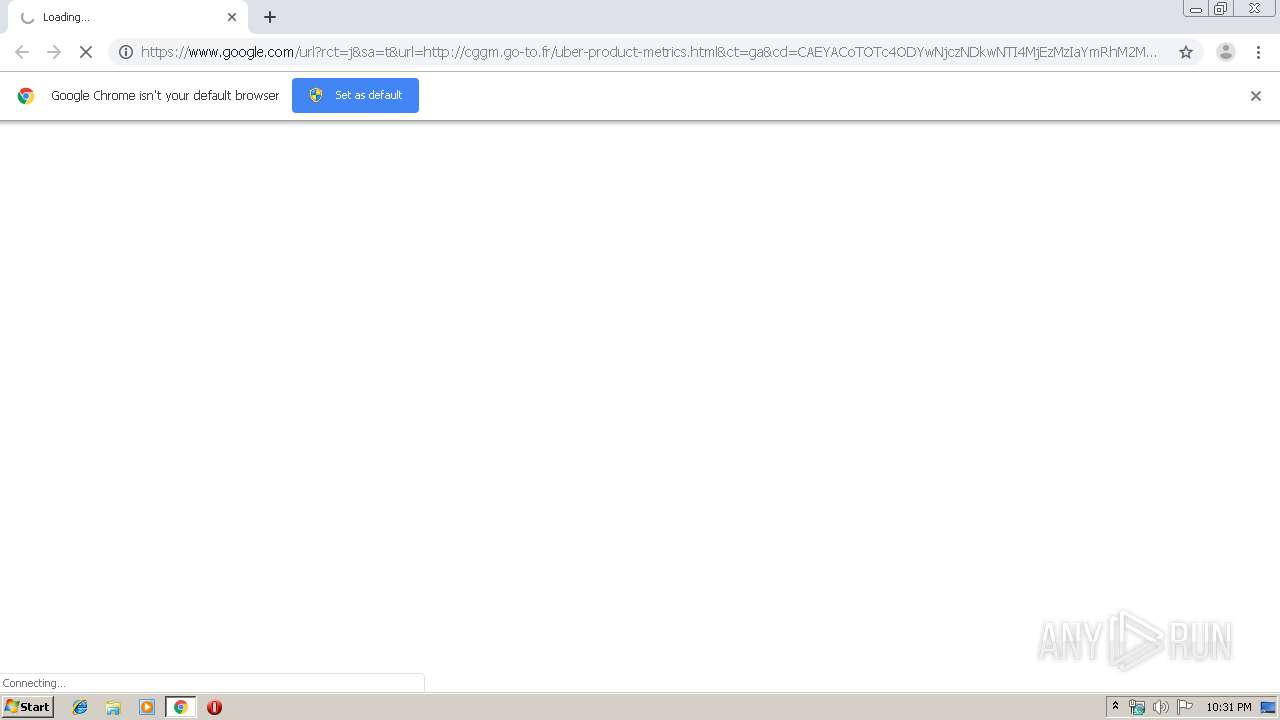
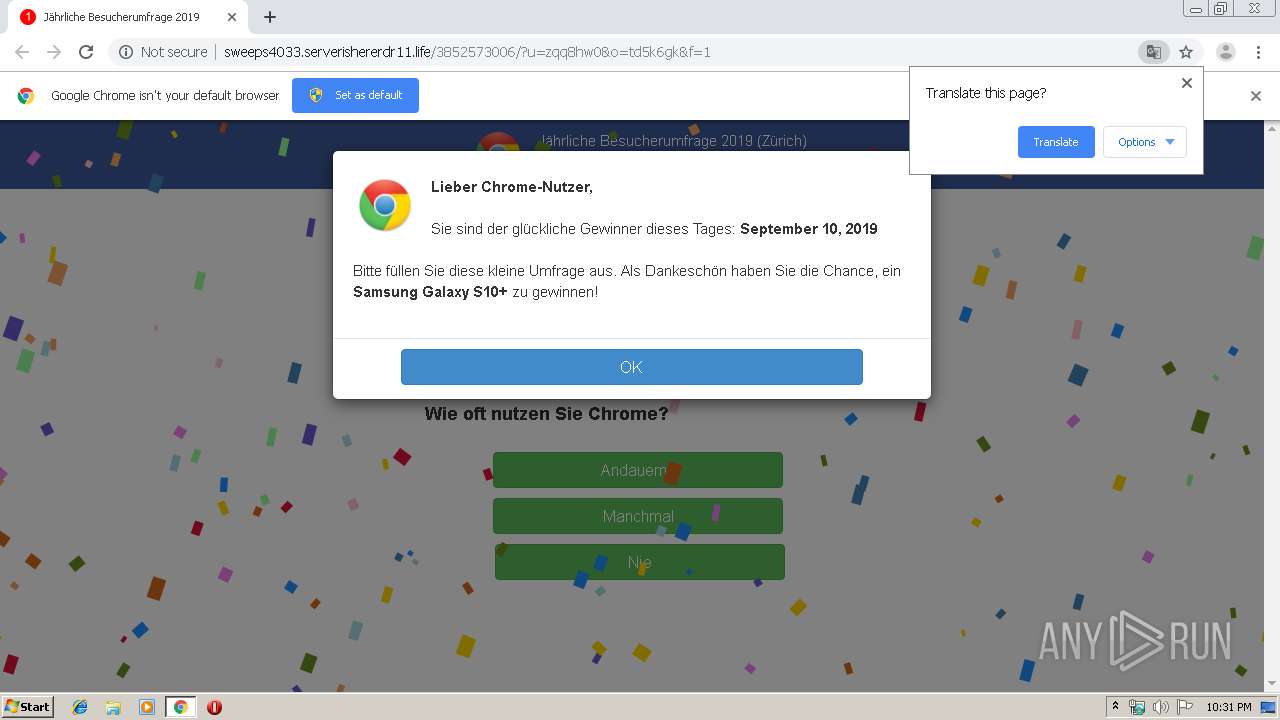
| URL: | https://www.google.com/url?rct=j&sa=t&url=http://cggm.go-to.fr/uber-product-metrics.html&ct=ga&cd=CAEYACoTOTc4ODYwNjczNDkwNTI4MjEzMzIaYmRhM2M4ZjVkN2UyNmU5Yzpjb206ZW46VVM&usg=AFQjCNHu0p_4GxdzgZBeuZLigcYDzX2Pag |
| Full analysis: | https://app.any.run/tasks/d84d9cbe-88a4-4d18-a7f5-2507d0f30d38 |
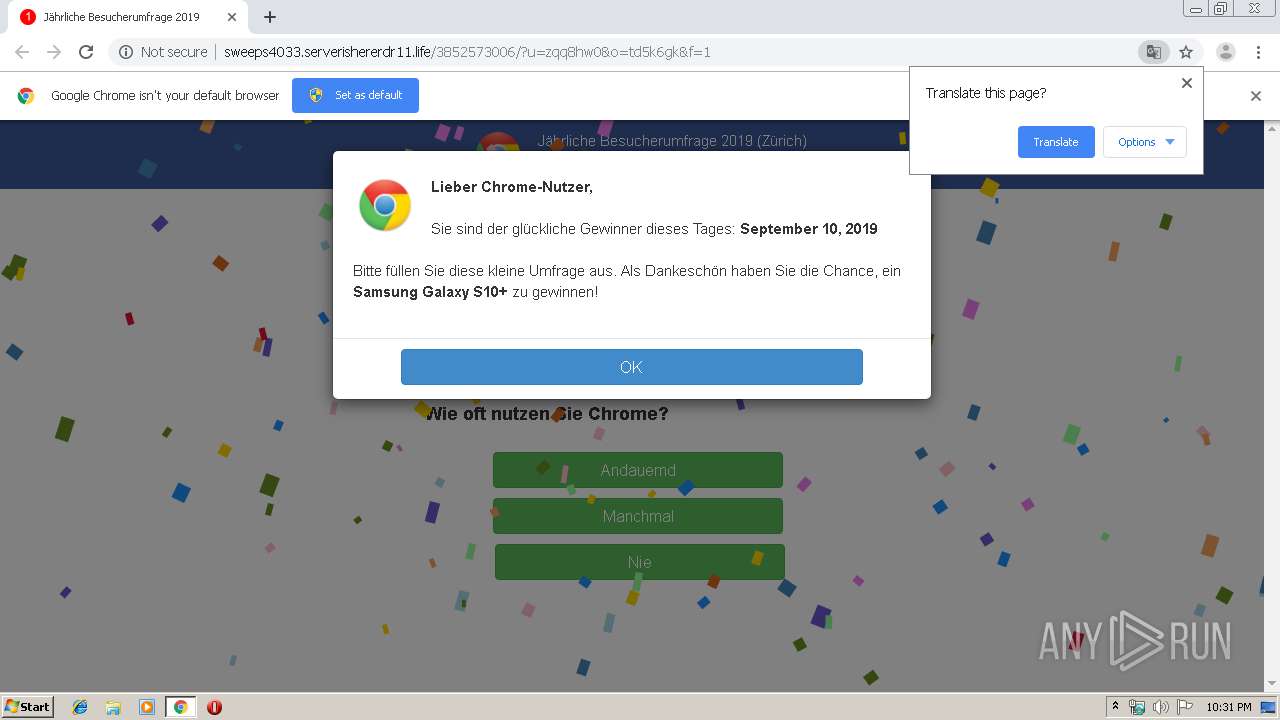
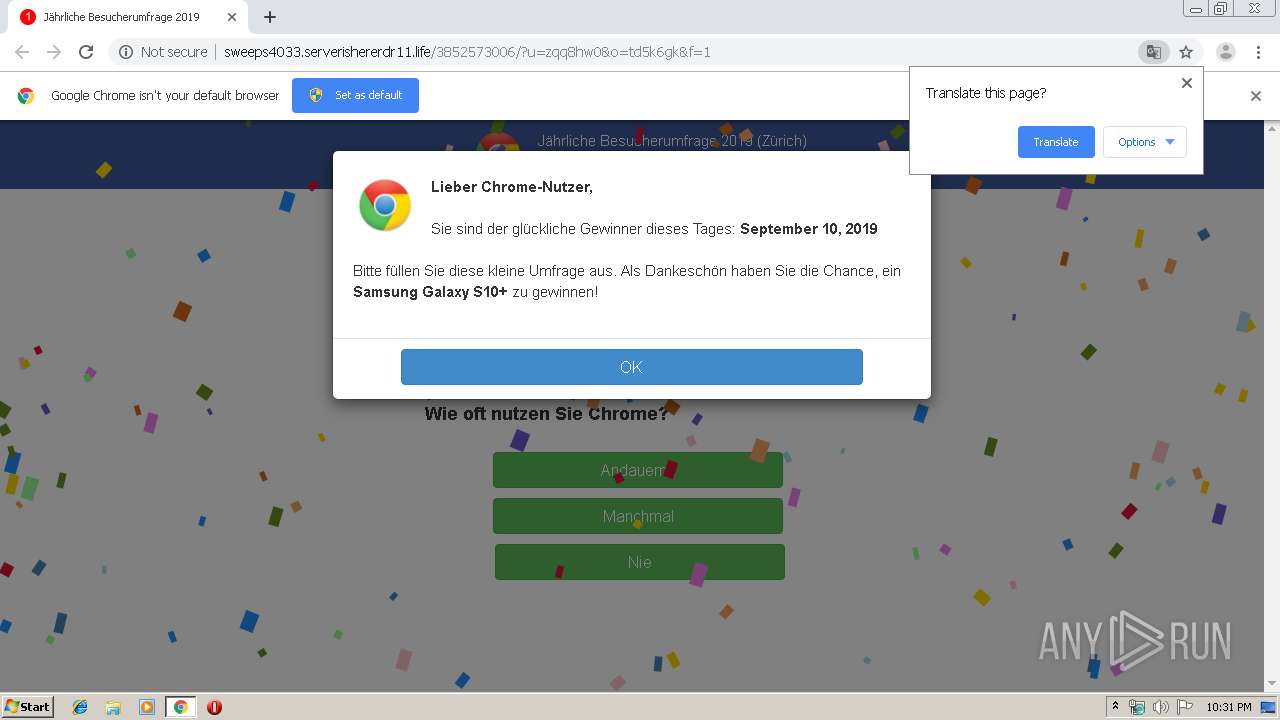
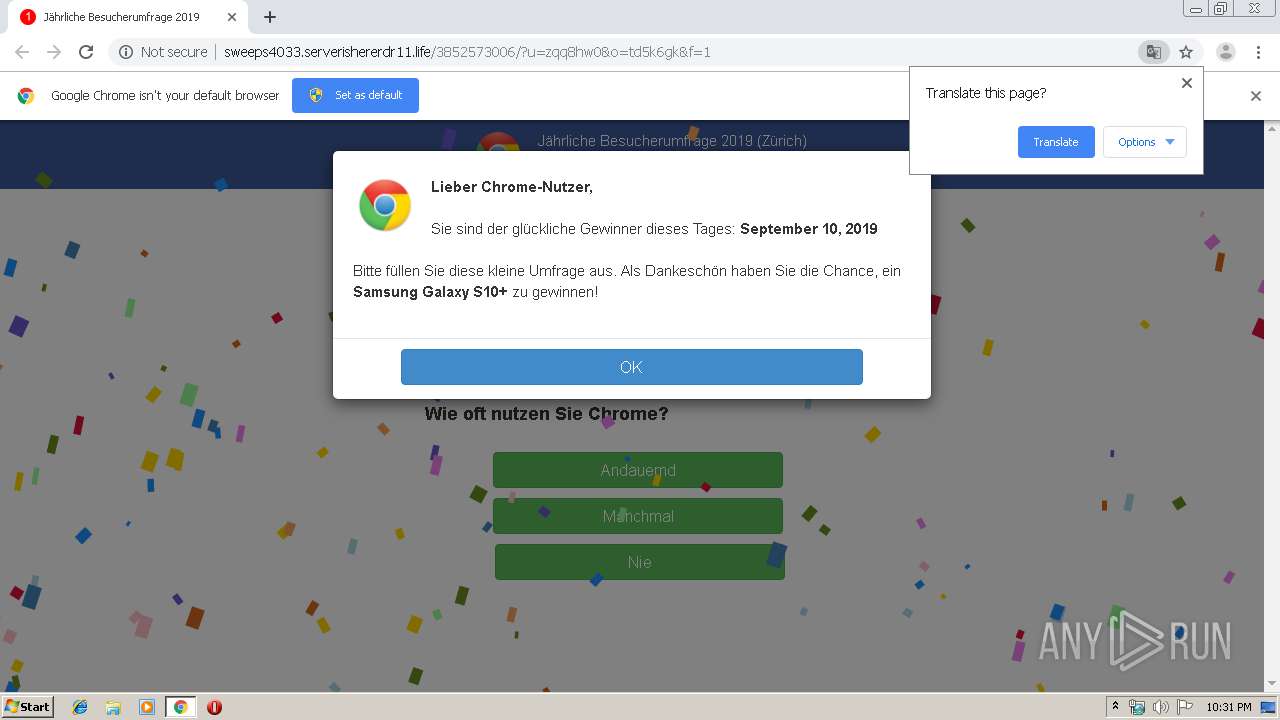
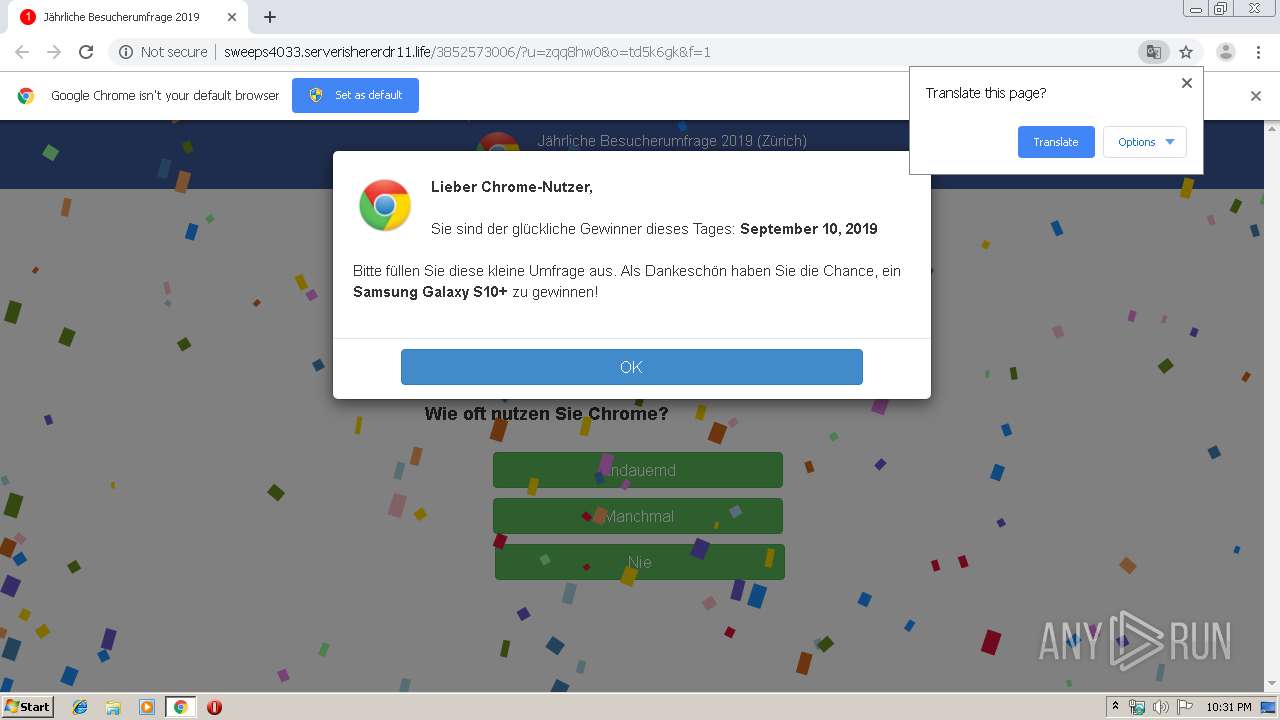
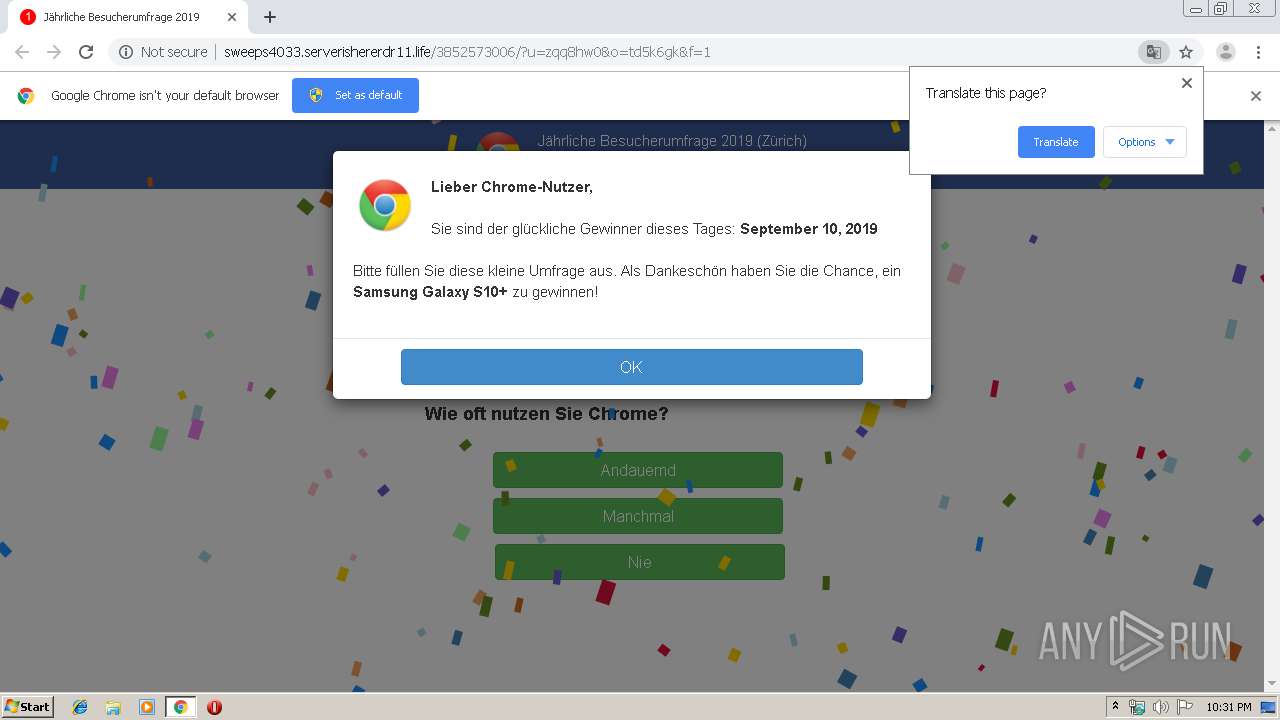
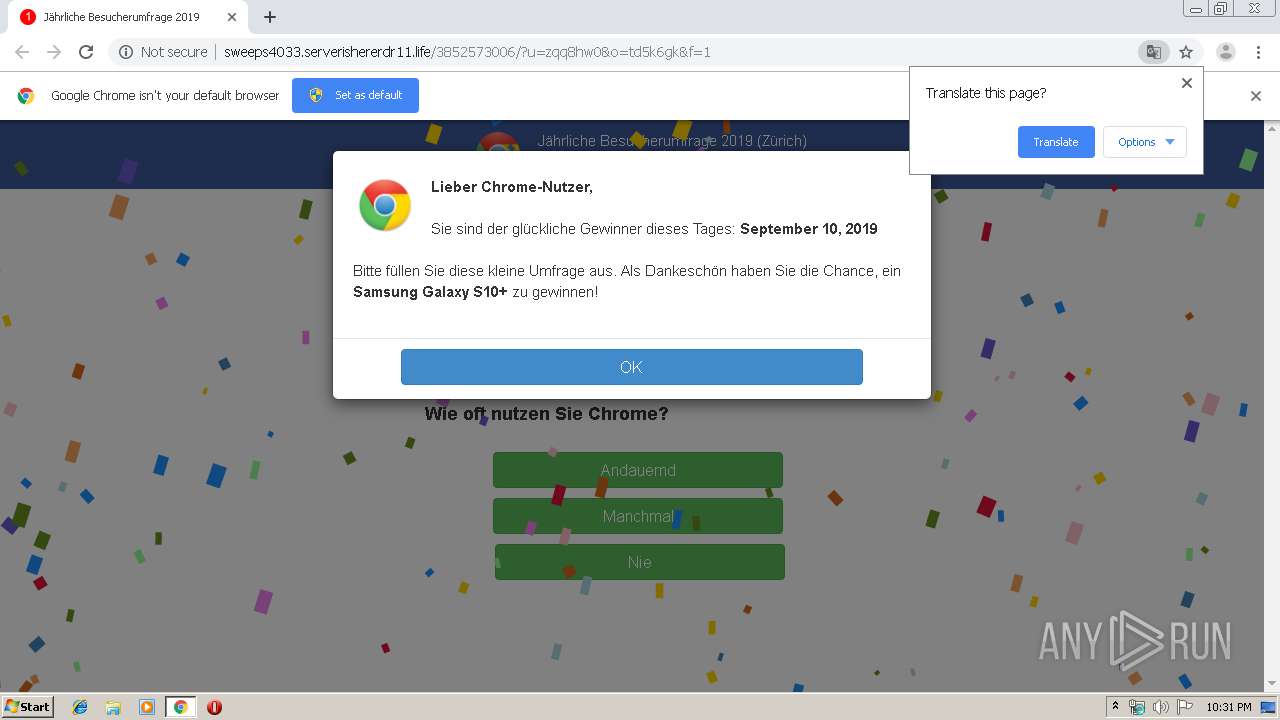
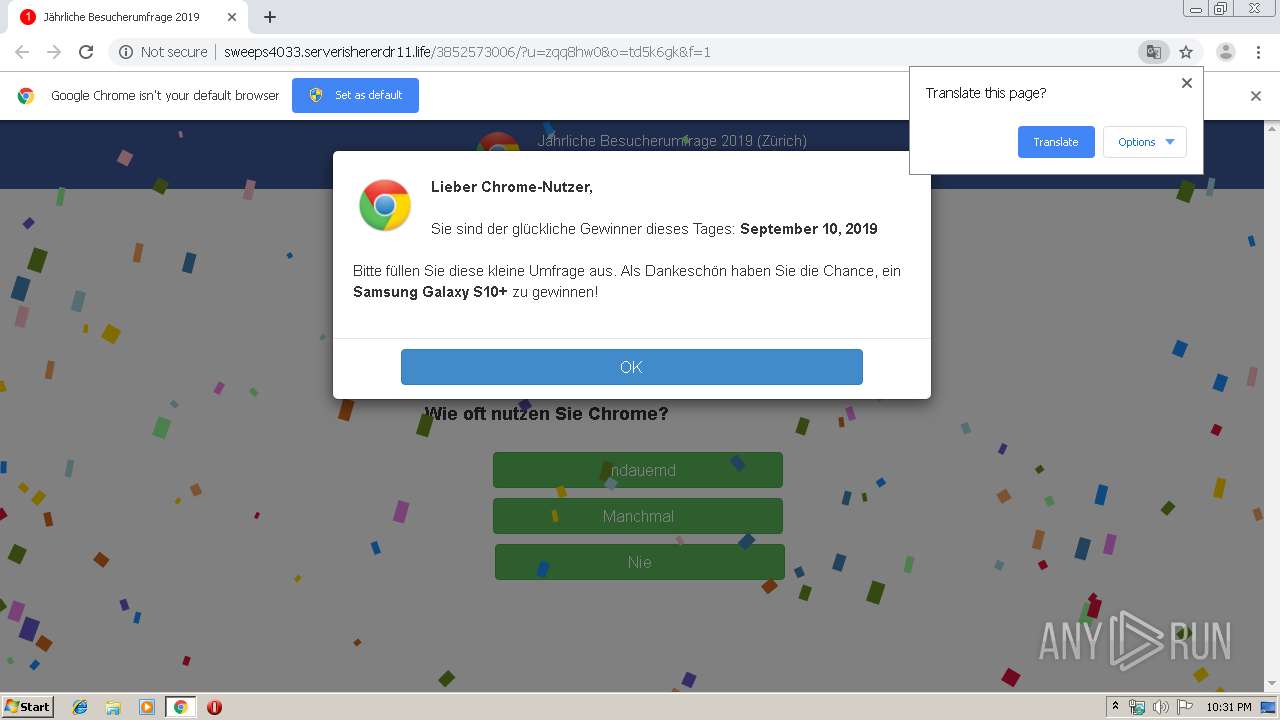
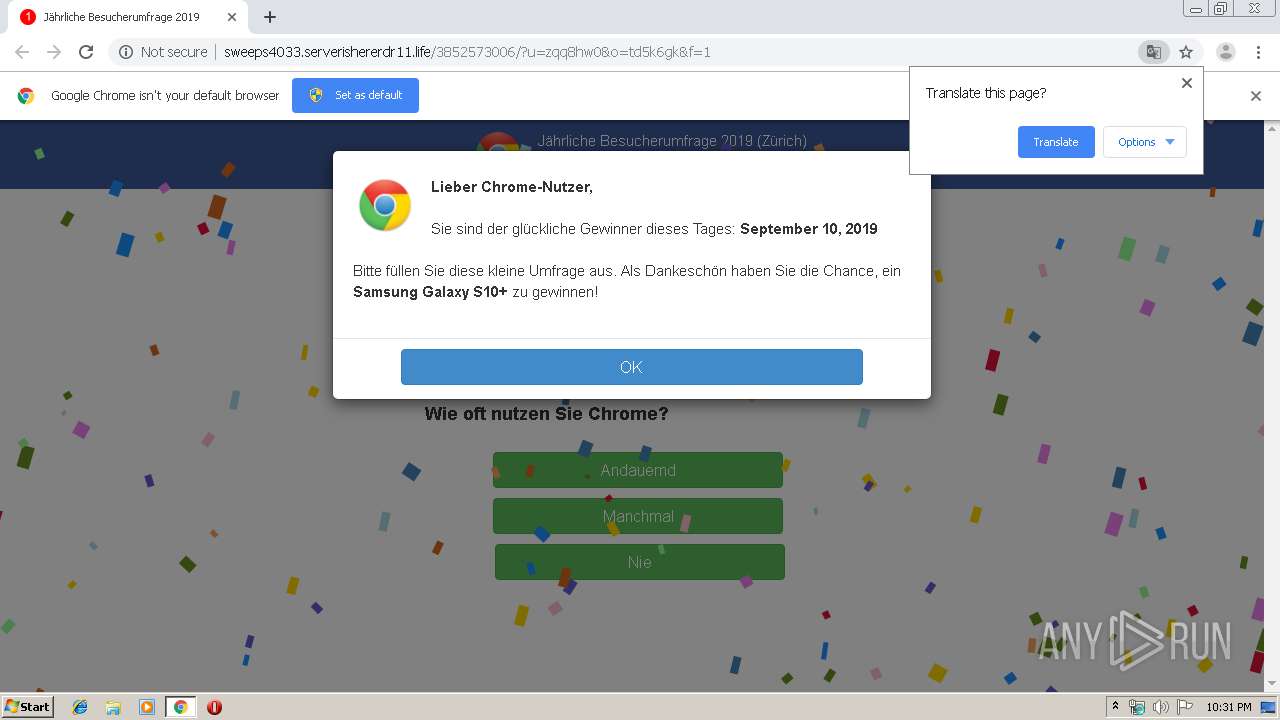
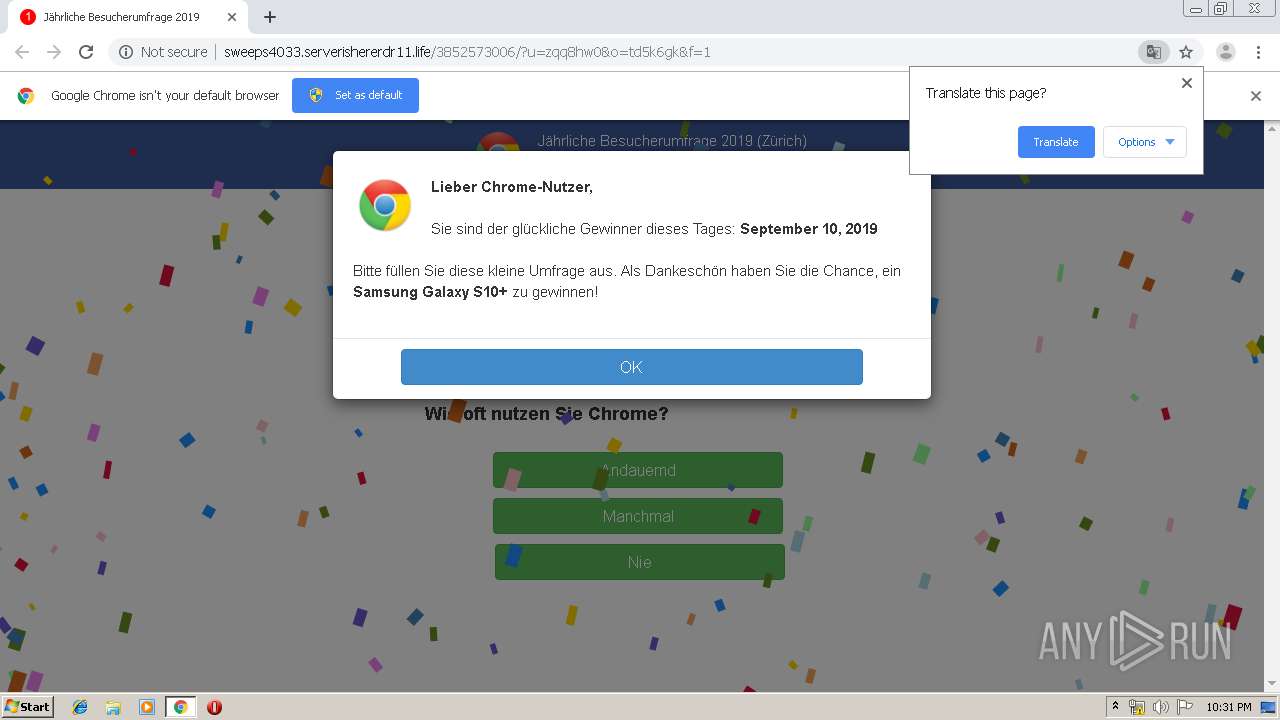
| Verdict: | Malicious activity |
| Analysis date: | September 10, 2019, 21:30:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B88C08F56389F12A55035D0FBF2B05B5 |
