| File name: | helper.exe |
| Full analysis: | https://app.any.run/tasks/cbd57633-004f-4e58-b974-d300605fbeb9 |
| Verdict: | Malicious activity |
| Analysis date: | June 30, 2024, 21:44:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E3F2F378468FB94E45ED6A20AD1FA451 |
| SHA1: | A5865838873E6F51421FE2B7F467EE9867779ED5 |
| SHA256: | 0AE1235B400D4B04B27ABAD5EFDDB58EDEAC732C24590AE74749D98943600C3A |
| SSDEEP: | 1536:/maCszB5r41TrPnMaqpqIZZZZZNOh5bMw2EndJyMjnx4HnFxbj/1L6ogziEapms:/R1aTrPnVqpNOh5Hpdt12VO/OEapb |
MALICIOUS
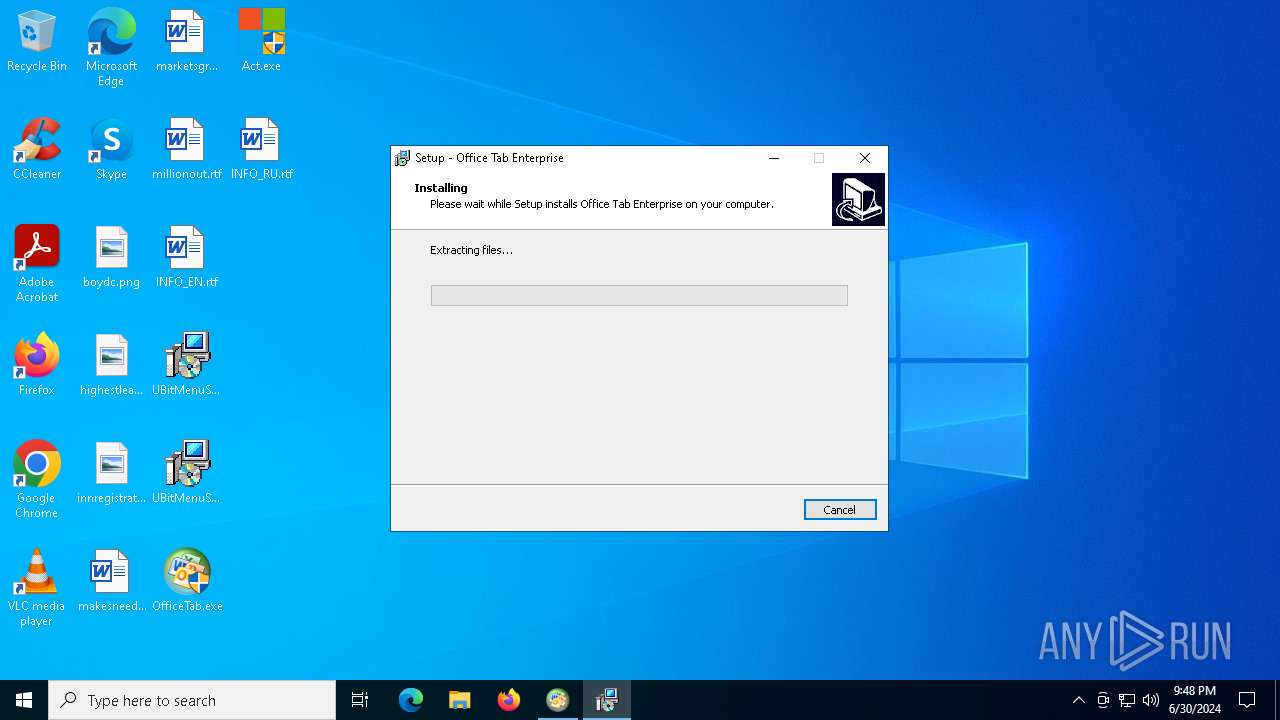
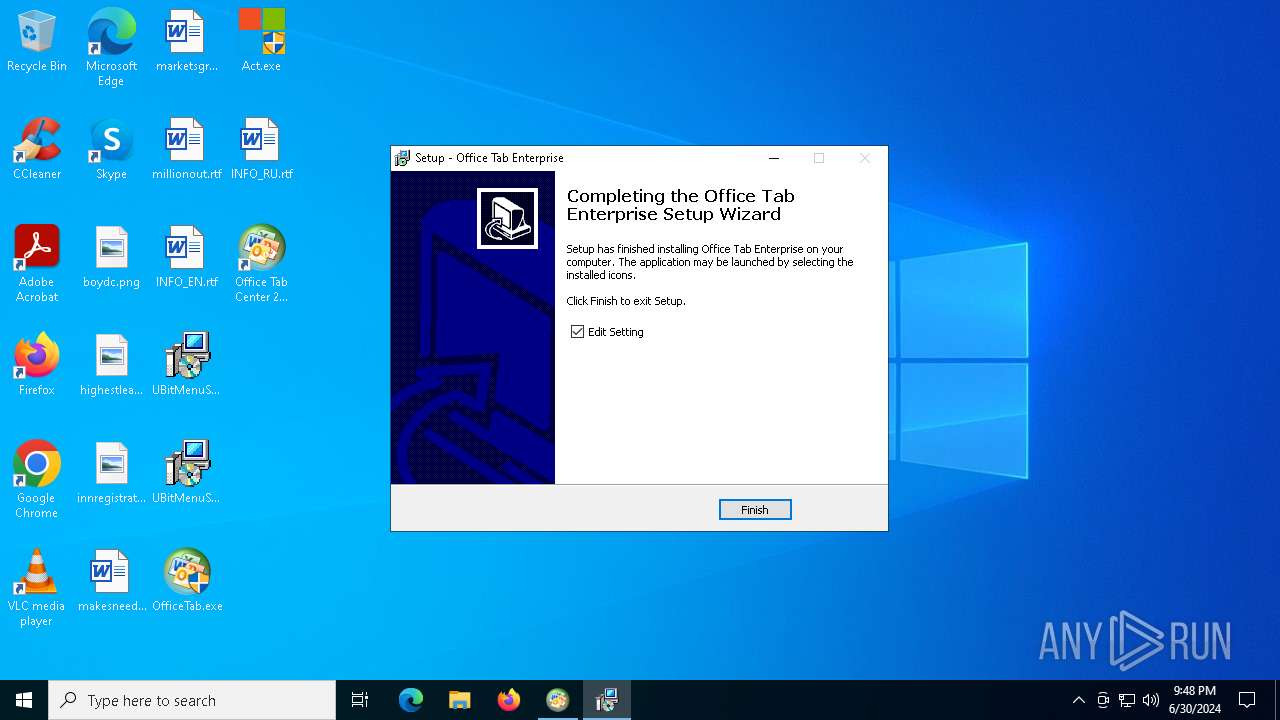
Drops the executable file immediately after the start
- helper.exe (PID: 1592)
- package.exe (PID: 4912)
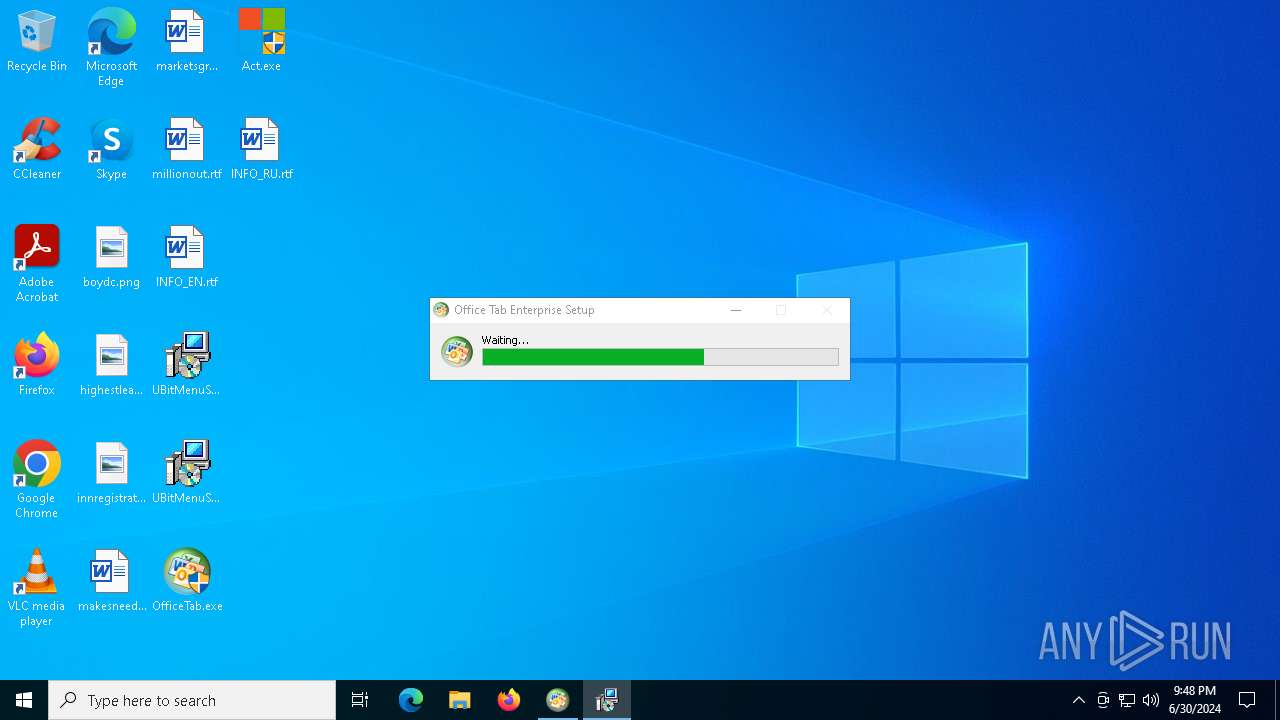
- OfficeTab.exe (PID: 4324)
- package.tmp (PID: 188)
Registers / Runs the DLL via REGSVR32.EXE
- package.tmp (PID: 188)
SUSPICIOUS
Reads security settings of Internet Explorer
- OfficeTab.exe (PID: 4324)
Executable content was dropped or overwritten
- OfficeTab.exe (PID: 4324)
- package.exe (PID: 4912)
- package.tmp (PID: 188)
Reads the Windows owner or organization settings
- package.tmp (PID: 188)
Adds/modifies Windows certificates
