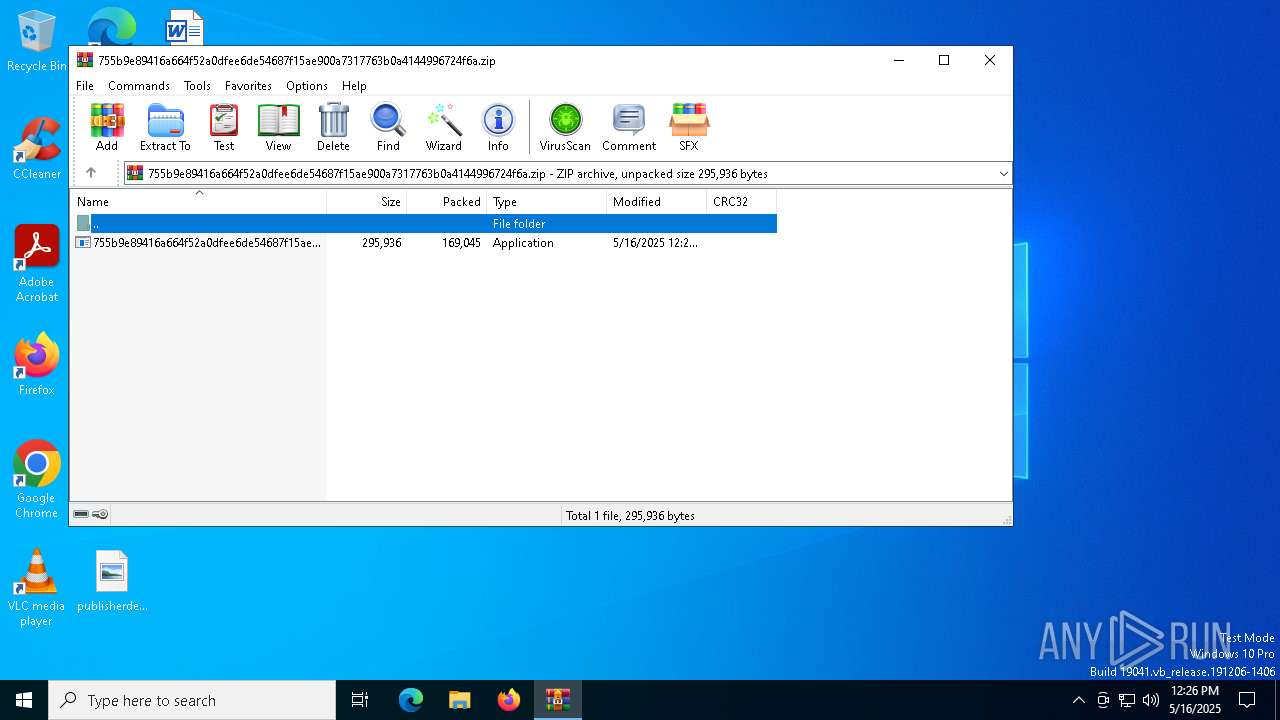
| File name: | 755b9e89416a664f52a0dfee6de54687f15ae900a7317763b0a4144996724f6a.zip |
| Full analysis: | https://app.any.run/tasks/829540cd-bcd3-4c02-96f3-4621610e1ada |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 12:26:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 063683BFB6DED458CFDF66C292B106FD |
| SHA1: | 19632BE655B7EDDC8161383F25CF6BFF29A35C86 |
| SHA256: | 0ABB65FF912DF2897E946A0F22EADD954207A2124DC8E49766DB45BAA78F05BE |
| SSDEEP: | 3072:0upGsvYI1fr1Qo+4MejSXXGEKqLkbN3FlotzN6YuGDj2PtsIj1Q5UfqfvR+:0UGKYGj1Qp0SHxfLETlUzAYaFKUfGvR+ |
MALICIOUS
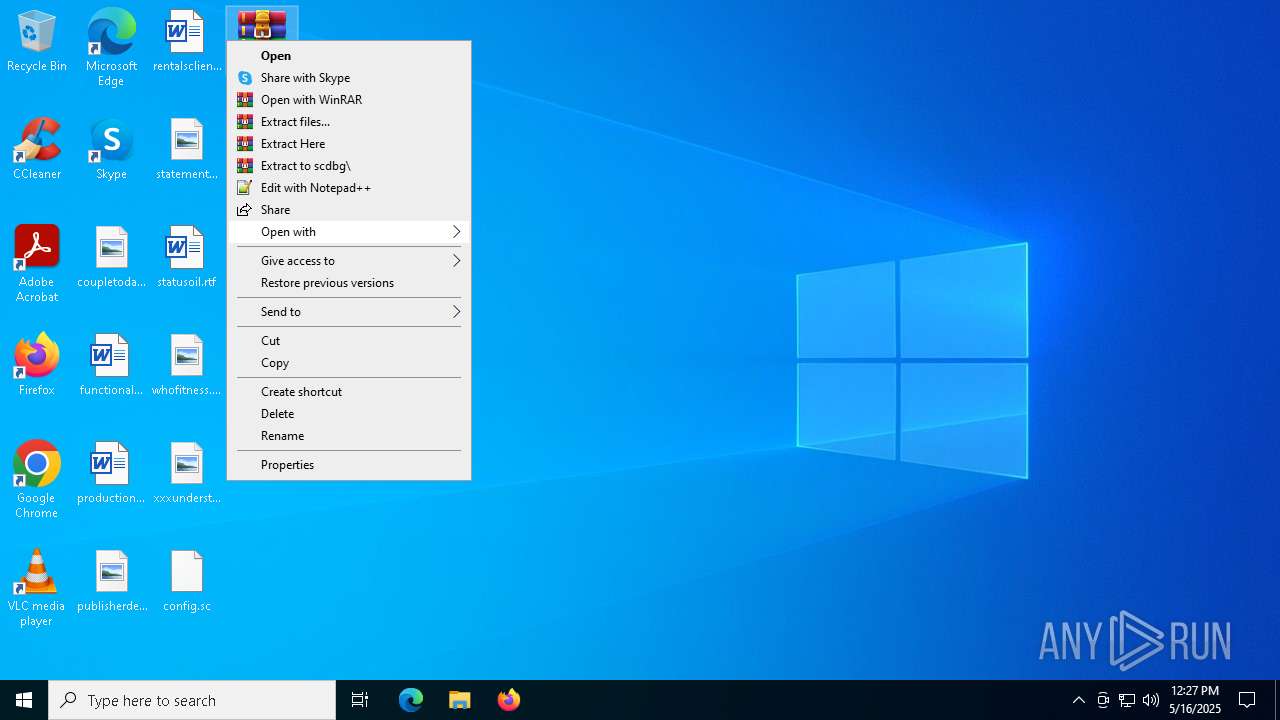
Generic archive extractor
- WinRAR.exe (PID: 6656)
SUSPICIOUS
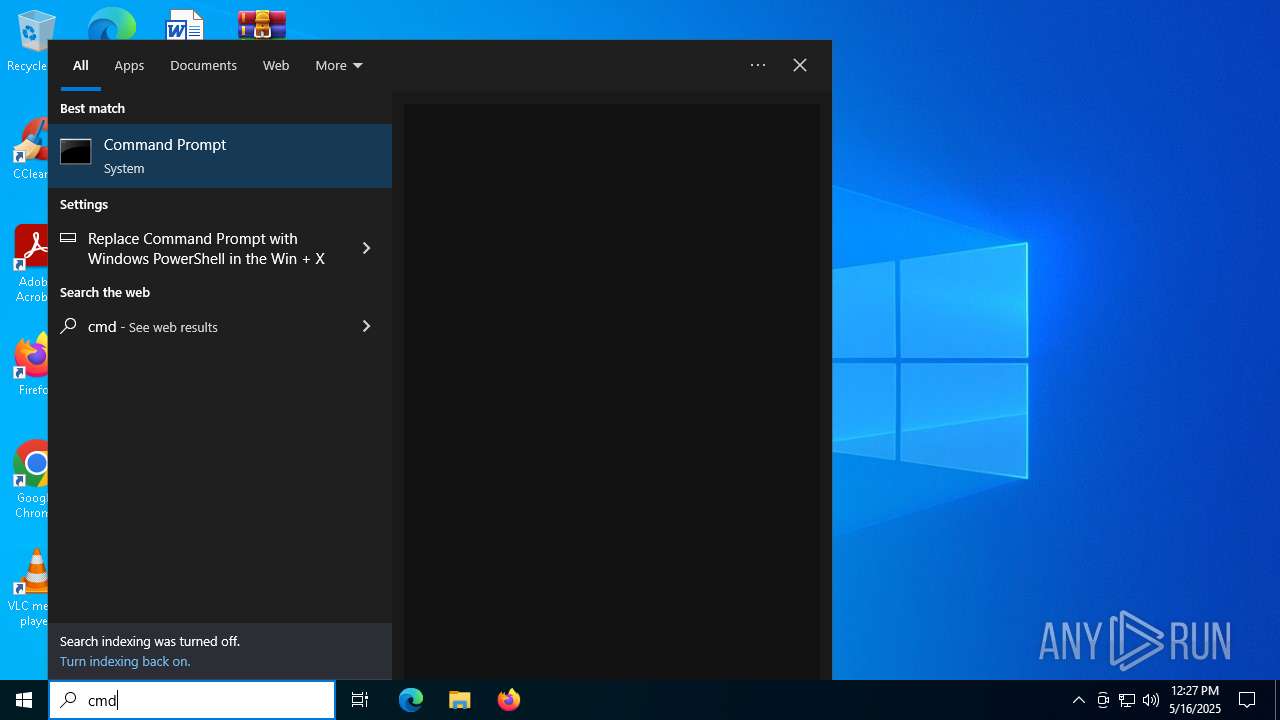
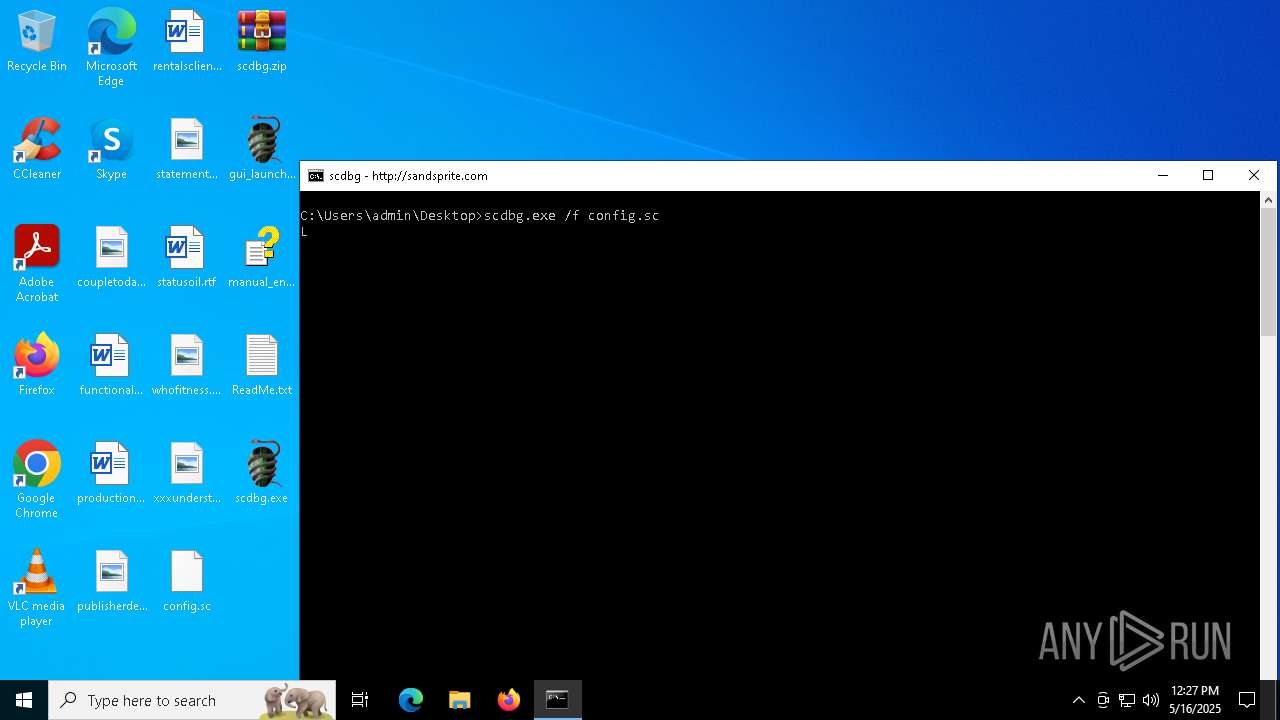
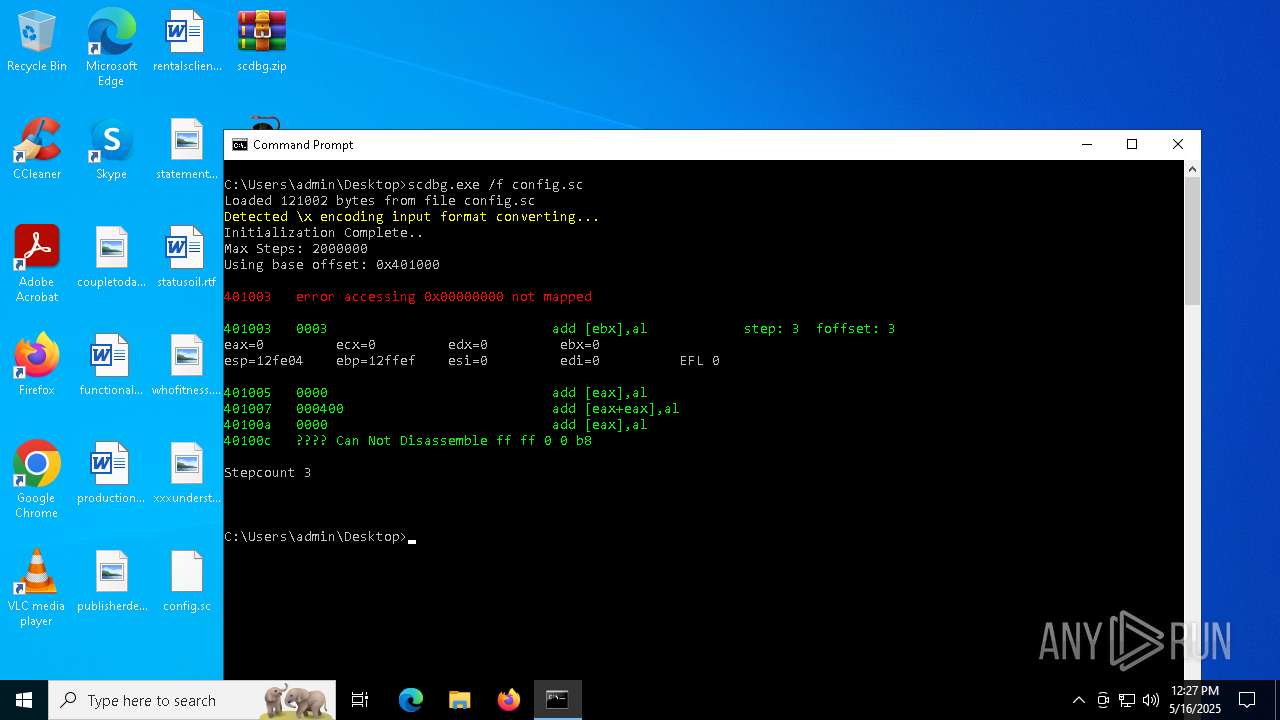
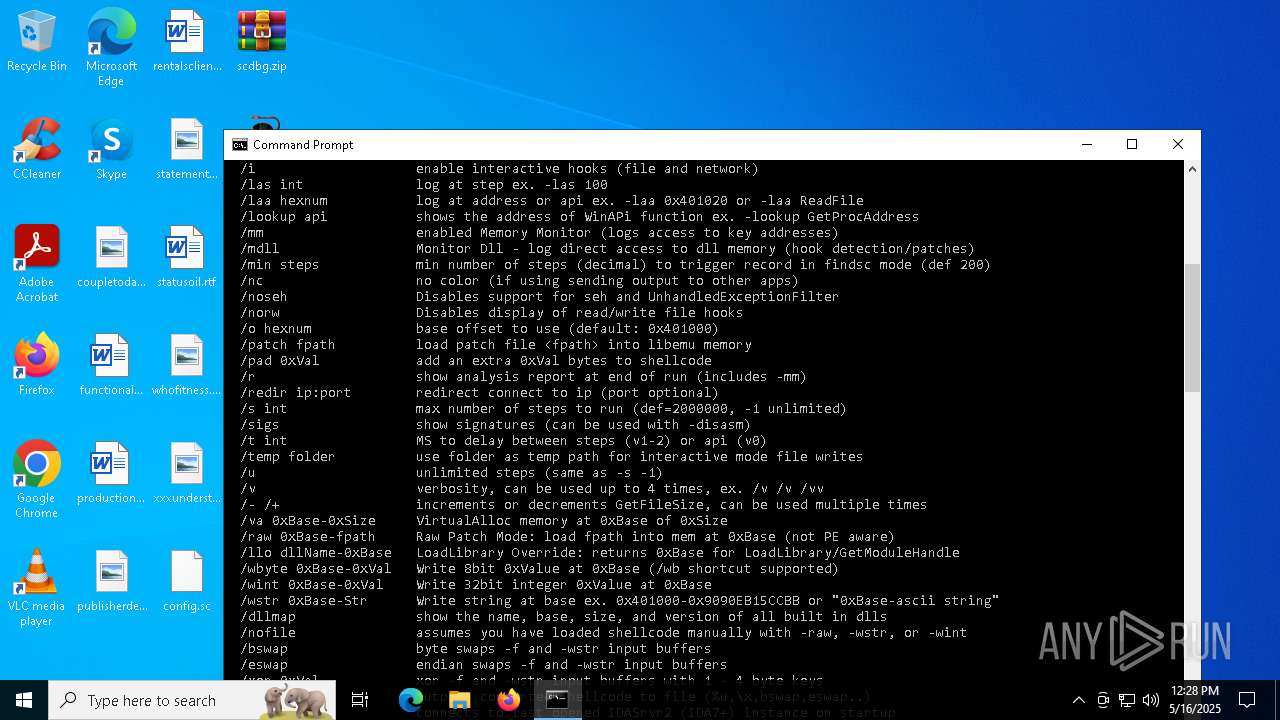
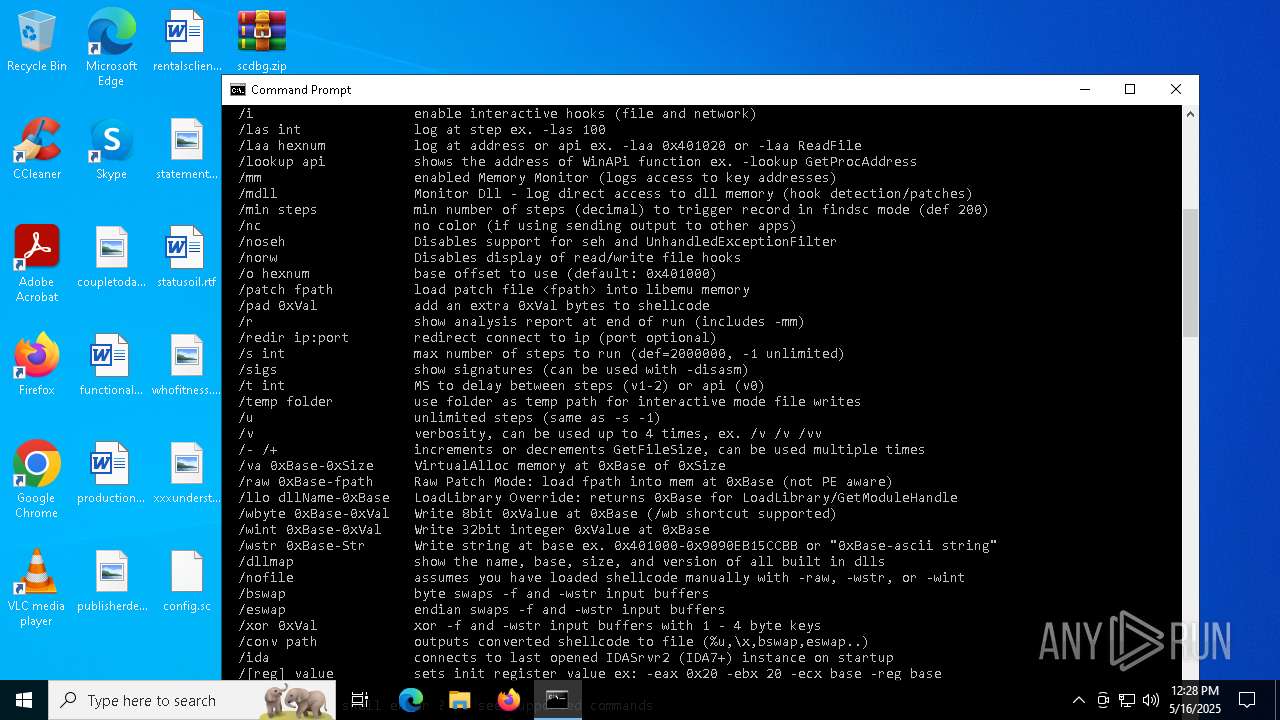
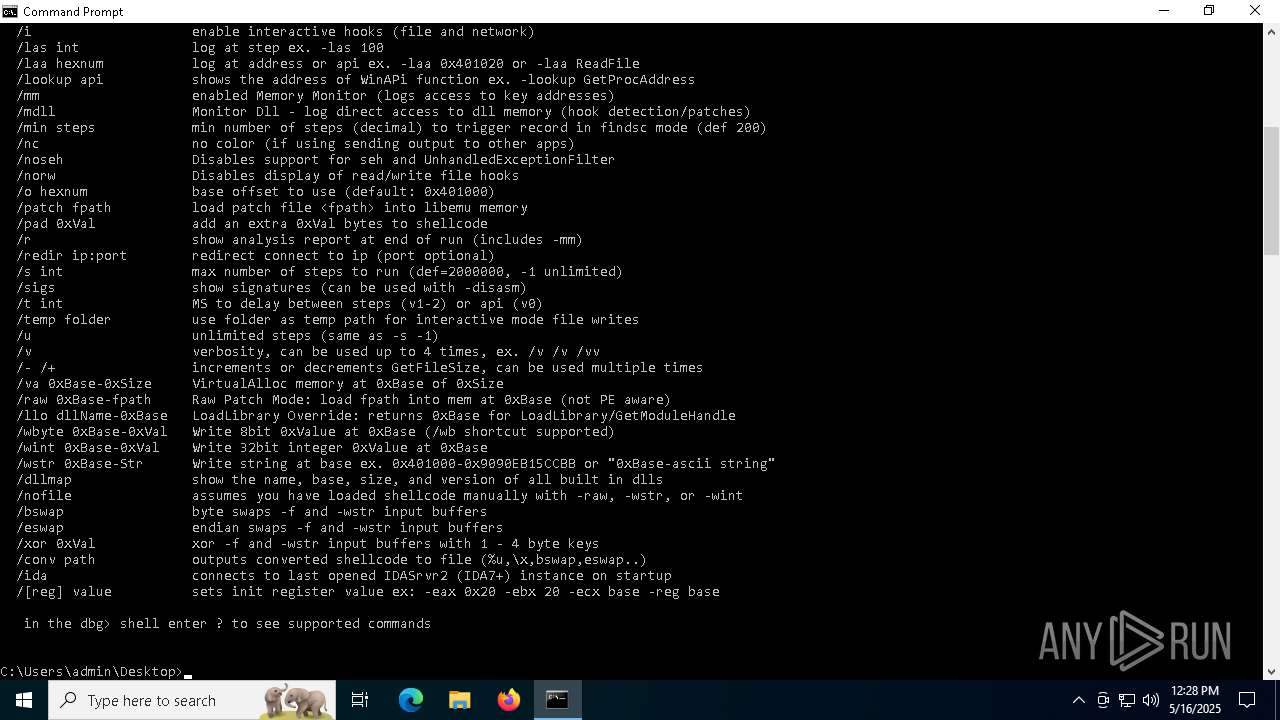
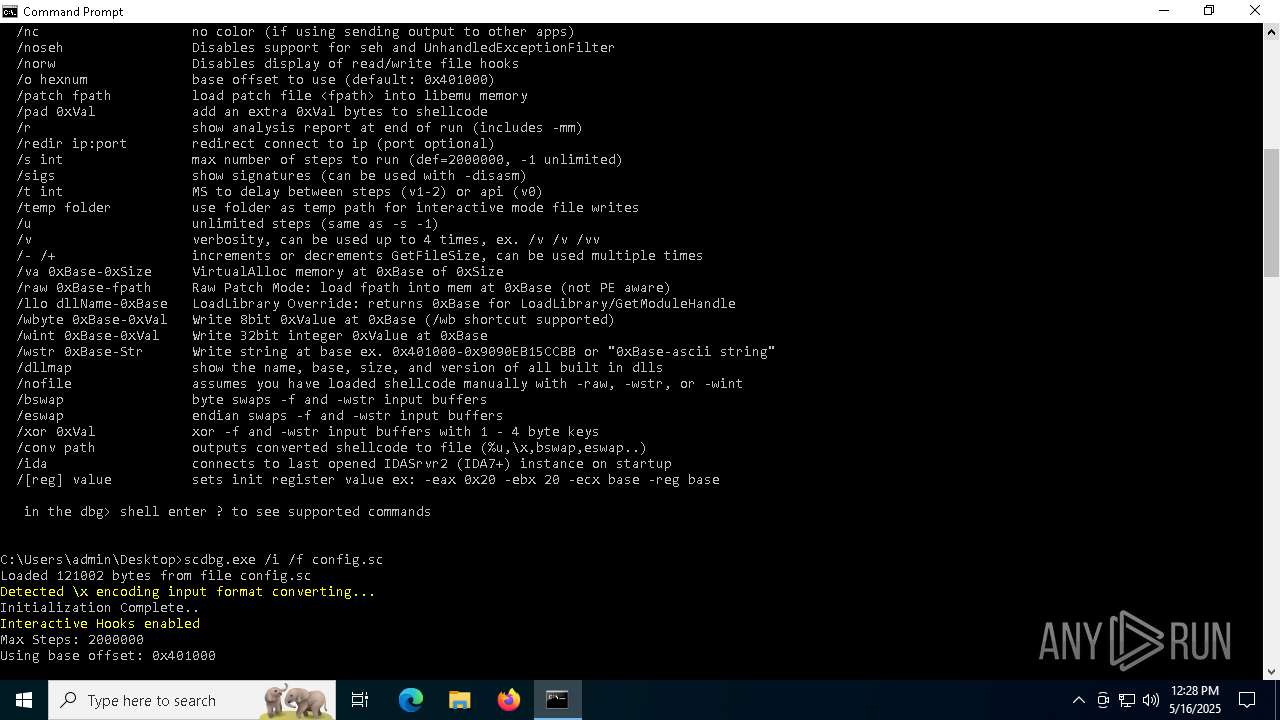
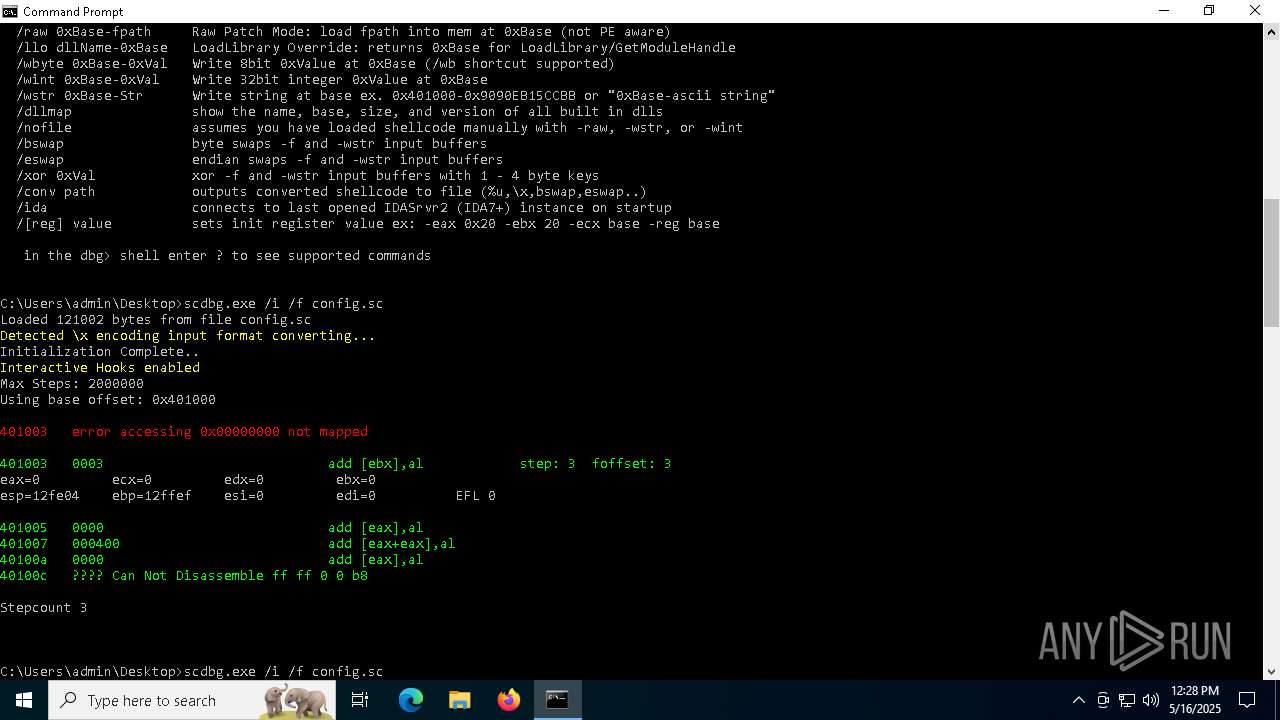
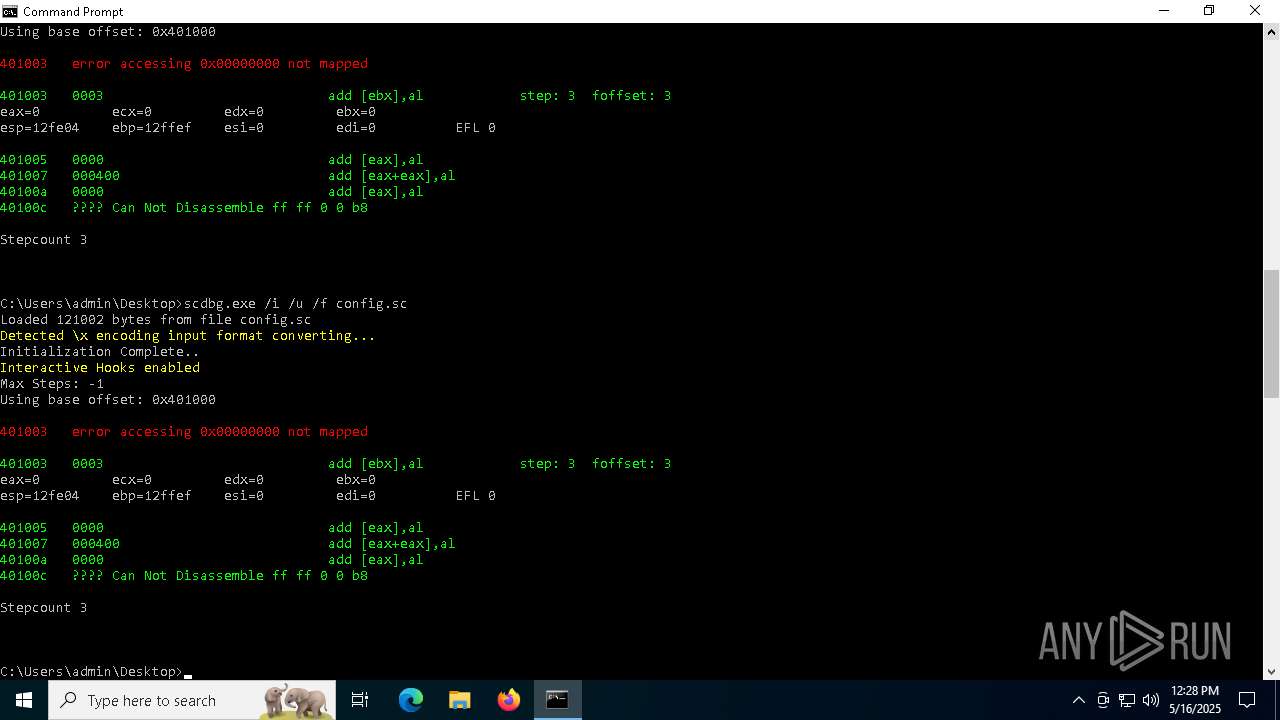
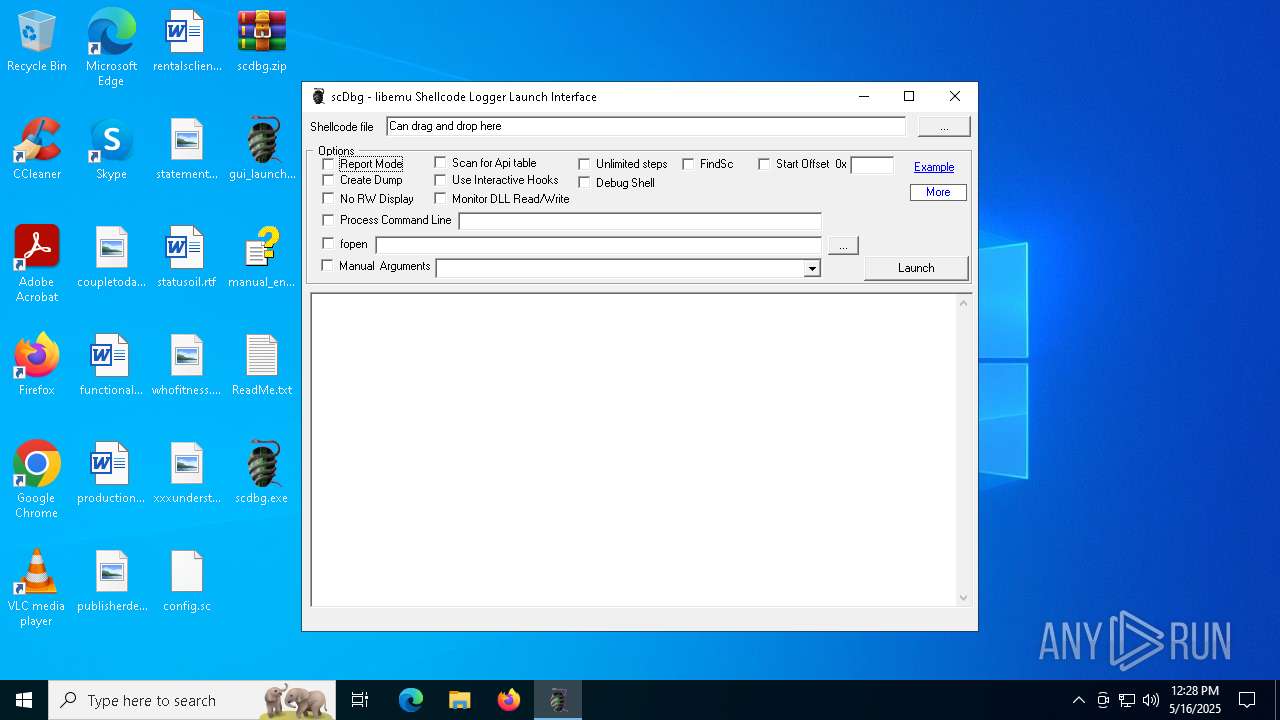
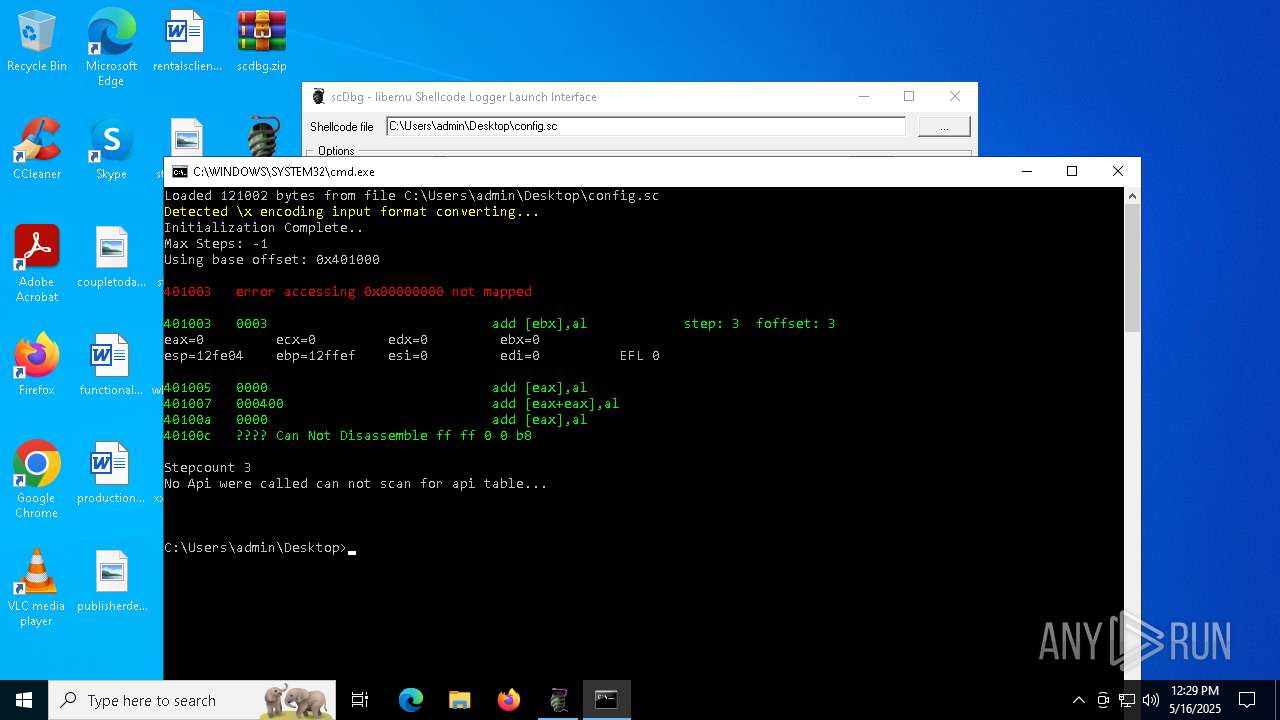
Starts CMD.EXE for commands execution
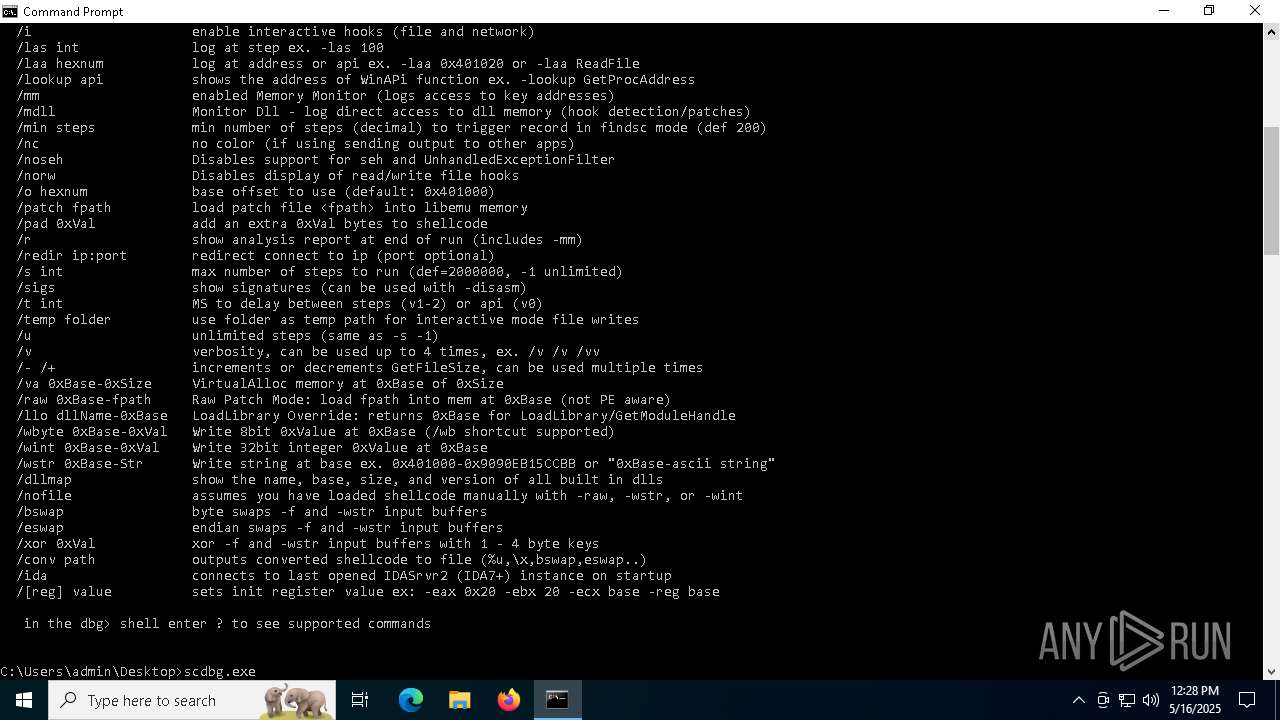
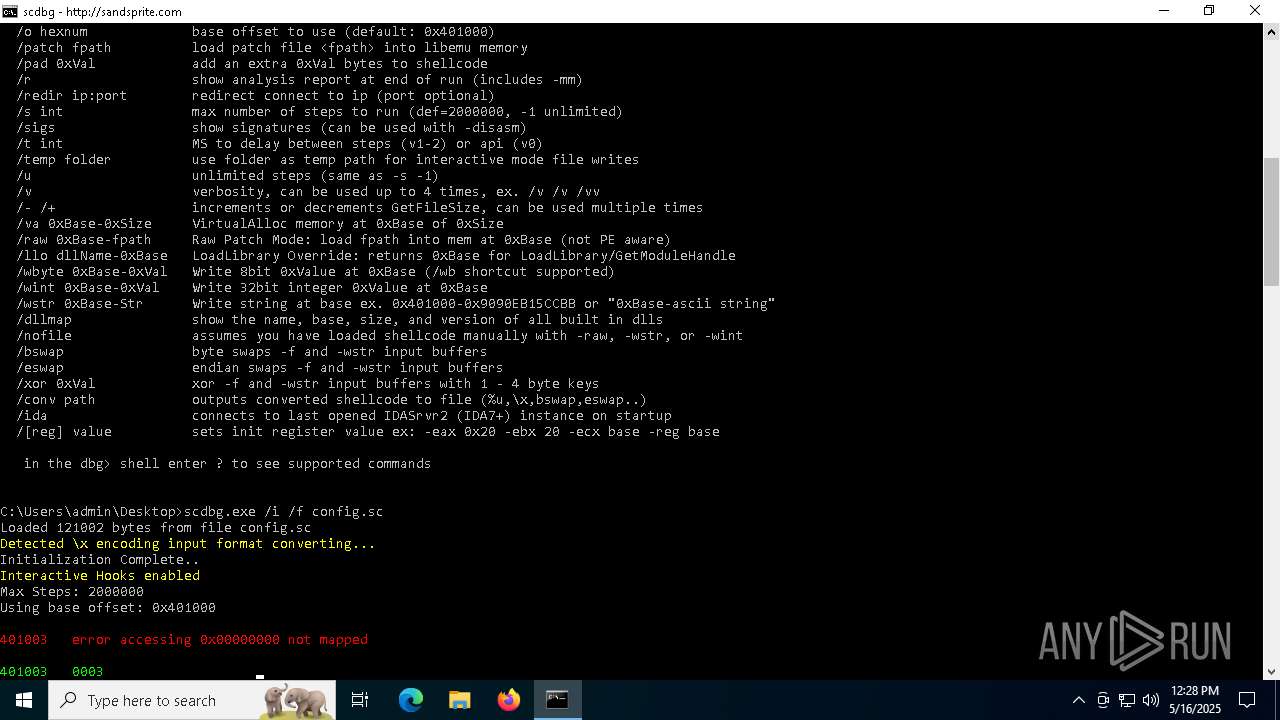
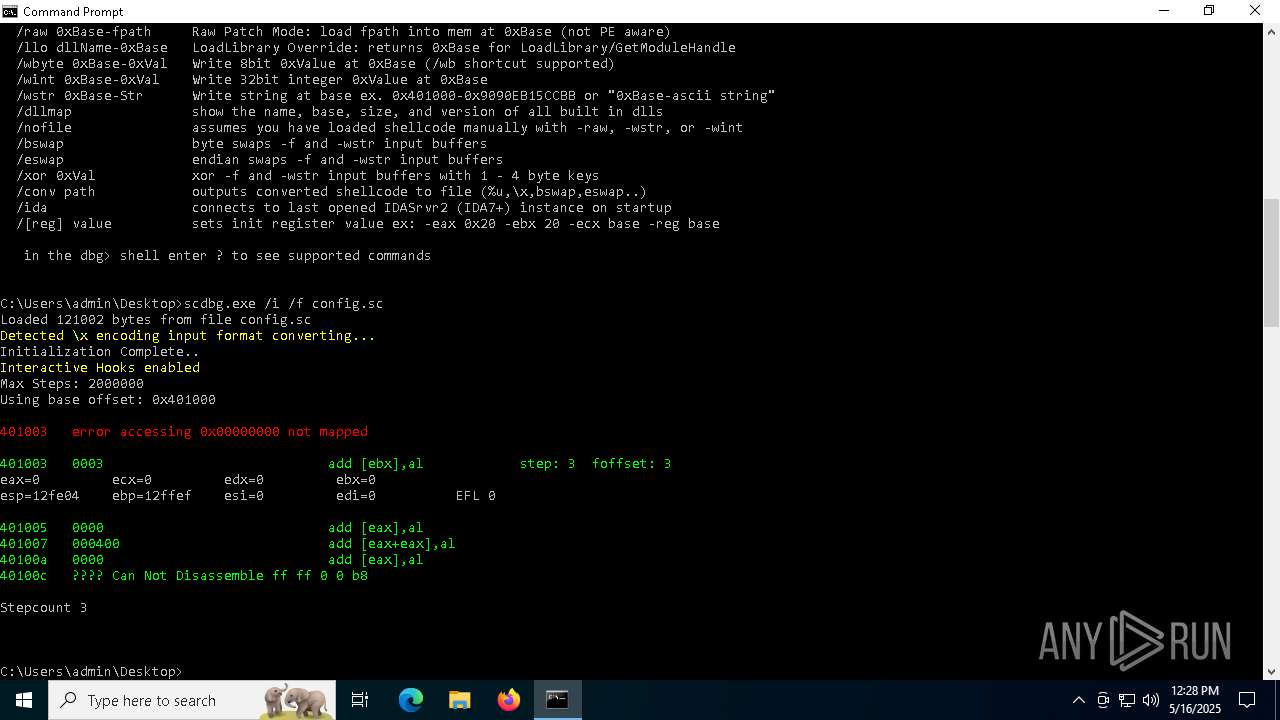
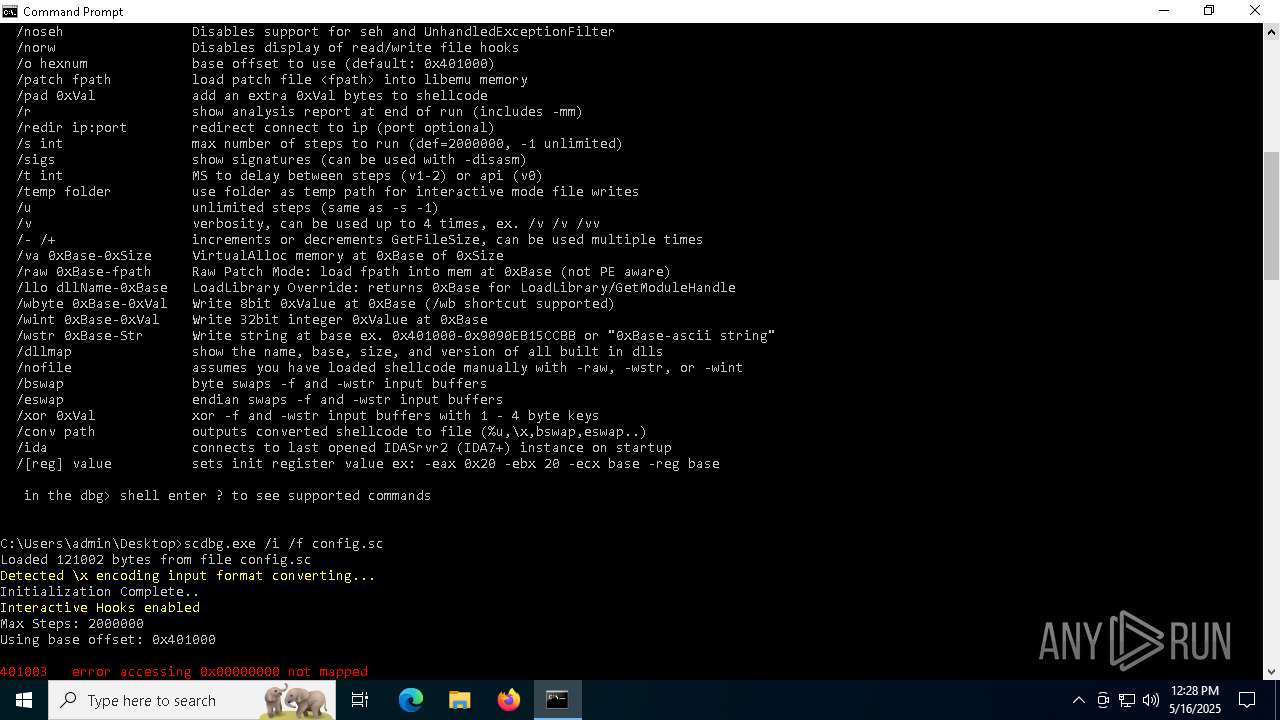
- scdbg.exe (PID: 2516)
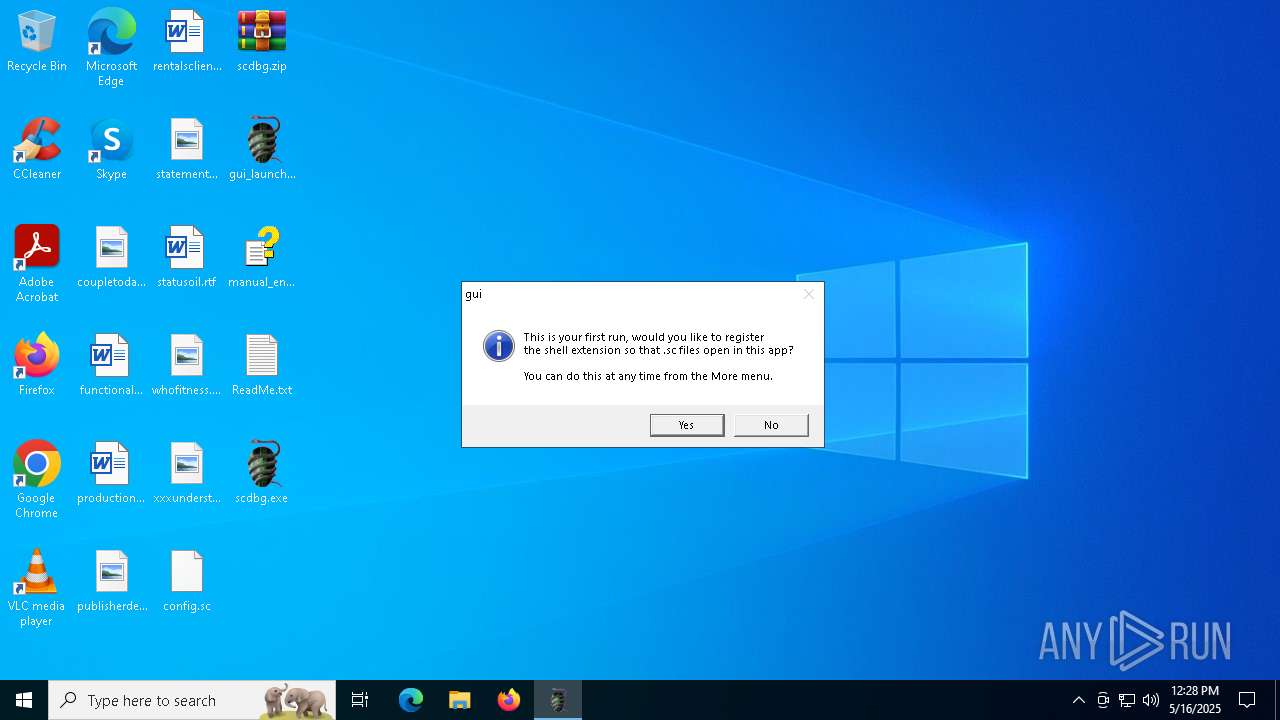
- gui_launcher.exe (PID: 6576)
- gui_launcher.exe (PID: 6940)
Reads security settings of Internet Explorer
- gui_launcher.exe (PID: 6940)
- gui_launcher.exe (PID: 6576)
There is functionality for taking screenshot (YARA)
- scdbg.exe (PID: 2504)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2516)
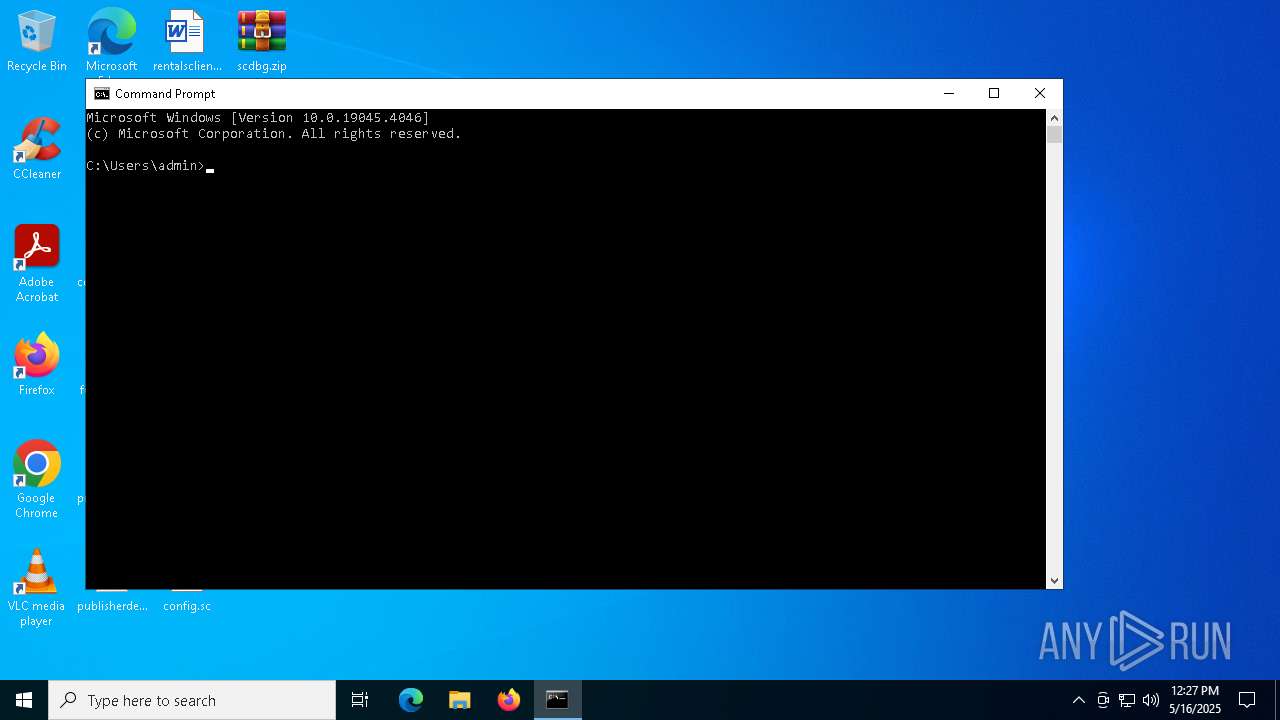
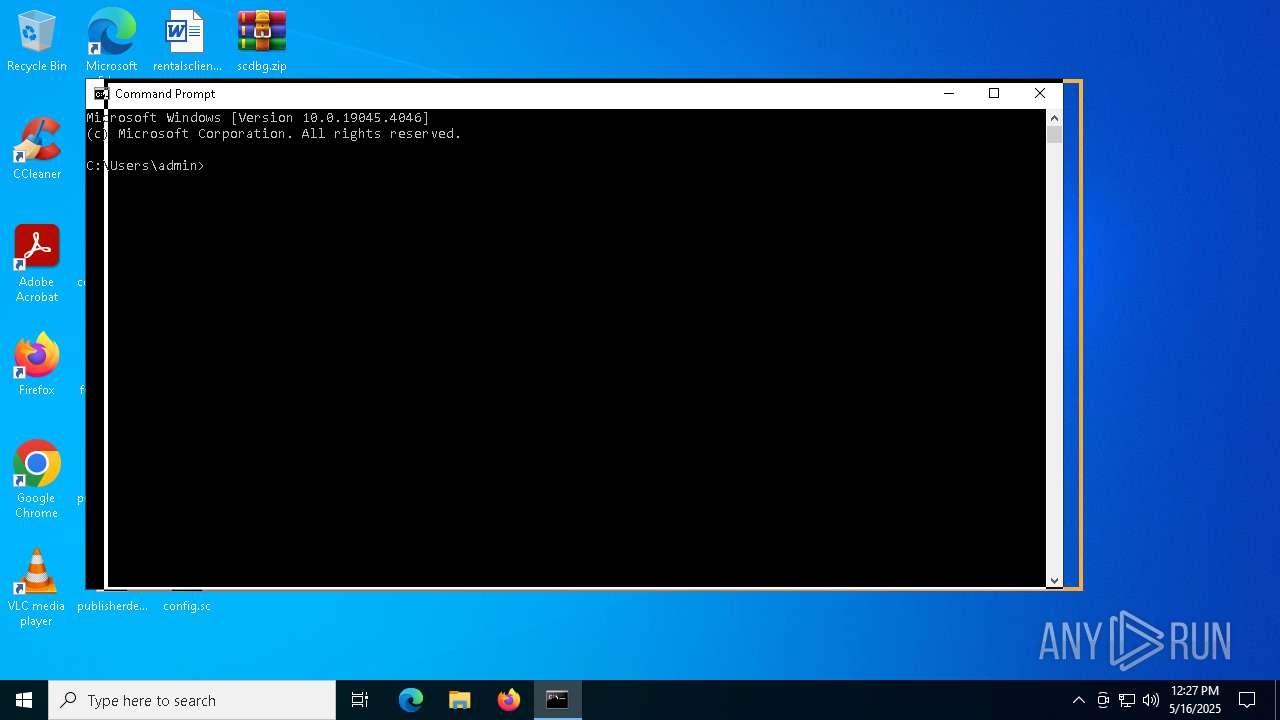
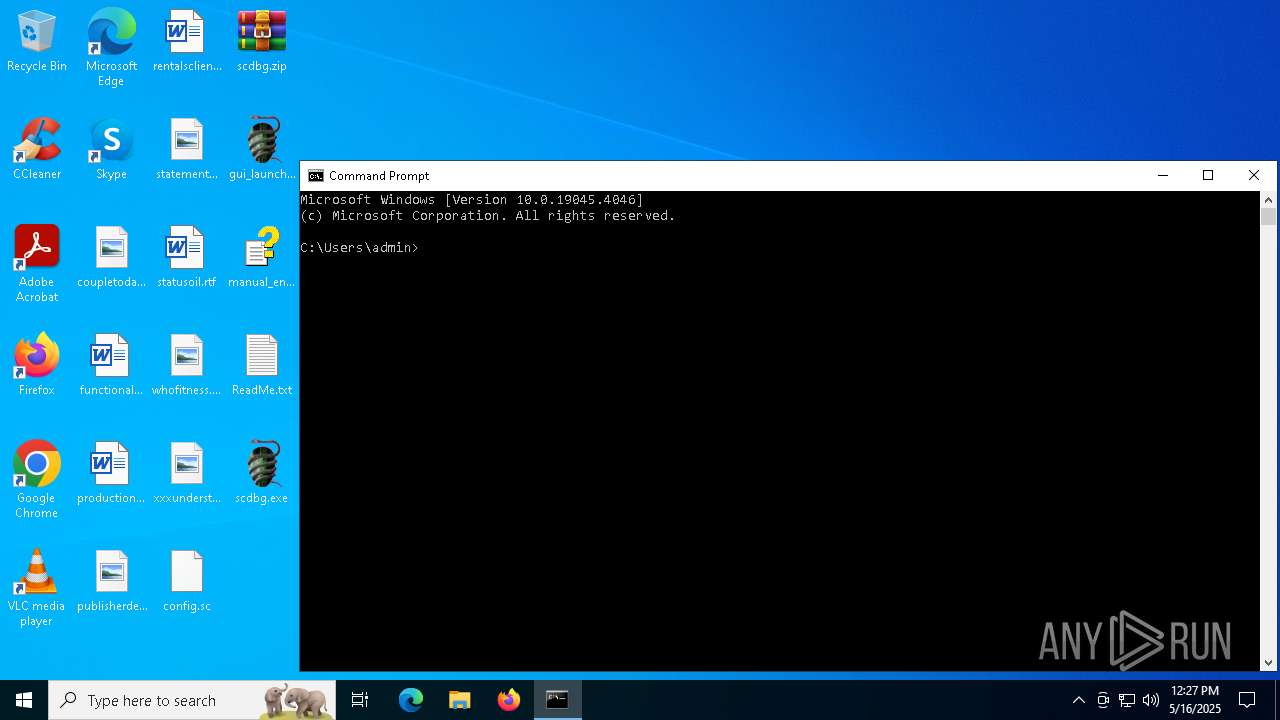
Manual execution by a user
- WinRAR.exe (PID: 2516)
- cmd.exe (PID: 1676)
- gui_launcher.exe (PID: 6576)
- gui_launcher.exe (PID: 6940)
Reads the software policy settings
- slui.exe (PID: 4776)
- slui.exe (PID: 864)
The sample compiled with english language support
- WinRAR.exe (PID: 2516)
Checks supported languages
- scdbg.exe (PID: 5720)
- scdbg.exe (PID: 6300)
- scdbg.exe (PID: 2516)
- scdbg.exe (PID: 2420)
- scdbg.exe (PID: 6240)
- scdbg.exe (PID: 4172)
- scdbg.exe (PID: 5624)
- scdbg.exe (PID: 2904)
- gui_launcher.exe (PID: 6940)
- gui_launcher.exe (PID: 6576)
- scdbg.exe (PID: 6808)
Reads the computer name
- gui_launcher.exe (PID: 6576)
- gui_launcher.exe (PID: 6940)
Create files in a temporary directory
- gui_launcher.exe (PID: 6576)
- gui_launcher.exe (PID: 6940)
Checks proxy server information
- slui.exe (PID: 864)
UPX packer has been detected
- scdbg.exe (PID: 2504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:16 12:21:16 |
| ZipCRC: | 0x2efbd210 |
| ZipCompressedSize: | 169045 |
| ZipUncompressedSize: | 295936 |
| ZipFileName: | 755b9e89416a664f52a0dfee6de54687f15ae900a7317763b0a4144996724f6a.exe |
Total processes
168
Monitored processes
35
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | cmd /c ftype Shellcode.Document="C:\Users\admin\Desktop\gui_launcher.exe" %1 && assoc .sc=Shellcode.Document | C:\Windows\SysWOW64\cmd.exe | — | gui_launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
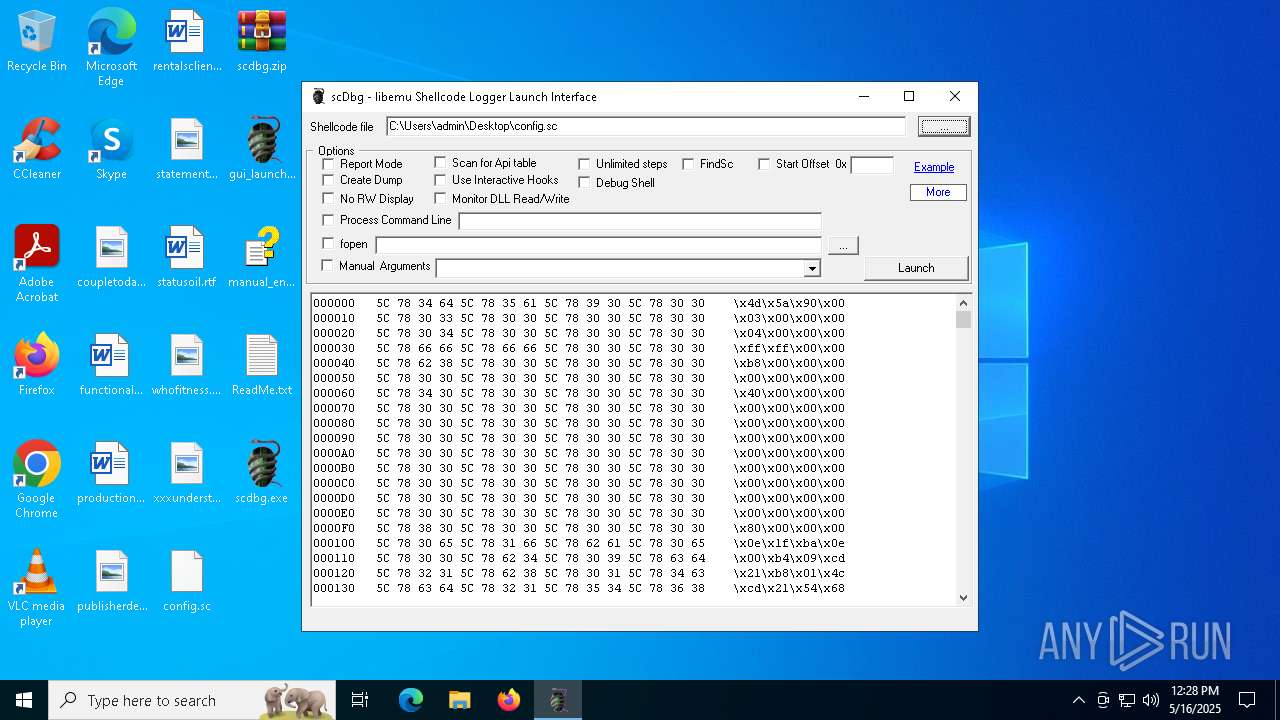
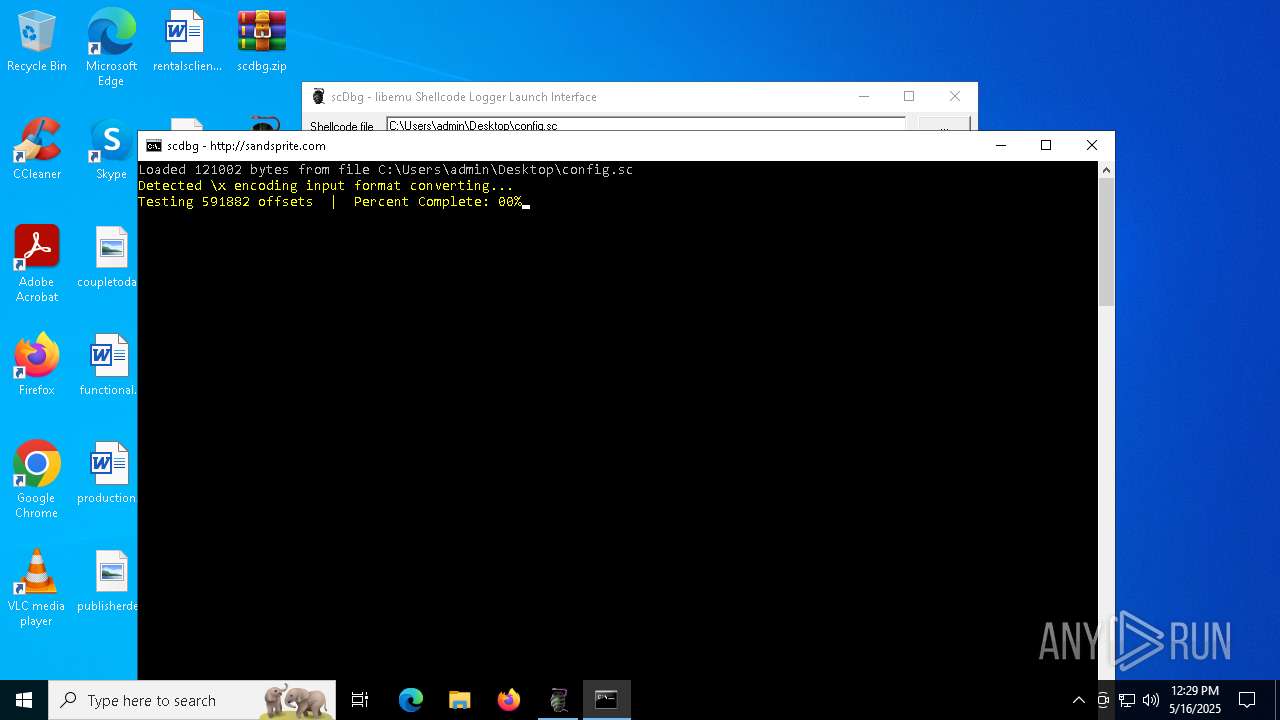
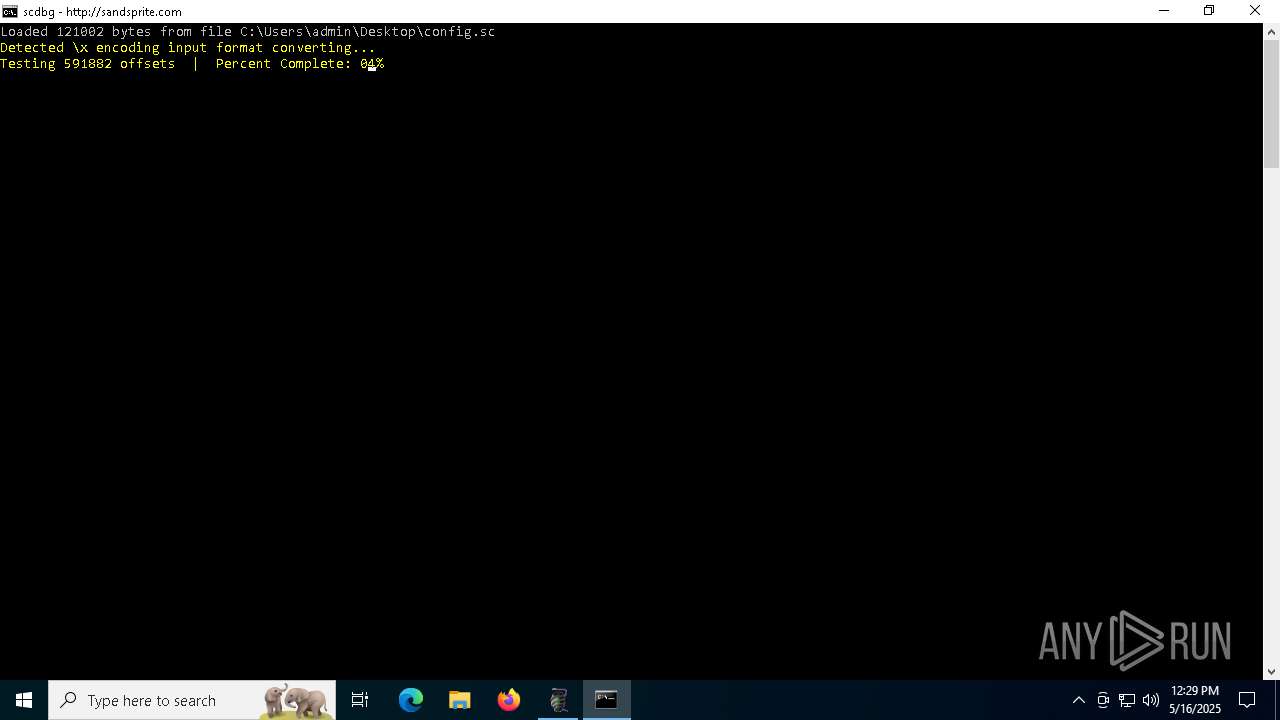
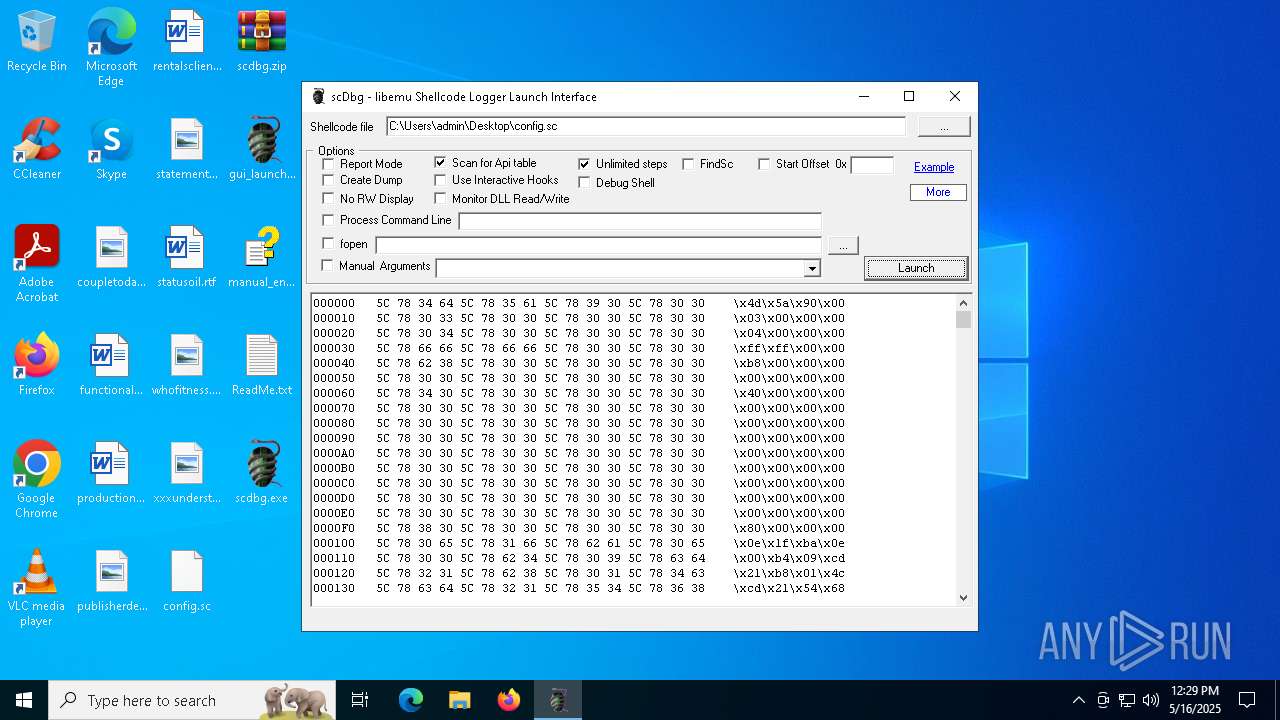
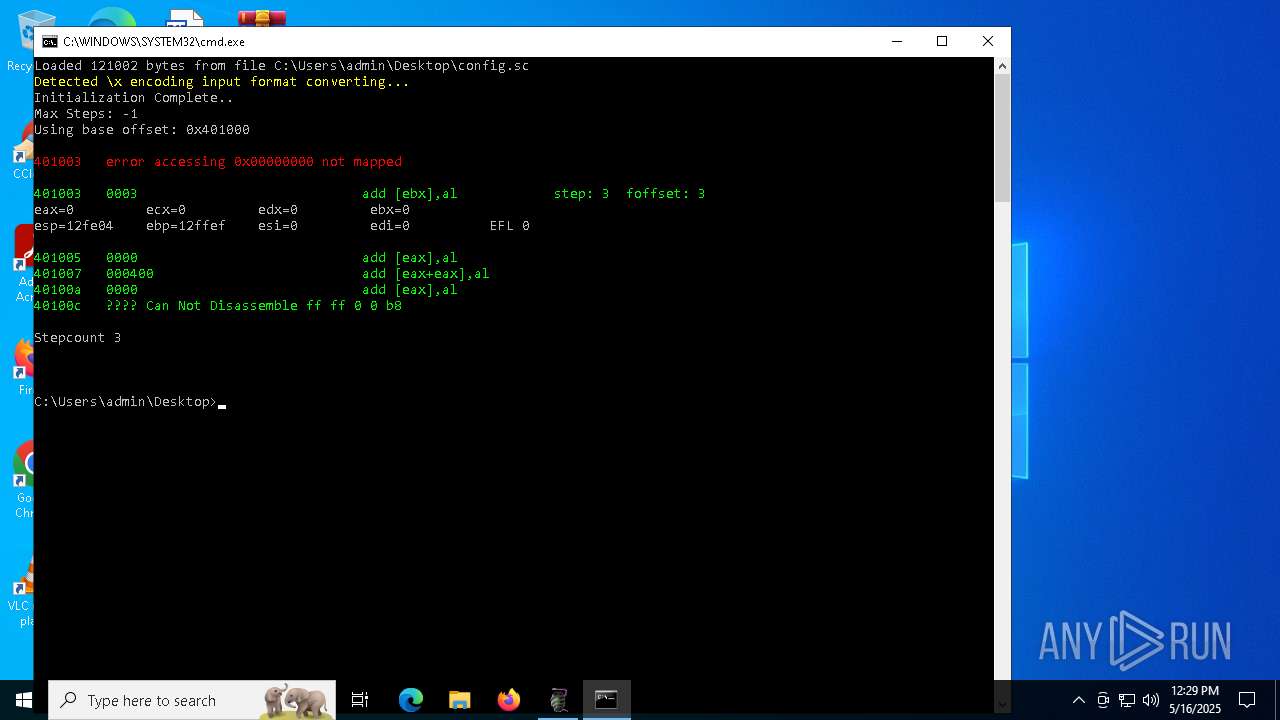
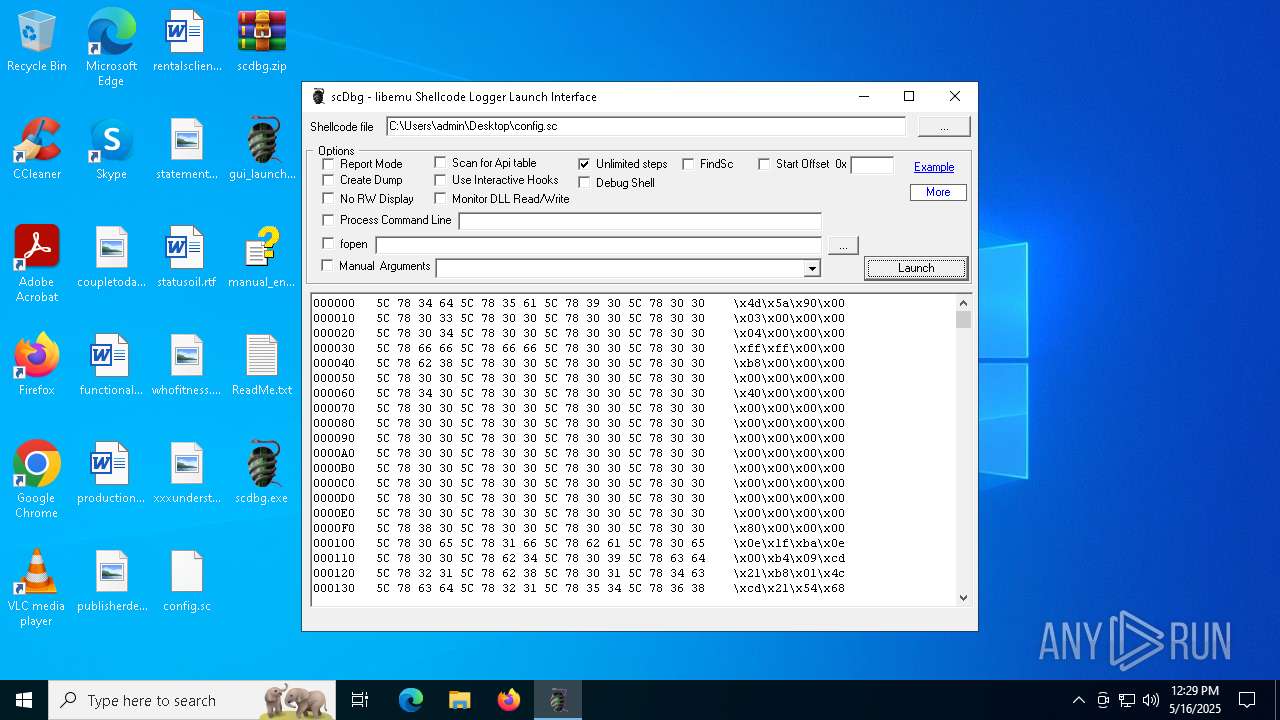
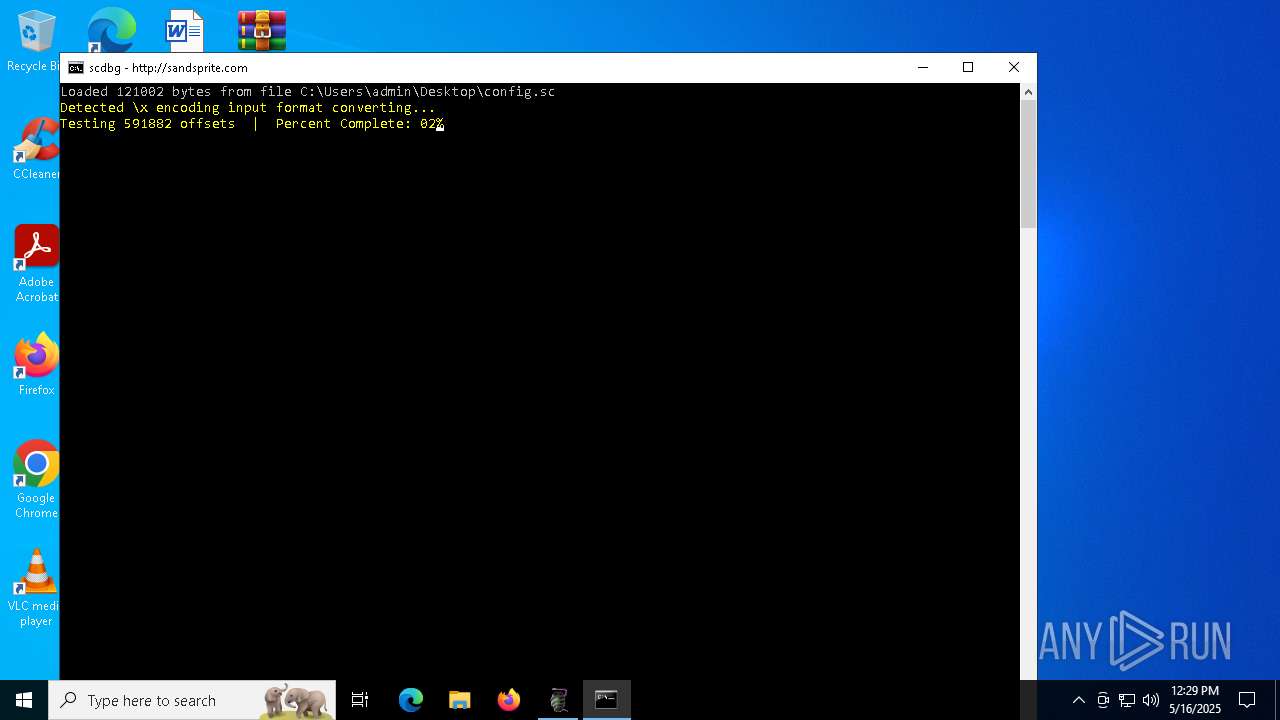
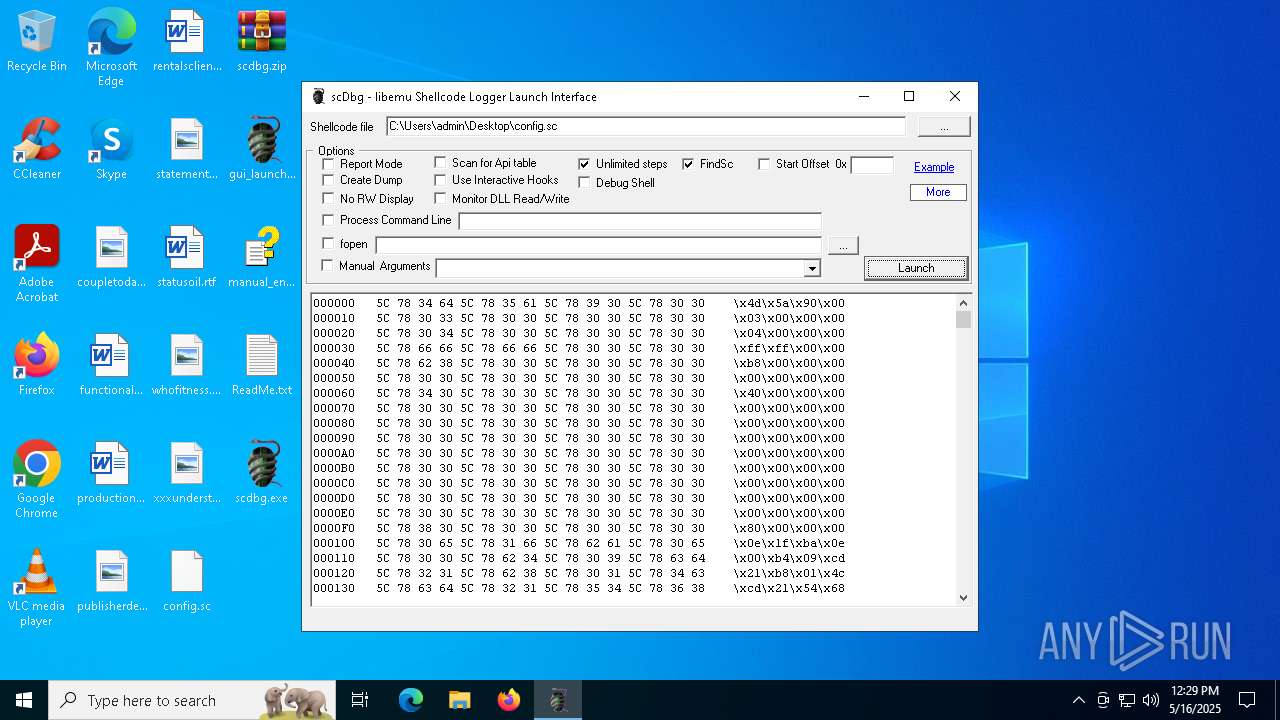
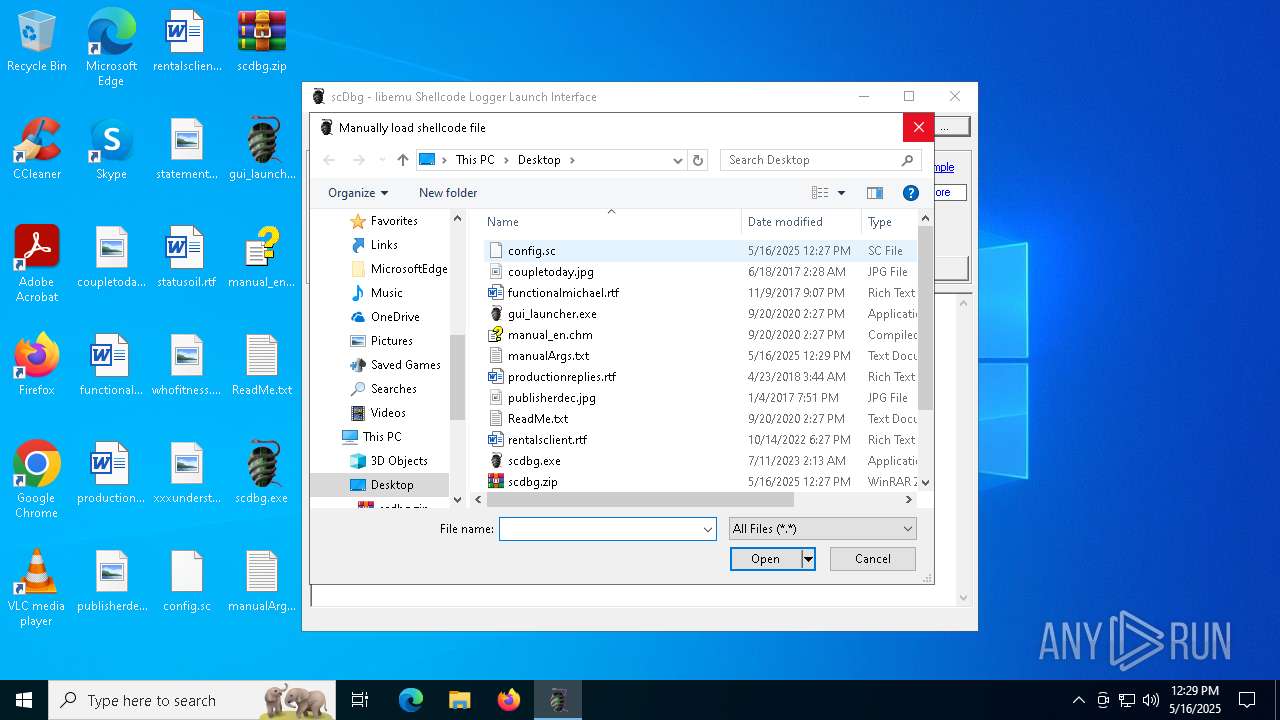
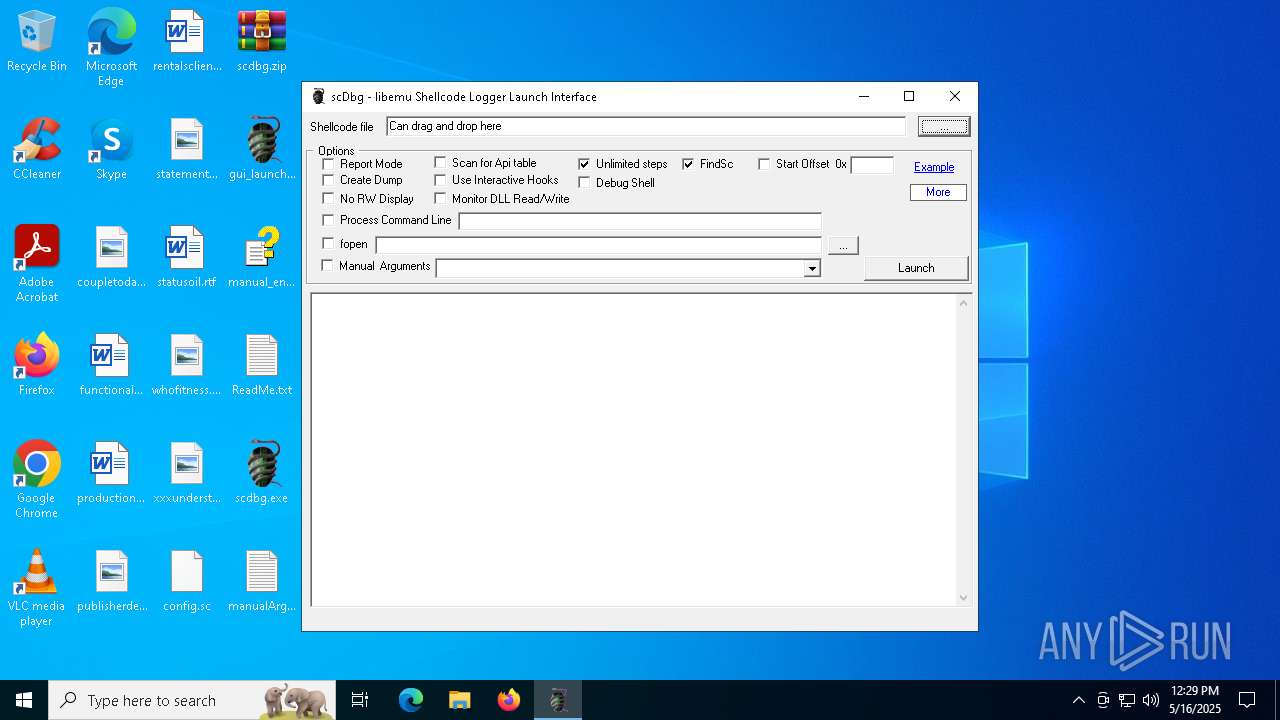
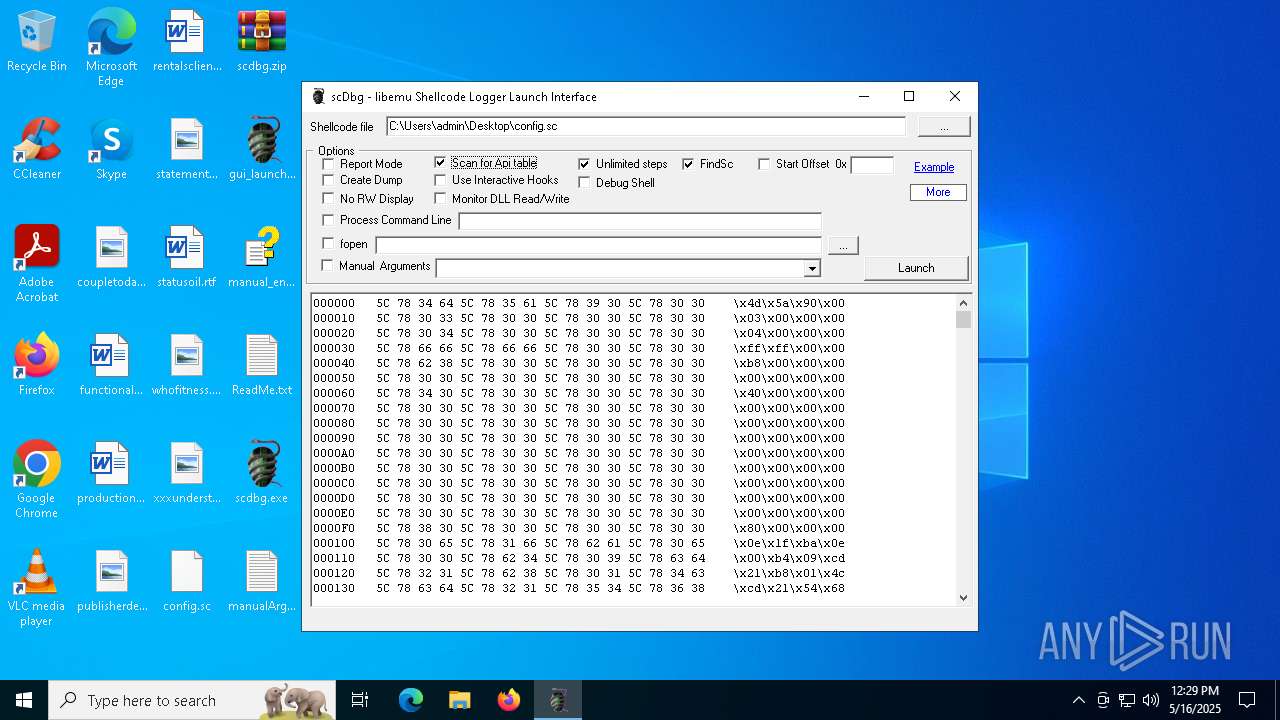
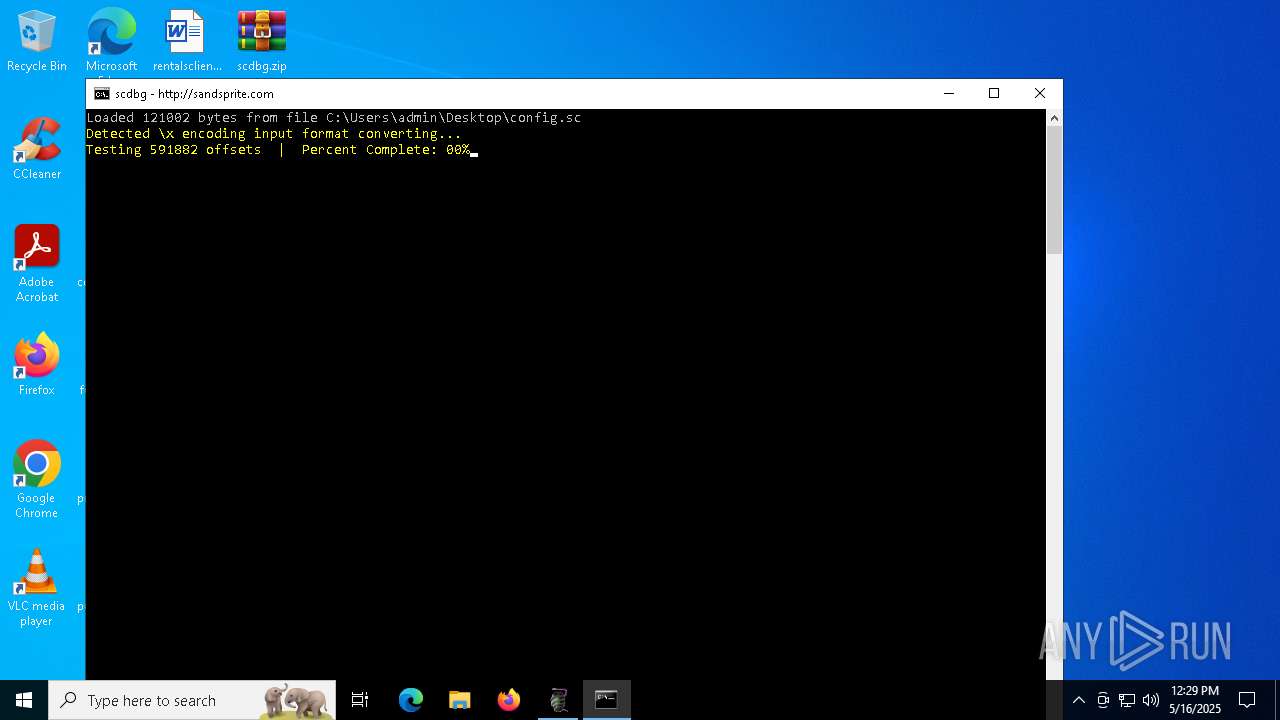
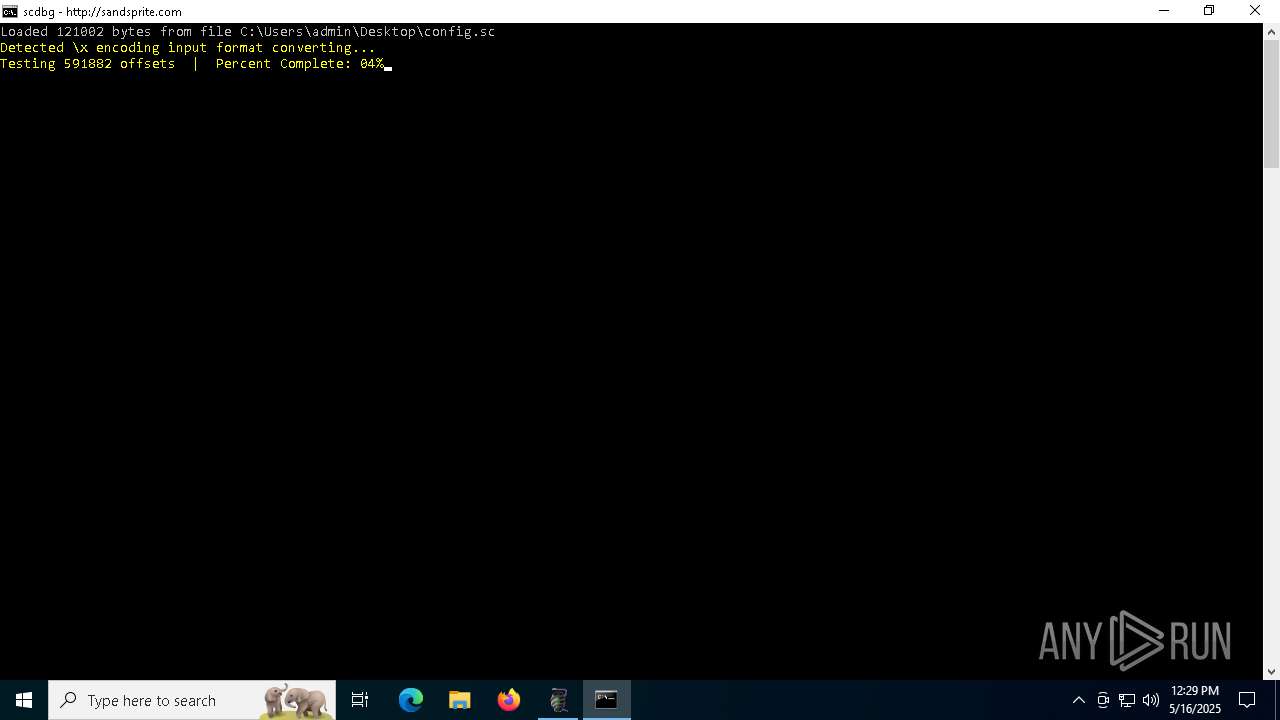
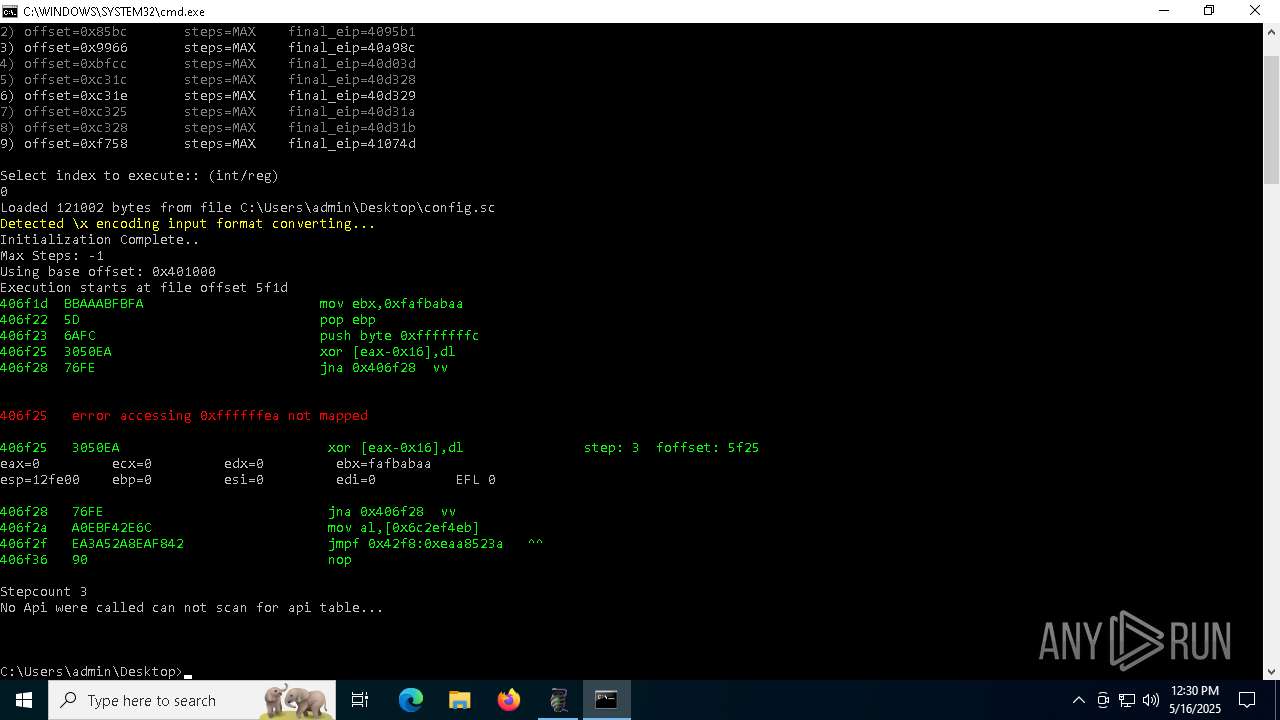
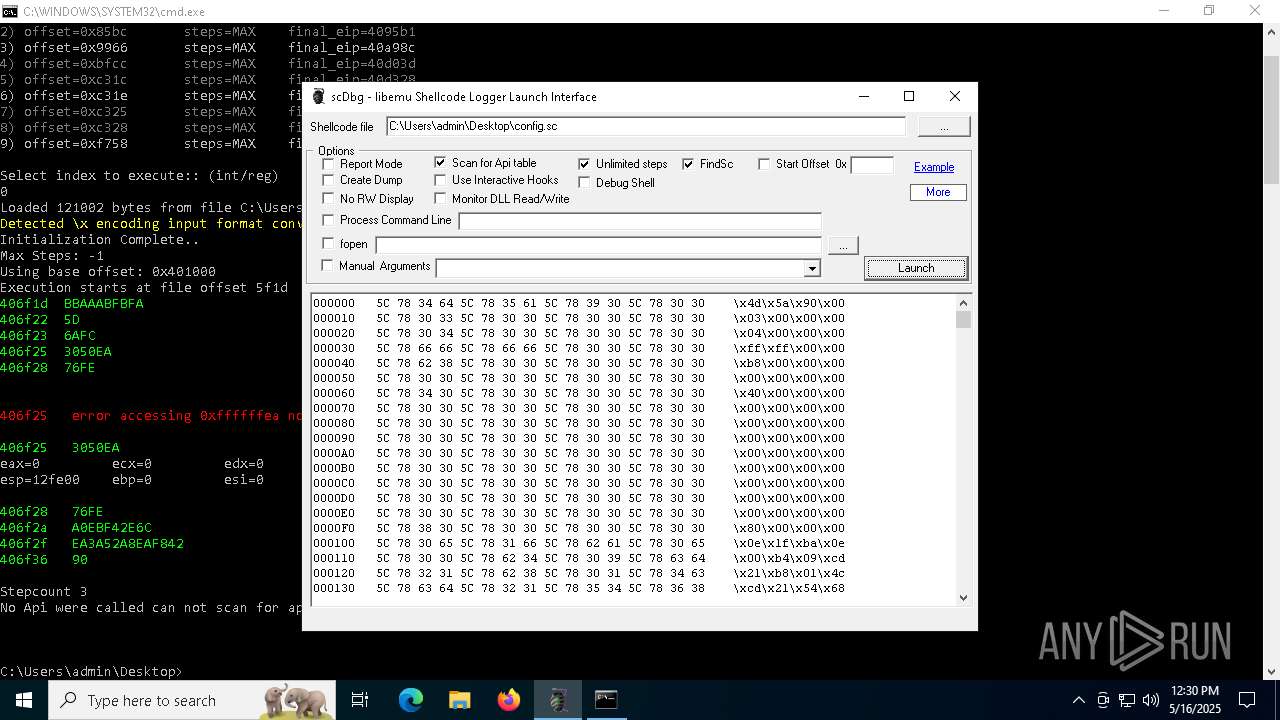
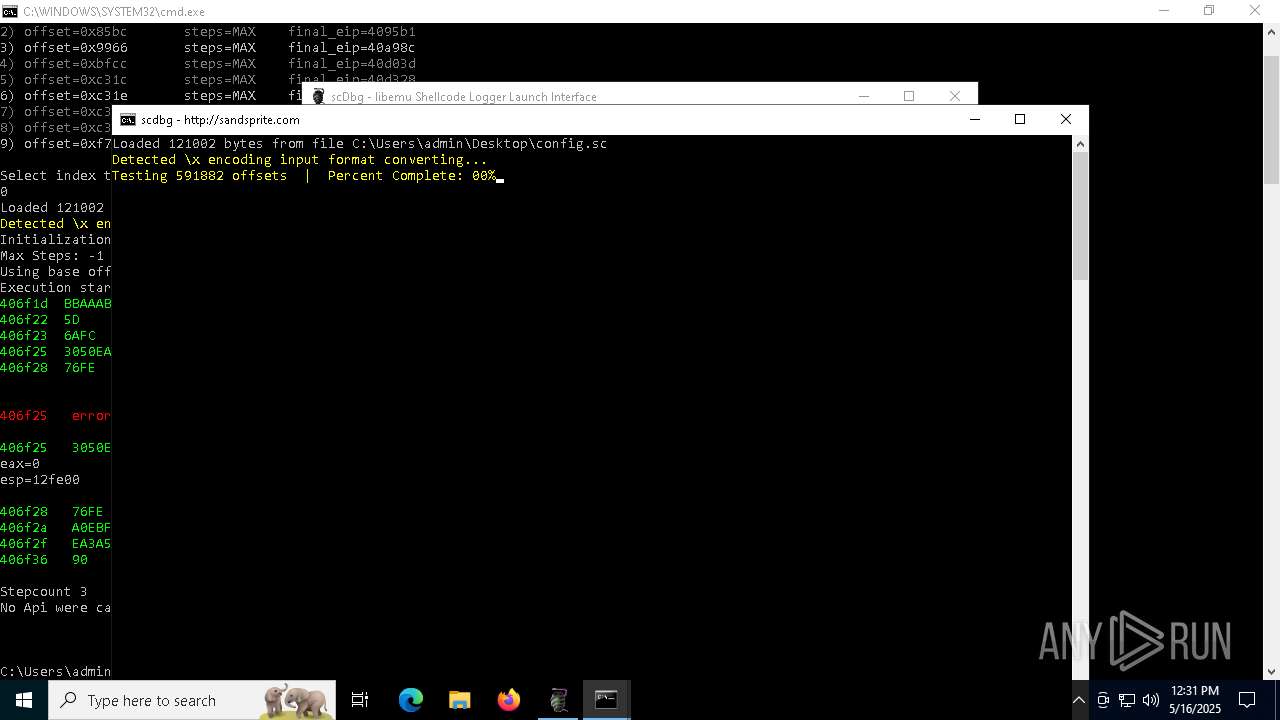
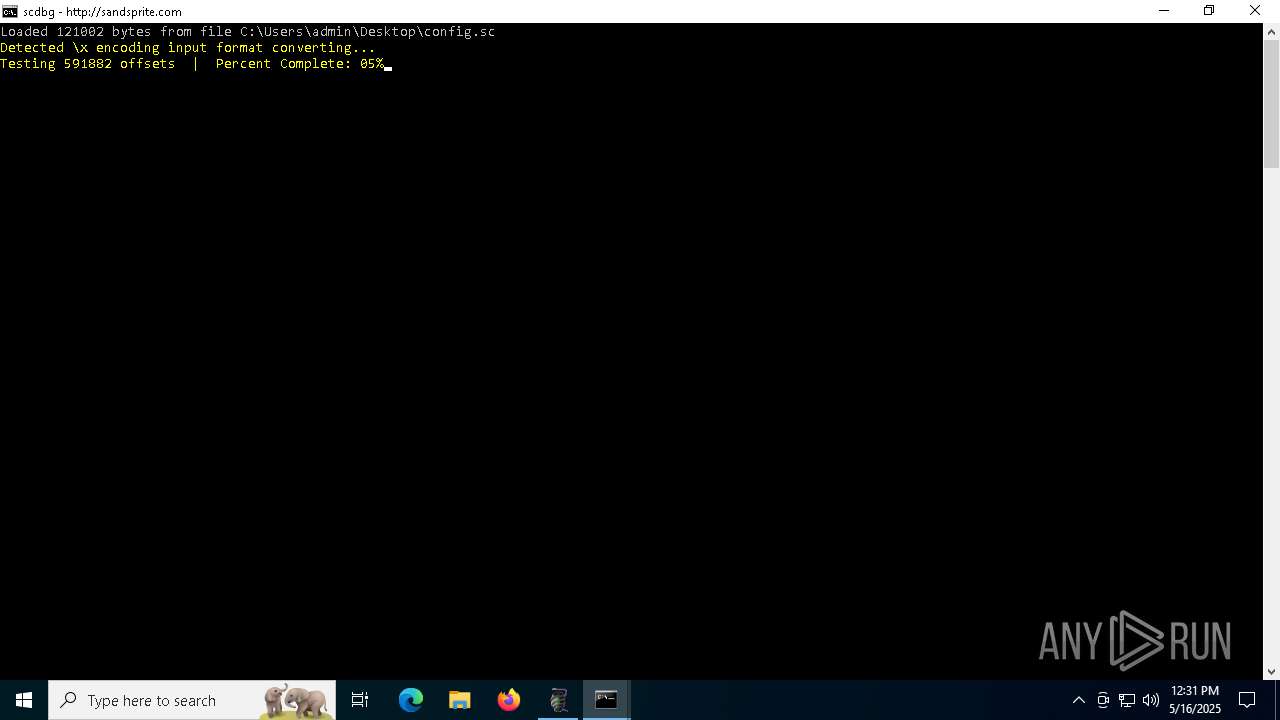
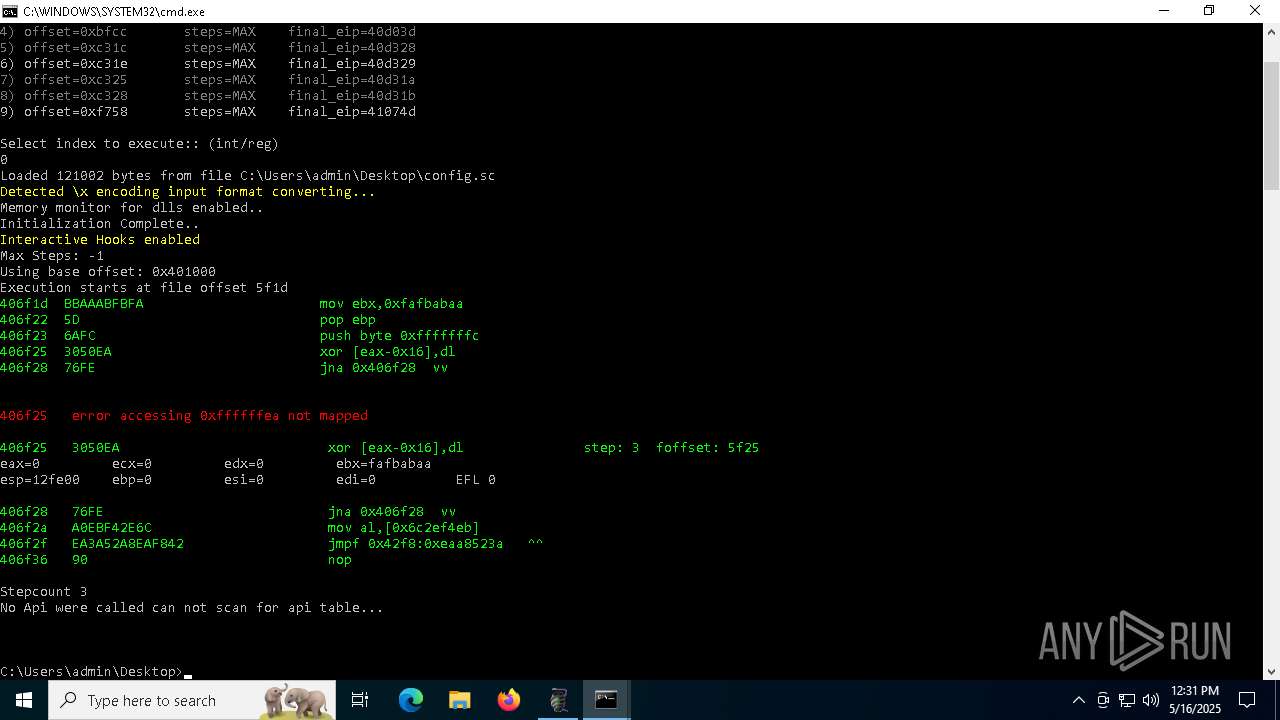
| 1676 | C:\Users\admin\Desktop\scdbg.exe -api -i -s -1 -findsc -mdll -f C:\Users\admin\Desktop\config.sc | C:\Users\admin\Desktop\scdbg.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3 Modules
| |||||||||||||||
| 2420 | scdbg.exe /f -s 100000000 config.sc | C:\Users\admin\Desktop\scdbg.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2504 | C:\Users\admin\Desktop\scdbg.exe -api -s -1 -findsc -f C:\Users\admin\Desktop\config.sc | C:\Users\admin\Desktop\scdbg.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3 Modules
| |||||||||||||||
| 2516 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\scdbg.zip" C:\Users\admin\Desktop\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2516 | scdbg.exe | C:\Users\admin\Desktop\scdbg.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
10 433
Read events
10 330
Write events
100
Delete events
3
Modification events
| (PID) Process: | (6656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\755b9e89416a664f52a0dfee6de54687f15ae900a7317763b0a4144996724f6a.zip | |||
| (PID) Process: | (6656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
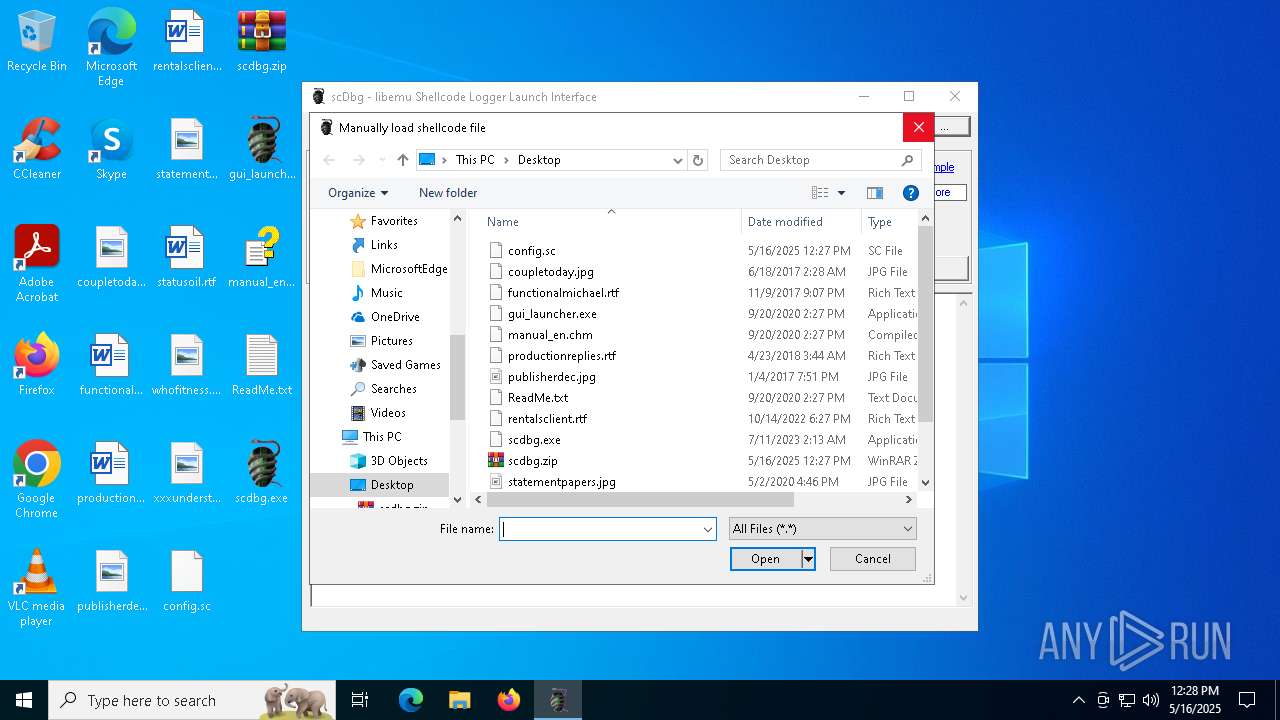
| 2516 | WinRAR.exe | C:\Users\admin\Desktop\gui_launcher.exe | executable | |
MD5:BF56803176596A68B180C2C25412EA71 | SHA256:02654879BC42871E8A4022A71D1EC7735568CC8714068A7C1753A51909266DE9 | |||
| 6576 | gui_launcher.exe | C:\Users\admin\AppData\Local\Temp\~DFA1A7149F13DE176F.TMP | binary | |
MD5:EE352C98413EDF7615C170BC55B5DEAE | SHA256:56D5C501EE431D01B7E8A575EFDB782711E2E174F8BC641991EC748E46E38123 | |||
| 2516 | WinRAR.exe | C:\Users\admin\Desktop\scdbg.exe | executable | |
MD5:20E4ECA7F5FE1CE430251BBB584F522B | SHA256:E2B9EC7D08EA722DC14242FC6AEFC39971AA00ED3FC26D8B84D77359BB462418 | |||
| 2516 | WinRAR.exe | C:\Users\admin\Desktop\manual_en.chm | binary | |
MD5:E2D80CA1B6AA5BD8454F7A4CE10FC755 | SHA256:C9D605BA51DA3B8E2648E150E404D6B5DE2D4B60E1896141D02F591590CA64CF | |||
| 2516 | WinRAR.exe | C:\Users\admin\Desktop\ReadMe.txt | text | |
MD5:FD29E3161C46ABB2FE1AF64B565BD877 | SHA256:CCCACEA67247CFA607532712B6C29893FE2B1E2136CC7EB421BD3270CFE00270 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
37
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
680 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
680 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
198.187.3.20.in-addr.arpa |
| unknown |