| SHA1: | 016D7DD4EE381559B84CB18F822C8F1EFD290718 |
| SHA256: | 0AB0F03E7B53DE2E7CCEA3121C4D6F3F7DD17C7F6C0407DAC25A986246ABB24C |
| SSDEEP: | 6:2OLI2AtURdCTfQQI7HKj2OxsHMIv0/PrCC:2V2SJCHK65HMbuC |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3448)
INFO
Application launched itself
- chrome.exe (PID: 3448)
Reads the hosts file
- chrome.exe (PID: 2976)
- chrome.exe (PID: 3448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,2886449756845325712,7010374824833954455,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14380555680134833873 --mojo-platform-channel-handle=2472 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fd9a9d0,0x6fd9a9e0,0x6fd9a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,2886449756845325712,7010374824833954455,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13034281081803327633 --mojo-platform-channel-handle=1028 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,2886449756845325712,7010374824833954455,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8291045353645052412 --mojo-platform-channel-handle=2224 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,2886449756845325712,7010374824833954455,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15561039314602064516 --mojo-platform-channel-handle=3868 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,2886449756845325712,7010374824833954455,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17213840525956968974 --mojo-platform-channel-handle=2340 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,2886449756845325712,7010374824833954455,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8299283185172028259 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,2886449756845325712,7010374824833954455,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18147687699976492502 --mojo-platform-channel-handle=1640 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,2886449756845325712,7010374824833954455,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14362272515693931848 --mojo-platform-channel-handle=3956 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,2886449756845325712,7010374824833954455,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3127347075337571853 --mojo-platform-channel-handle=3156 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
610
Read events
524
Write events
81
Delete events
5
Modification events
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3448-13212624662069500 |
Value: 259 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3448) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
23
Text files
230
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\703e90cc-e3e0-4224-b0e4-aff84ca1e581.tmp | — | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169cb2.TMP | text | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169ce1.TMP | text | |
MD5:— | SHA256:— | |||
| 3448 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
26
DNS requests
13
Threats
40
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2976 | chrome.exe | GET | 302 | 104.28.29.89:80 | http://cggm.go-to.fr/uber-product-metrics.html | US | — | — | shared |
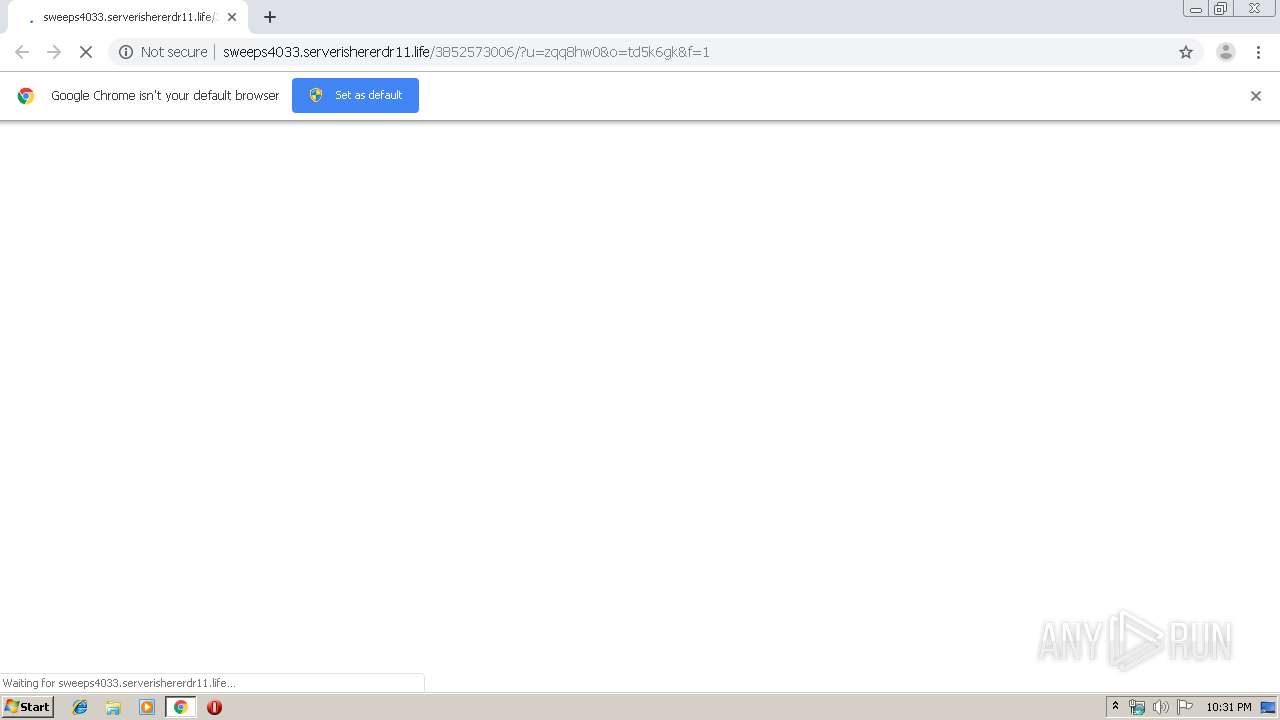
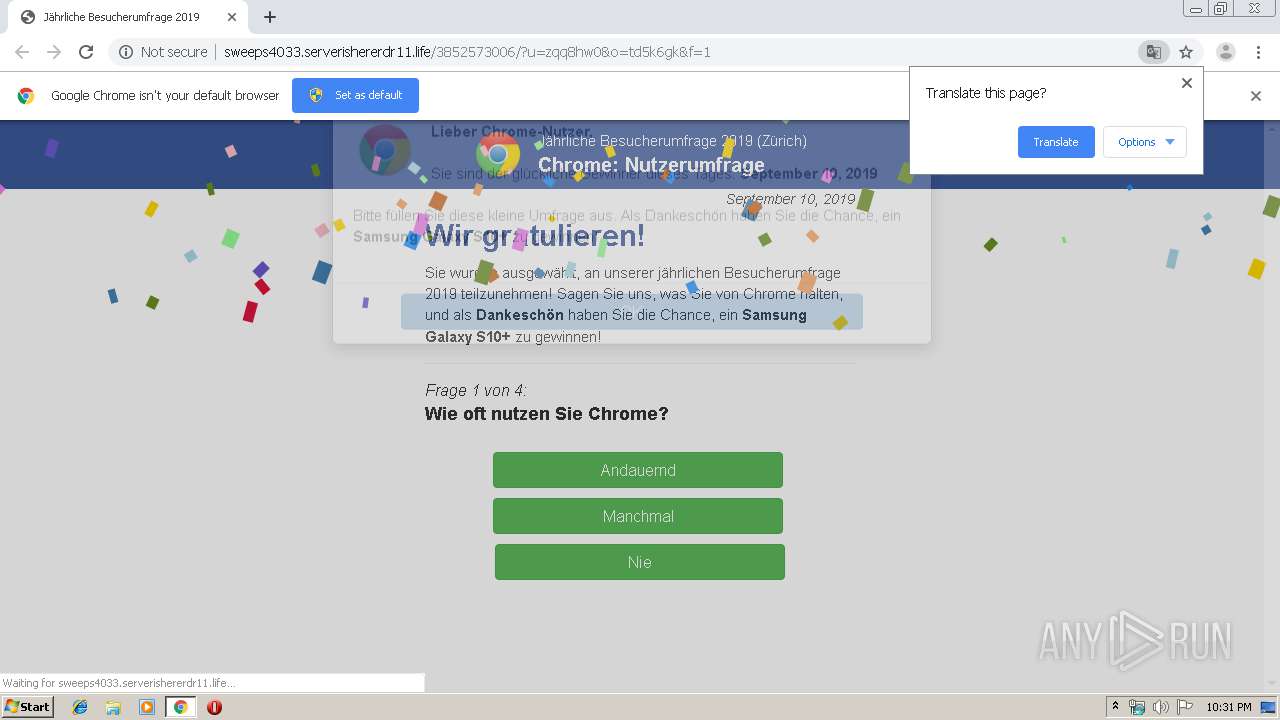
2976 | chrome.exe | GET | 200 | 185.89.102.7:80 | http://sweeps4033.serverishererdr11.life/media/mainstream/us/wap/mobsurvey/logo1.js | UA | text | 12.7 Kb | suspicious |
2976 | chrome.exe | GET | 200 | 185.89.102.7:80 | http://sweeps4033.serverishererdr11.life/3852573006/?u=zqq8hw0&o=td5k6gk&f=1 | UA | html | 16.8 Kb | suspicious |
2976 | chrome.exe | GET | 200 | 185.89.102.7:80 | http://sweeps4033.serverishererdr11.life/media/mainstream/us/wap/mobsurvey/comment.js | UA | text | 2.77 Kb | suspicious |
2976 | chrome.exe | GET | 200 | 185.89.102.7:80 | http://sweeps4033.serverishererdr11.life/media/mainstream/de/wap/mobsurvey/modernizr-2.6.2-respond-1.1.0.min.js | UA | html | 17.8 Kb | suspicious |
2976 | chrome.exe | GET | 200 | 185.89.102.7:80 | http://sweeps4033.serverishererdr11.life/media/mainstream/de/wap/mobsurvey/main.css | UA | text | 7.03 Kb | suspicious |
2976 | chrome.exe | GET | 200 | 185.89.102.7:80 | http://sweeps4033.serverishererdr11.life/media/mainstream/de/wap/mobsurvey/de-en.js | UA | text | 5.03 Kb | suspicious |
2976 | chrome.exe | GET | 200 | 185.89.102.7:80 | http://sweeps4033.serverishererdr11.life/media/mainstream/us/wap/mobsurvey/logo2.js | UA | text | 12.8 Kb | suspicious |
2976 | chrome.exe | GET | 200 | 185.89.102.7:80 | http://sweeps4033.serverishererdr11.life/media/mainstream/de/wap/mobsurvey/font-awesome.css | UA | text | 17.2 Kb | suspicious |
2976 | chrome.exe | GET | 200 | 185.89.102.7:80 | http://sweeps4033.serverishererdr11.life/media/mainstream/de/wap/mobsurvey/returnDate.de.js | UA | text | 1.23 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2976 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2976 | chrome.exe | 79.110.27.103:443 | take-prizes-here4.life | — | UA | suspicious |
2976 | chrome.exe | 216.58.206.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2976 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
— | — | 216.58.206.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
— | — | 173.194.160.70:80 | r1---sn-1gi7znes.gvt1.com | Google Inc. | US | whitelisted |
2976 | chrome.exe | 185.89.102.7:80 | sweeps4033.serverishererdr11.life | LLHost Inc | UA | suspicious |
2976 | chrome.exe | 173.194.160.70:80 | r1---sn-1gi7znes.gvt1.com | Google Inc. | US | whitelisted |
2976 | chrome.exe | 172.217.21.234:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
2976 | chrome.exe | 185.50.248.72:443 | tdsjsext1.com | LLHost Inc | RO | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cggm.go-to.fr |
| unknown |
take-prizes-here4.life |
| suspicious |
sweeps4033.serverishererdr11.life |
| suspicious |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-1gi7znes.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
2976 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
2976 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2976 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2976 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2976 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2976 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2976 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
2976 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.life Domain |
1 ETPRO signatures available at the full report