- package.tmp (PID: 188)
Process drops legitimate windows executable
- package.tmp (PID: 188)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1960)
- regsvr32.exe (PID: 2064)
- regsvr32.exe (PID: 5316)
- regsvr32.exe (PID: 2308)
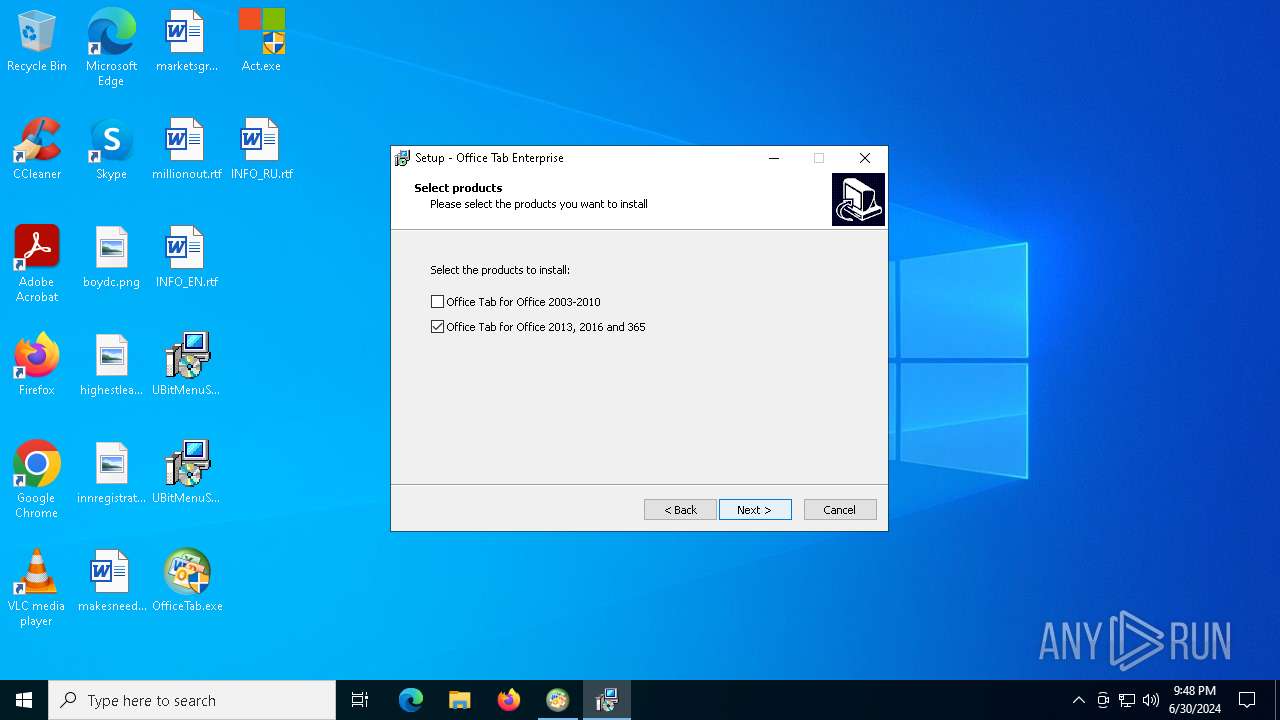
Searches for installed software
- OfficeTab.exe (PID: 4324)
INFO
Create files in a temporary directory
- helper.exe (PID: 1592)
- package.exe (PID: 4912)
- OfficeTab.exe (PID: 4324)
- package.tmp (PID: 188)
Checks supported languages
- helper.exe (PID: 1592)
- OfficeTab.exe (PID: 4324)
- package.exe (PID: 4912)
- package.tmp (PID: 188)
- _setup64.tmp (PID: 1064)
- TabsforOfficeCenter1316.exe (PID: 1192)
Reads the computer name
- helper.exe (PID: 1592)
- OfficeTab.exe (PID: 4324)
- package.tmp (PID: 188)
- TabsforOfficeCenter1316.exe (PID: 1192)
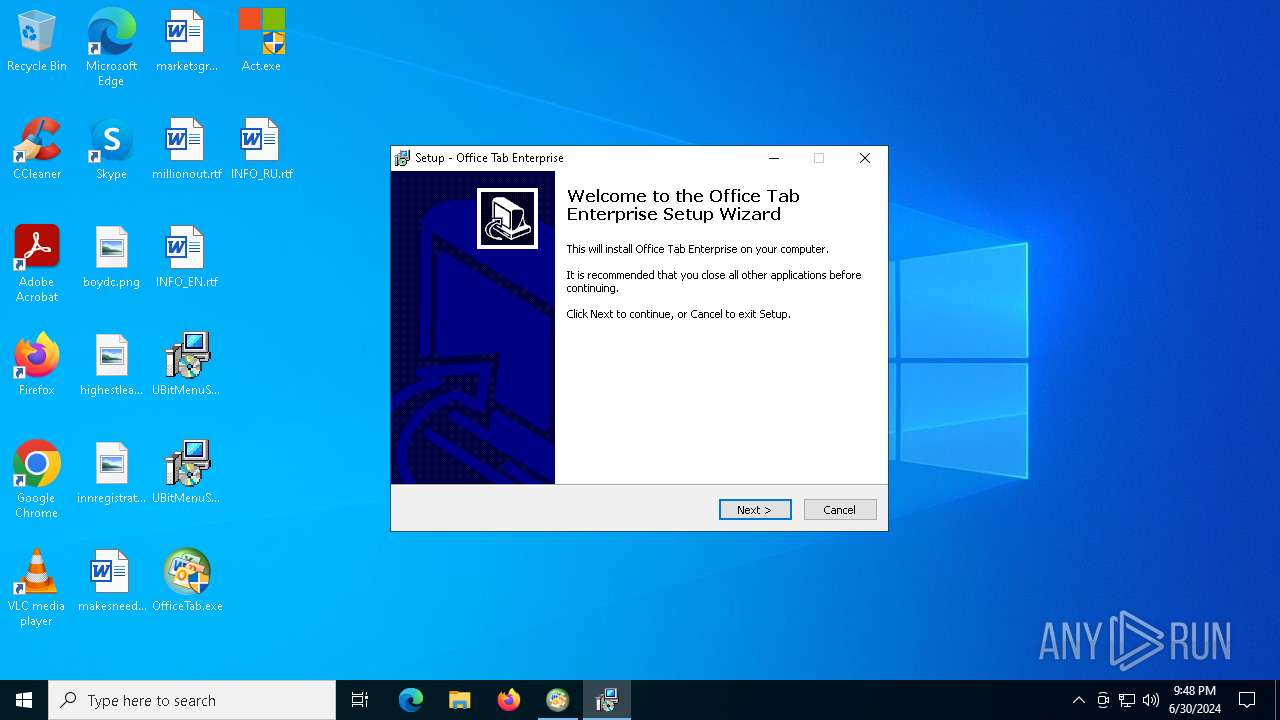
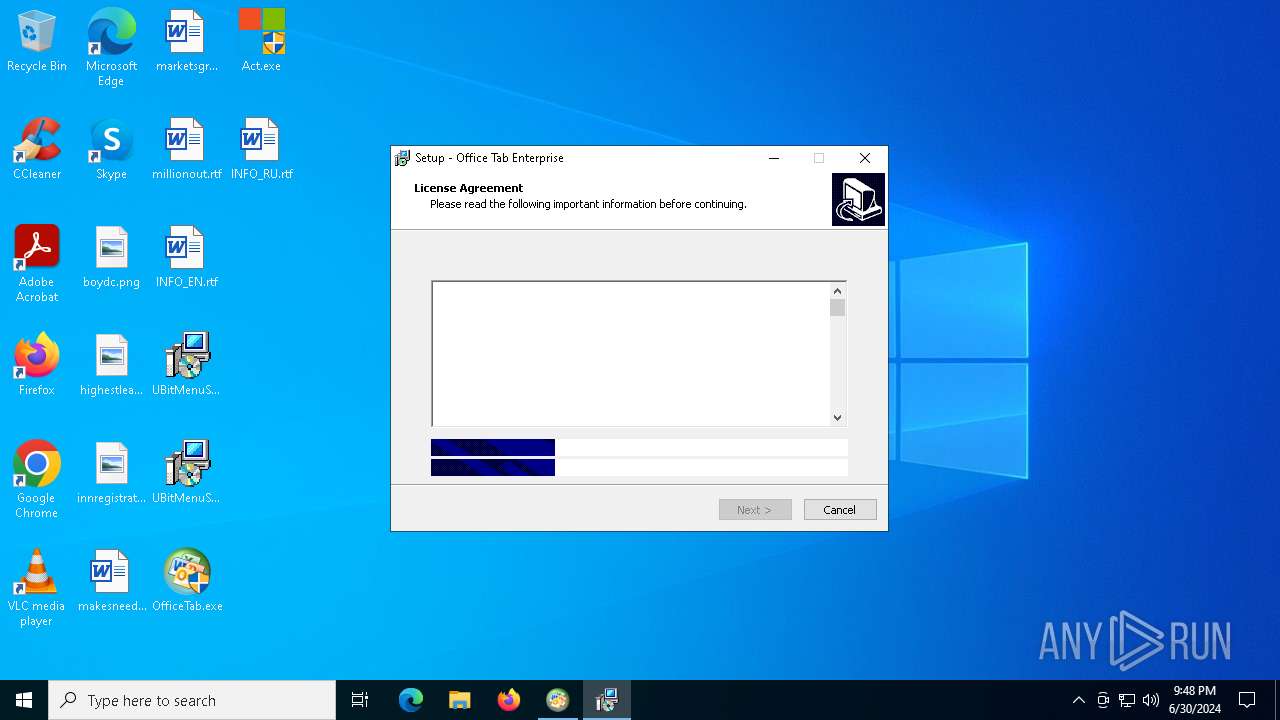
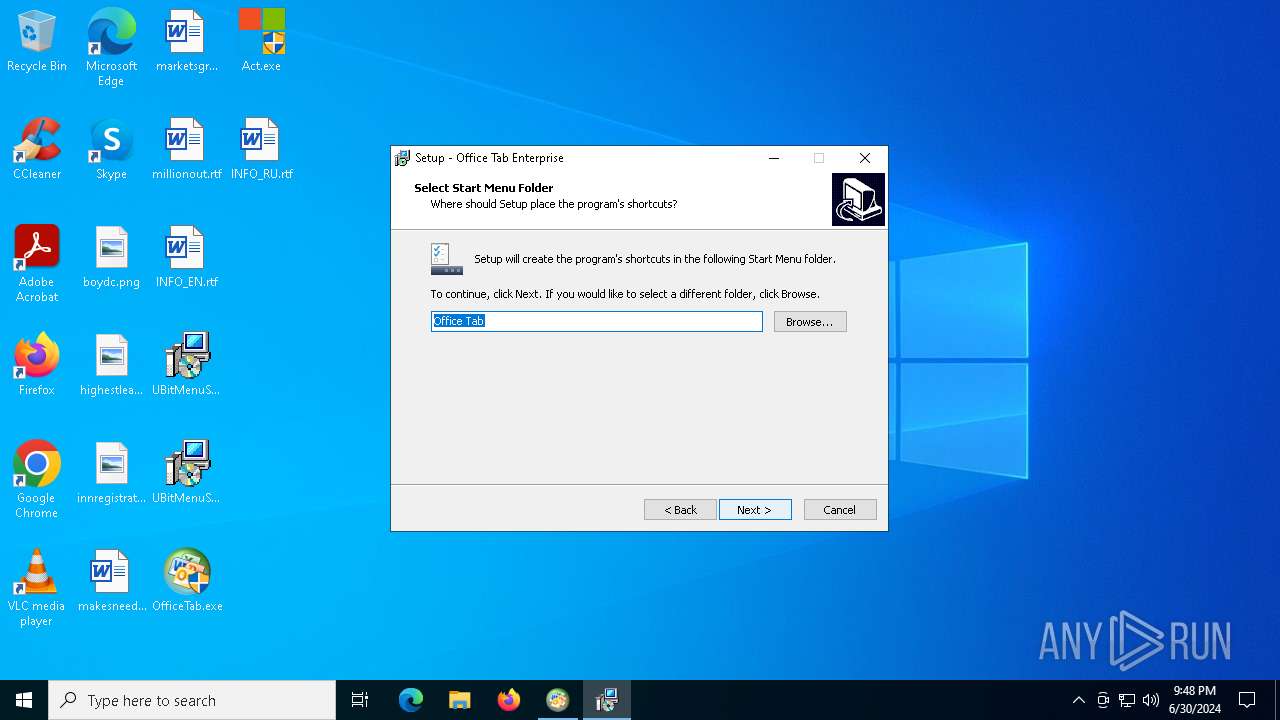
Manual execution by a user
- OfficeTab.exe (PID: 4324)
- OfficeTab.exe (PID: 4628)
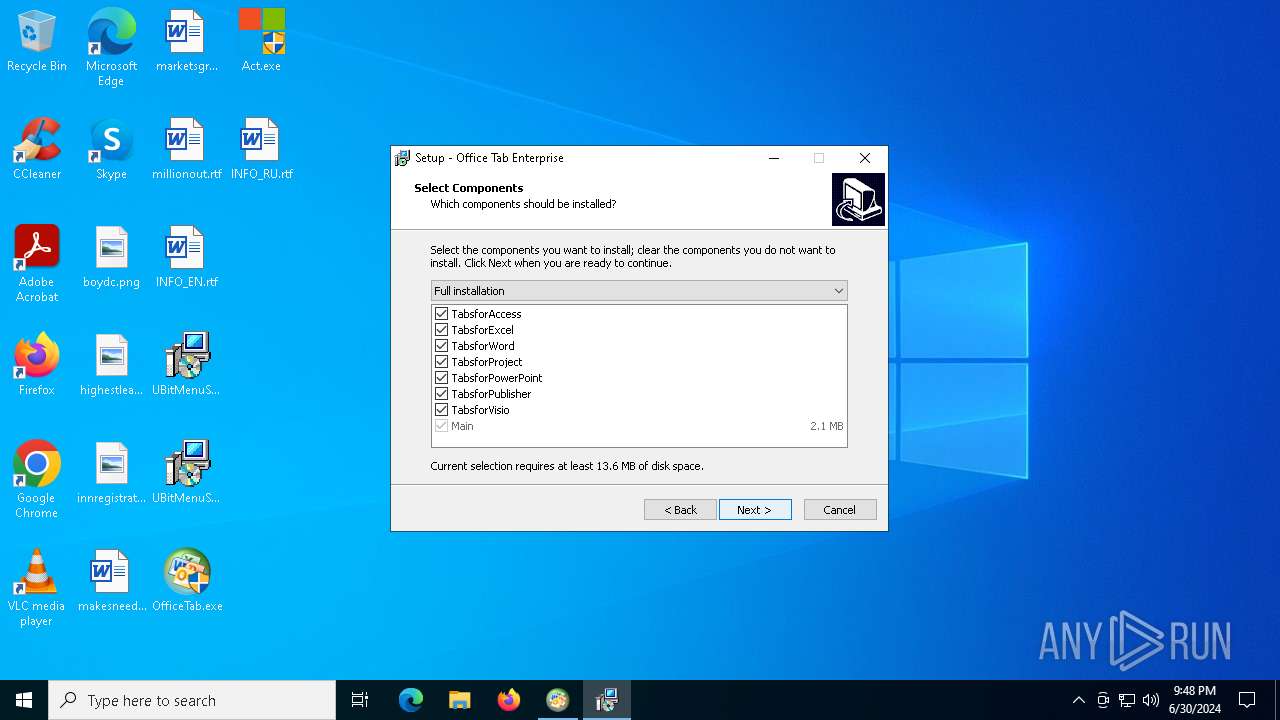
Creates files in the program directory
- package.tmp (PID: 188)
Reads Microsoft Office registry keys
- package.tmp (PID: 188)
