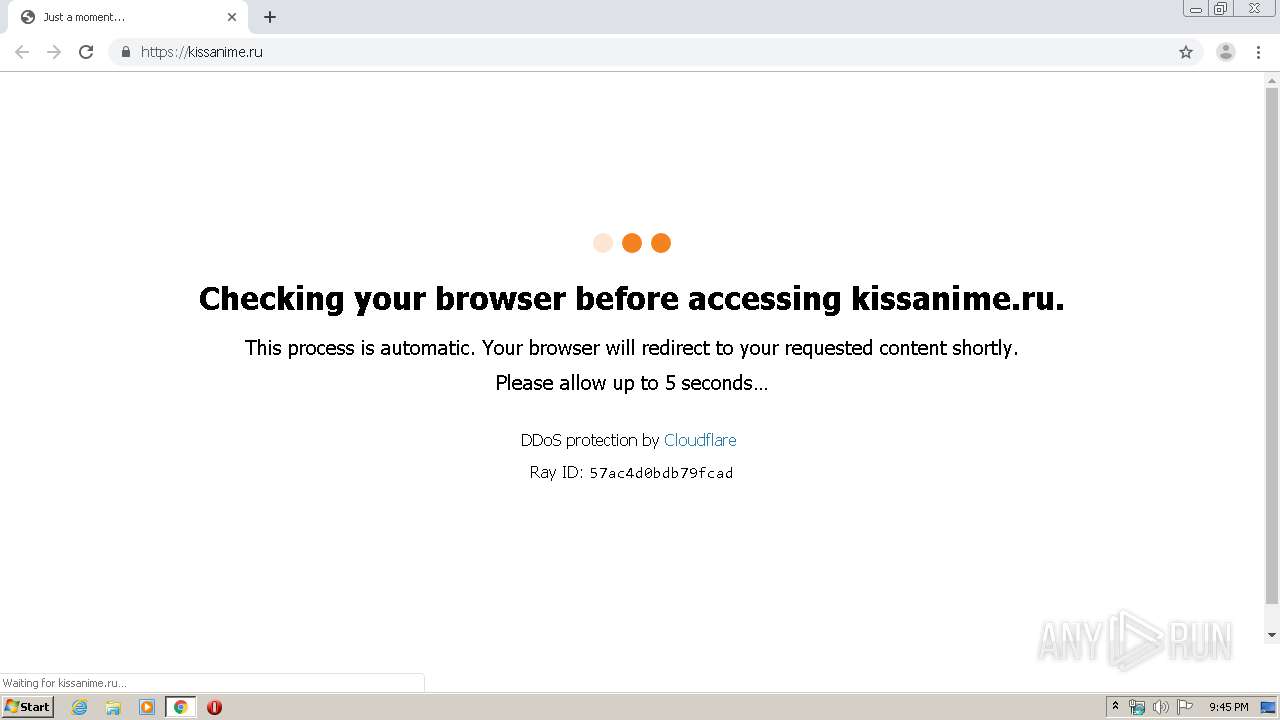
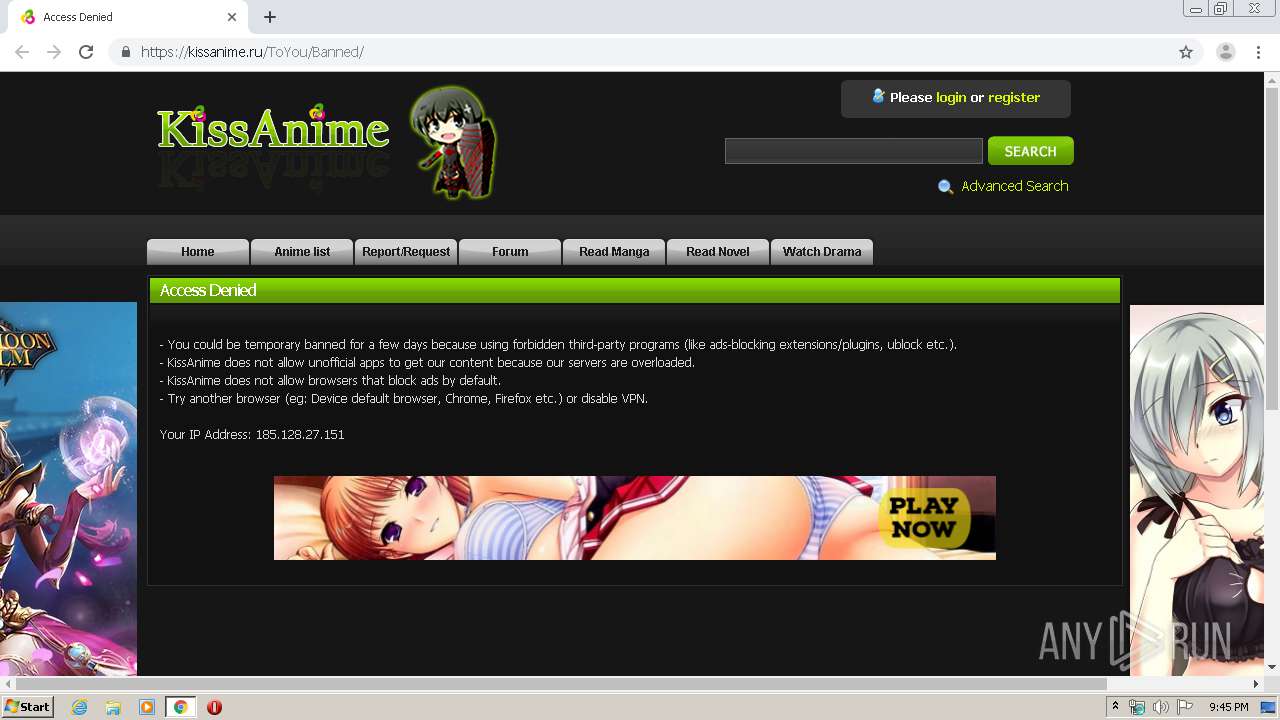
| URL: | http://www.kissanime.ru |
| Full analysis: | https://app.any.run/tasks/9df36c57-2d84-4500-a322-0d0f41362433 |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2020, 21:45:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 154BBAC3DA585762044D01B0A03A4D6A |
| SHA1: | 492ACE78240B0995EEFB579CD4B5BE538811CB85 |
| SHA256: | 0AC52F4BE06627AD6F506469C624694EB22BC2168792F5A693DBFA28FDD93024 |
| SSDEEP: | 3:N1KJS4tBQ:Cc4/Q |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1720)
INFO
Reads the hosts file
- chrome.exe (PID: 1720)
- chrome.exe (PID: 2648)
Reads settings of System Certificates
- chrome.exe (PID: 2648)
Application launched itself
- chrome.exe (PID: 1720)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14752951786025908288,2833826062875599267,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8709011566533318727 --mojo-platform-channel-handle=4424 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,14752951786025908288,2833826062875599267,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17806634943744066497 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4412 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14752951786025908288,2833826062875599267,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14140856693342300374 --mojo-platform-channel-handle=3512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.kissanime.ru" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2952 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,14752951786025908288,2833826062875599267,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8092457982313073856 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3840 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,14752951786025908288,2833826062875599267,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10696306519320008669 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14752951786025908288,2833826062875599267,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=125279131331180056 --mojo-platform-channel-handle=4124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,14752951786025908288,2833826062875599267,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10610815739084644374 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
681
Read events
598
Write events
78
Delete events
5
Modification events
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1720-13229819142862125 |
Value: 259 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
34
Text files
171
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E7E7407-6B8.pma | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3046e351-ec52-4a17-b467-94dbaa0e3579.tmp | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66bd2.TMP | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66c01.TMP | text | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66d87.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
31
DNS requests
25
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2648 | chrome.exe | GET | 301 | 104.22.1.150:80 | http://kissanime.ru/favicon.ico | US | — | — | whitelisted |
2648 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
2648 | chrome.exe | GET | 302 | 216.58.205.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 520 b | whitelisted |
2648 | chrome.exe | GET | 200 | 104.22.1.150:80 | http://kissanime.ru/cdn-cgi/images/trace/jschal/nojs/transparent.gif?ray=57ac4cf13fd159d0 | US | image | 42 b | whitelisted |
2648 | chrome.exe | GET | 503 | 104.22.1.150:80 | http://kissanime.ru/ | US | html | 13.4 Kb | whitelisted |
2648 | chrome.exe | GET | 200 | 104.22.1.150:80 | http://kissanime.ru/cdn-cgi/images/trace/jschal/js/transparent.gif?ray=57ac4cf13fd159d0 | US | image | 42 b | whitelisted |
2648 | chrome.exe | GET | 200 | 74.125.99.91:80 | http://r5---sn-hpa7kn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.128.27.151&mm=28&mn=sn-hpa7kn7s&ms=nvh&mt=1585345511&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2648 | chrome.exe | POST | 301 | 104.22.1.150:80 | http://kissanime.ru/?__cf_chl_jschl_tk__=0e4d21e09c2d149b46db1f94d232c1b63bd895df-1585345548-0-AR1AEOGtIYLhhQX19FwDrdCtJUX2-dWuKk5mnrT1O7RQgGe-C3nBdLLxQfJLN5HACsYg3JPgsm-IPfP-Mi7ie1SKr2W-5j8AEWZzJ7aUWxnbM42npTyCi1e8kxZi647OGP_KDfqCMwyiGRKt3NIRL-1RGF_Ie-117P6DIY9MSxWP_kohjbG81iWxmw0jIn7QfVG3EpaAvKz4DtA5QZxW1JmjP5iSmSIbHPSiaf30m1n-4d3nBHekdG7EDf9W8yMy5rbkKdsNKPZ_hKcgG9KdS2o | US | image | 42 b | whitelisted |
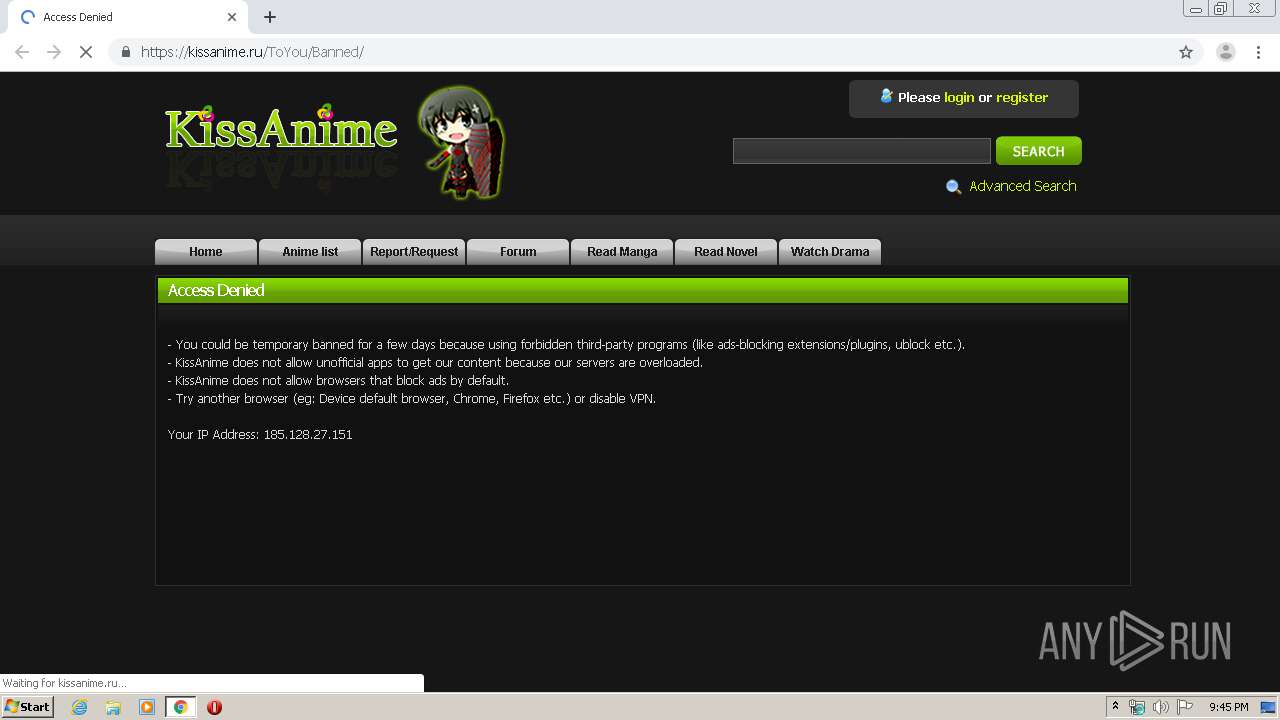
2648 | chrome.exe | POST | 301 | 104.22.1.150:80 | http://www.kissanime.ru/?__cf_chl_jschl_tk__=bc22673b93543f472739b9aeec515fee505901d5-1585345544-0-Af3NJdM1kBFROmiP88s4IxwgC9x-AwVhTCmIl2O7e-YR8YXo8spzSRSeaZc9CA554tinrw4EaMKlCWQQXdiEhIjtgsHOAF6o-Hb2C56ytXDeE8dAcfL9JwSjkCOx9kXcQwgkyZpqfmTCwis2Cd0Tn58cM9bfa0-k9eJKscg7HtaZjwD04dckV975hVvvFSgXXVJebDg63Ls6B35mqefbyLtpPJxXoTCL4fEWmeOJcE-qDcpBG1ueDzznCasrrylQ4KKDaqjqbUebP-hm7-To5Fo | US | image | 42 b | suspicious |
2648 | chrome.exe | GET | 200 | 74.125.99.91:80 | http://r5---sn-hpa7kn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=185.128.27.151&mm=28&mn=sn-hpa7kn7s&ms=nvh&mt=1585345511&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2648 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 104.22.1.150:80 | www.kissanime.ru | Cloudflare Inc | US | suspicious |
2648 | chrome.exe | 104.22.1.150:443 | www.kissanime.ru | Cloudflare Inc | US | suspicious |
2648 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2648 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 172.217.23.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 216.58.205.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 216.58.205.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2648 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kissanime.ru |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.cloudflare.com |
| whitelisted |
kissanime.ru |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-hpa7kn7s.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2648 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |
2648 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains pass= in cleartext |