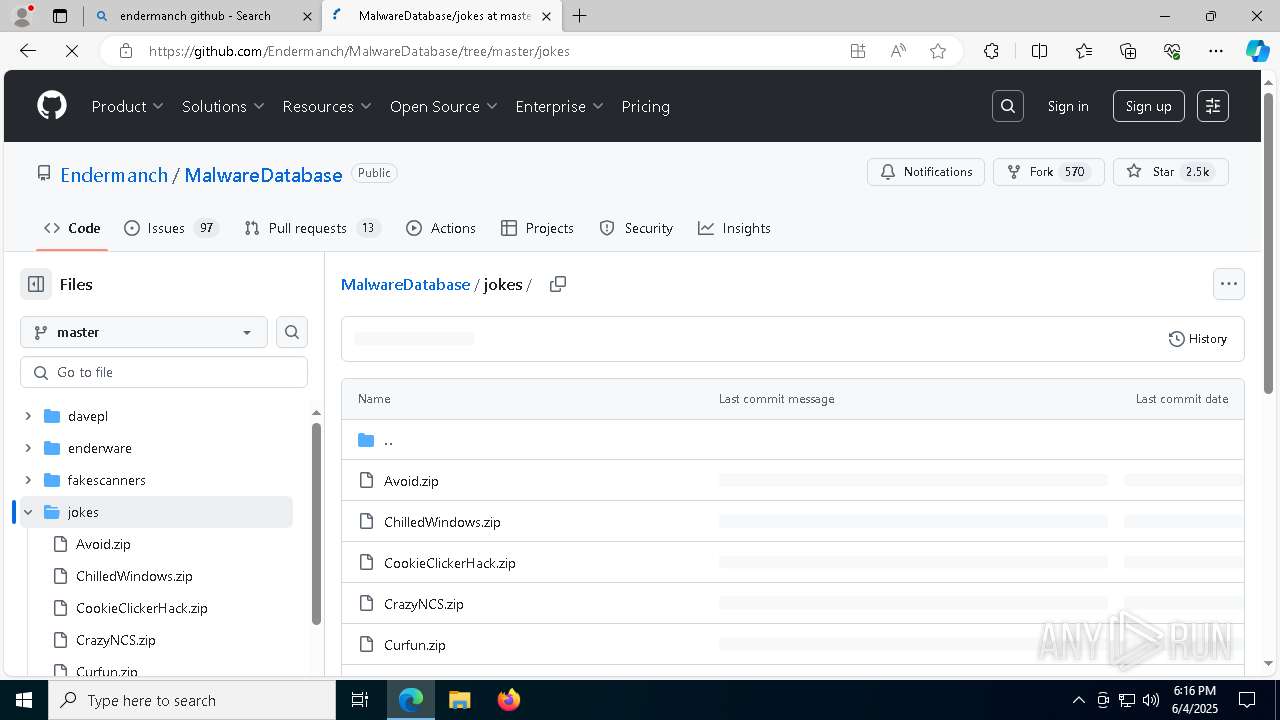
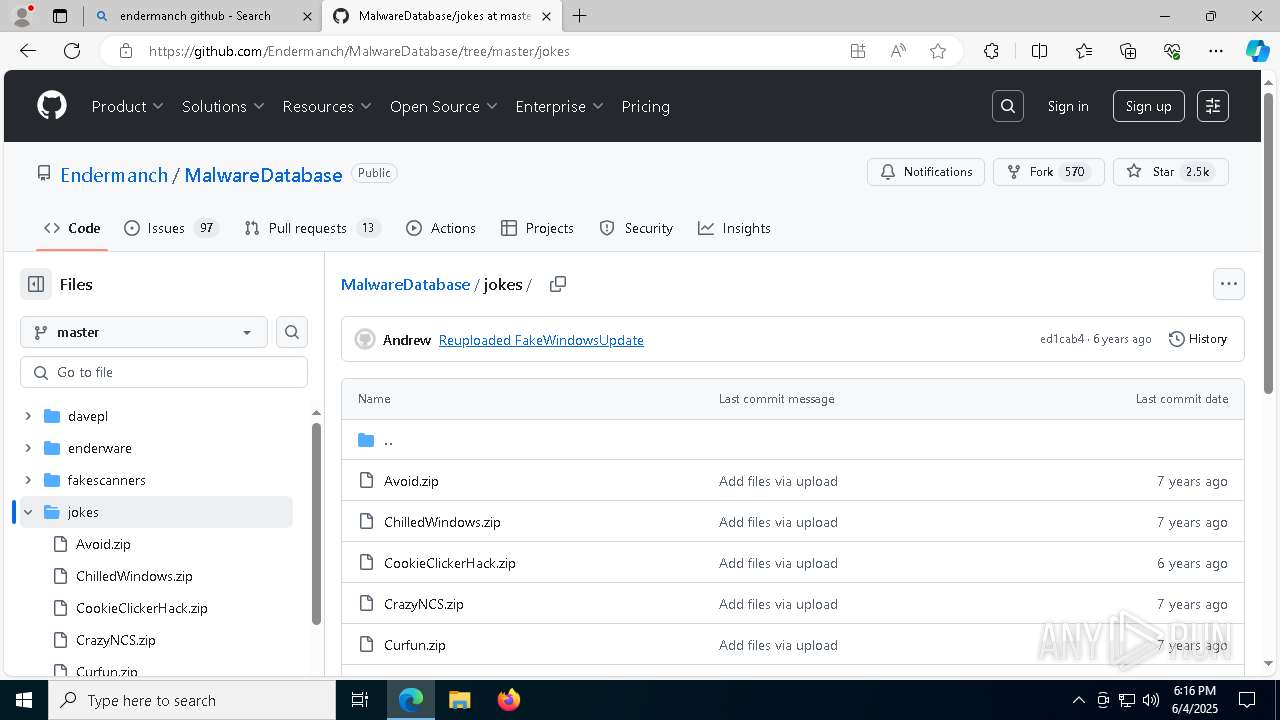
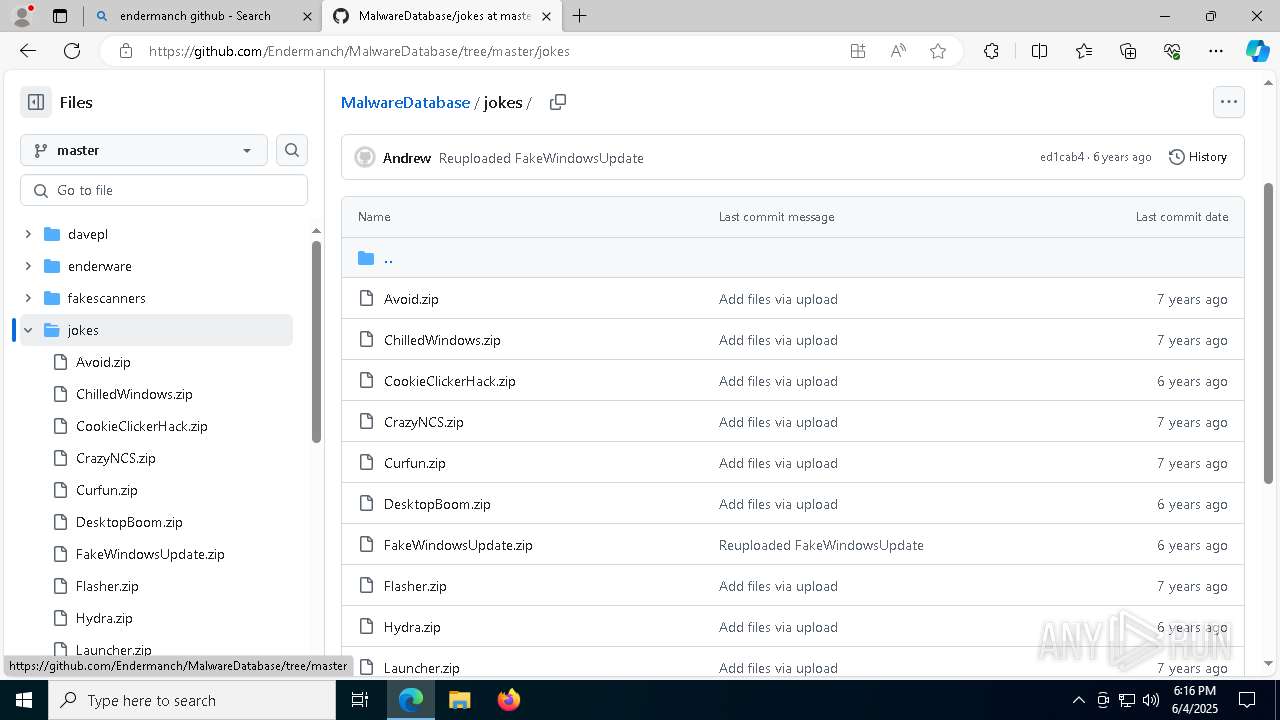
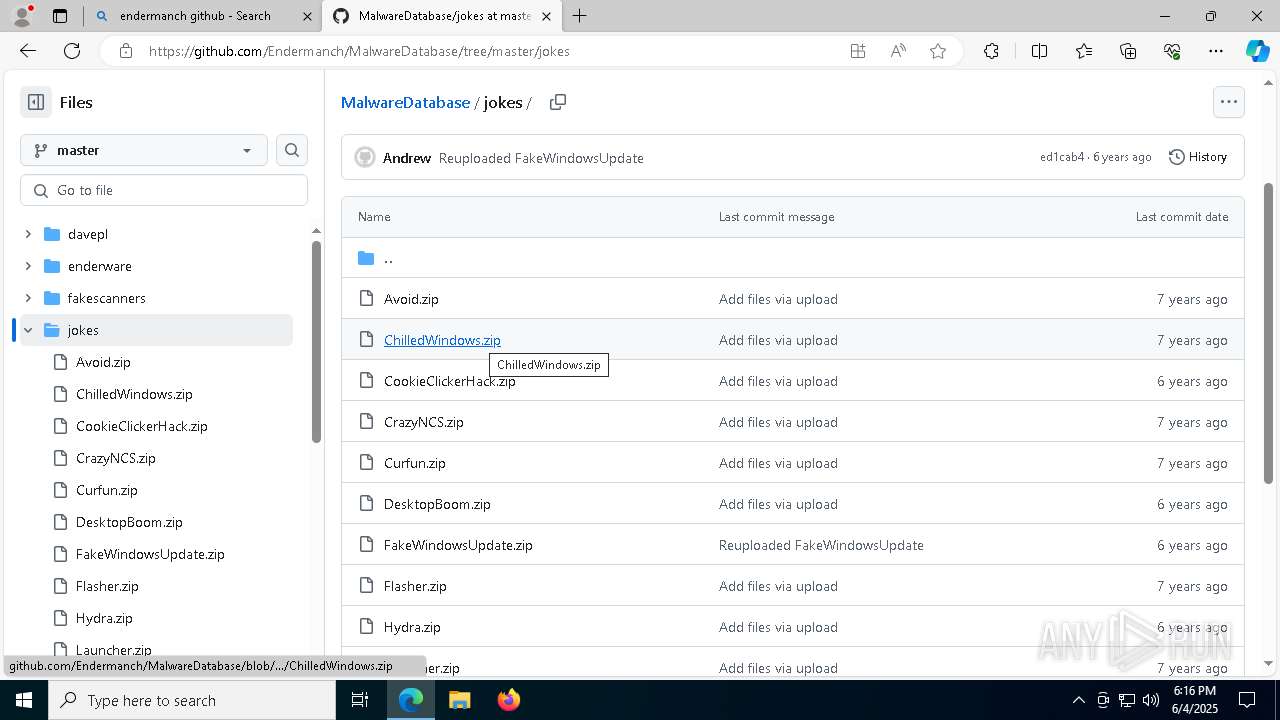
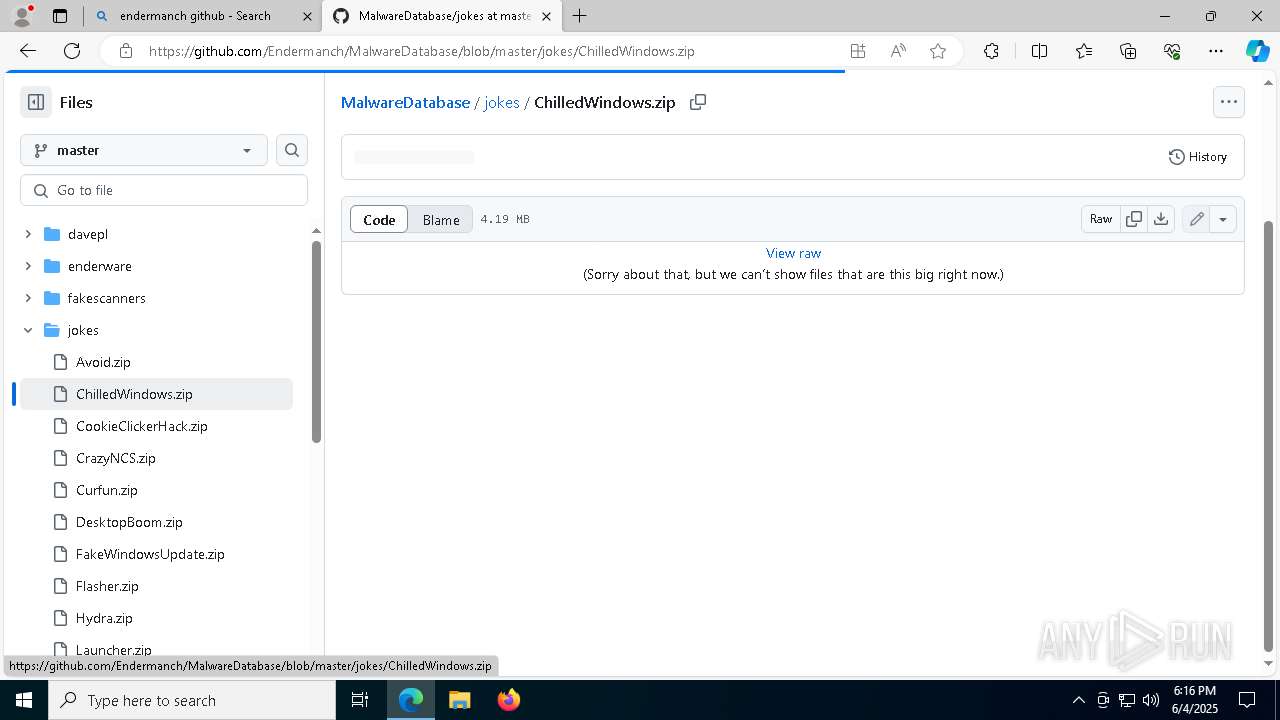
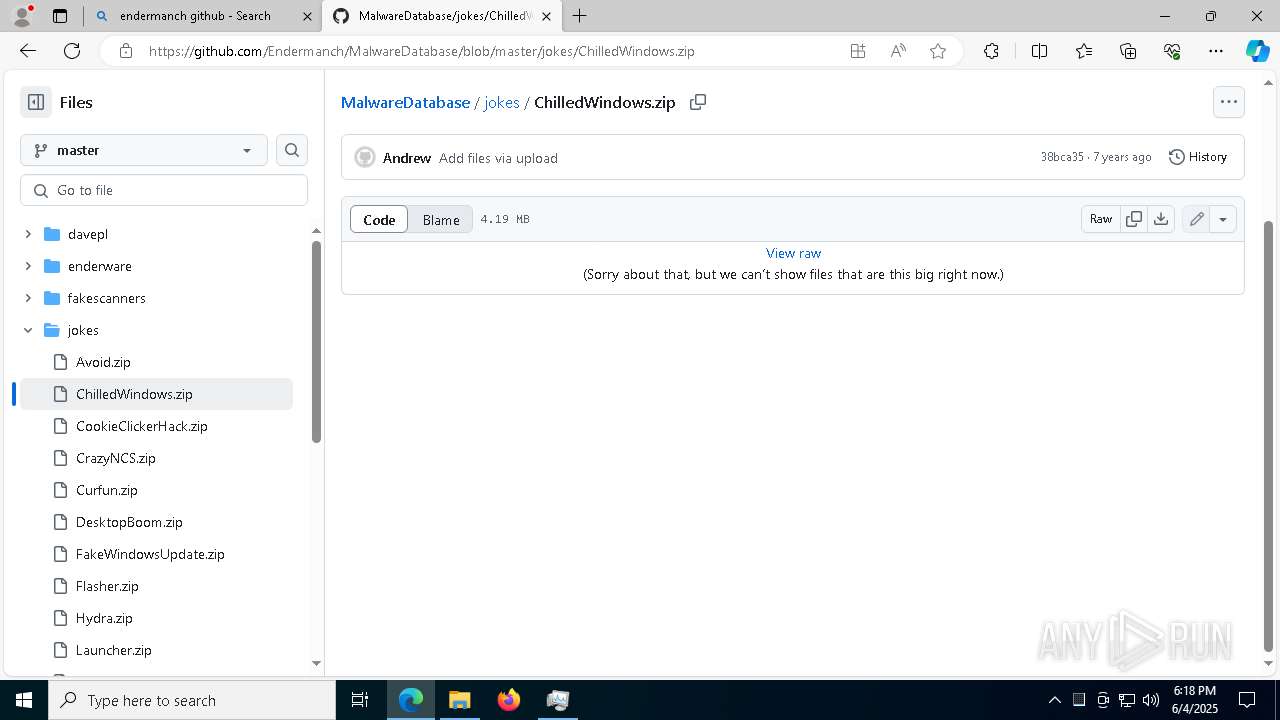
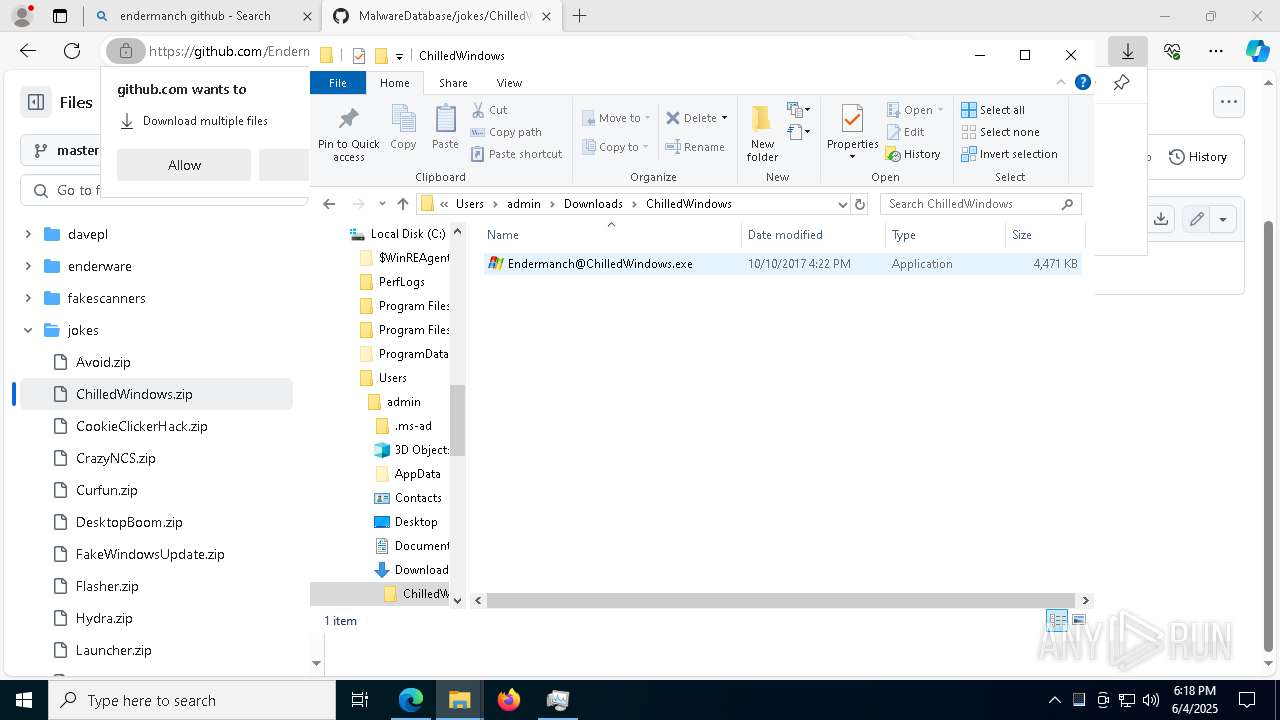
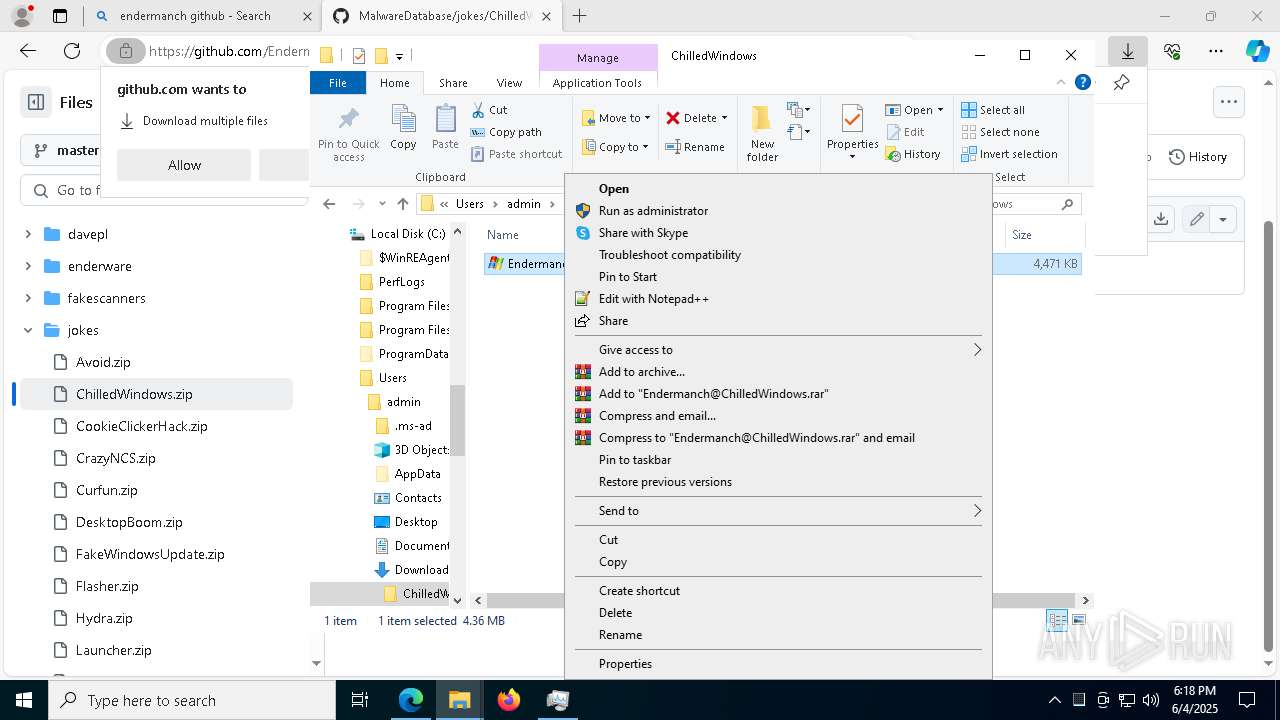
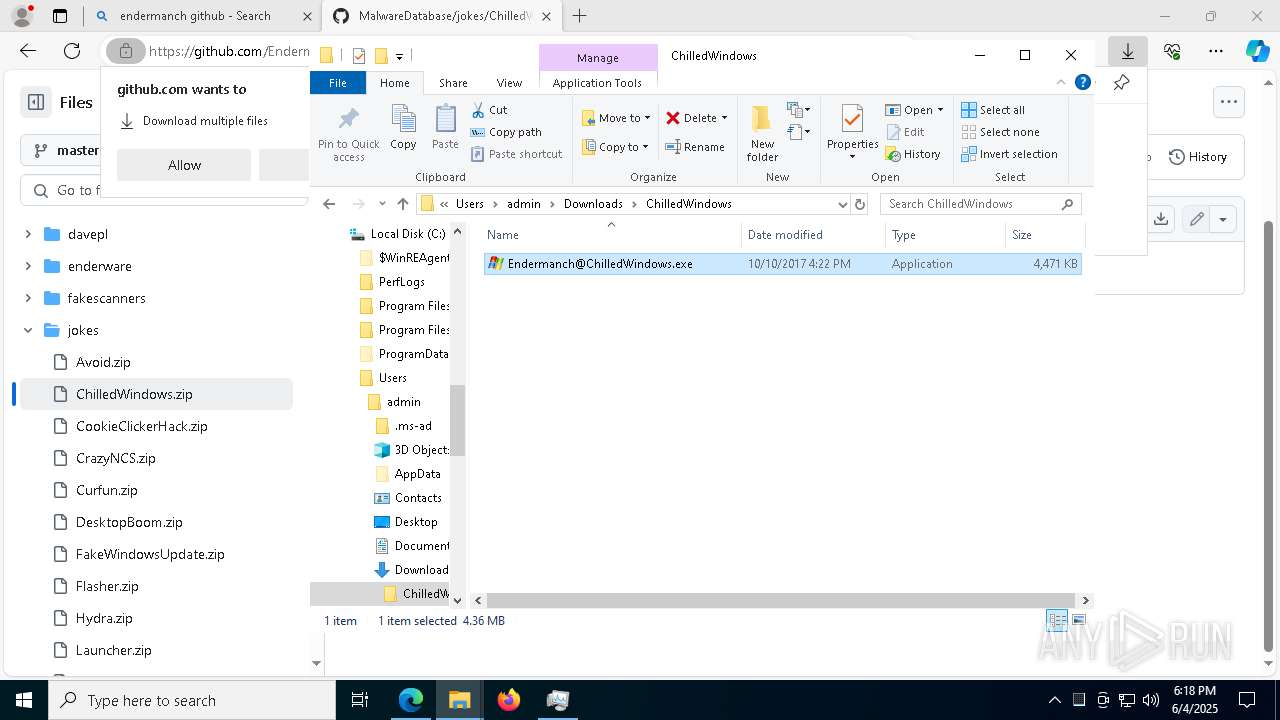
- Endermanch@ChilledWindows.exe (PID: 8064)
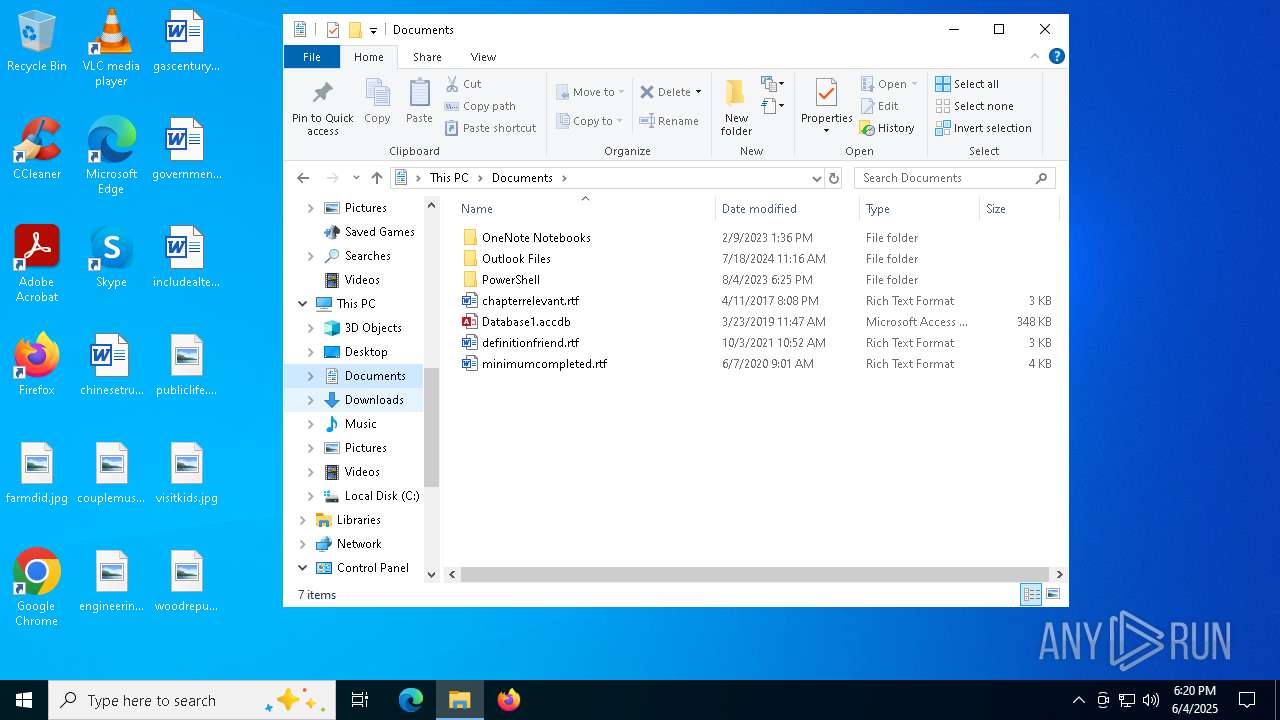
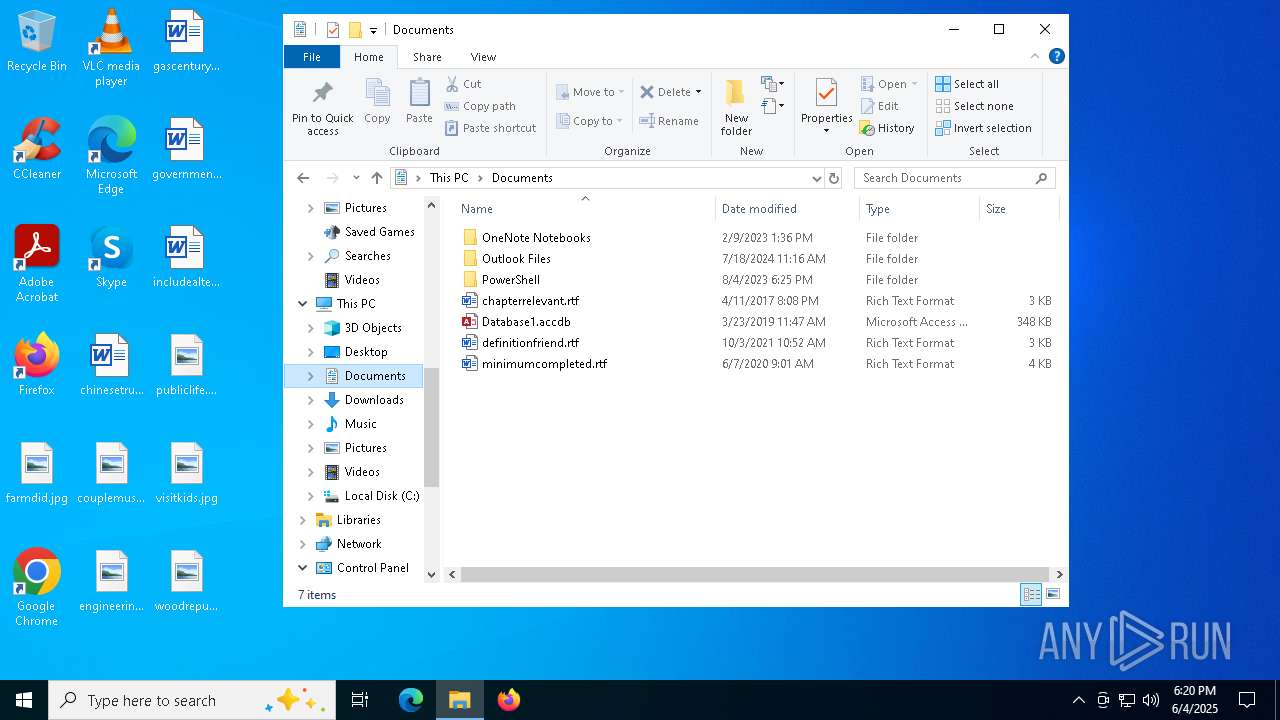
Executable content was dropped or overwritten
- DB.EXE (PID: 1240)
- Endermanch@Ana.exe (PID: 6592)
- SB.EXE (PID: 7308)
- CCleaner64.exe (PID: 6692)
- CCleaner64.exe (PID: 7088)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 780)
Application launched itself
- CCleaner64.exe (PID: 6500)
- CCleaner64.exe (PID: 6692)
Starts CMD.EXE for commands execution
- EN.EXE (PID: 7928)
- DB.EXE (PID: 1240)
Contacting a server suspected of hosting an CnC
- DB.EXE (PID: 1240)
Executing commands from a ".bat" file
- DB.EXE (PID: 1240)
Checks for external IP
- CCleaner64.exe (PID: 6692)
INFO
Application launched itself
- msedge.exe (PID: 1168)
Reads the computer name
- identity_helper.exe (PID: 7408)
Checks supported languages
- identity_helper.exe (PID: 7408)
Reads Environment values
- identity_helper.exe (PID: 7408)
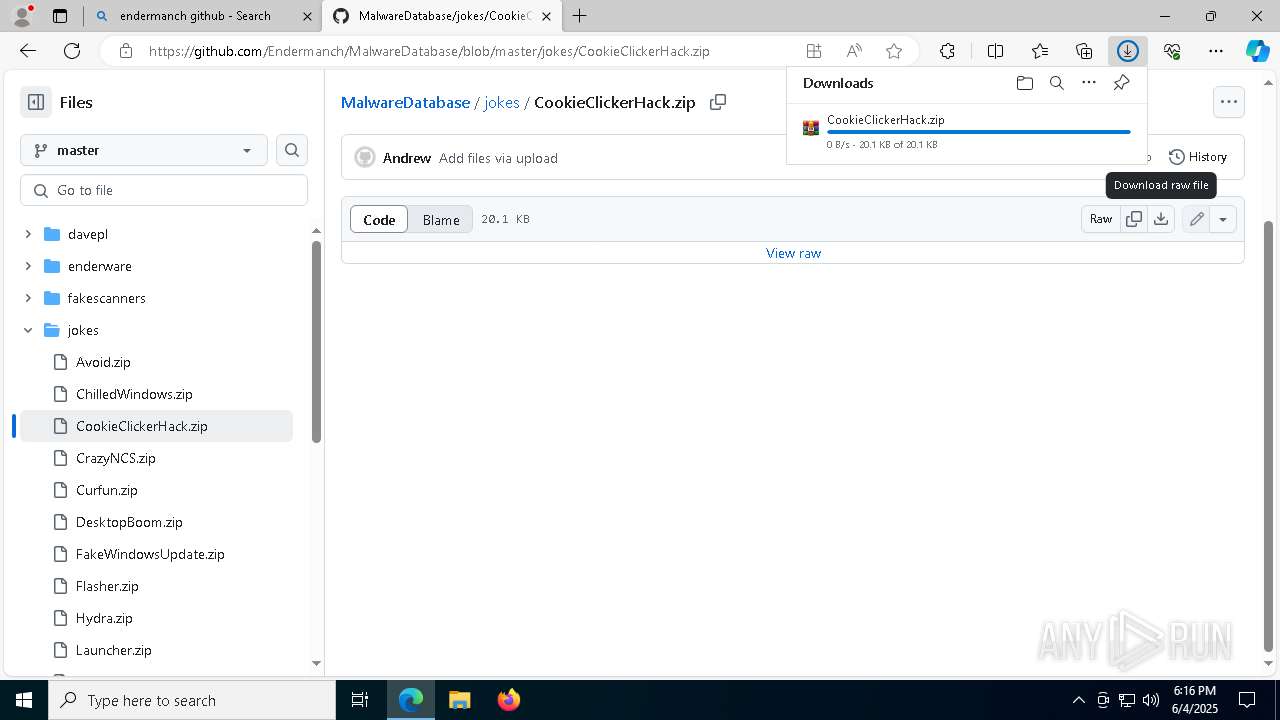
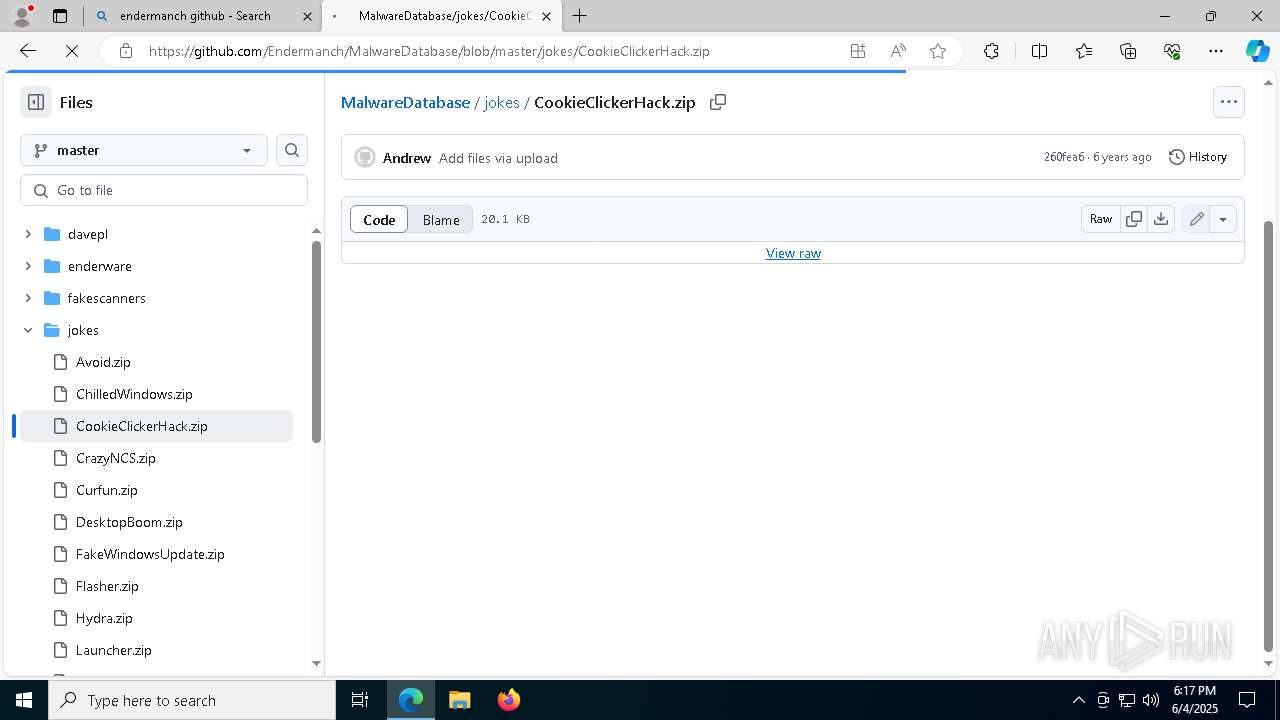
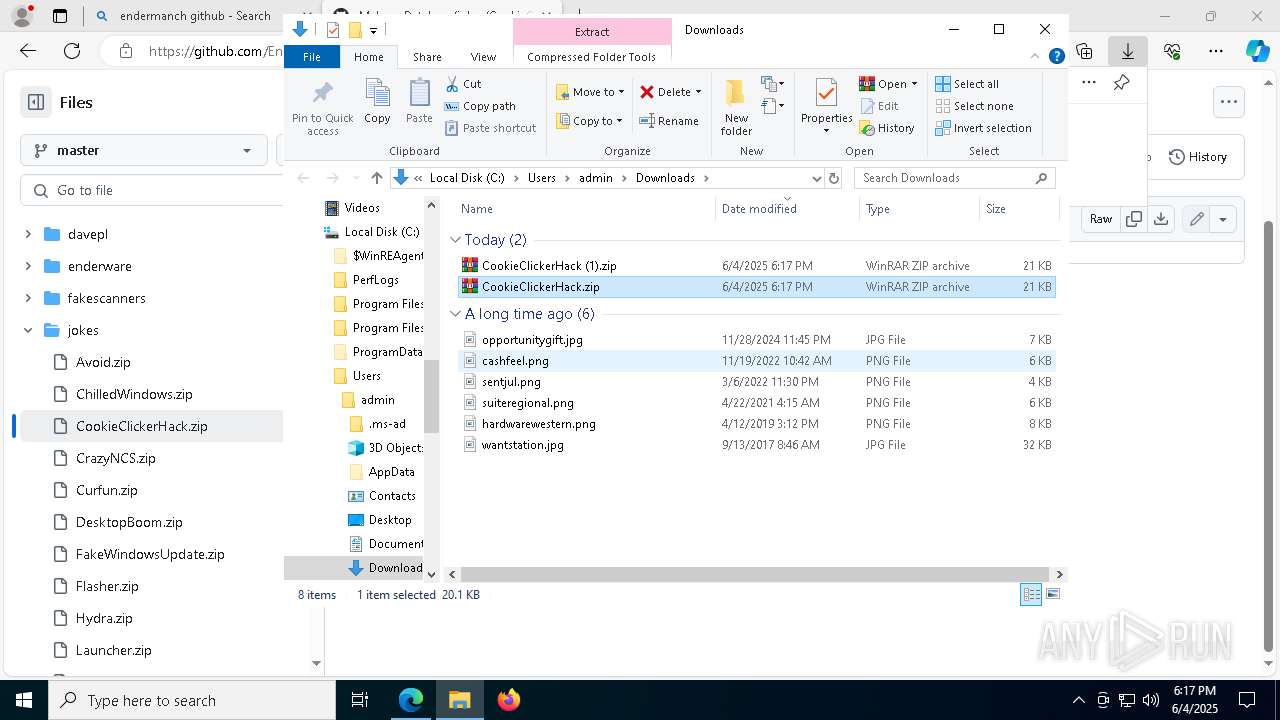
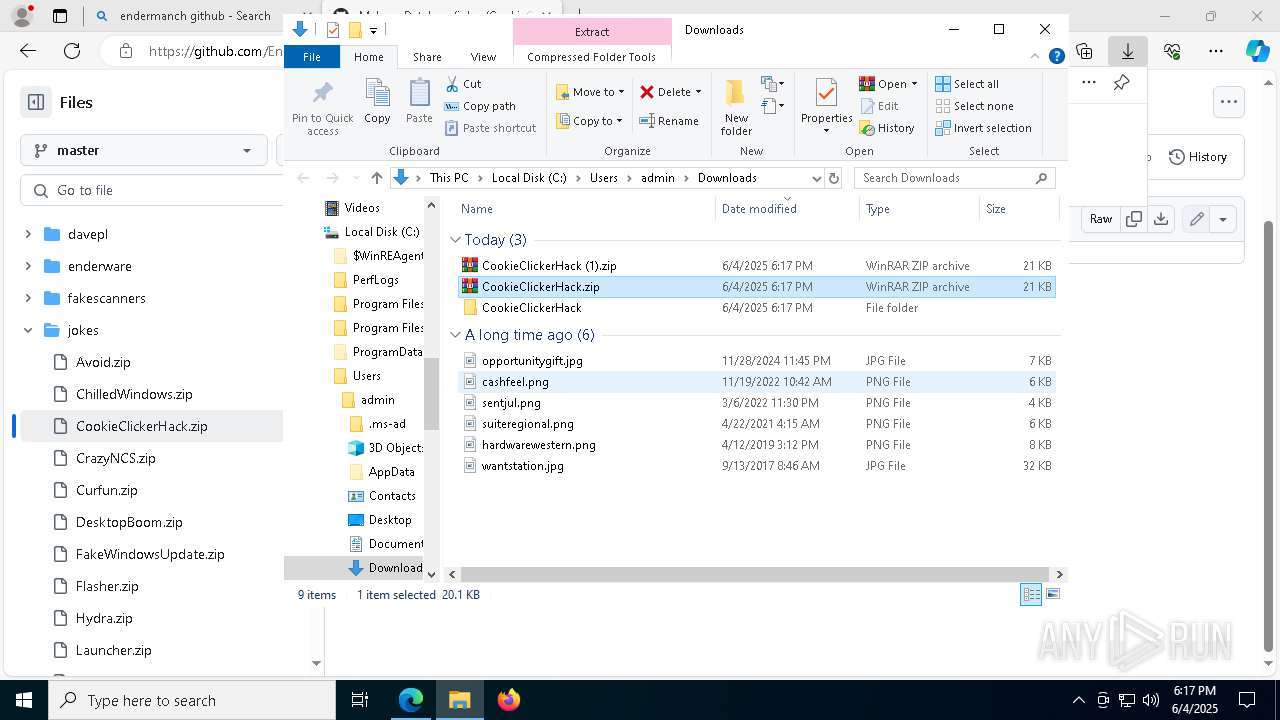
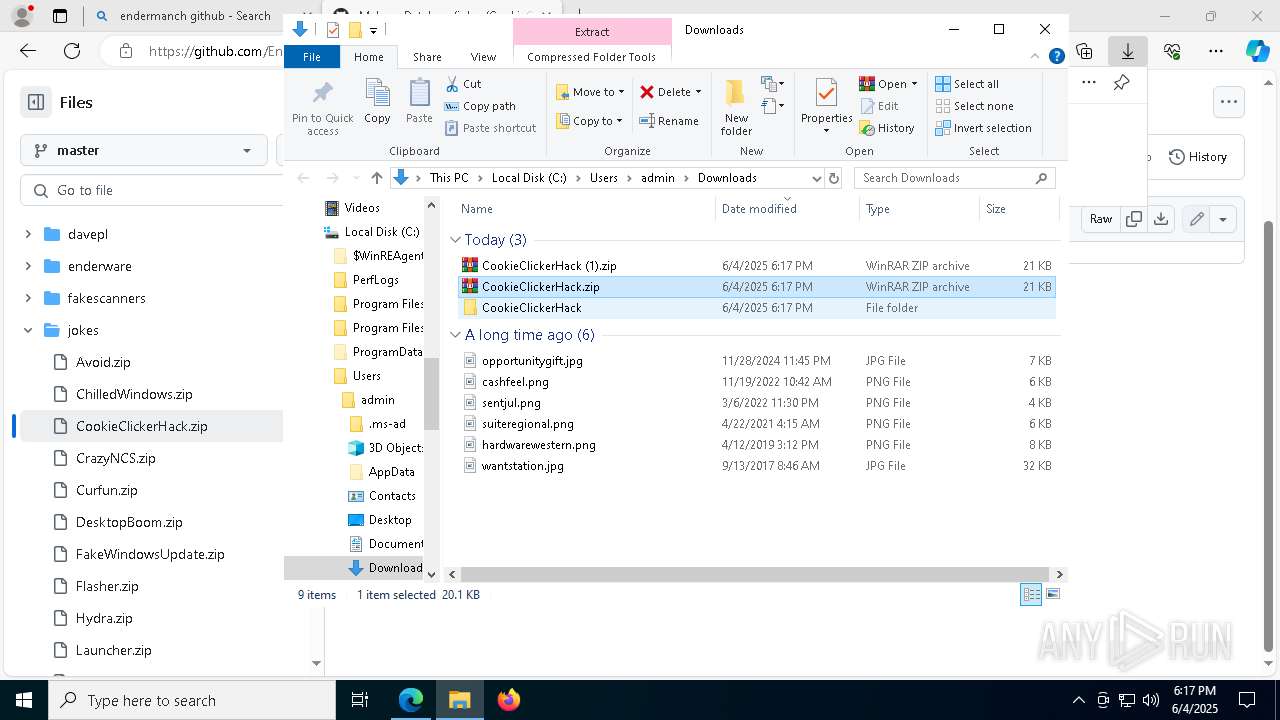
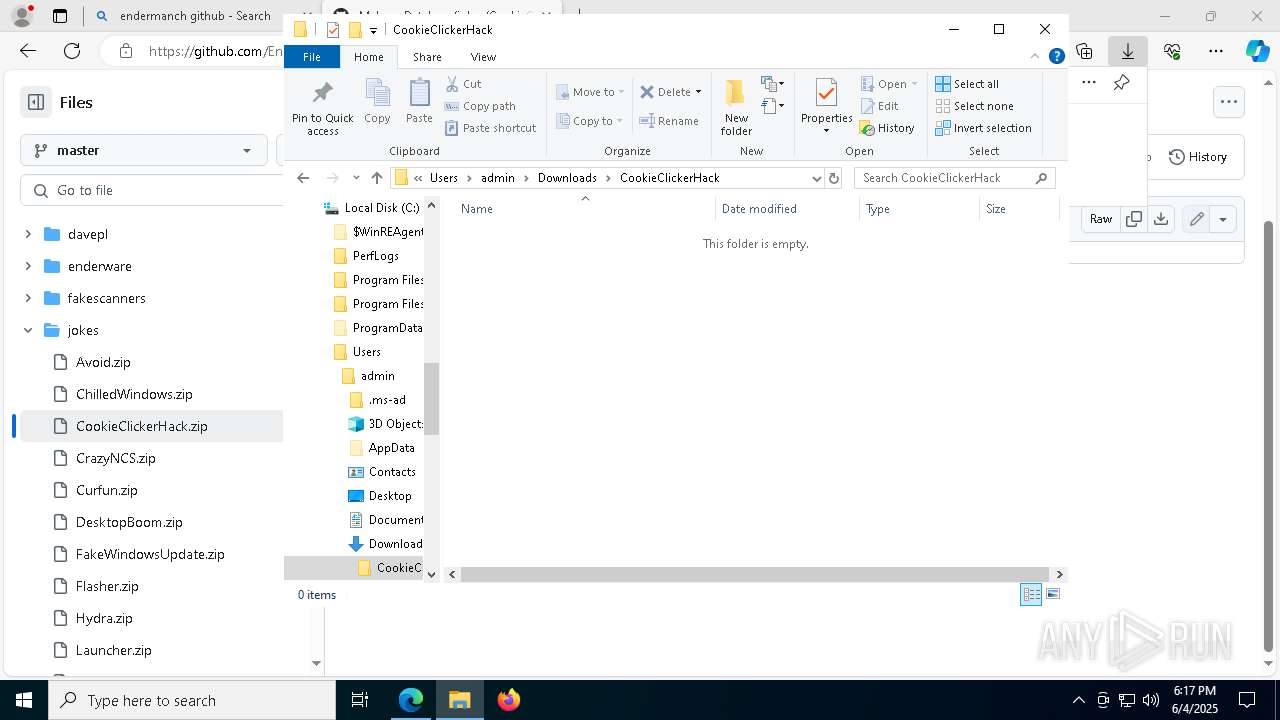
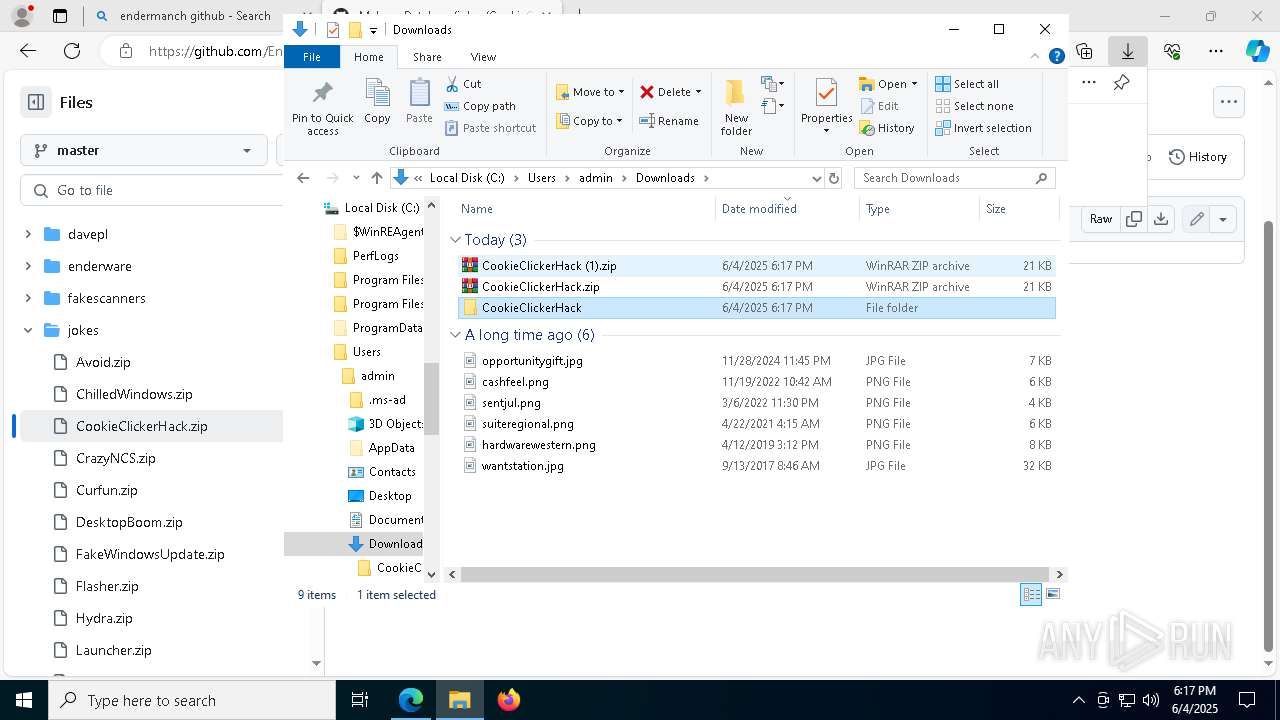
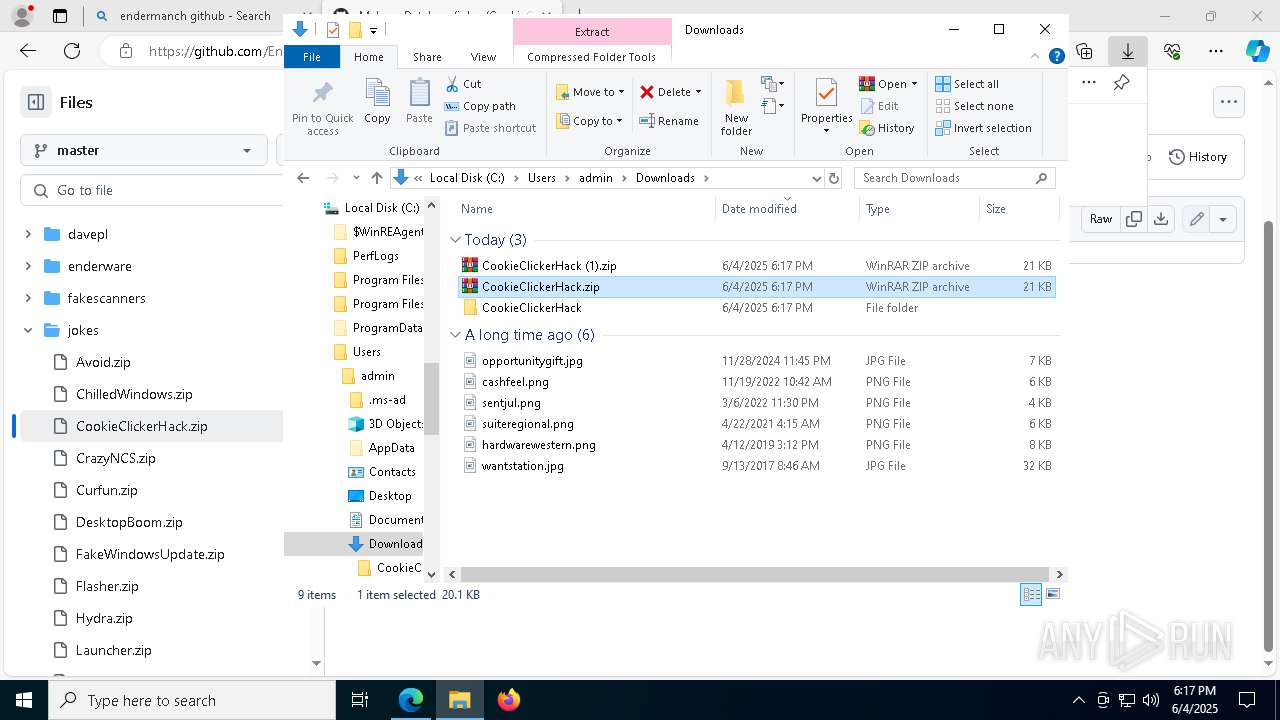
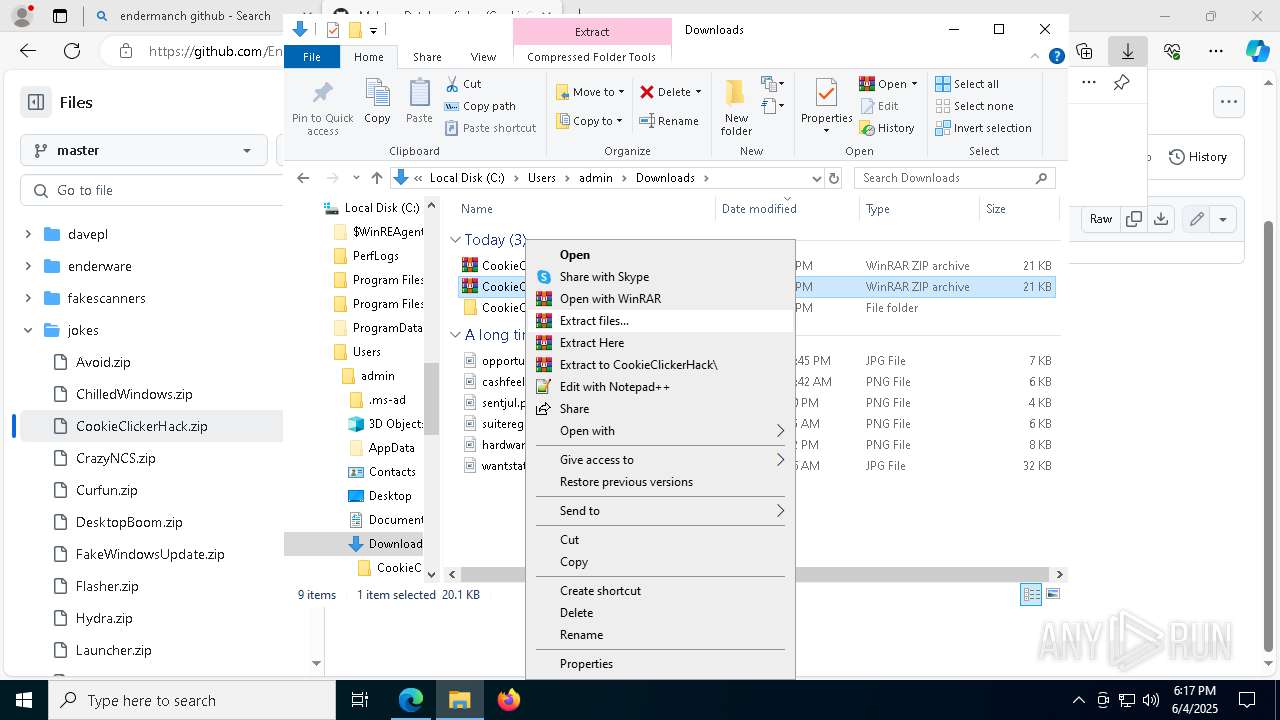
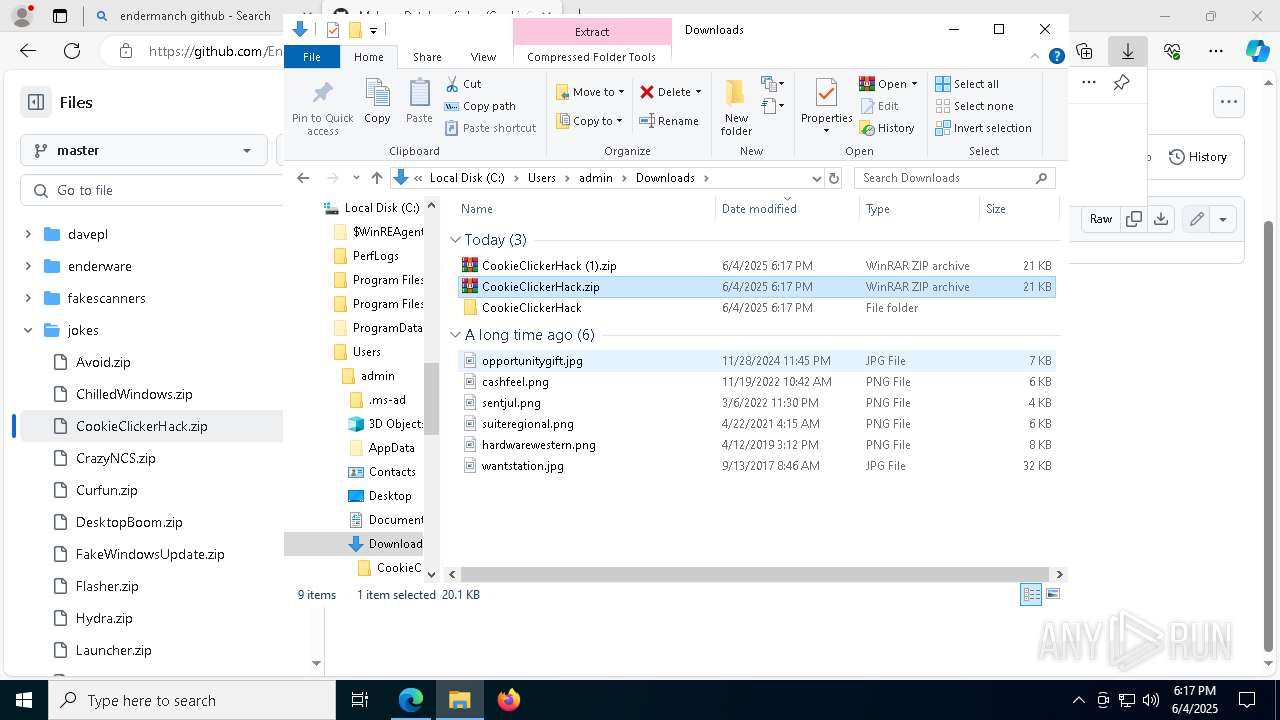
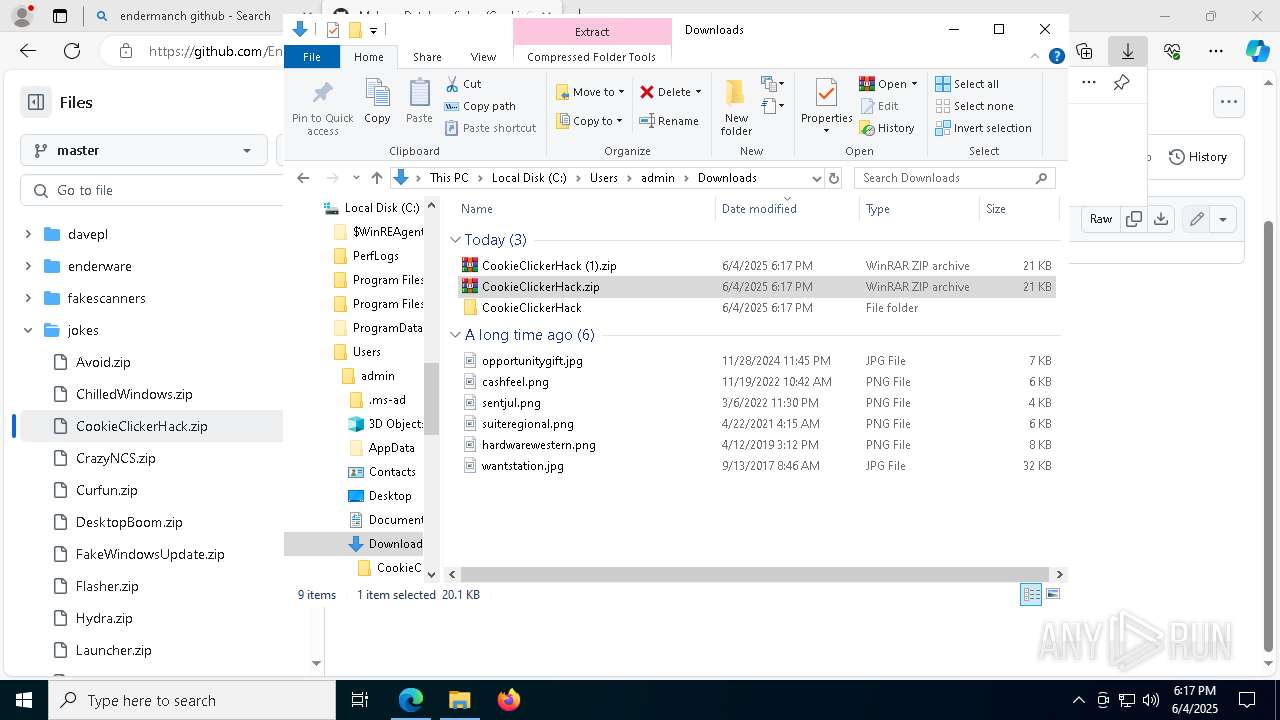
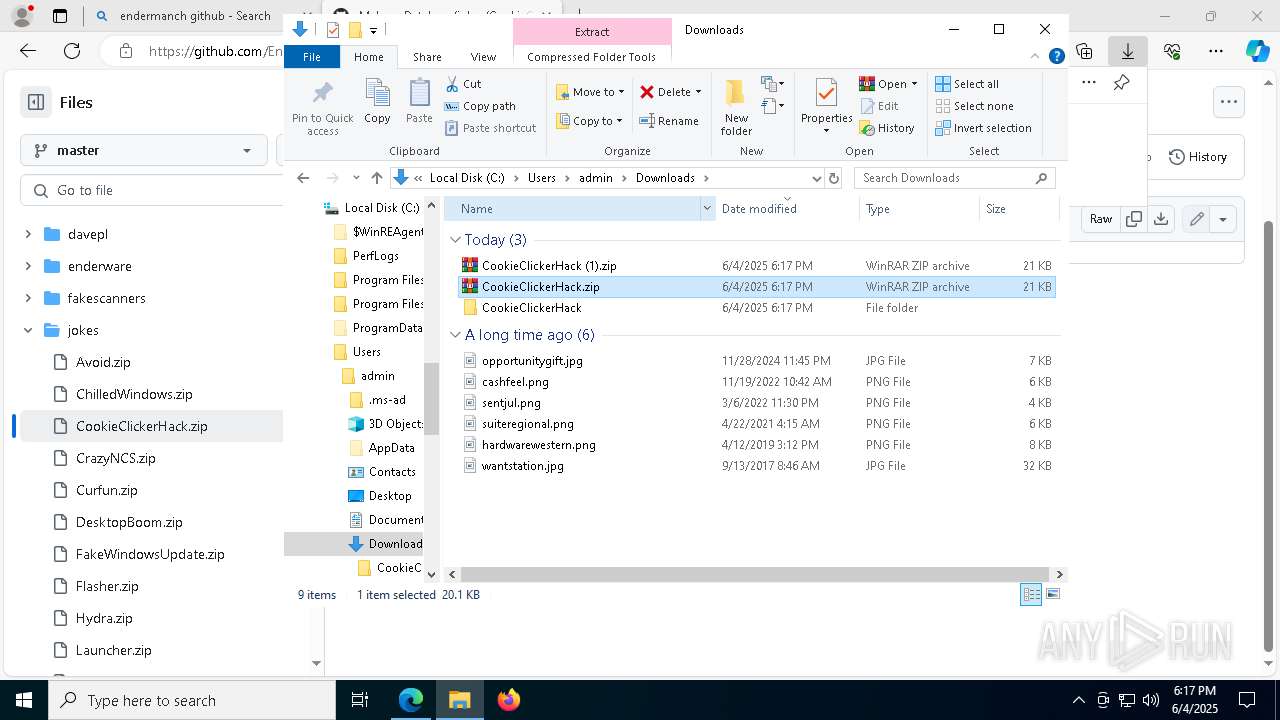
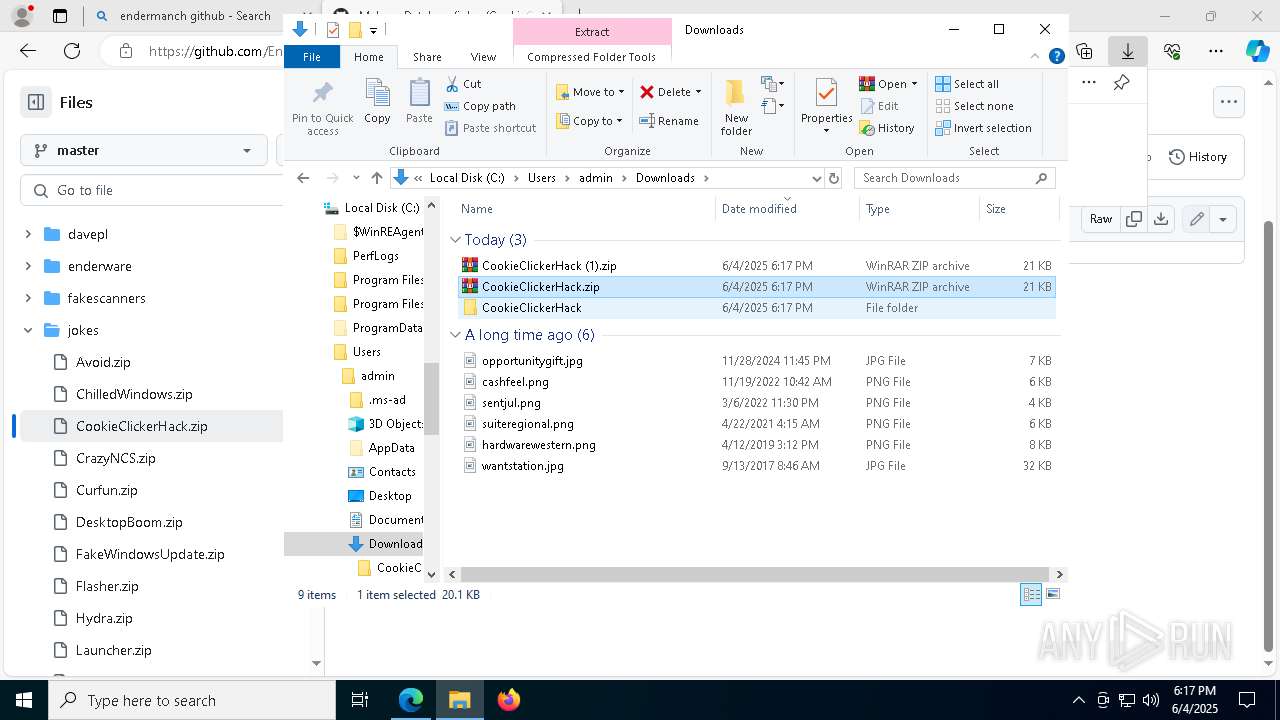
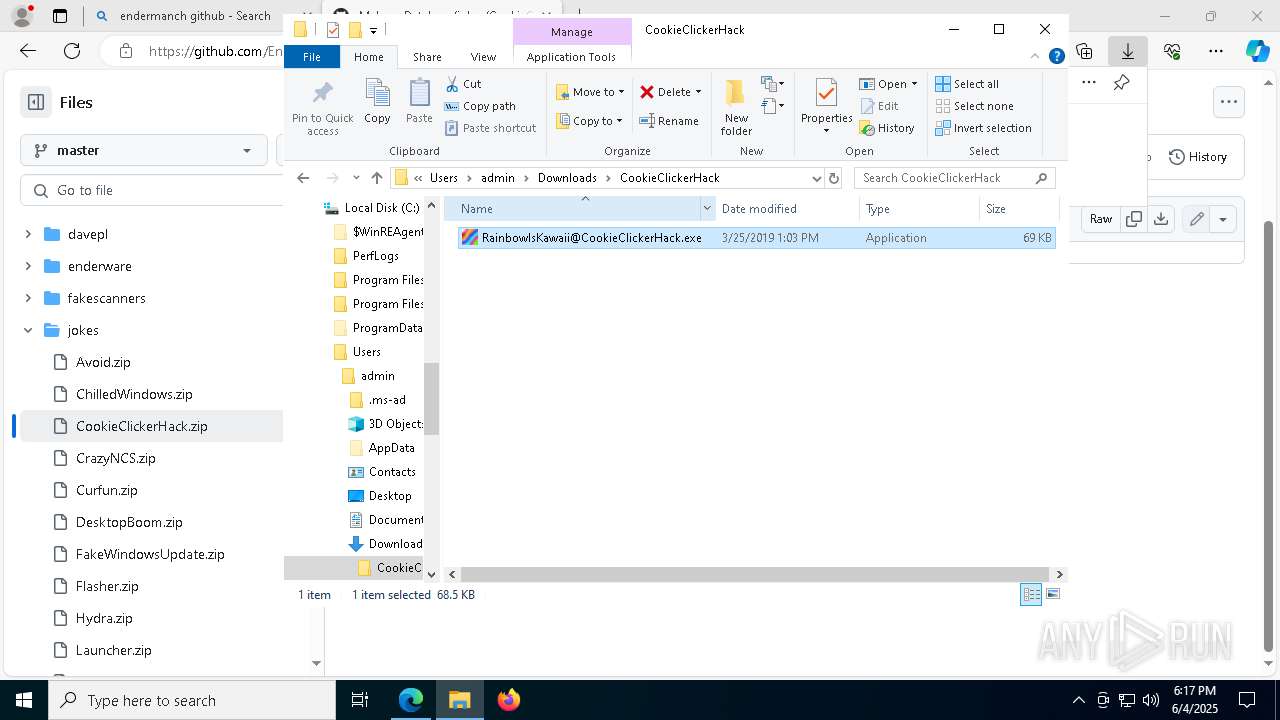
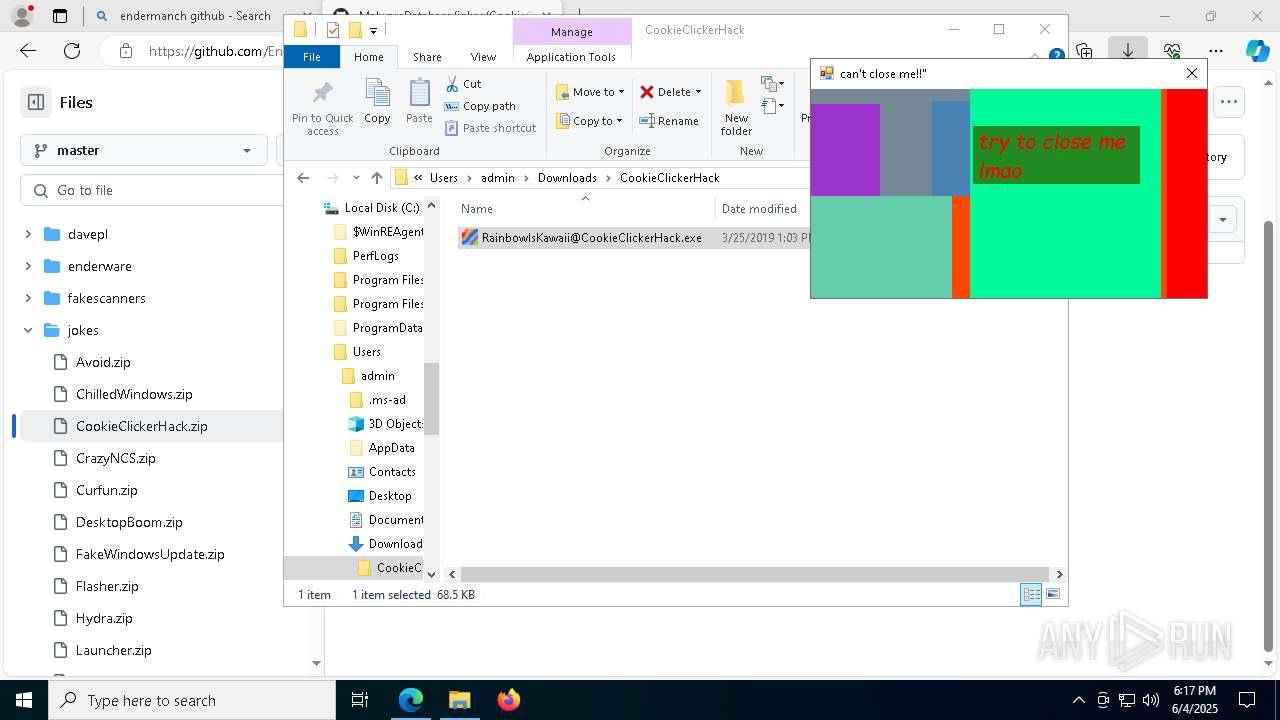
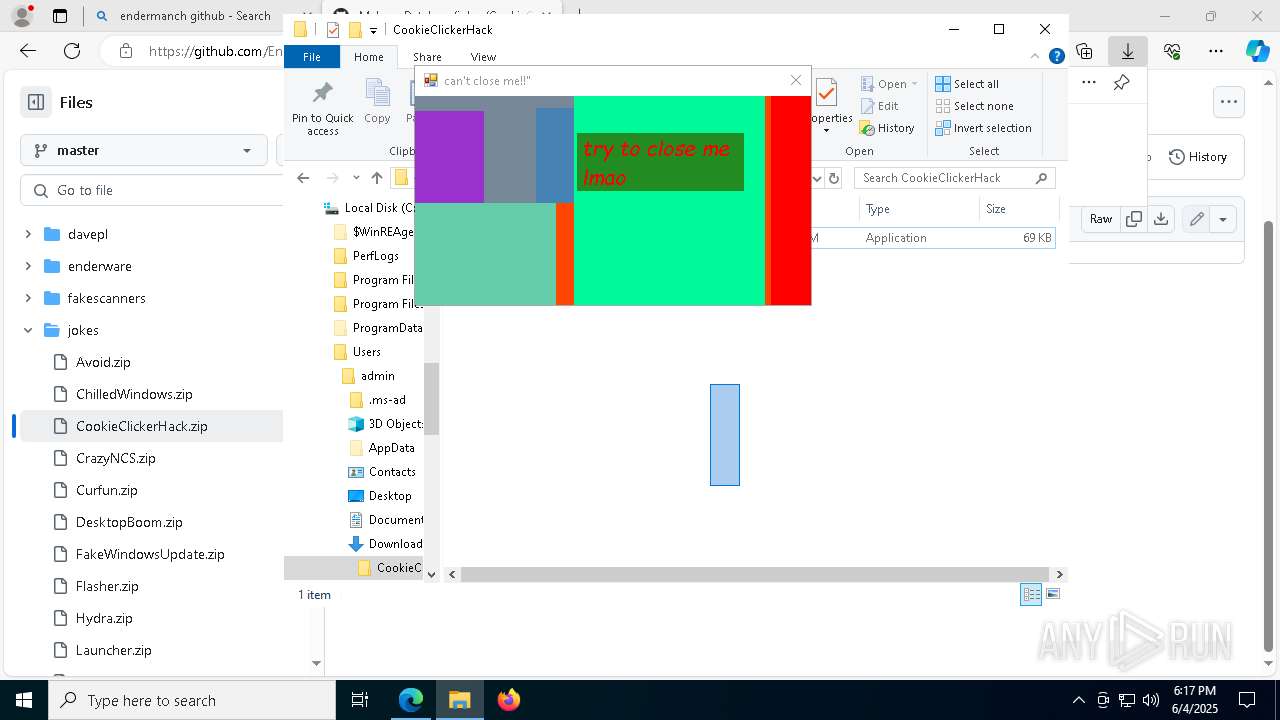
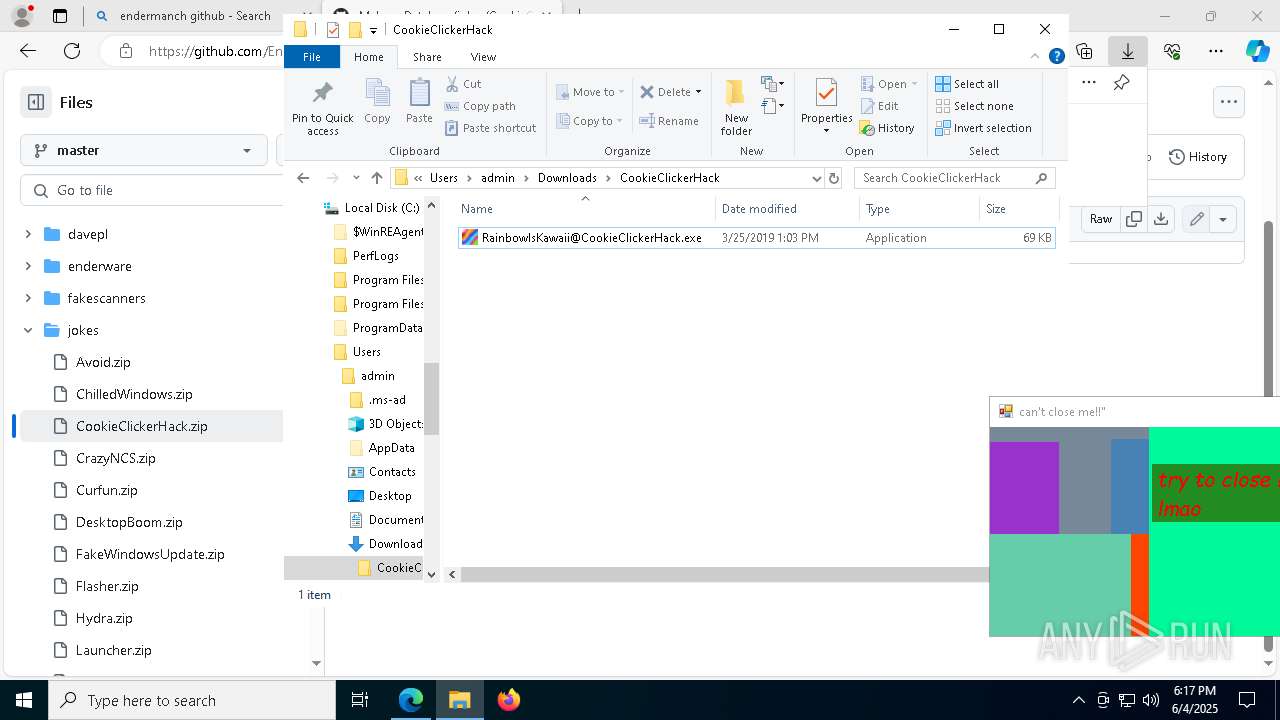
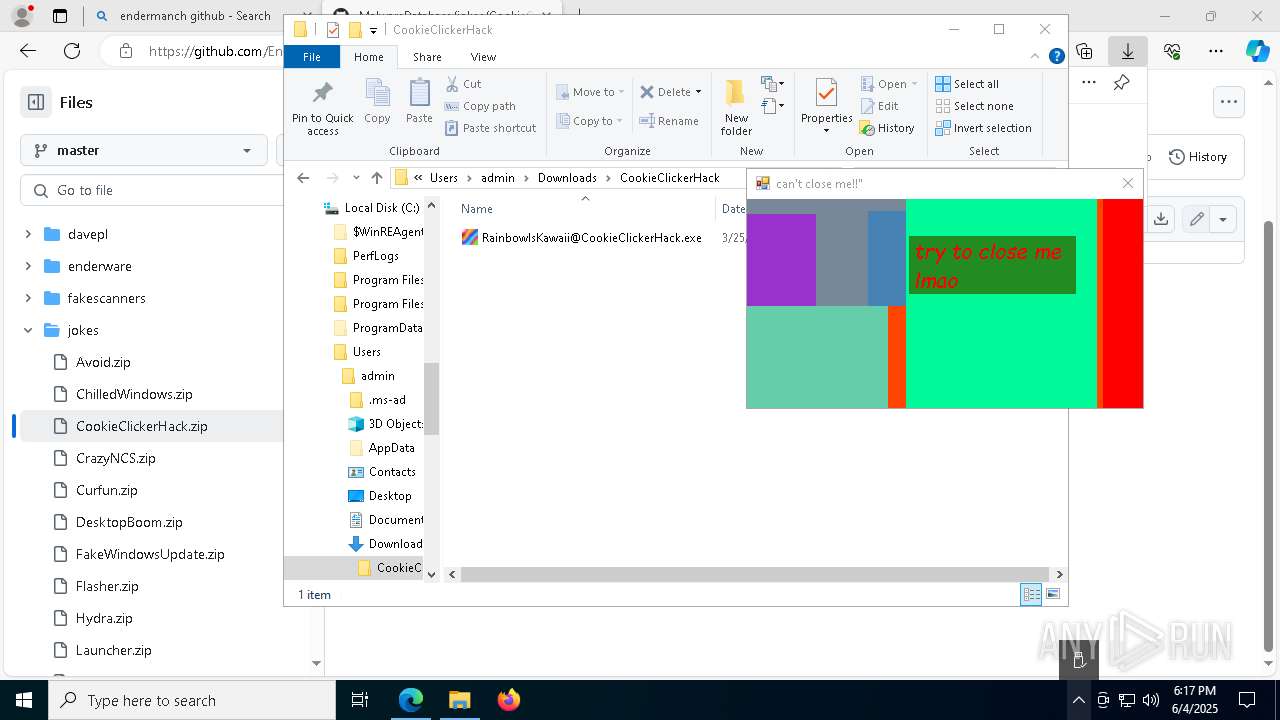
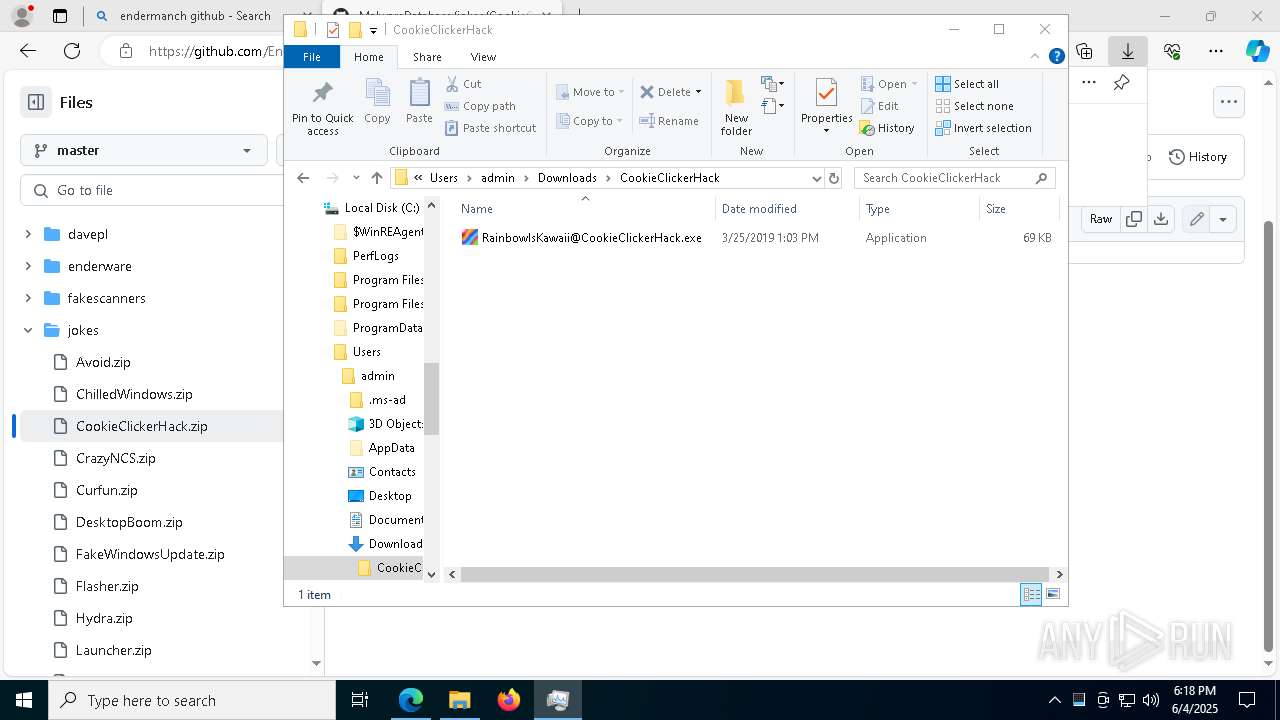
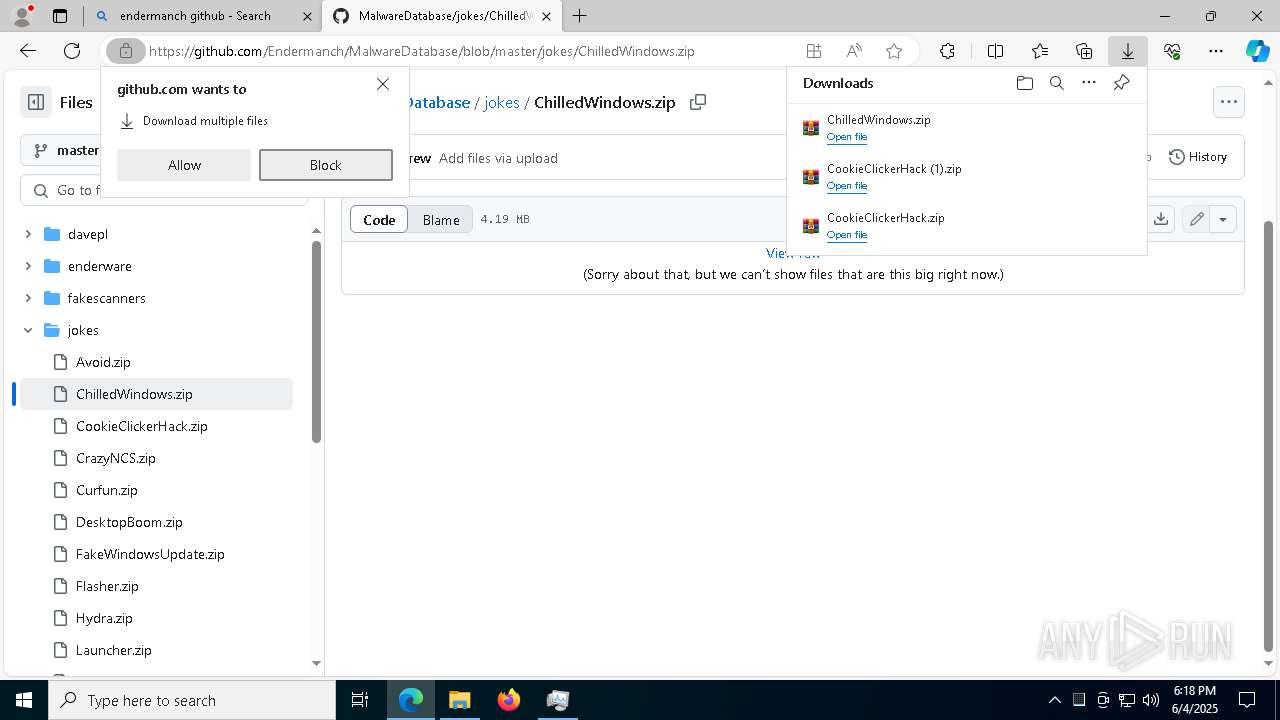
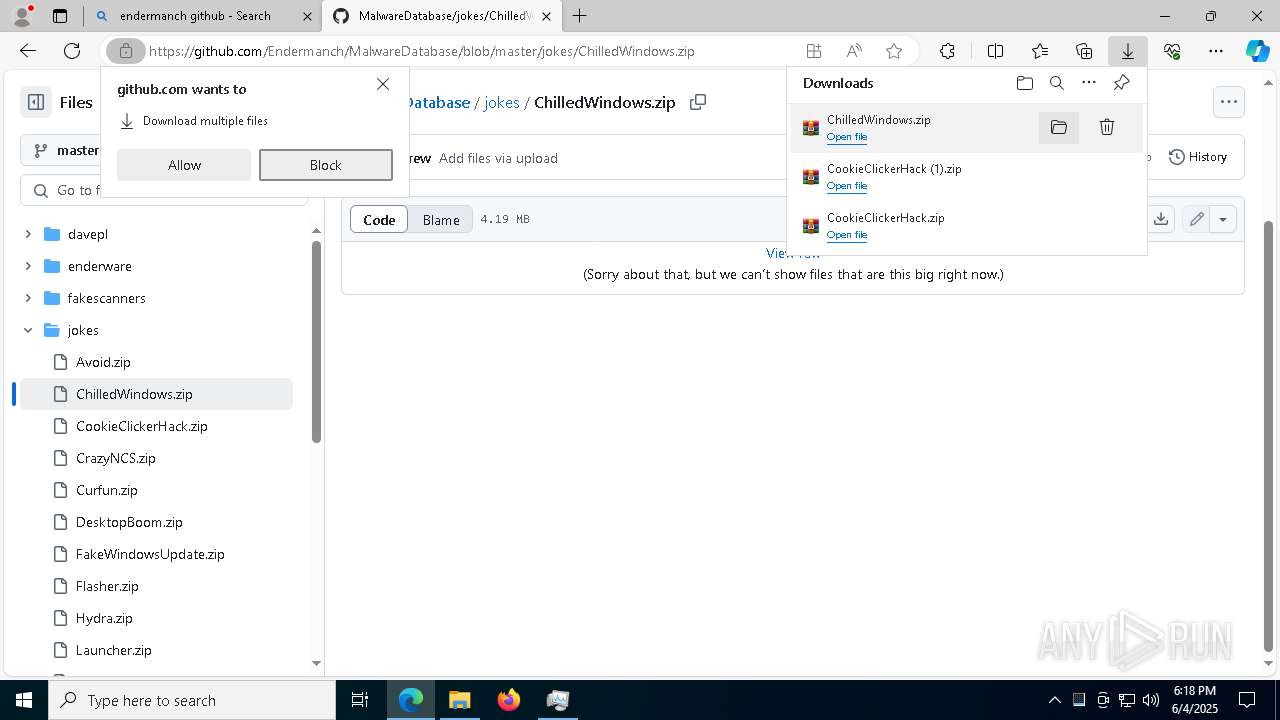
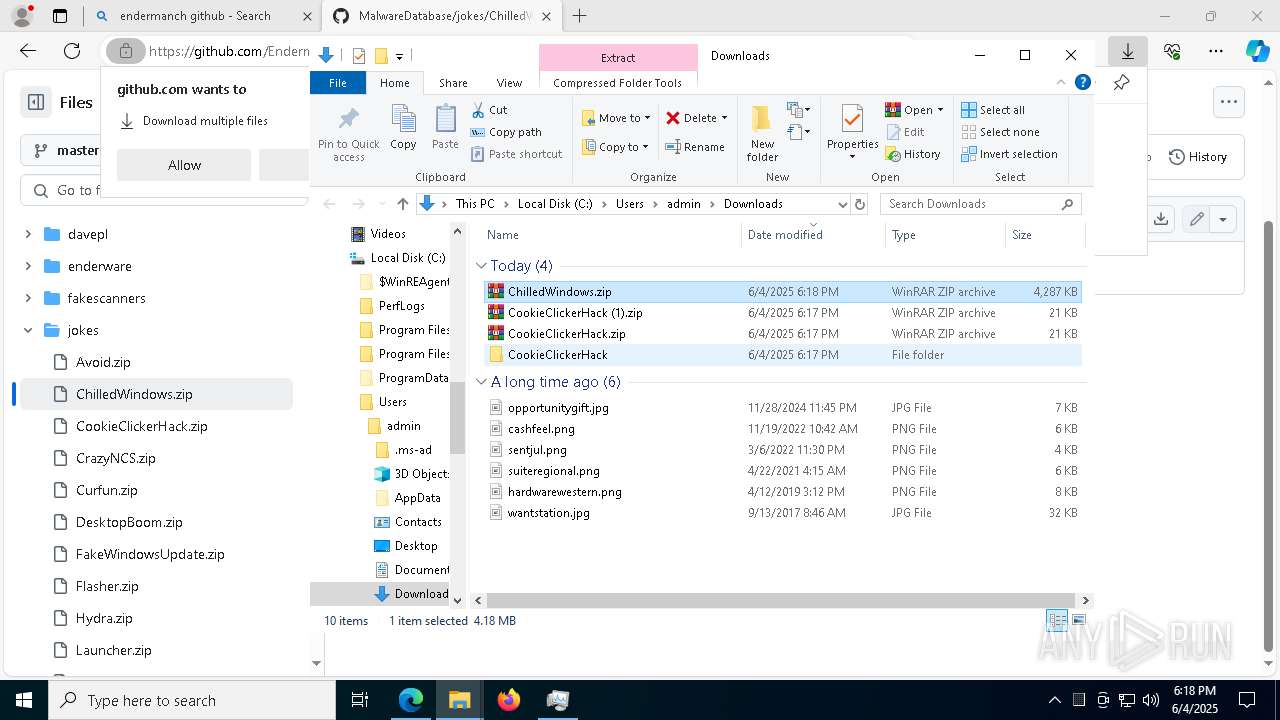
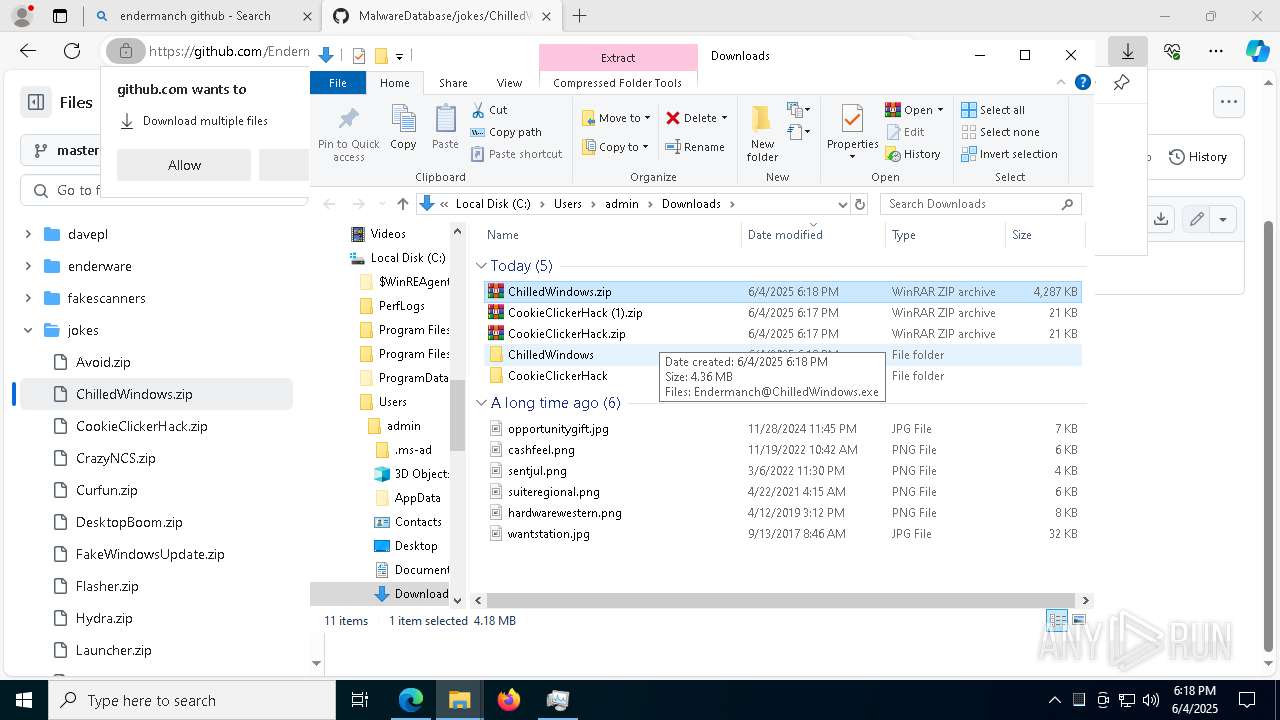
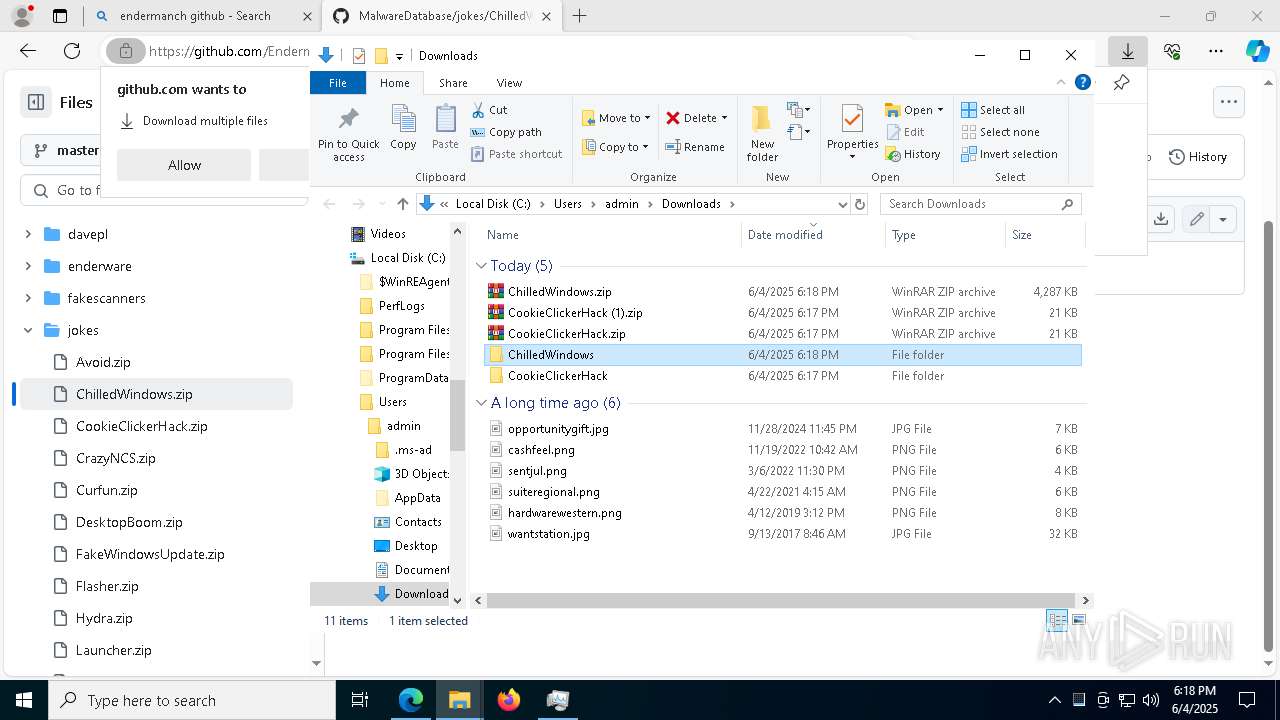
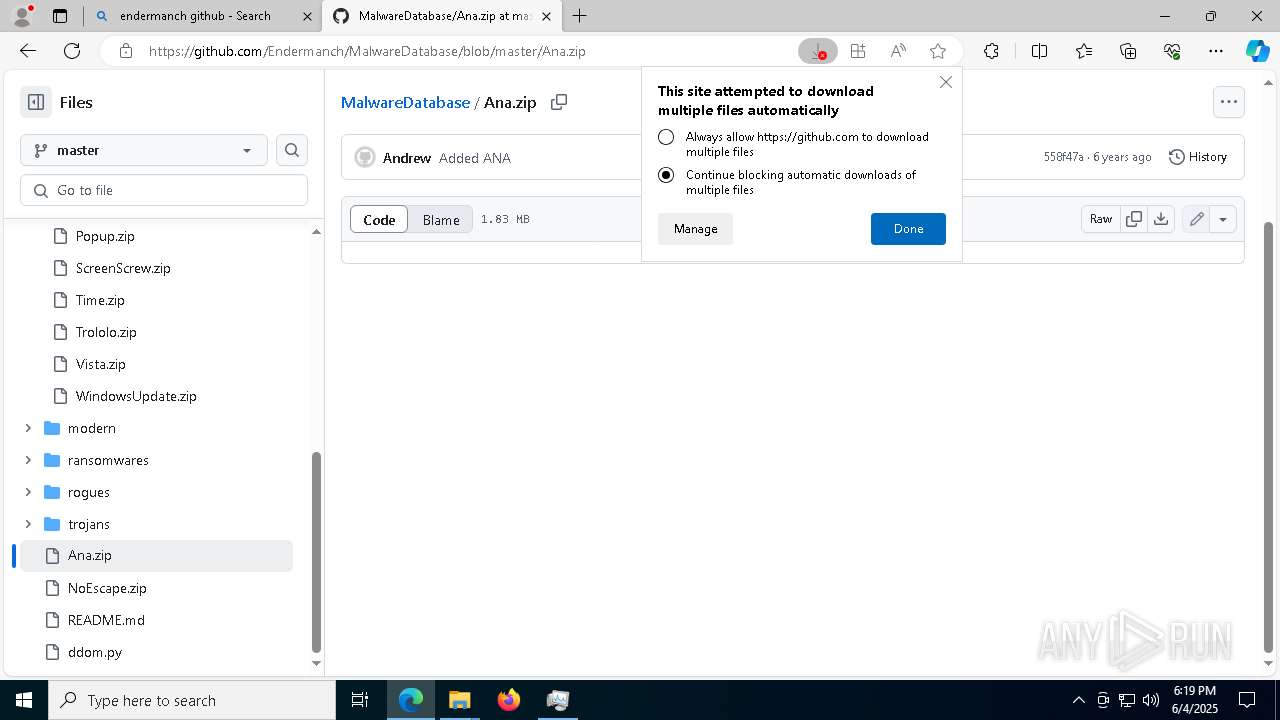
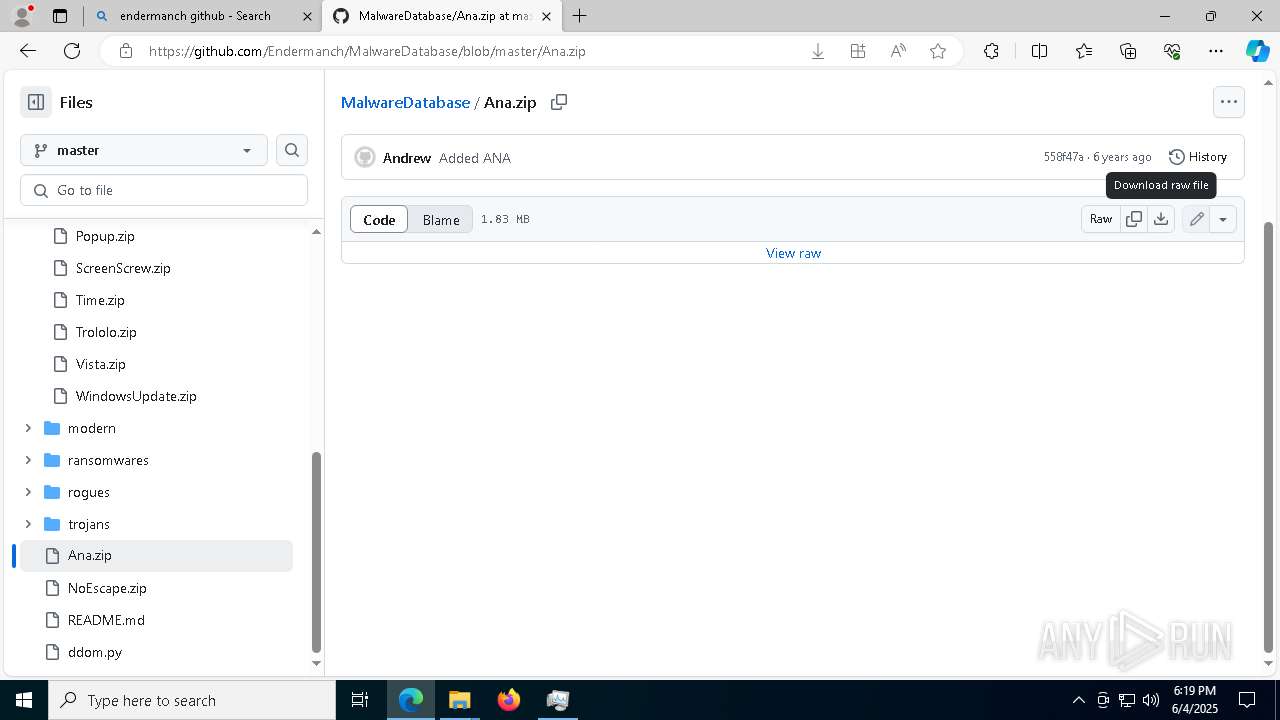
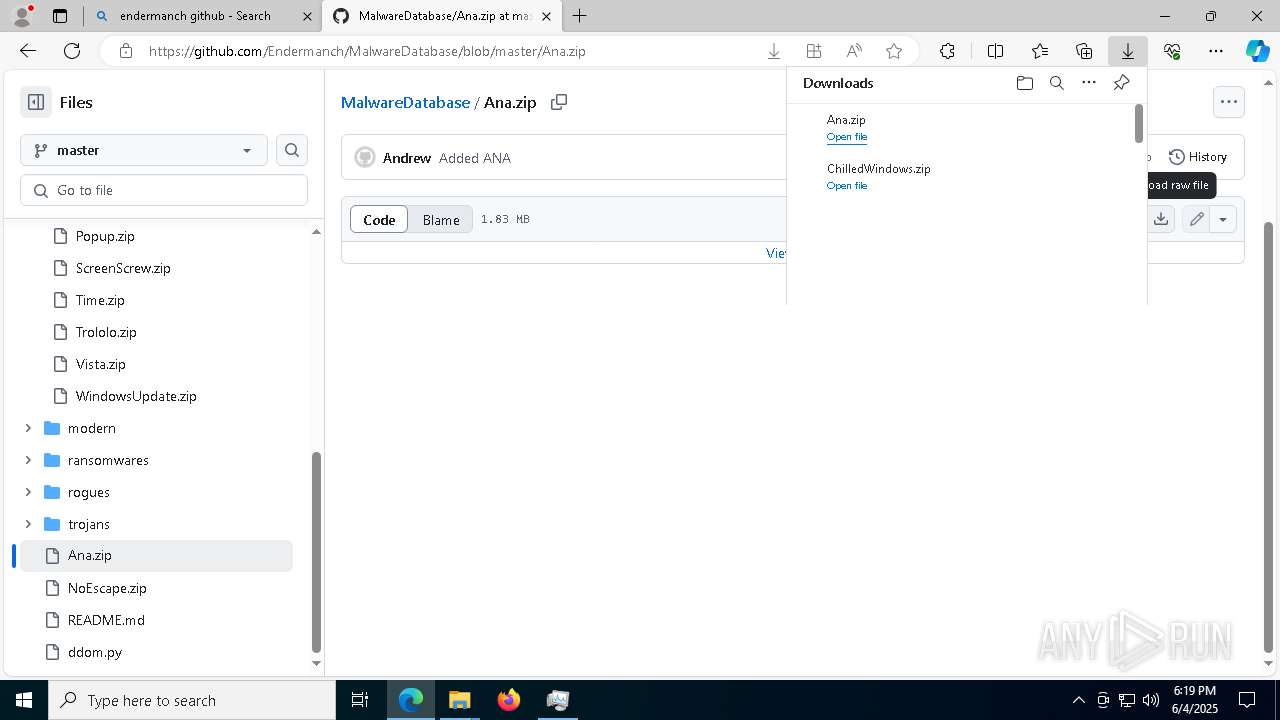
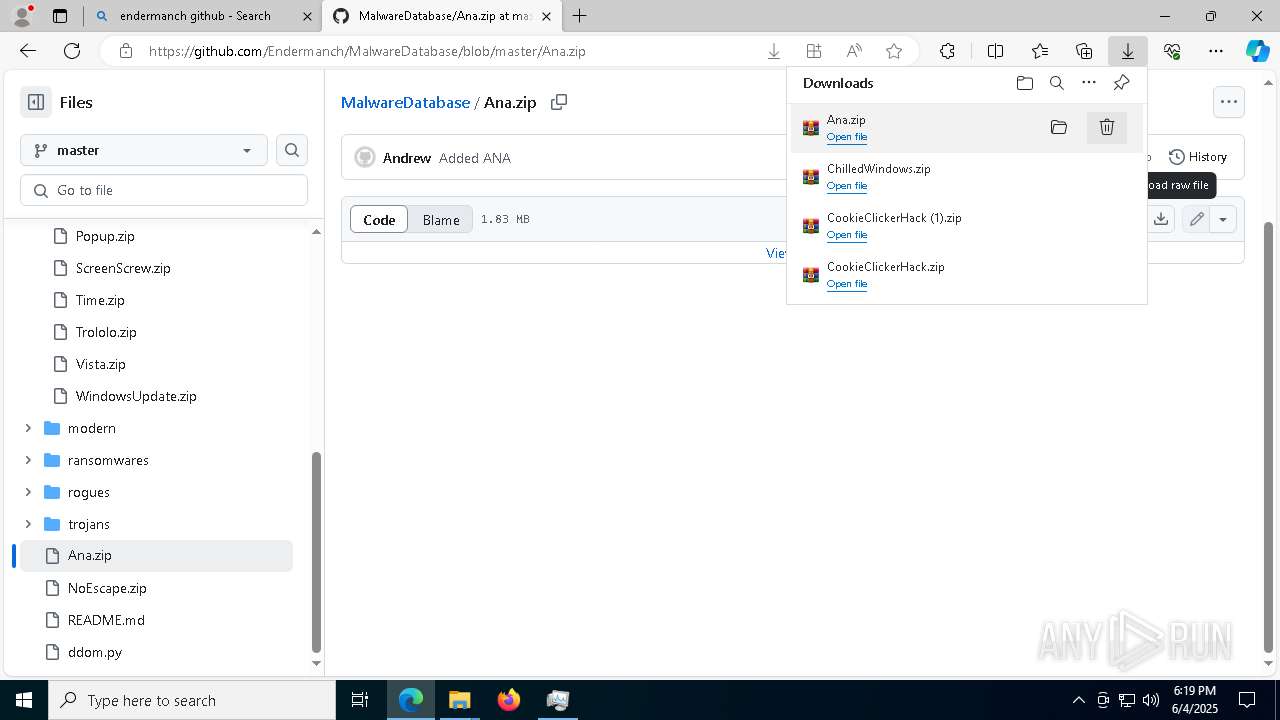
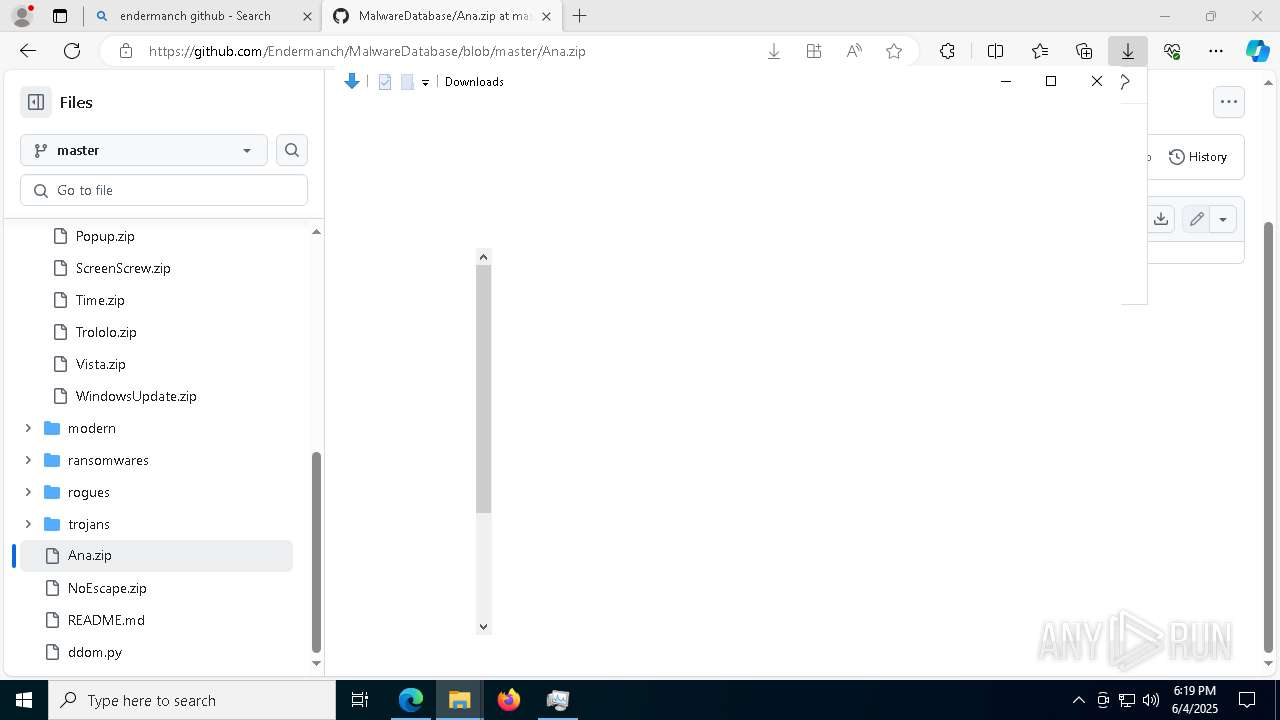
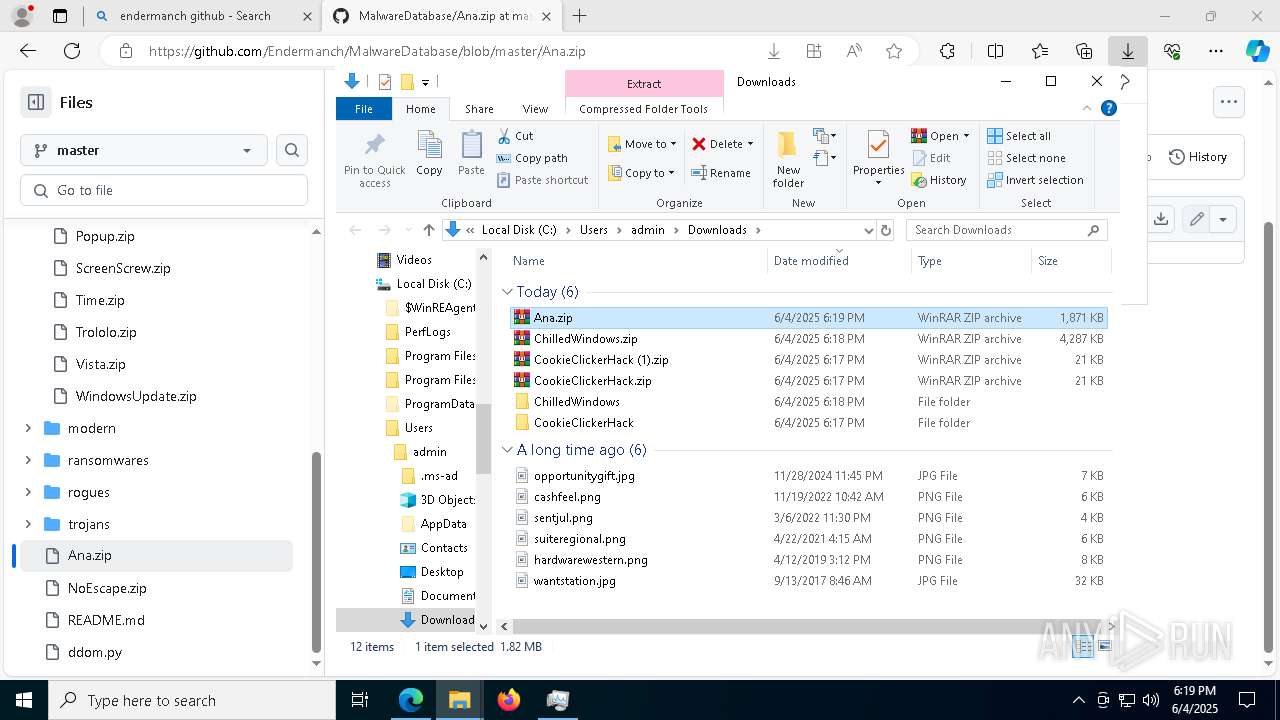
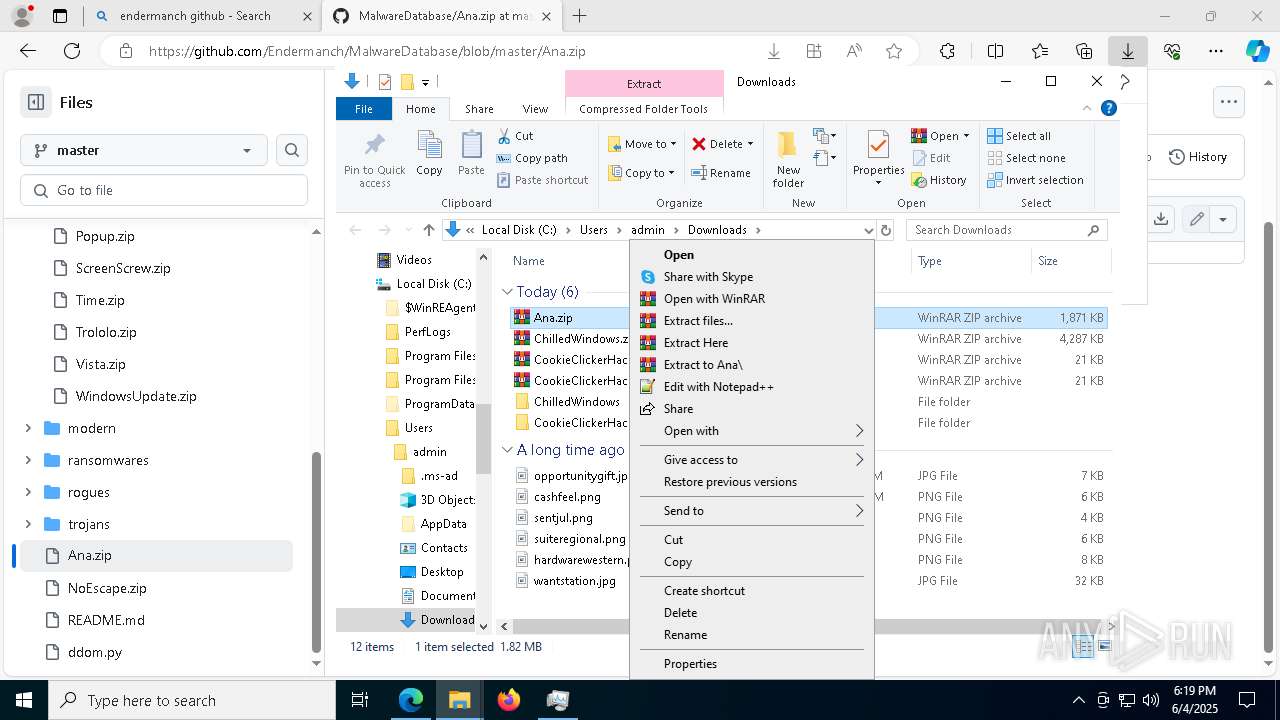
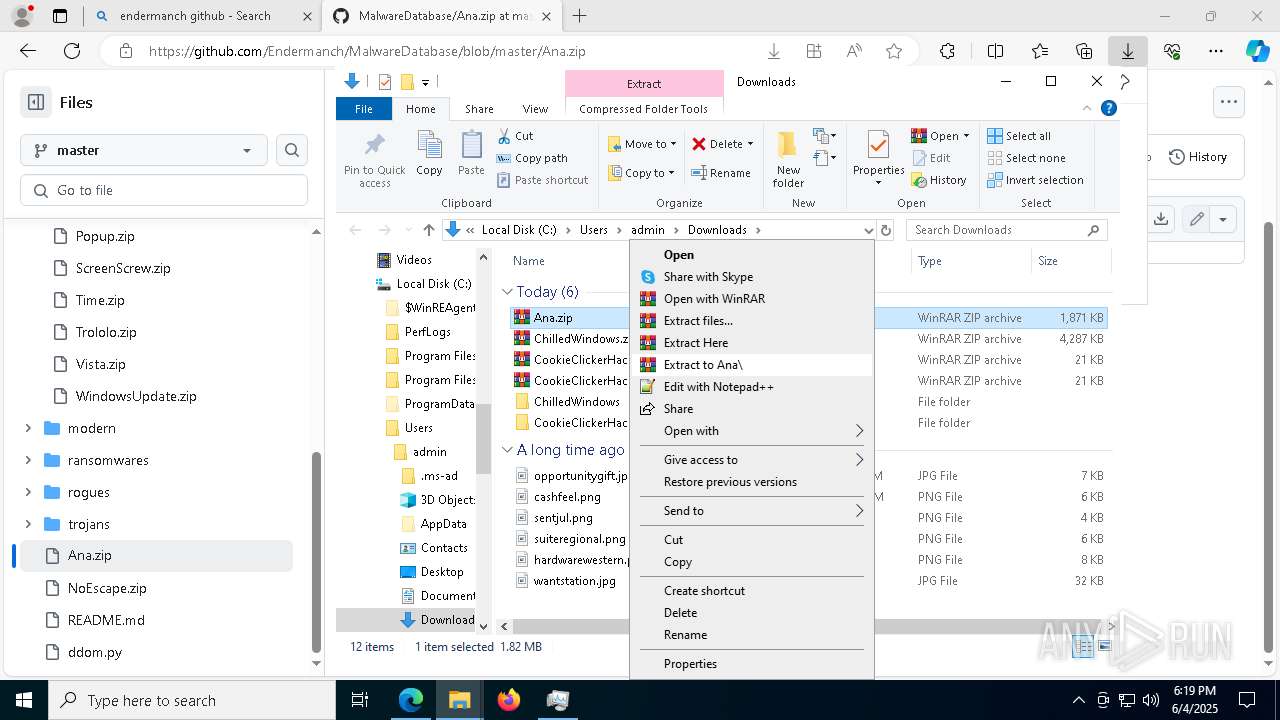
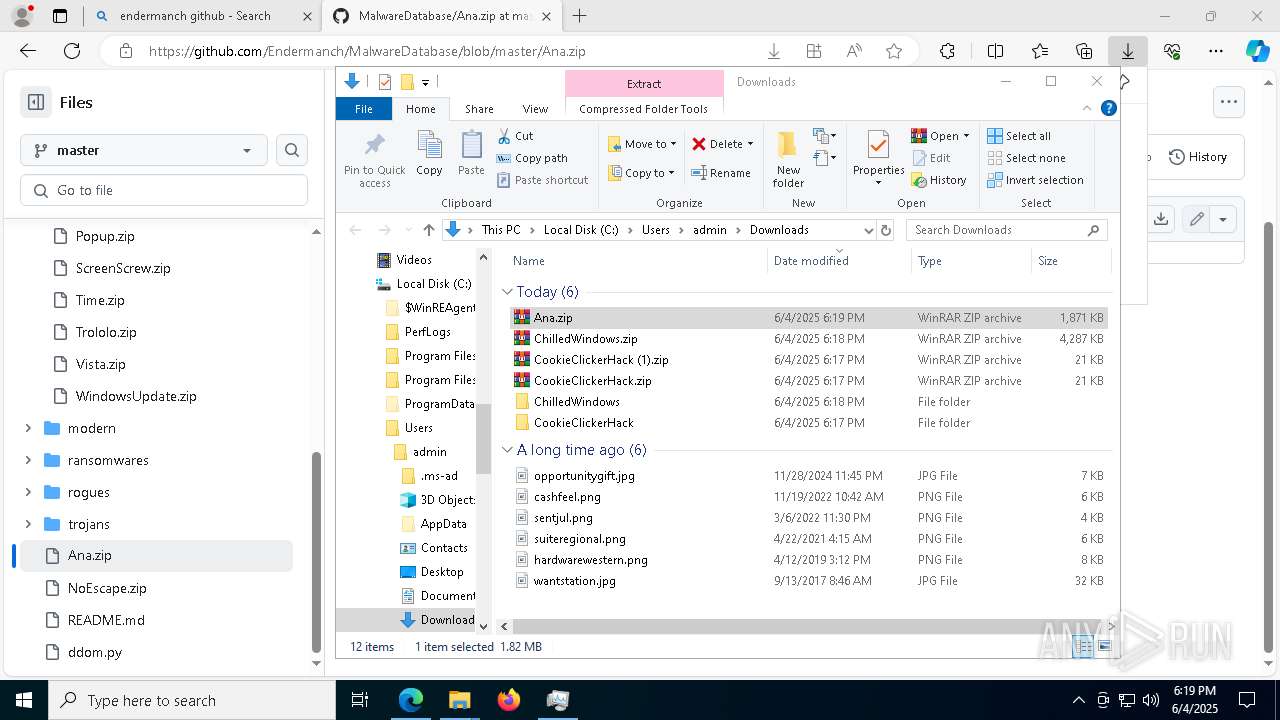
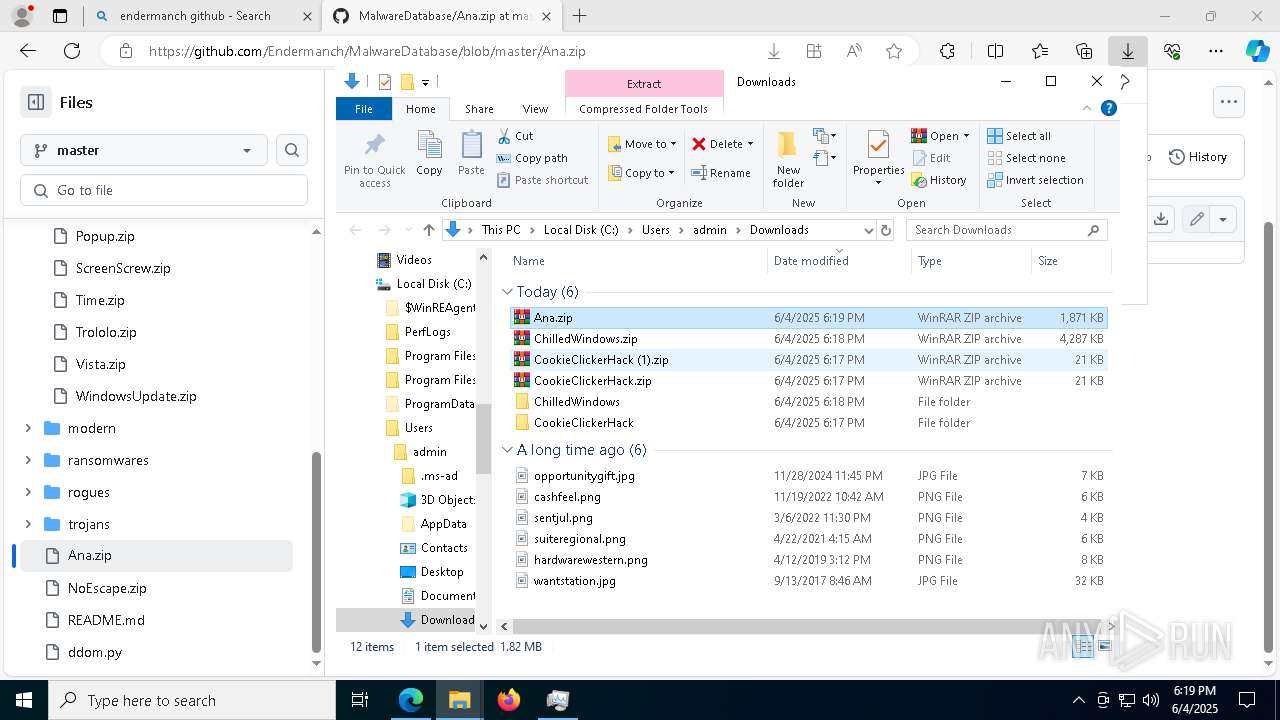
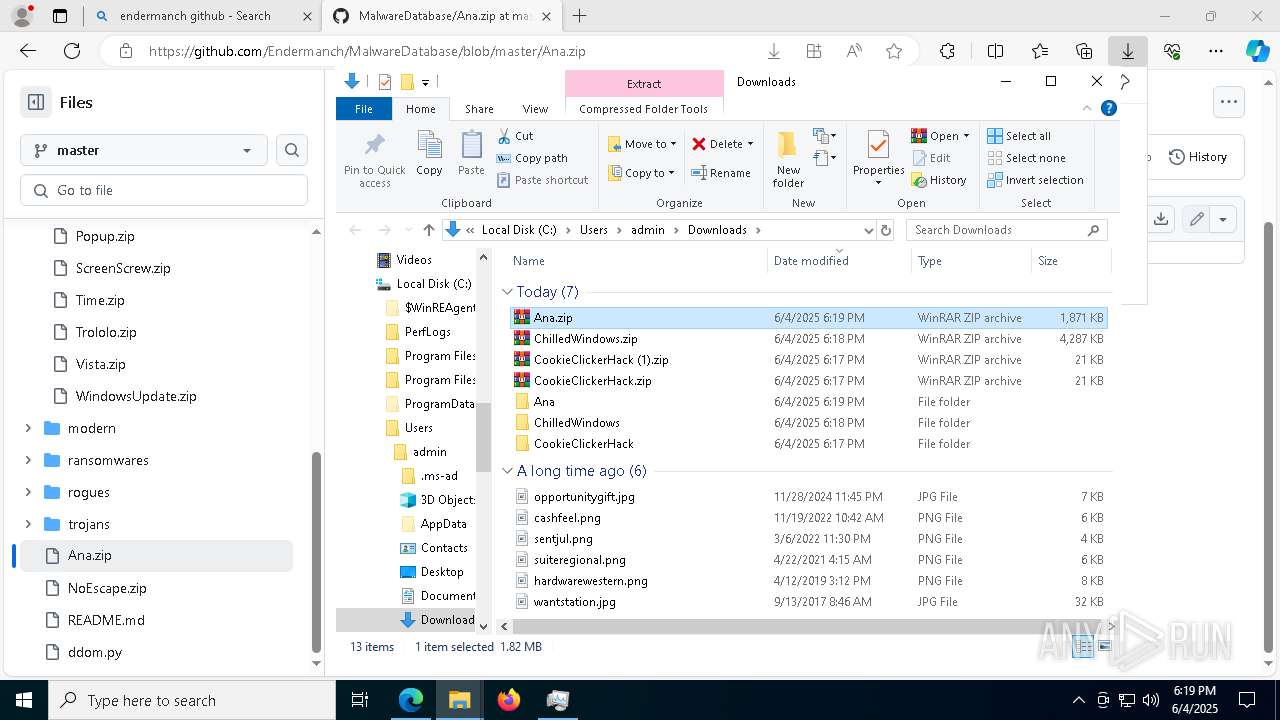
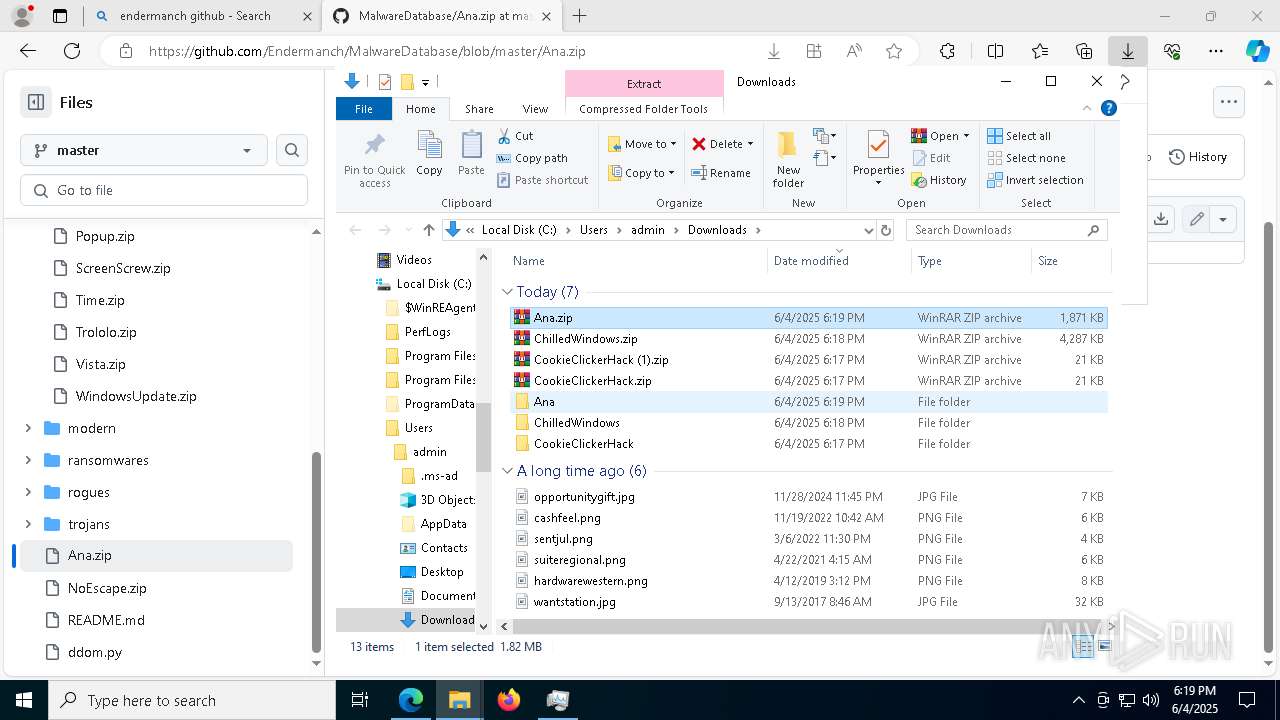
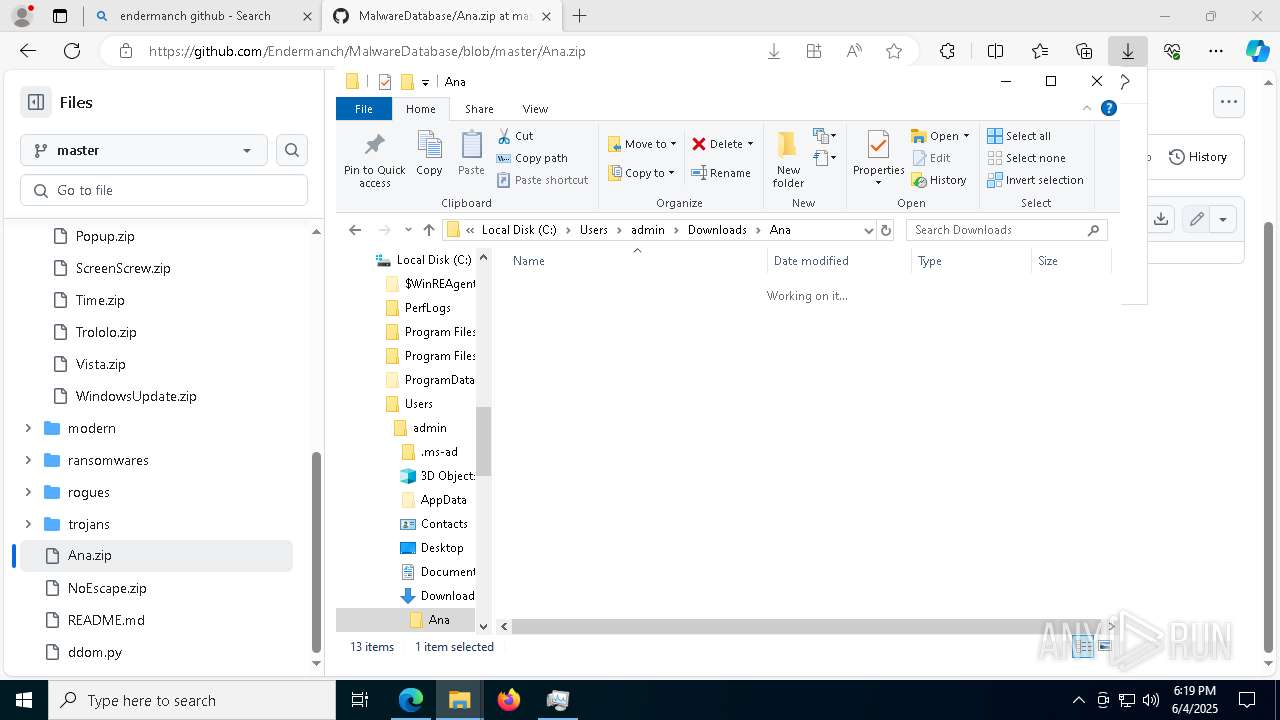
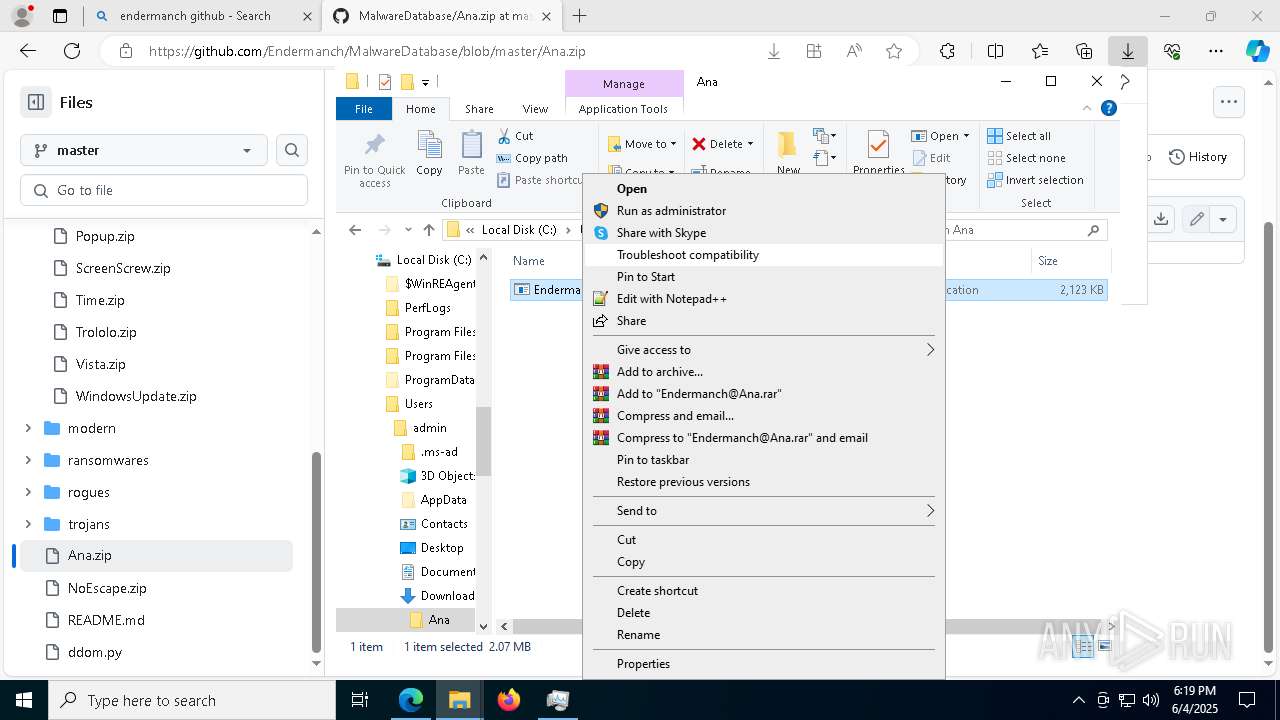
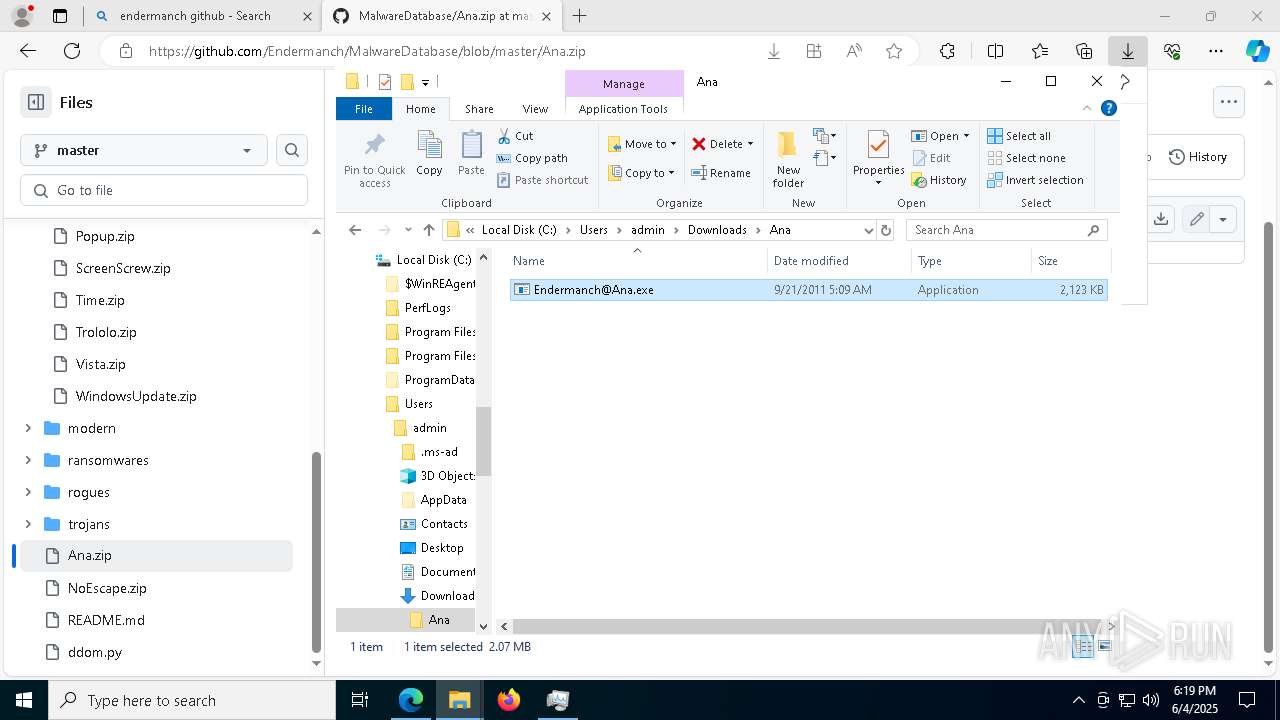
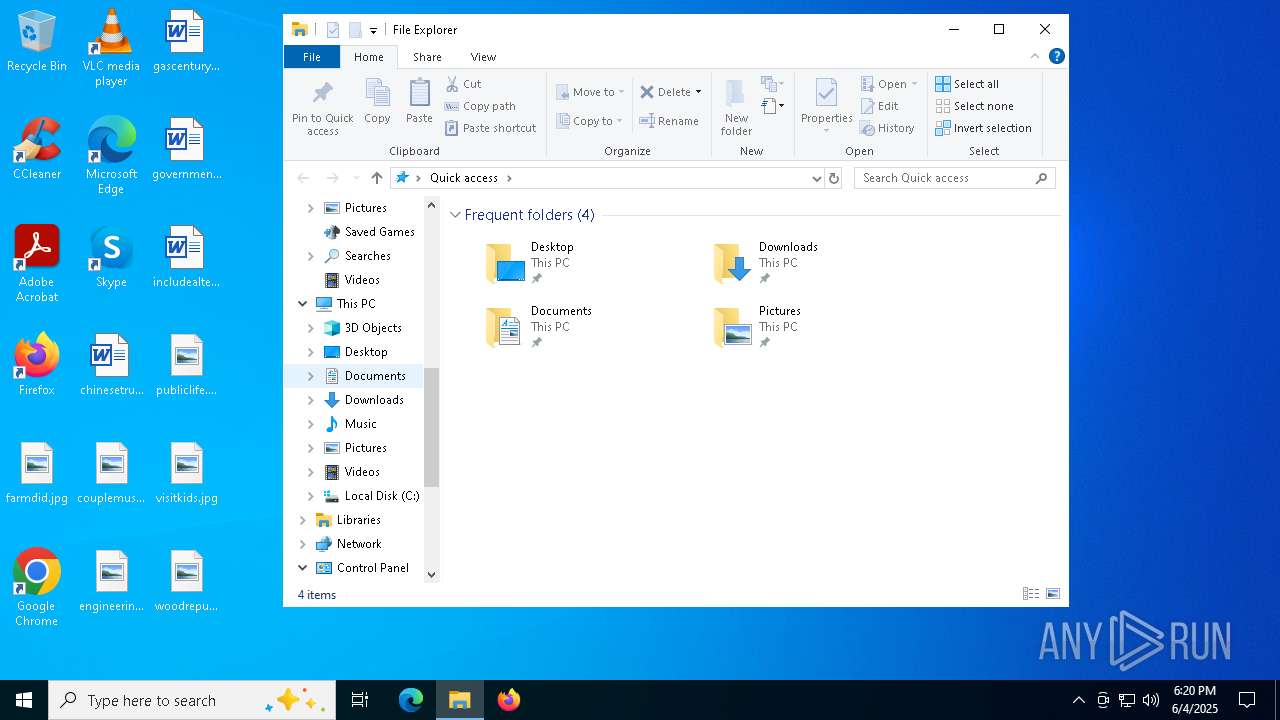
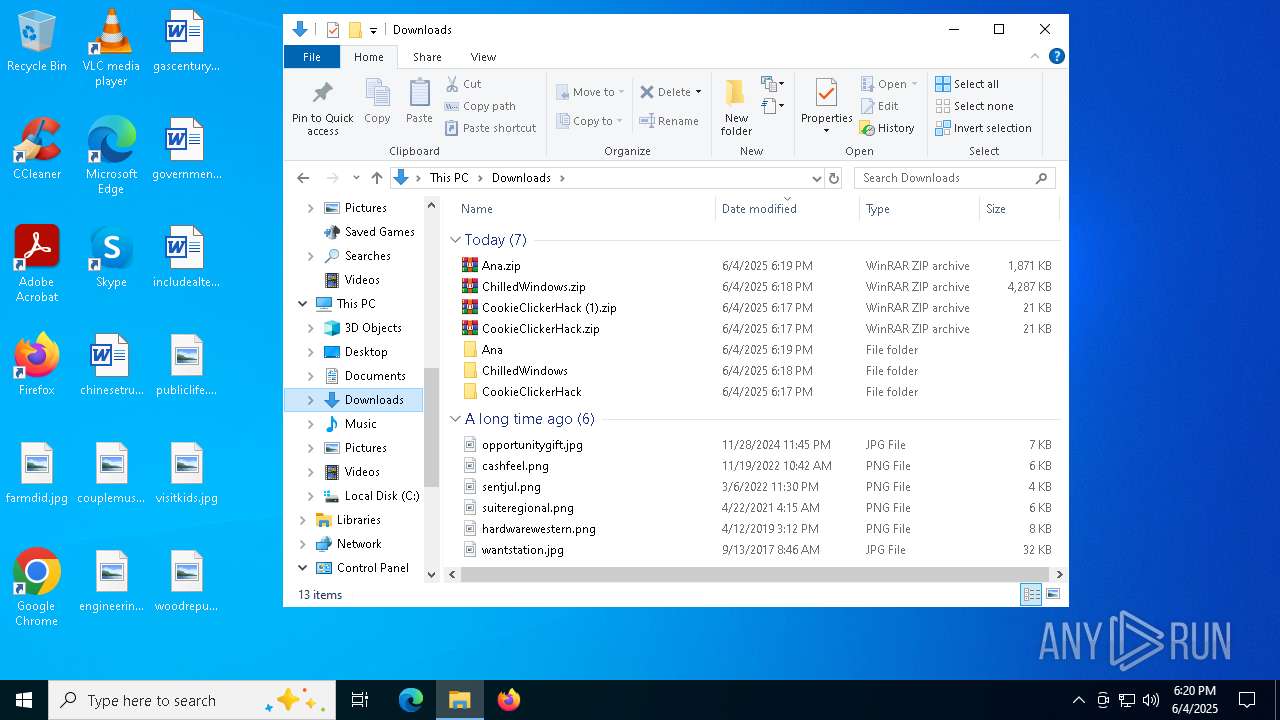
Launching a file from the Downloads directory
- msedge.exe (PID: 1168)
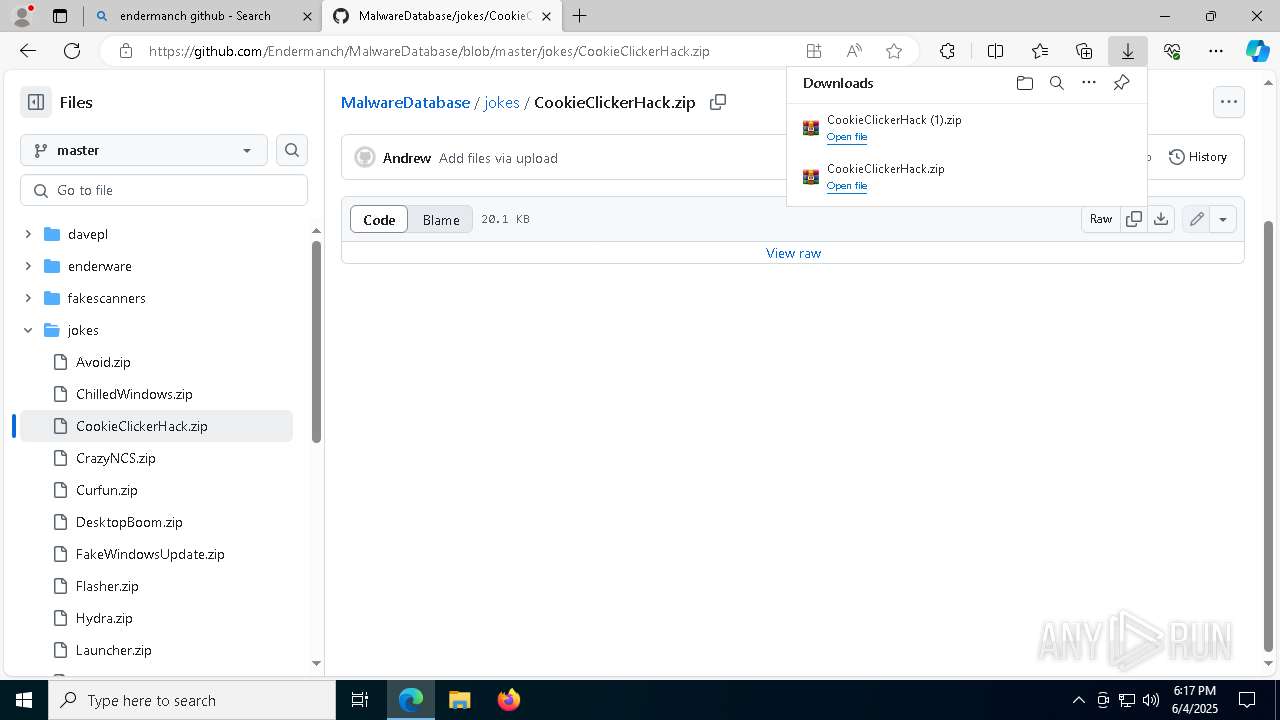
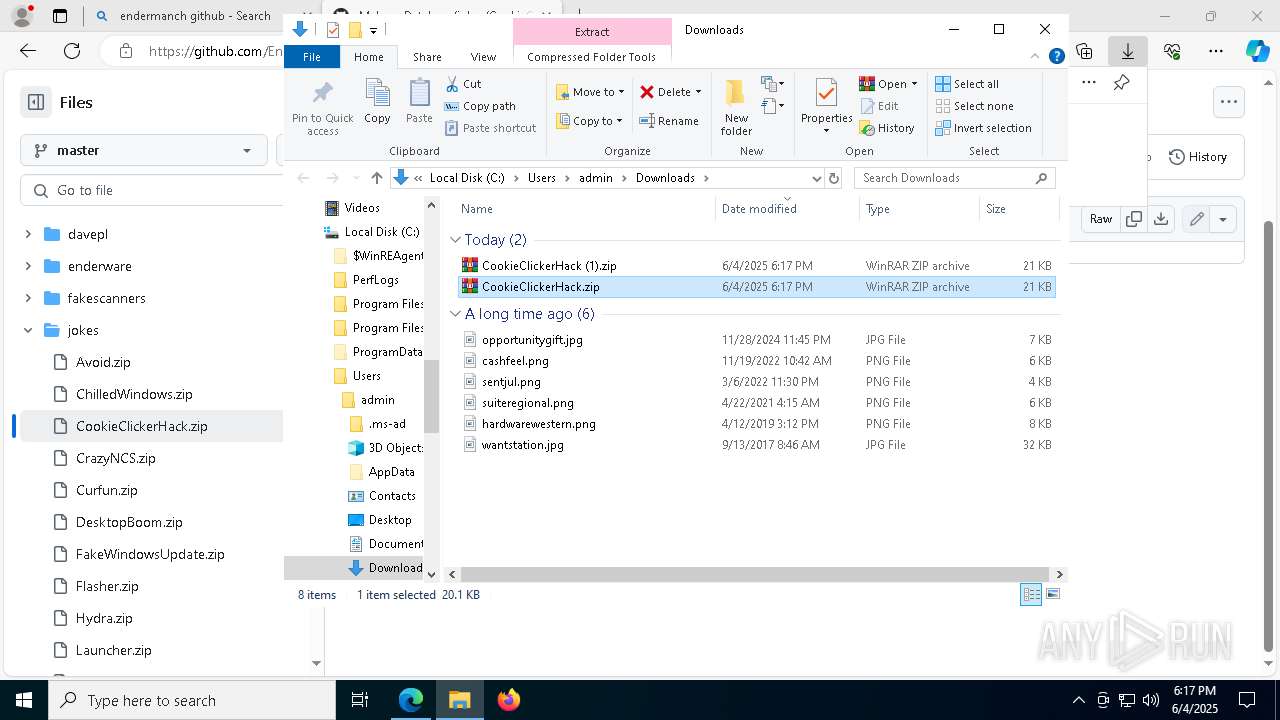
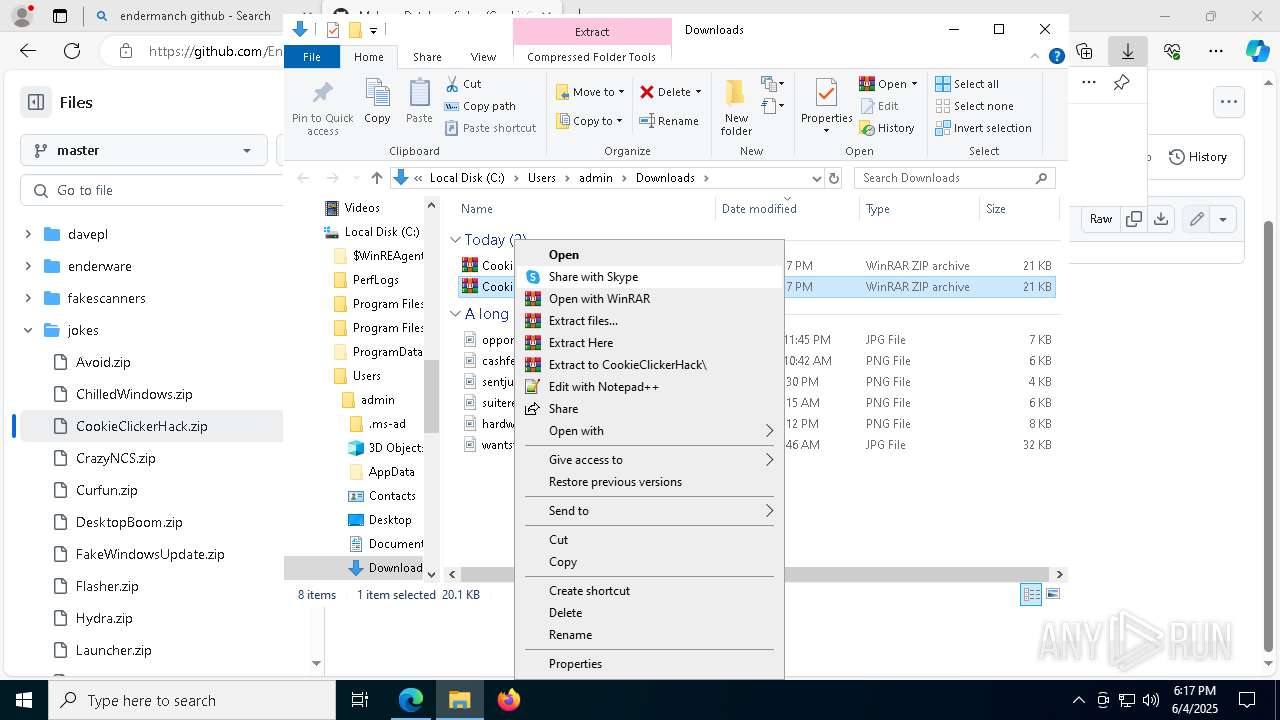
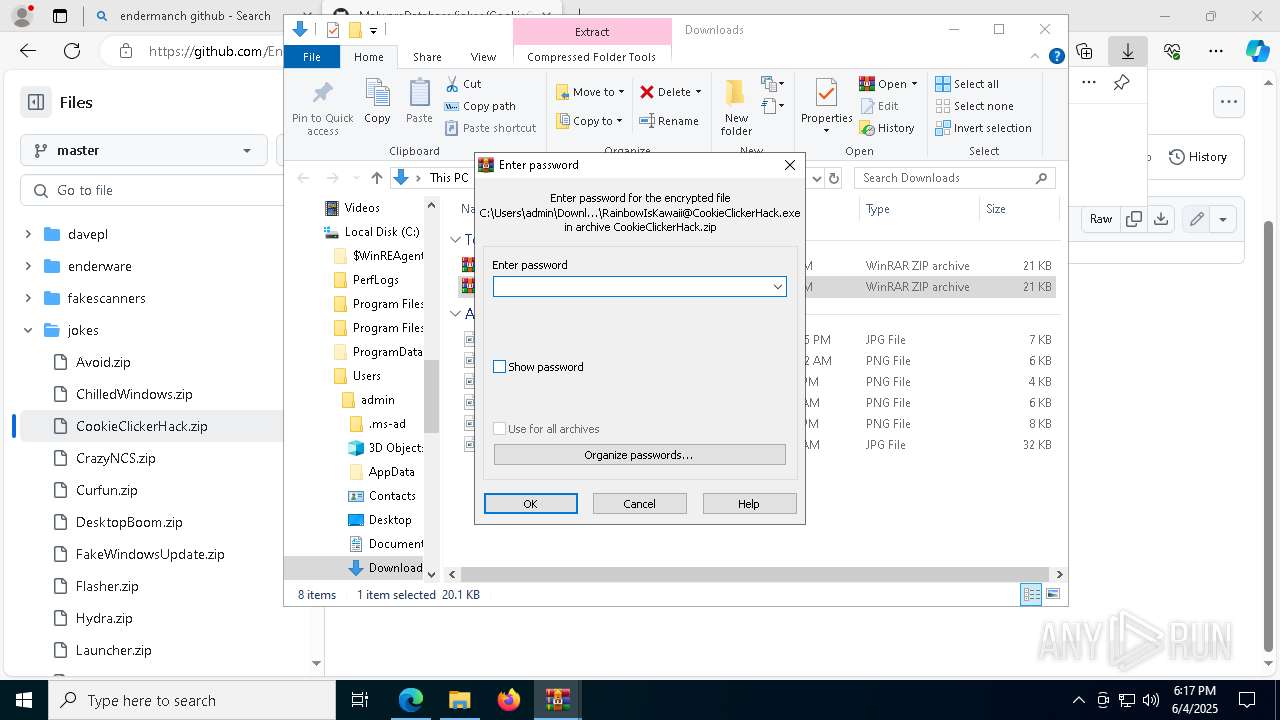
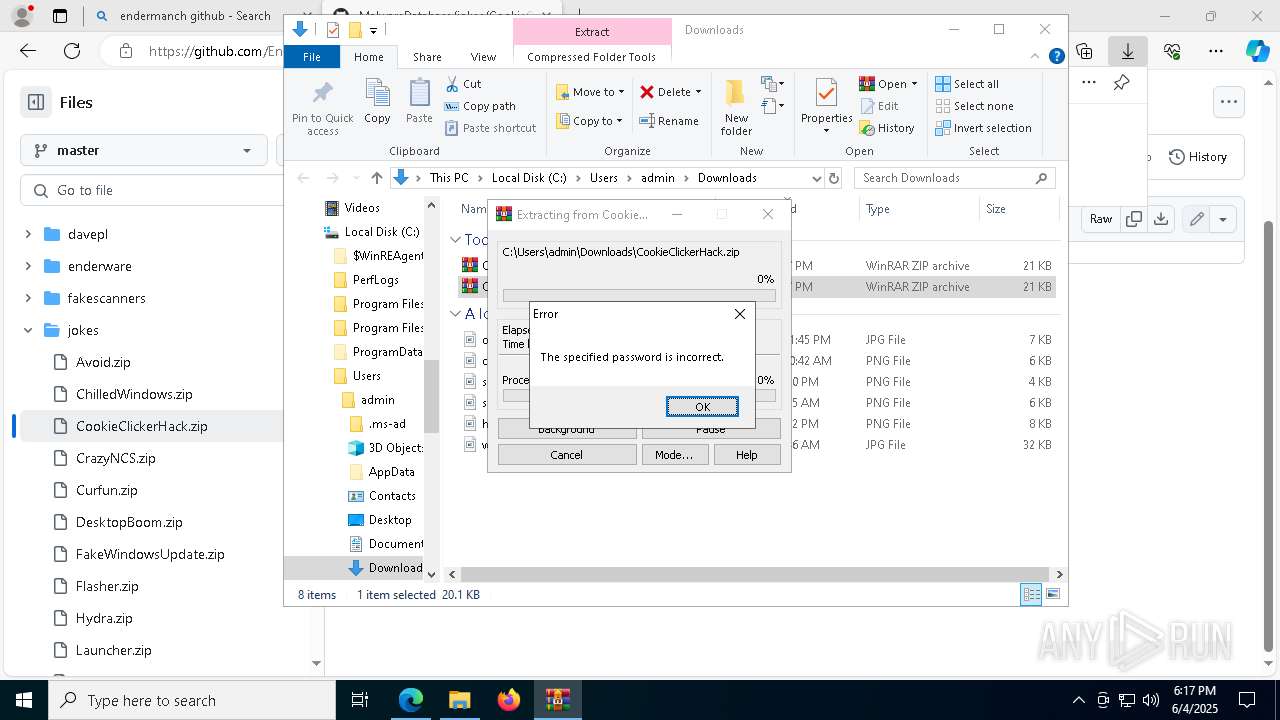
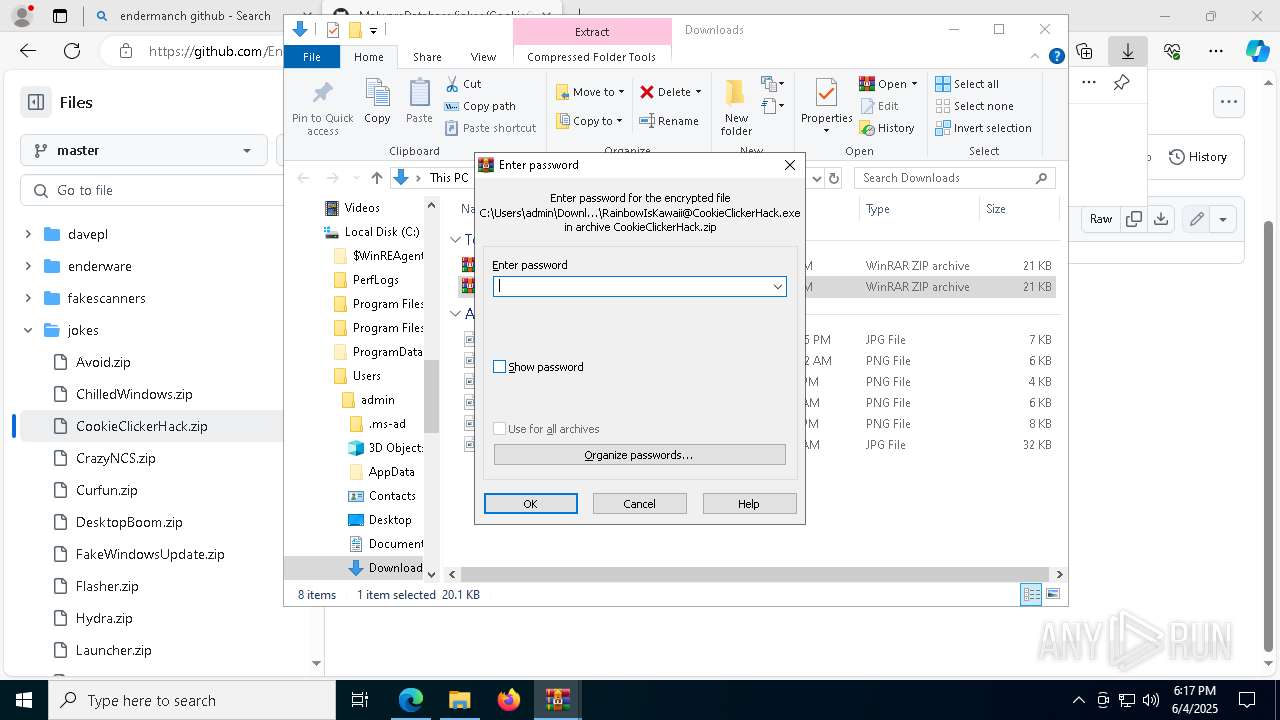
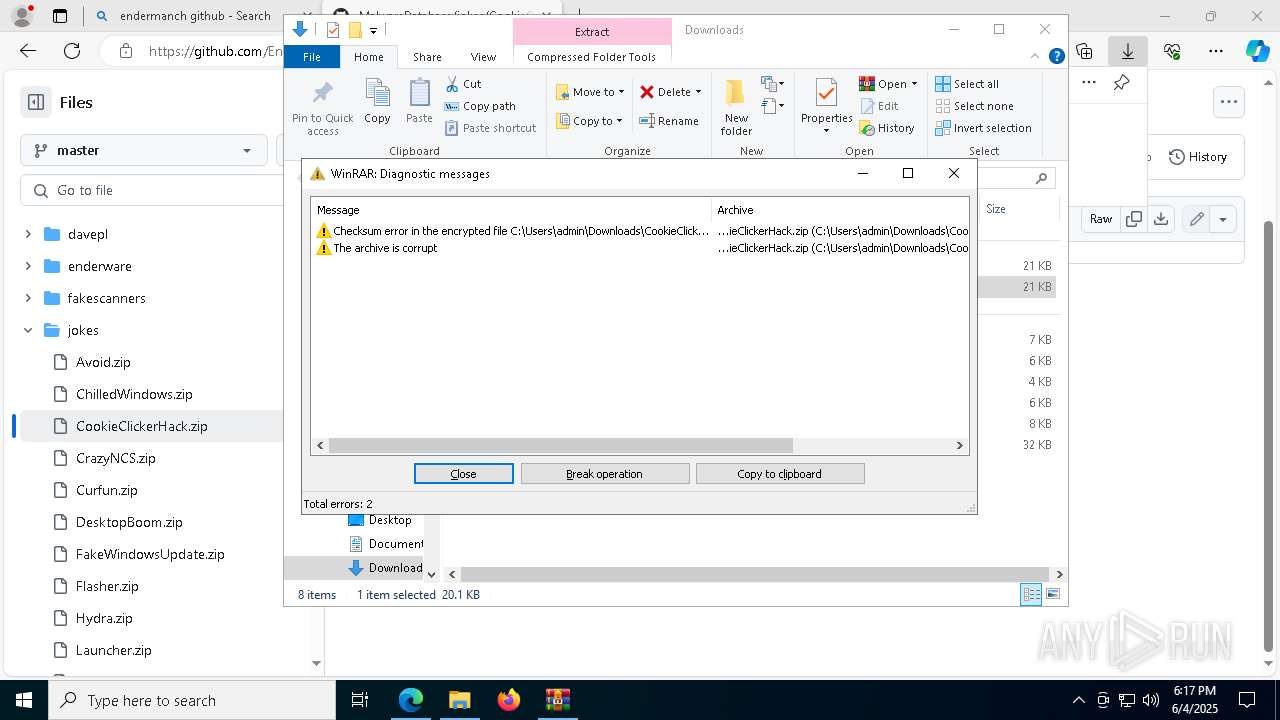
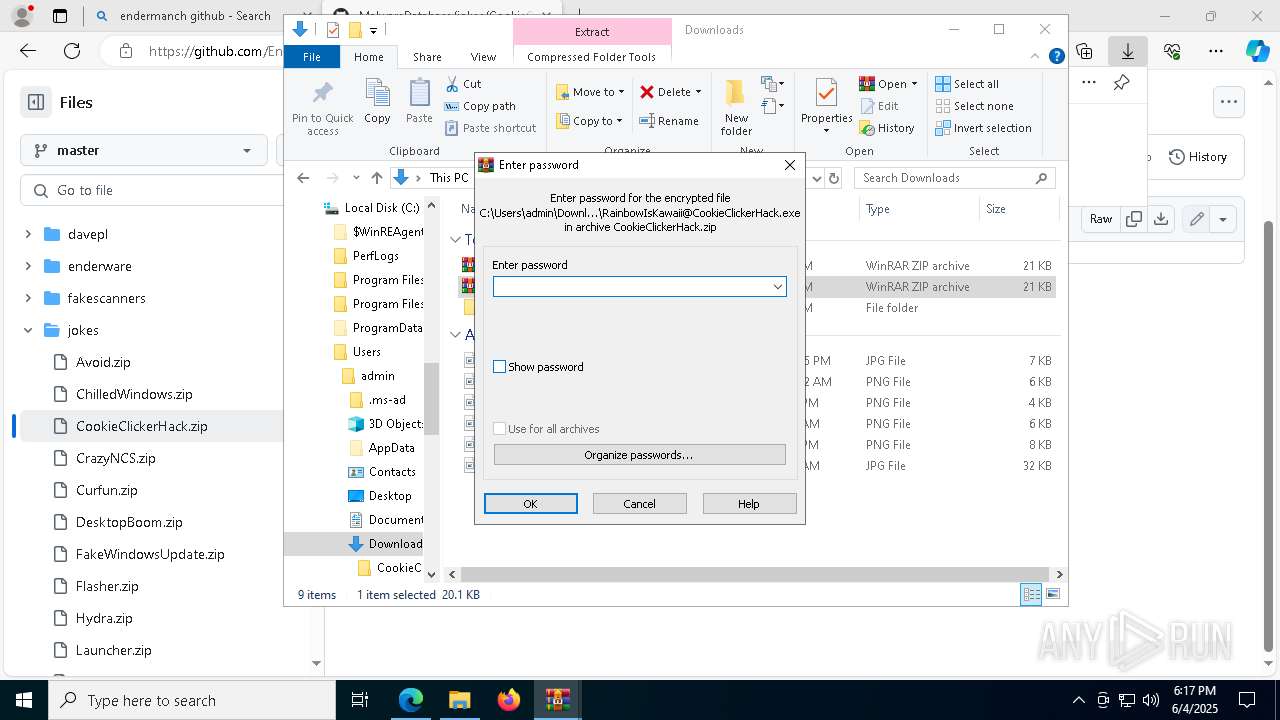
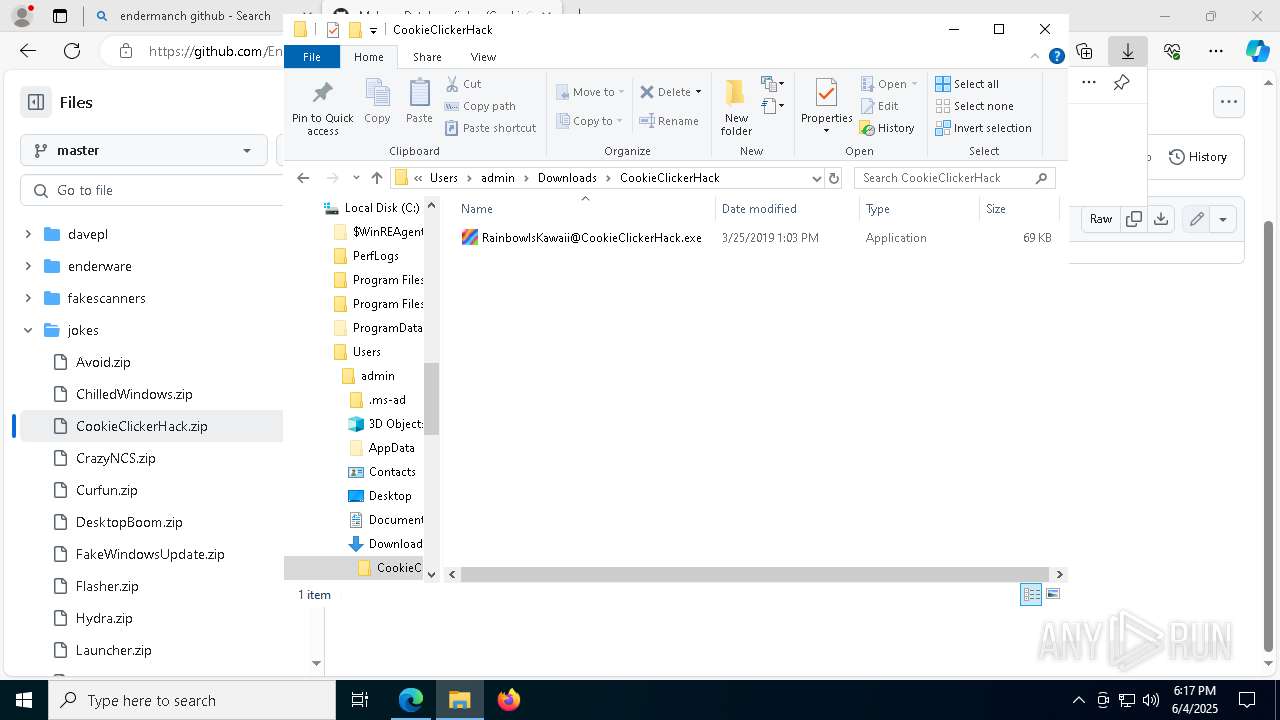
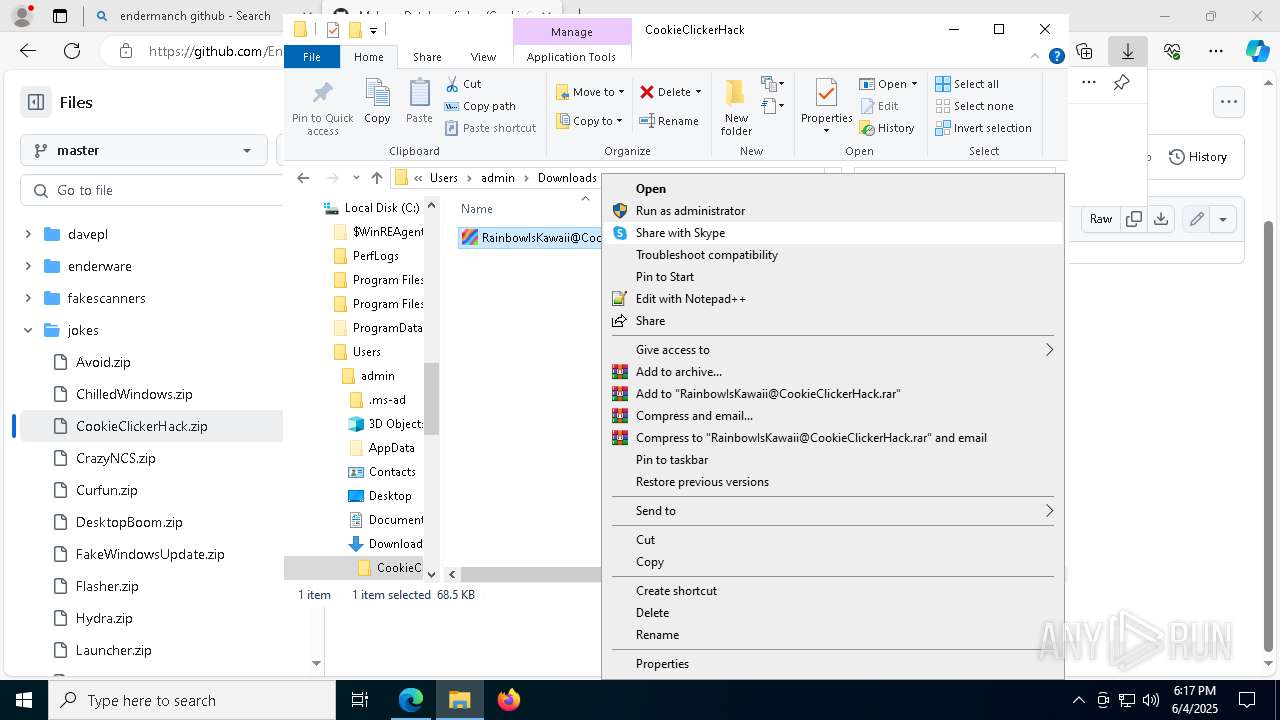
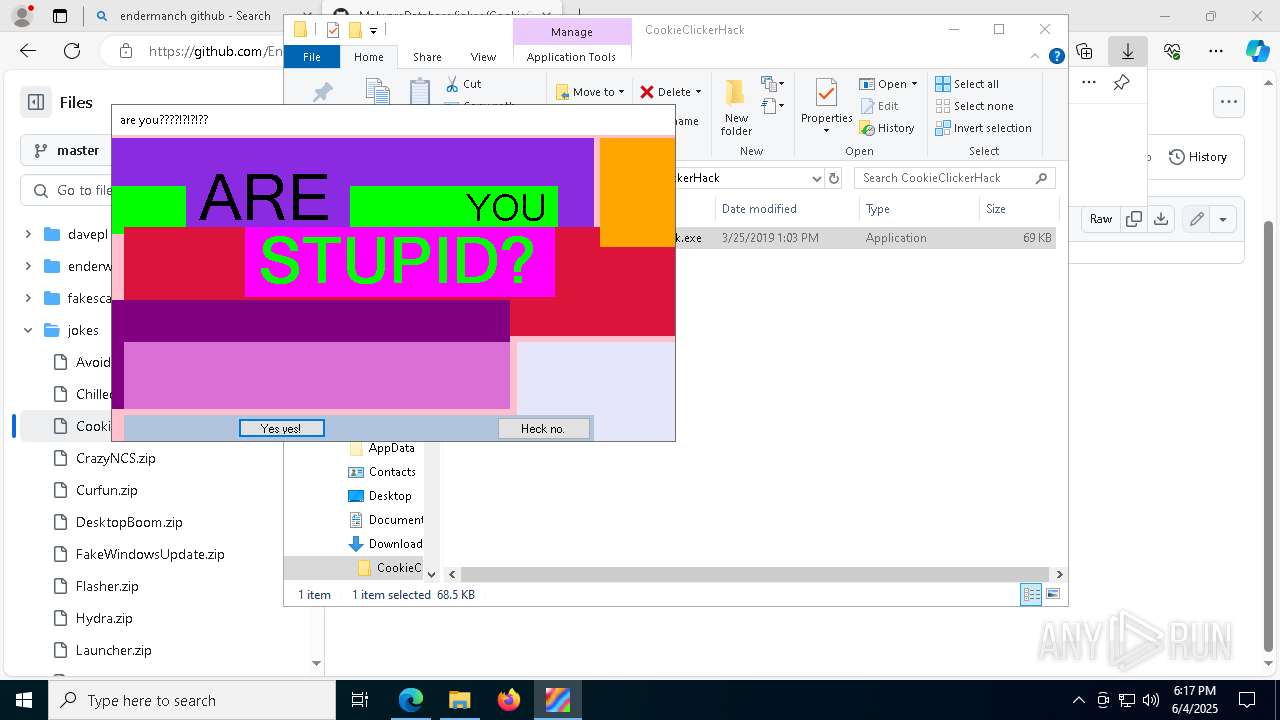
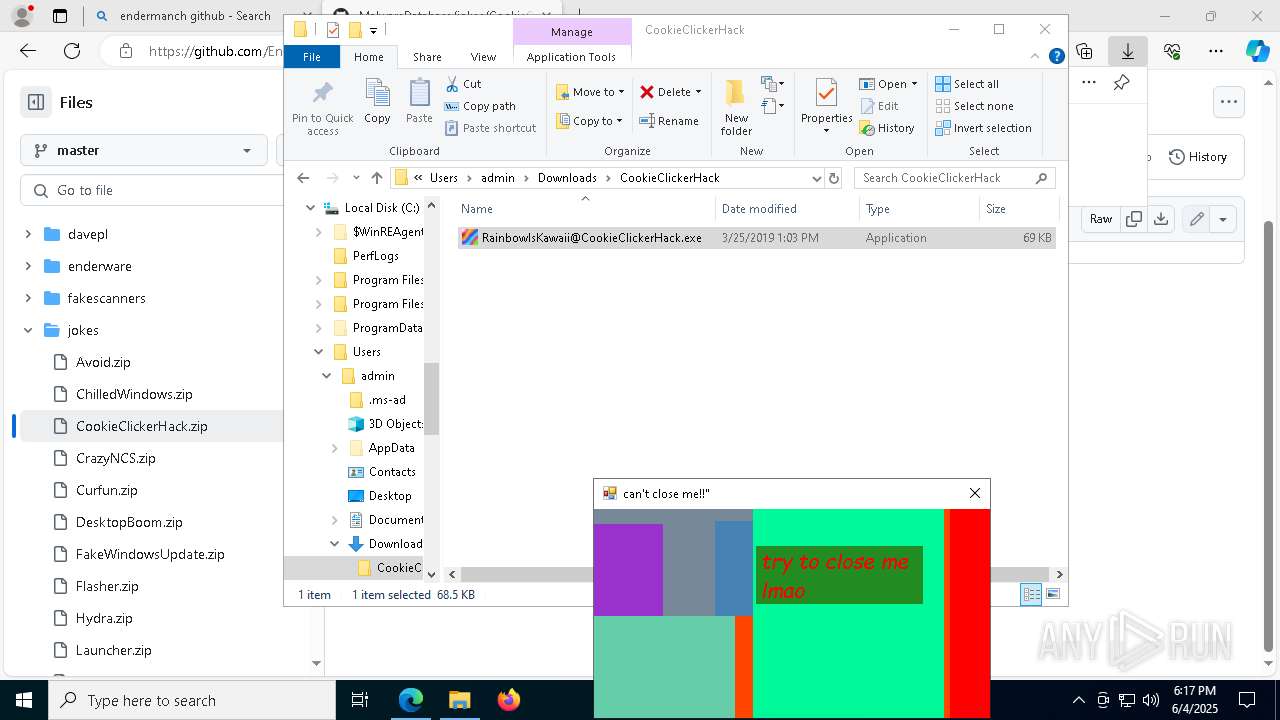
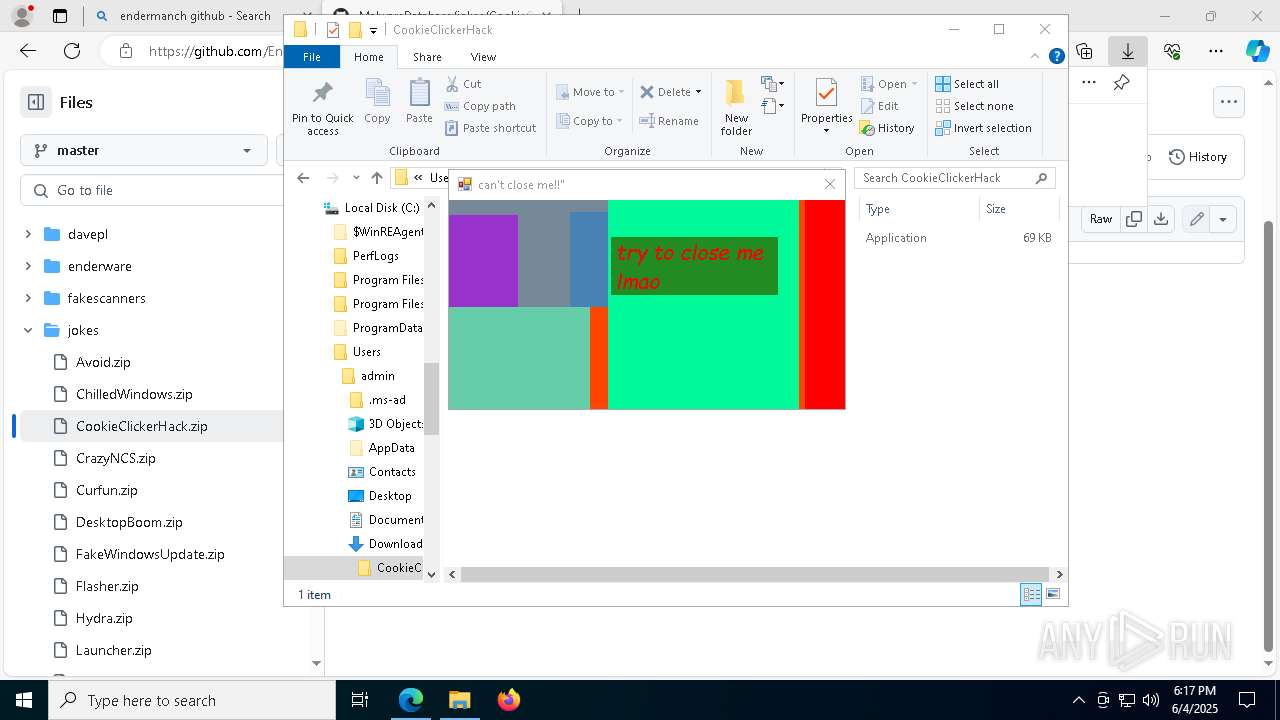
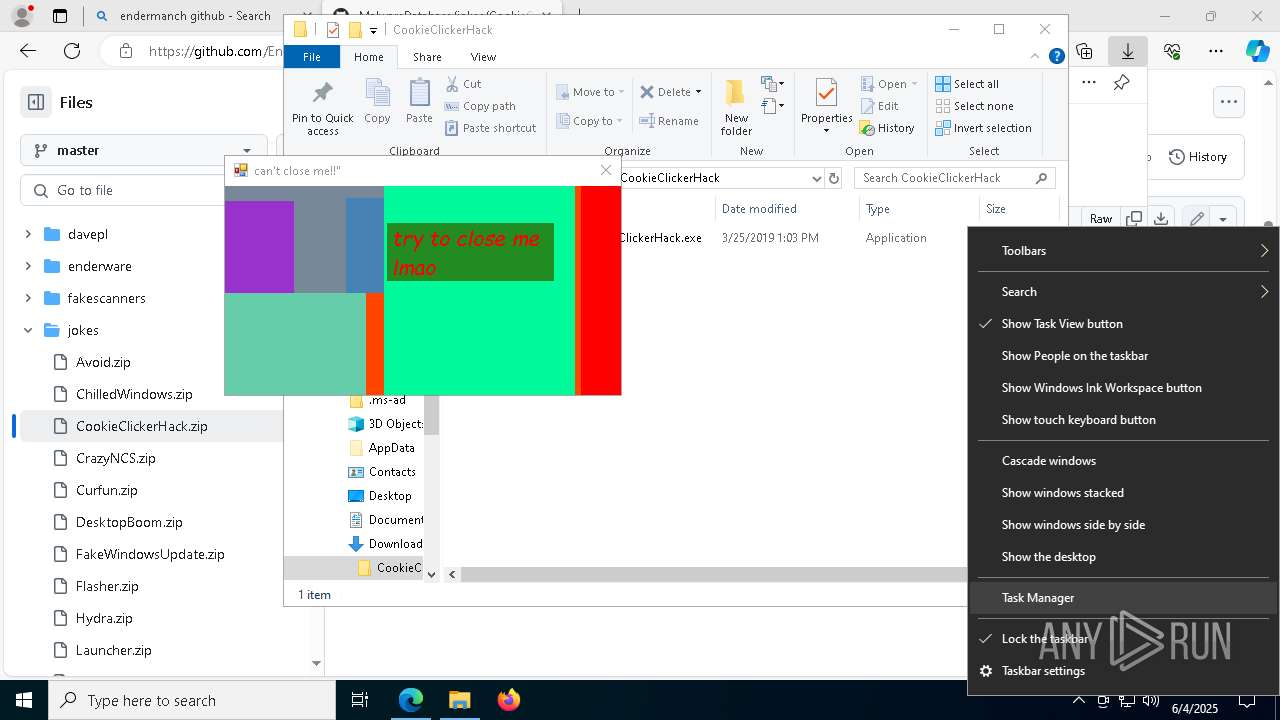
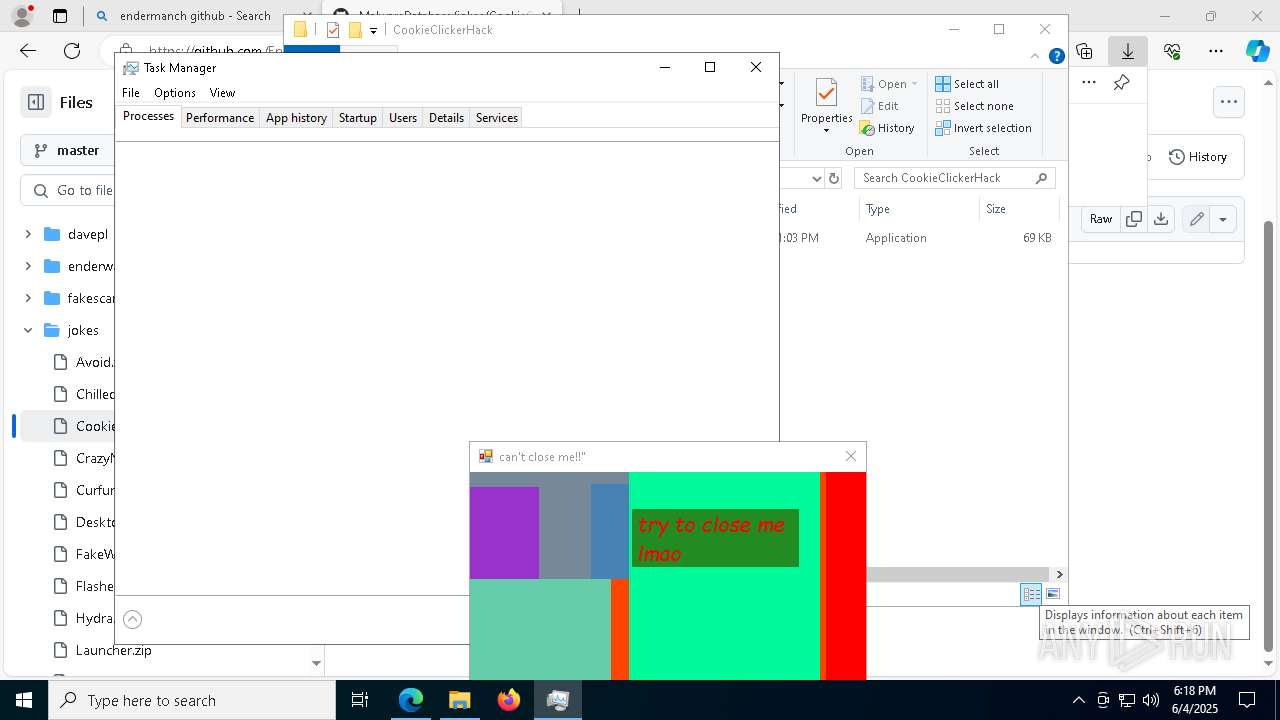
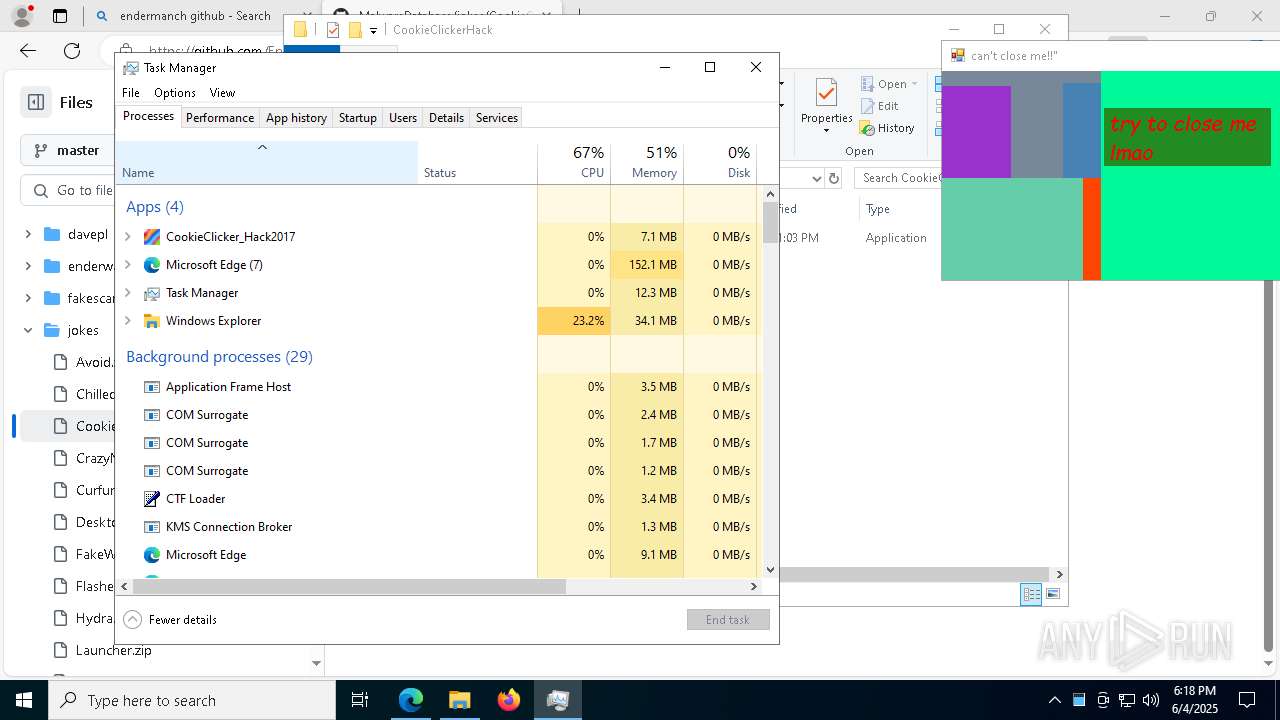
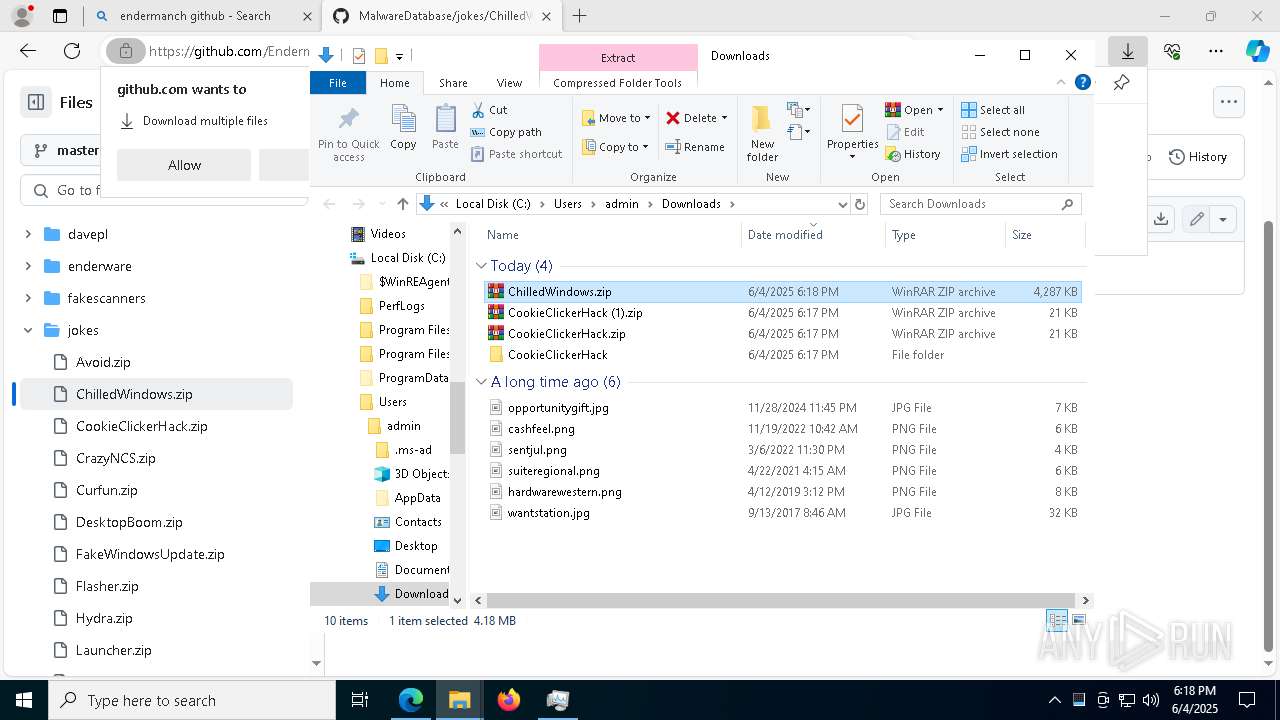
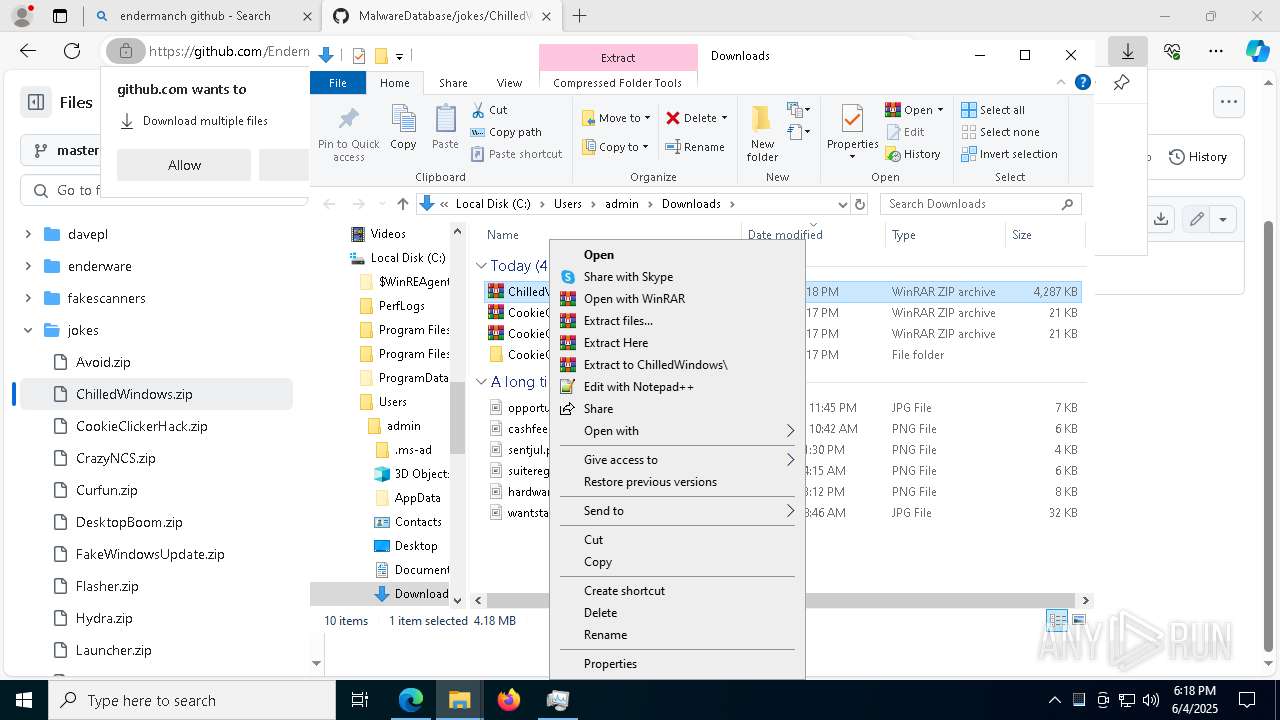
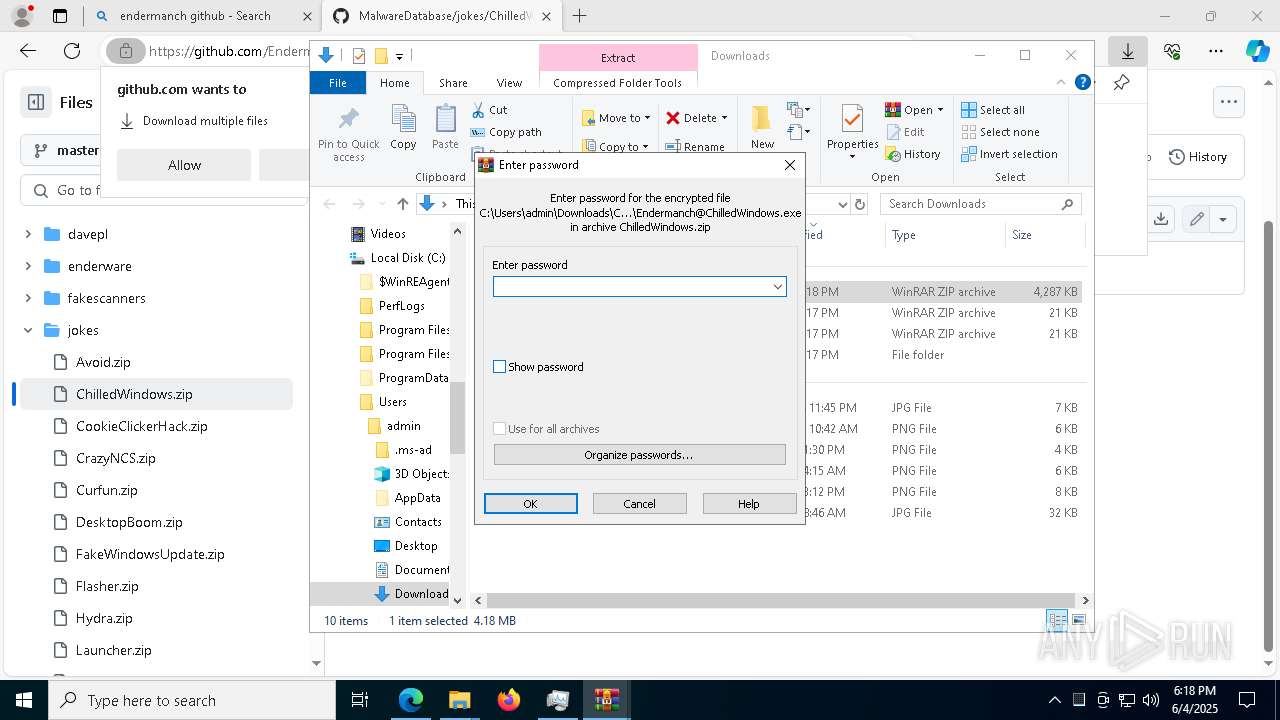
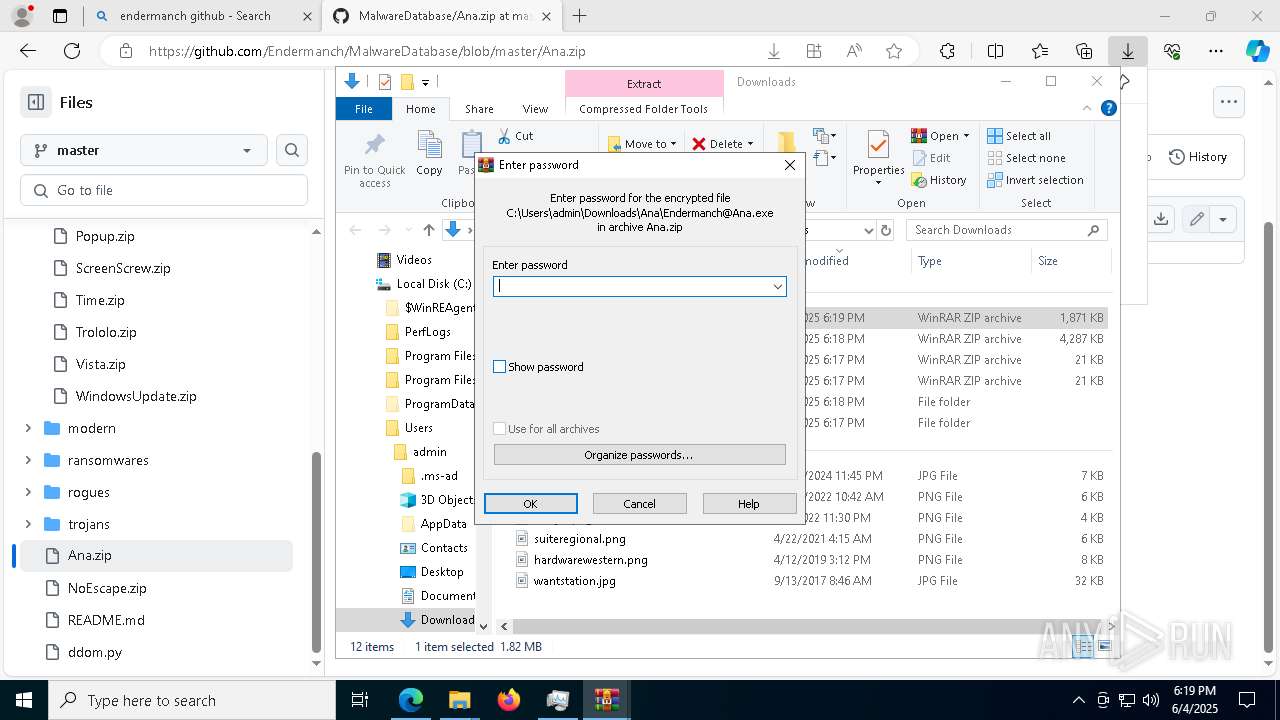
Manual execution by a user
- WinRAR.exe (PID: 4648)
- WinRAR.exe (PID: 4448)
- Endermanch@Ana.exe (PID: 6592)
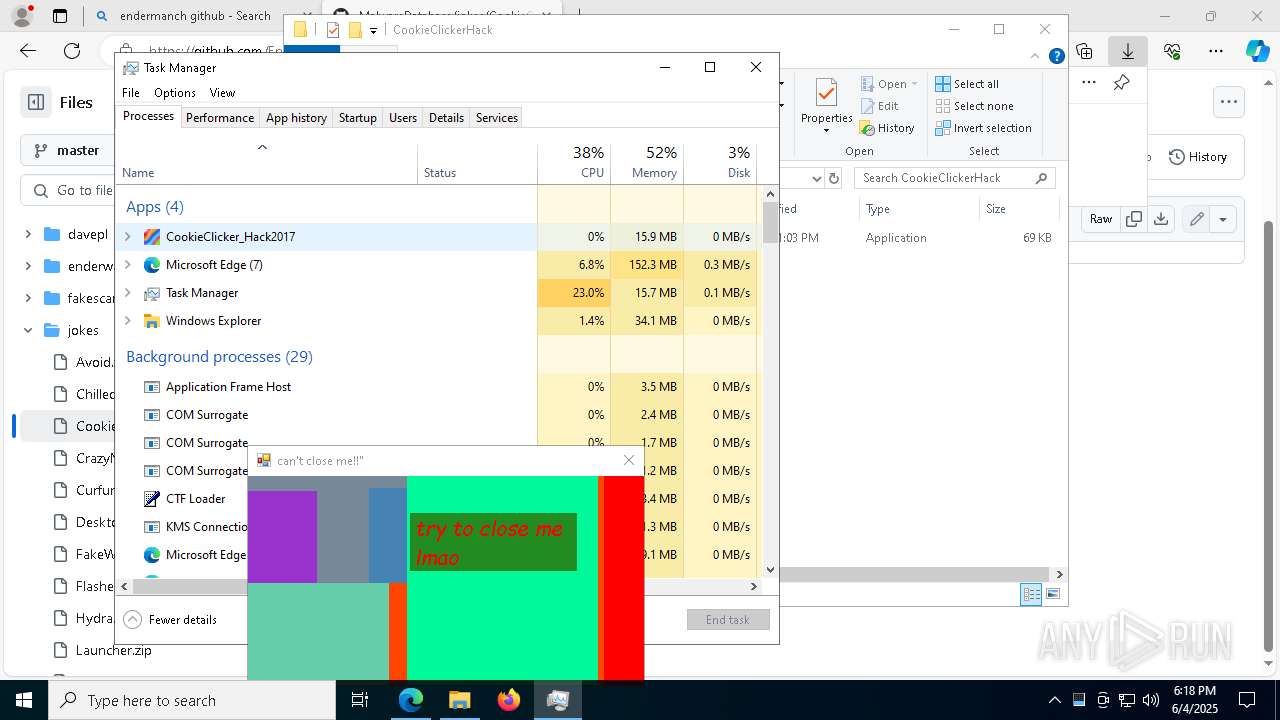
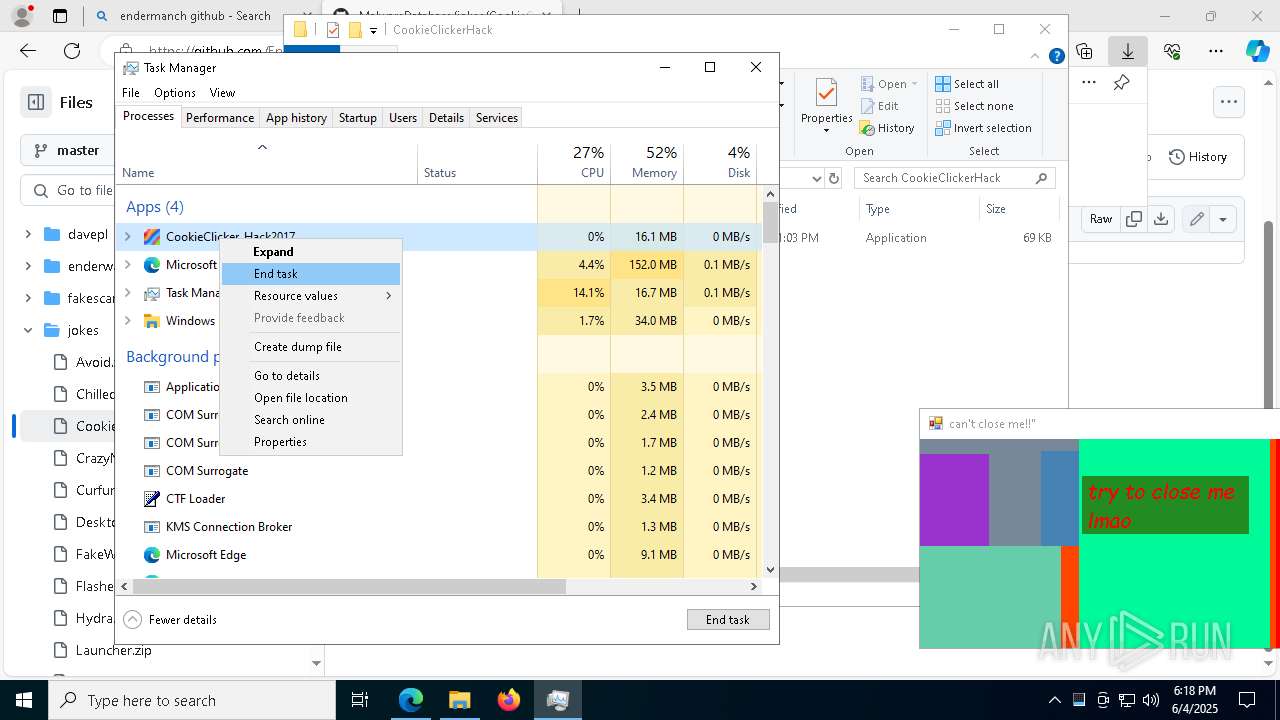
- RainbowIsKawaii@CookieClickerHack.exe (PID: 8136)
- WinRAR.exe (PID: 2780)
- Taskmgr.exe (PID: 6272)
- Taskmgr.exe (PID: 2504)
- Endermanch@ChilledWindows.exe (PID: 8064)
- WinRAR.exe (PID: 2568)
- CCleaner64.exe (PID: 6500)
Reads the software policy settings
- slui.exe (PID: 7360)
The sample compiled with english language support
- Endermanch@Ana.exe (PID: 6592)
- msedge.exe (PID: 6028)
- CCleaner64.exe (PID: 6692)
- CCleaner64.exe (PID: 7088)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4448)
- WinRAR.exe (PID: 2780)
- msedge.exe (PID: 6028)
- WinRAR.exe (PID: 2568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
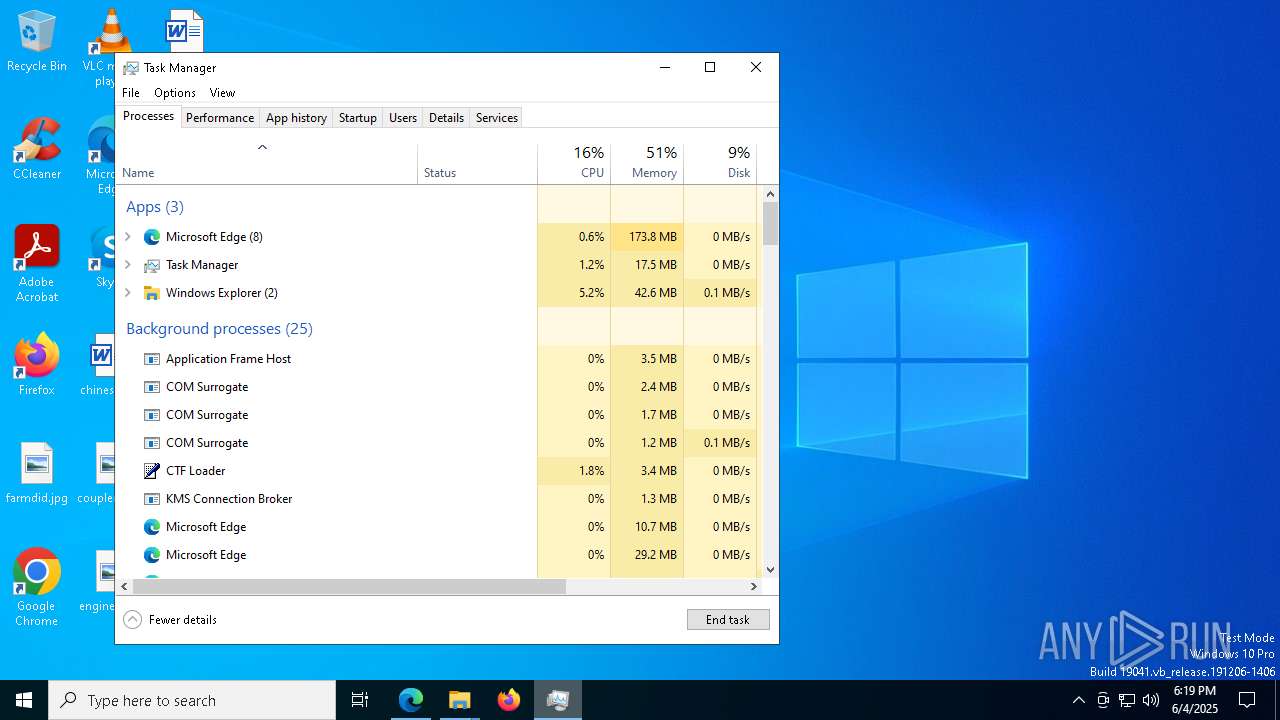
Total processes
354
Monitored processes
90
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=7136 --field-trial-handle=2564,i,7860254475336890888,6309639164013257060,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4080 --field-trial-handle=2564,i,7860254475336890888,6309639164013257060,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 208 | C:\WINDOWS\system32\WerFault.exe -u -p 8064 -s 4640 | C:\Windows\System32\WerFault.exe | — | Endermanch@ChilledWindows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6204 --field-trial-handle=2564,i,7860254475336890888,6309639164013257060,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=8124 --field-trial-handle=2564,i,7860254475336890888,6309639164013257060,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4356 --field-trial-handle=2564,i,7860254475336890888,6309639164013257060,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6032 --field-trial-handle=2564,i,7860254475336890888,6309639164013257060,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6400 --field-trial-handle=2564,i,7860254475336890888,6309639164013257060,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=46 --mojo-platform-channel-handle=7444 --field-trial-handle=2564,i,7860254475336890888,6309639164013257060,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
42 031
Read events
41 709
Write events
250
Delete events
72
Modification events
| (PID) Process: | (1168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1168) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A025B44759952F00 | |||
| (PID) Process: | (1168) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C33CBC4759952F00 | |||
| (PID) Process: | (1168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656050 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6243CE3D-7843-41D3-ACFE-984B51AFE3FE} | |||
| (PID) Process: | (1168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656050 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {713F76B2-06A0-4AED-9B92-2A23CF669020} | |||
| (PID) Process: | (1168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656050 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {417725F6-6930-4502-9EBD-019B818DC60D} | |||
| (PID) Process: | (1168) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\656050 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5B254FC5-E658-4C38-AC2E-9E484FD73865} | |||
Executable files
16
Suspicious files
799
Text files
110
Unknown types
113
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11f4fc.TMP | — | |
MD5:— | SHA256:— | |||
| 1168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11f4fc.TMP | — | |
MD5:— | SHA256:— | |||
| 1168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11f4fc.TMP | — | |
MD5:— | SHA256:— | |||
| 1168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11f51b.TMP | — | |
MD5:— | SHA256:— | |||
| 1168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11f51b.TMP | — | |
MD5:— | SHA256:— | |||
| 1168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1168 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11f53a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
161
DNS requests
154
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6800 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7448 | svchost.exe | HEAD | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1749089966&P2=404&P3=2&P4=b3VvZFNxJnVX7QDSesmYh5d4AZb8%2fhb3owVCtLwJIDUQNz5Nz1ElTmkZT%2b36RvTdujNmQ931NtG62p%2b5v3f6Yg%3d%3d | unknown | — | — | whitelisted |
7448 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1749089966&P2=404&P3=2&P4=b3VvZFNxJnVX7QDSesmYh5d4AZb8%2fhb3owVCtLwJIDUQNz5Nz1ElTmkZT%2b36RvTdujNmQ931NtG62p%2b5v3f6Yg%3d%3d | unknown | — | — | whitelisted |
6800 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7448 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1749089966&P2=404&P3=2&P4=b3VvZFNxJnVX7QDSesmYh5d4AZb8%2fhb3owVCtLwJIDUQNz5Nz1ElTmkZT%2b36RvTdujNmQ931NtG62p%2b5v3f6Yg%3d%3d | unknown | — | — | whitelisted |
7448 | svchost.exe | GET | 206 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1749089966&P2=404&P3=2&P4=b3VvZFNxJnVX7QDSesmYh5d4AZb8%2fhb3owVCtLwJIDUQNz5Nz1ElTmkZT%2b36RvTdujNmQ931NtG62p%2b5v3f6Yg%3d%3d | unknown | — | — | whitelisted |
7448 | svchost.exe | HEAD | 200 | 208.89.74.19:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a480f387-b8f7-4ebb-b61a-a51d3b7fe260?P1=1749631545&P2=404&P3=2&P4=D%2bus7aM3lZIvOCc2i26SA4daoa2zWWxOXdwOMirXOBJghDkKhMI208ZnXtIVep4mhB%2fbvfK%2bow2K78fAIpSbUA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7328 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
7964 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1168 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7488 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7488 | msedge.exe | 2.19.96.91:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7488 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.bing.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
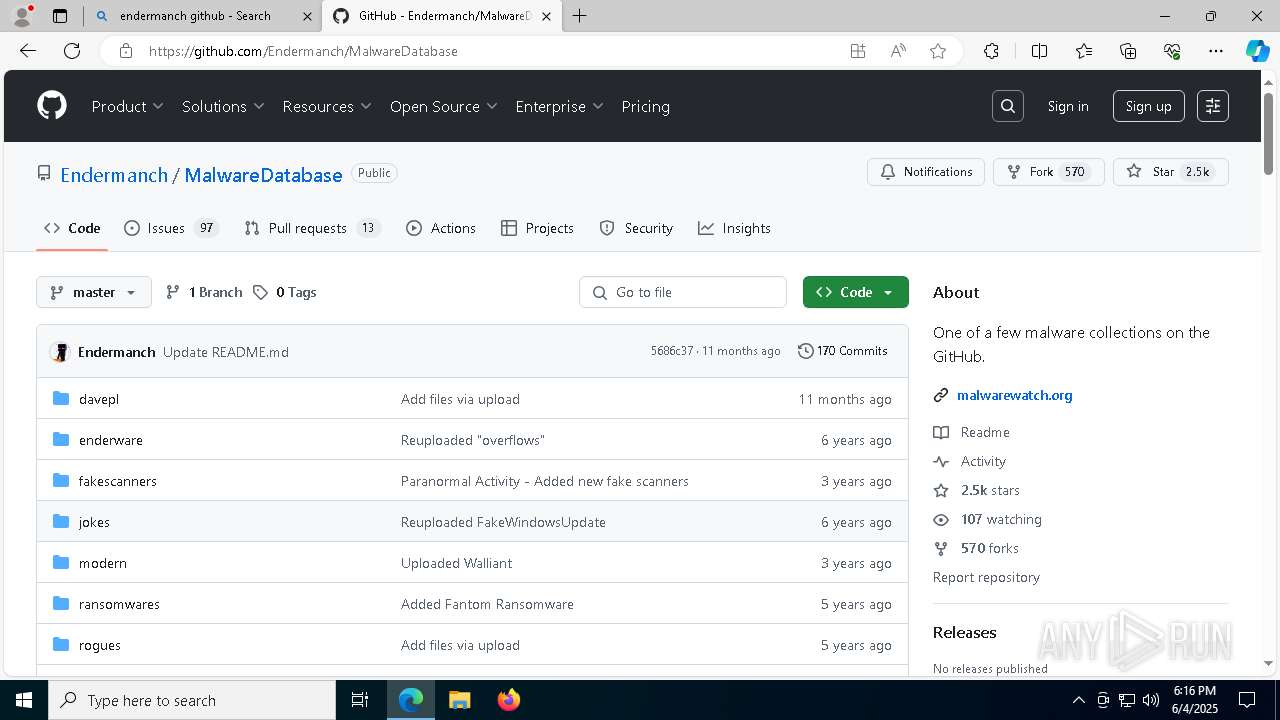
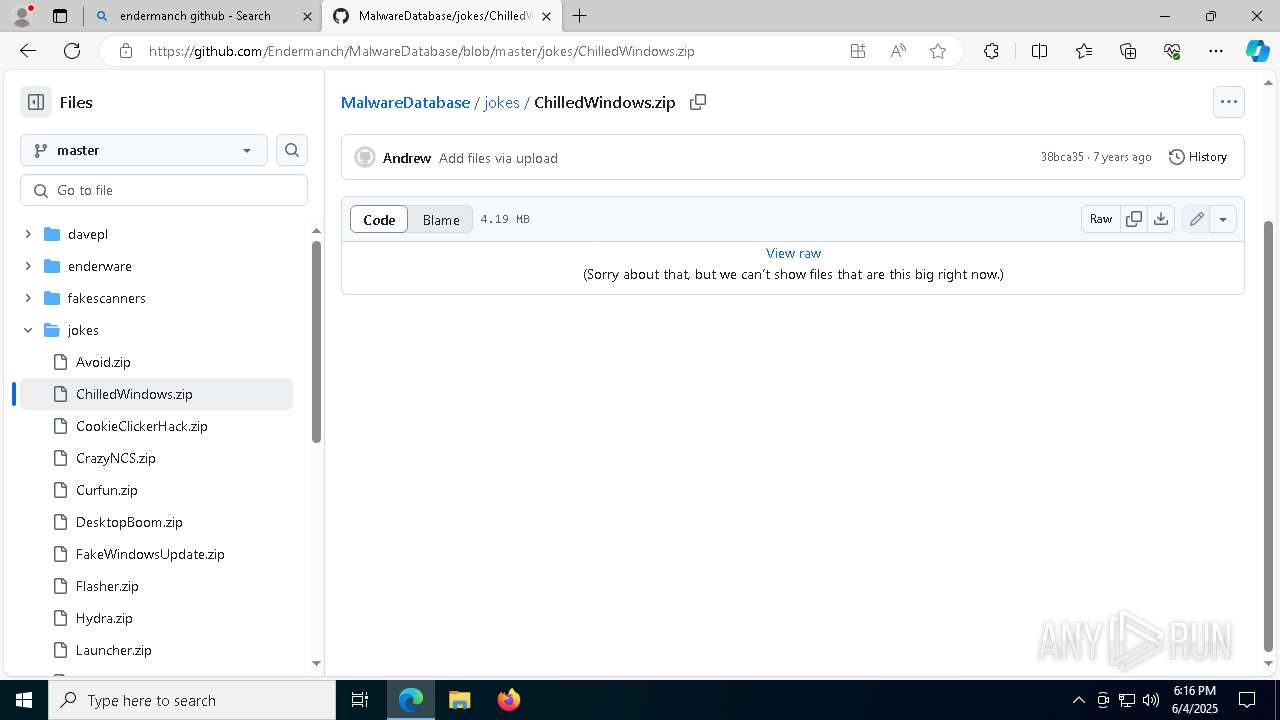
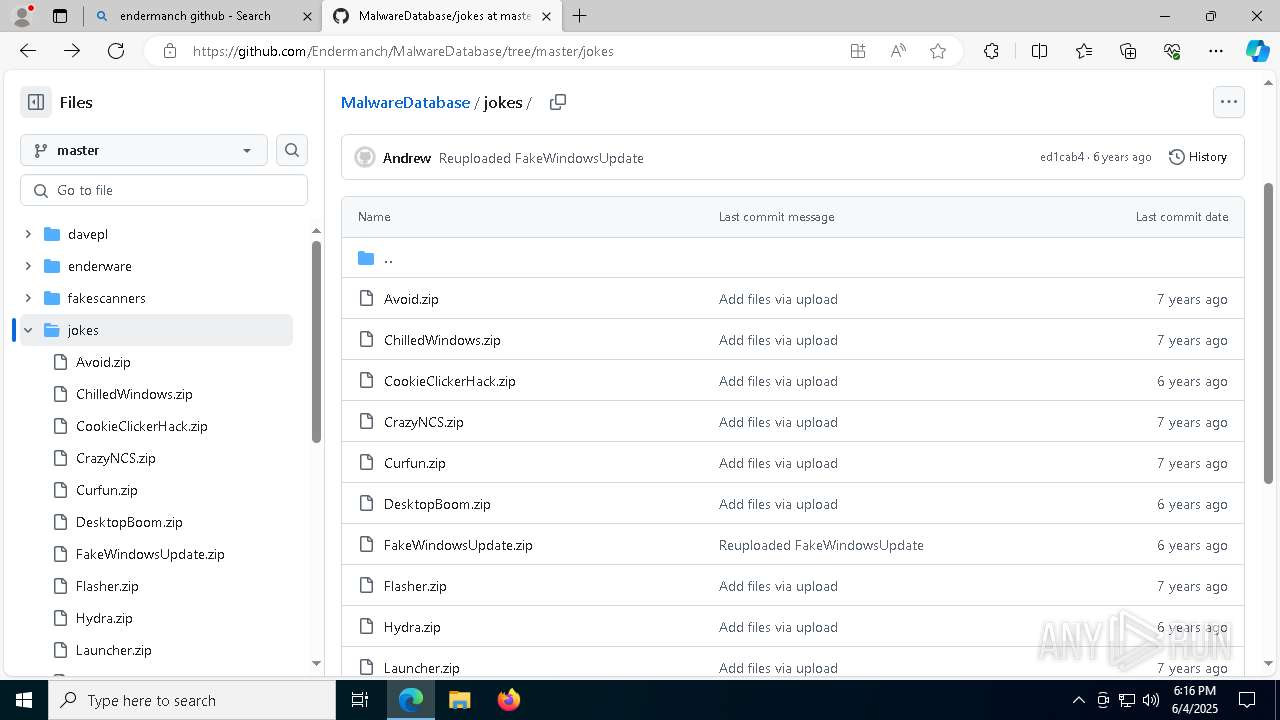
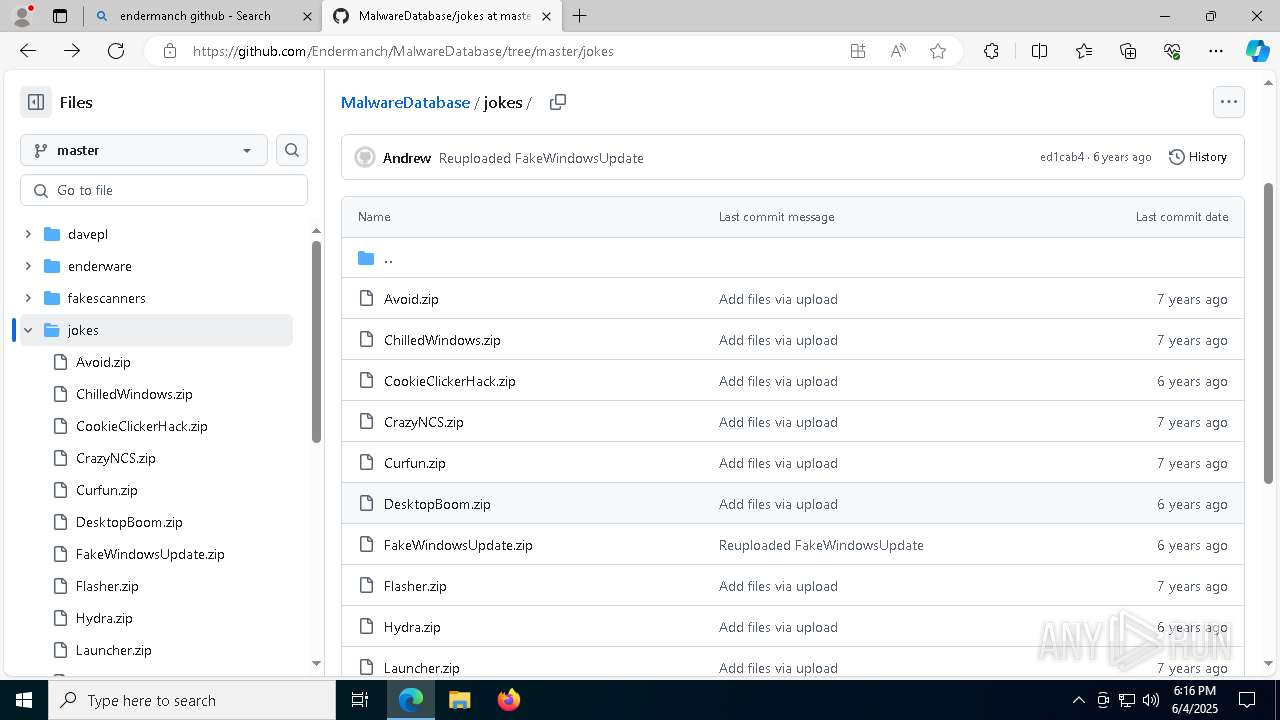
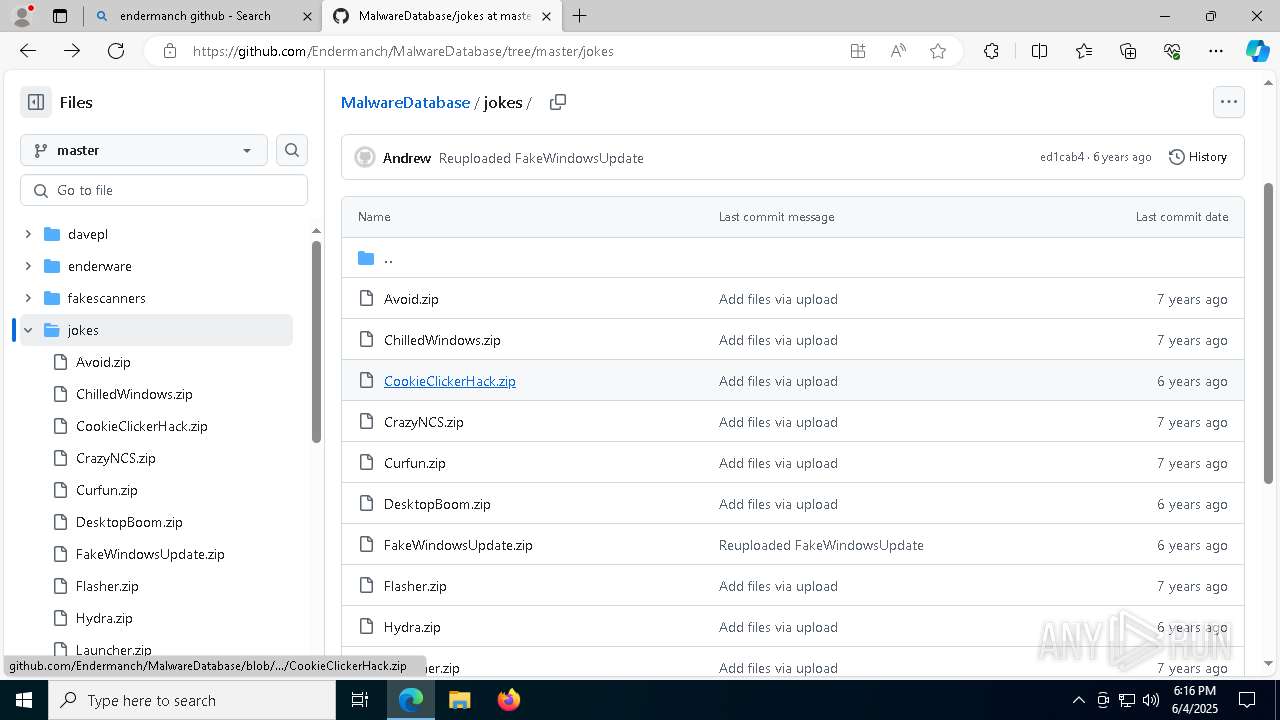
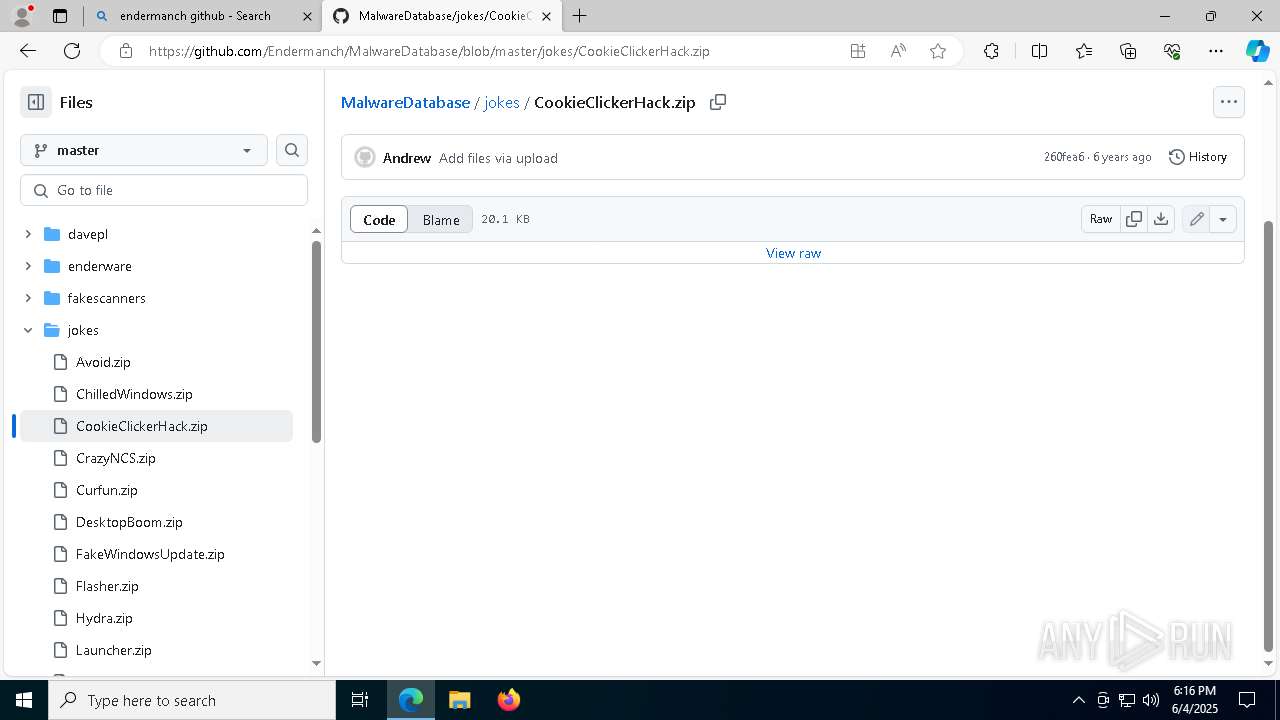
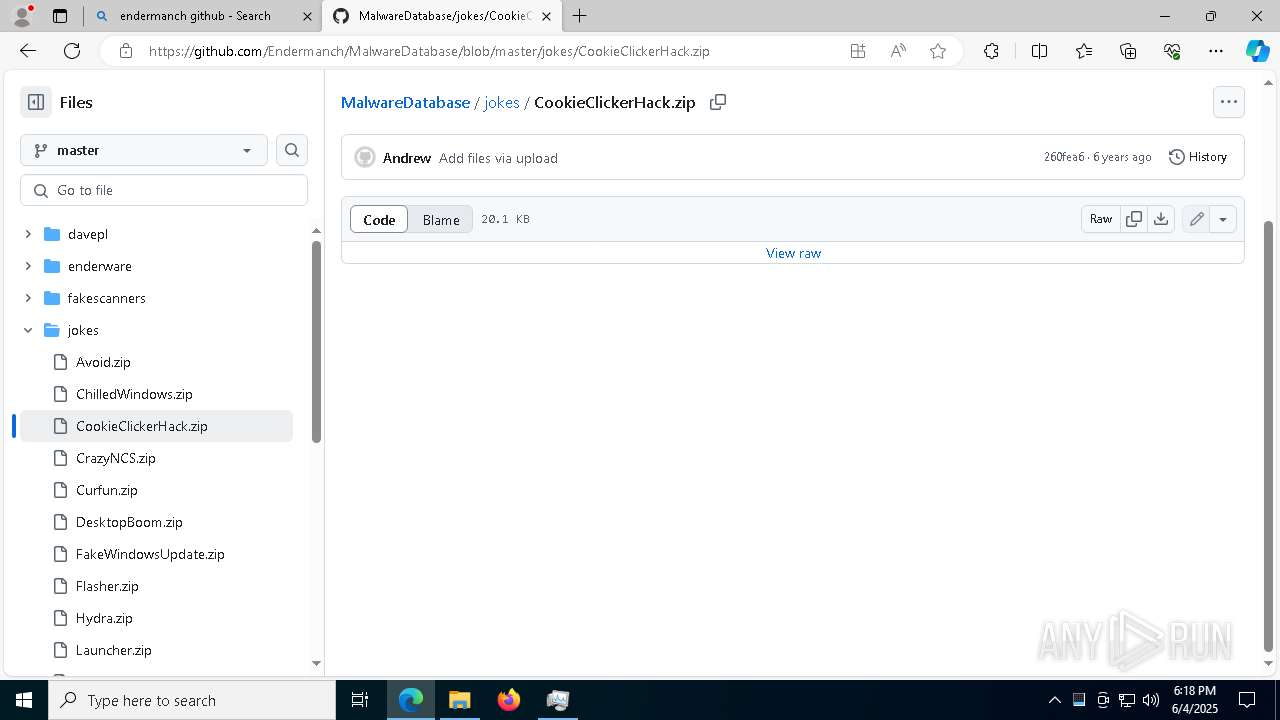
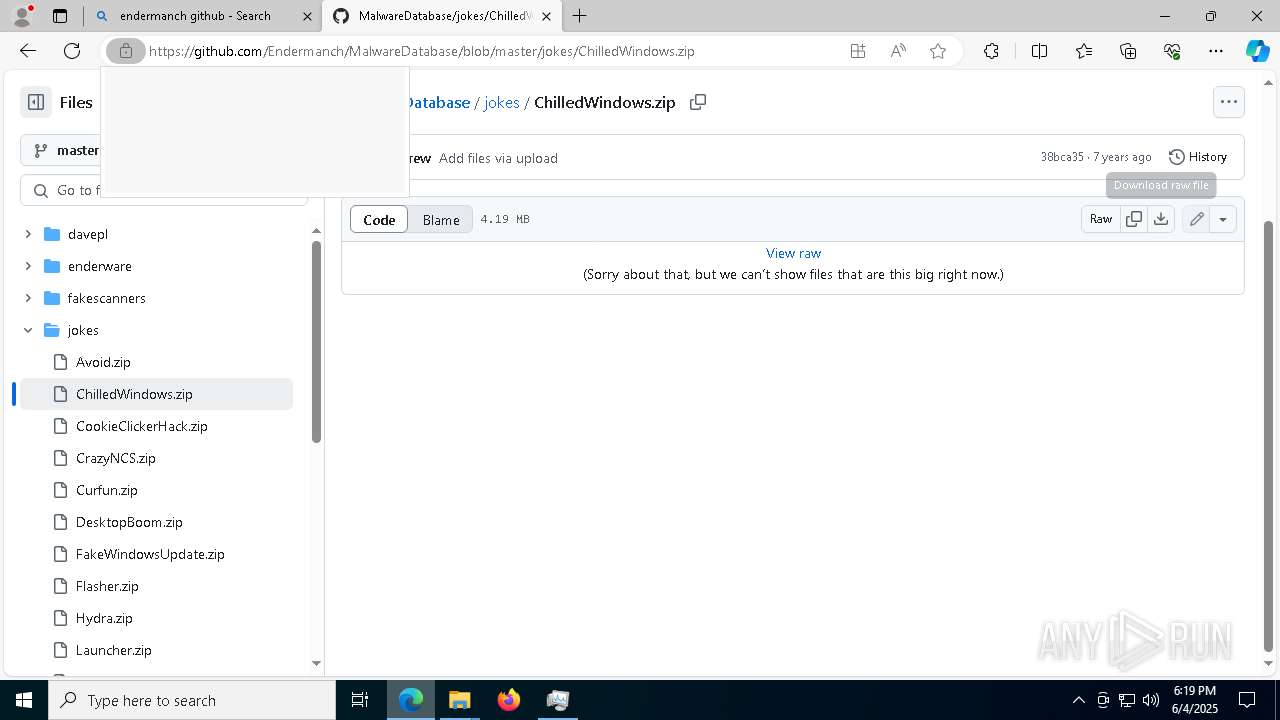
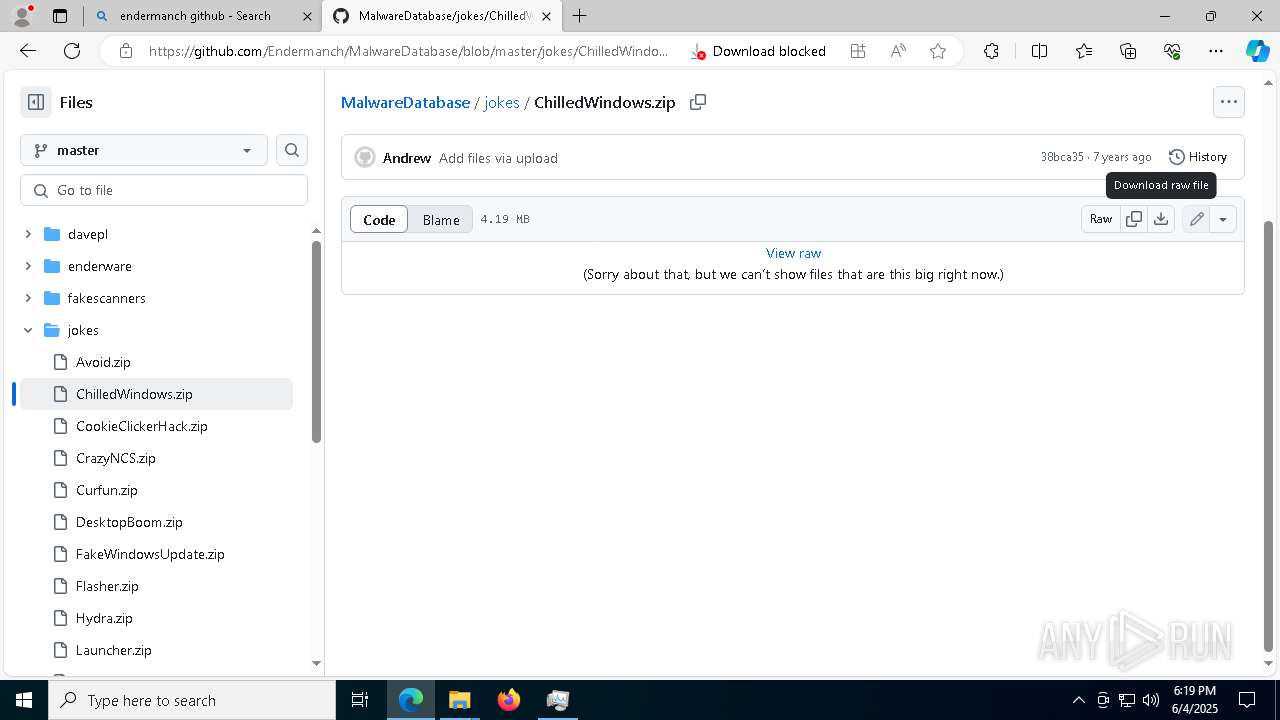
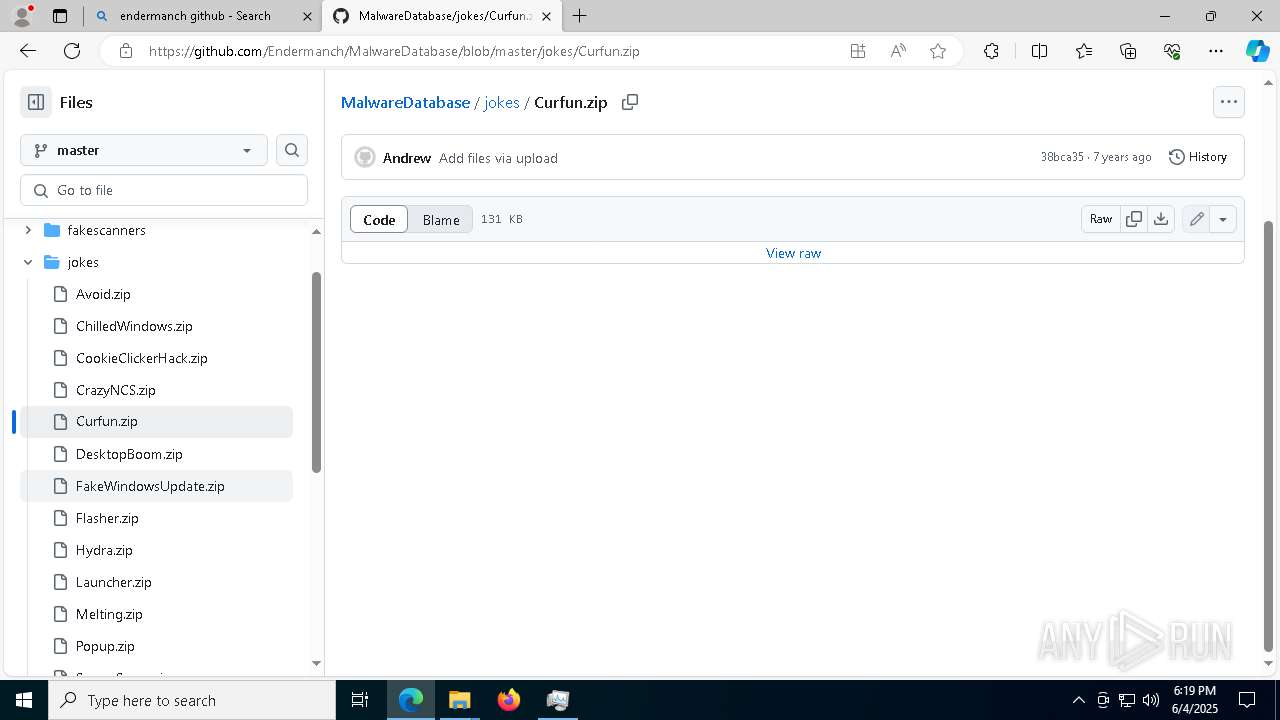
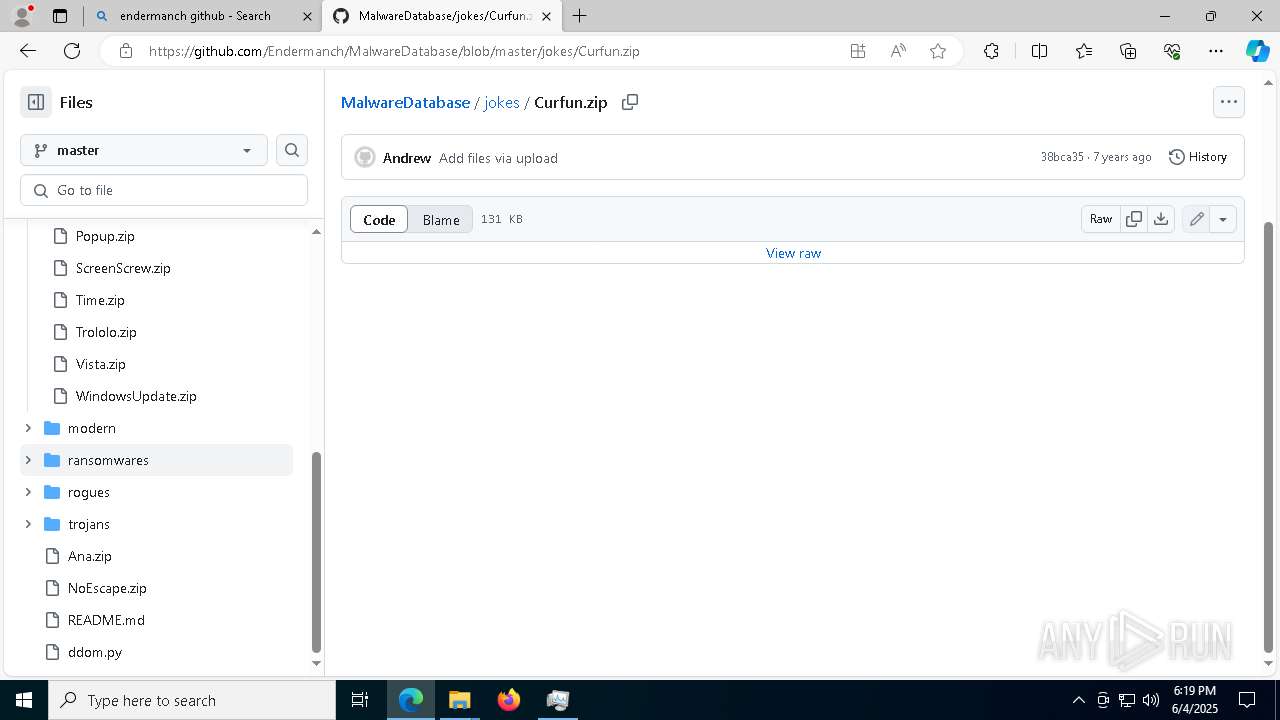
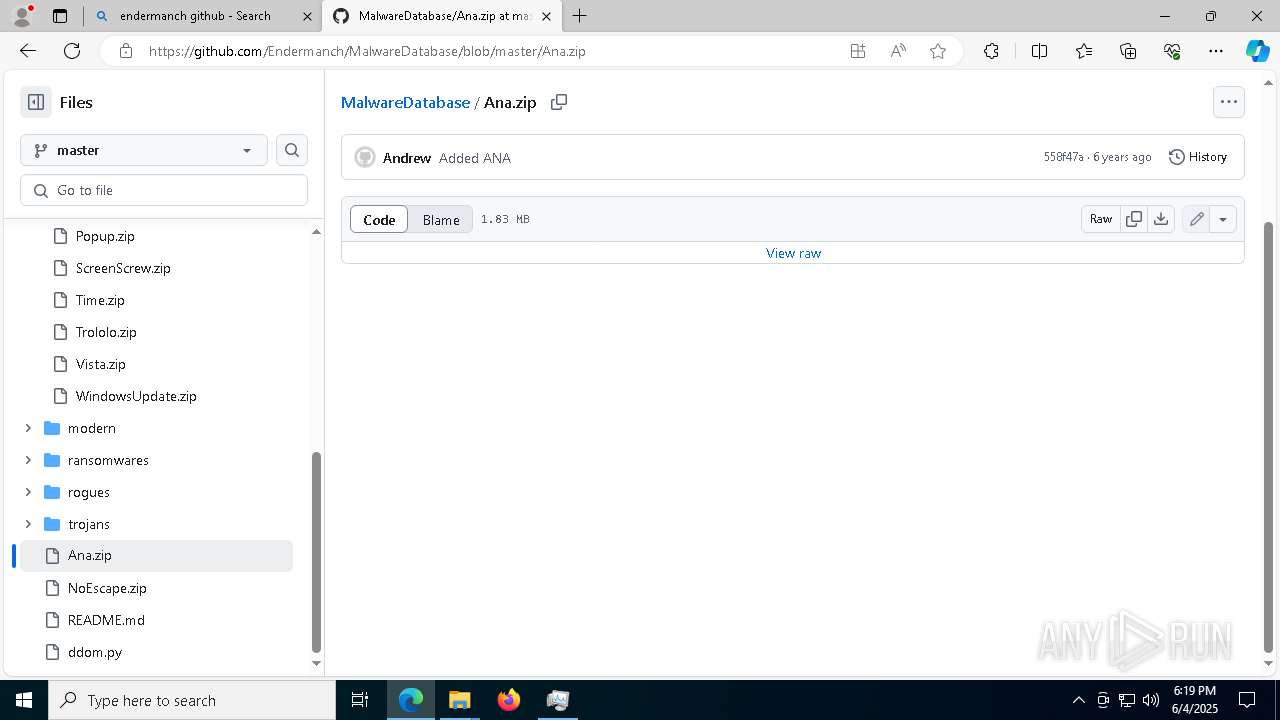
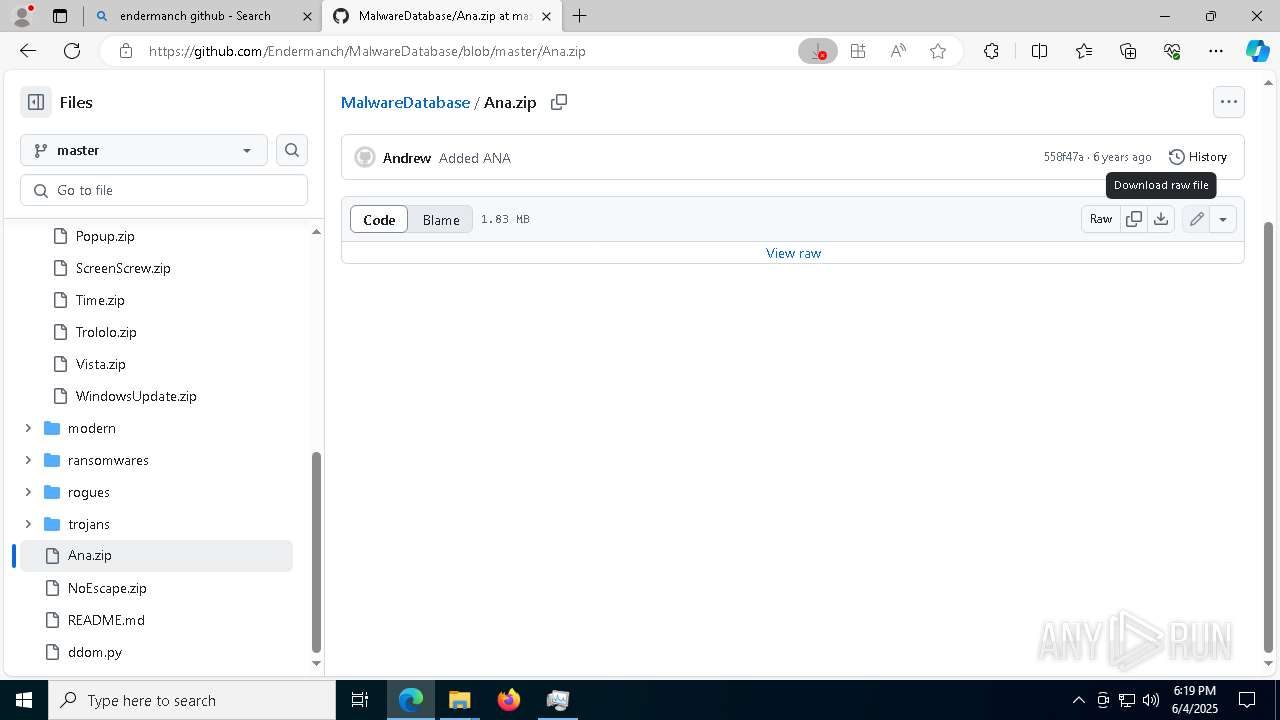
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7488 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1240 | DB.EXE | Malware Command and Control Activity Detected | ET MALWARE Ponmocup C2 Post-infection Checkin |
1240 | DB.EXE | A Network Trojan was detected | ET MALWARE Spoofed MSIE 8 User-Agent Likely Ponmocup |
1240 | DB.EXE | Malware Command and Control Activity Detected | ET MALWARE Ponmocup C2 Post-infection Checkin |
1240 | DB.EXE | A Network Trojan was detected | ET MALWARE Spoofed MSIE 8 User-Agent Likely Ponmocup |