- TabsforOfficeCenter1316.exe (PID: 1192)
VMProtect protector has been detected
- package.tmp (PID: 188)
Creates a software uninstall entry
- package.tmp (PID: 188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 19:19:59+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Cyrillic |
| Comments: | - |
| CompanyName: | KpoJIuK |
| FileDescription: | Office Install Helper |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | © KpoJIuK |
| ProductName: | Office Install Helper |
Total processes
146
Monitored processes
13
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Users\admin\AppData\Local\Temp\is-MGIRL.tmp\package.tmp" /SL5="$8027A,19854278,119296,C:\Users\admin\AppData\Local\Temp\nskF3EA.tmp\package.exe" | C:\Users\admin\AppData\Local\Temp\is-MGIRL.tmp\package.tmp | package.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 964 | "C:\Users\admin\AppData\Local\Temp\helper.exe" | C:\Users\admin\AppData\Local\Temp\helper.exe | — | explorer.exe | |||||||||||
User: admin Company: KpoJIuK Integrity Level: MEDIUM Description: Office Install Helper Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1064 | helper 105 0x568 | C:\Users\admin\AppData\Local\Temp\is-AMJ1J.tmp\_isetup\_setup64.tmp | — | package.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
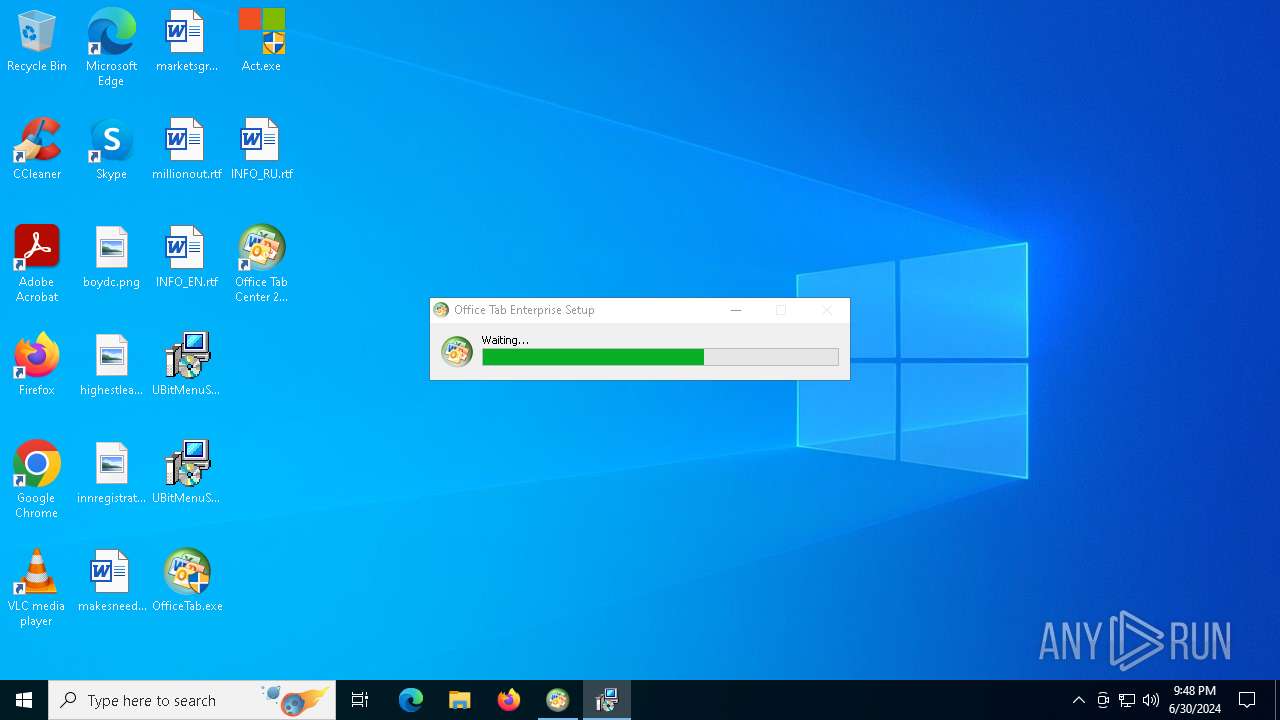
| 1192 | "C:\Program Files\Detong\Office Tab\TabsforOfficeCenter1316.exe" | C:\Program Files\Detong\Office Tab\TabsforOfficeCenter1316.exe | — | package.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 13.1.0.228 Modules
| |||||||||||||||
| 1592 | "C:\Users\admin\AppData\Local\Temp\helper.exe" | C:\Users\admin\AppData\Local\Temp\helper.exe | explorer.exe | ||||||||||||
User: admin Company: KpoJIuK Integrity Level: HIGH Description: Office Install Helper Exit code: 2 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1960 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files\Detong\Office Tab\TabsforOfficeHelper32.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | package.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files\Detong\Office Tab\TabsforOfficeHelper64.dll" | C:\Windows\System32\regsvr32.exe | — | package.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | _setup64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2308 | "C:\WINDOWS\system32\regsvr32.exe" /s "C:\Program Files\Detong\Office Tab\TabsforOffice1316x32.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | package.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4324 | "C:\Users\admin\Desktop\OfficeTab.exe" | C:\Users\admin\Desktop\OfficeTab.exe | explorer.exe | ||||||||||||
User: admin Company: Detong Technology Ltd. Integrity Level: HIGH Description: Office Tab Enterprise v13.10 Exit code: 0 Version: 13.10.0.0 Modules
| |||||||||||||||
Total events
6 374
Read events
6 057
Write events
298
Delete events
19
Modification events
| (PID) Process: | (4324) OfficeTab.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4324) OfficeTab.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4324) OfficeTab.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4324) OfficeTab.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (188) package.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: BC000000AF6F5B3337CBDA01 | |||
| (PID) Process: | (188) package.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: B9A58F4076CF4BFBB821773EDF28F4ECEC051511E6D86353935D8BB6E7A17D5C | |||
| (PID) Process: | (188) package.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (188) package.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Detong\Office Tab\TabsforOfficeHelper32.dll | |||
| (PID) Process: | (188) package.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 590248AA02DFC7560D99E1AE7BD4BDFF2793FC3EA1EC4A098DE9406277807338 | |||
| (PID) Process: | (188) package.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Office\ClickToRun\REGISTRY\MACHINE\Software\Microsoft\AppV\Subsystem\VirtualRegistry |
| Operation: | write | Name: | PassThroughPaths |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Policies | |||
Executable files
33
Suspicious files
7
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 188 | package.tmp | C:\Users\admin\AppData\Local\Temp\is-AMJ1J.tmp\_isetup\_setup64.tmp | executable | |
MD5:526426126AE5D326D0A24706C77D8C5C | SHA256:B20A8D88C550981137ED831F2015F5F11517AEB649C29642D9D61DEA5EBC37D1 | |||
| 4324 | OfficeTab.exe | C:\Users\admin\AppData\Local\Temp\nskF3EA.tmp\repackme.gif | image | |
MD5:23D3840ADB8F4F1EFC083A1F7E640191 | SHA256:82A1454402156D74F4F23C992D5D772B665546208EFF44790871B8DCB36D2304 | |||
| 4324 | OfficeTab.exe | C:\Users\admin\AppData\Local\Temp\~DF53C2C8E10A97D065.TMP | binary | |
MD5:95B12D577ACF72079520F0E6442531C3 | SHA256:EFB4DFC2D87385CCF00D001F86361364E082188134832B61F033E986B5D0980D | |||
| 4324 | OfficeTab.exe | C:\Users\admin\AppData\Local\Temp\nskF3EA.tmp\newadvsplash.dll | executable | |
MD5:55A723E125AFBC9B3A41D46F41749068 | SHA256:0A70CC4B93D87ECD93E538CFBED7C9A4B8B5C6F1042C6069757BDA0D1279ED06 | |||
| 188 | package.tmp | C:\Users\admin\AppData\Local\Temp\is-AMJ1J.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 1592 | helper.exe | C:\Users\admin\AppData\Local\Temp\nsjD15C.tmp | binary | |
MD5:EE368A52CAADB2168ED0445B0BFD07EB | SHA256:7D9964B8389027400BCE333D6066BFE531CF4396CD232F60A00A230C398EE3A5 | |||
| 188 | package.tmp | C:\Program Files\Detong\Office Tab\is-TQ4TM.tmp | executable | |
MD5:3E7AC1D4D411CF03FACF3F62434E35B7 | SHA256:730E46FC60754221C02095AC08B8E1850EC5D0CF7DB6A363F6D7473EA694F850 | |||
| 188 | package.tmp | C:\Users\Public\Documents\Office Tab\Language\Language.xml | xml | |
MD5:1624128D82751DE207538ADF7D7832FB | SHA256:89ED621D144500B336AF36C70C92B5B96A74CFE8B985022674D1949779ACF67D | |||
| 188 | package.tmp | C:\Users\Public\Documents\Office Tab\Language\is-5BJDD.tmp | xml | |
MD5:1624128D82751DE207538ADF7D7832FB | SHA256:89ED621D144500B336AF36C70C92B5B96A74CFE8B985022674D1949779ACF67D | |||
| 188 | package.tmp | C:\Users\Public\Documents\Office Tab\Language\is-3Q1VE.tmp | text | |
MD5:05BF4665042E26EA0D99FBA6360668AB | SHA256:074F3996951F032E497459E387A494AA614CBF3665612D34C1EC3DA8F321B9CE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
70
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
1544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
3040 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | unknown |
5524 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
4084 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
4524 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
4084 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2336 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6068 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4656 | SearchApp.exe | 104.126.37.161:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1544 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
1544 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4656 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | unknown |
1060 | svchost.exe | 184.30.17.189:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
r.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |