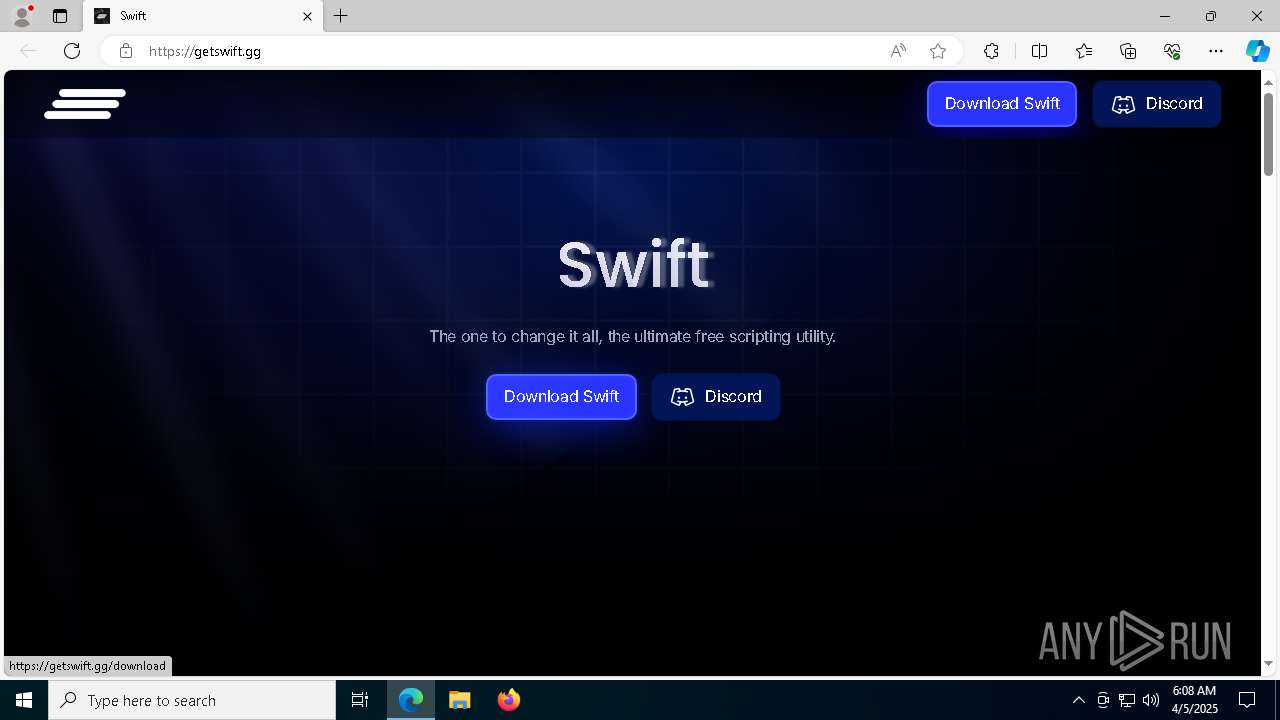
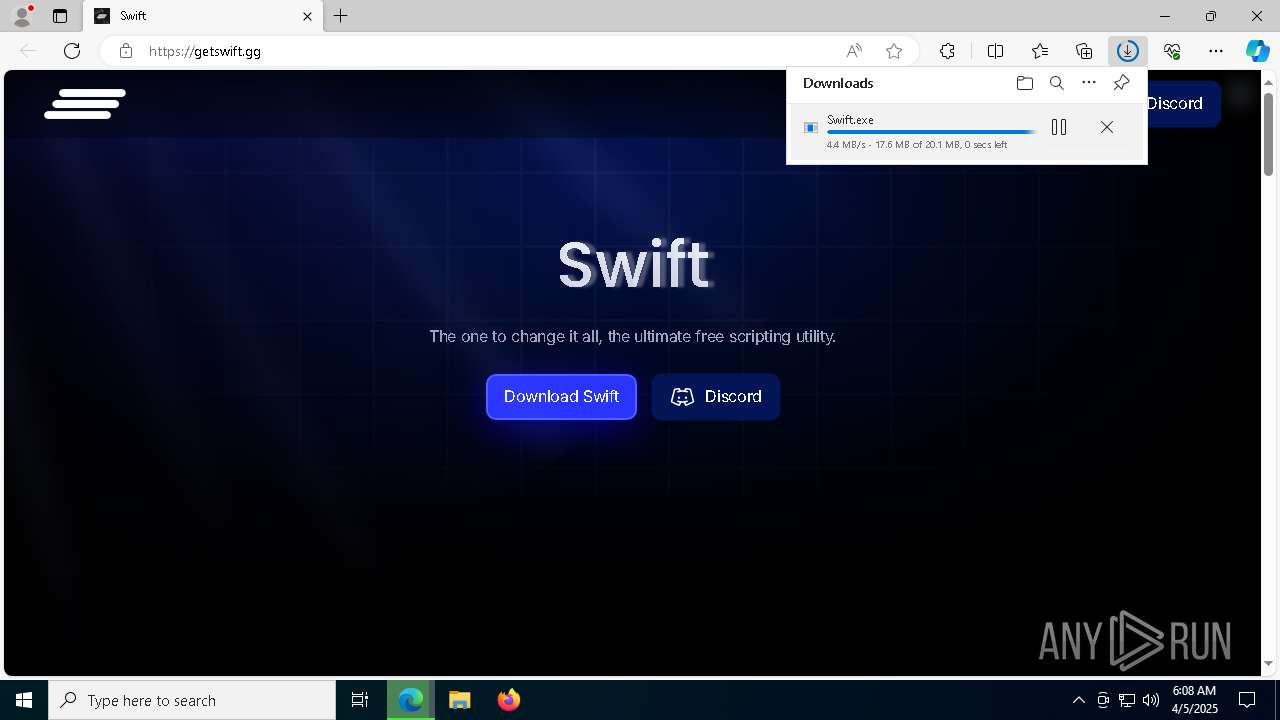
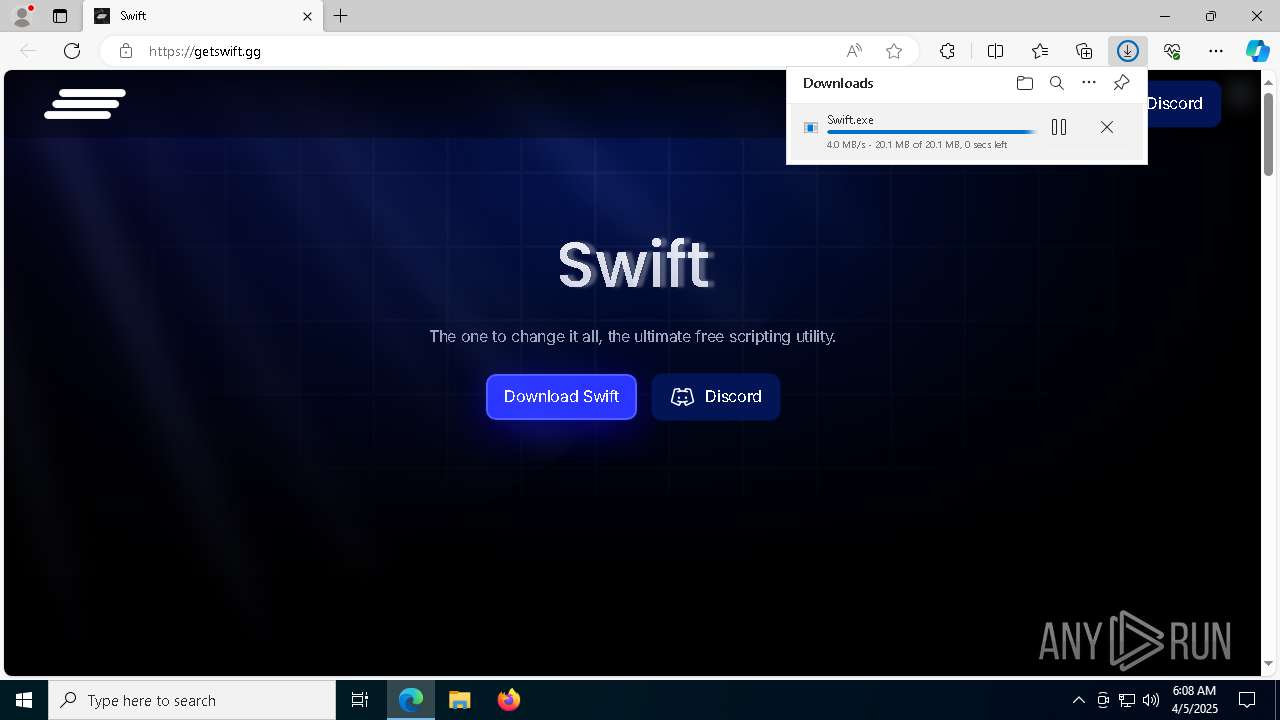
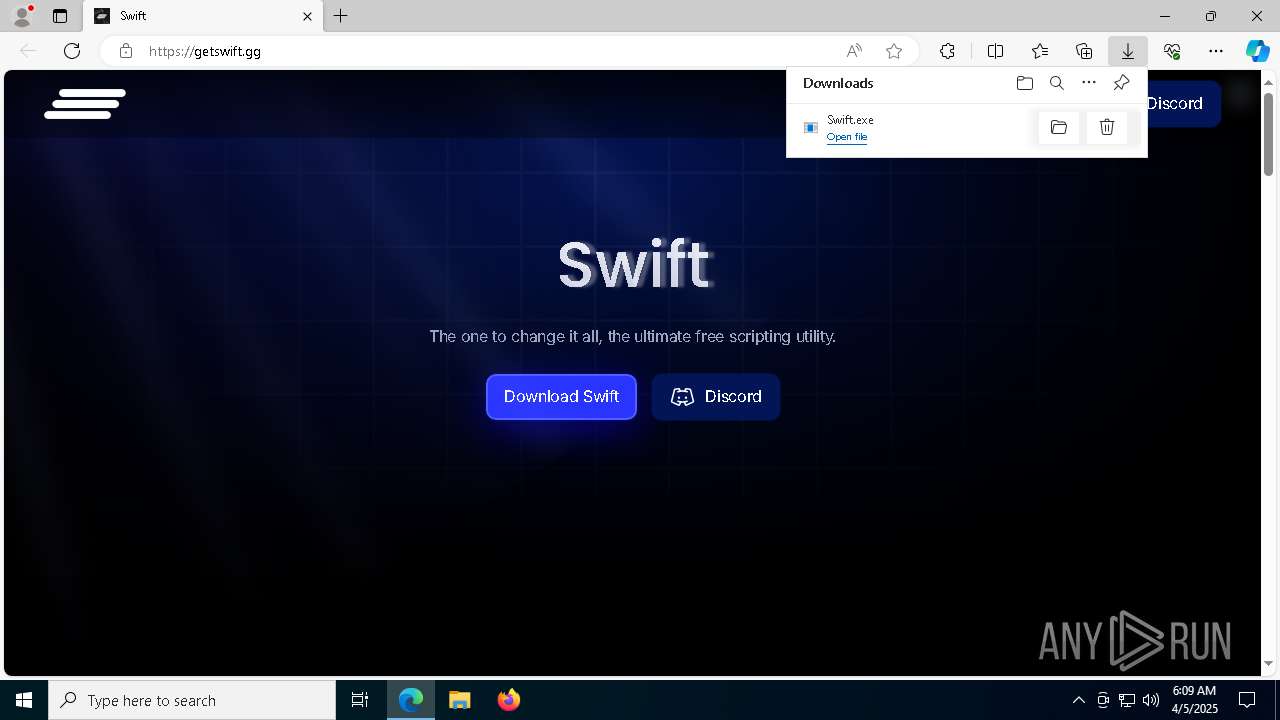
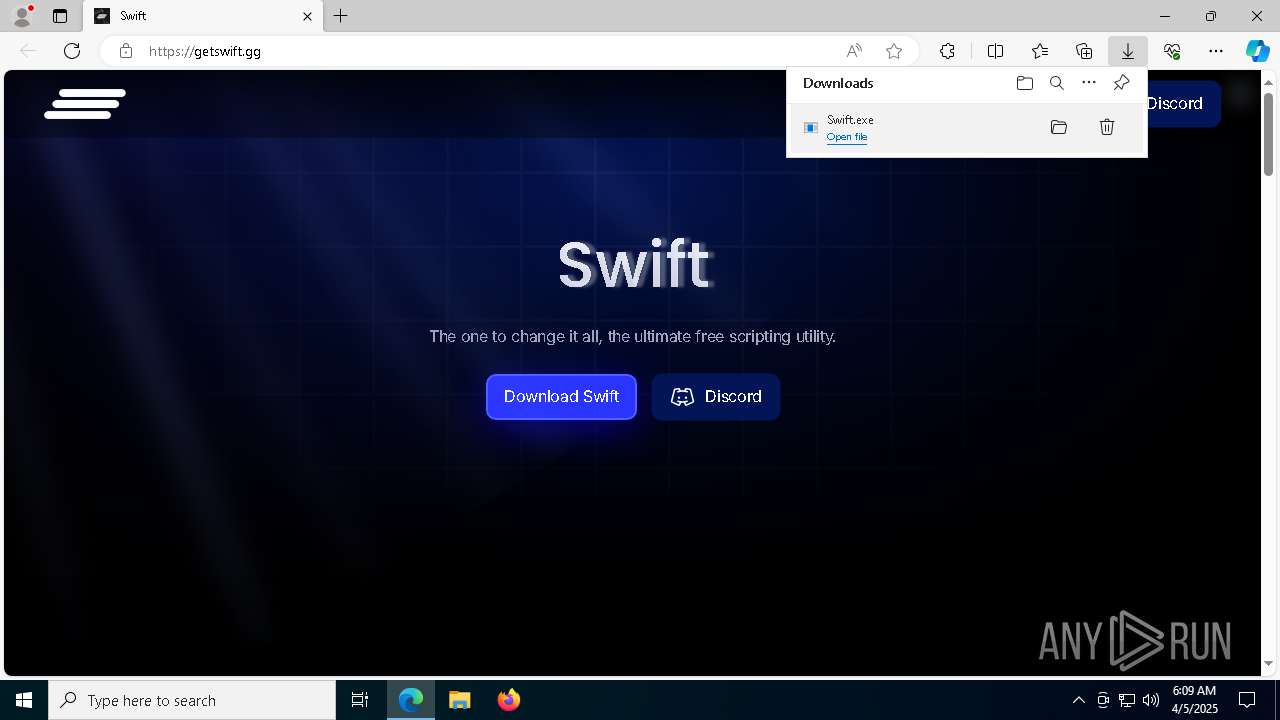
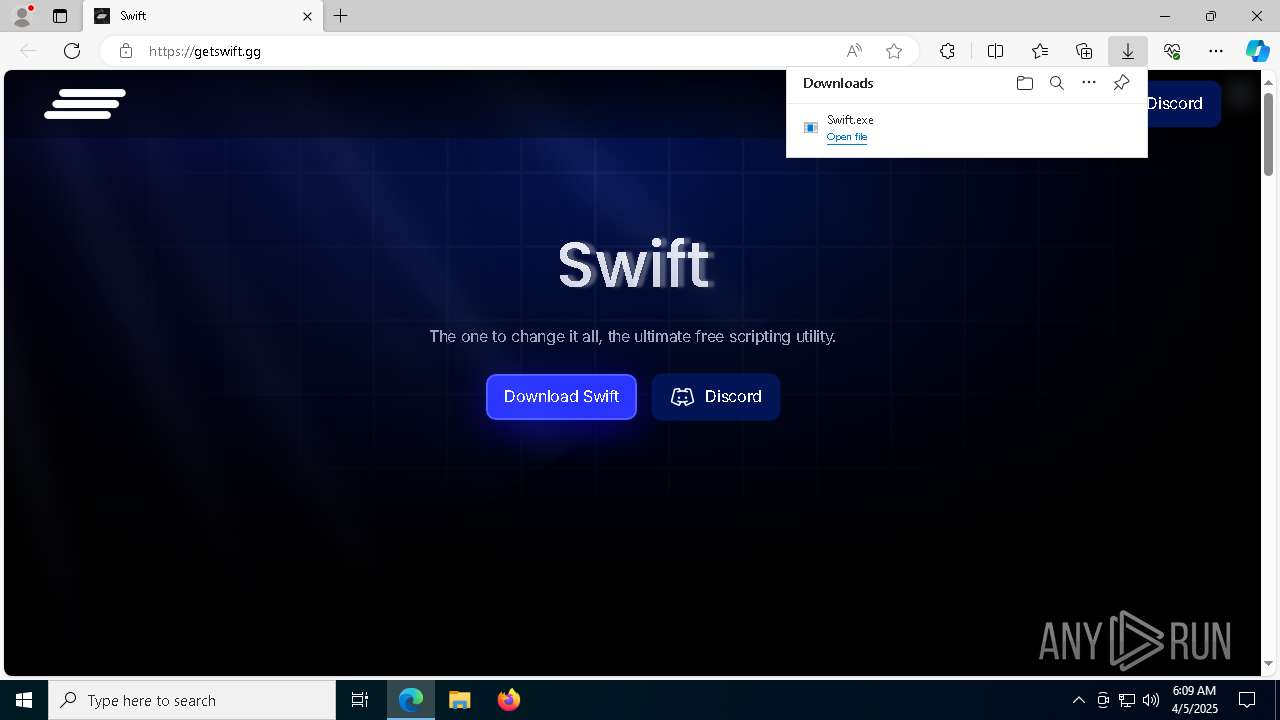
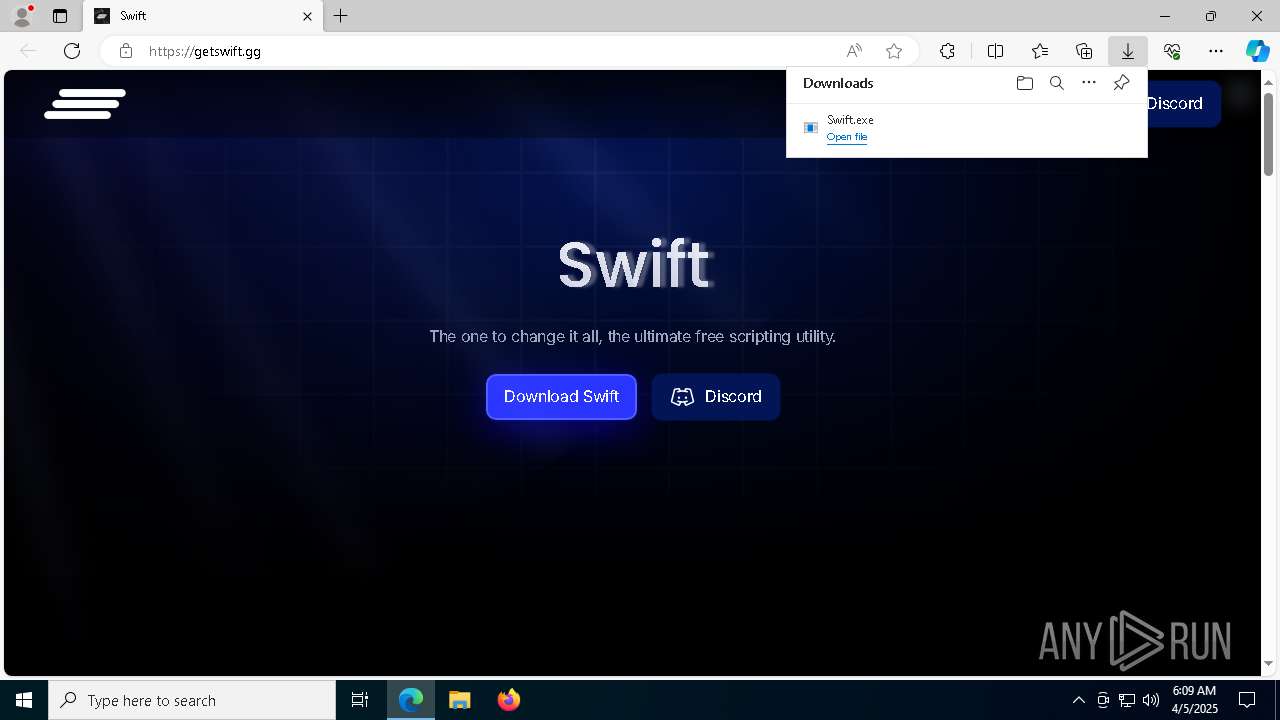
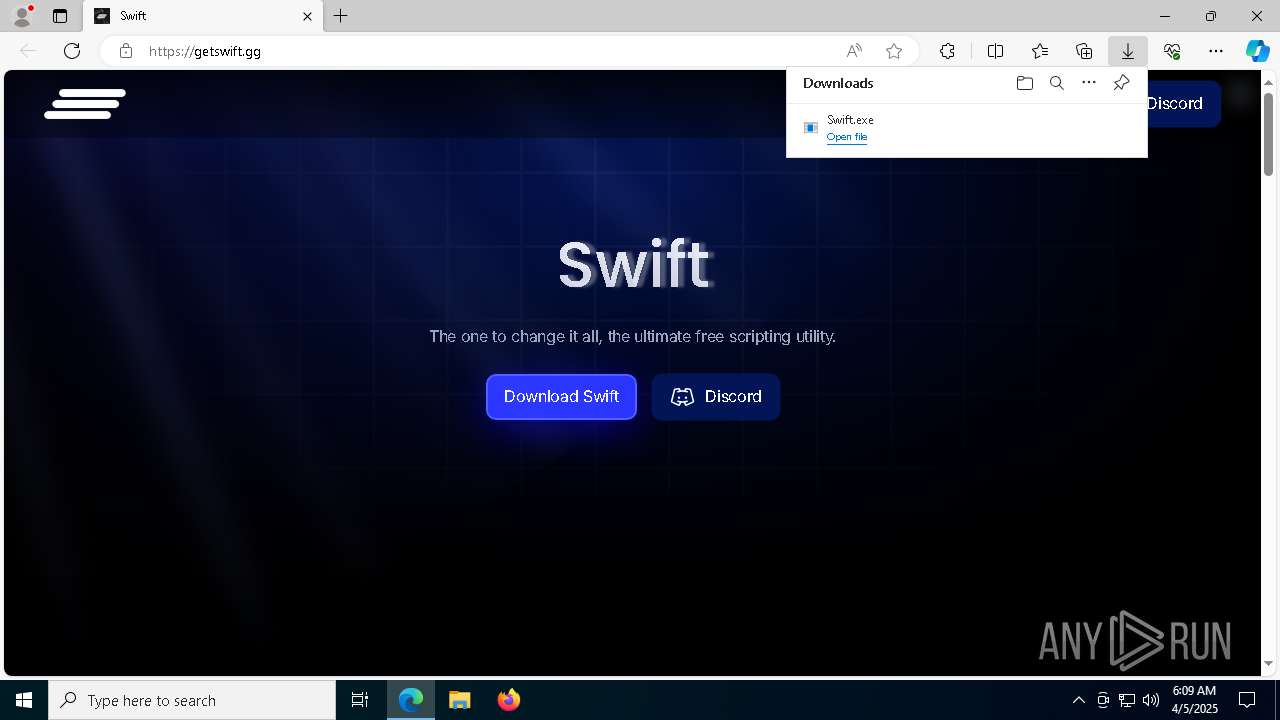
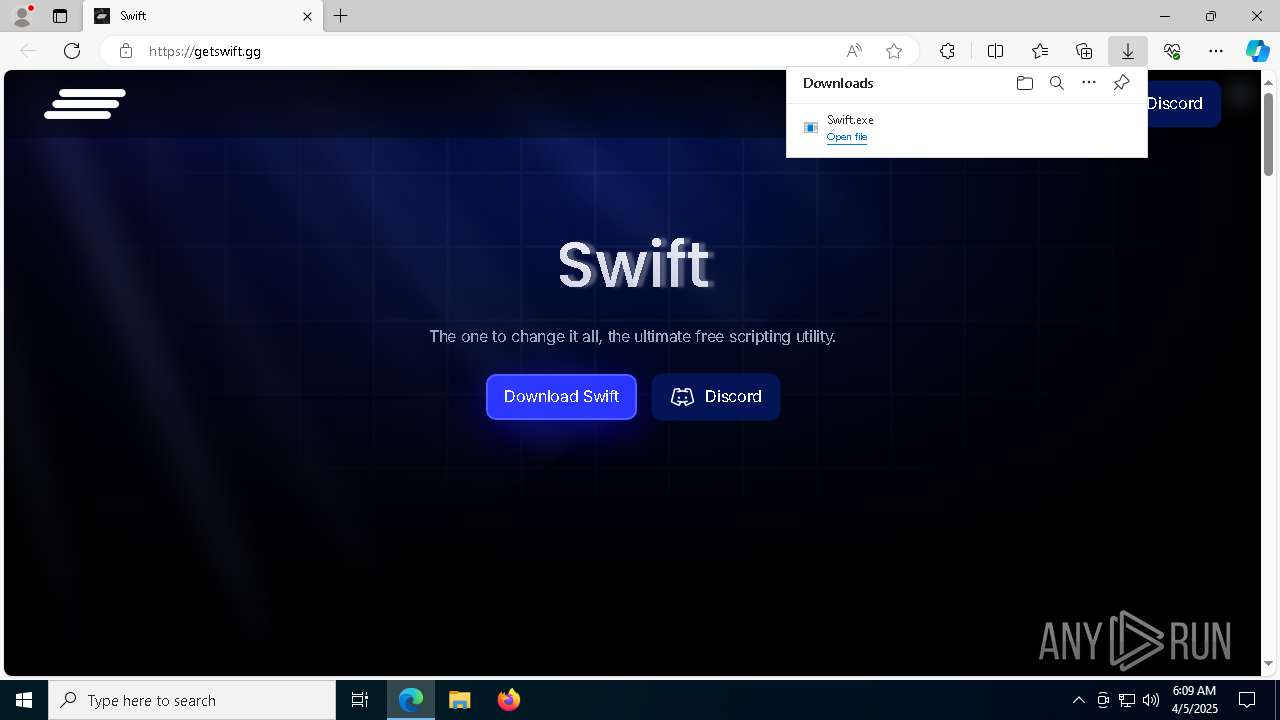
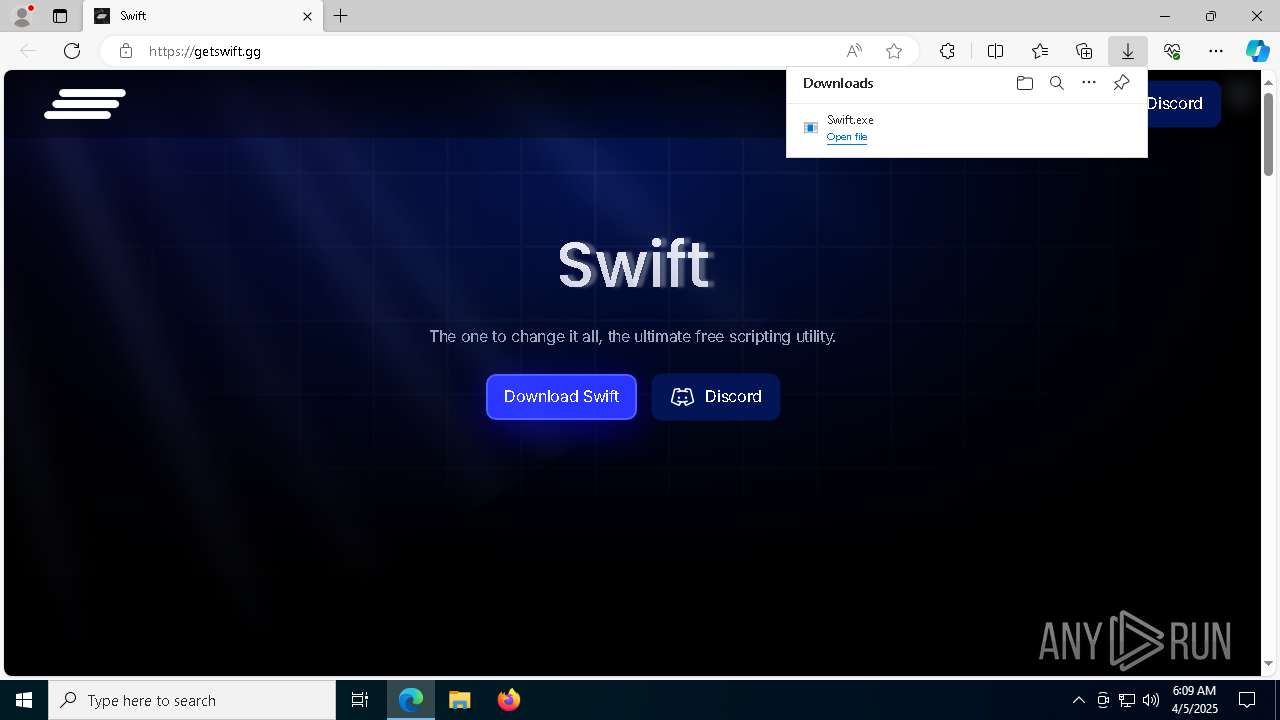
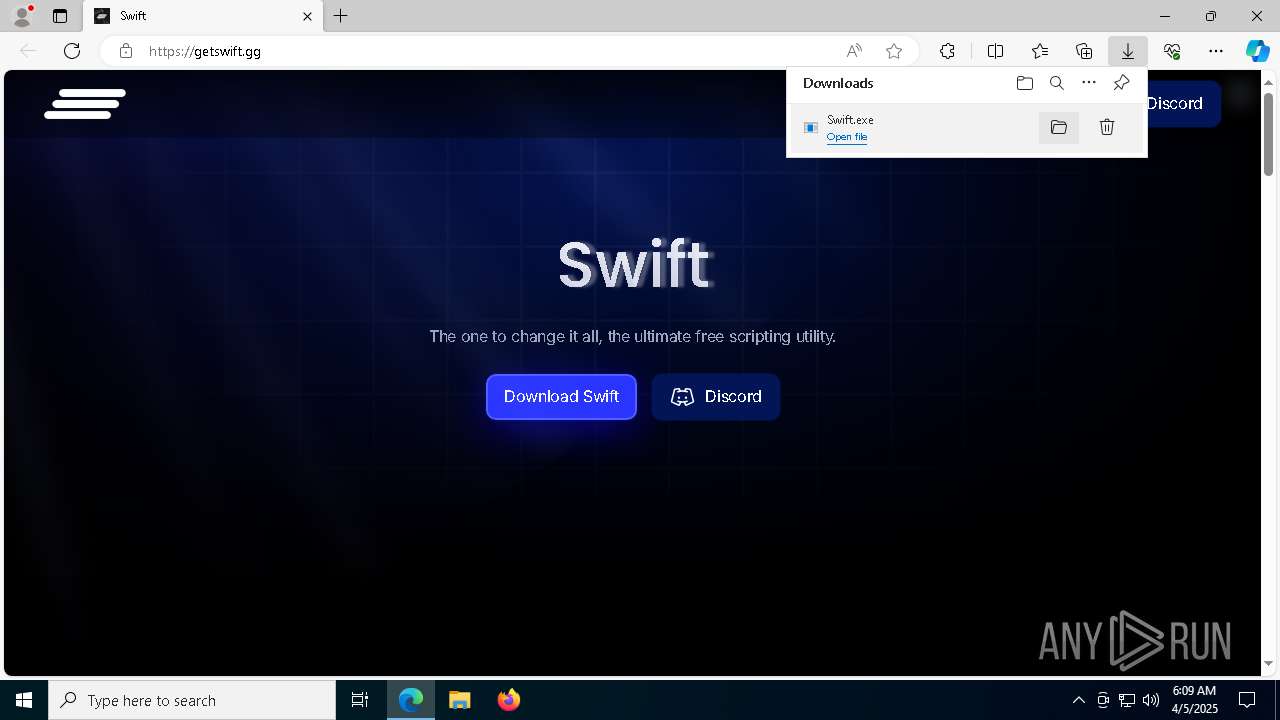
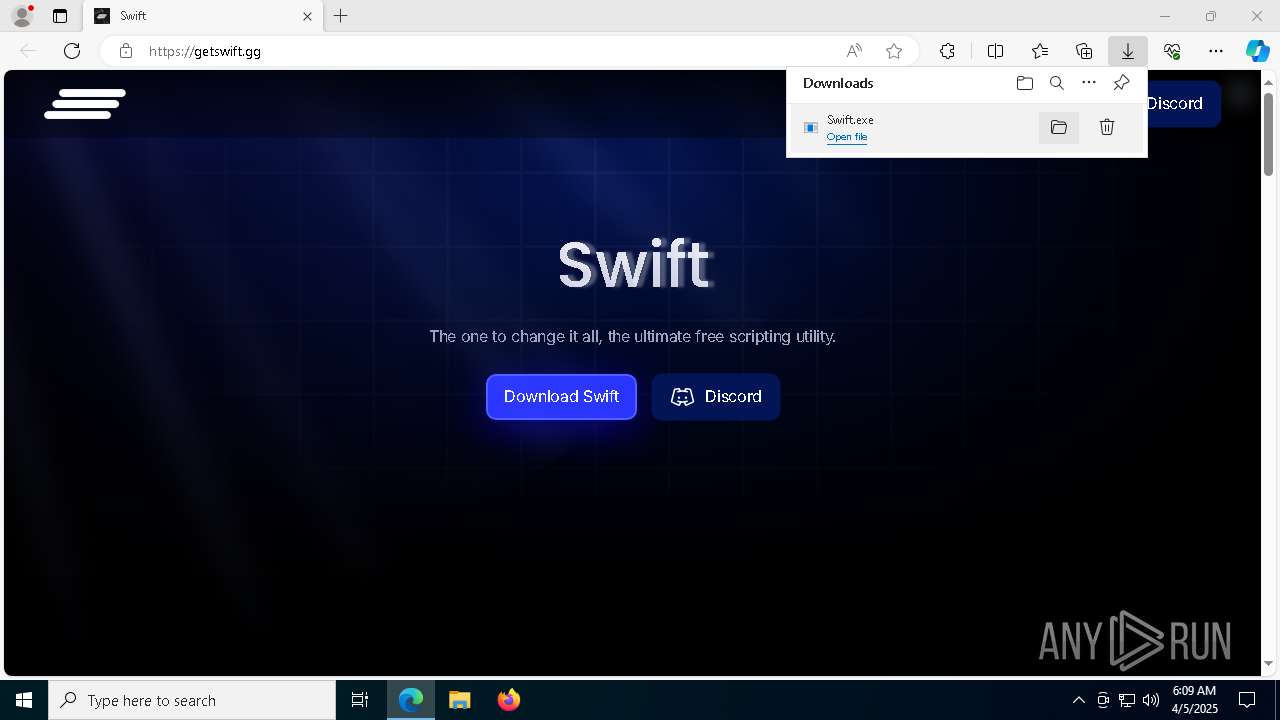
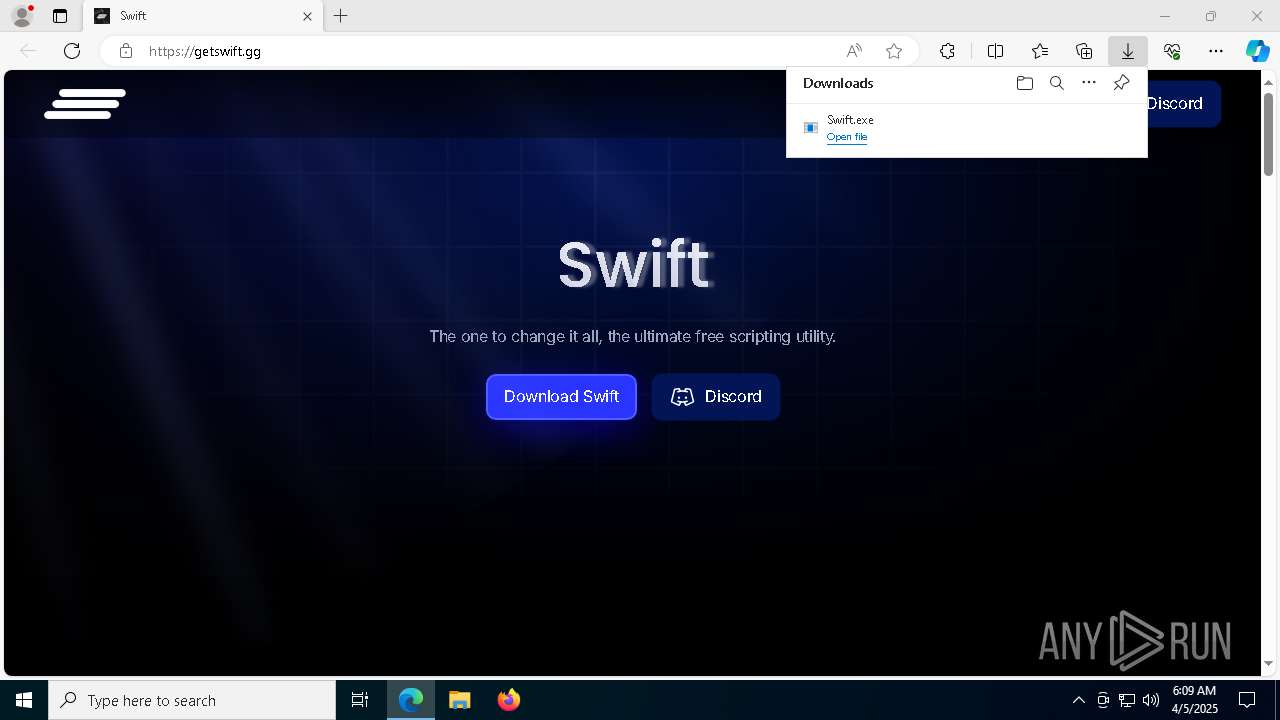
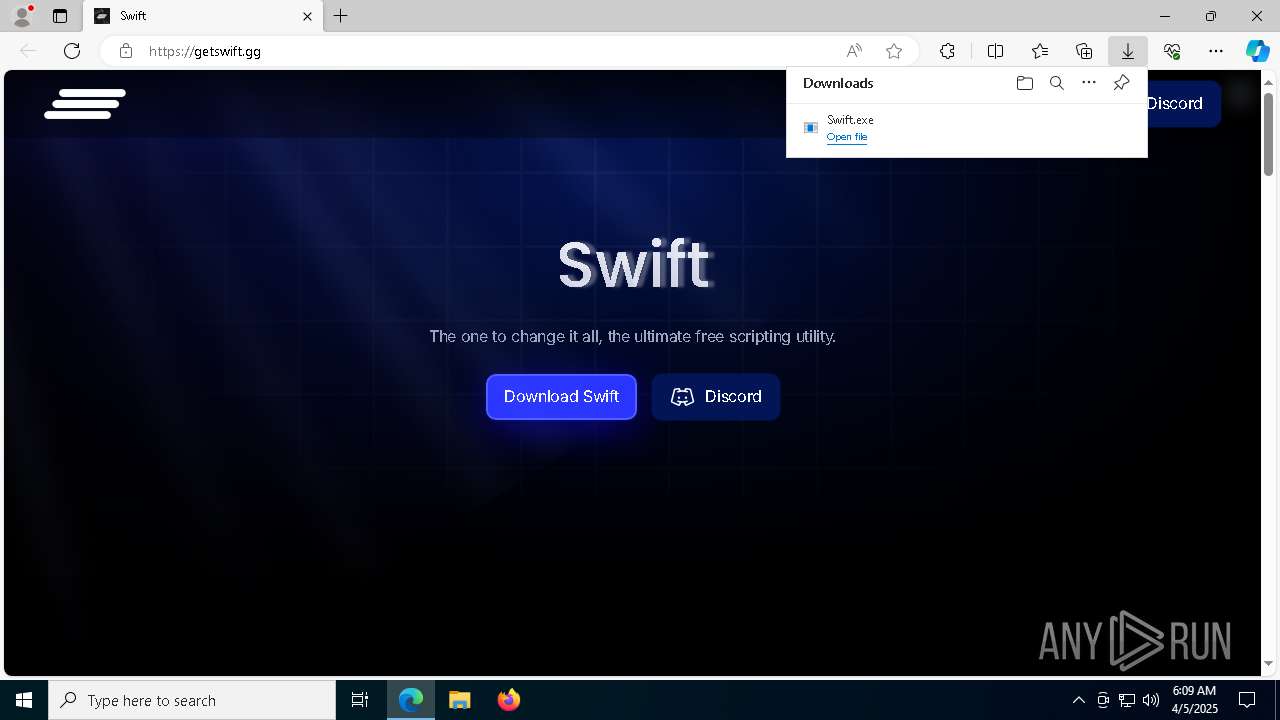
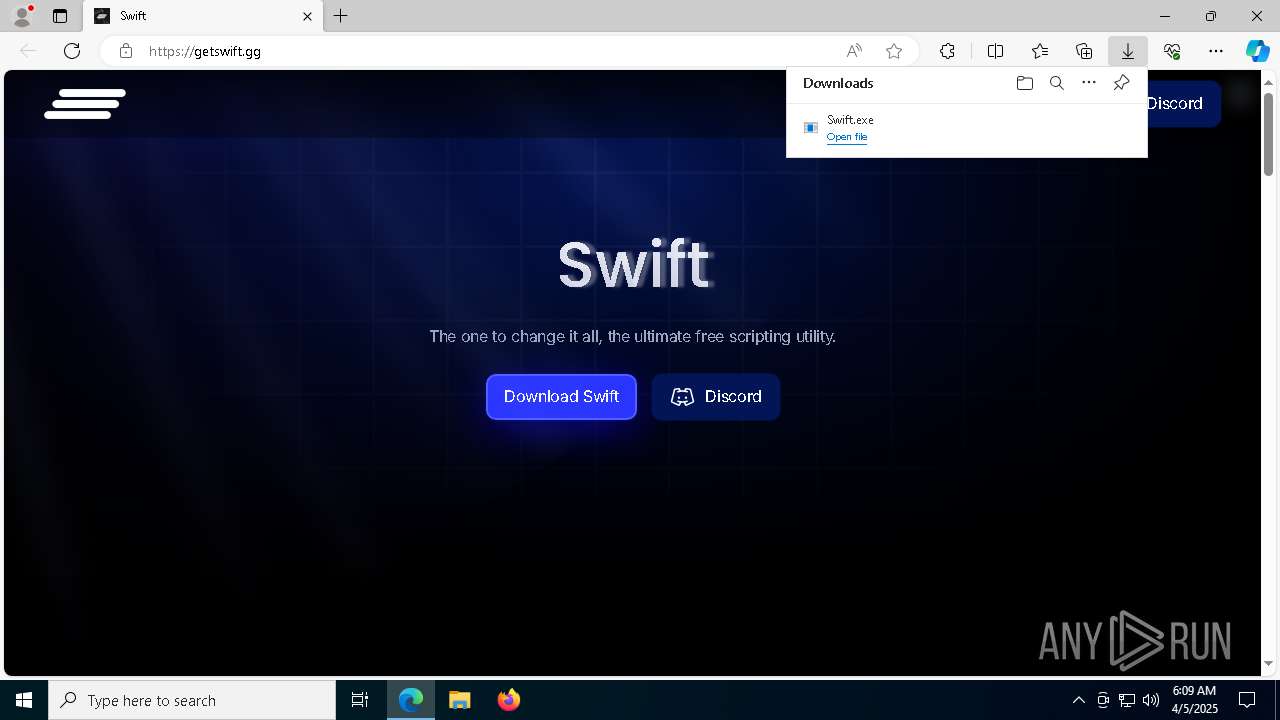
| URL: | https://getswift.gg/ |
| Full analysis: | https://app.any.run/tasks/7fb9f900-93fc-4793-9a5b-53dcd11e8d48 |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2025, 06:08:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | A35FB9DE8F1671D796A9FBC064A895A6 |
| SHA1: | 5760C001924DC10AF206C594C03F8659647F50D6 |
| SHA256: | 0AD73028C793777371200E2F86656C946D9D91529BEA4633458843FC712B3241 |
| SSDEEP: | 3:N8hnMDtCJ:2GD6 |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6808)
- powershell.exe (PID: 4244)
- powershell.exe (PID: 920)
- powershell.exe (PID: 2984)
- powershell.exe (PID: 7940)
- powershell.exe (PID: 4228)
SUSPICIOUS
Reads the BIOS version
- Swift.exe (PID: 7960)
- Swift.exe (PID: 6752)
The process bypasses the loading of PowerShell profile settings
- Swift.exe (PID: 7960)
- Swift.exe (PID: 6752)
Starts POWERSHELL.EXE for commands execution
- Swift.exe (PID: 7960)
- Swift.exe (PID: 6752)
The process hide an interactive prompt from the user
- Swift.exe (PID: 7960)
- Swift.exe (PID: 6752)
INFO
Reads the computer name
- identity_helper.exe (PID: 8564)
- Swift.exe (PID: 7960)
- Swift.exe (PID: 6752)
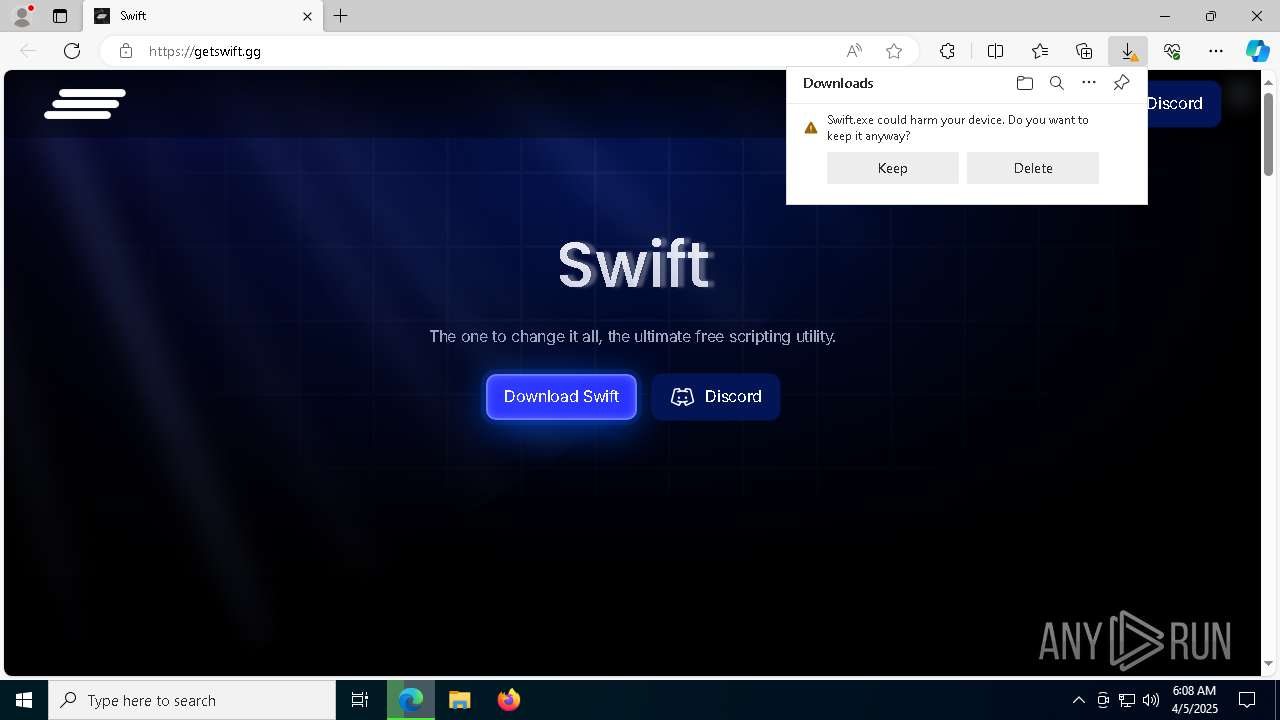
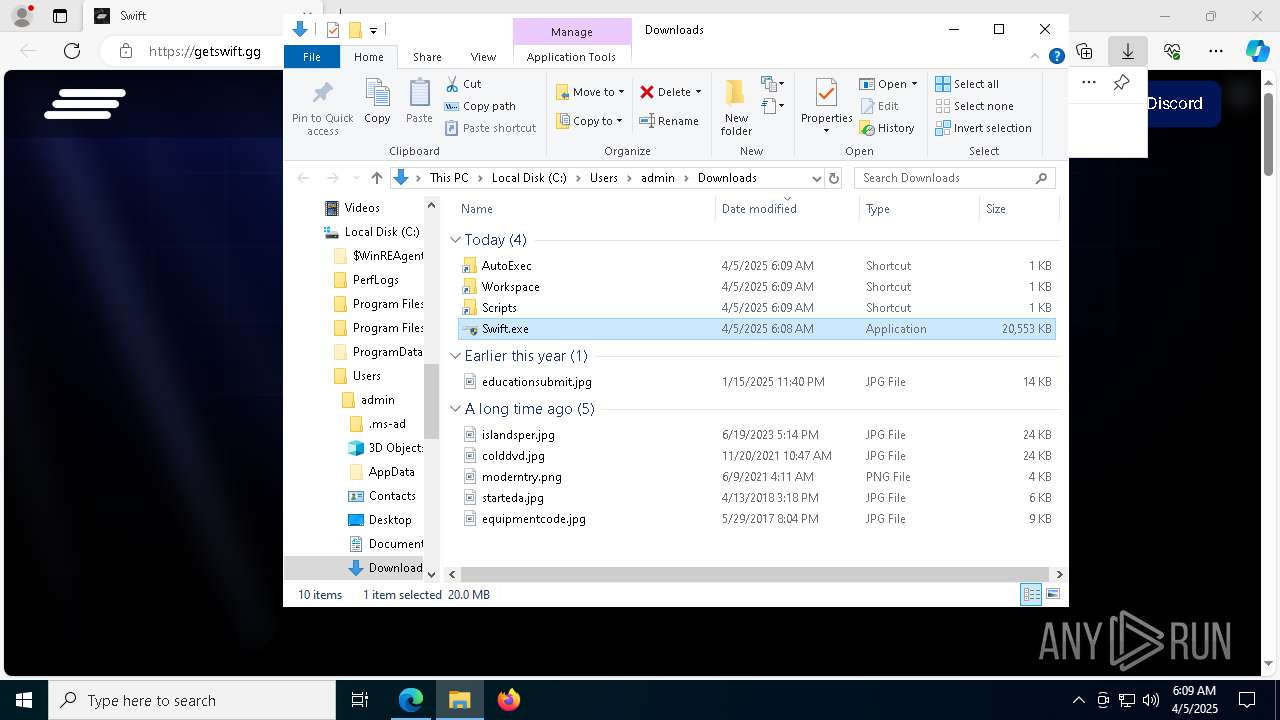
Executable content was dropped or overwritten
- msedge.exe (PID: 7364)
- msedge.exe (PID: 668)
Checks supported languages
- identity_helper.exe (PID: 8564)
- Swift.exe (PID: 7960)
- Swift.exe (PID: 6752)
Reads Environment values
- identity_helper.exe (PID: 8564)
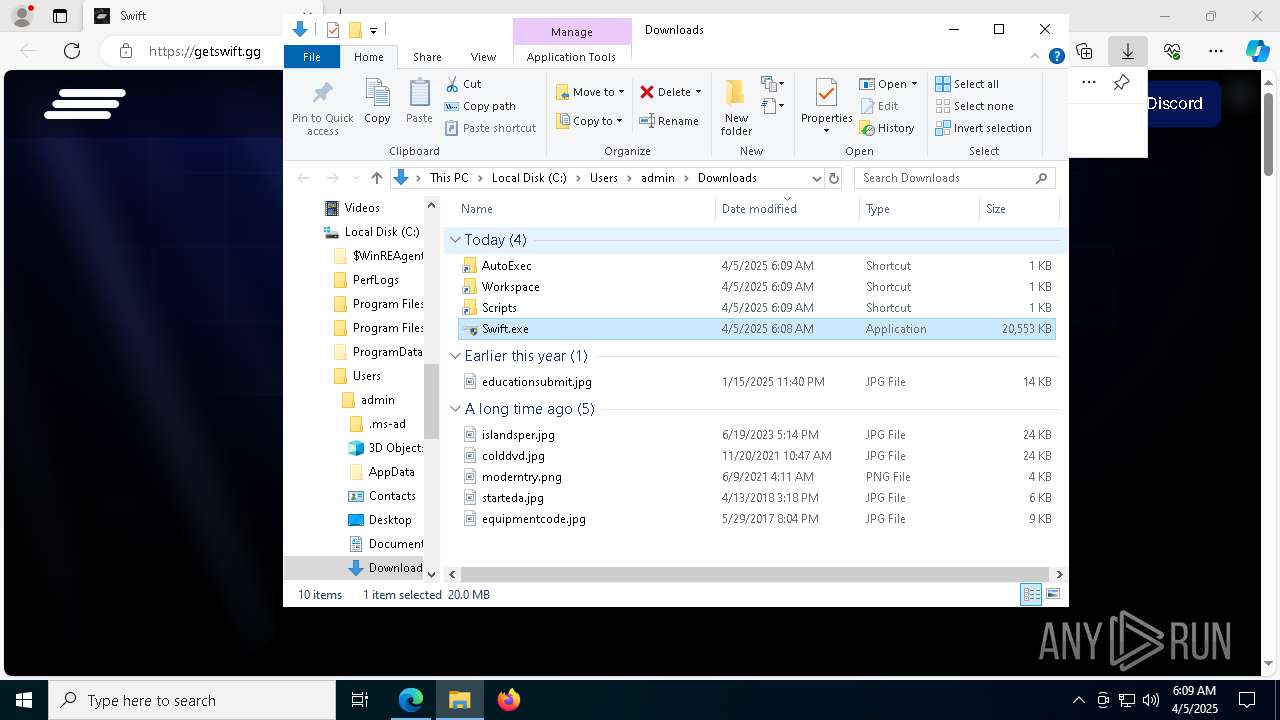
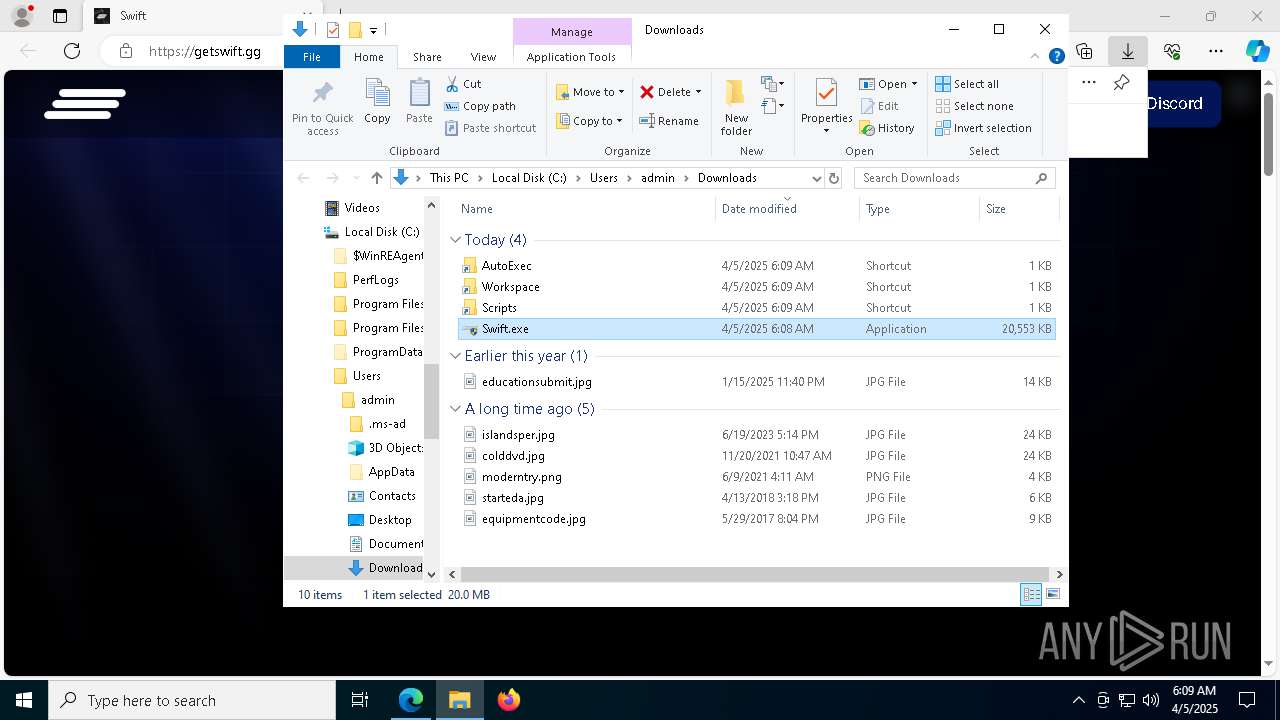
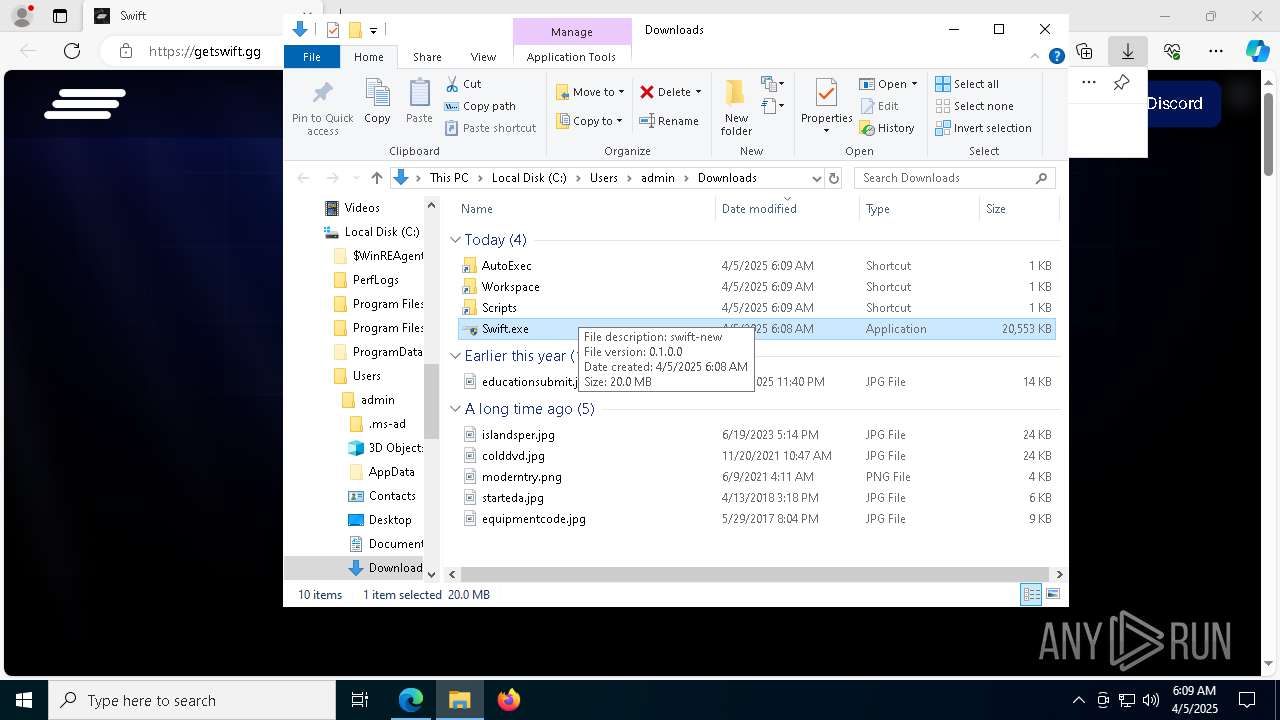
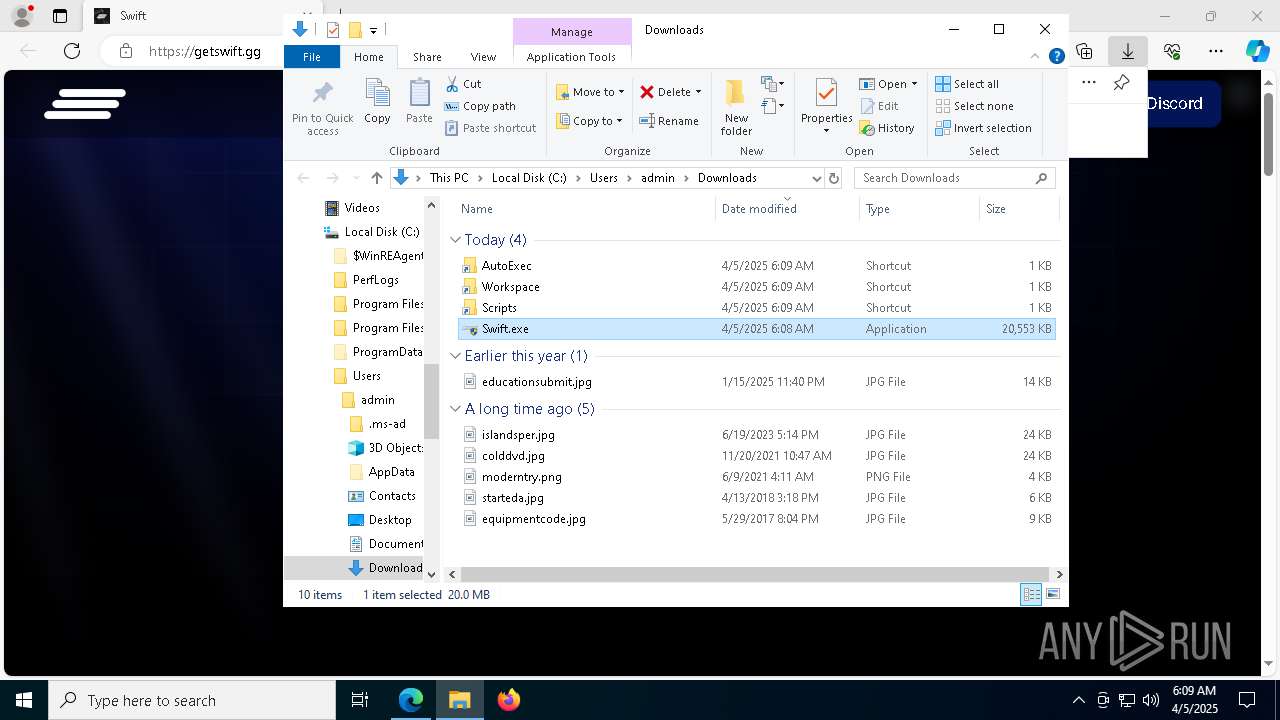
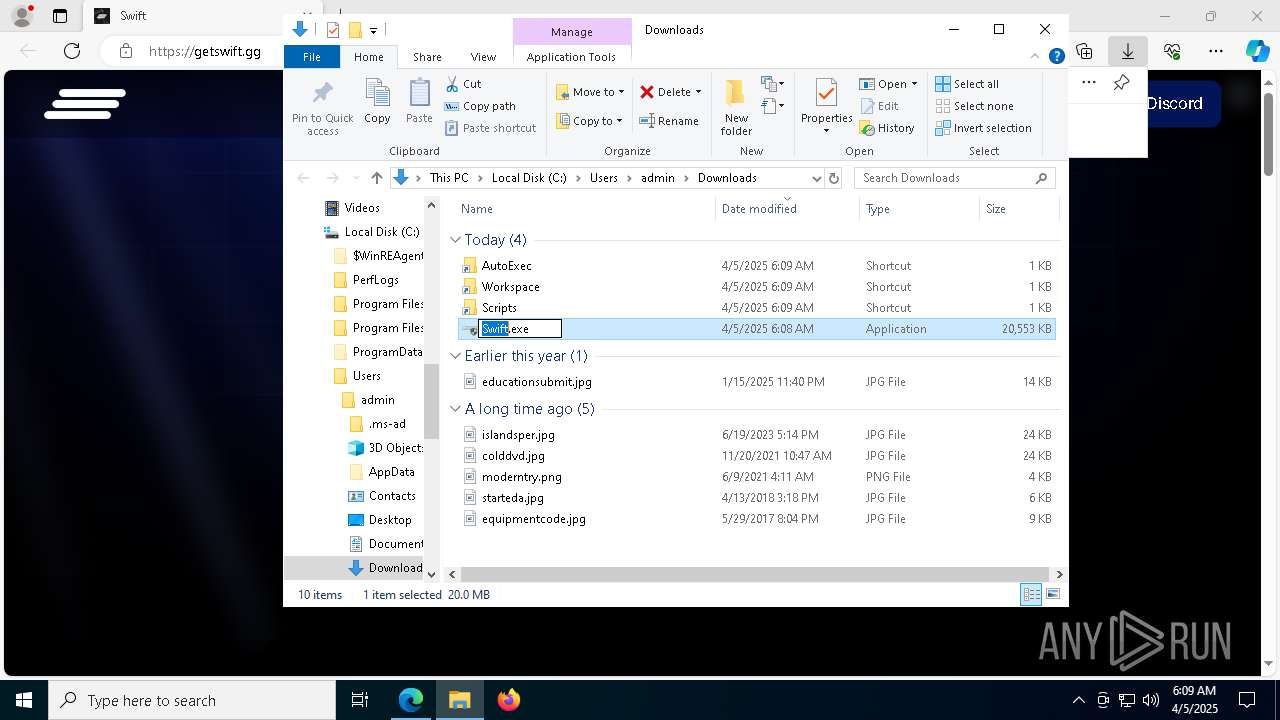
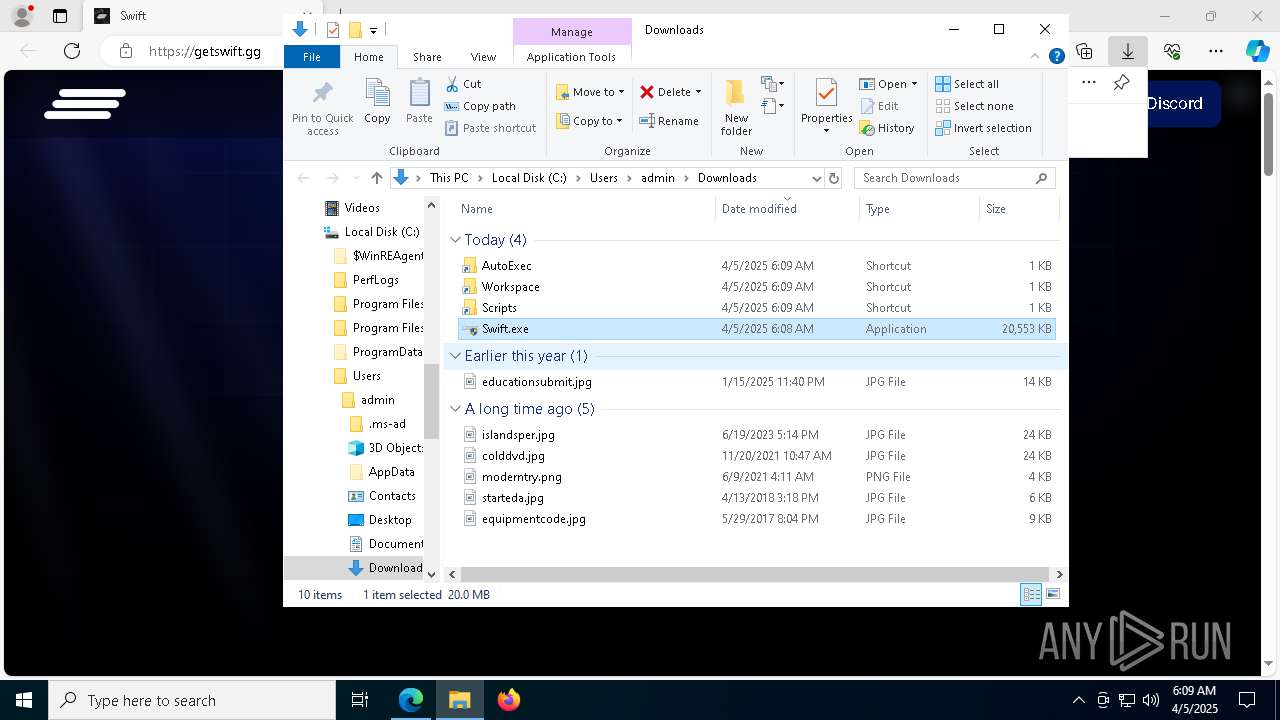
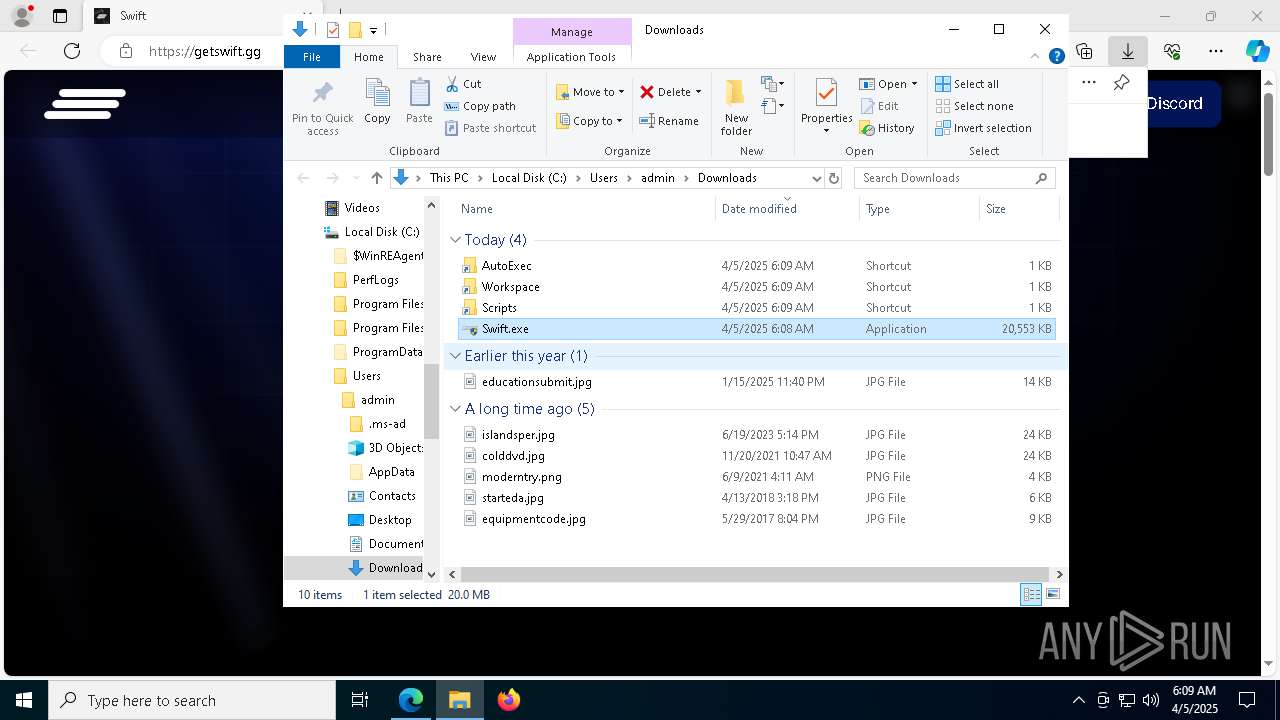
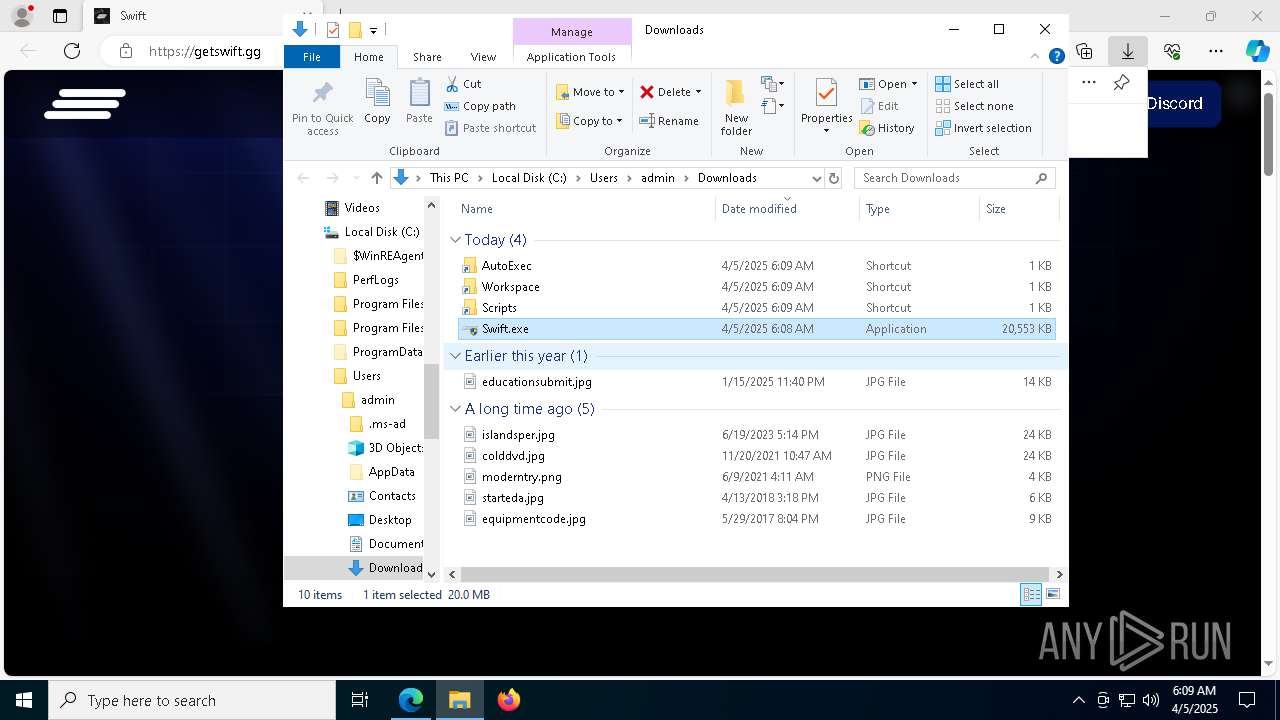
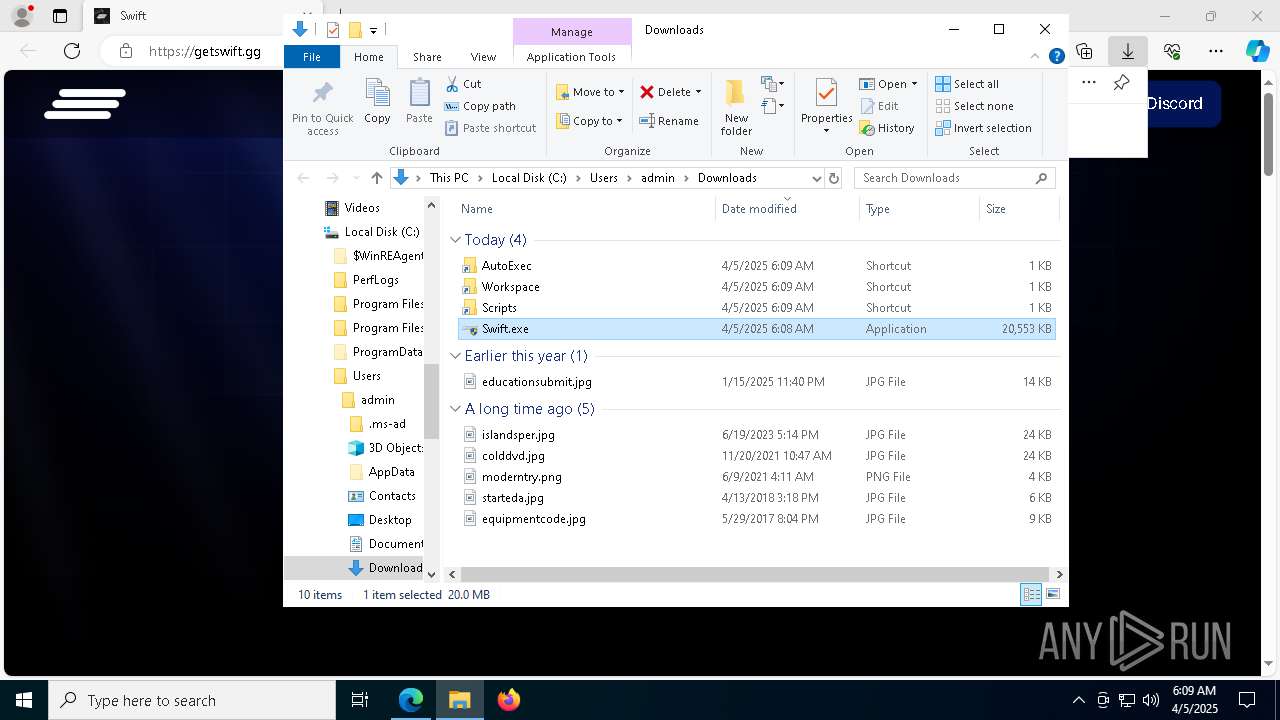
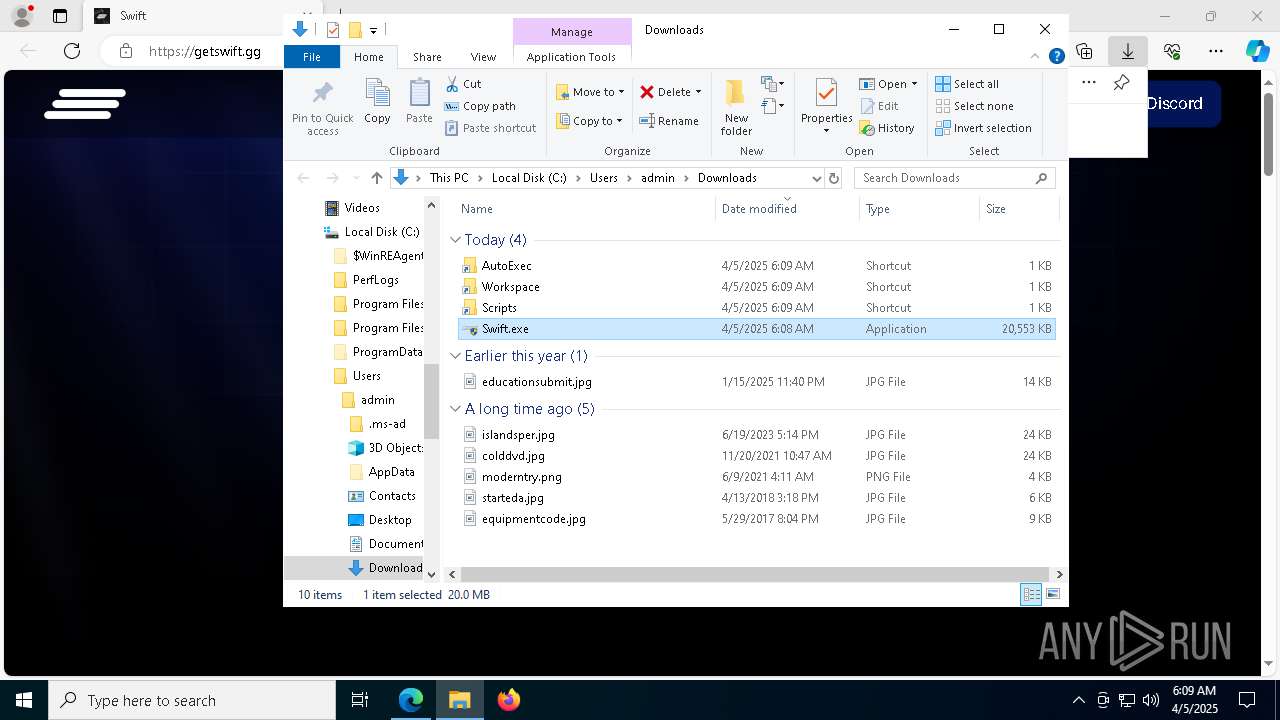
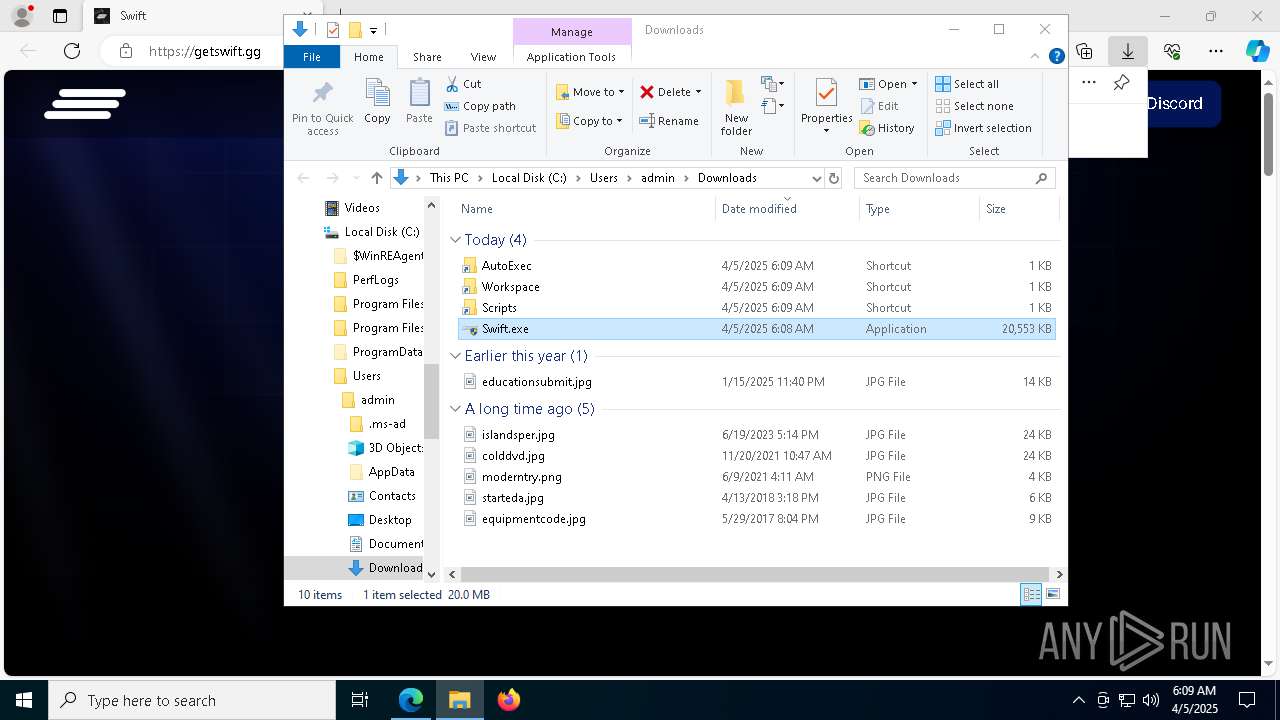
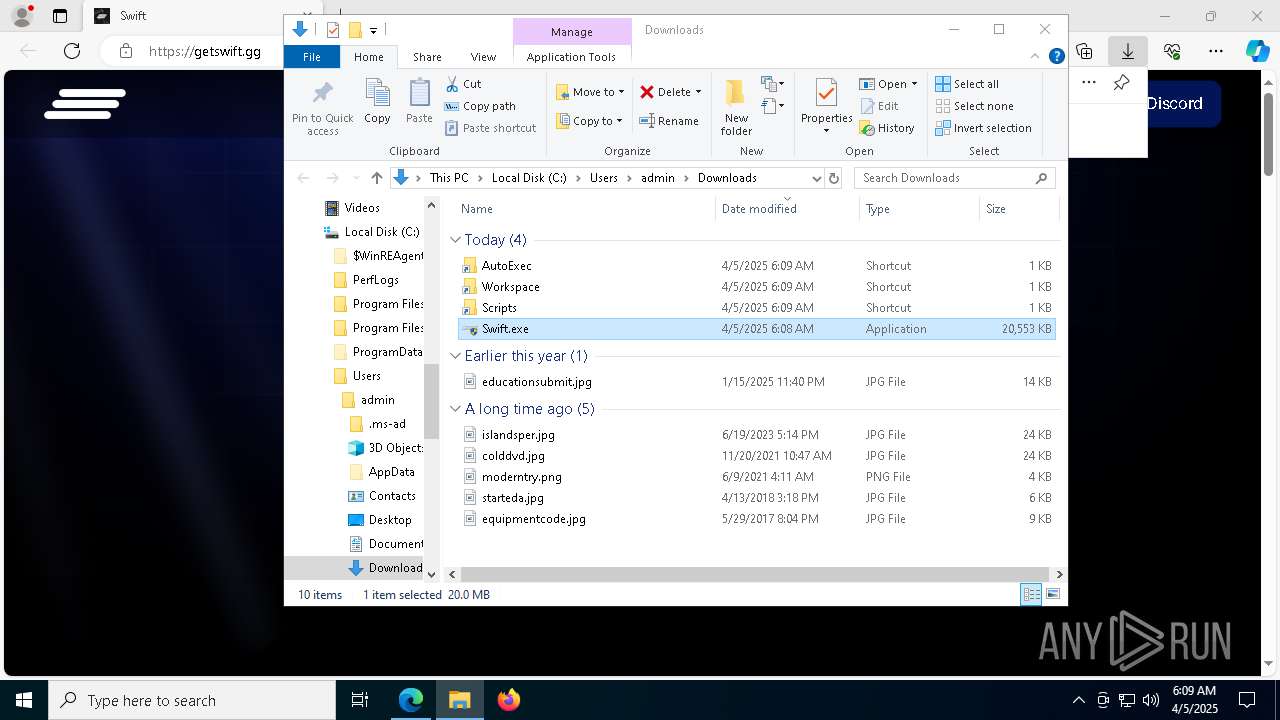
Autorun file from Downloads
- msedge.exe (PID: 8088)
- msedge.exe (PID: 668)
Process checks whether UAC notifications are on
- Swift.exe (PID: 7960)
- Swift.exe (PID: 6752)
Manual execution by a user
- Swift.exe (PID: 2420)
- Swift.exe (PID: 6752)
Application launched itself
- msedge.exe (PID: 668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
180
Monitored processes
49
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://getswift.gg/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "powershell" -WindowStyle Hidden -NoProfile -NonInteractive -Command "$WshShell = New-Object -comObject WScript.Shell; $Shortcut = $WshShell.CreateShortcut('C:\Users\admin\Downloads\AutoExec.lnk'); $Shortcut.TargetPath = 'C:\Users\admin\AppData\Roaming\Swift\AutoExec'; $Shortcut.Save()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Swift.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1520 --field-trial-handle=2280,i,16402973220783981466,13792401303261666192,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | "C:\Users\admin\Downloads\Swift.exe" | C:\Users\admin\Downloads\Swift.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: swift-new Exit code: 3221226540 Version: 0.1.0 Modules
| |||||||||||||||
| 2984 | "powershell" -WindowStyle Hidden -NoProfile -NonInteractive -Command "$WshShell = New-Object -comObject WScript.Shell; $Shortcut = $WshShell.CreateShortcut('C:\Users\admin\Downloads\Scripts.lnk'); $Shortcut.TargetPath = 'C:\Users\admin\AppData\Roaming\Swift\Scripts'; $Shortcut.Save()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Swift.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7832 --field-trial-handle=2280,i,16402973220783981466,13792401303261666192,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4228 | "powershell" -WindowStyle Hidden -NoProfile -NonInteractive -Command "$WshShell = New-Object -comObject WScript.Shell; $Shortcut = $WshShell.CreateShortcut('C:\Users\admin\Downloads\AutoExec.lnk'); $Shortcut.TargetPath = 'C:\Users\admin\AppData\Roaming\Swift\AutoExec'; $Shortcut.Save()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Swift.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4244 | "powershell" -WindowStyle Hidden -NoProfile -NonInteractive -Command "$WshShell = New-Object -comObject WScript.Shell; $Shortcut = $WshShell.CreateShortcut('C:\Users\admin\Downloads\Workspace.lnk'); $Shortcut.TargetPath = 'C:\Users\admin\AppData\Roaming\Swift\Workspace'; $Shortcut.Save()" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Swift.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 225
Read events
32 208
Write events
17
Delete events
0
Modification events
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 36EB8C1E98902F00 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 98ED971E98902F00 | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A90F1155-D379-4A6E-A1C9-49648D0AD800} | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1372F014-6597-4B58-8F55-C629ED3D83B2} | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2803901E-3772-4484-91AE-E12CDAEE773B} | |||
| (PID) Process: | (668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F75BD610-66C3-4759-A091-F36AA19BDC7C} | |||
Executable files
11
Suspicious files
231
Text files
49
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b5c5.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b5f4.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b603.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b5d5.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b613.TMP | — | |
MD5:— | SHA256:— | |||
| 668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
71
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
8828 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
8828 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
668 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7364 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7364 | msedge.exe | 104.26.4.120:443 | getswift.gg | CLOUDFLARENET | US | unknown |
7364 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7364 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
getswift.gg |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |