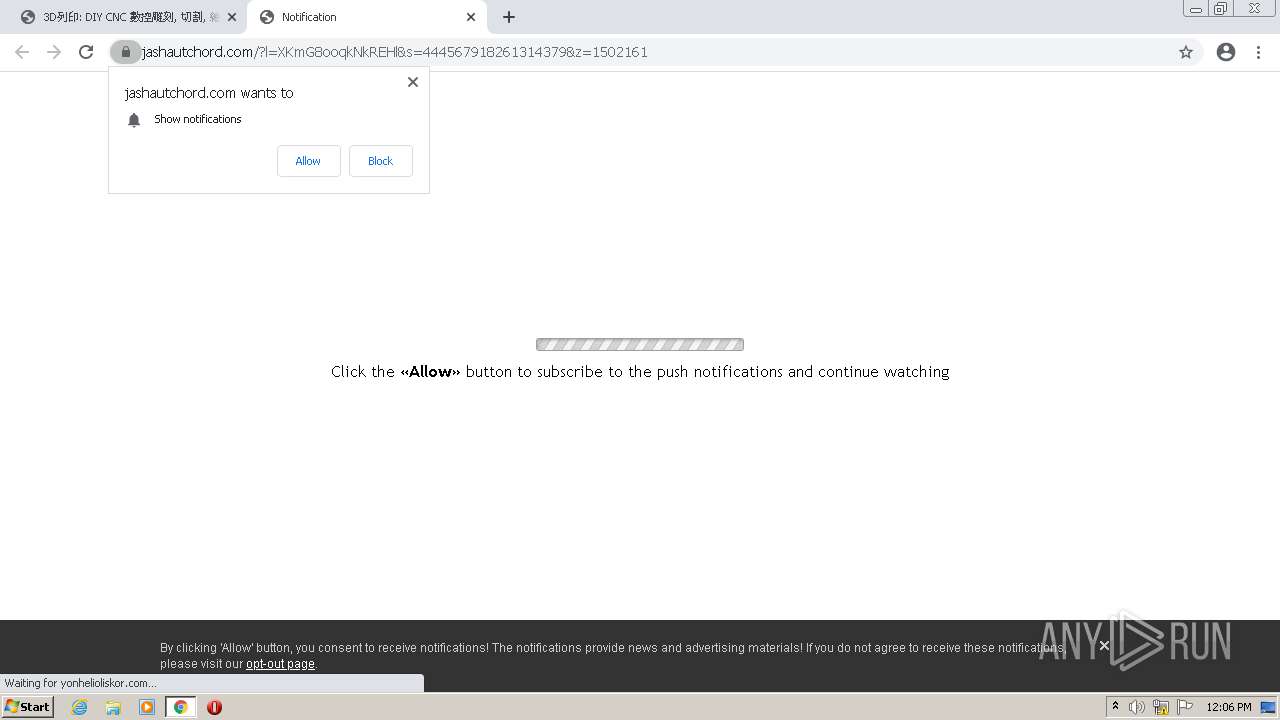
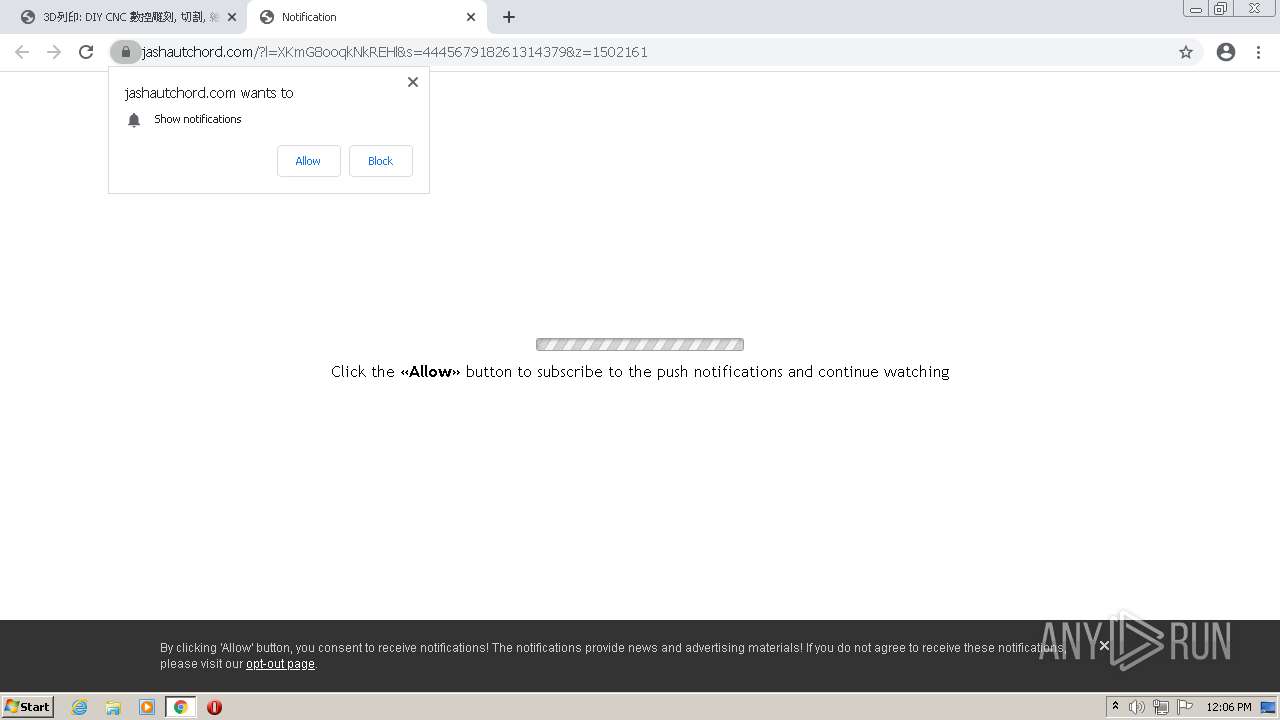
| URL: | https://rvwab.com/videos/watch/L0B8liHeKDU&wy=0&wx=0&ww=1920&wh=1040&cw=1903&wiw=1920&wih=937&wfc=2&sah=1040&drf |
| Full analysis: | https://app.any.run/tasks/41dd60cf-98ce-43ad-9160-4738ad39f6d7 |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2021, 11:05:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AA9DBA661FB217FB374F84E2071F199E |
| SHA1: | 751438641E3A411CEF204DD3D36A928F26358731 |
| SHA256: | 0AB416DDF6FC49860C5988B2679D51C44E07A01C288D21A30F0135FB7A1B38AC |
| SSDEEP: | 3:N8RyTKTlKAgdJIc4hDhYUcFiYAQ7NcJSDPSURp:2kKR26wUcZAQxccDfRp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Drops a file with a compile date too recent
- chrome.exe (PID: 2788)
INFO
Reads the computer name
- chrome.exe (PID: 2788)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 1420)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 2424)
- chrome.exe (PID: 1096)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 1136)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 3732)
Checks supported languages
- chrome.exe (PID: 2788)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 360)
- chrome.exe (PID: 1364)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 1184)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 1420)
- chrome.exe (PID: 1272)
- chrome.exe (PID: 1136)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 3760)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 1096)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 1332)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2424)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 736)
- chrome.exe (PID: 980)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 3464)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 3980)
- chrome.exe (PID: 412)
- chrome.exe (PID: 1444)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 3732)
Reads the hosts file
- chrome.exe (PID: 2444)
- chrome.exe (PID: 2788)
Reads settings of System Certificates
- chrome.exe (PID: 2444)
Application launched itself
- chrome.exe (PID: 2788)
Reads the date of Windows installation
- chrome.exe (PID: 1096)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
35
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5890924197468107845,17033049455559895741,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=patch.mojom.FilePatcher --field-trial-handle=1060,5890924197468107845,17033049455559895741,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3276 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5890924197468107845,17033049455559895741,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3824 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5890924197468107845,17033049455559895741,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ec8d988,0x6ec8d998,0x6ec8d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,5890924197468107845,17033049455559895741,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1740 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1060,5890924197468107845,17033049455559895741,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4044 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5890924197468107845,17033049455559895741,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5890924197468107845,17033049455559895741,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1392 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,5890924197468107845,17033049455559895741,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
15 318
Read events
15 205
Write events
108
Delete events
5
Modification events
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
137
Text files
186
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61028B9D-AE4.pma | — | |
MD5:— | SHA256:— | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:6410BEB61C9A892C95BF84D15FA91FF9 | SHA256:04880AE29B74FC17D94970BBABA1AC4E0D2801C29BA8161CC0ED6CA0ED6C63C4 | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF36e97e.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF36ead6.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF36f0e1.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\38f31d62-647c-4489-ae49-85162d5e76cb.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:CDB4EE2AEA69CC6A83331BBE96DC2CAA9A299D21329EFB0336FC02A82E1839A8 | |||
| 2788 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
127
DNS requests
103
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
904 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | — | — | whitelisted |
904 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | binary | 7.10 Kb | whitelisted |
904 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | pgc | 9.90 Kb | whitelisted |
904 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | binary | 719 Kb | whitelisted |
904 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/Pu4v-tN-kWF2q40ZuKM9Sg_9.28.0/AJF3c7ikkTZsKlD4Mc2H2vA | US | binary | 386 Kb | whitelisted |
904 | svchost.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/Pu4v-tN-kWF2q40ZuKM9Sg_9.28.0/AJF3c7ikkTZsKlD4Mc2H2vA | US | — | — | whitelisted |
904 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | bs | 9.90 Kb | whitelisted |
904 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AJD927i74k1lBFPyofryMko_1.3.36.91/bMPY3gg4TVlmGEtJqGkFyw | US | binary | 358 Kb | whitelisted |
904 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adfssds5ag3kelhtktgk3mu6bi2a_6759/hfnkpimlhhgieaddgfemjhofmfblmnib_6759_all_acnffmkwgtjl2vpr5nhg7ckj4haq.crx3 | US | crx | 24.8 Kb | whitelisted |
904 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTQ3QUFYQzF5VF9DcWNsa0ZkMGdTQmdvQQ/1.0.0.8_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | crx | 2.85 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2444 | chrome.exe | 151.101.1.229:443 | cdn.jsdelivr.net | Fastly | US | suspicious |
2444 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
2444 | chrome.exe | 142.250.185.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
2444 | chrome.exe | 104.21.30.223:443 | rvwab.com | Cloudflare Inc | US | suspicious |
2444 | chrome.exe | 192.99.8.28:443 | sstatic1.histats.com | OVH SAS | CA | suspicious |
2444 | chrome.exe | 139.45.197.238:443 | soaheeme.net | — | US | malicious |
2444 | chrome.exe | 139.45.195.8:443 | my.rtmark.net | — | US | suspicious |
2444 | chrome.exe | 139.45.197.237:443 | dozubatan.com | — | US | malicious |
2444 | chrome.exe | 142.250.185.97:443 | images1-focus-opensocial.googleusercontent.com | Google Inc. | US | whitelisted |
2444 | chrome.exe | 139.45.197.243:443 | onmarshtompor.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
rvwab.com |
| malicious |
clients2.google.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
images1-focus-opensocial.googleusercontent.com |
| whitelisted |
static.addtoany.com |
| whitelisted |
sstatic1.histats.com |
| malicious |
soaheeme.net |
| malicious |
my.rtmark.net |
| whitelisted |
propeller-tracking.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
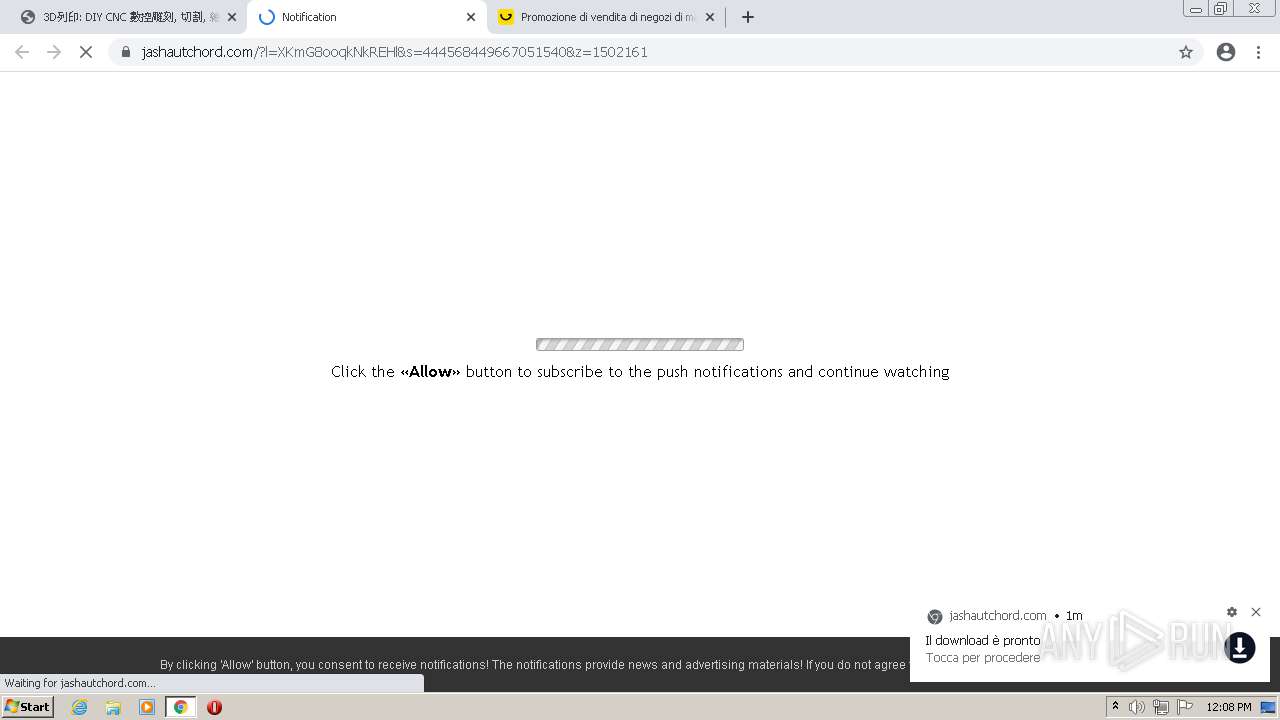
2444 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2444 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2444 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2444 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2444 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2444 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2444 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2444 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2444 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
2444 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |